| File name: | DM2.2_Install.exe |
| Full analysis: | https://app.any.run/tasks/79f7cb48-3f1b-4c3c-af4f-bca602cd2da4 |
| Verdict: | Malicious activity |
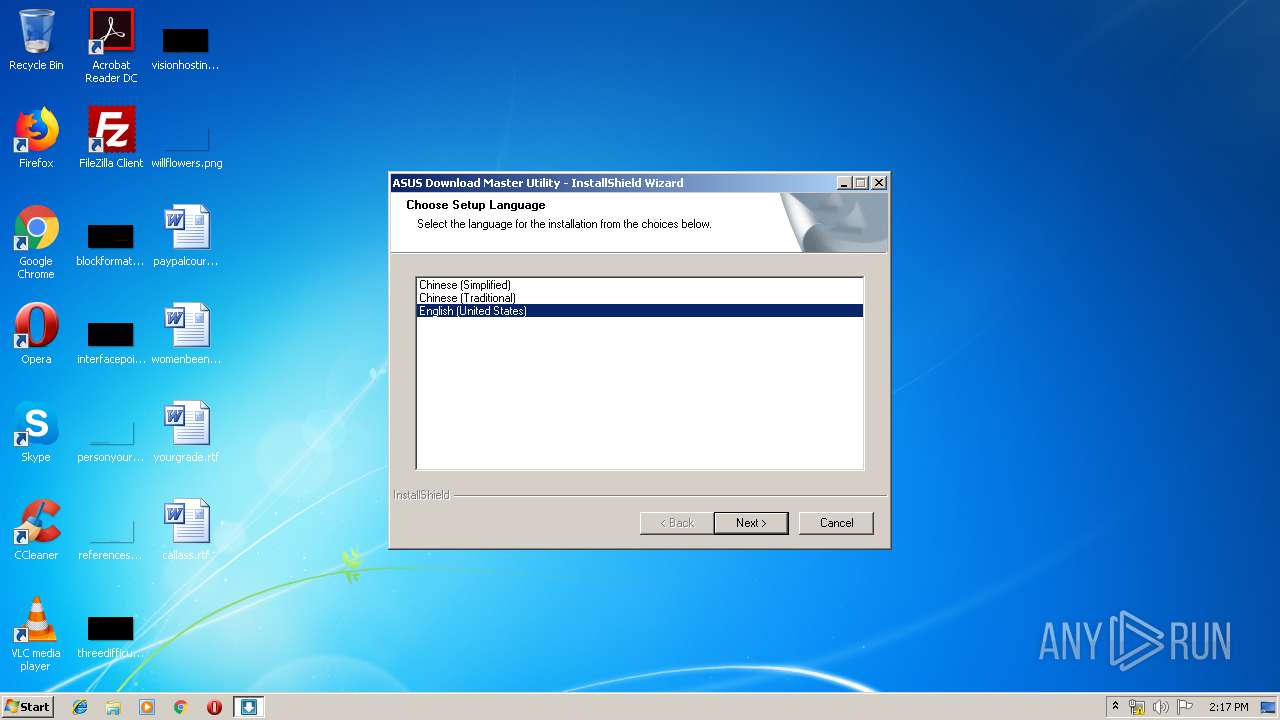
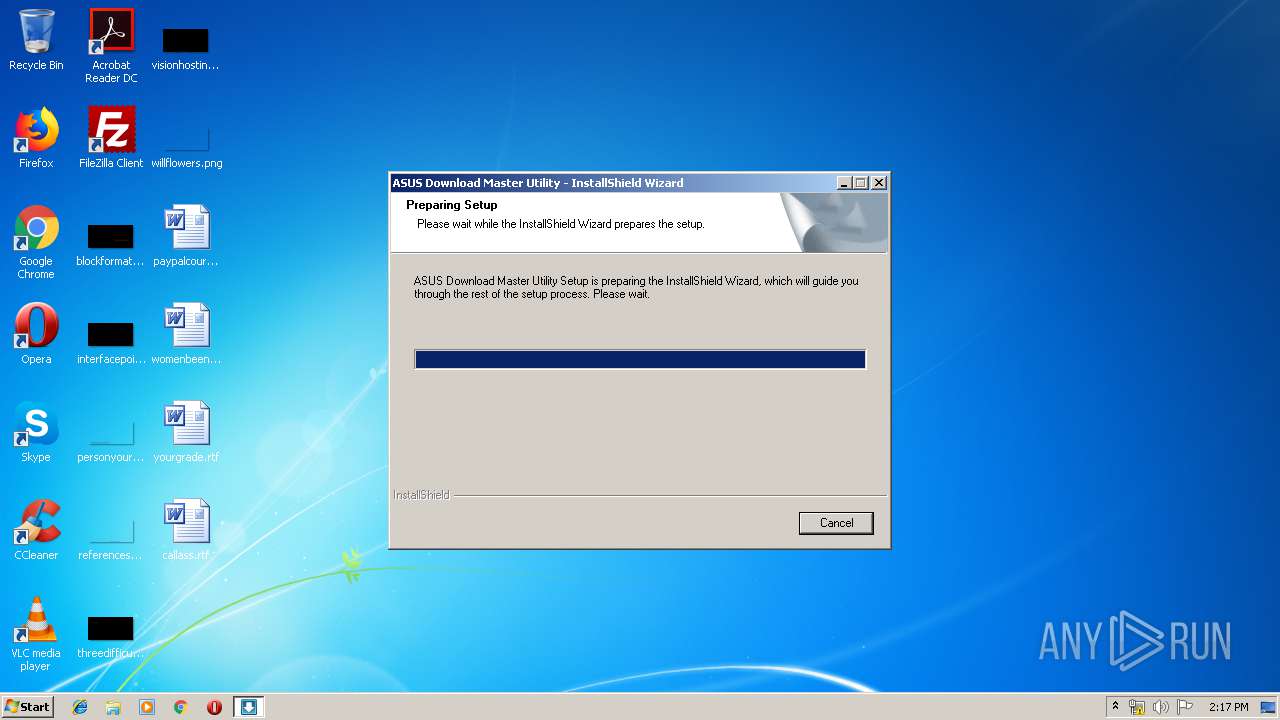
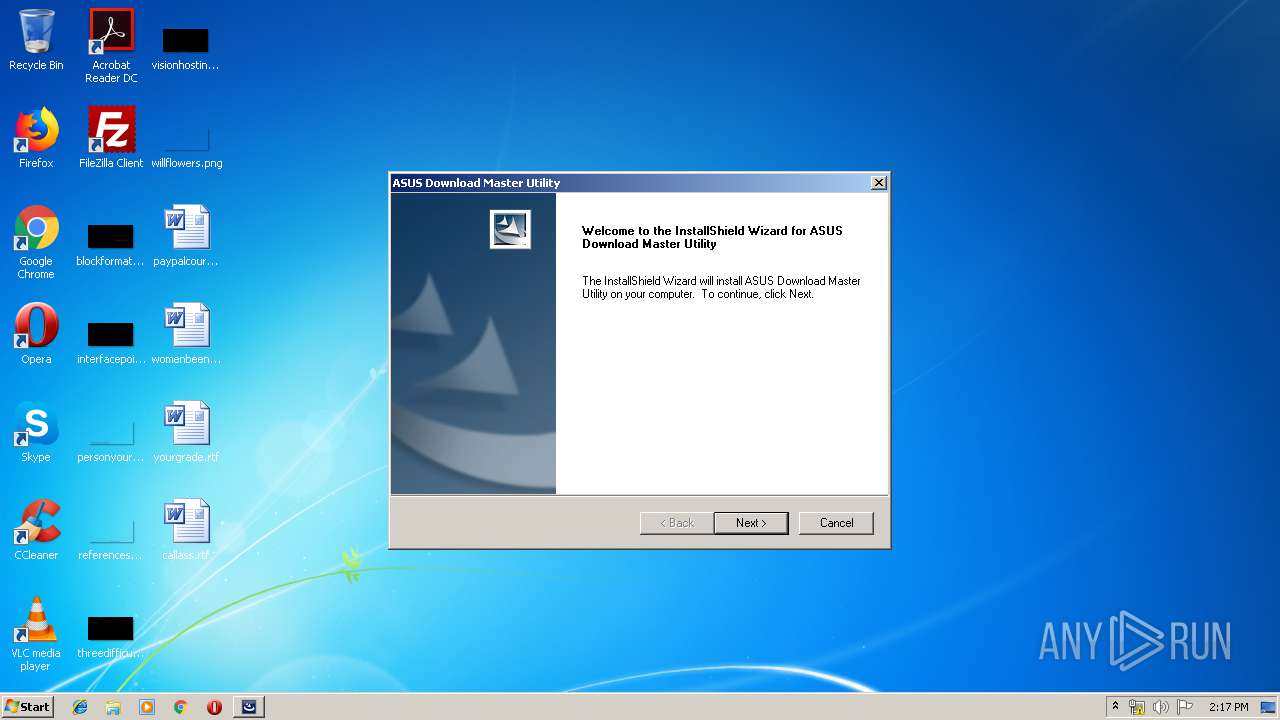
| Analysis date: | May 17, 2019, 13:17:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 33149B8B44E63FDE84FC068E74FA9922 |
| SHA1: | A5C7479617062DA5E43194EFB19A67B215C3992D |
| SHA256: | 9193334B1BFD3A6543693F222F9907E9131B39D7E080FFA8FC9F7BF704478CDF |
| SSDEEP: | 196608:Yqtp+S9KQyIYI4/quWW6NILzgK0DvA6K4bVi+ox5:lp+S9K/suWW600fDvA6PQr |
MALICIOUS
Loads dropped or rewritten executable
- DM2.2_Install.exe (PID: 3544)
- DM2.2.exe (PID: 1840)
Application was dropped or rewritten from another process
- asusfwctrl.exe (PID: 3904)
- DM2.2.exe (PID: 1840)
SUSPICIOUS
Searches for installed software
- DM2.2_Install.exe (PID: 3544)
Creates a software uninstall entry
- DM2.2_Install.exe (PID: 3544)
Modifies the open verb of a shell class
- DM2.2_Install.exe (PID: 3544)
Executable content was dropped or overwritten
- DM2.2_Install.exe (PID: 3544)
Creates files in the program directory
- DM2.2_Install.exe (PID: 3544)
INFO
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3676)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3420)
Changes settings of System certificates
- DrvInst.exe (PID: 3676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (37.6) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (v2.x) (11) |
| .exe | | | InstallShield setup (8) |
| .exe | | | Win32 EXE PECompact compressed (generic) (7.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:09:22 05:59:51+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 416256 |
| InitializedDataSize: | 397824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3d484 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 16.0.0.400 |
| ProductVersionNumber: | 16.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Acresso Software Inc. |
| FileDescription: | InstallScript Setup Launcher |
| FileVersion: | 16.0.400 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (C) 2009 Acresso Software Inc. and/or InstallShield Co. Inc. All Rights Reserved. |
| OriginalFileName: | Setup.exe |
| ProductName: | InstallShield |
| ProductVersion: | 16.0 |
| InternalBuildNumber: | 92881 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Sep-2009 03:59:51 |
| Detected languages: |
|
| CompanyName: | Acresso Software Inc. |
| FileDescription: | InstallScript Setup Launcher |
| FileVersion: | 16.0.400 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (C) 2009 Acresso Software Inc. and/or InstallShield Co. Inc. All Rights Reserved. |
| OriginalFilename: | Setup.exe |
| ProductName: | InstallShield |
| ProductVersion: | 16.0 |
| Internal Build Number: | 92881 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Sep-2009 03:59:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00065833 | 0x00065A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60063 |
.rdata | 0x00067000 | 0x0000E176 | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43761 |
.data | 0x00076000 | 0x000092B4 | 0x00007800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.49489 |
.rsrc | 0x00080000 | 0x0004B700 | 0x0004B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.45476 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1867 | 1147 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.45744 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.43398 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.14965 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.18448 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.85842 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.57777 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.81004 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 6.06596 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.22977 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
LZ32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
Total processes
43
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
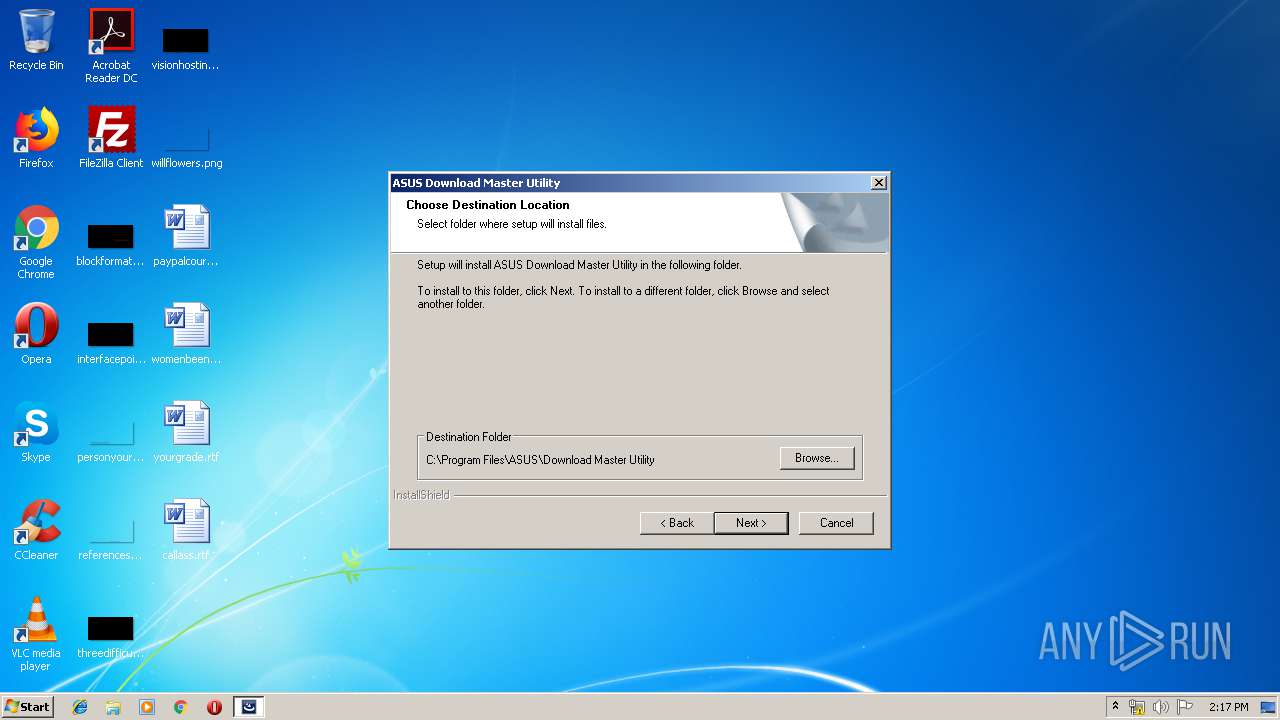
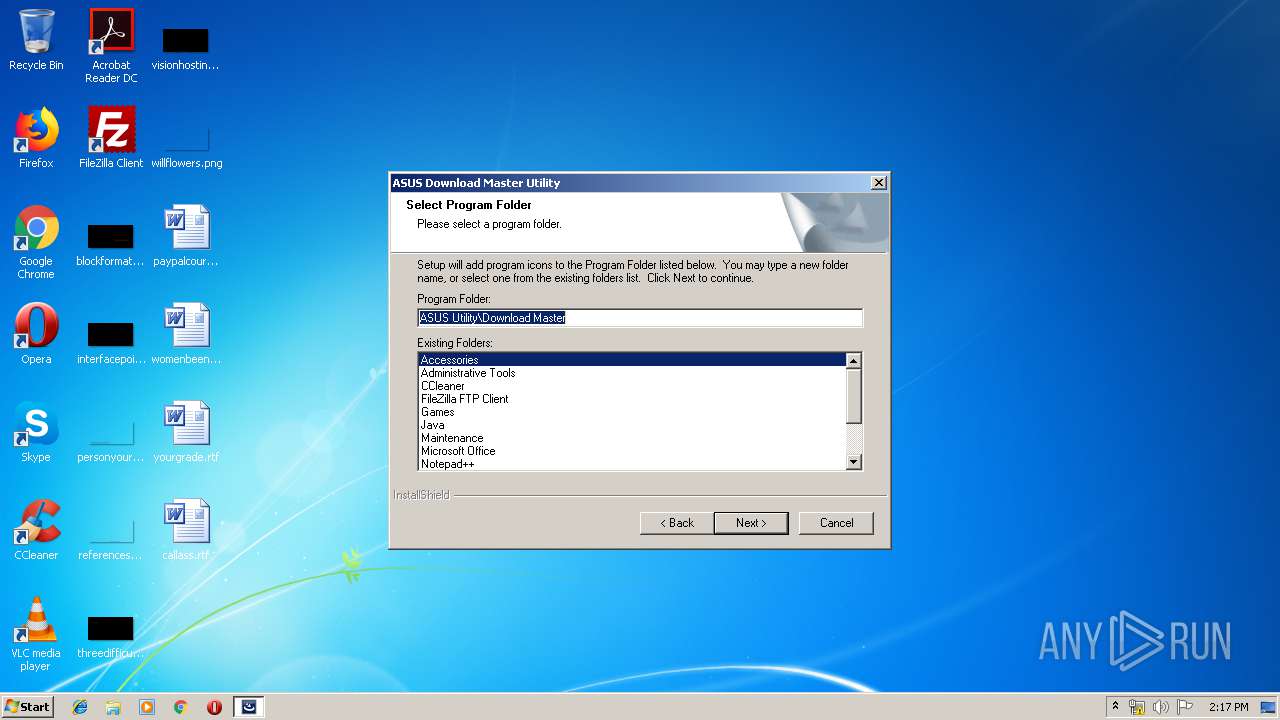
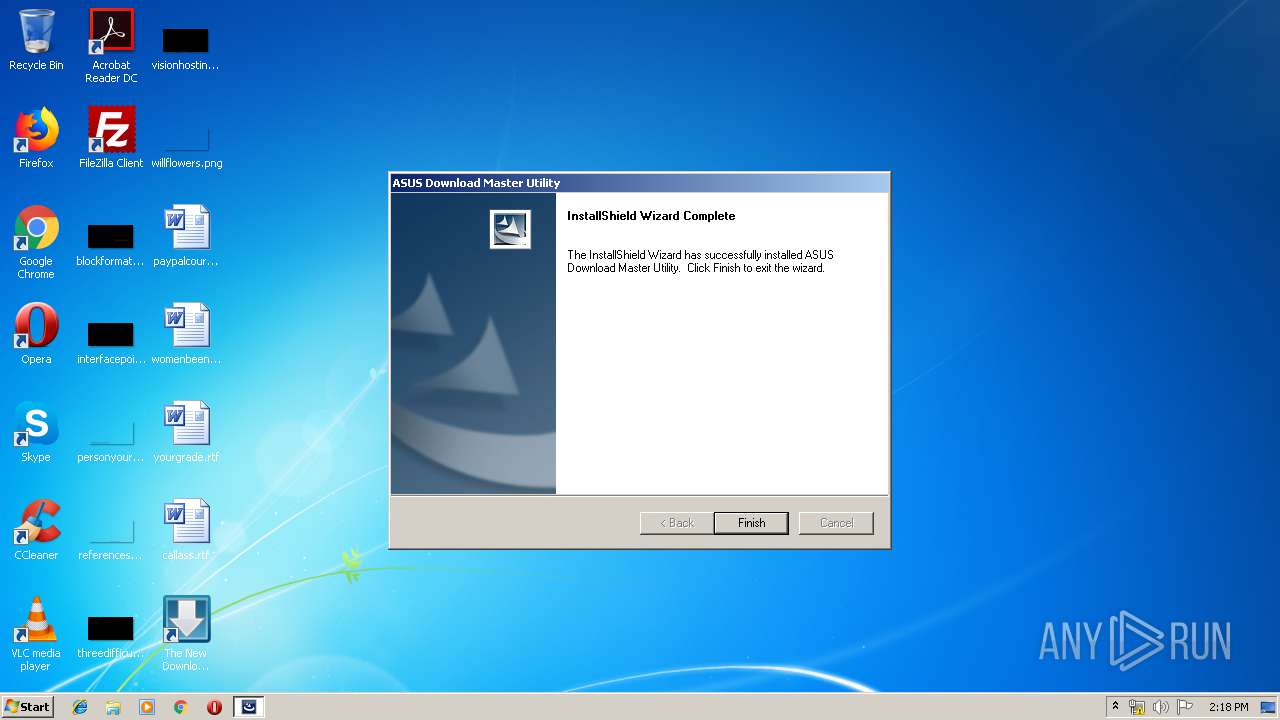
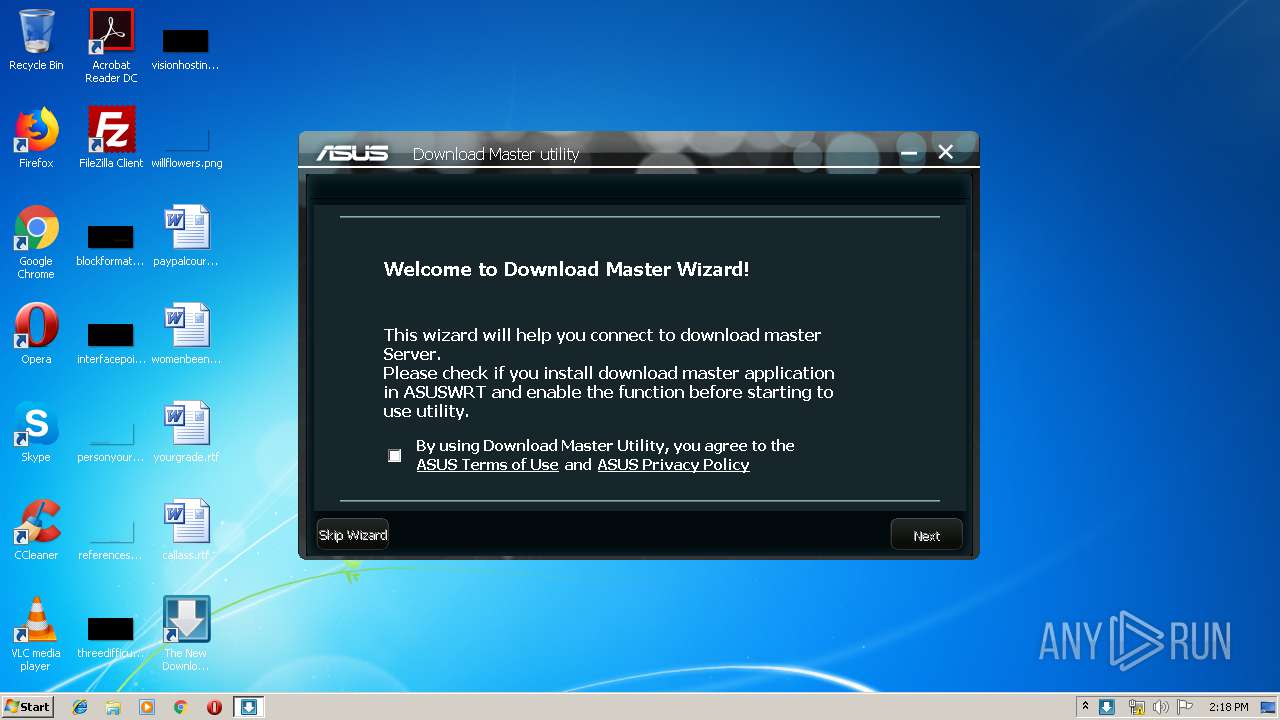
| 1840 | "C:\Program Files\ASUS\Download Master Utility\DM2.2.exe" | C:\Program Files\ASUS\Download Master Utility\DM2.2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.2.3.2 Modules
| |||||||||||||||
| 3060 | "C:\Users\admin\AppData\Local\Temp\DM2.2_Install.exe" | C:\Users\admin\AppData\Local\Temp\DM2.2_Install.exe | — | explorer.exe | |||||||||||
User: admin Company: Acresso Software Inc. Integrity Level: MEDIUM Description: InstallScript Setup Launcher Exit code: 3221226540 Version: 16.0.400 Modules
| |||||||||||||||
| 3420 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
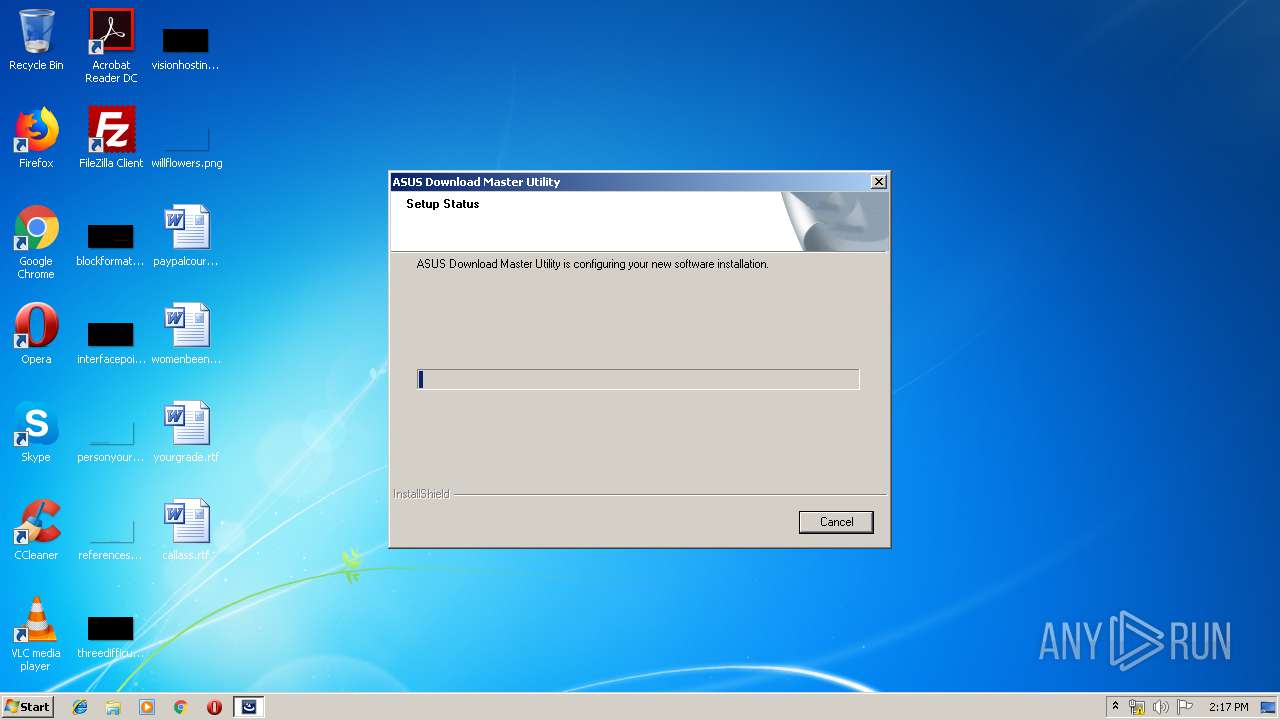
| 3544 | "C:\Users\admin\AppData\Local\Temp\DM2.2_Install.exe" | C:\Users\admin\AppData\Local\Temp\DM2.2_Install.exe | explorer.exe | ||||||||||||
User: admin Company: Acresso Software Inc. Integrity Level: HIGH Description: InstallScript Setup Launcher Exit code: 0 Version: 16.0.400 Modules
| |||||||||||||||
| 3676 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000003C4" "00000560" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | "C:\Program Files\ASUS\Download Master Utility\asusfwctrl.exe" "C:\Program Files\ASUS\Download Master Utility\DM2.2.exe" "ASUS Download Master 2 Application" | C:\Program Files\ASUS\Download Master Utility\asusfwctrl.exe | DM2.2_Install.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
498
Read events
285
Write events
213
Delete events
0
Modification events
| (PID) Process: | (3544) DM2.2_Install.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 400000000000000028231CE9B20CD501D80D0000140E0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3544) DM2.2_Install.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 400000000000000028231CE9B20CD501D80D0000140E0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3544) DM2.2_Install.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (3544) DM2.2_Install.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000FA6C87E9B20CD501D80D0000140E0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3544) DM2.2_Install.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000AE318CE9B20CD501D80D000094070000E80300000100000000000000000000003CAFFBC9BCE7CB4898447FDE8FA2581C0000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D8A6A1E9B20CD5015C0D0000D00A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D8A6A1E9B20CD5015C0D000070090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D8A6A1E9B20CD5015C0D00006C0F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D8A6A1E9B20CD5015C0D0000E40D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3420) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 40000000000000005C7EB9E9B20CD5015C0D00006C0F0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
19
Suspicious files
16
Text files
136
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\{8722B86D-2664-4C75-B307-892C3855F54C}\setu193d.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\{8722B86D-2664-4C75-B307-892C3855F54C}\Font193d.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\{8722B86D-2664-4C75-B307-892C3855F54C}\DIFx194d.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\core194d.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\dotn194d.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\{8722B86D-2664-4C75-B307-892C3855F54C}\Stri195c.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{5A029415-D905-487C-B0F6-F67A0A3821DF}\Disk1\setup.inx | binary | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\{8722B86D-2664-4C75-B307-892C3855F54C}\isrt195c.rra | — | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{5A029415-D905-487C-B0F6-F67A0A3821DF}\setup.ini | text | |
MD5:— | SHA256:— | |||
| 3544 | DM2.2_Install.exe | C:\Users\admin\AppData\Local\Temp\{3194358D-BEC3-46CA-A21B-6DFA664AE3C7}\{8722B86D-2664-4C75-B307-892C3855F54C}\defa195c.rra | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
asusfwctrl.exe | Ths OS is WIN_7 |
asusfwctrl.exe | MpsSvc is runing! |
asusfwctrl.exe | Call AddAppInWinFWExcepList_ADV |
asusfwctrl.exe | C:\Program Files\ASUS\Download Master Utility\DM2.2.exe |
asusfwctrl.exe | ASUS Download Master 2 Application |
asusfwctrl.exe | The rule group is not exist, will add now... |
asusfwctrl.exe | The rule group is added now. |
asusfwctrl.exe | C:\Program Files\ASUS\Download M |
asusfwctrl.exe | C:\Program Files\ASUS\Download Master Utility\DM2.2.exe |
asusfwctrl.exe | ASUS Download Master 2 Application |