| URL: | https://app.pandadoc.com/document/v2?token=2126fee3194112970cb23c51d0c56249323ace2b |
| Full analysis: | https://app.any.run/tasks/5adeab36-f039-4327-bd91-b9b804525b9b |
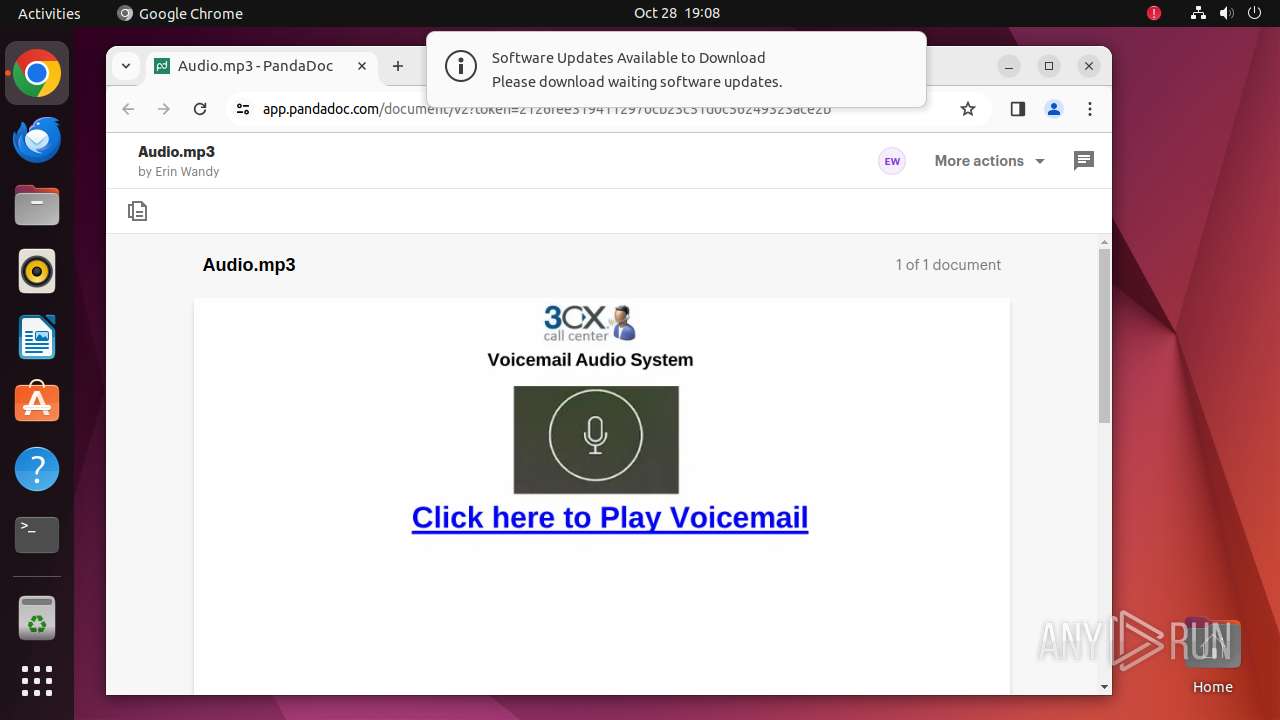
| Verdict: | Malicious activity |
| Analysis date: | October 28, 2024, 19:08:16 |
| OS: | Ubuntu 22.04.2 LTS |
| Tags: | |
| Indicators: | |
| MD5: | 39DDACA272376EF6E68128B0B4BBC535 |
| SHA1: | B0312227B2AA25FDD942C33A6BCA49611D5B7B94 |
| SHA256: | 91A2F30B070E39F6F5C7CA3579ADC16BB3801D564B10B371B438D93270FCCC5C |
| SSDEEP: | 3:N8aSOB3IK8JRqZ7D2yOjVCWHUBsA1Ws:2a73IBJEZWy+gWHU6A17 |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 445)
SUSPICIOUS
Reads /proc/mounts (likely used to find writable filesystems)
- python3.10 (PID: 36070)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
315
Monitored processes
99
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 35783 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://app\.pandadoc\.com/document/v2?token=2126fee3194112970cb23c51d0c56249323ace2b " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 35784 | sudo -iu user google-chrome https://app.pandadoc.com/document/v2?token=2126fee3194112970cb23c51d0c56249323ace2b | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 35785 | /usr/bin/google-chrome https://app.pandadoc.com/document/v2?token=2126fee3194112970cb23c51d0c56249323ace2b | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 35786 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35787 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35788 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35789 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 35790 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 35791 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
240
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 35785 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 35785 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
92
DNS requests
120
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.49:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.49:80 | changelogs.ubuntu.com | Canonical Group Limited | US | whitelisted |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 169.150.255.181:443 | odrs.gnome.org | — | GB | whitelisted |
— | — | 207.211.211.26:443 | odrs.gnome.org | — | US | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
35830 | chrome | 172.217.16.195:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
35785 | chrome | 239.255.255.250:1900 | — | — | — | whitelisted |
35830 | chrome | 173.194.79.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
35830 | chrome | 142.250.185.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
odrs.gnome.org |
| whitelisted |
google.com |
| whitelisted |
connectivity-check.ubuntu.com |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
app.pandadoc.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
x4whrmz.x.incapdns.net |
| unknown |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
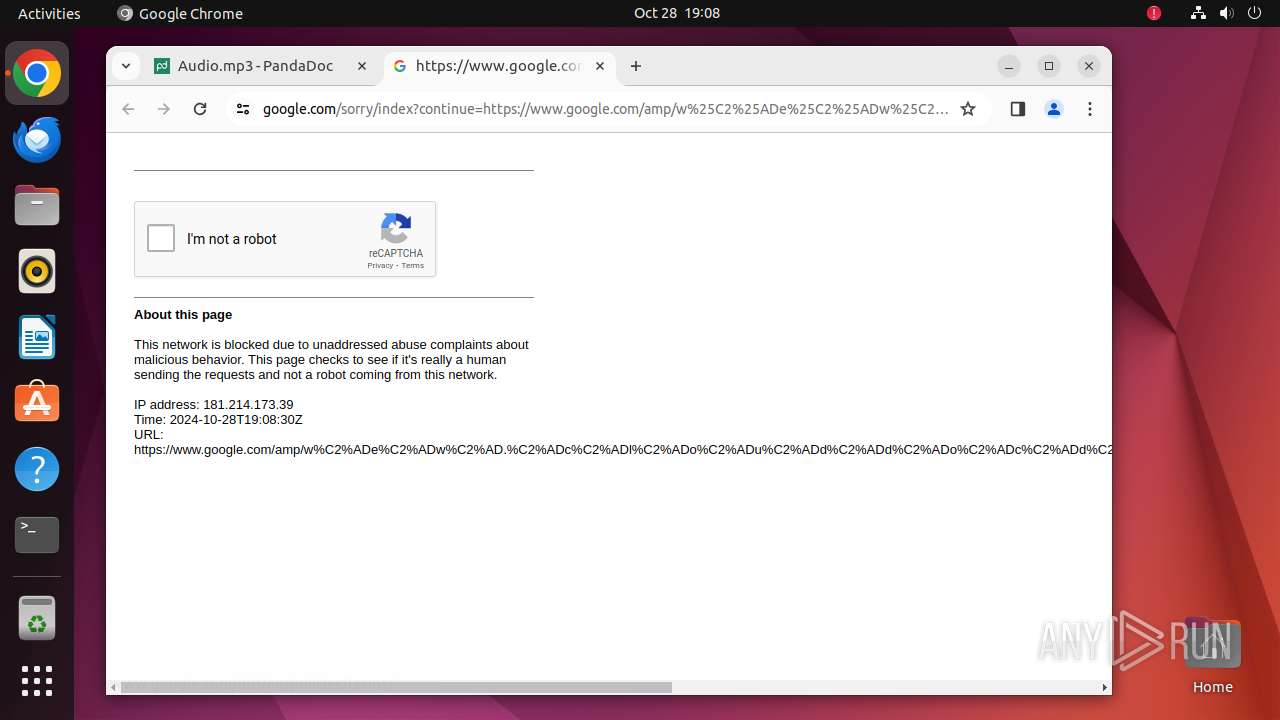
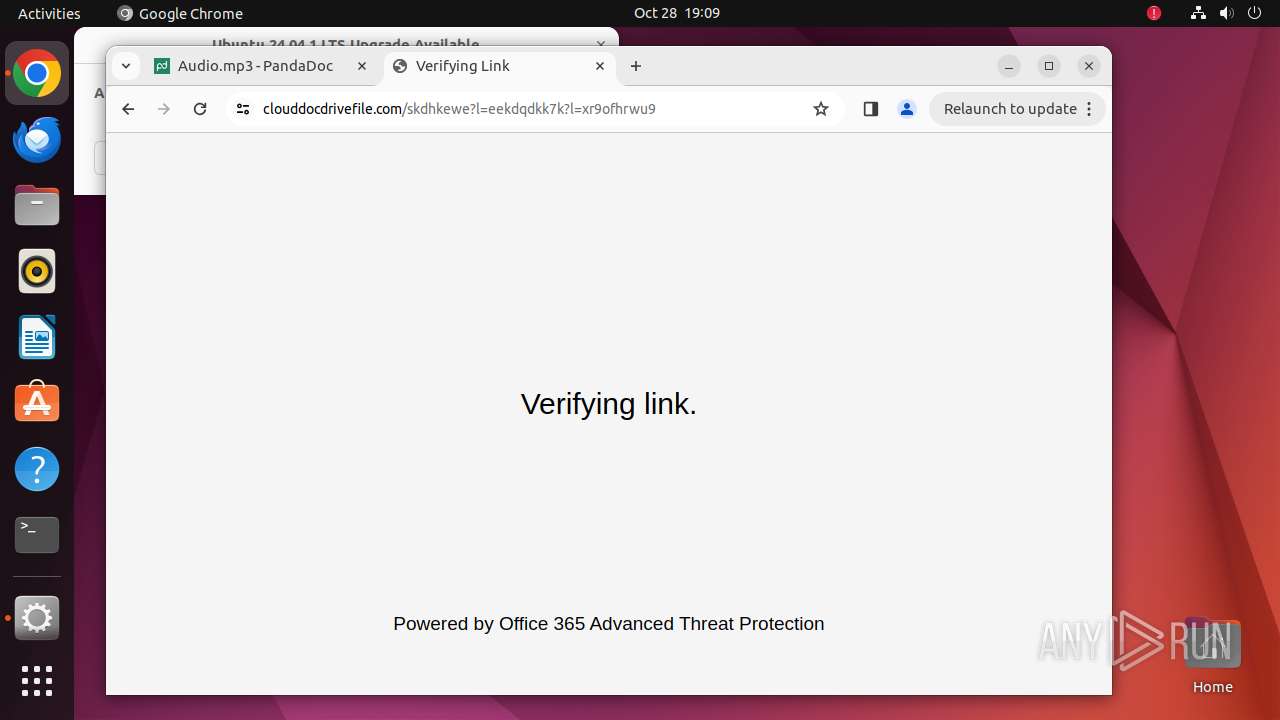
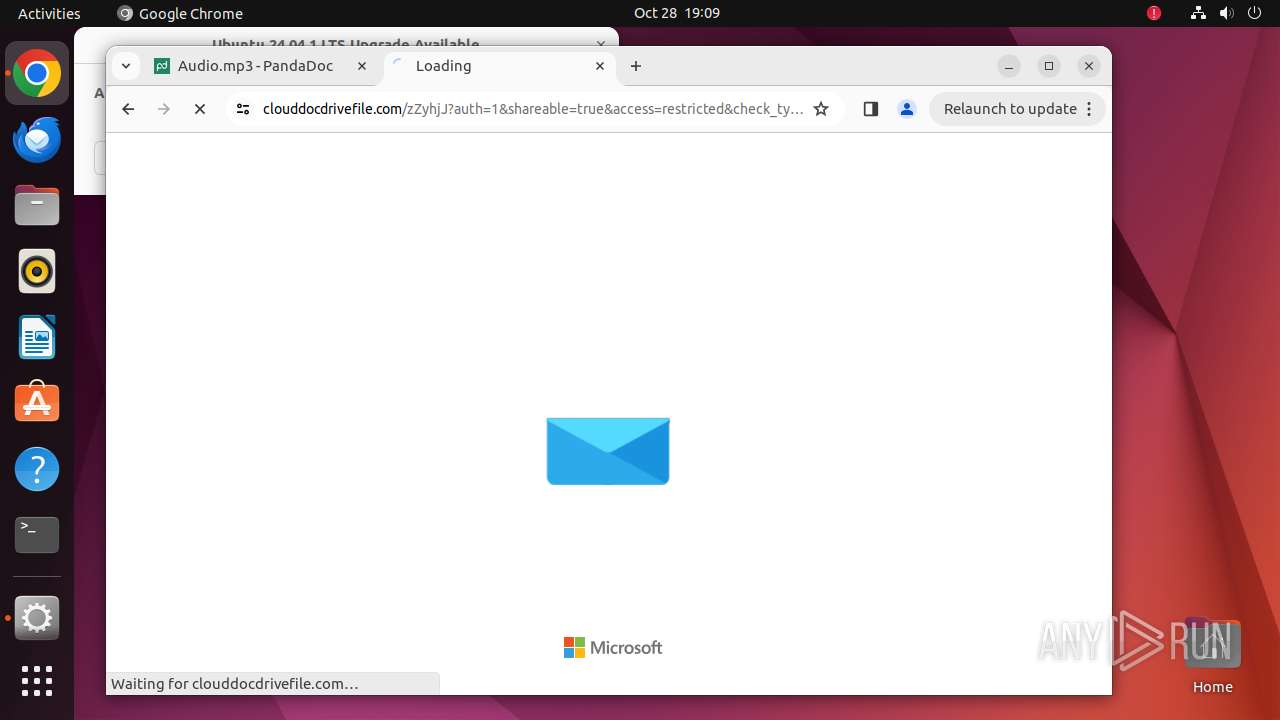
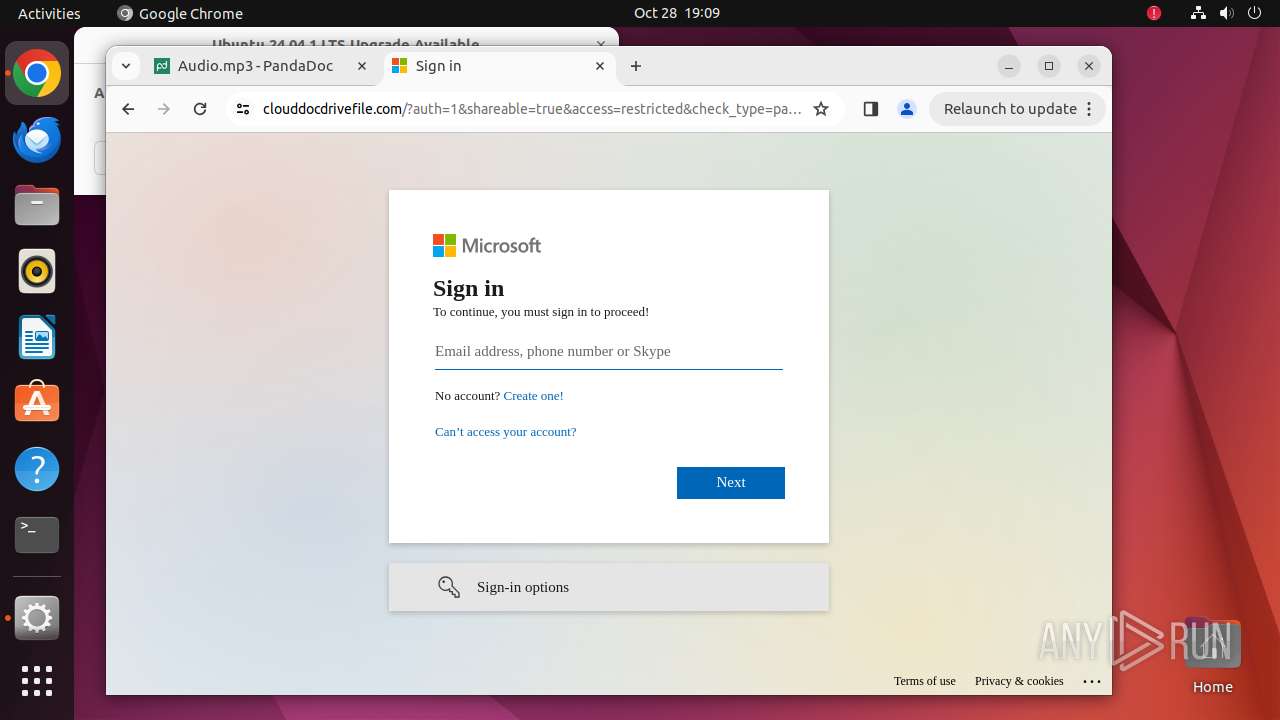
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by CrossDomain ( .clouddocdrivefile .com) |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing Domain by CrossDomain ( .clouddocdrivefile .com) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Request to Azure content delivery network (aadcdn .msauth .net) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |