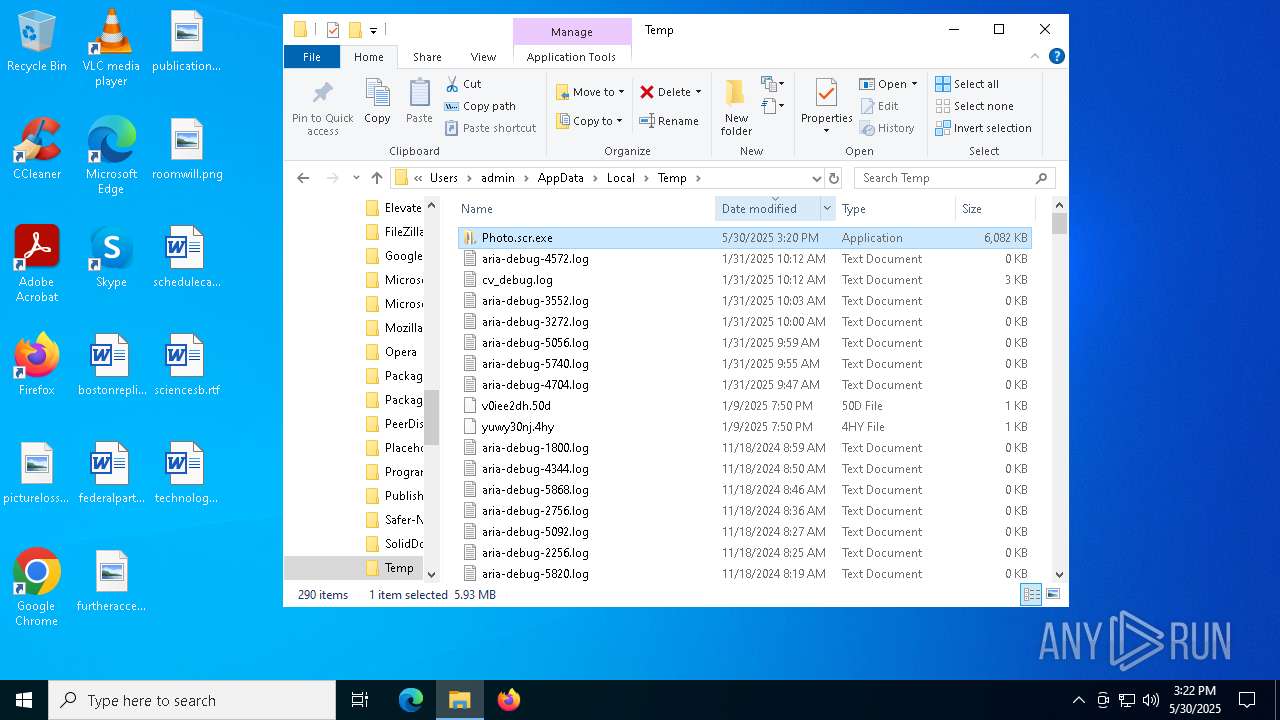
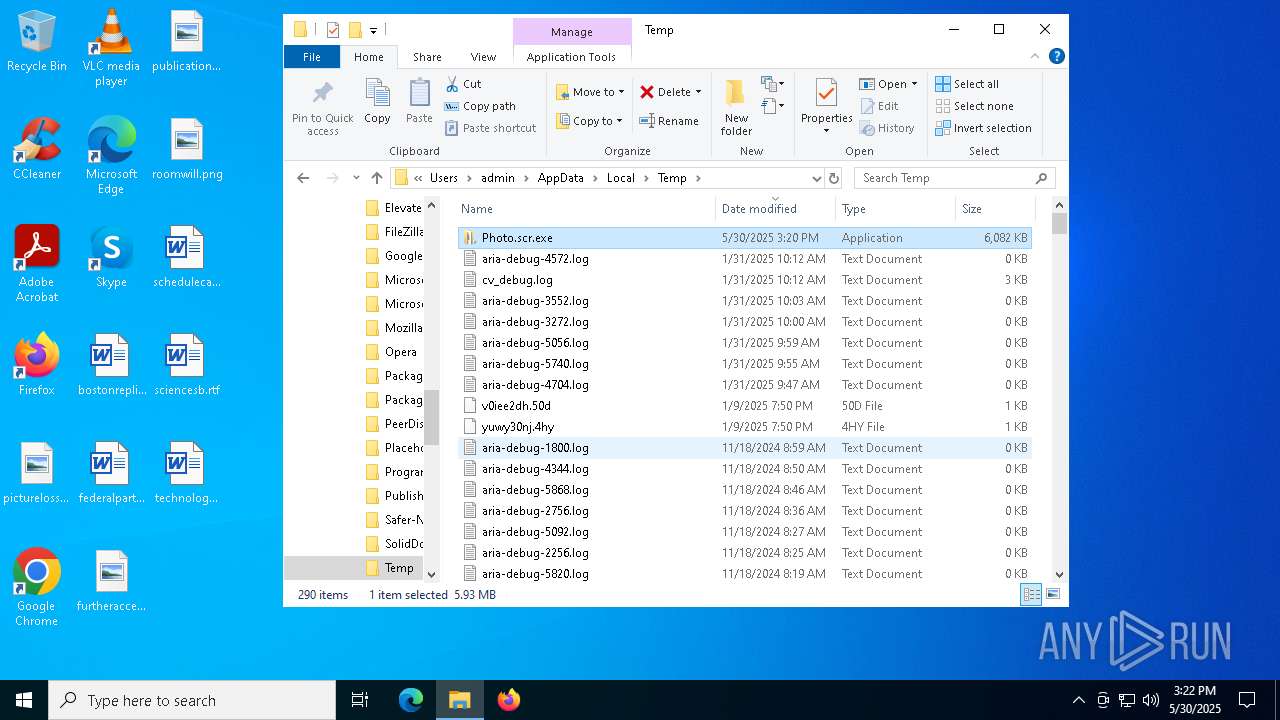
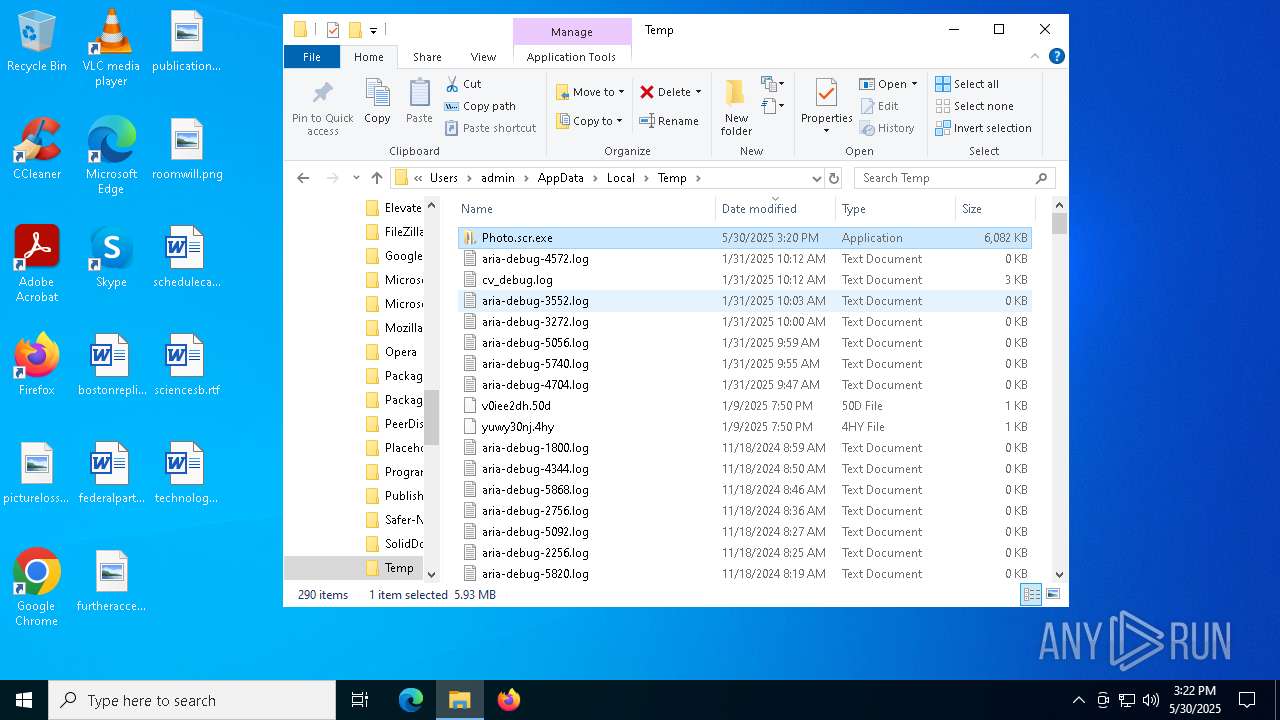
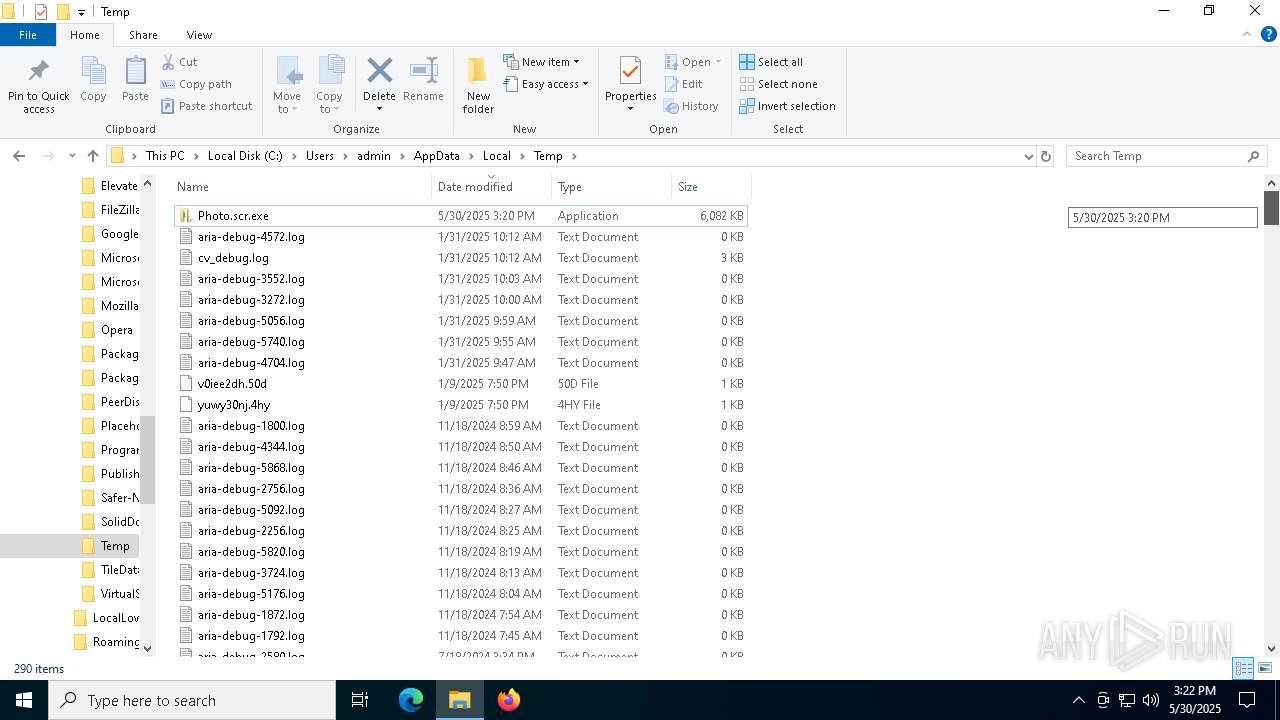
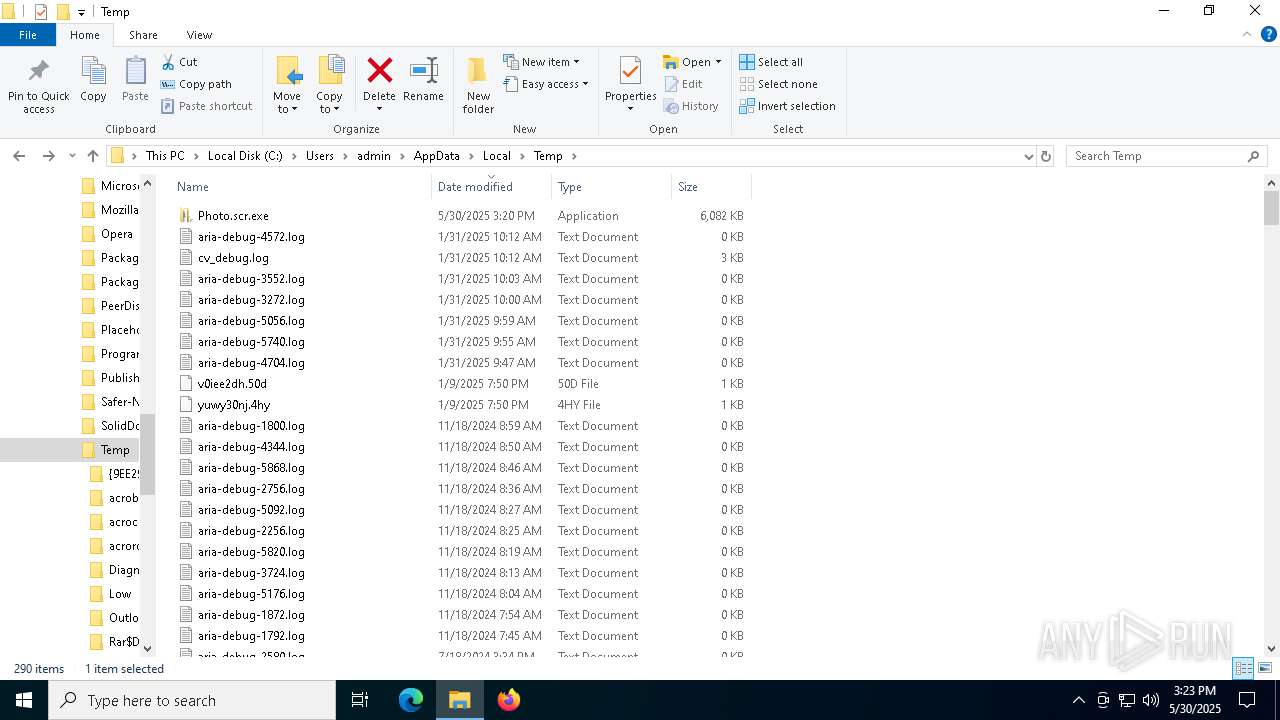
| File name: | Photo.scr |
| Full analysis: | https://app.any.run/tasks/c95dd6d1-f94a-45be-864b-7713fca4eed8 |
| Verdict: | Malicious activity |
| Analysis date: | May 30, 2025, 15:20:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 5616A3471565D34D779B5B3D0520BB70 |
| SHA1: | 42DF726156BEE4A54EA328BD72A659602AB7D03E |
| SHA256: | 9194B57673209C8534888F61B0CDEFA34F463AE50CD78F72AB2B3348220BAAF9 |
| SSDEEP: | 98304:dqMq5w41tP2IHHAHuw4lUSlulY+fWEoOB/xsmCDGID95NM+x48rzPH9ATnVlYLYv:heuGME+pGoSYe4k |
MALICIOUS
BITTORRENT has been detected (SURICATA)
- HelpPane.exe (PID: 1472)
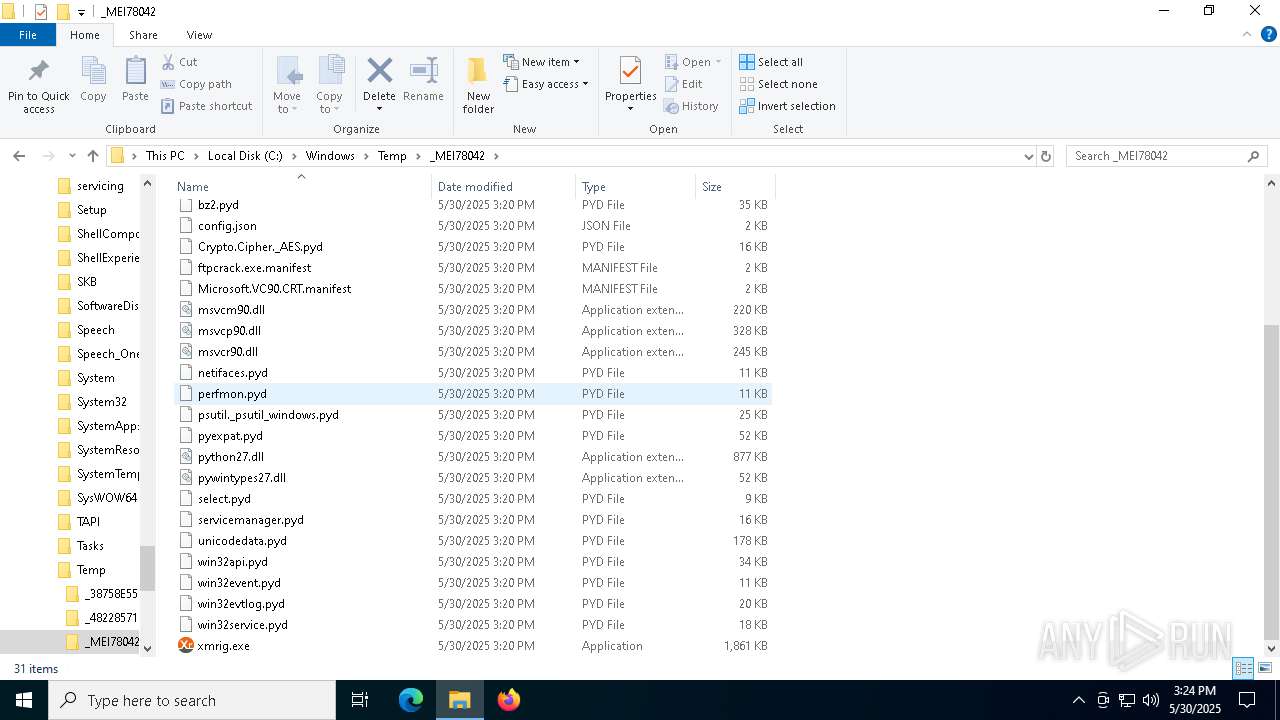
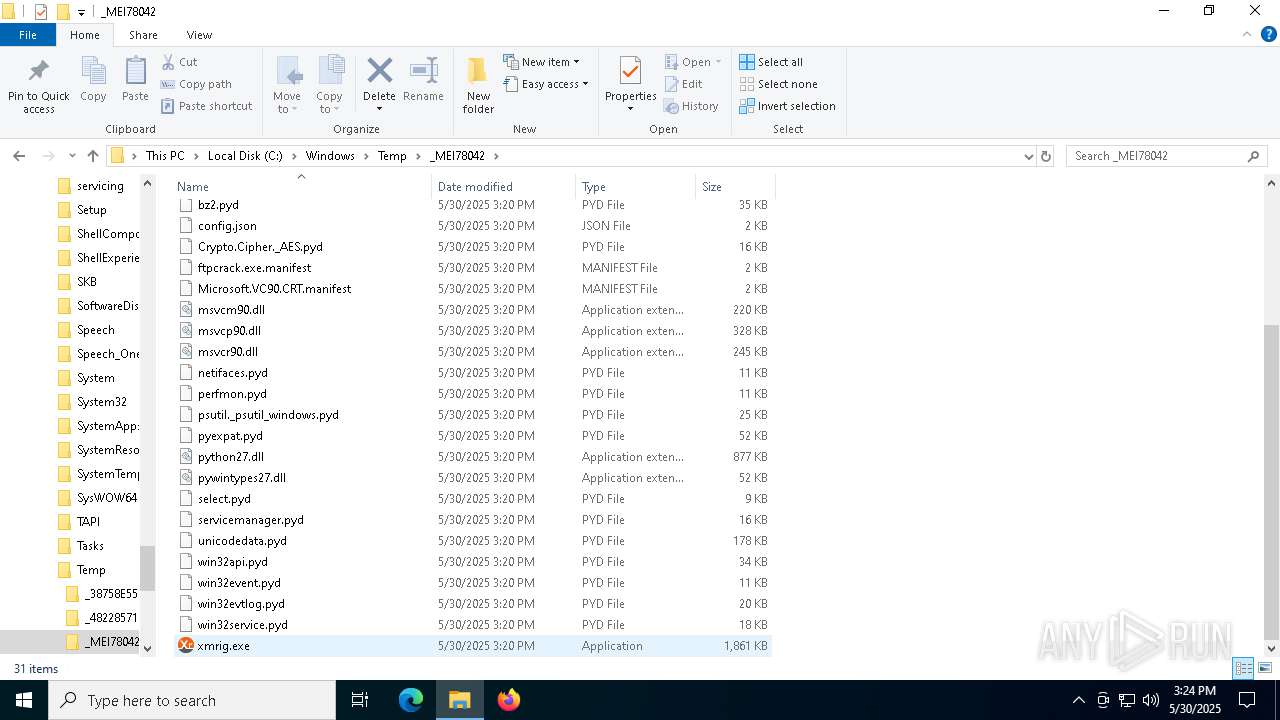
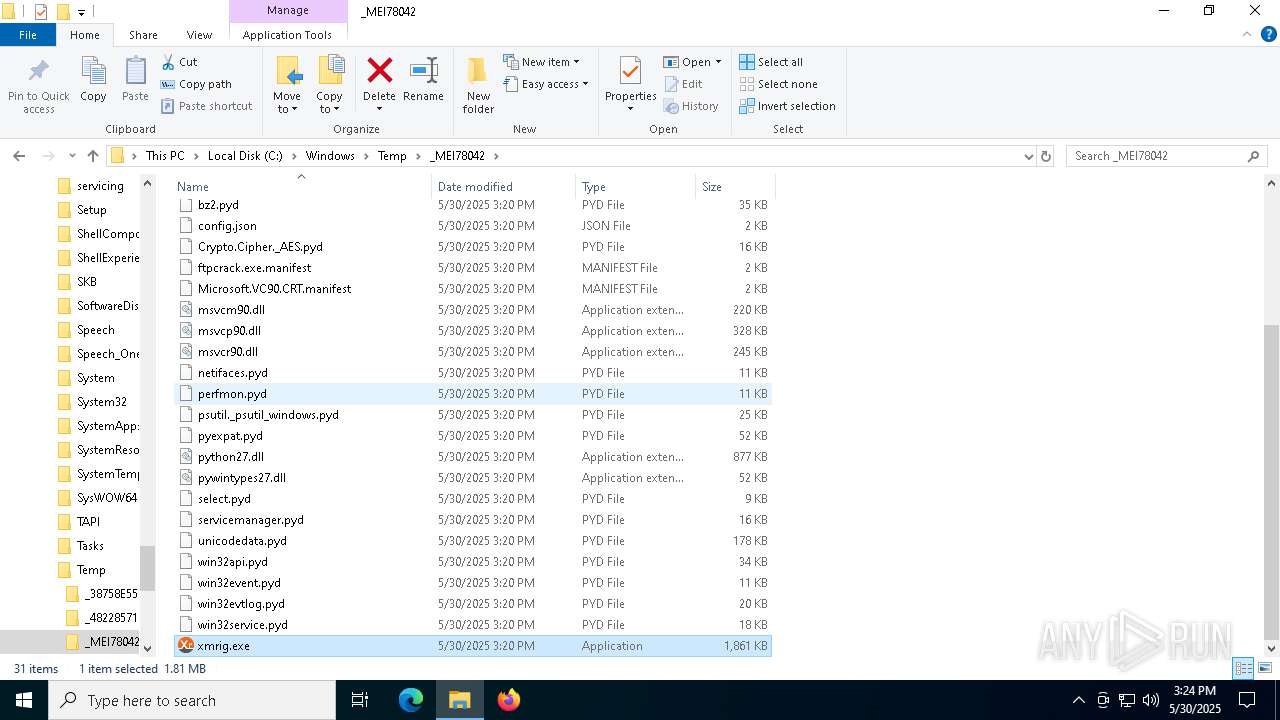
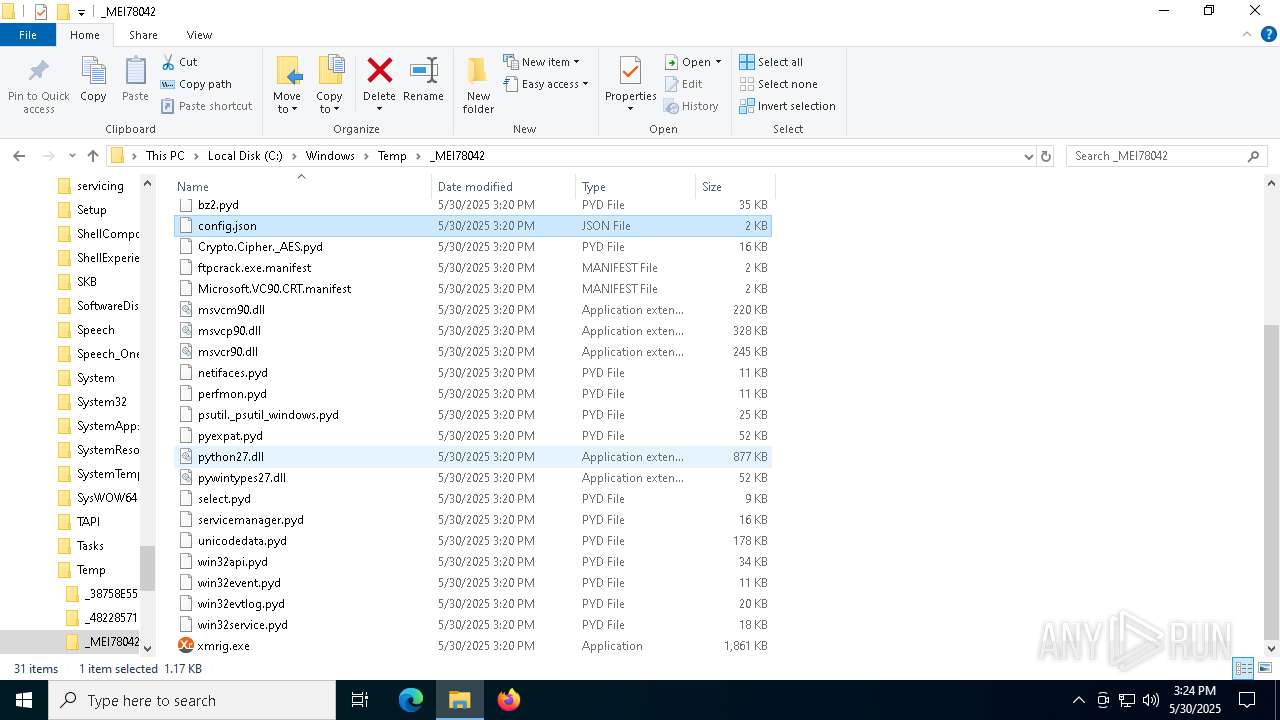
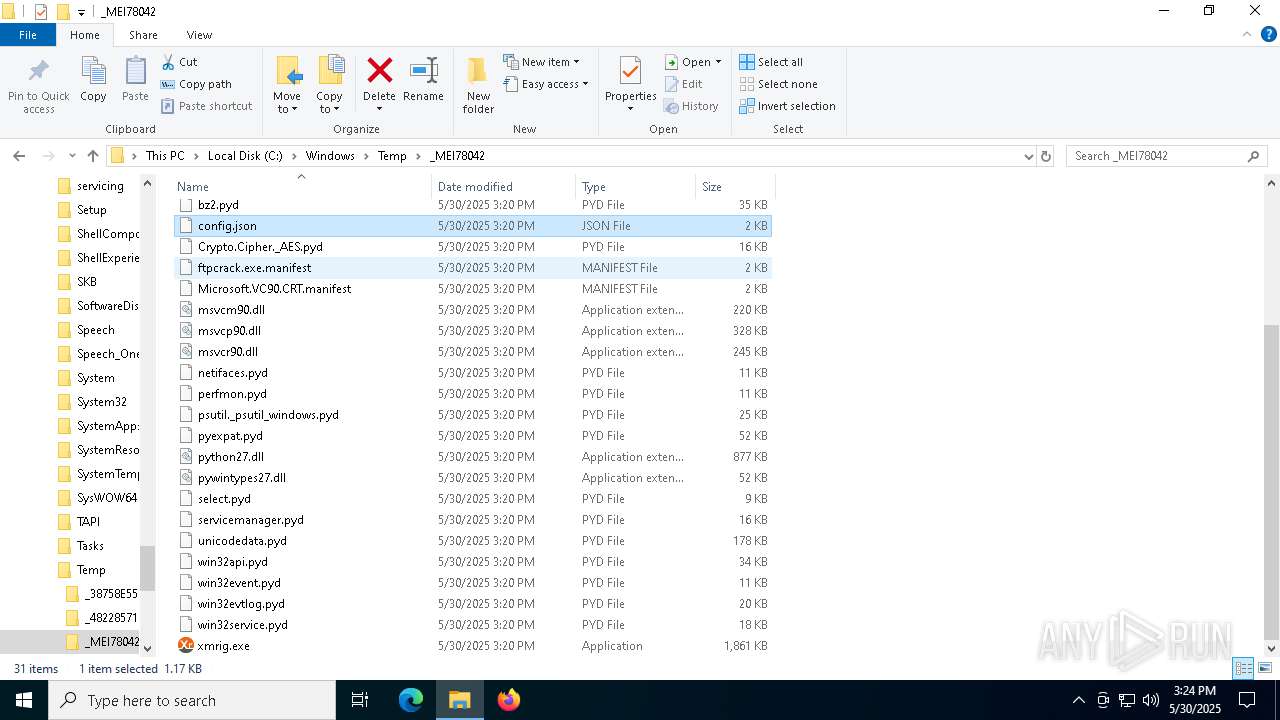
XMRIG has been detected (YARA)
- xmrig.exe (PID: 5864)
SUSPICIOUS
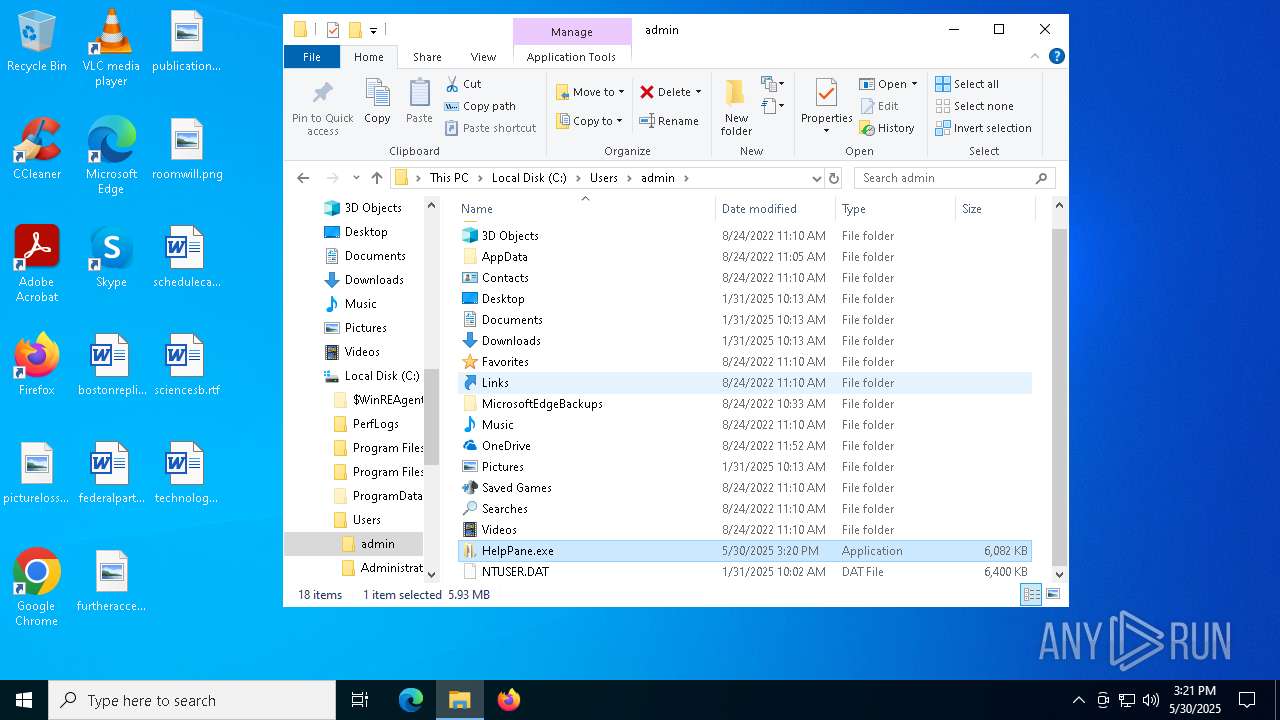
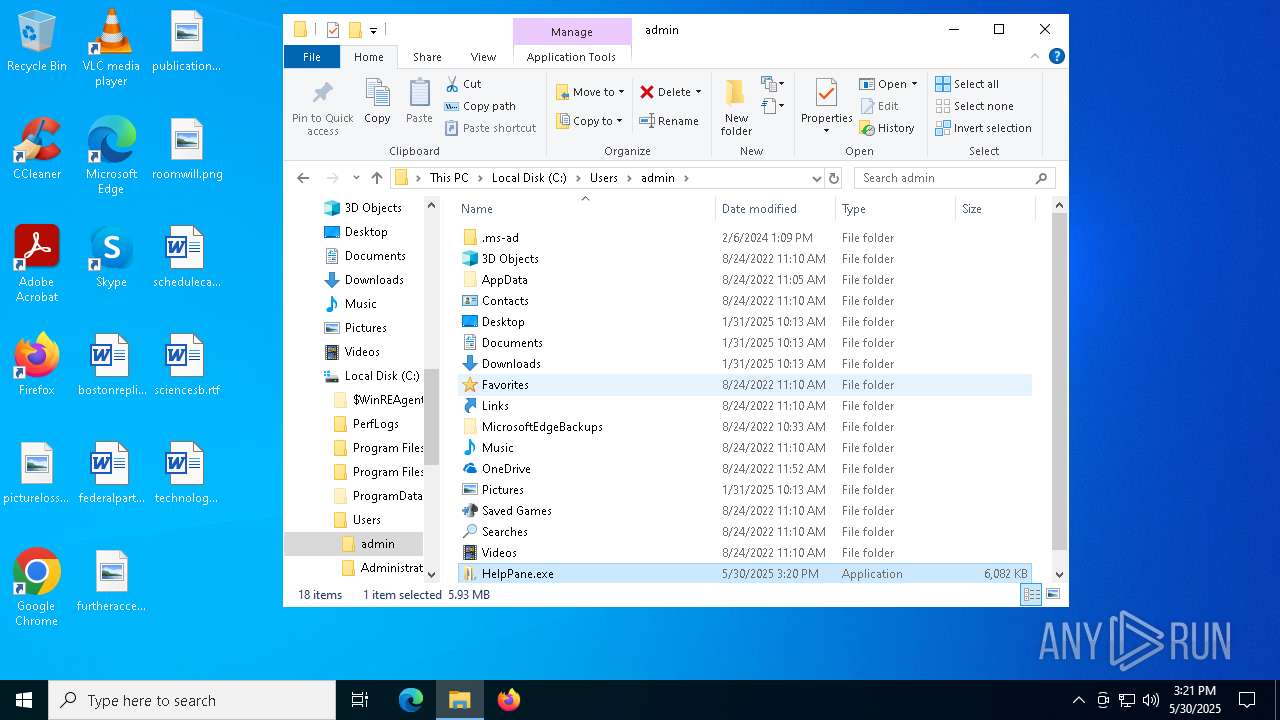
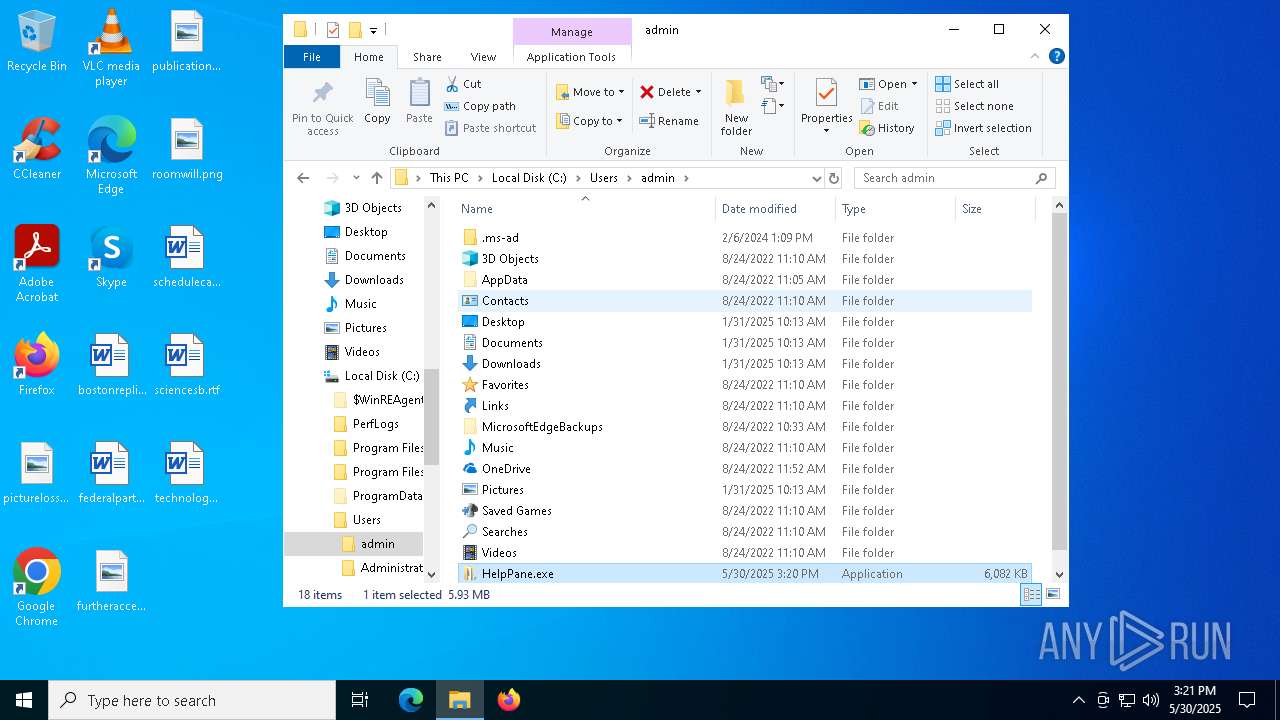
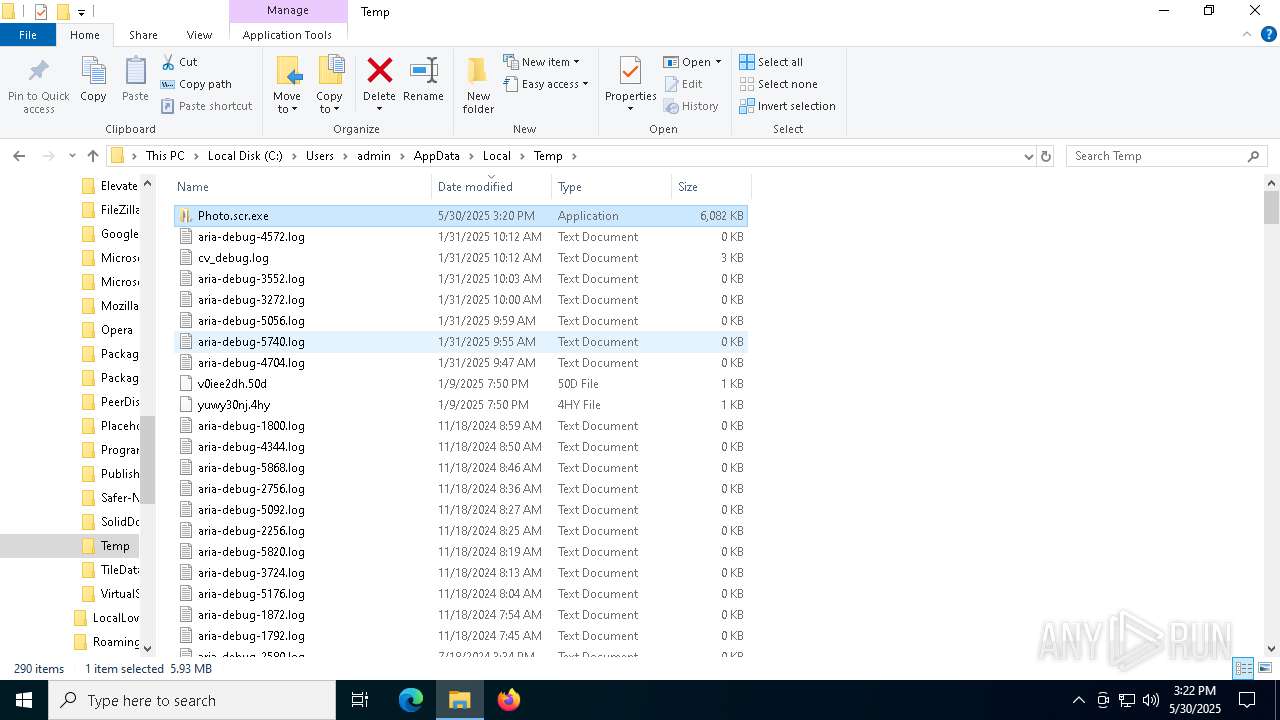
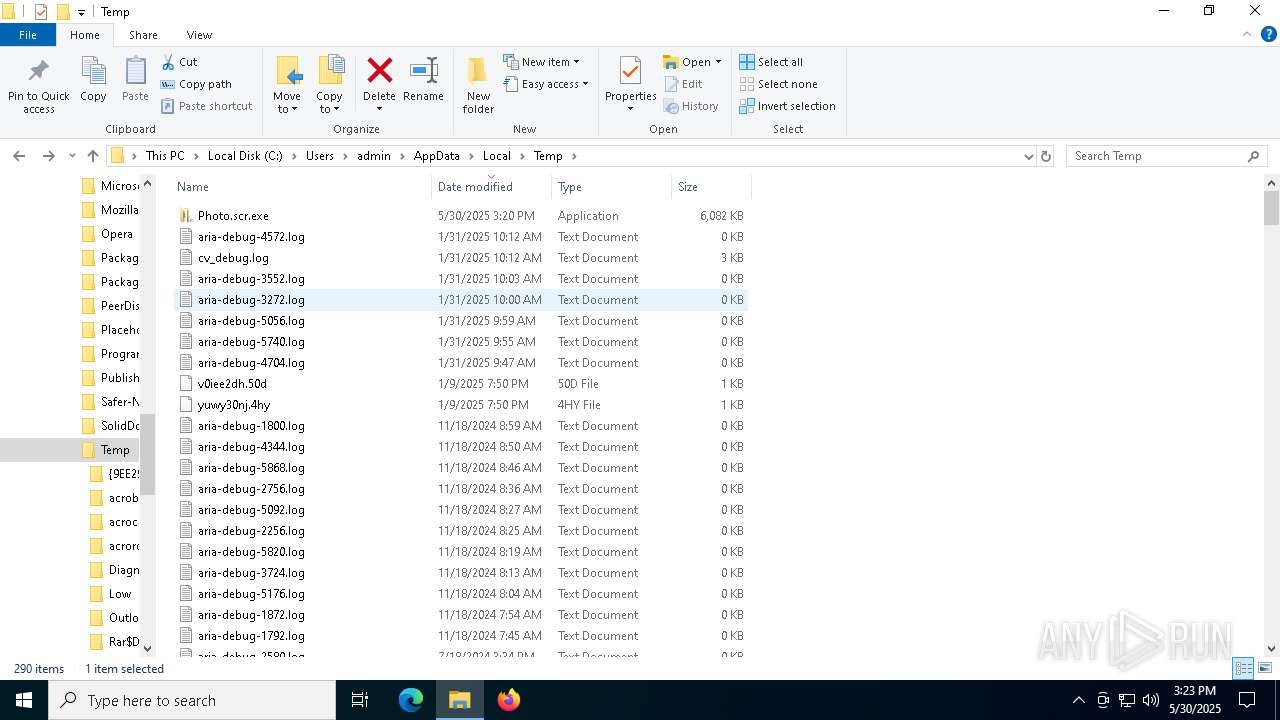
Executable content was dropped or overwritten
- Photo.scr.exe (PID: 7876)
- HelpPane.exe (PID: 7496)
- cmd.exe (PID: 7588)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7804)
- cmd.exe (PID: 2800)
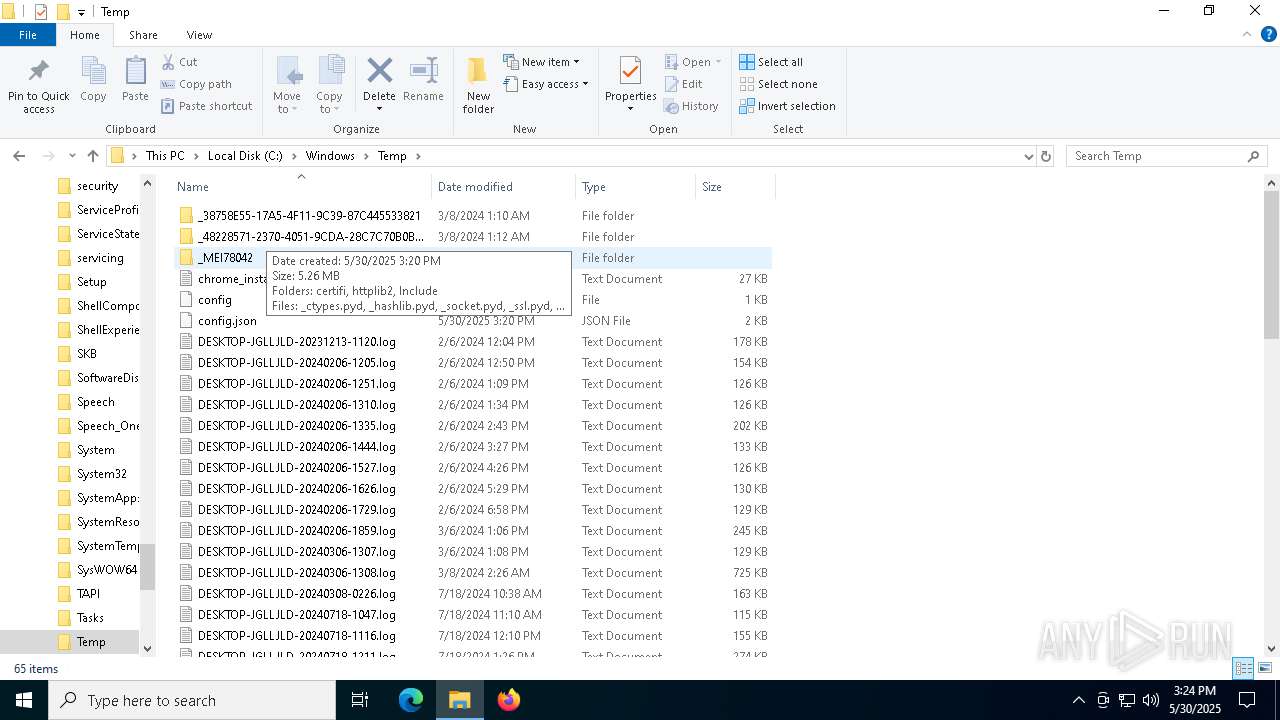
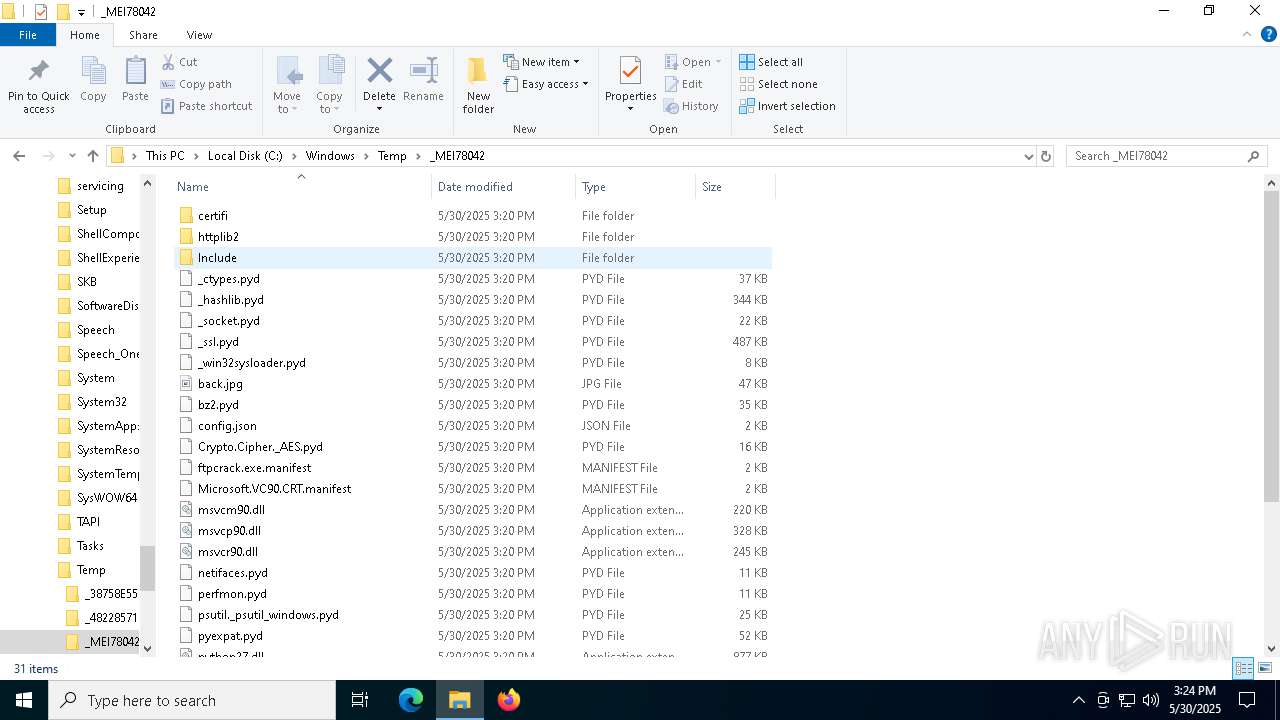
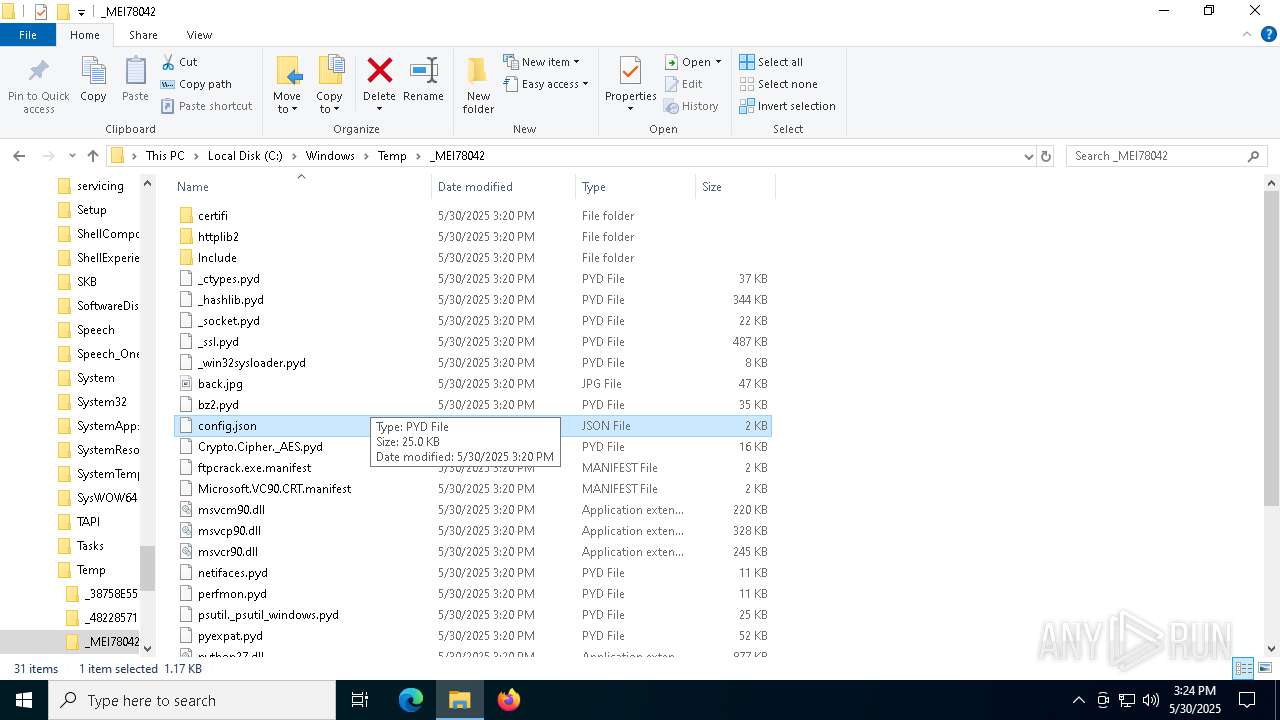
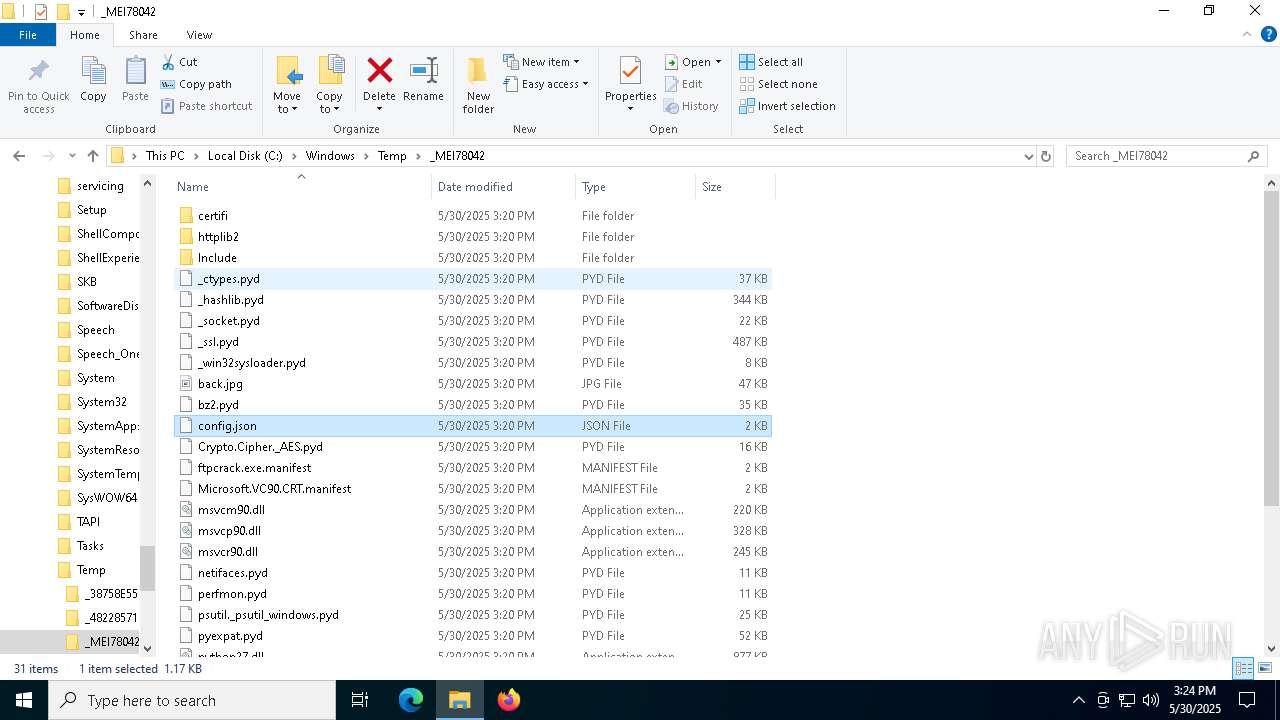
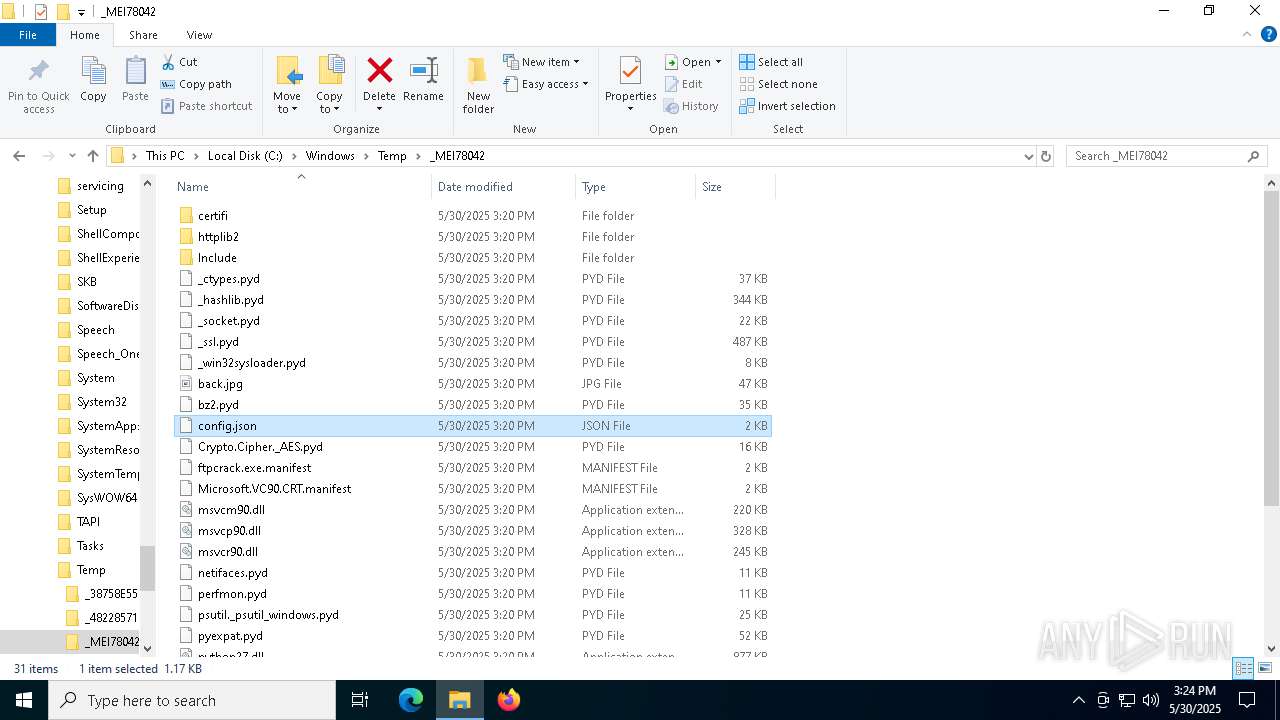
Process drops python dynamic module
- Photo.scr.exe (PID: 7876)
- HelpPane.exe (PID: 7496)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7804)
Application launched itself
- Photo.scr.exe (PID: 7876)
- Photo.scr.exe (PID: 7820)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7804)
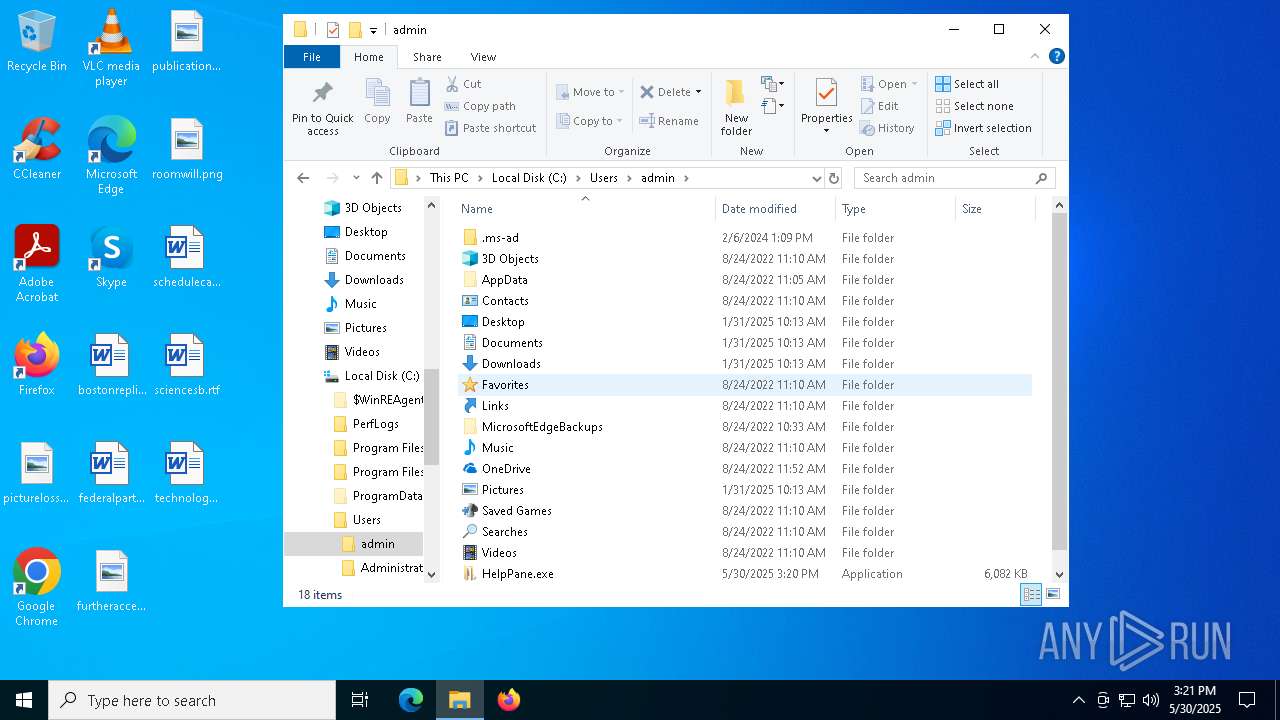
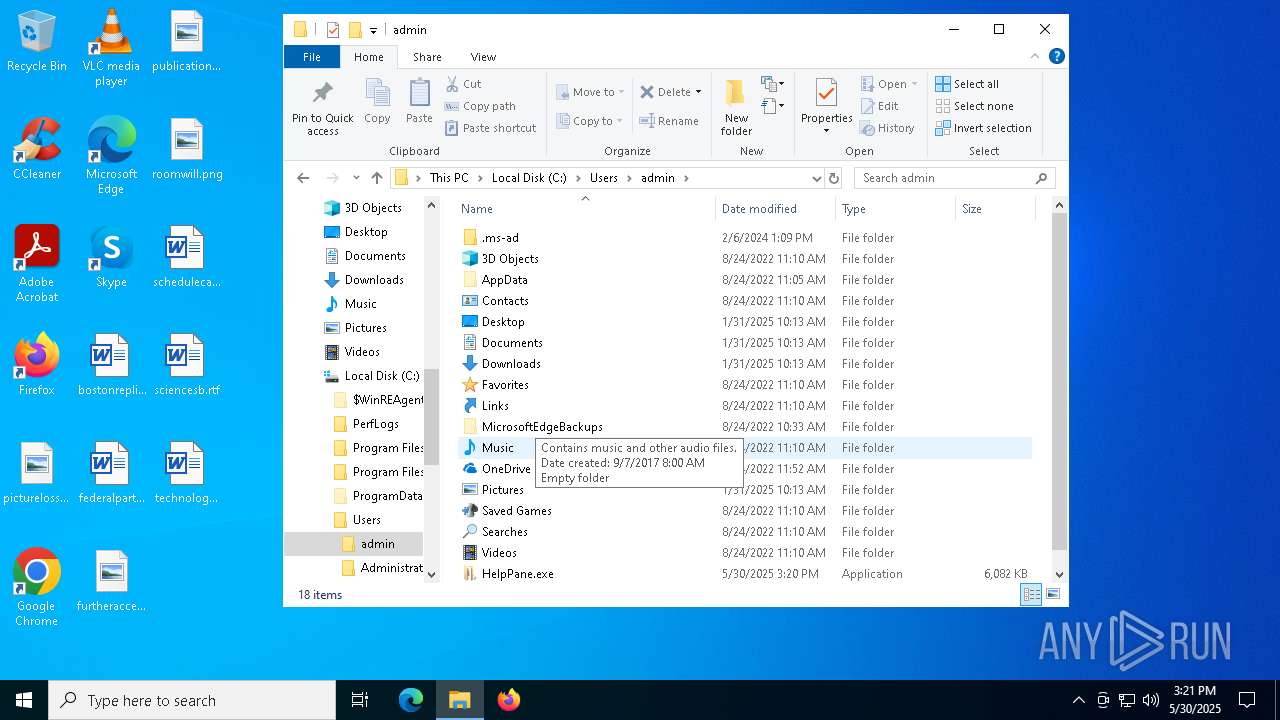
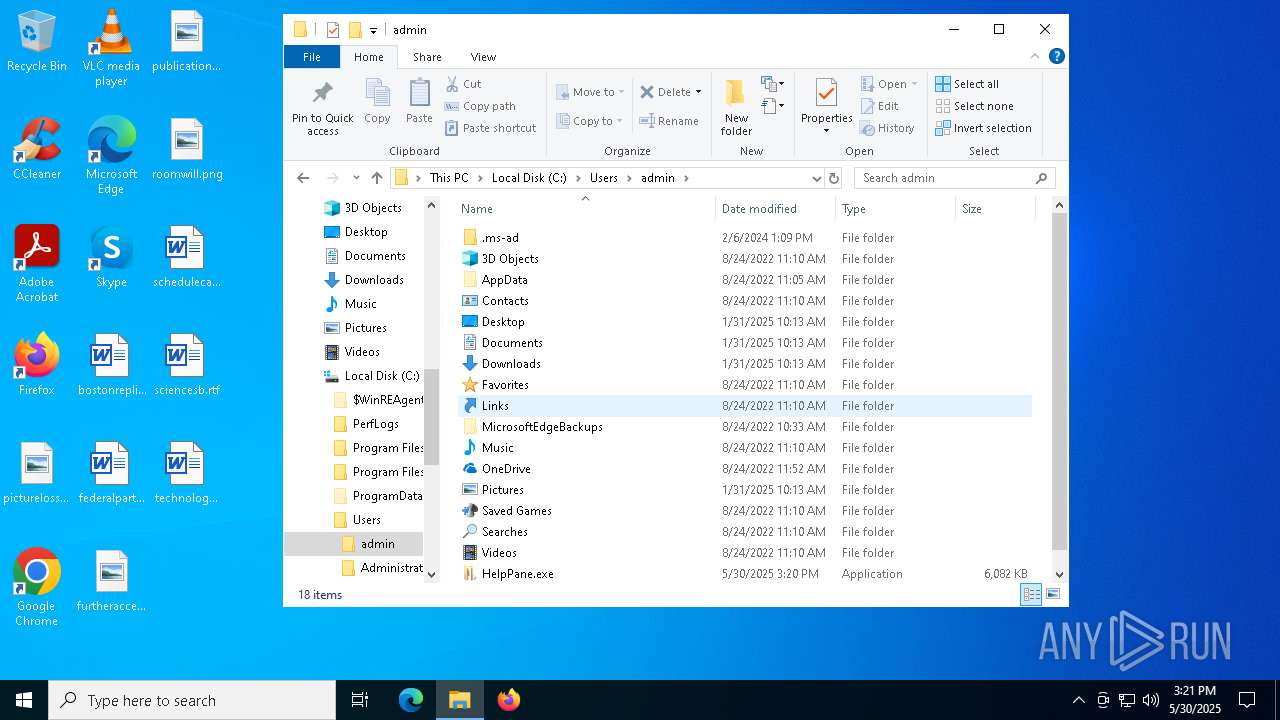
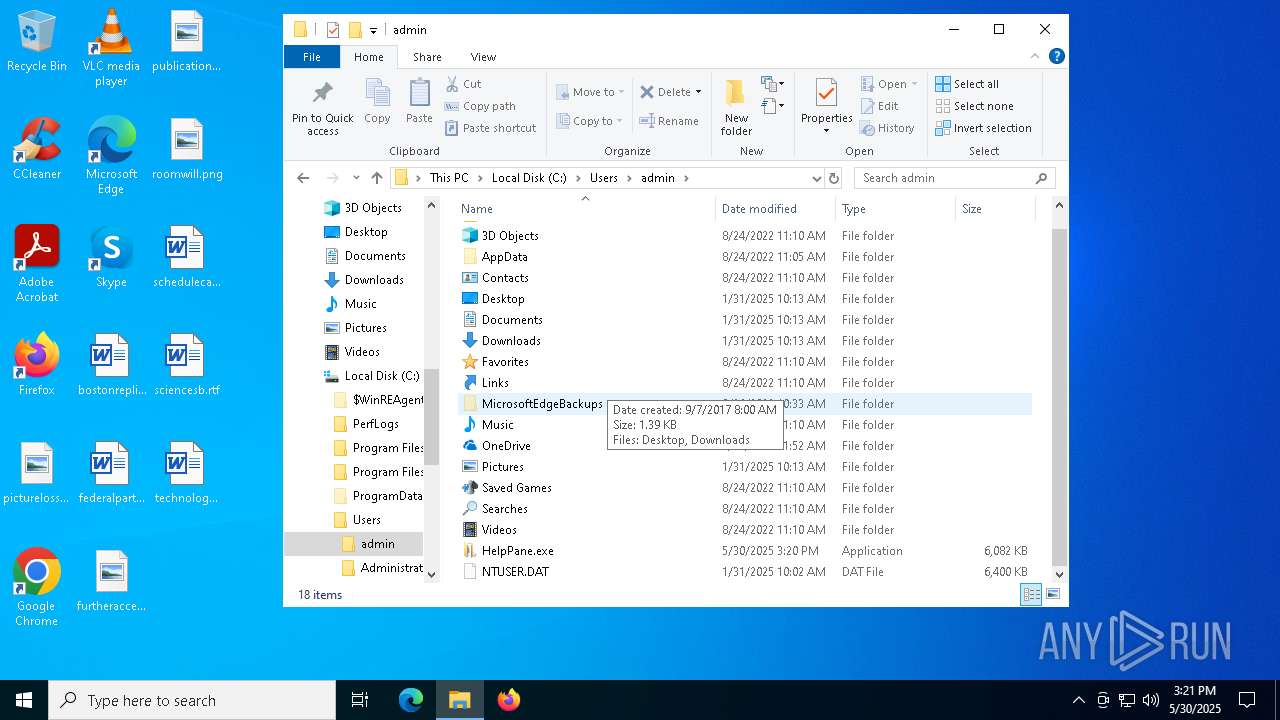
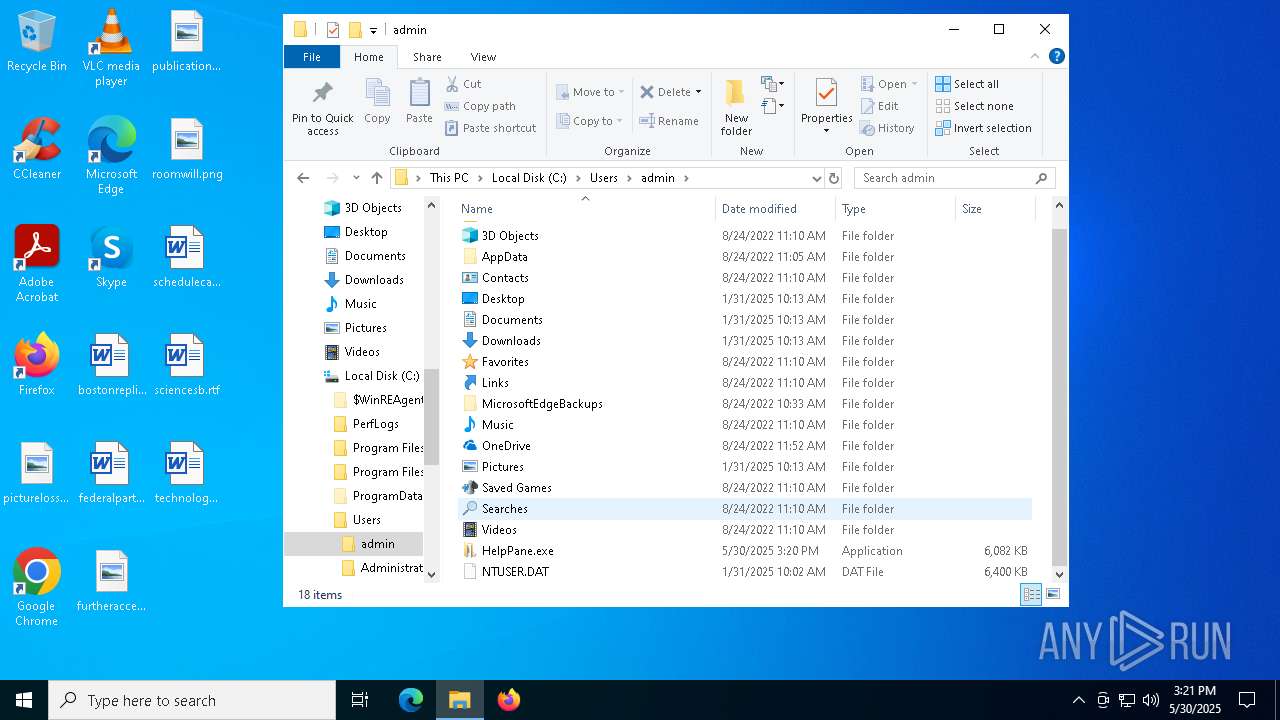
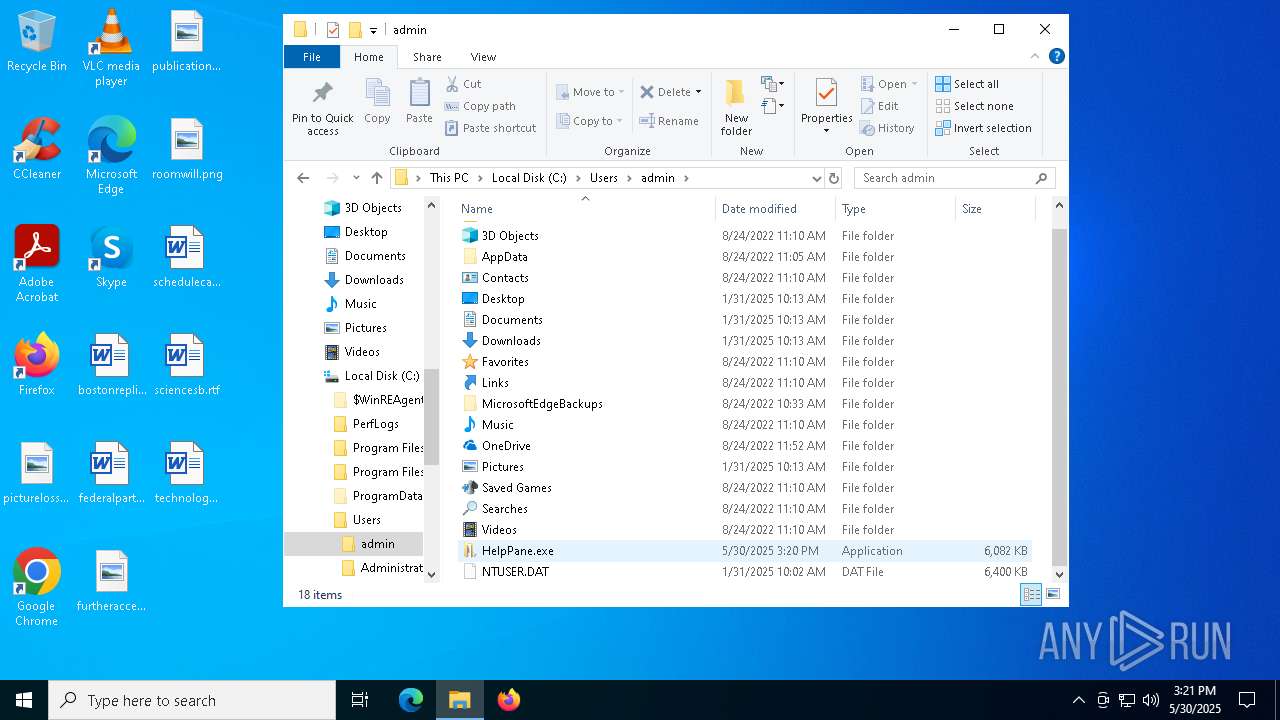
Process drops legitimate windows executable
- Photo.scr.exe (PID: 7876)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7804)
The process drops C-runtime libraries
- Photo.scr.exe (PID: 7876)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7804)
Loads Python modules
- Photo.scr.exe (PID: 7820)
- Photo.scr.exe (PID: 7376)
- HelpPane.exe (PID: 7404)
- HelpPane.exe (PID: 7888)
- HelpPane.exe (PID: 1472)
Reads security settings of Internet Explorer
- Photo.scr.exe (PID: 7820)
Starts CMD.EXE for commands execution
- Photo.scr.exe (PID: 7376)
- HelpPane.exe (PID: 1472)
The executable file from the user directory is run by the CMD process
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
Executes as Windows Service
- HelpPane.exe (PID: 7804)
- spoolsv.exe (PID: 4336)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 644)
Uses NETSH.EXE to add a firewall rule or allowed programs
- HelpPane.exe (PID: 1472)
There is functionality for taking screenshot (YARA)
- HelpPane.exe (PID: 1472)
Connects to FTP
- HelpPane.exe (PID: 1472)
Connects to unusual port
- HelpPane.exe (PID: 1472)
INFO
Checks supported languages
- Photo.scr.exe (PID: 7876)
- Photo.scr.exe (PID: 7820)
- Photo.scr.exe (PID: 6040)
- Photo.scr.exe (PID: 7376)
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7888)
- HelpPane.exe (PID: 7804)
- HelpPane.exe (PID: 7404)
- HelpPane.exe (PID: 1472)
- xmrig.exe (PID: 5864)
The sample compiled with english language support
- Photo.scr.exe (PID: 7876)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
- HelpPane.exe (PID: 7804)
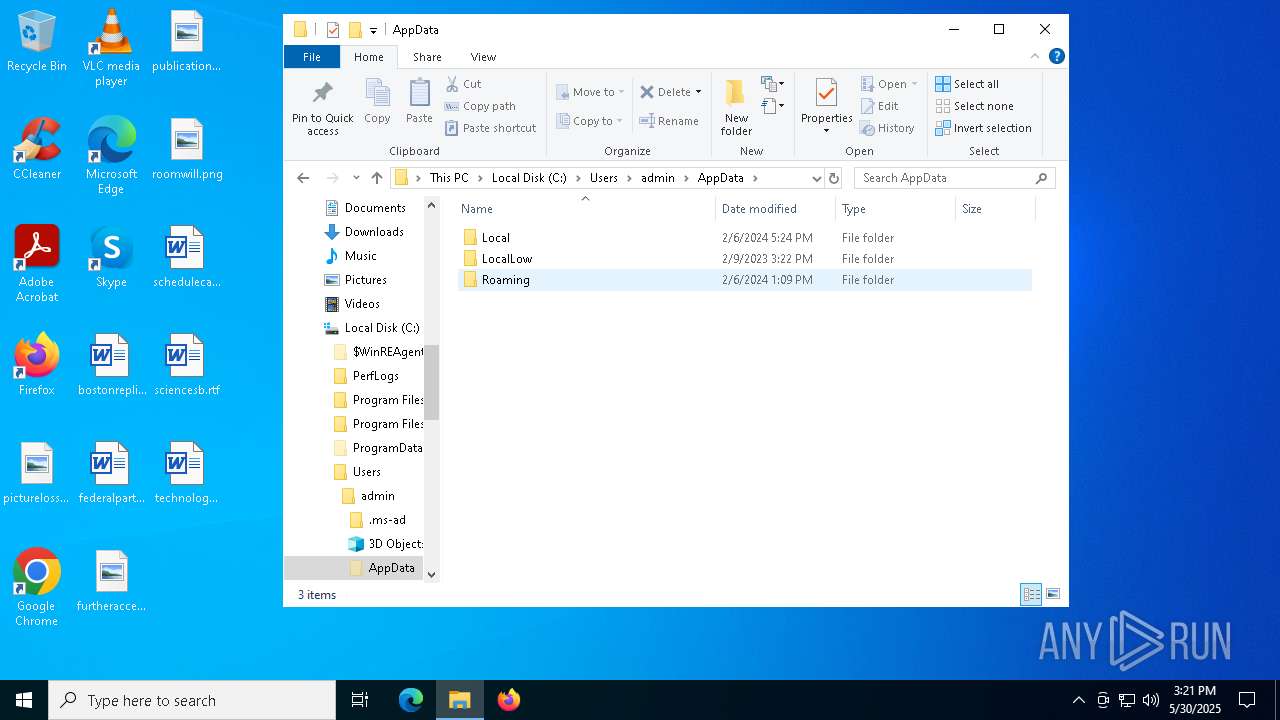
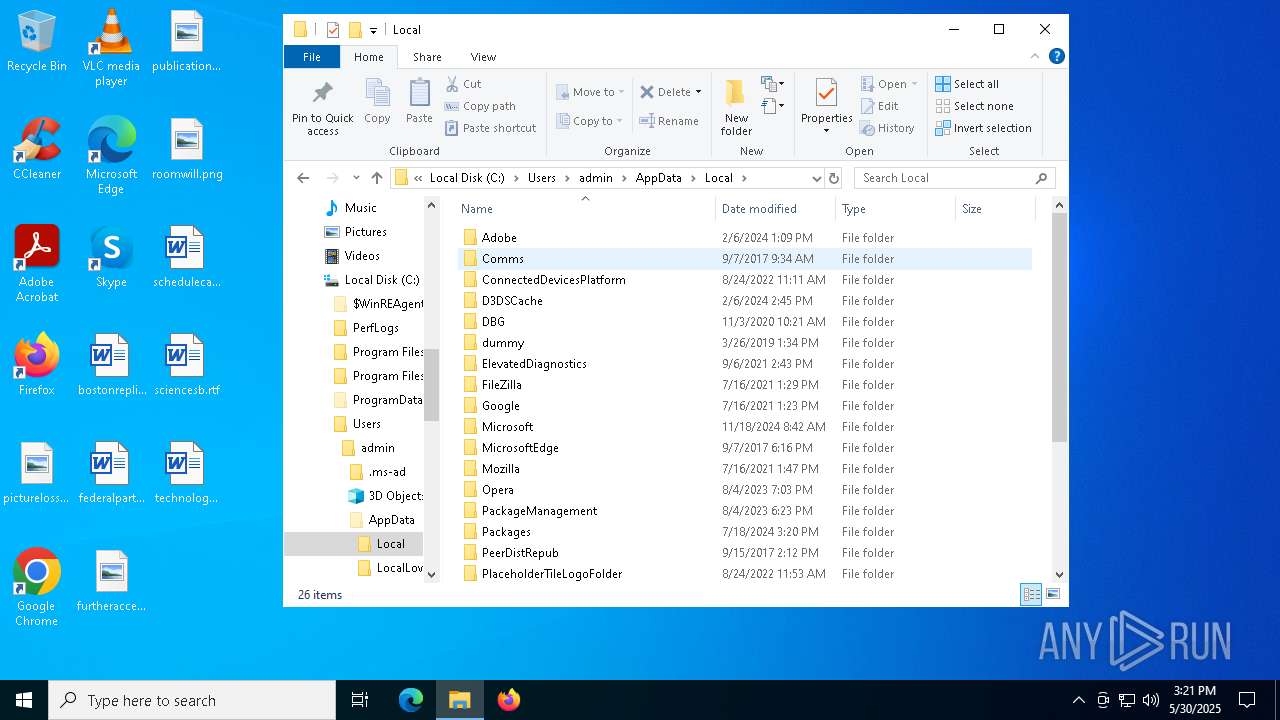
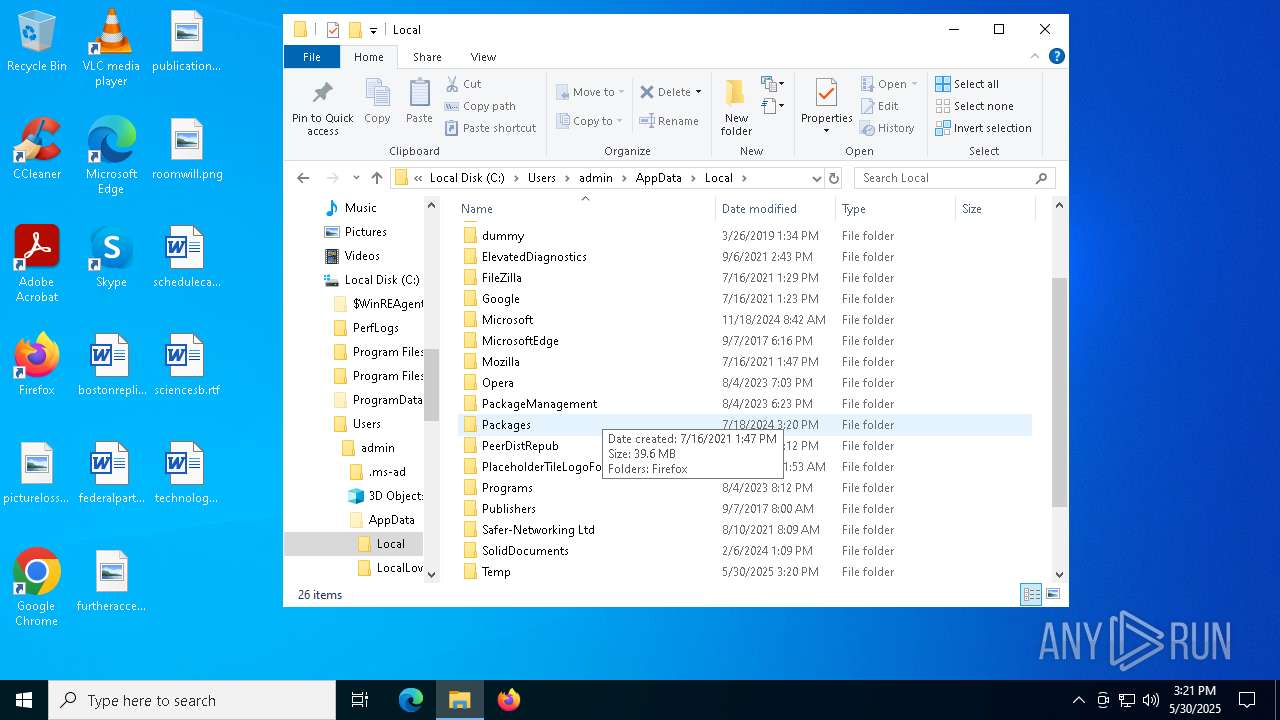
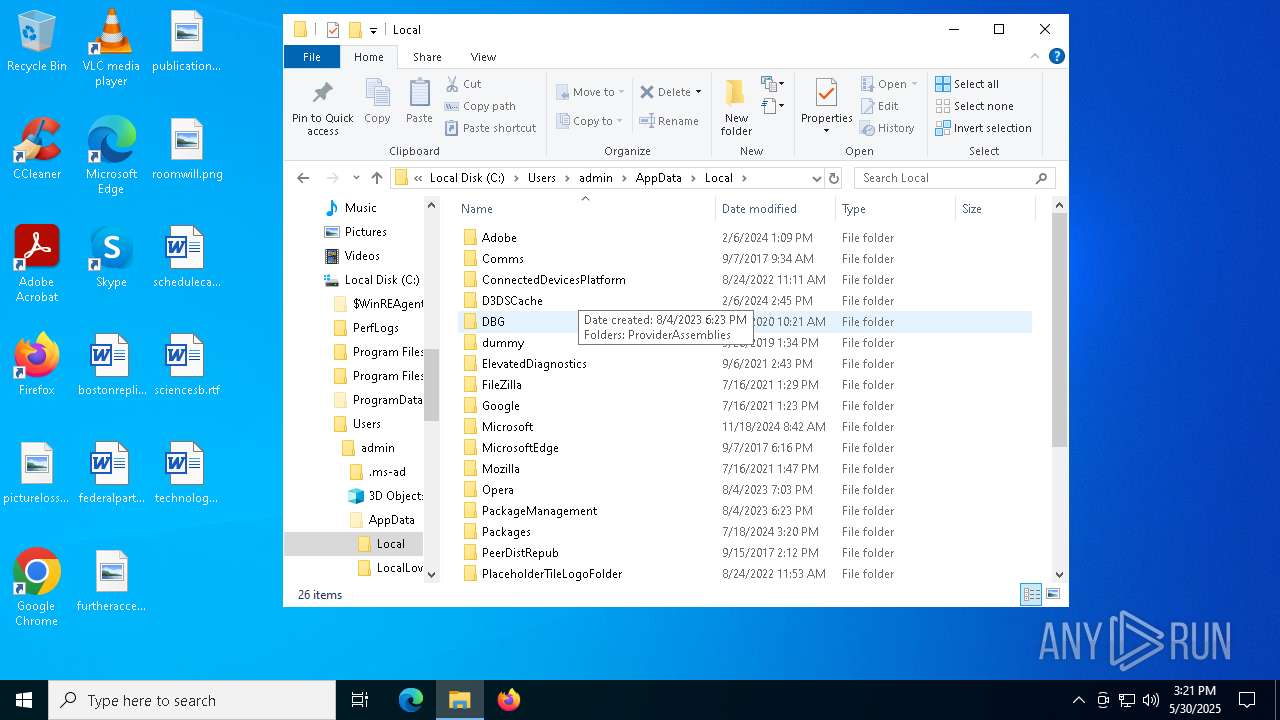
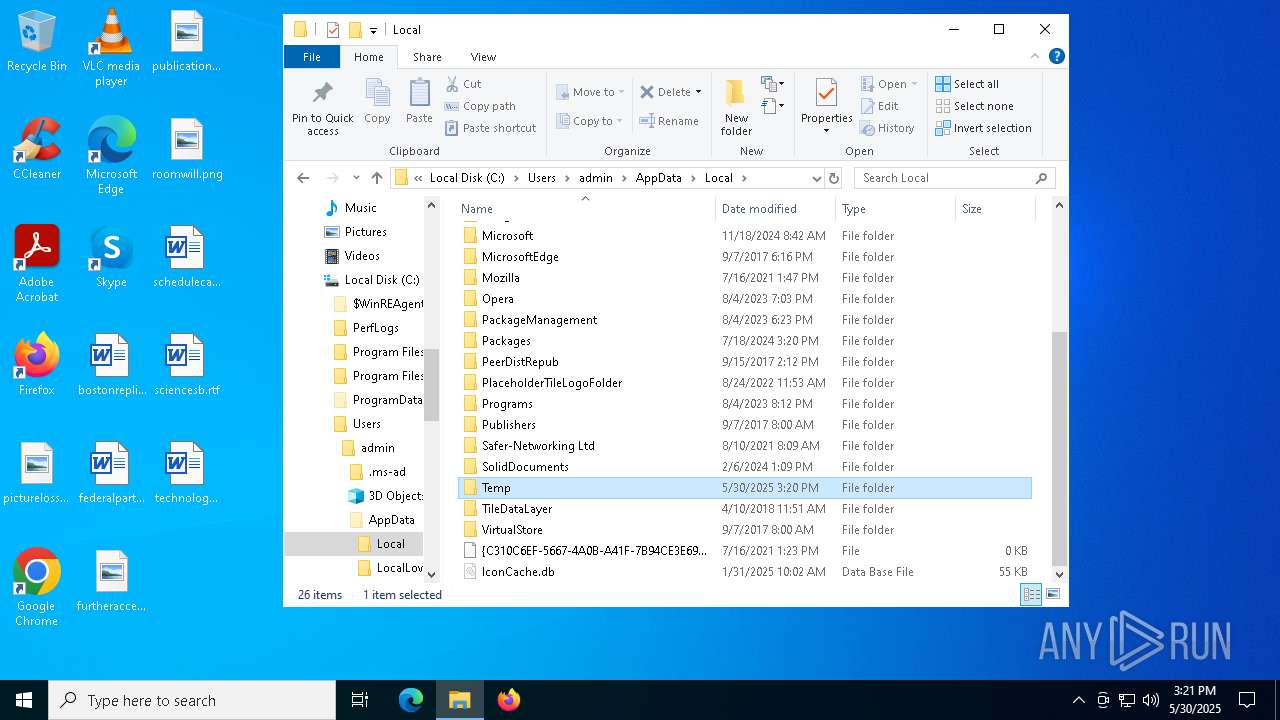
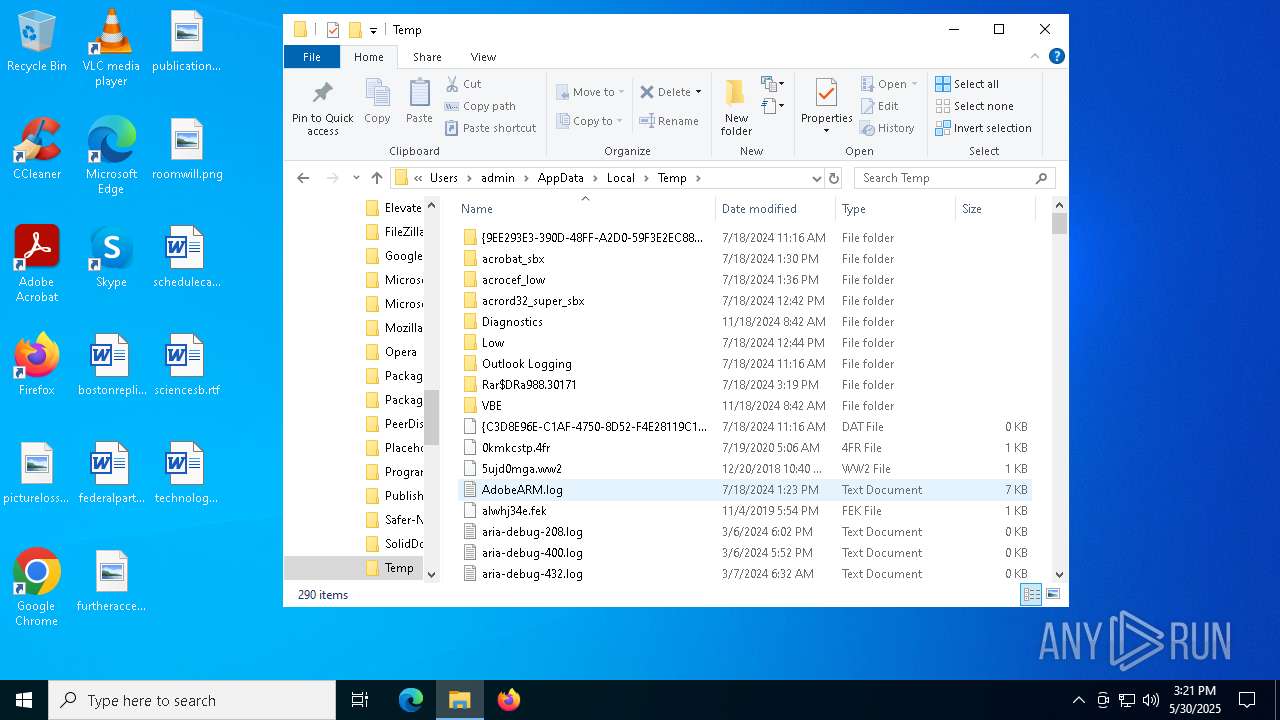
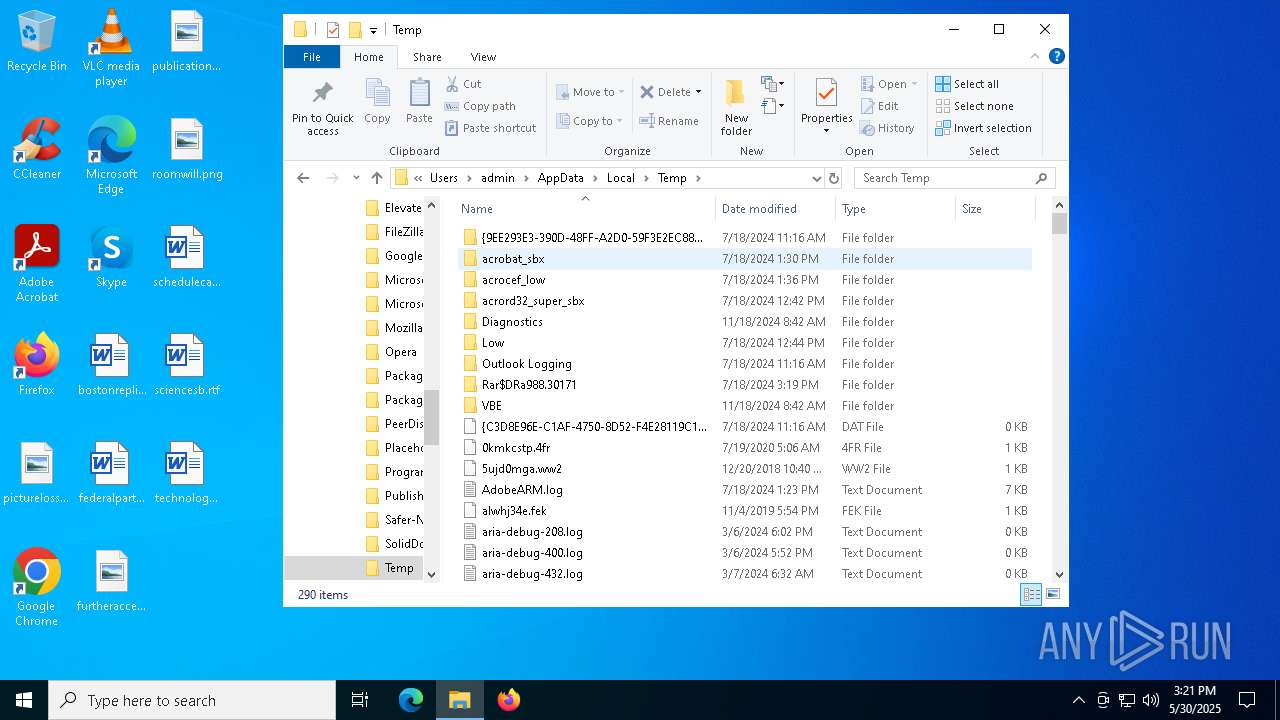
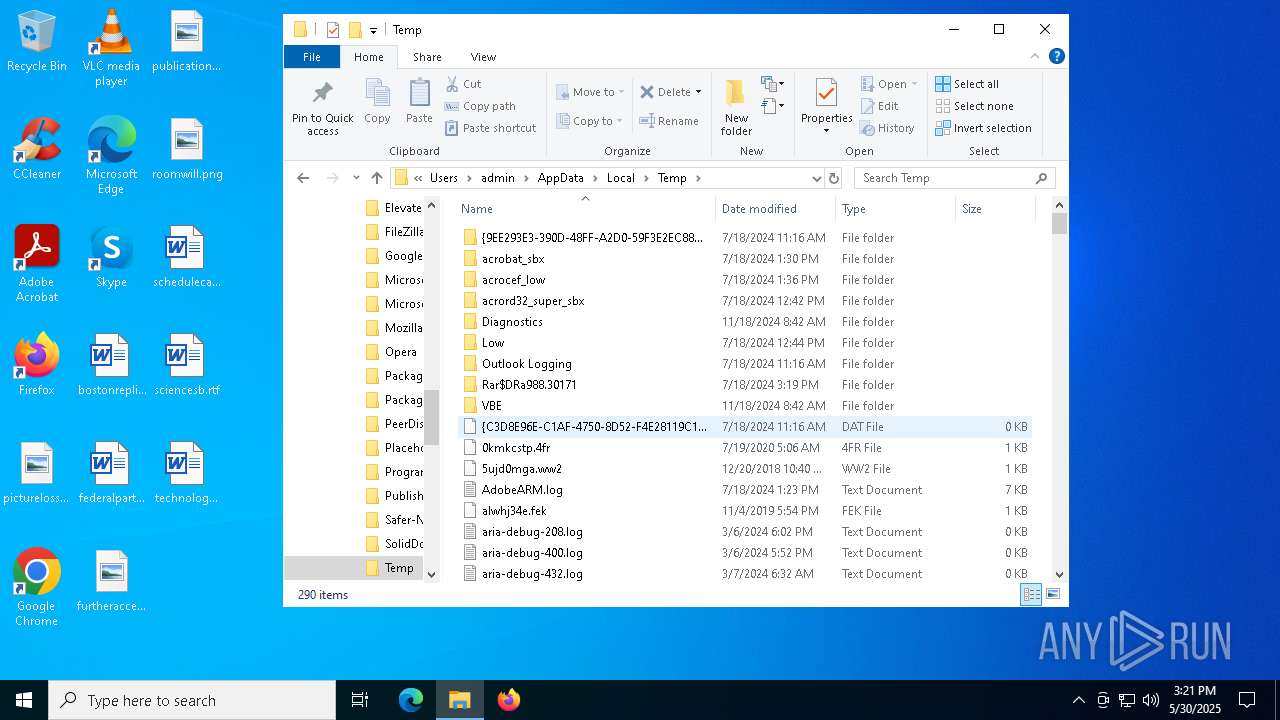
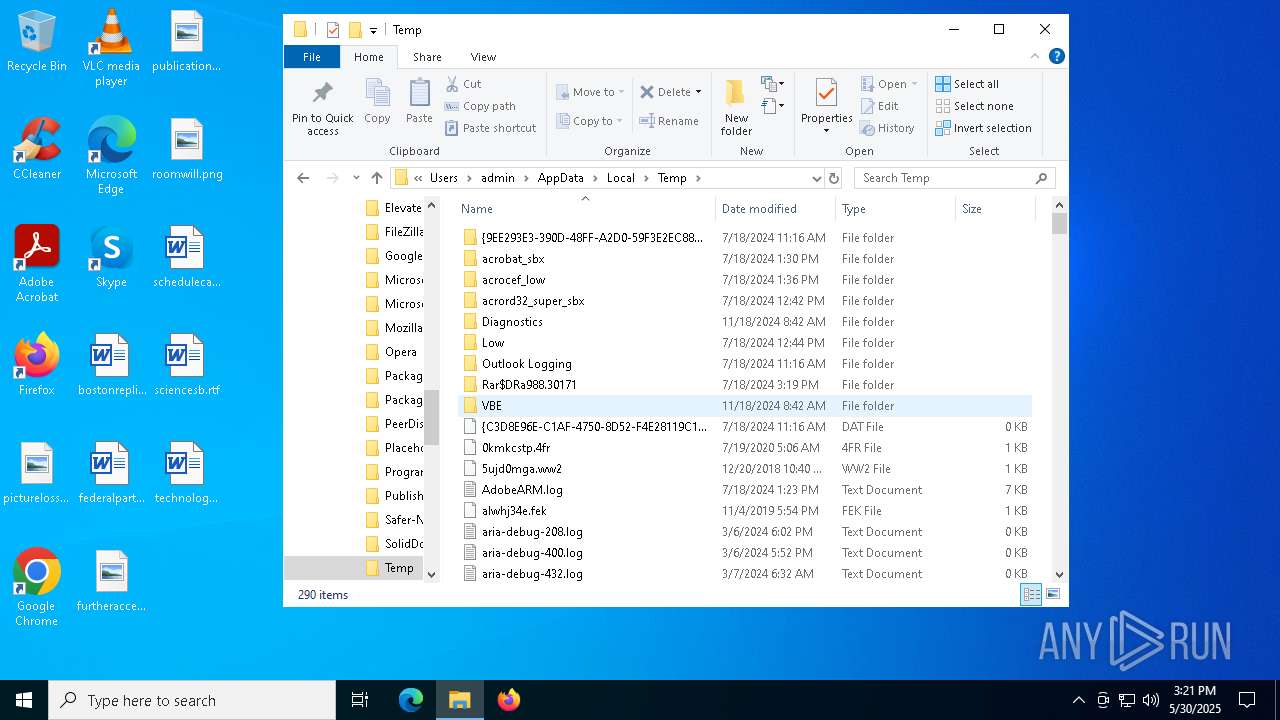
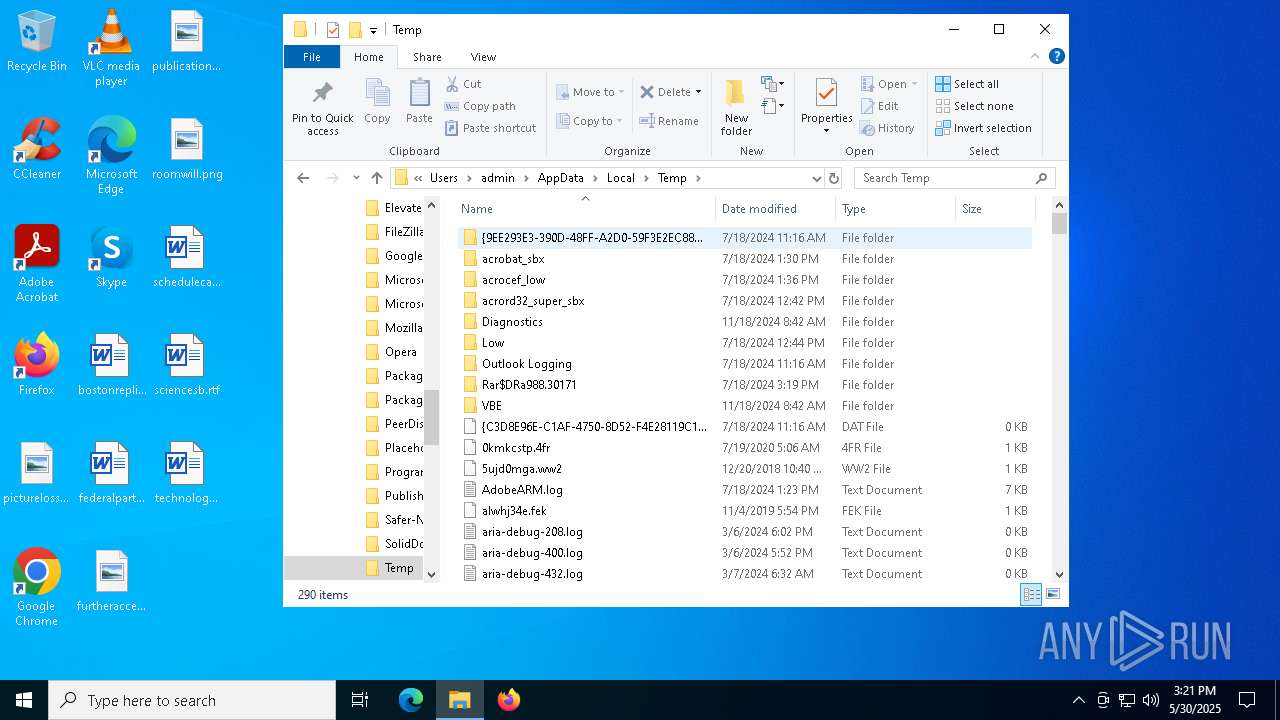
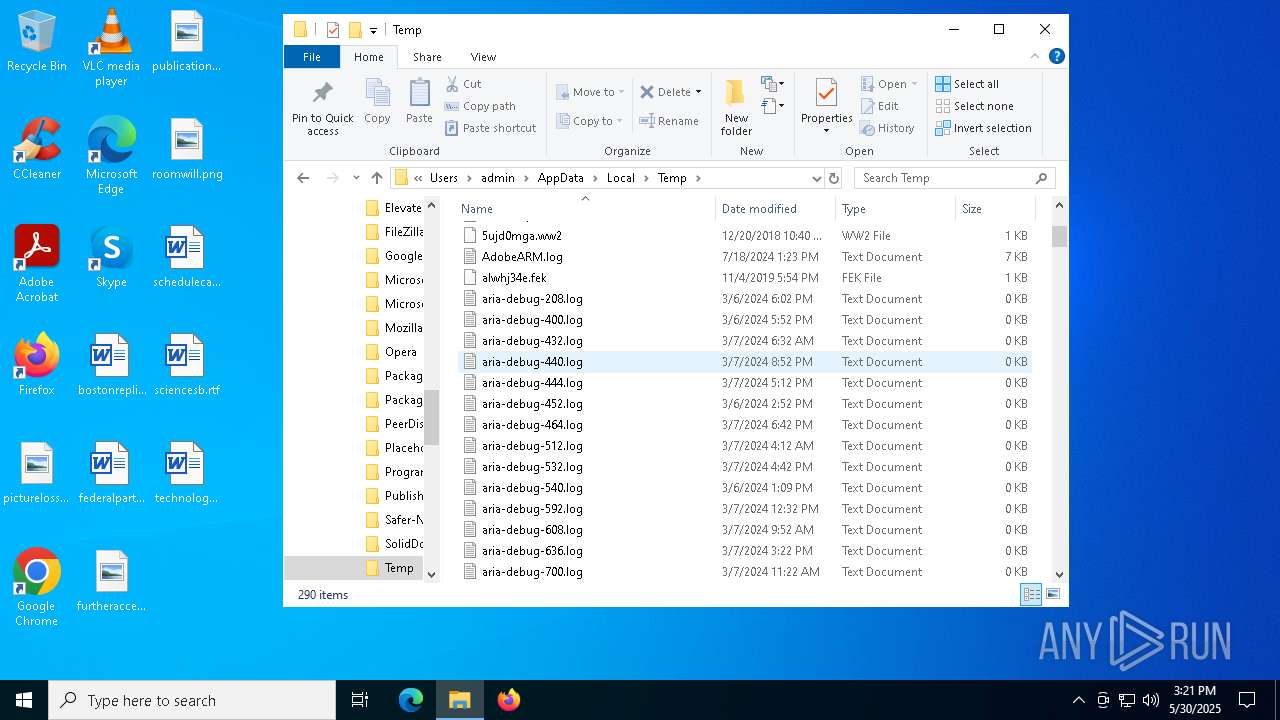
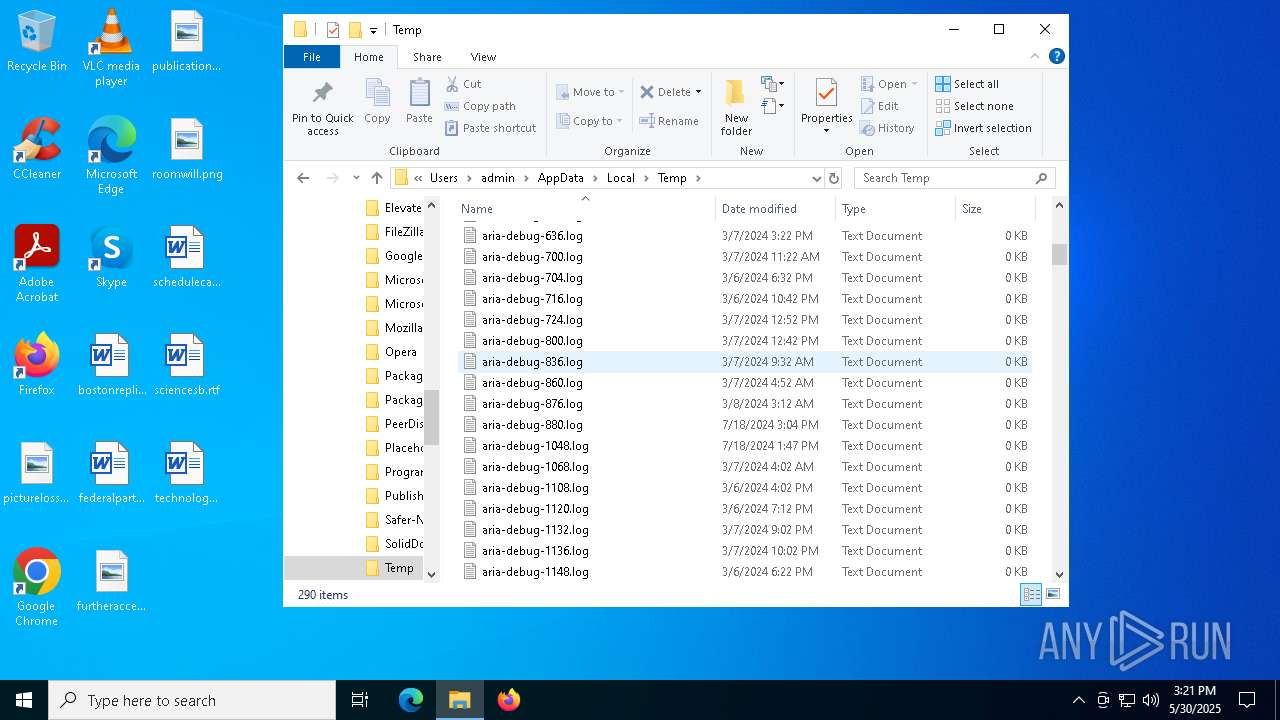
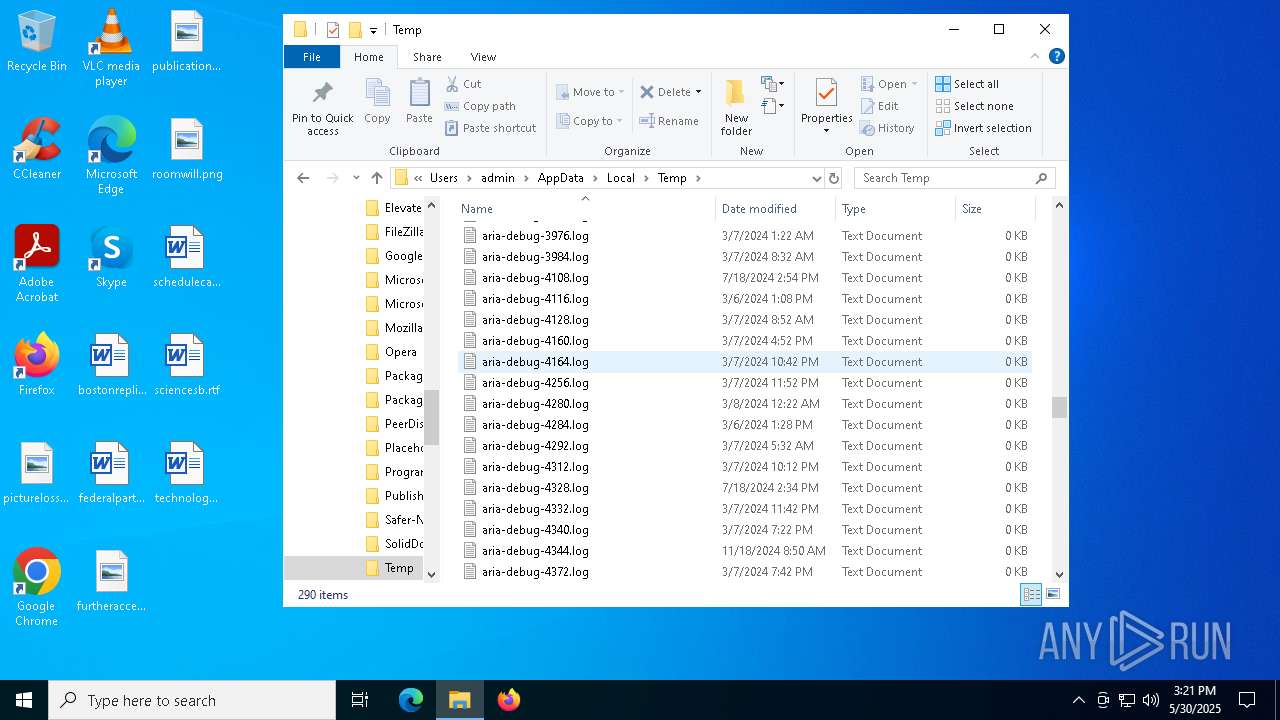
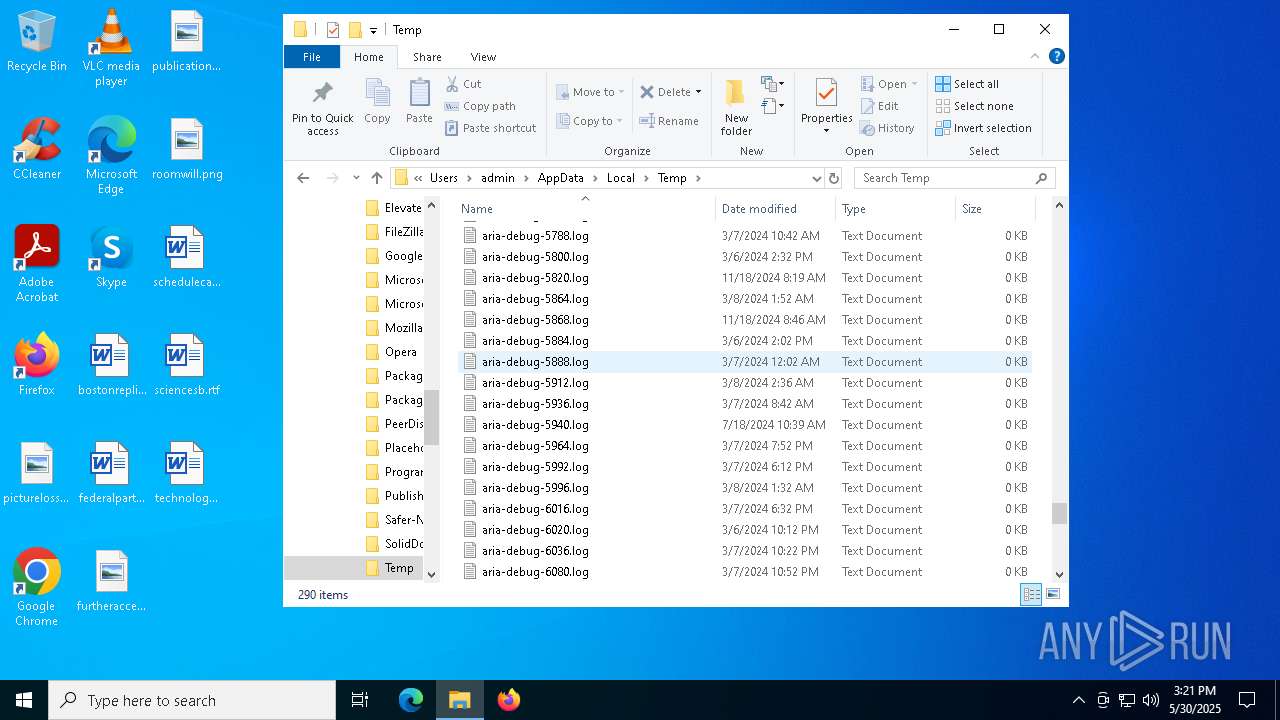
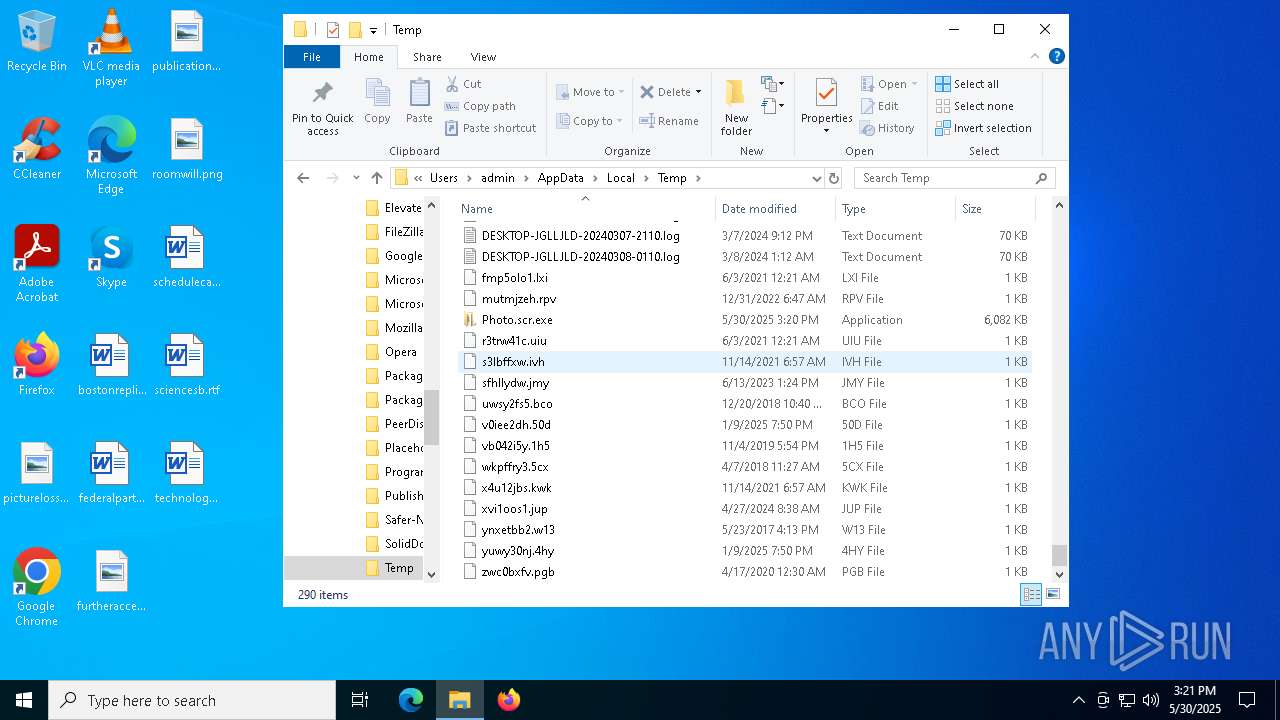
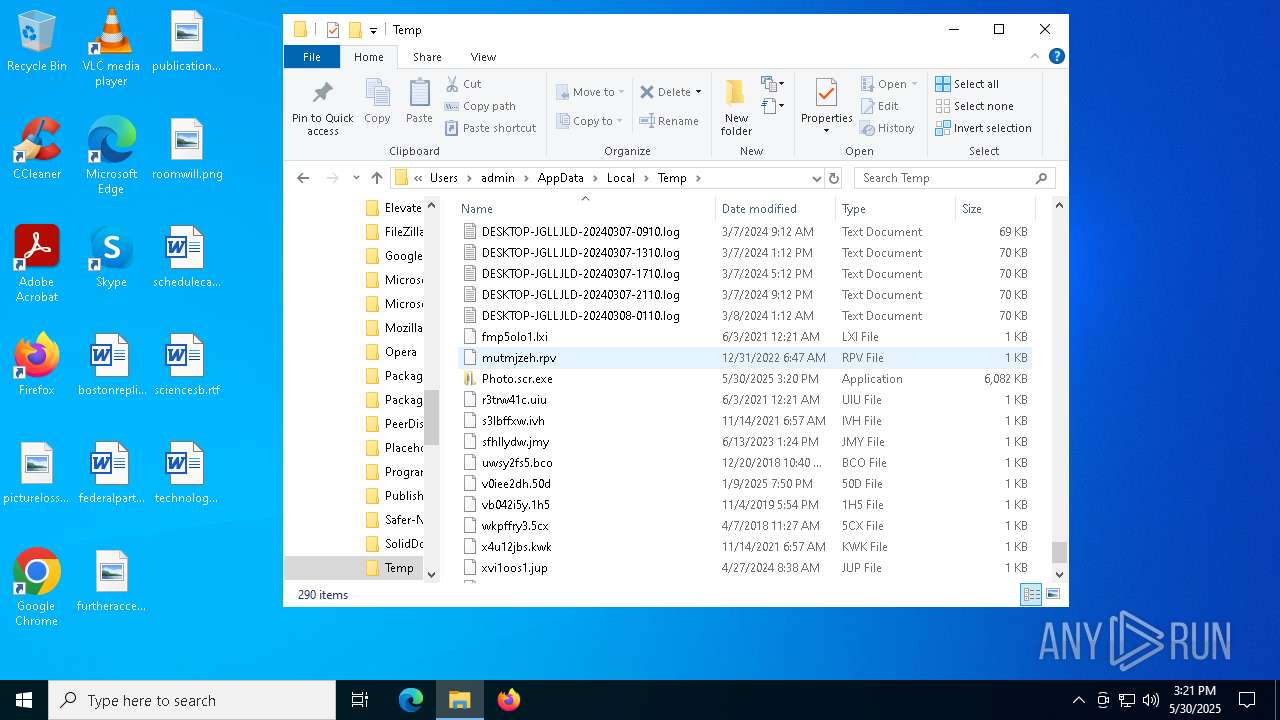
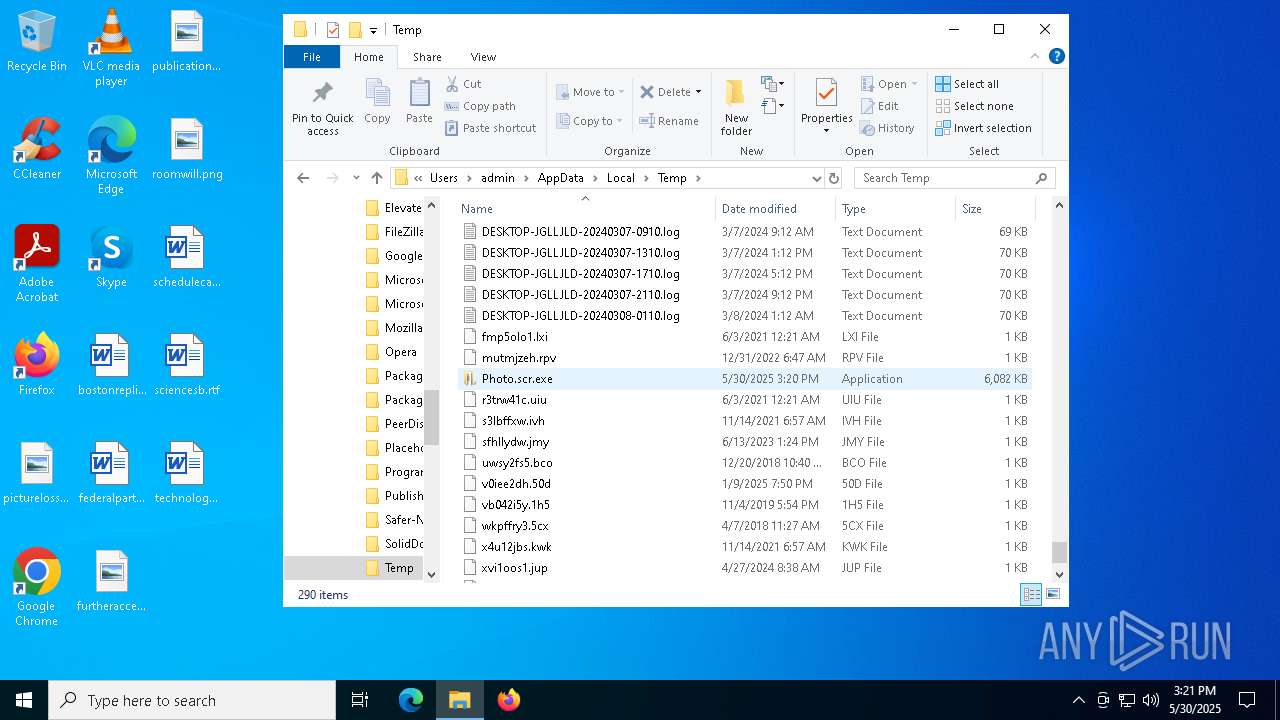
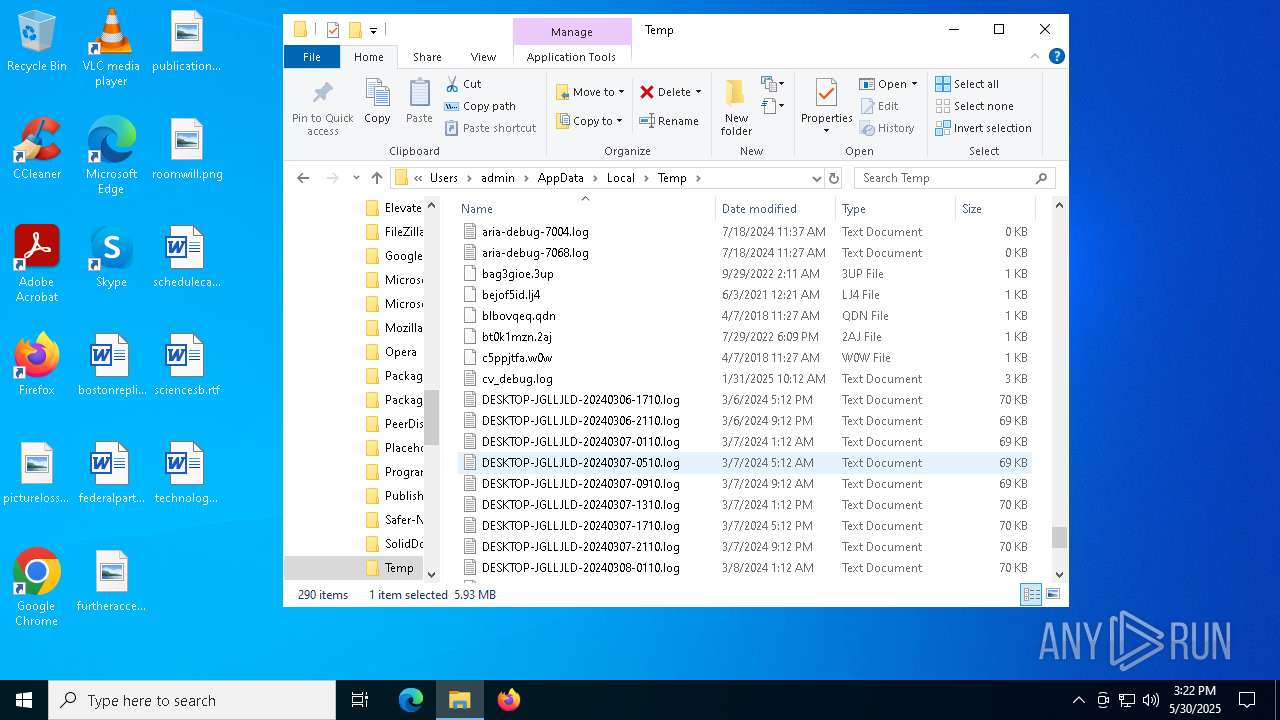
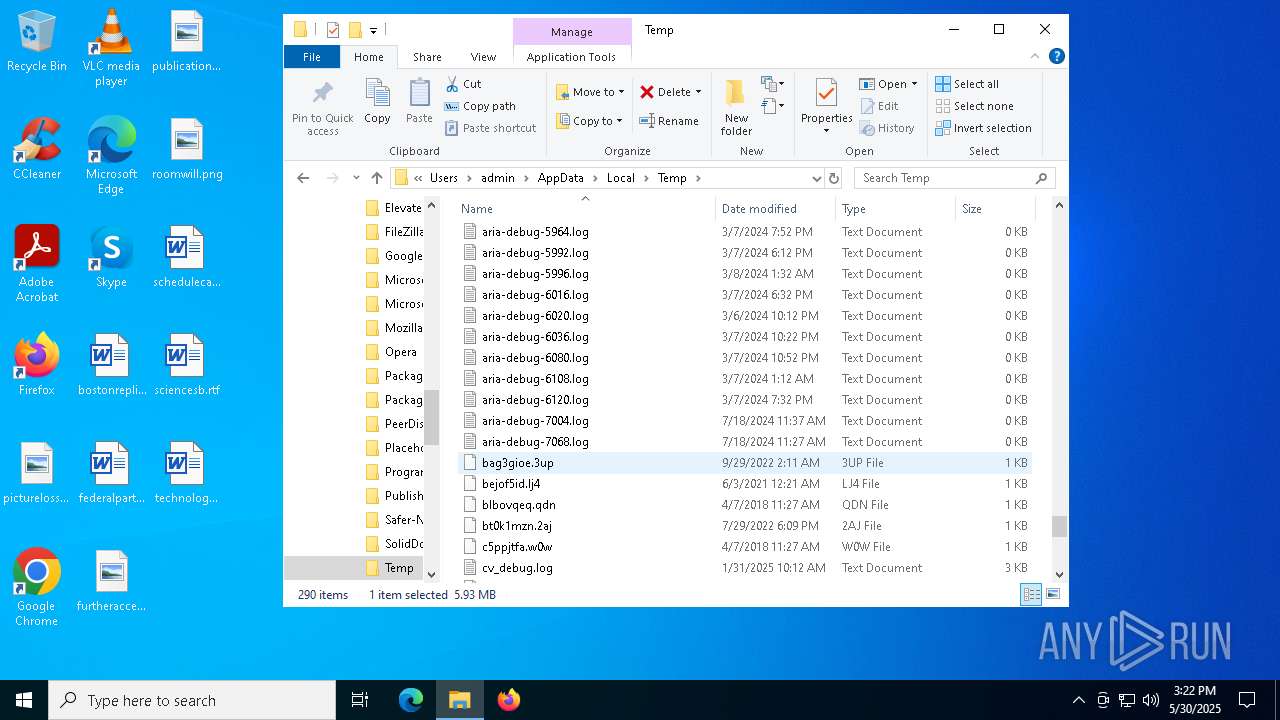
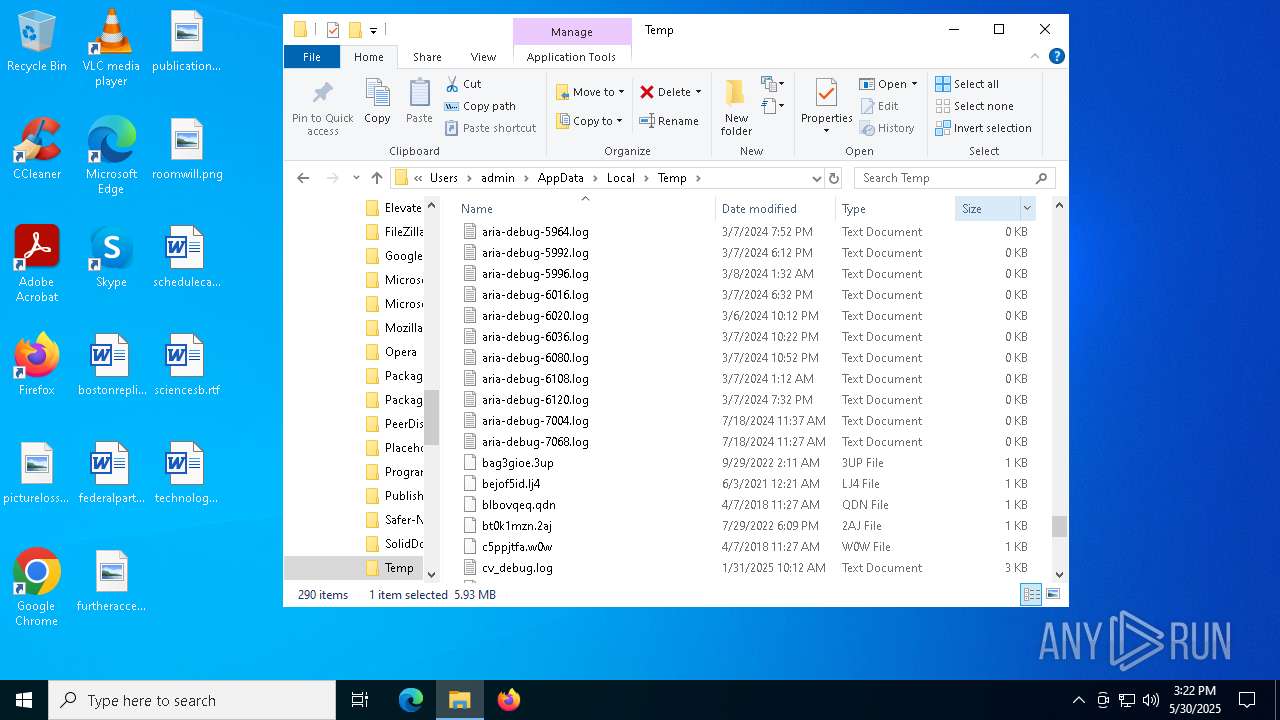
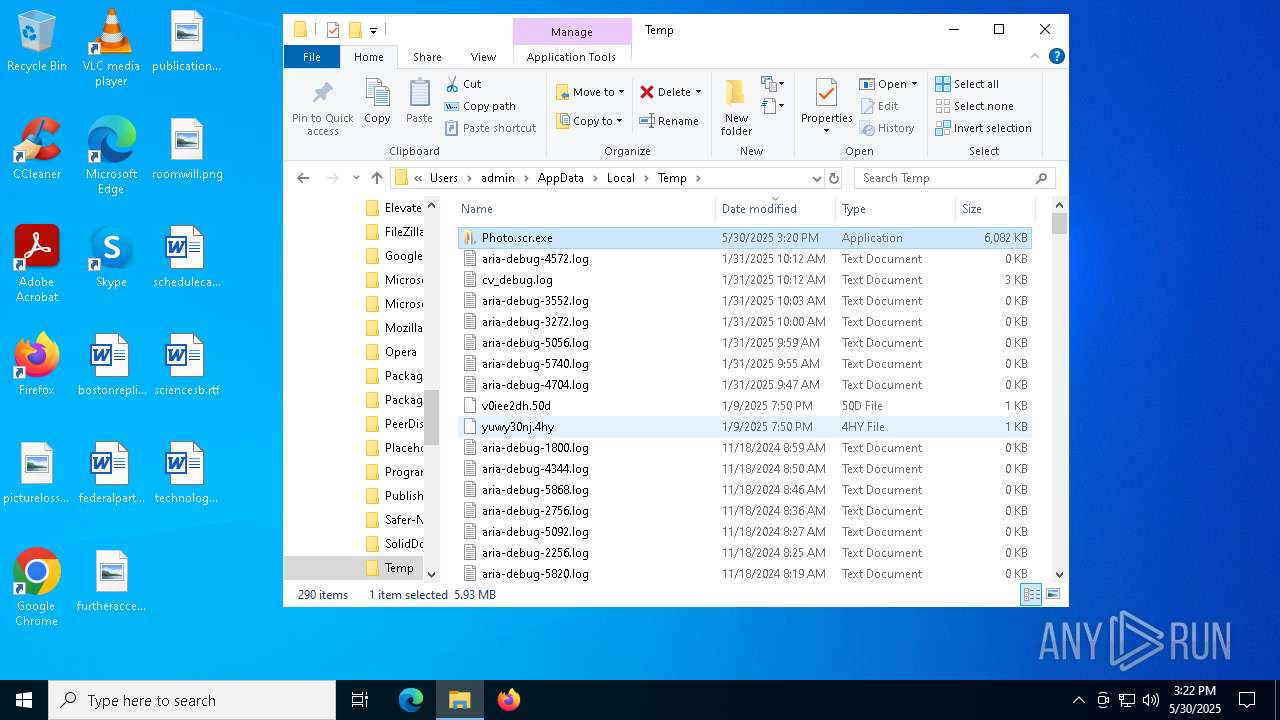
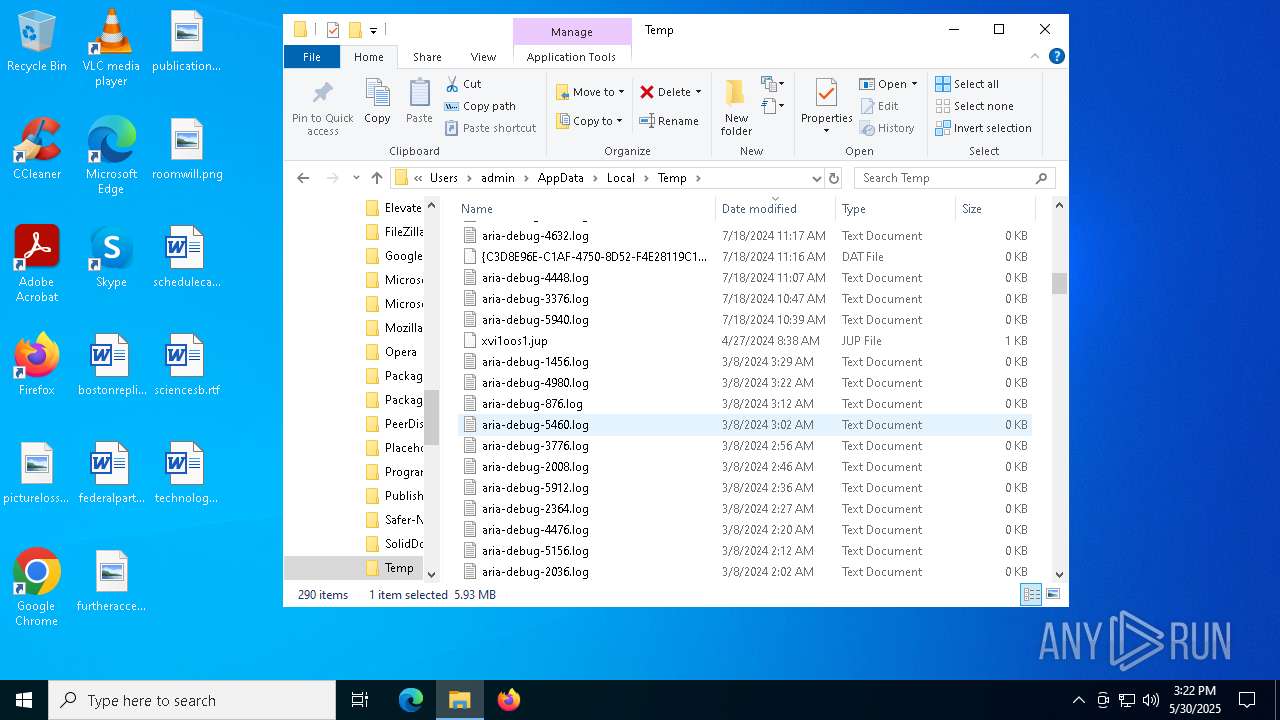
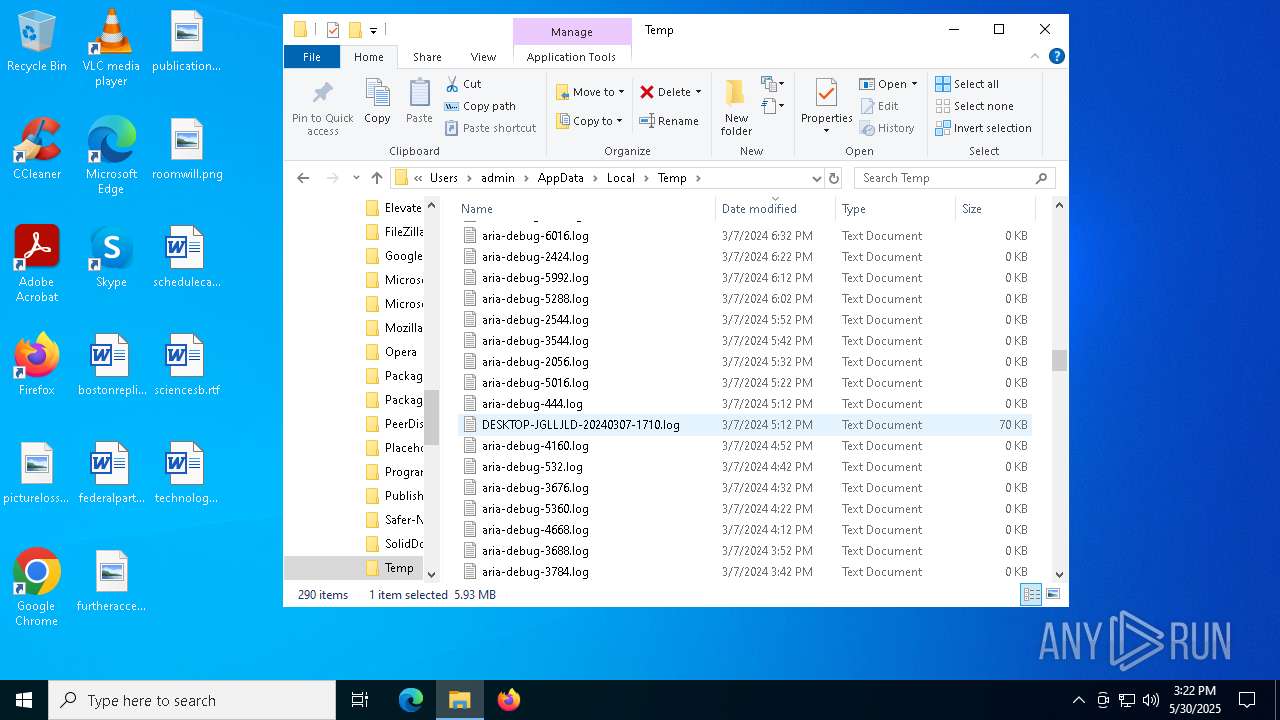
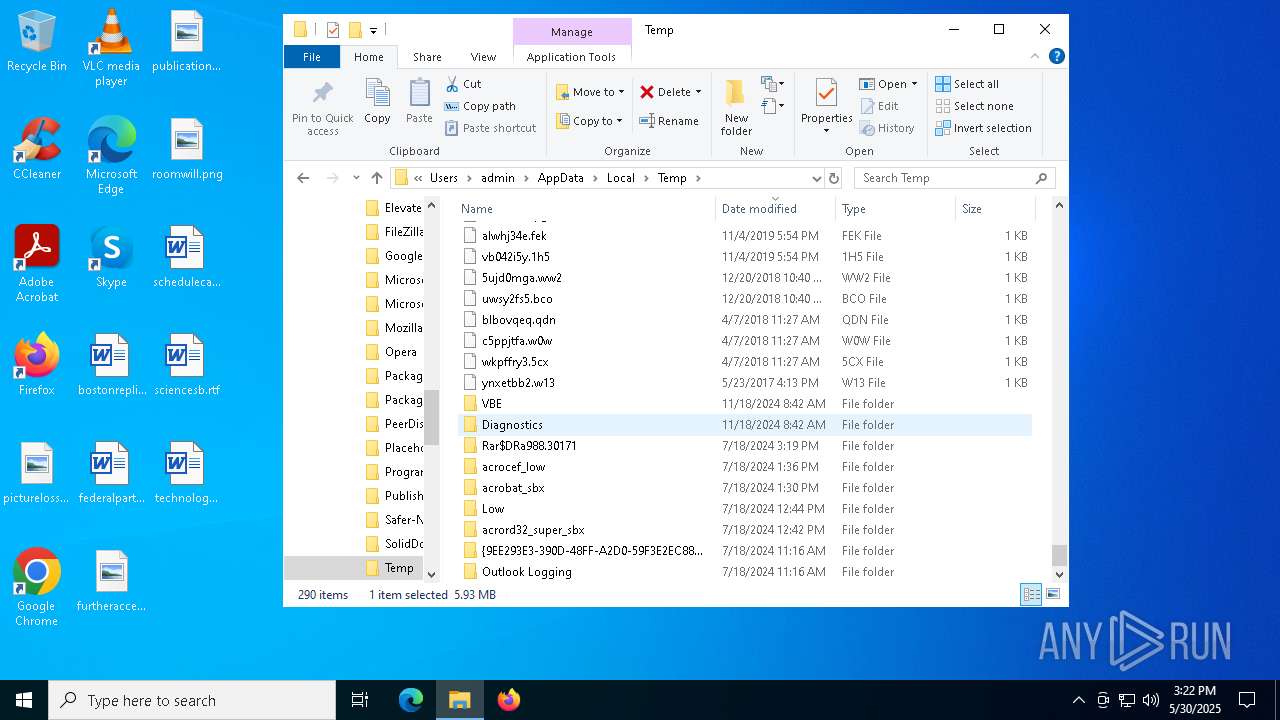
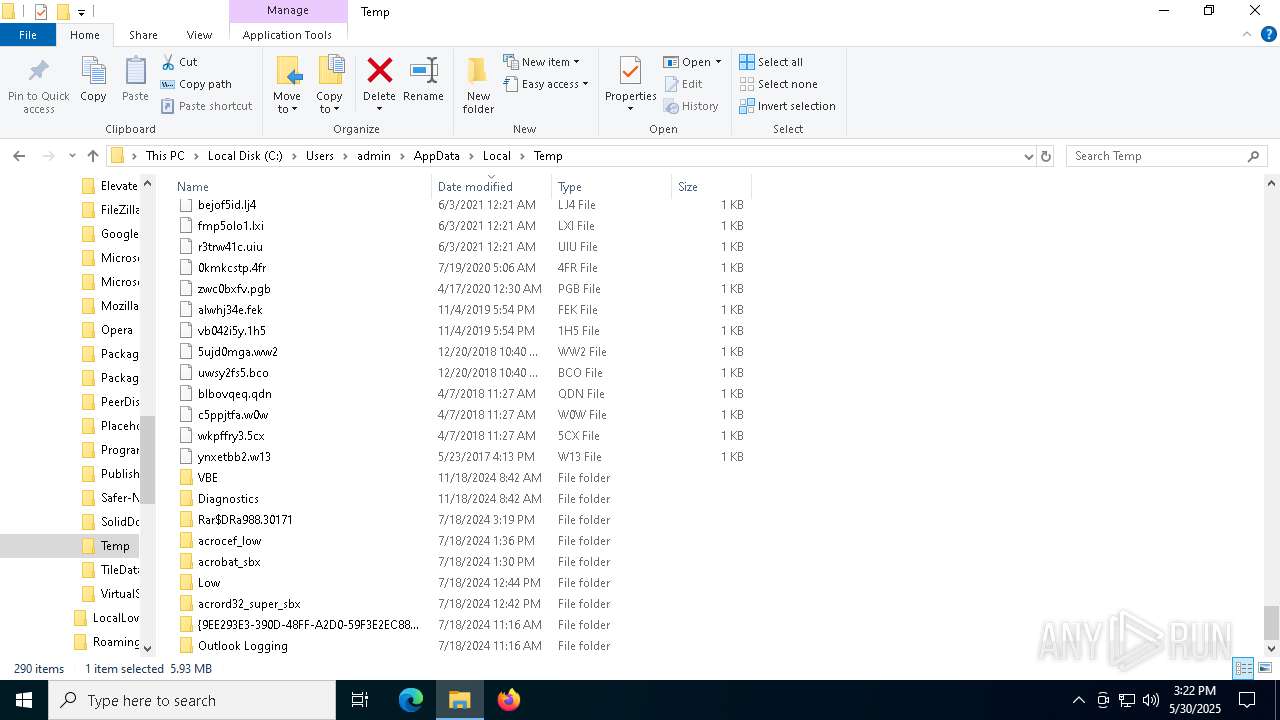
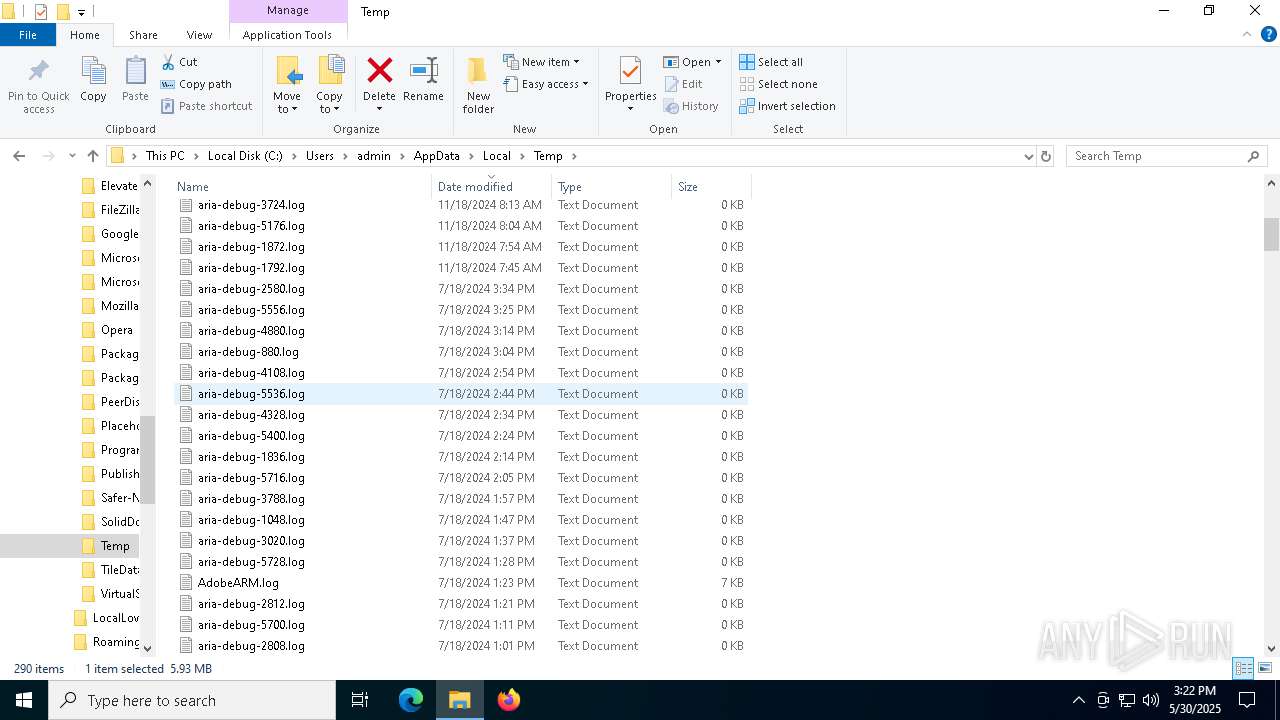
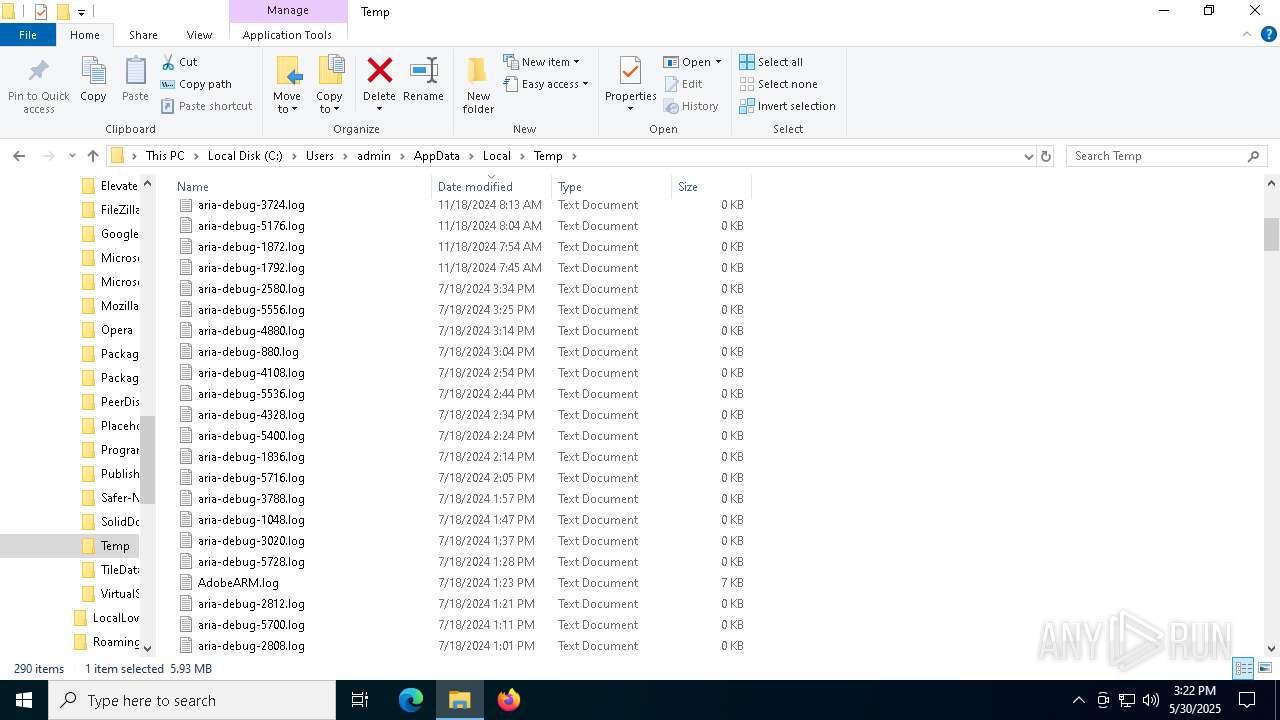
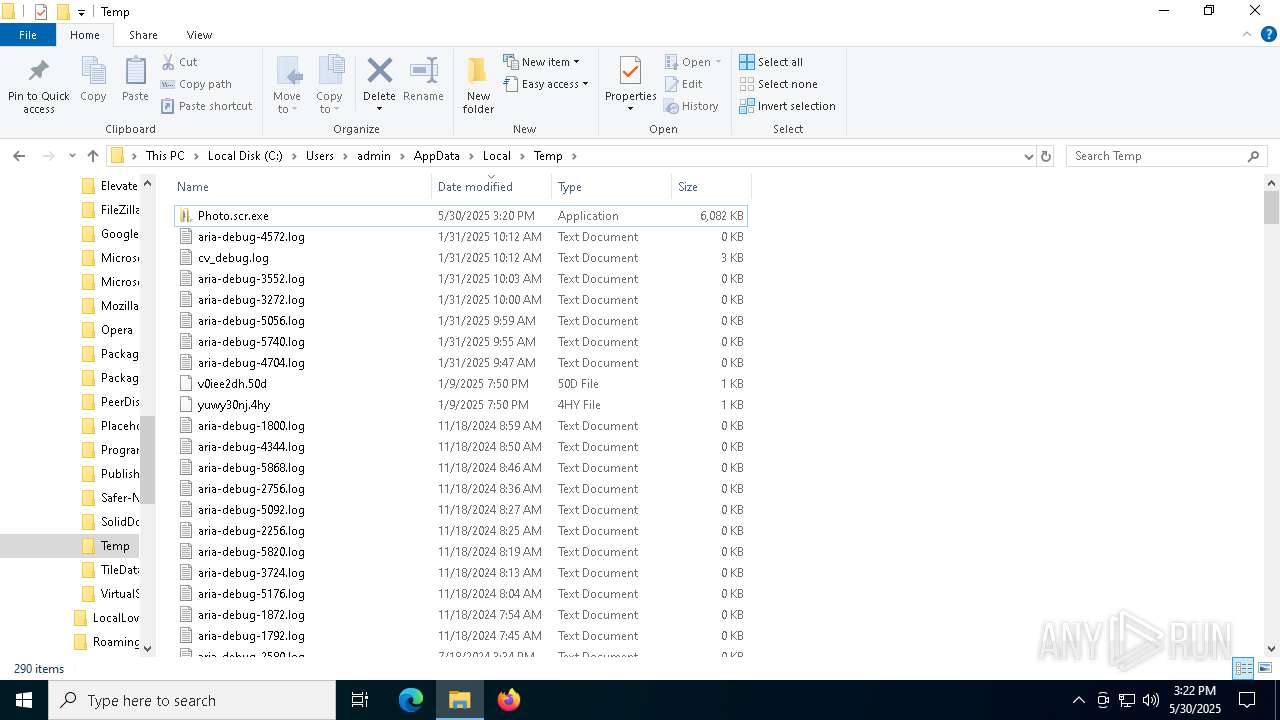
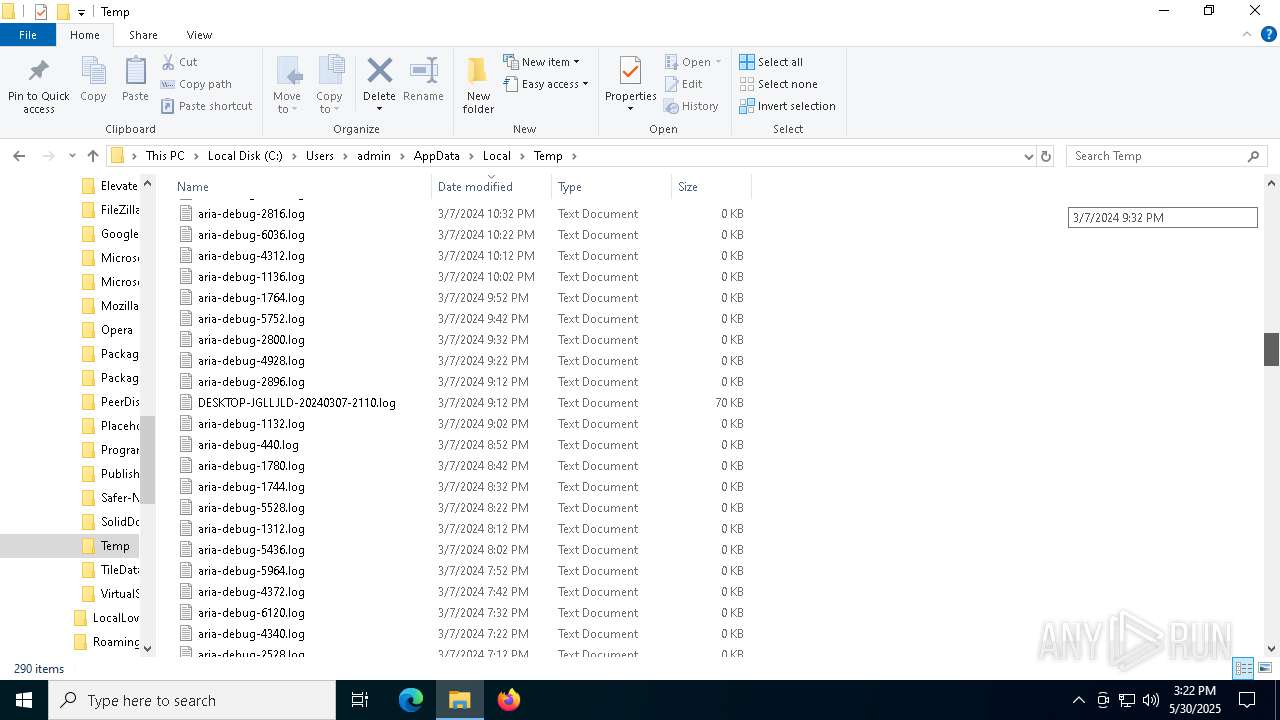
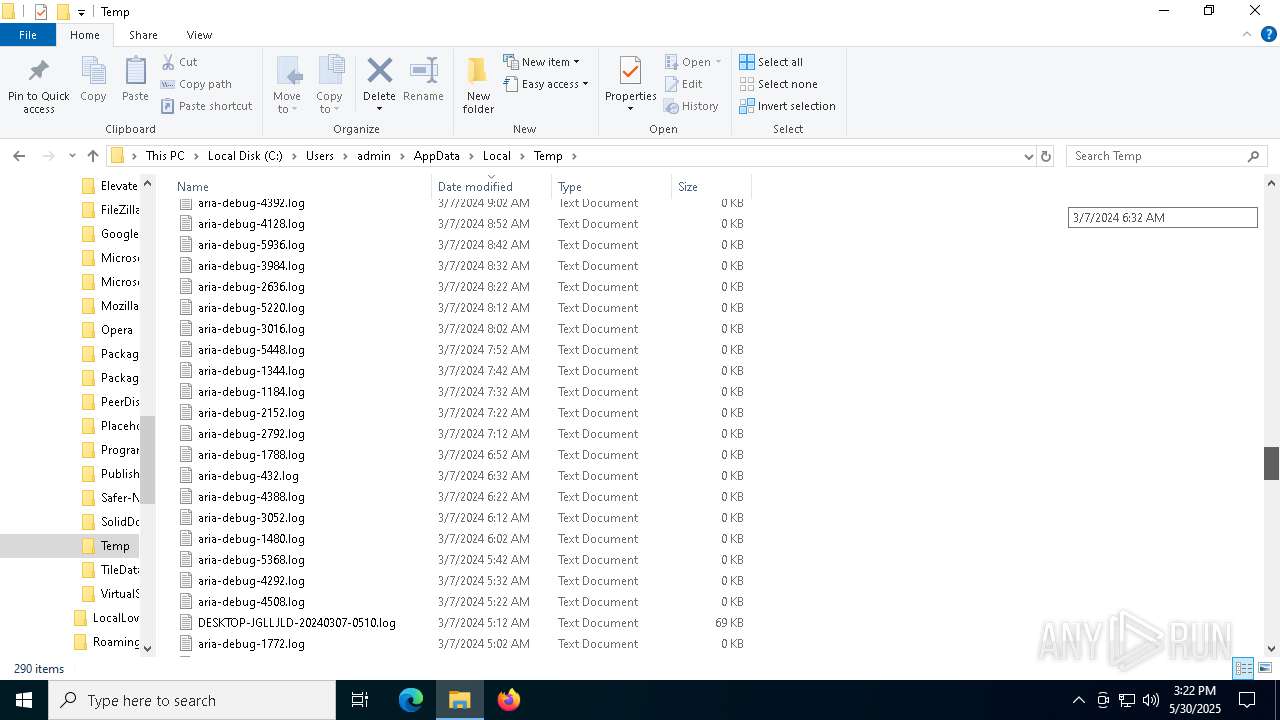
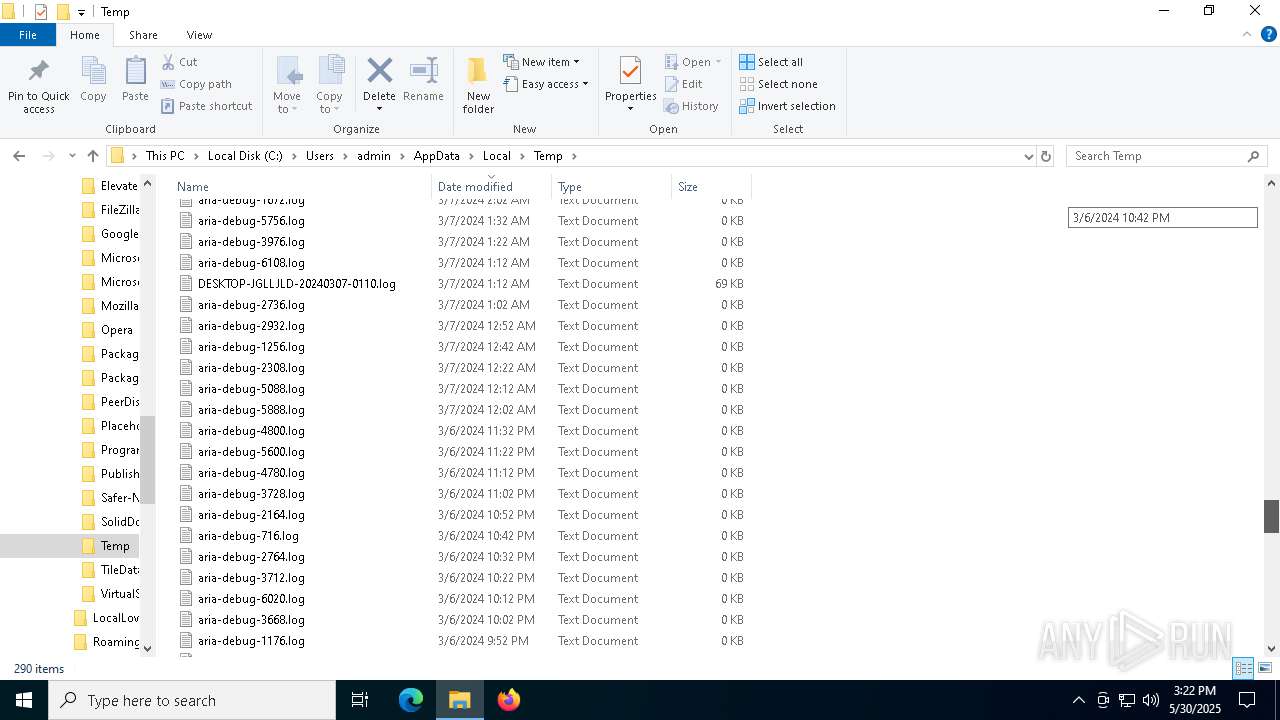
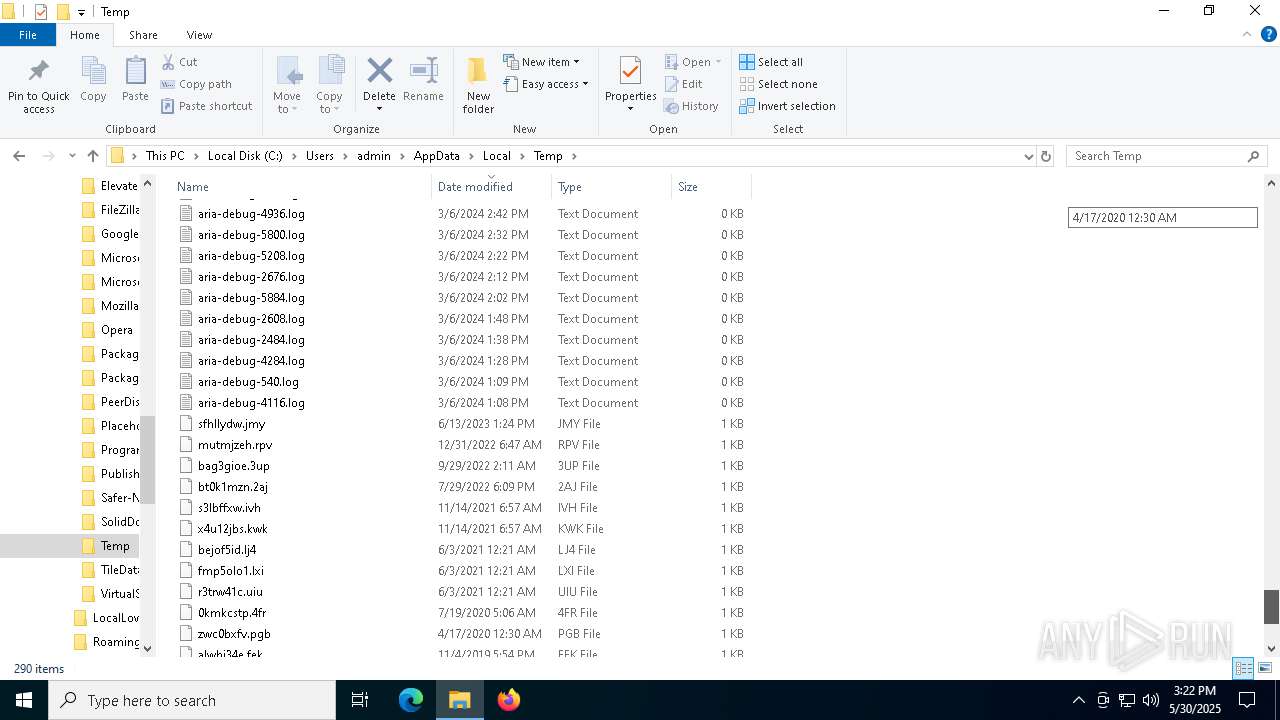
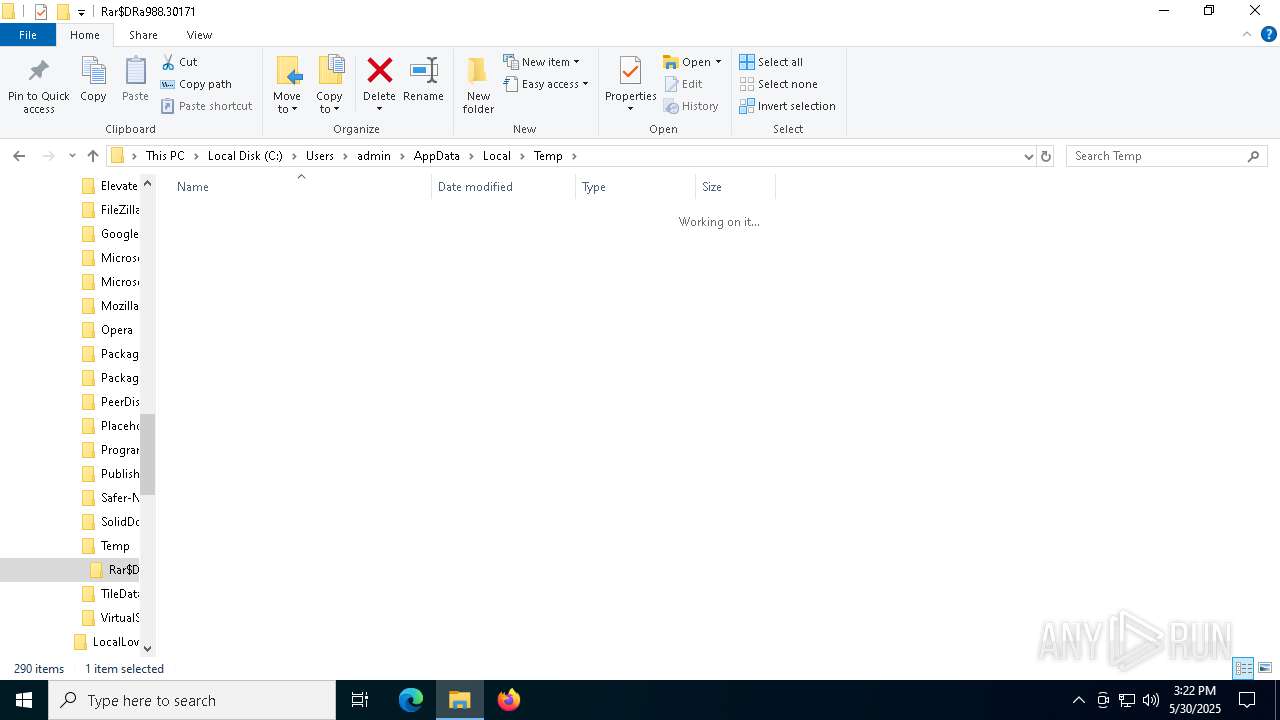
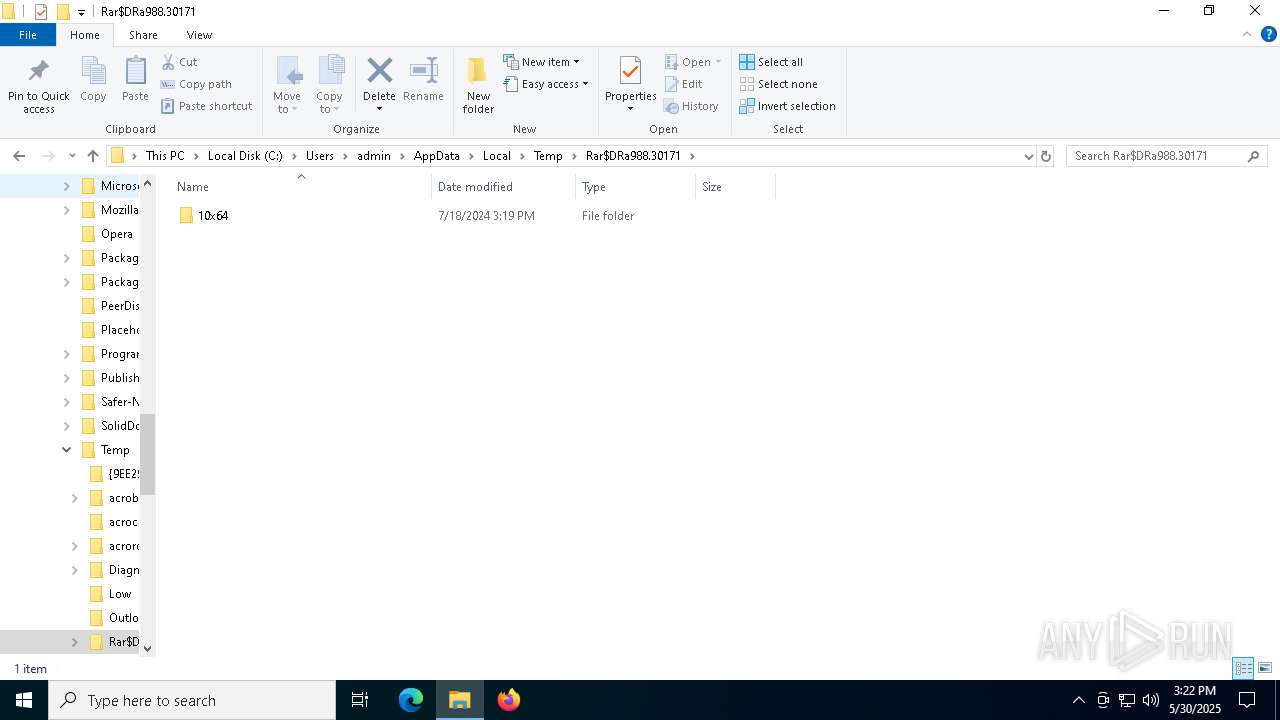
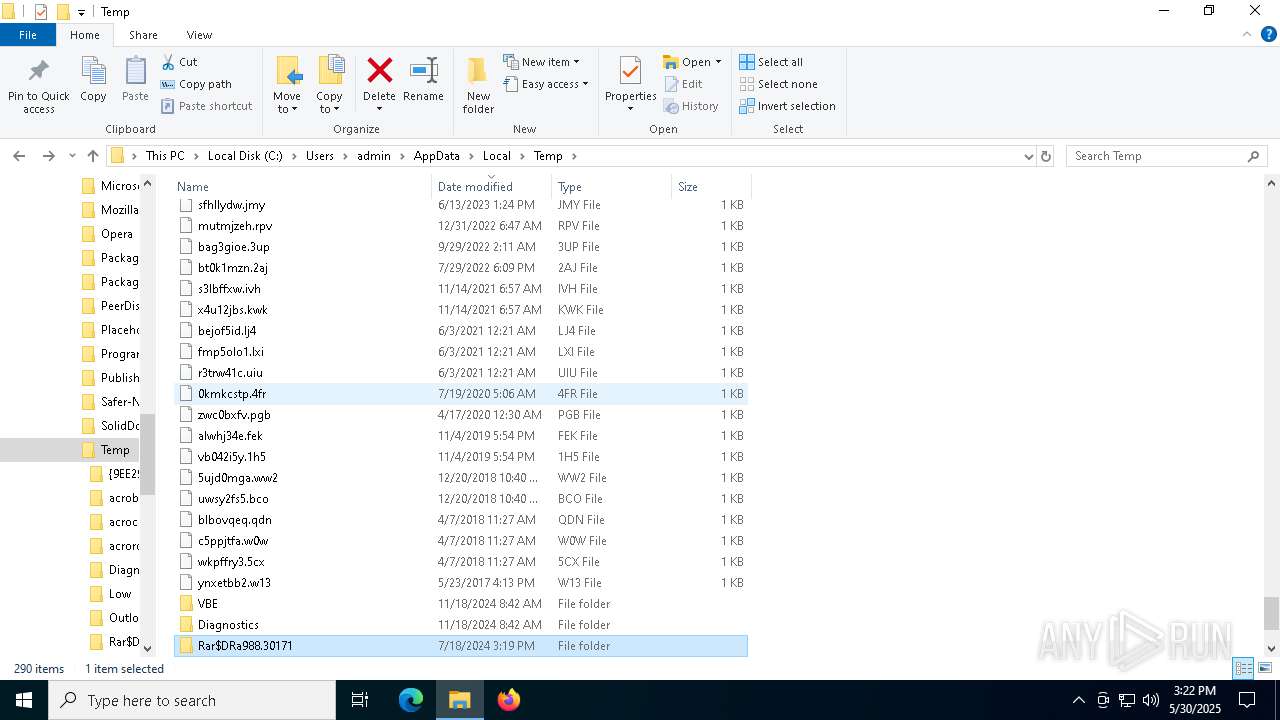
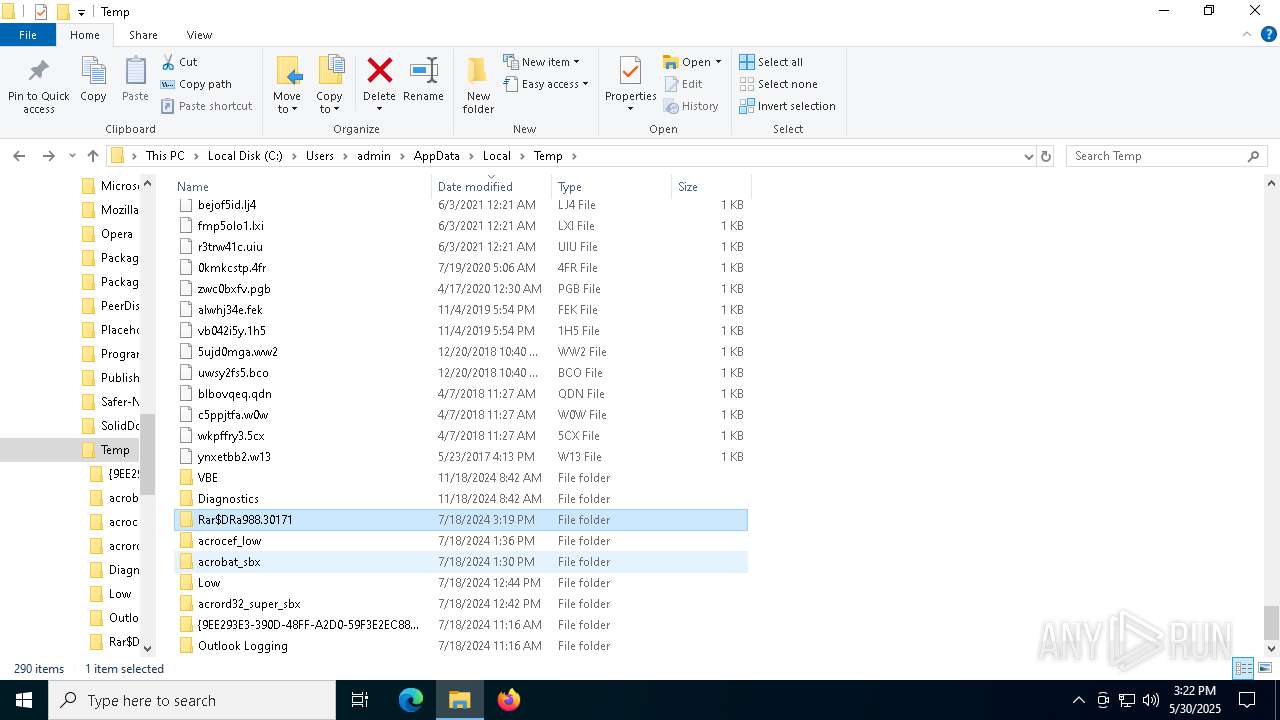
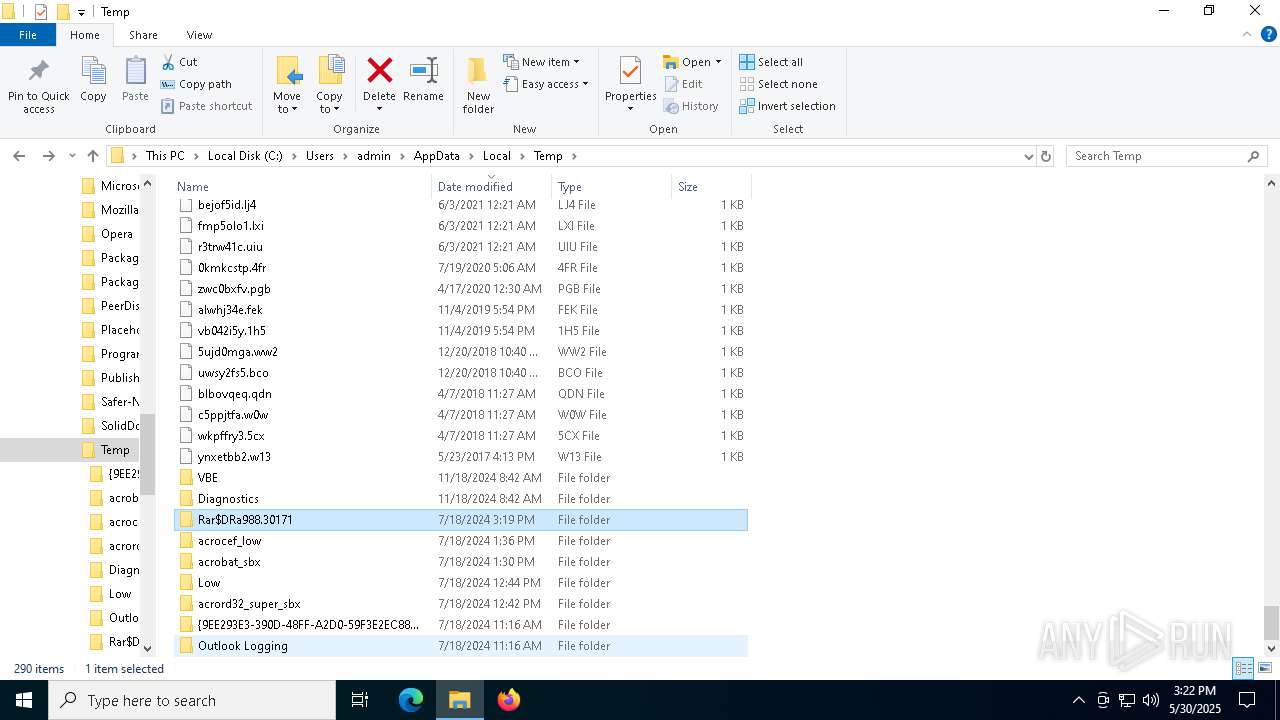
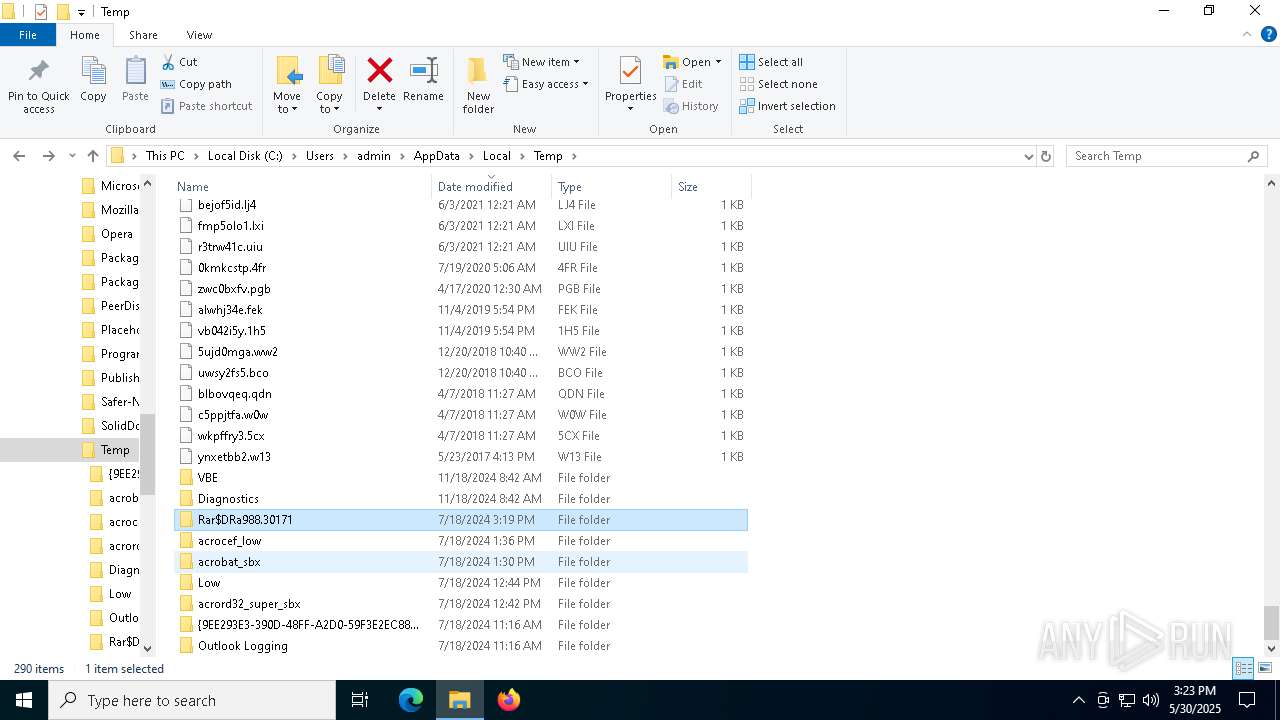
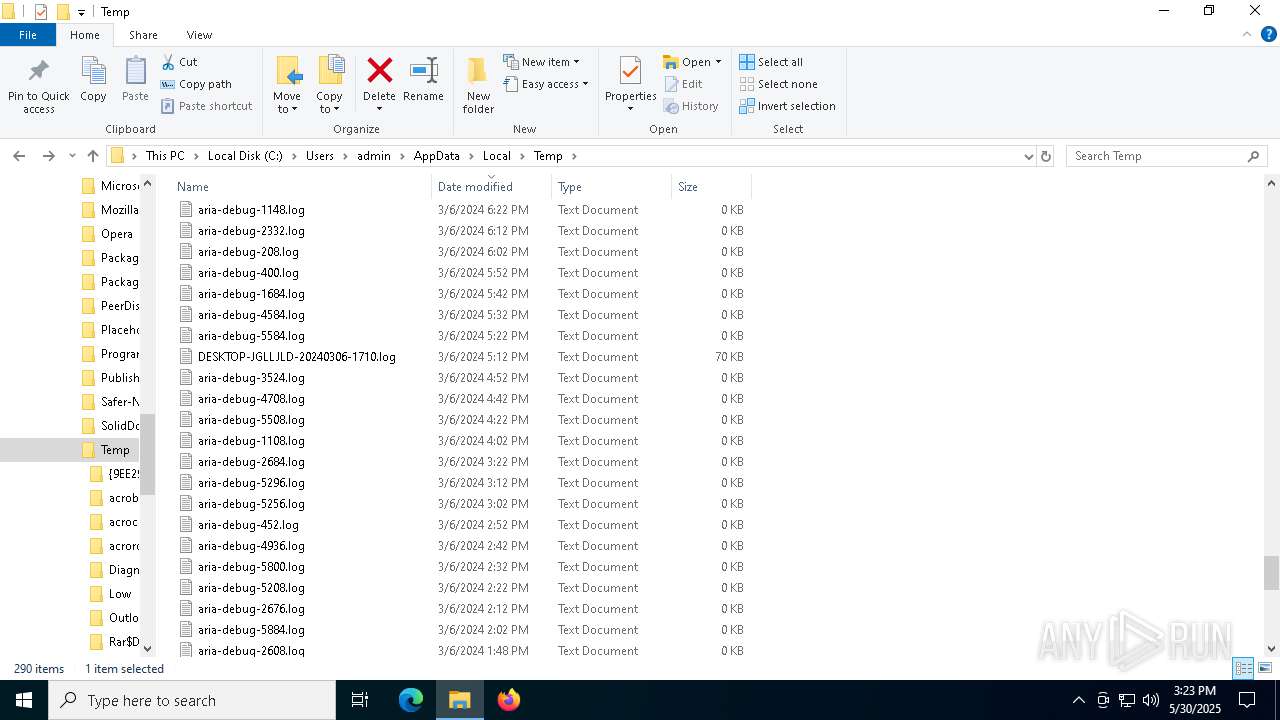
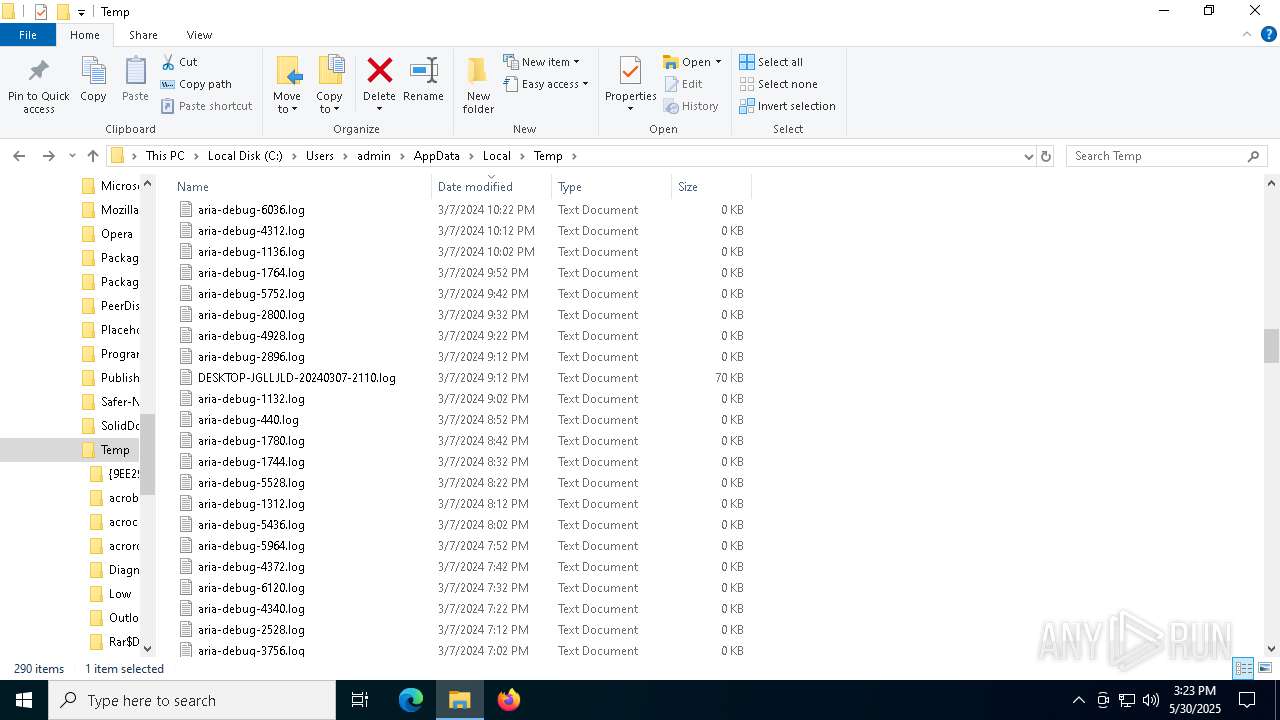
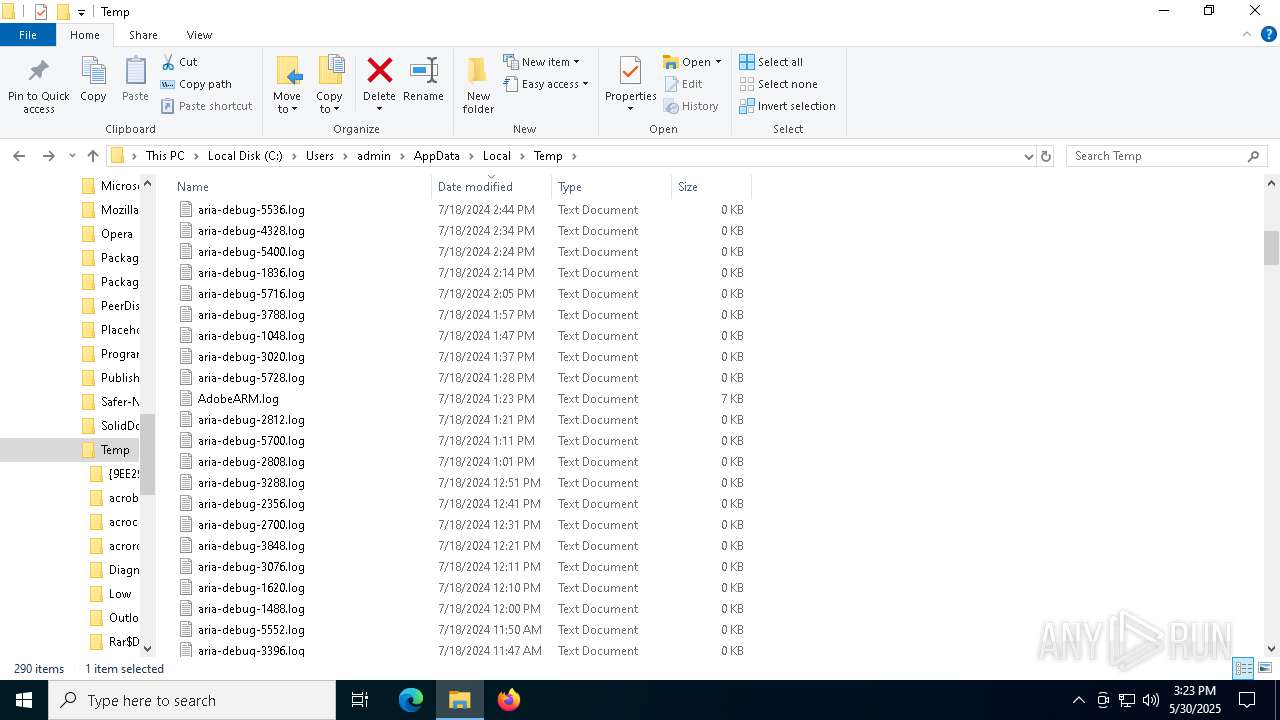
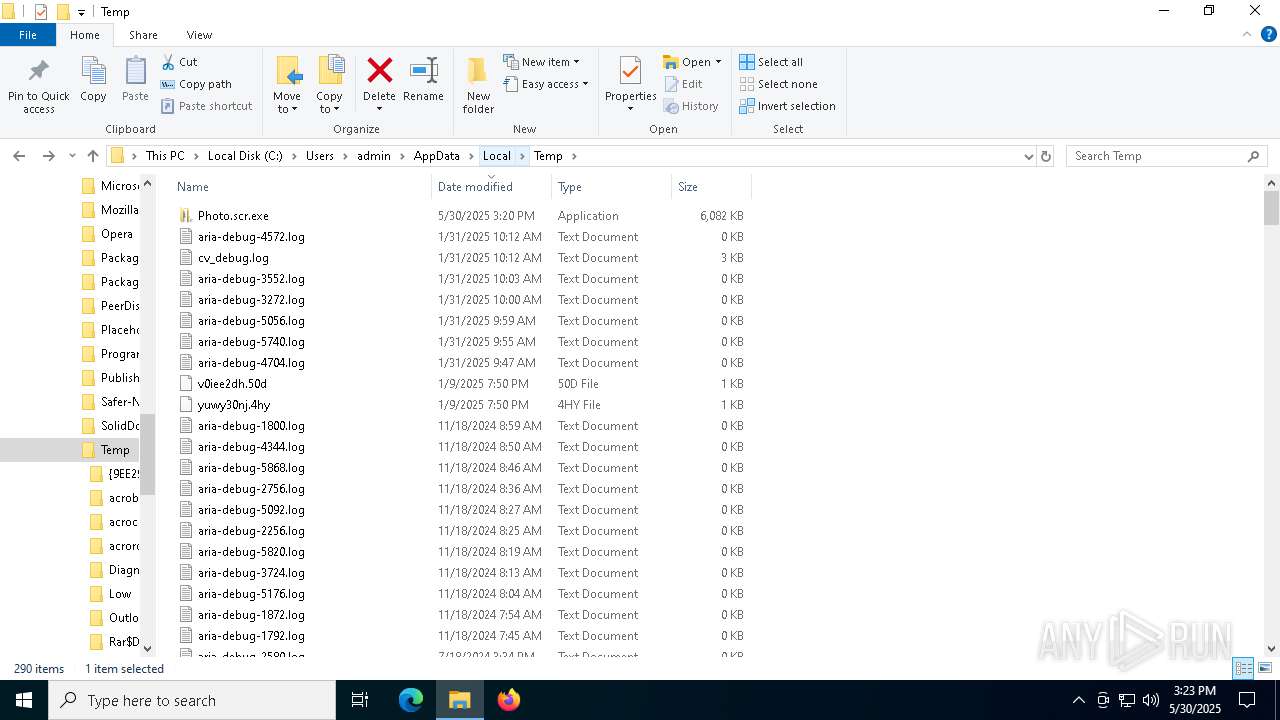
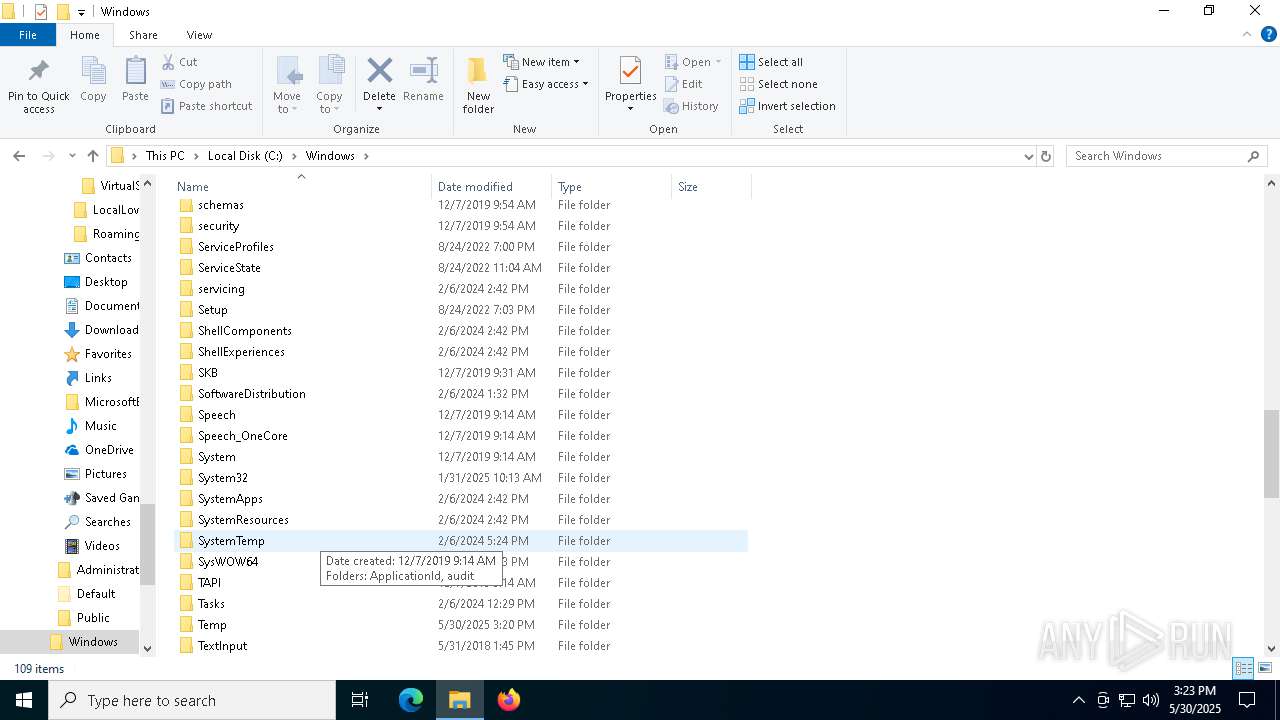
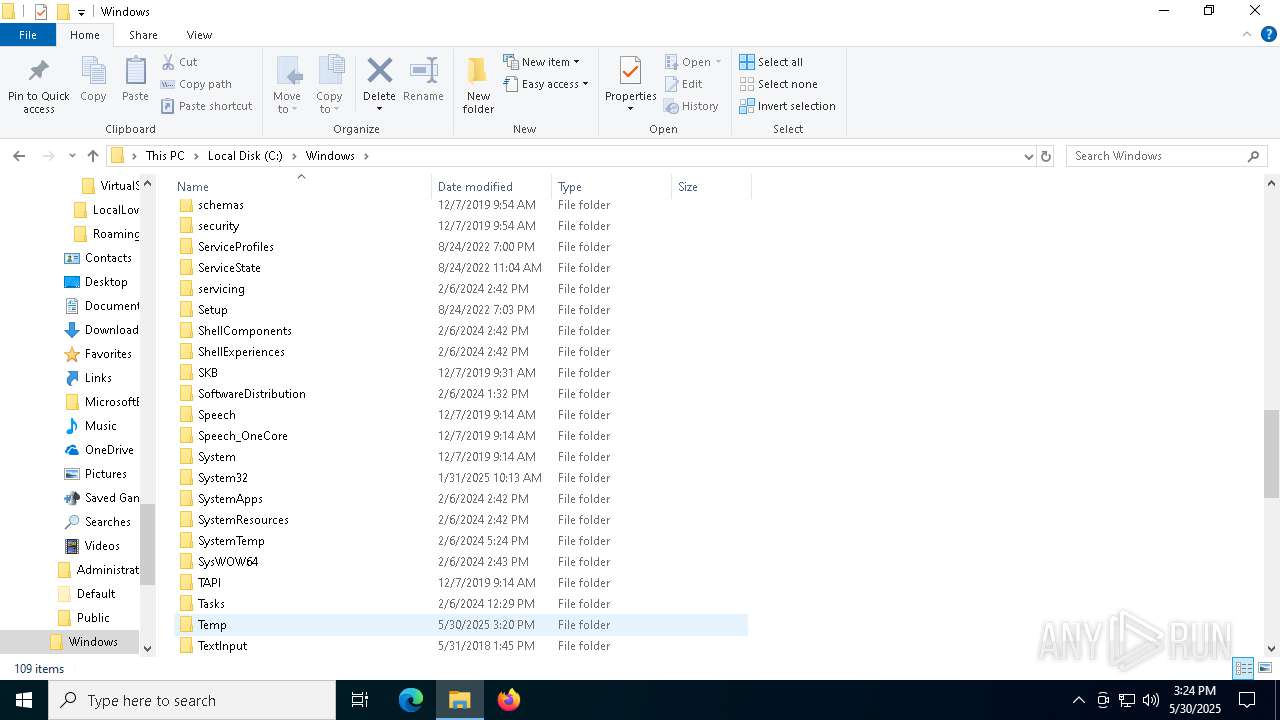
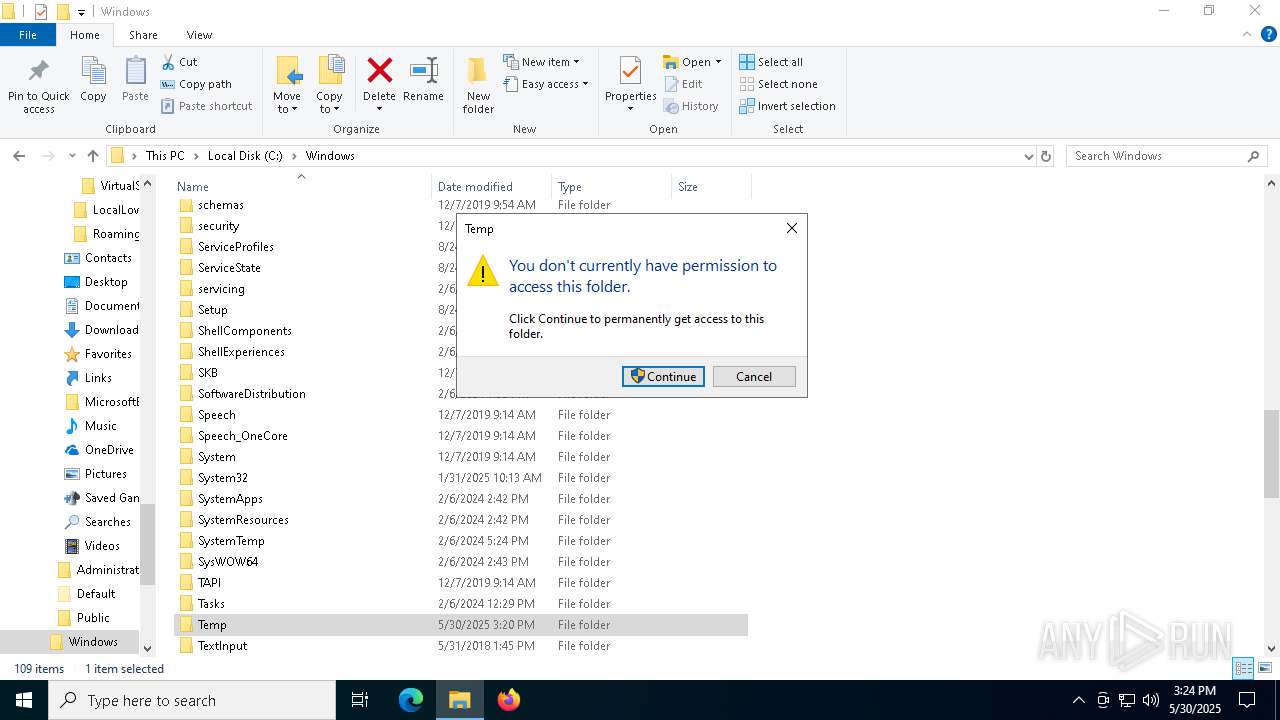
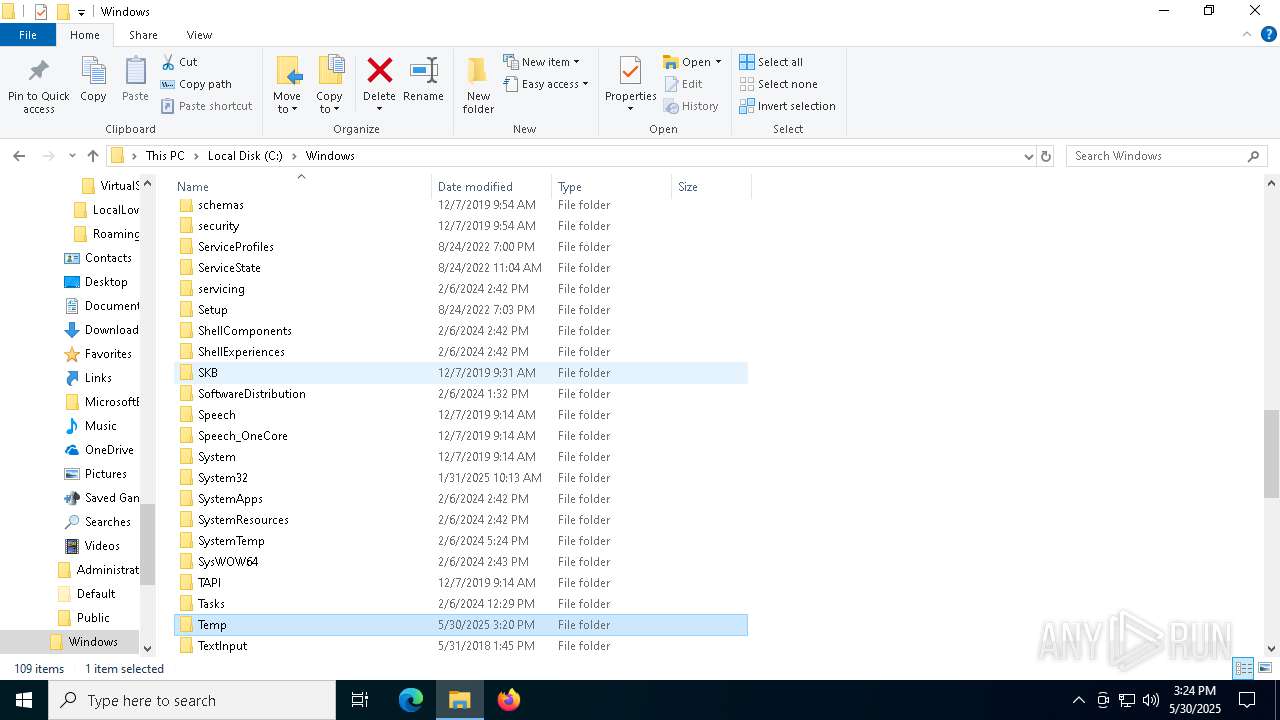
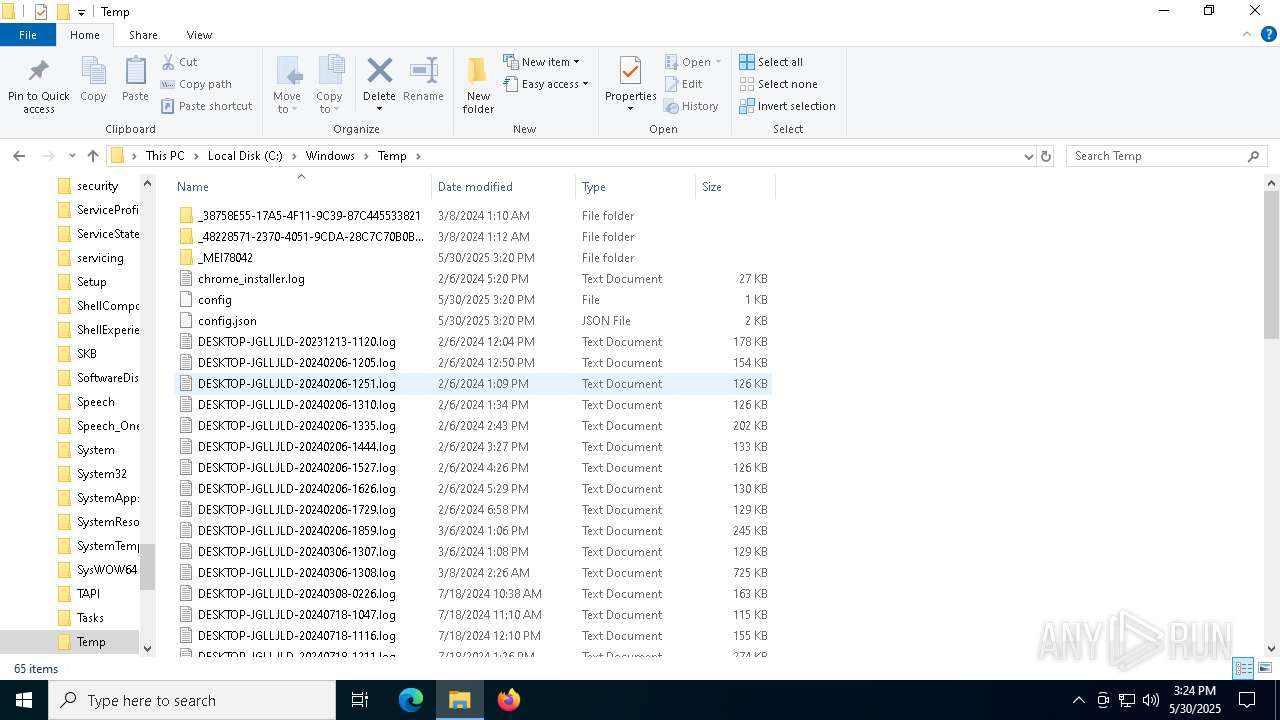
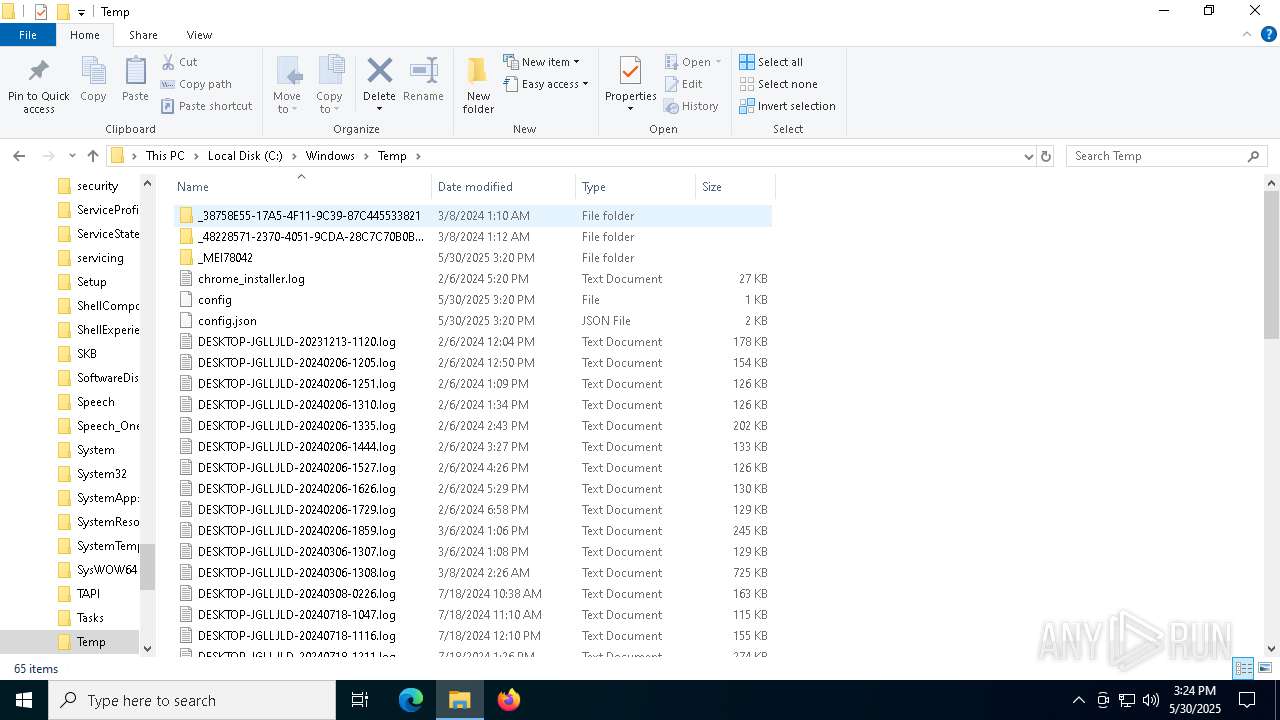
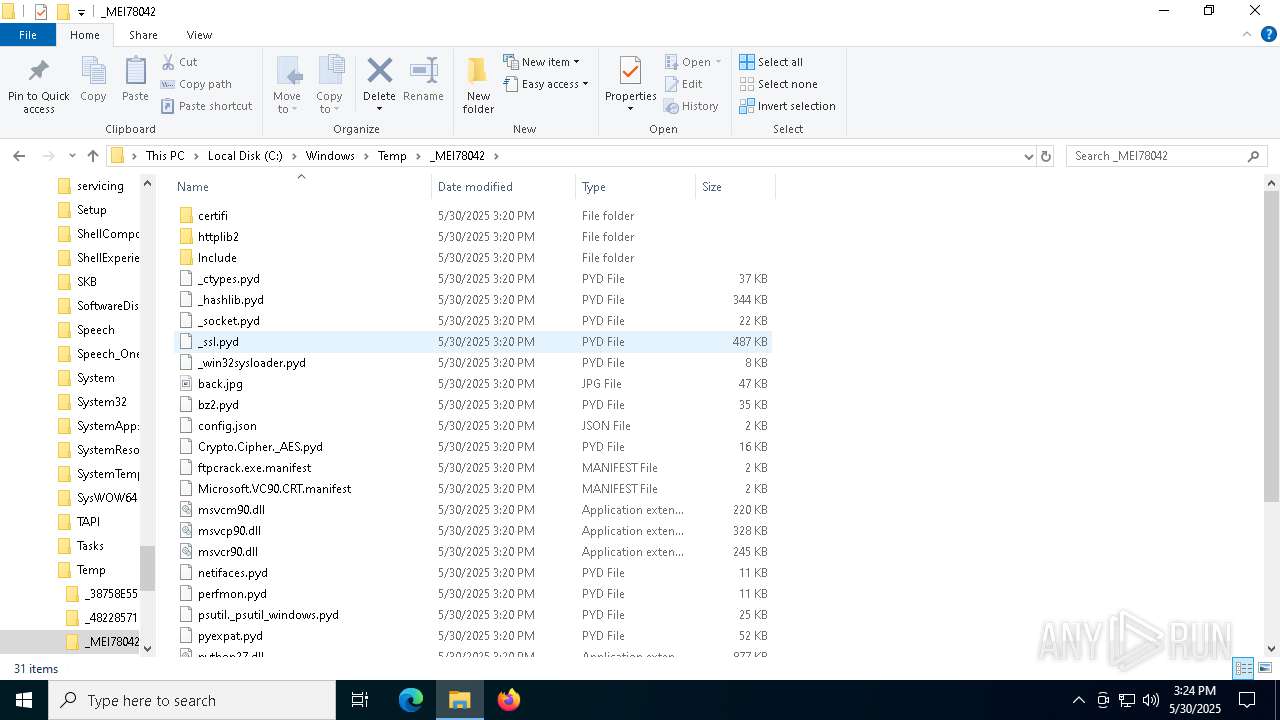
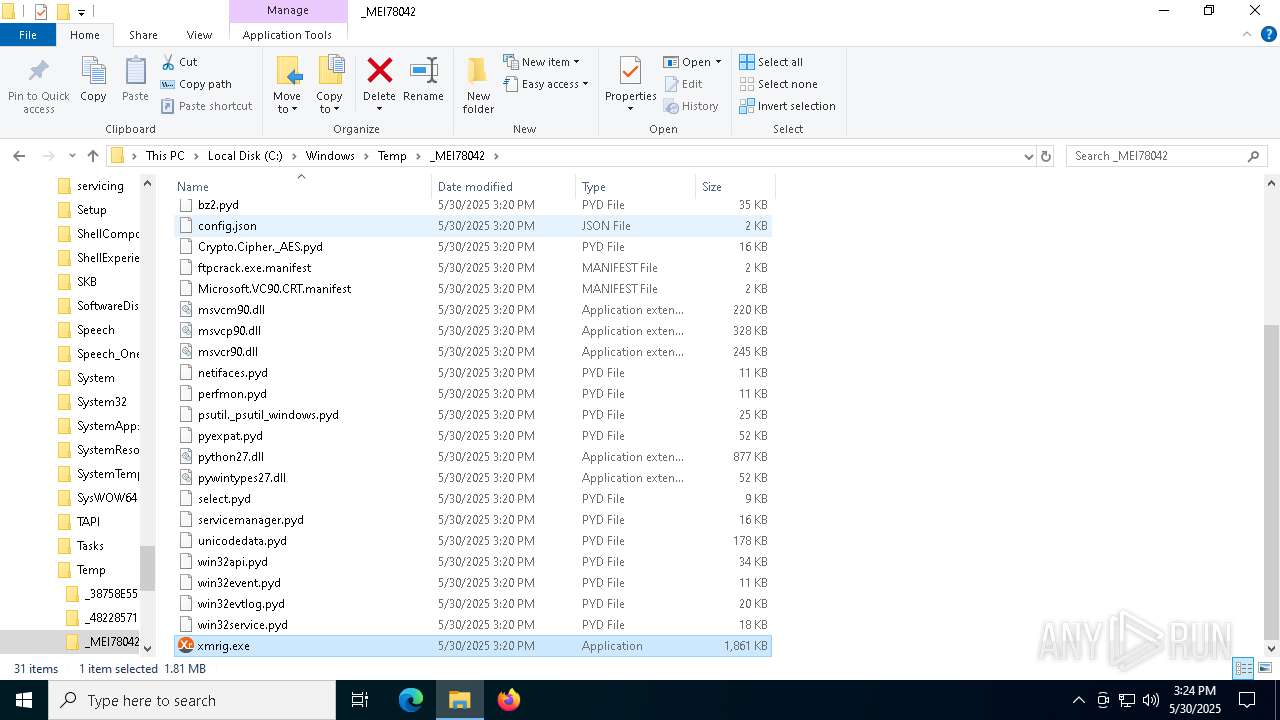
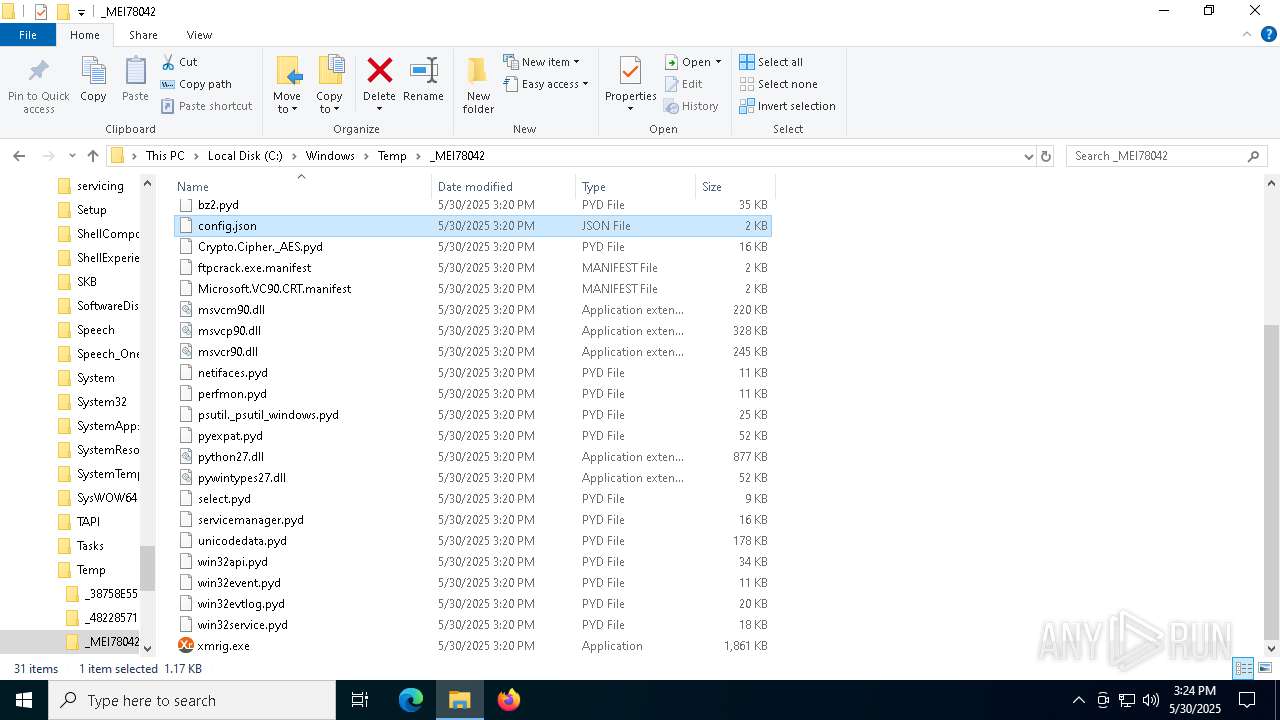
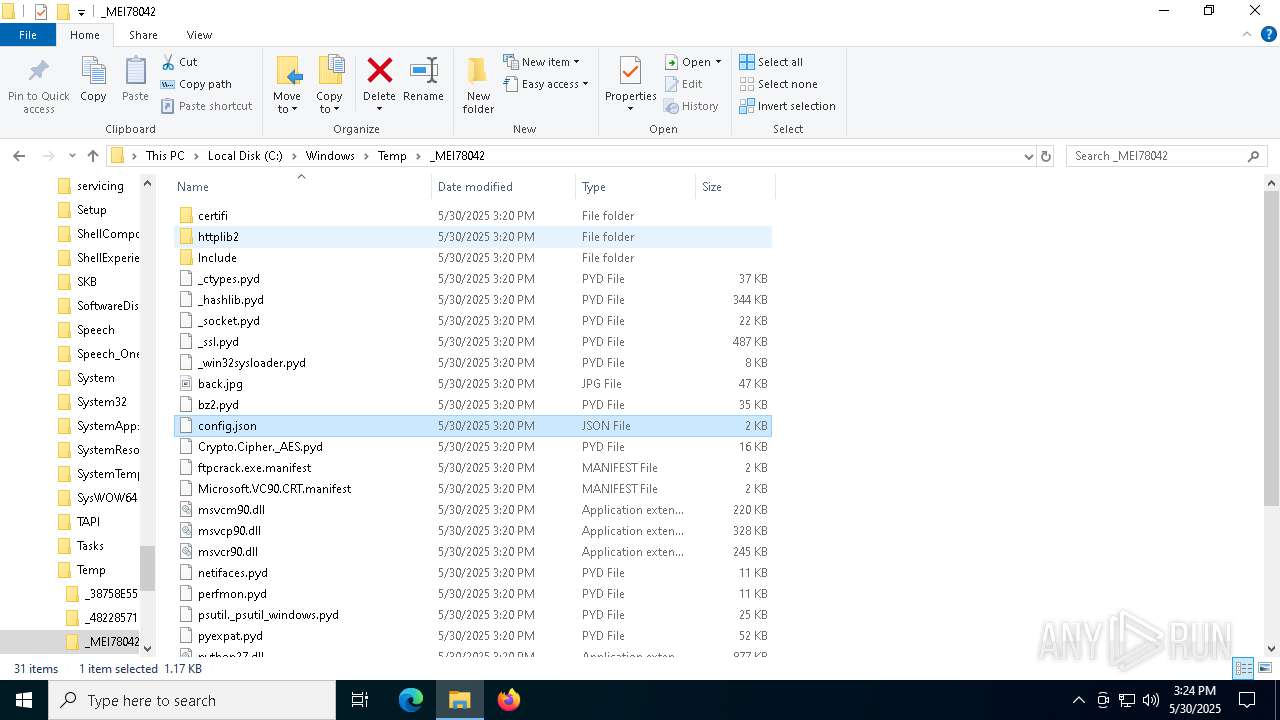
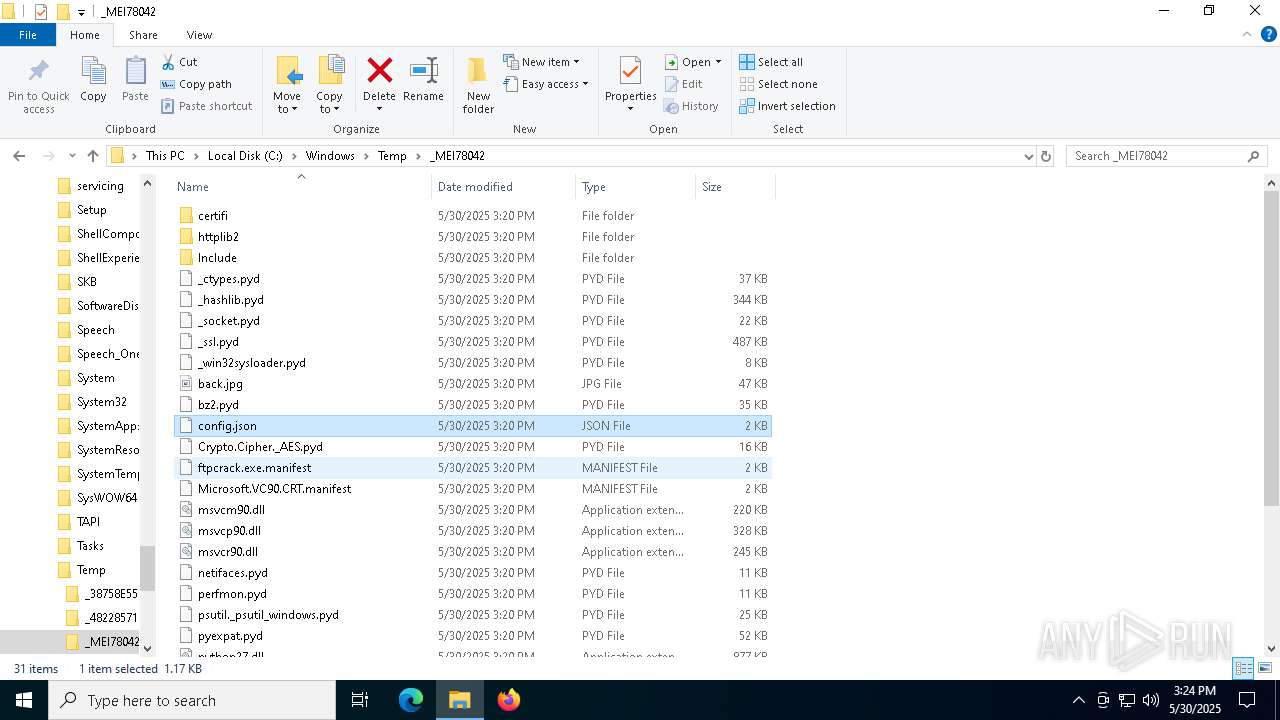
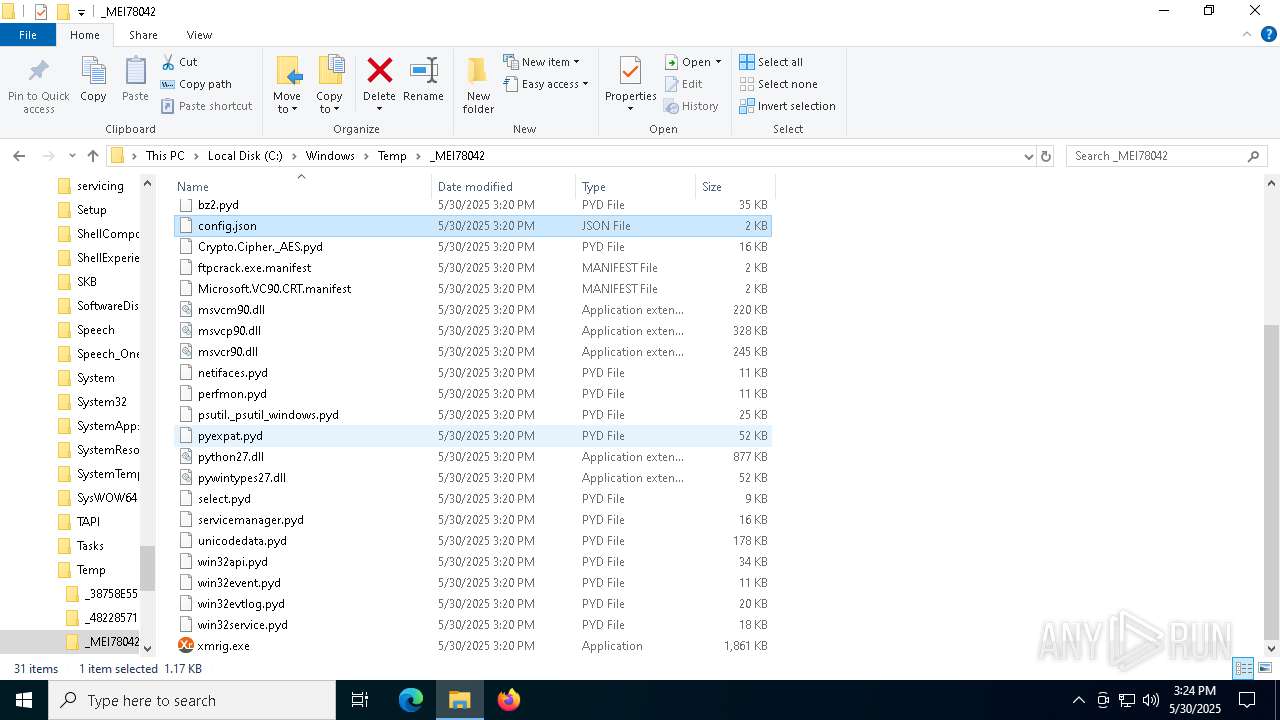
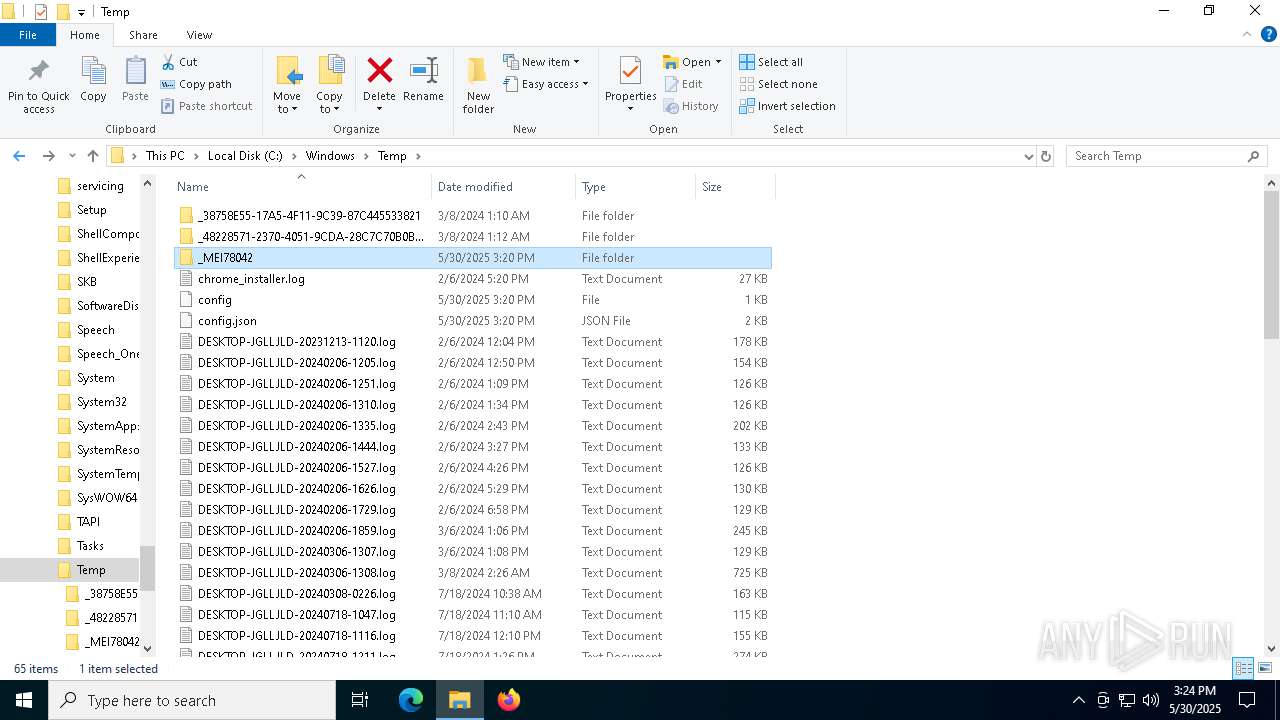
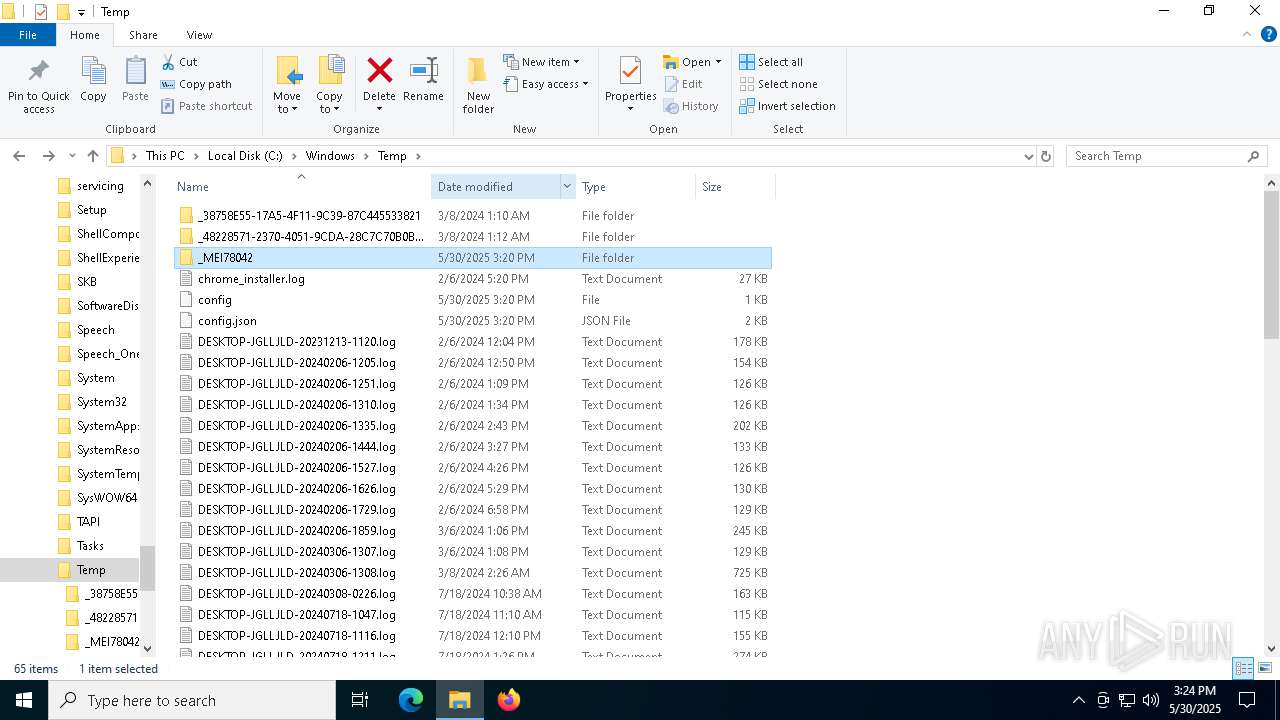
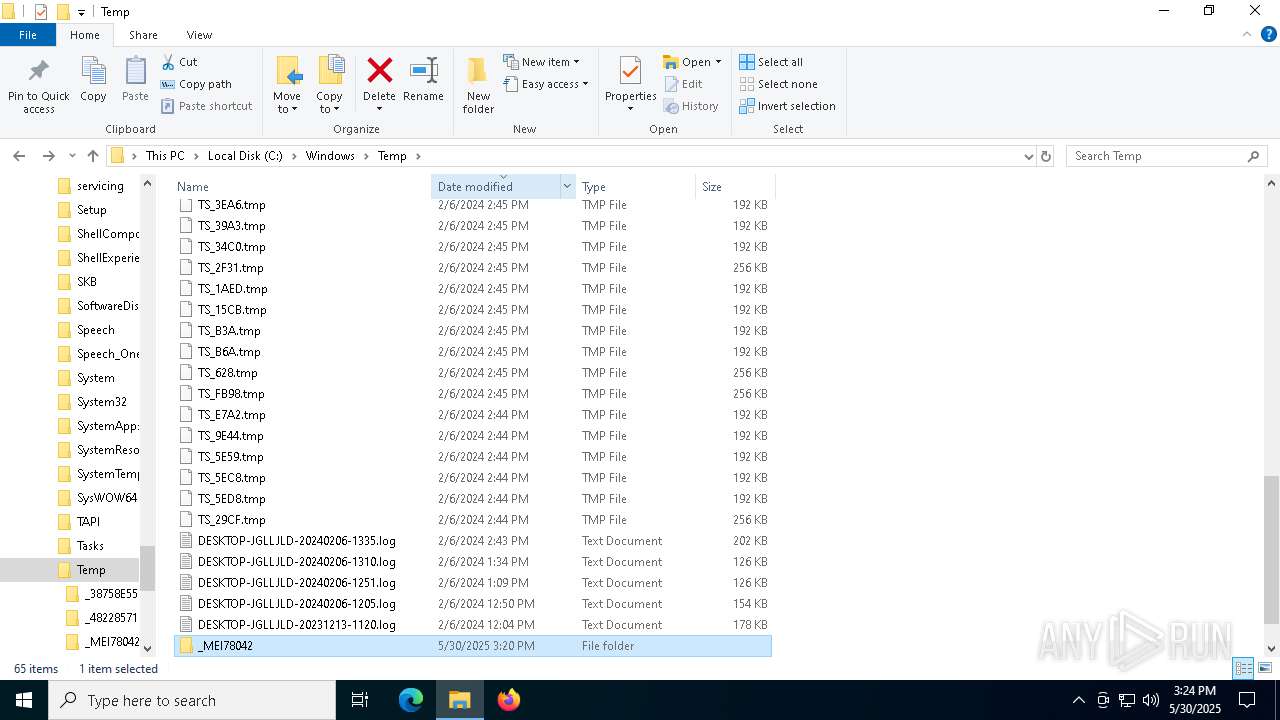
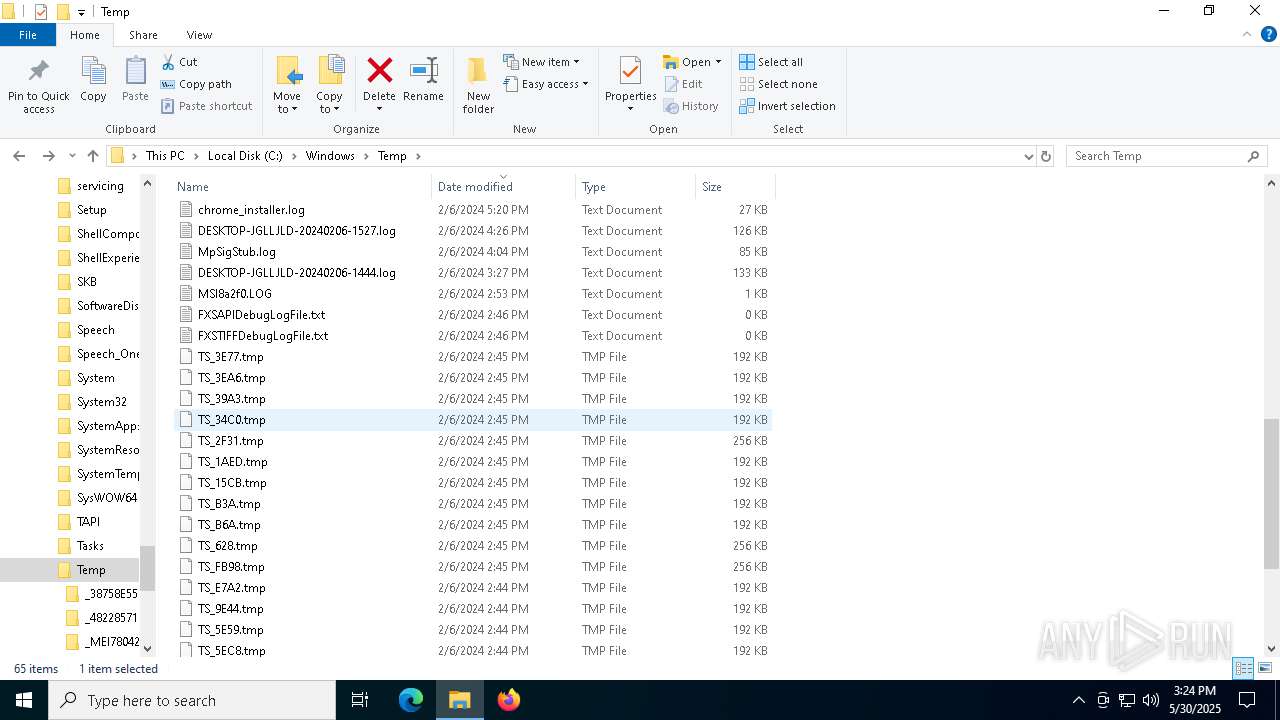
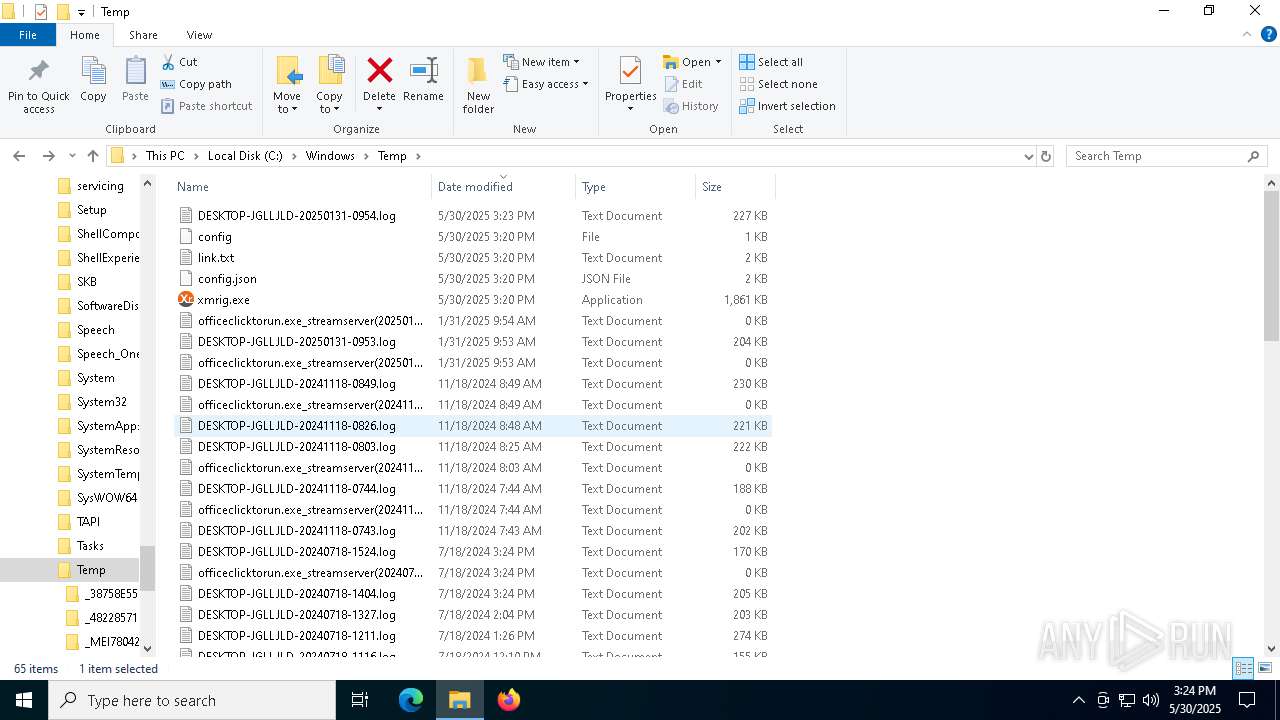
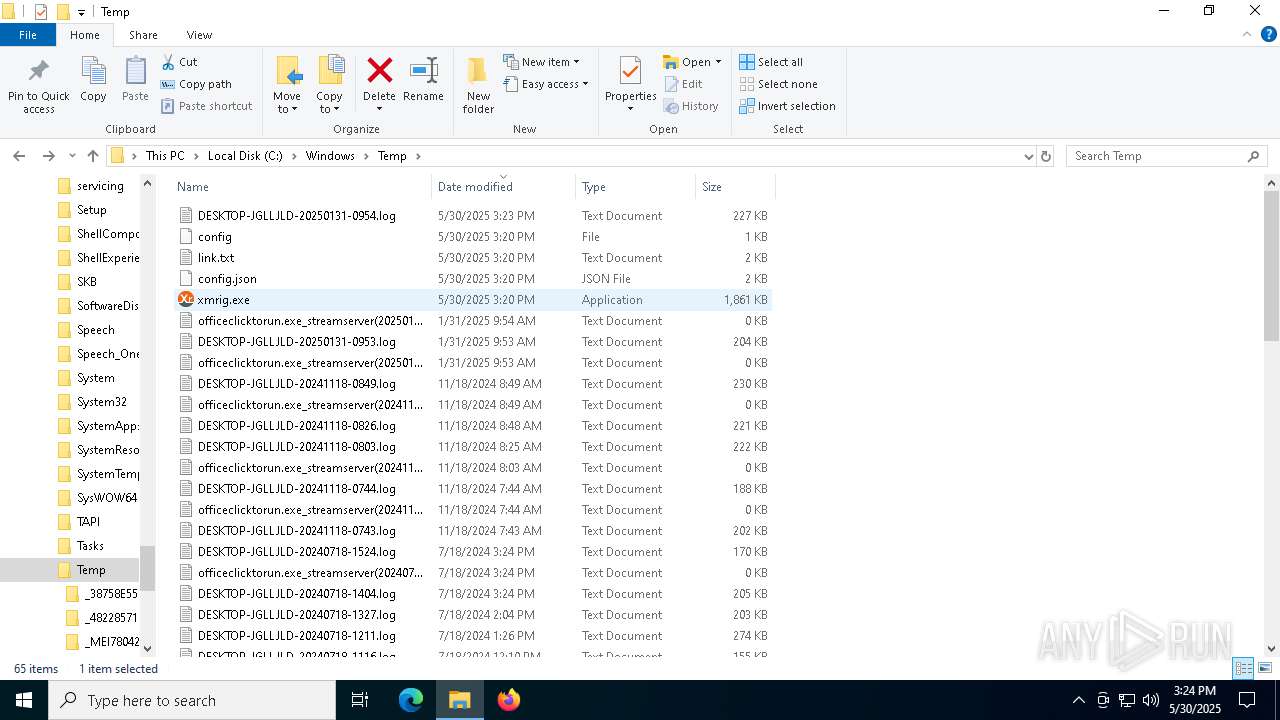
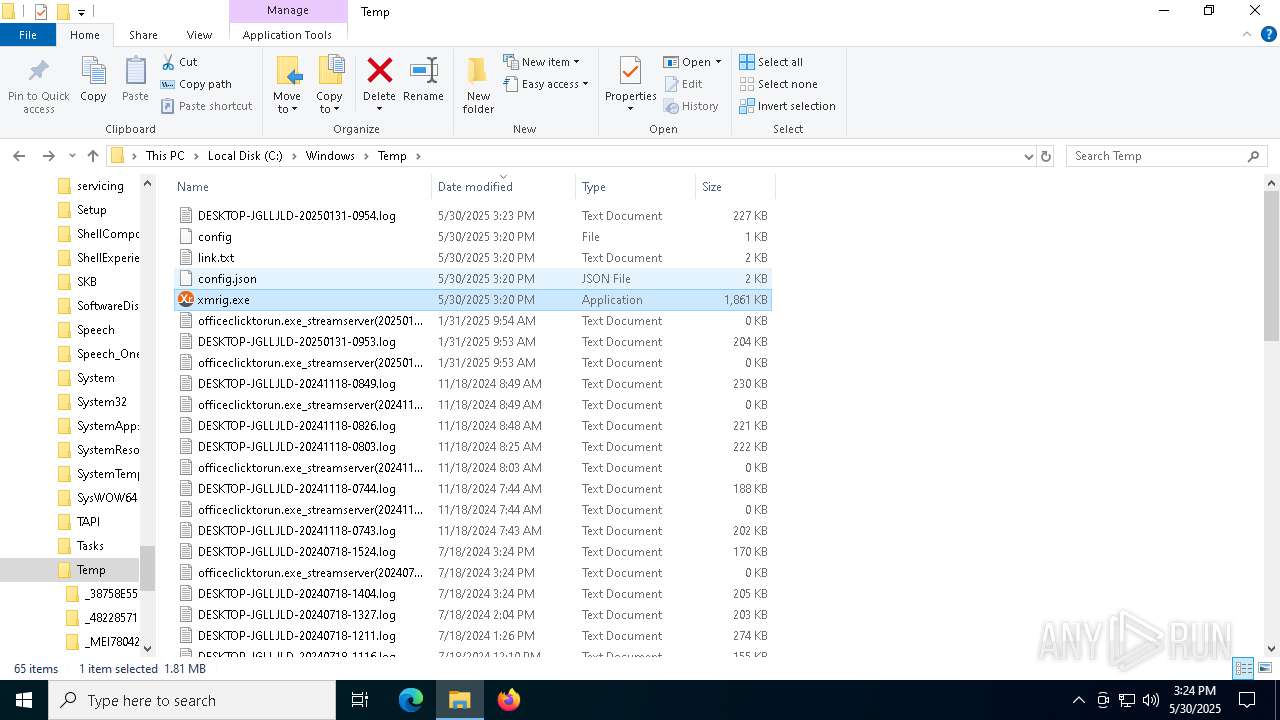
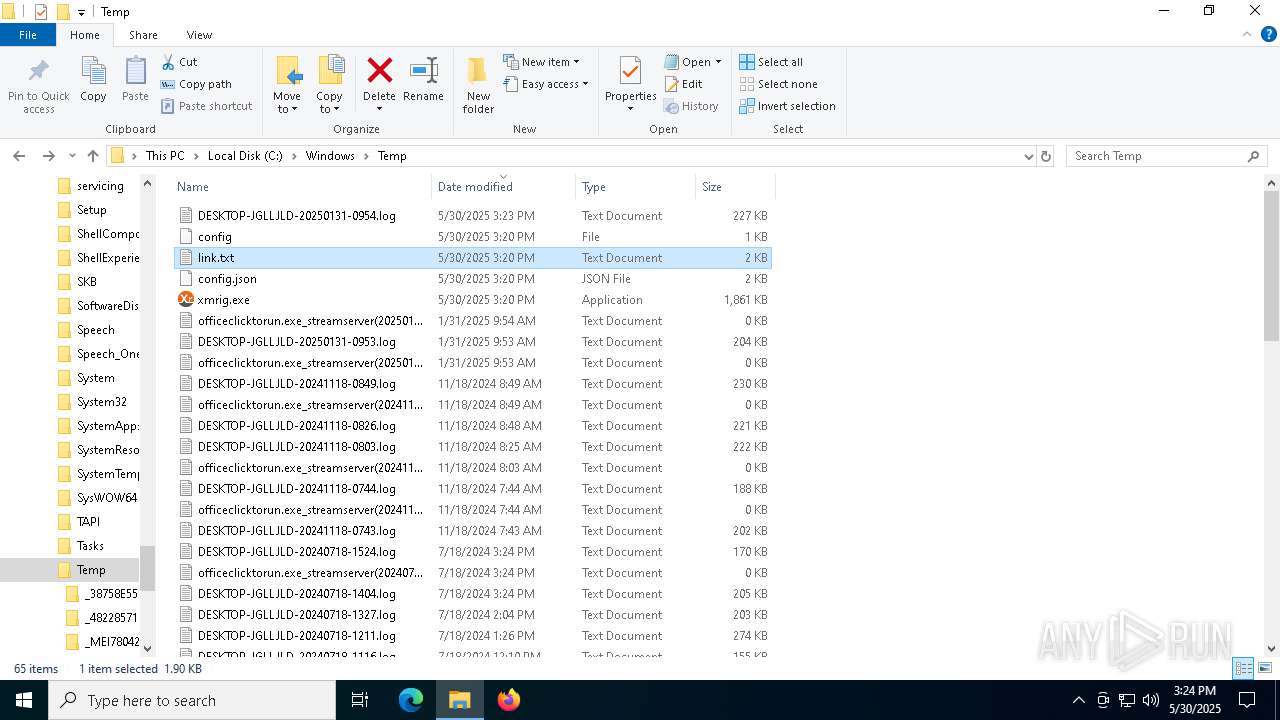
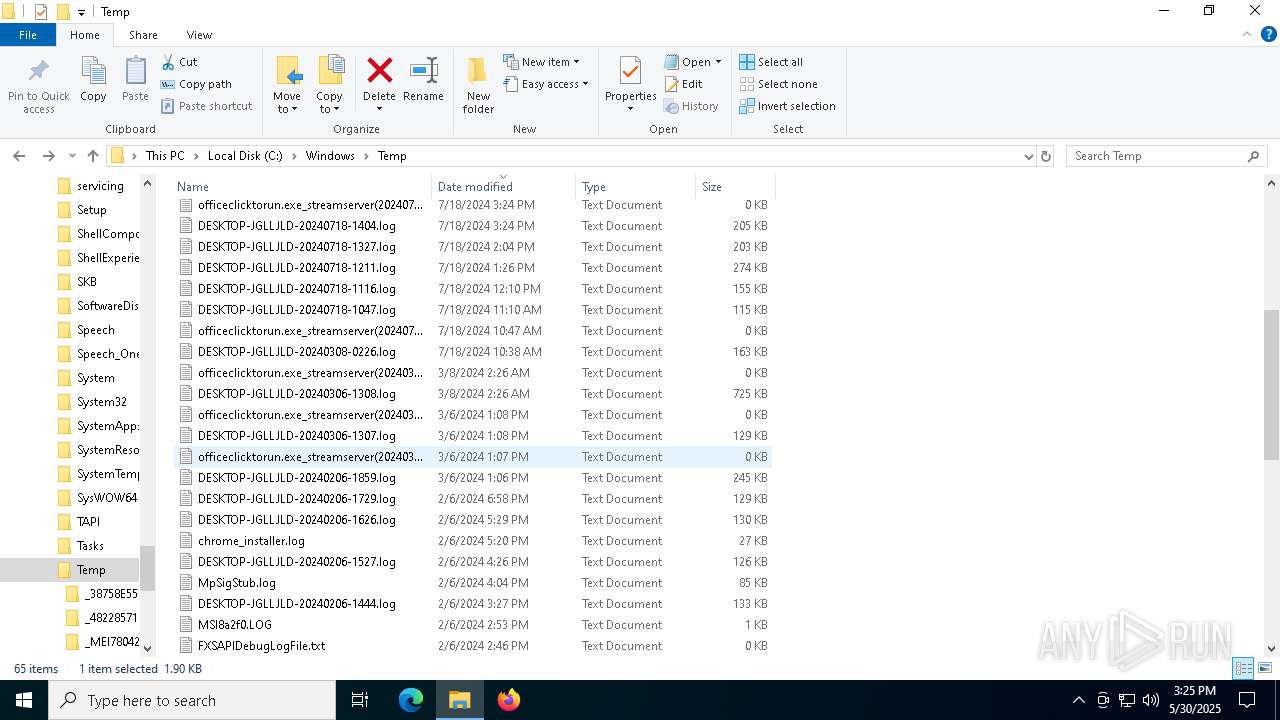
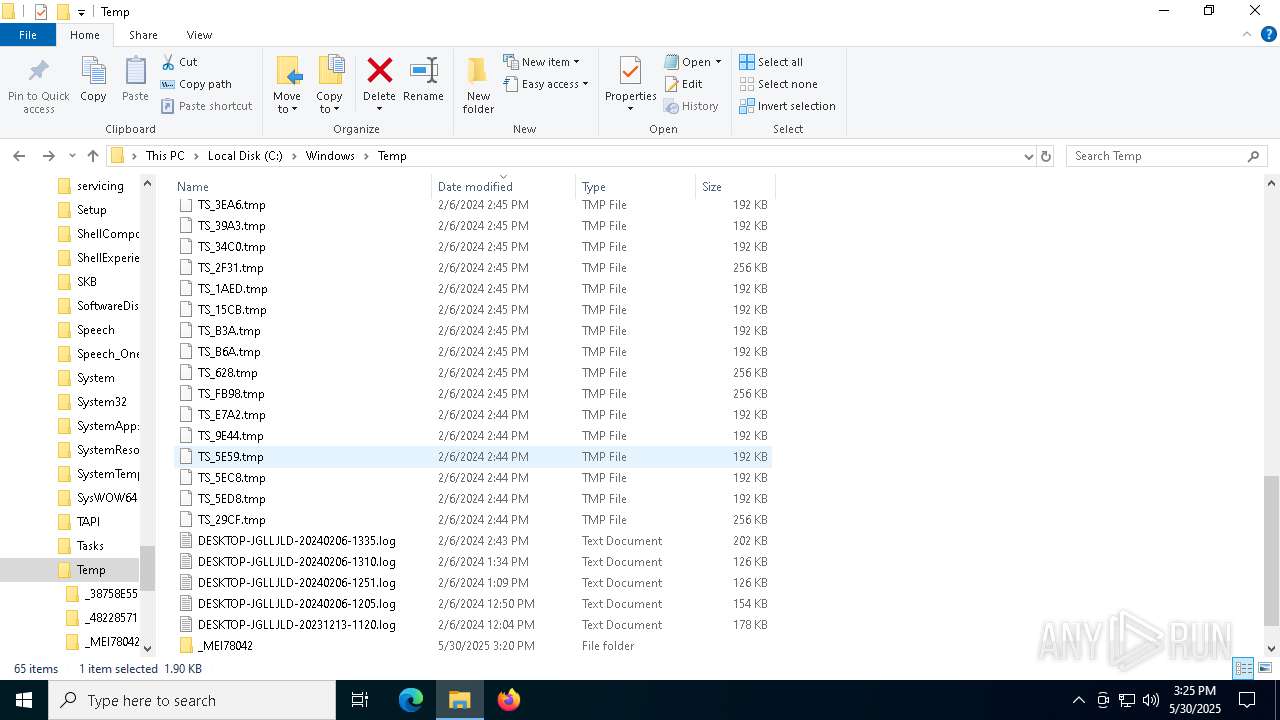
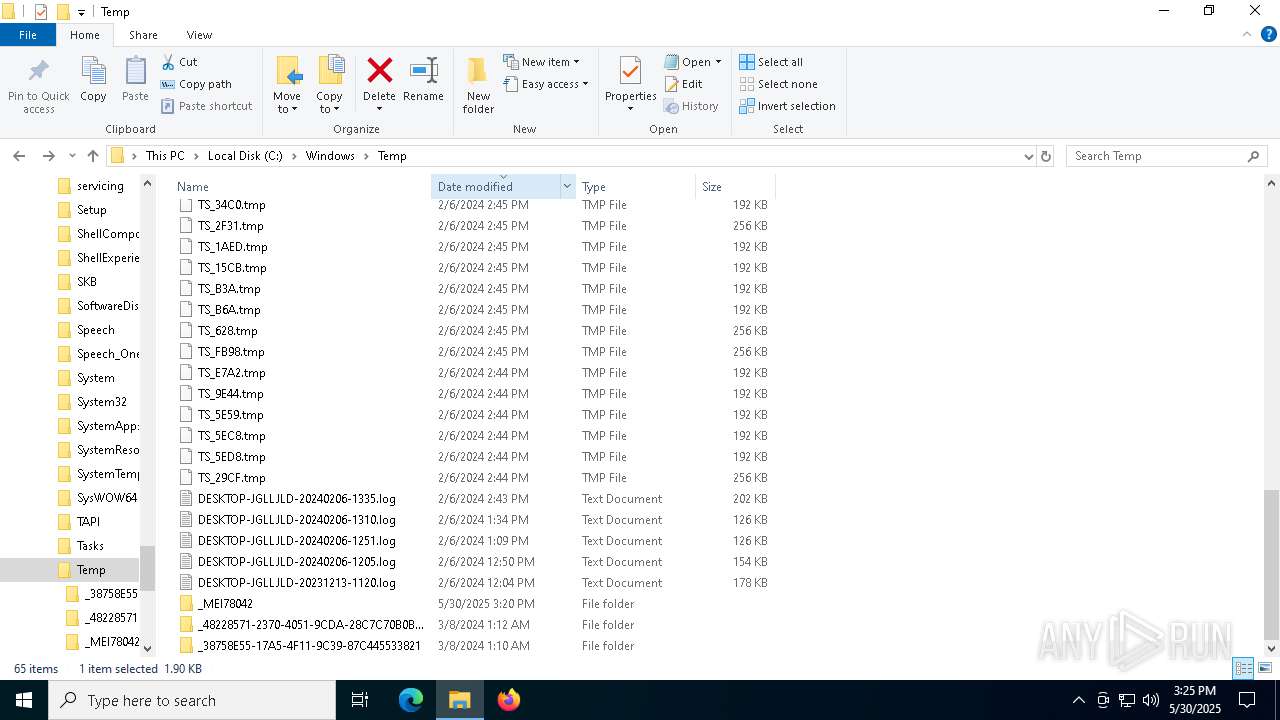
Create files in a temporary directory
- Photo.scr.exe (PID: 7876)
- Photo.scr.exe (PID: 6040)
- HelpPane.exe (PID: 7496)
- HelpPane.exe (PID: 6268)
Reads the computer name
- Photo.scr.exe (PID: 7820)
- Photo.scr.exe (PID: 7376)
- HelpPane.exe (PID: 7404)
- HelpPane.exe (PID: 7888)
- HelpPane.exe (PID: 1472)
- xmrig.exe (PID: 5864)
Reads the machine GUID from the registry
- Photo.scr.exe (PID: 7820)
- Photo.scr.exe (PID: 7376)
- HelpPane.exe (PID: 7888)
- HelpPane.exe (PID: 7404)
- HelpPane.exe (PID: 1472)
Process checks computer location settings
- Photo.scr.exe (PID: 7820)
PyInstaller has been detected (YARA)
- HelpPane.exe (PID: 7804)
- HelpPane.exe (PID: 1472)
Reads the software policy settings
- slui.exe (PID: 7448)
- slui.exe (PID: 7296)
UPX packer has been detected
- HelpPane.exe (PID: 1472)
- xmrig.exe (PID: 5864)
Checks proxy server information
- slui.exe (PID: 7296)
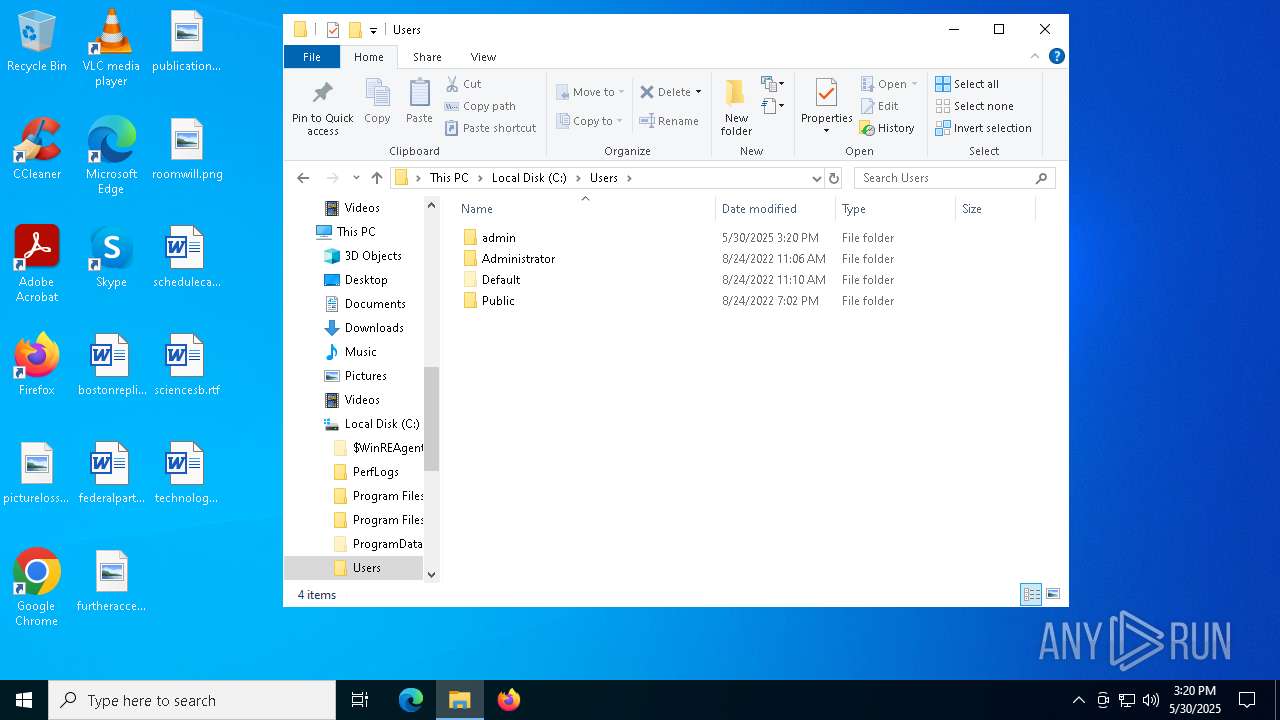
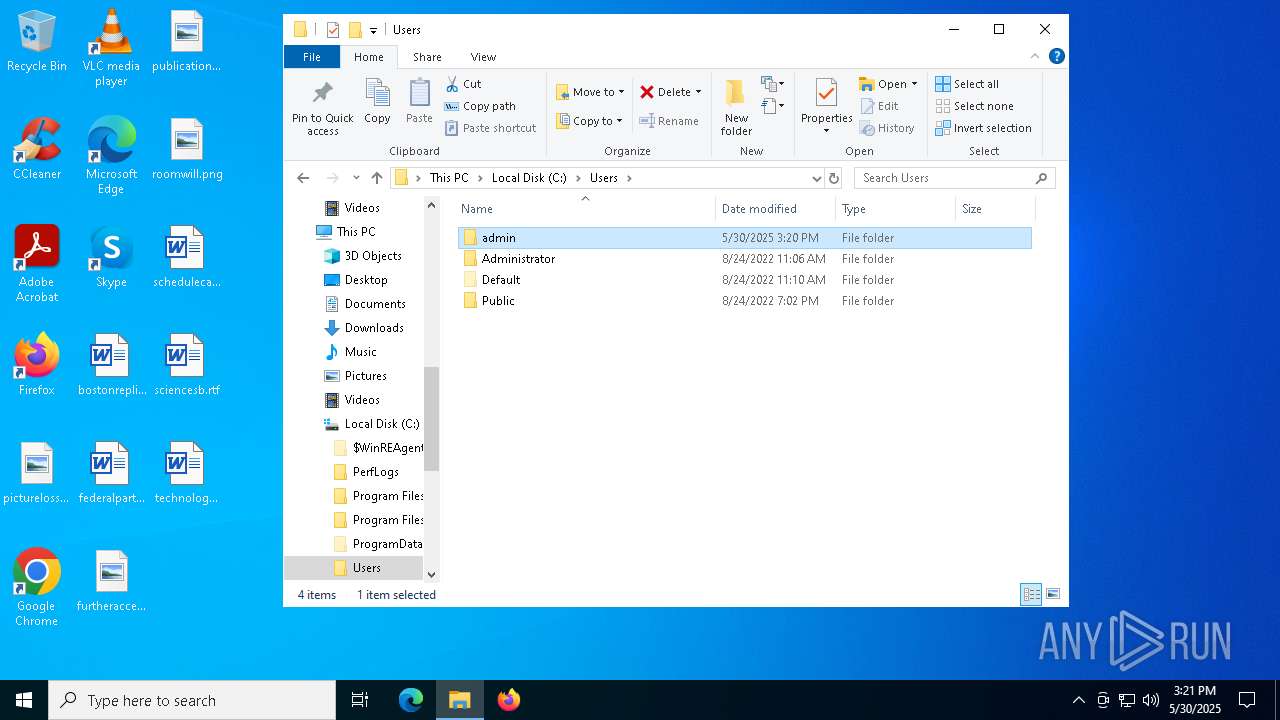
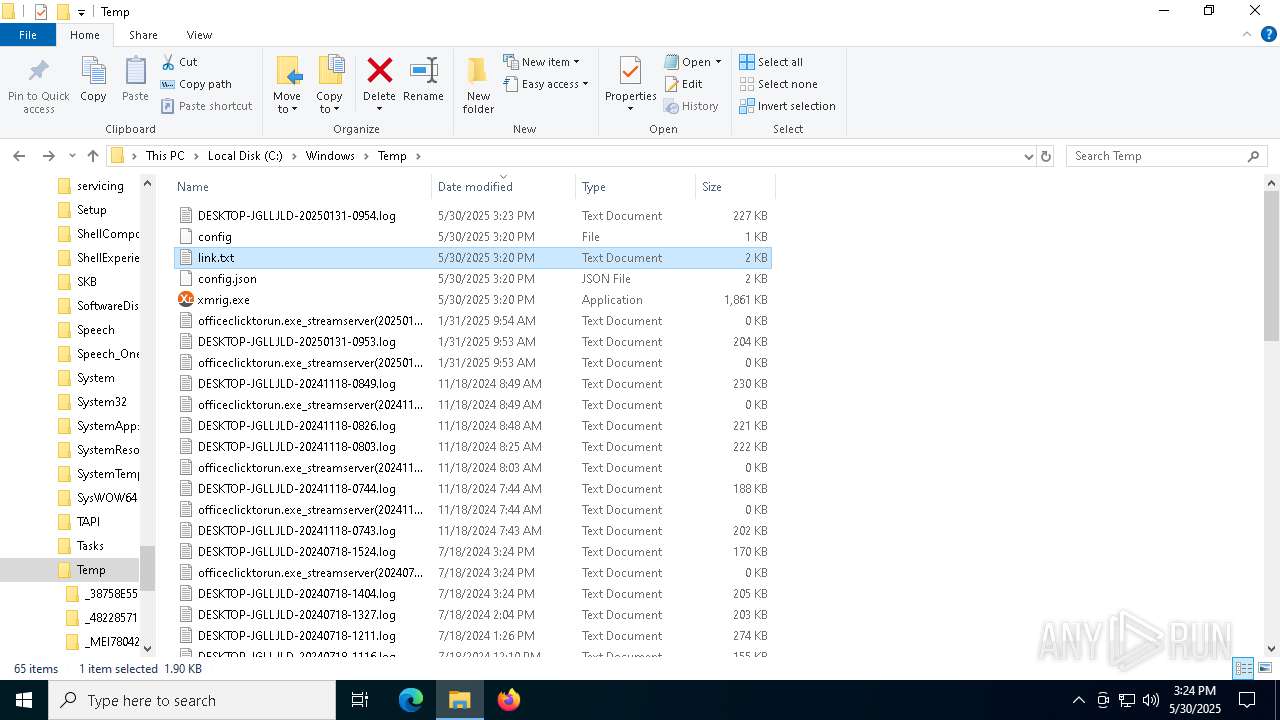
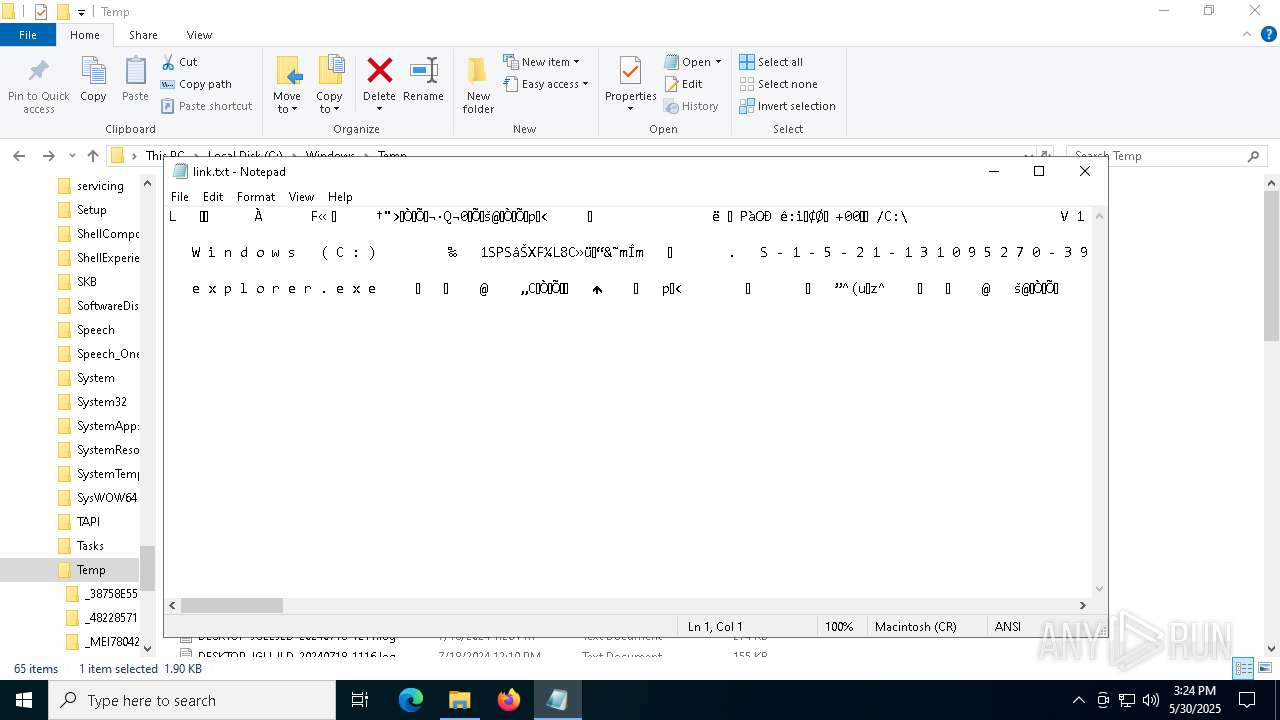
Manual execution by a user
- notepad.exe (PID: 5588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 14:43:33+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 125952 |
| InitializedDataSize: | 122368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x79d3 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
168
Monitored processes
35
Malicious processes
9
Suspicious processes
2
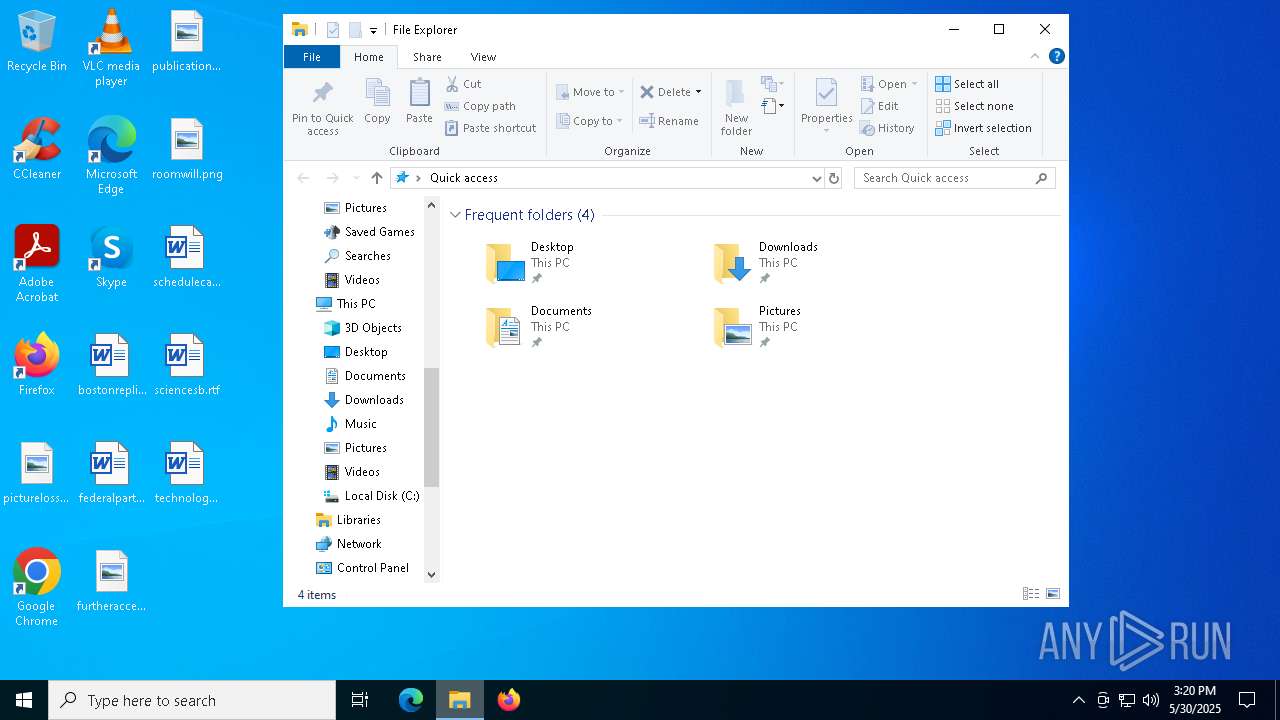
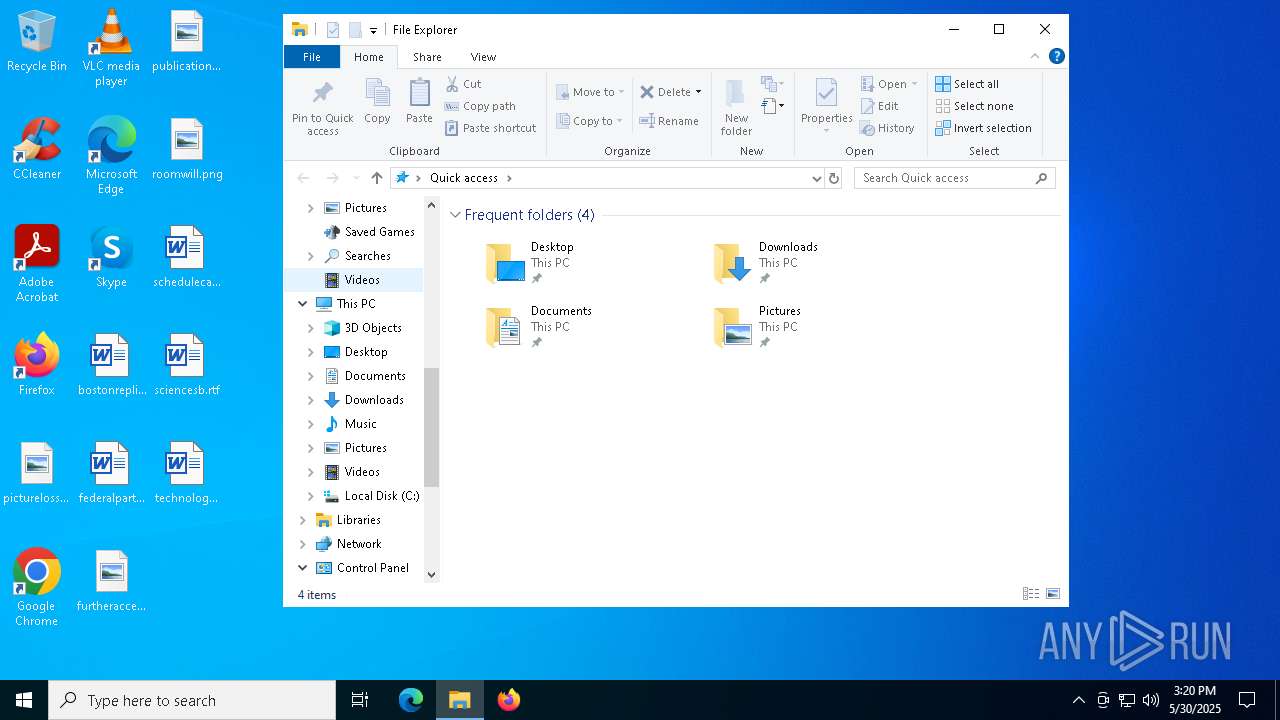
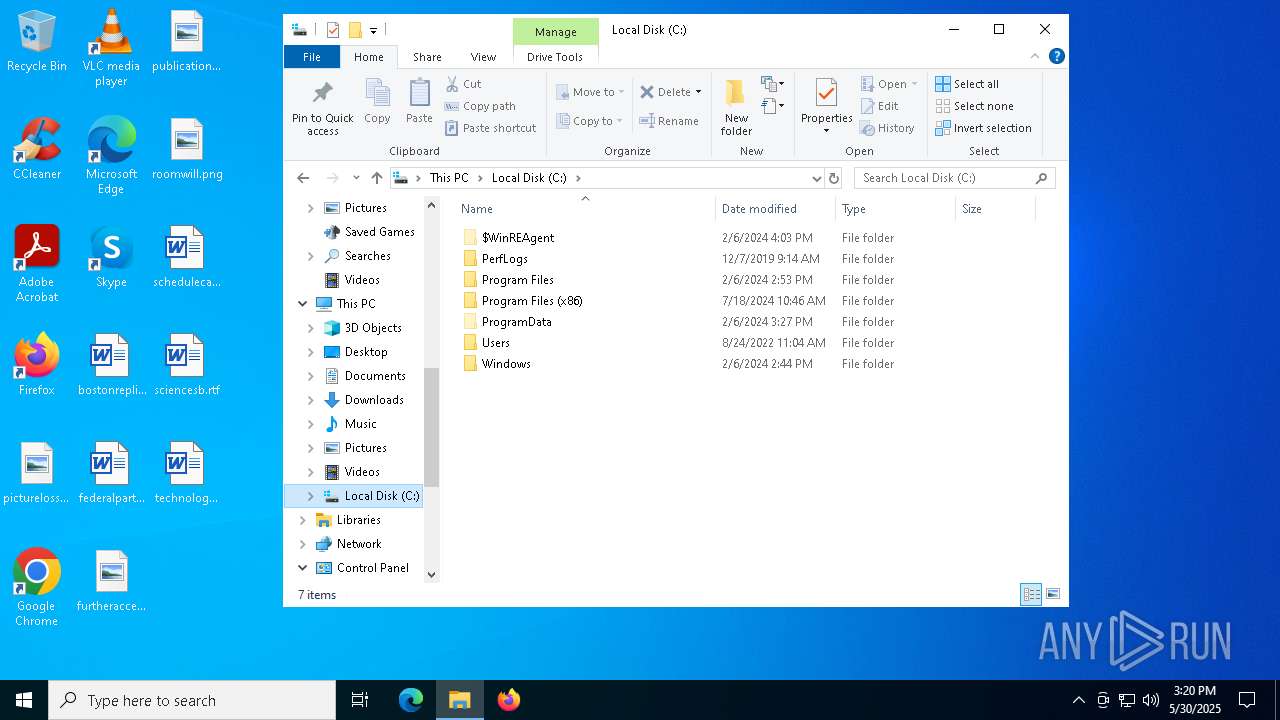
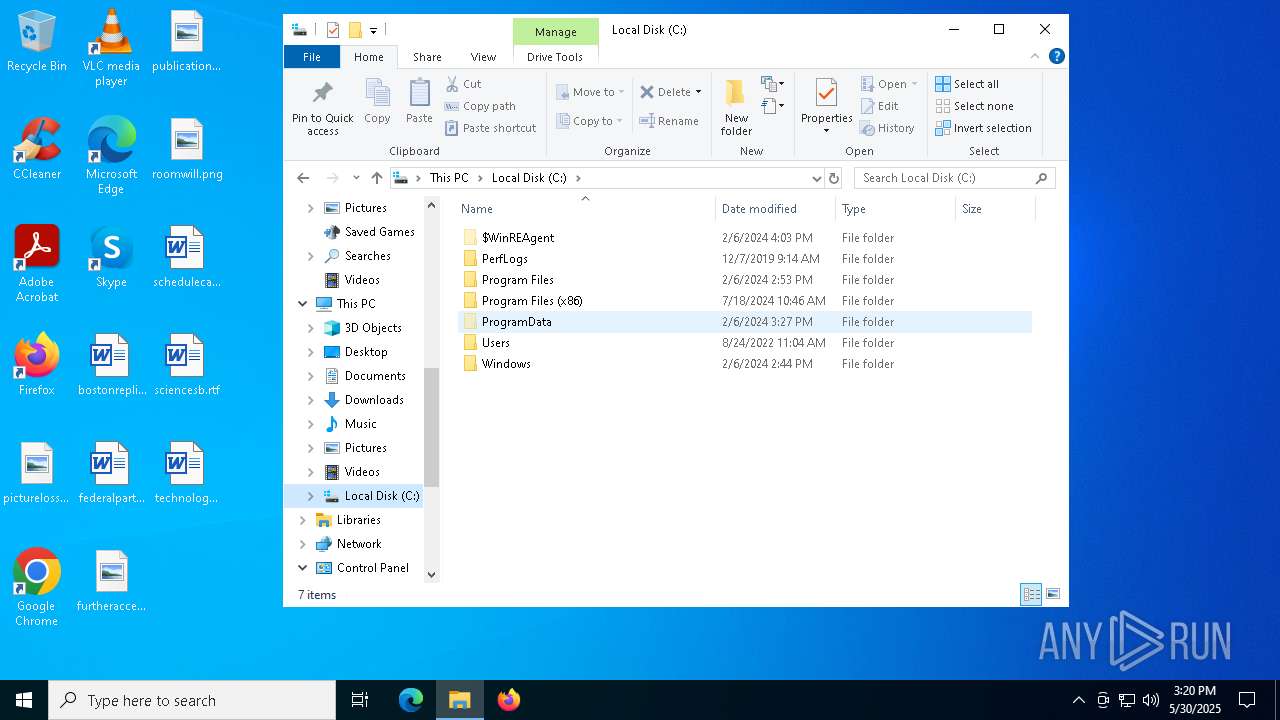
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | xmrig.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\WINDOWS\system32\cmd.exe /c taskkill /pid 2732 /f | C:\Windows\SysWOW64\cmd.exe | — | HelpPane.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\system32\cmd.exe /c C:\Users\admin\HelpPane.exe start | C:\Windows\SysWOW64\cmd.exe | — | Photo.scr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1472 | "C:\Users\admin\HelpPane.exe" | C:\Users\admin\HelpPane.exe | HelpPane.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Modules
| |||||||||||||||
| 1672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | C:\WINDOWS\system32\cmd.exe /c copy /y C:\WINDOWS\TEMP\_MEI78~1\\xmrig.exe C:\WINDOWS\TEMP\xmrig.exe | C:\Windows\SysWOW64\cmd.exe | HelpPane.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3268 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4200 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | C:\WINDOWS\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 284
Read events
5 204
Write events
80
Delete events
0
Modification events
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Print |
| Operation: | write | Name: | BeepEnabled |
Value: 0 | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Print\Printers |
| Operation: | write | Name: | DefaultSpoolDirectory |
Value: C:\Windows\system32\spool\PRINTERS | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Devices |
| Operation: | write | Name: | OneNote (Desktop) |
Value: winspool,nul: | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\PrinterPorts |
| Operation: | write | Name: | OneNote (Desktop) |
Value: winspool,nul:,15,45 | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Ports |
| Operation: | write | Name: | Ne00: |
Value: | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Devices |
| Operation: | write | Name: | Microsoft XPS Document Writer |
Value: winspool,Ne00: | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\PrinterPorts |
| Operation: | write | Name: | Microsoft XPS Document Writer |
Value: winspool,Ne00:,15,45 | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Ports |
| Operation: | write | Name: | Ne01: |
Value: | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Devices |
| Operation: | write | Name: | Microsoft Print to PDF |
Value: winspool,Ne01: | |||
| (PID) Process: | (4336) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\PrinterPorts |
| Operation: | write | Name: | Microsoft Print to PDF |
Value: winspool,Ne01:,15,45 | |||
Executable files
127
Suspicious files
6
Text files
26
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\_ctypes.pyd | executable | |
MD5:6CB8B560EFBC381651D2045F1571D7C8 | SHA256:6456FEA123E04BCEC8A8EED26160E1DF5482E69D187D3E1A0C428995472AC134 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\Crypto.Cipher._AES.pyd | executable | |
MD5:371397E80A55D432DA47311B8EF25317 | SHA256:C1A900615C9500C46B9602C30C53F299290B03632208EF1152AF8830AB73AD17 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\_socket.pyd | executable | |
MD5:BE47363992C7DD90019276D35FA8DA76 | SHA256:BE10254B111713BEF20A13D561DE61CA3C74A34C64DDC5B10825C64AB2C46734 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\msvcr90.dll | executable | |
MD5:199D34B03C7D0EB804A6D9869184B8D4 | SHA256:DF86421E354F817607F2BAFC9188569242FCF9DD564B28F3E2915C86A0BA1F54 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\servicemanager.pyd | executable | |
MD5:6A95BCF45E4BE23CC2634EF5BAD17660 | SHA256:60DA4B4E628B7DC1115615128AC554AEB29B50A61629AD5AEEB5CC9D2BD86202 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\netifaces.pyd | executable | |
MD5:C7807680A69196C3EE66C4CFB3E271AC | SHA256:1A6C57AC8031582477B1D3463A65B6EB006EEA704E27C8C4B812B99EA910428D | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\psutil._psutil_windows.pyd | executable | |
MD5:2FC800FCC46A597921C2ED447AEB09AC | SHA256:2E4AD3D08118DA77C928C4614BFECB34397CFAF53F5D46D7C7E5F1DA3172C1F1 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\ftpcrack.exe.manifest | xml | |
MD5:B5DEA49B86C5BB5D9CD8D64A09F70065 | SHA256:78B1160F6ADAB34D144AD19A0F4B83F83453F1E18460BBDFBE17AD354B62AF7D | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\pywintypes27.dll | executable | |
MD5:07B436BFA1C7B4FFC21FB39358158060 | SHA256:82C2926CB03A04392FA479801D505E2A387446BCA978FF930177121DB2FDB461 | |||
| 7876 | Photo.scr.exe | C:\Users\admin\AppData\Local\Temp\_MEI78762\_win32sysloader.pyd | executable | |
MD5:B4A567D80CCC08FB1C7FBB765847AFDA | SHA256:DBB0F9C499A710BBC8BCDE4ECC3577A6C9548262D6CE4434ED5A0708CBC787DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
379
DNS requests
79
Threats
180
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5408 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
7600 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6544 | svchost.exe | 20.190.160.4:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1472 | HelpPane.exe | 212.129.33.59:6881 | dht.transmissionbt.com | — | — | suspicious |
1472 | HelpPane.exe | 82.221.103.244:6881 | router.utorrent.com | — | — | whitelisted |
1472 | HelpPane.exe | 67.215.246.10:6881 | router.bittorrent.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
dht.transmissionbt.com |
| unknown |
router.bittorrent.com |
| whitelisted |
router.utorrent.com |
| whitelisted |
bttracker.debian.org |
| whitelisted |
xmr.crypto-pool.fr |
| unknown |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |
1472 | HelpPane.exe | Misc activity | INFO [ANY.RUN] FTP server is ready for the new user |