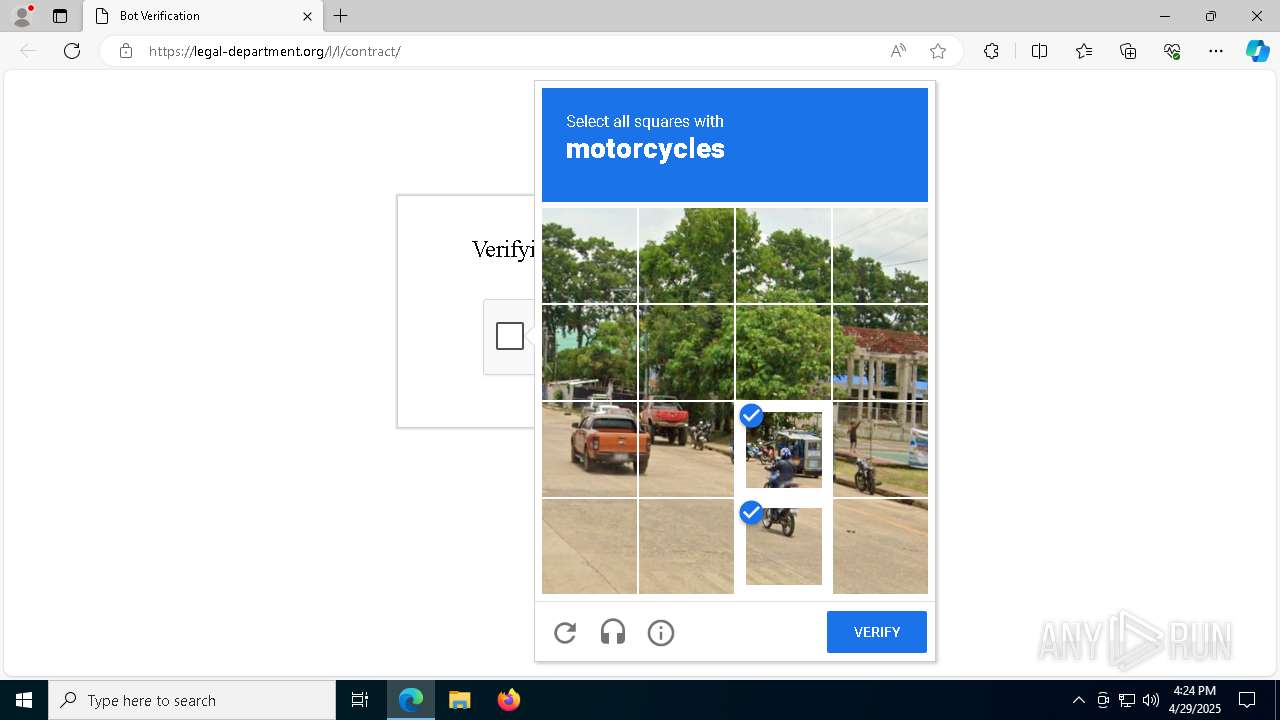
| URL: | https://click.pstmrk.it/3s/jhgjgh.short.gy%2F6FXcYh/6TPw/NwG9AQ/AQ/4a73f0b5-caed-4e14-9037-775368bb1516/1/_dzebH2eX_ |
| Full analysis: | https://app.any.run/tasks/8ac71592-b10f-4627-b617-ab841ac7f69c |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 16:24:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1F50E01D10E0DC5AE1996EB833B7F246 |
| SHA1: | D268A5A441DAEFC9F91DA7F87F6D5BF8AC00936B |
| SHA256: | 919068C7A536651E493D9ABA16C5FBC29FD4D469D843CF229FA5AAE110137BFC |
| SSDEEP: | 3:N8UEVN3WDgfy7HMG/90eAkImUPIGEH0BhIlX:2UEVNM8UHMW90DkITInX |
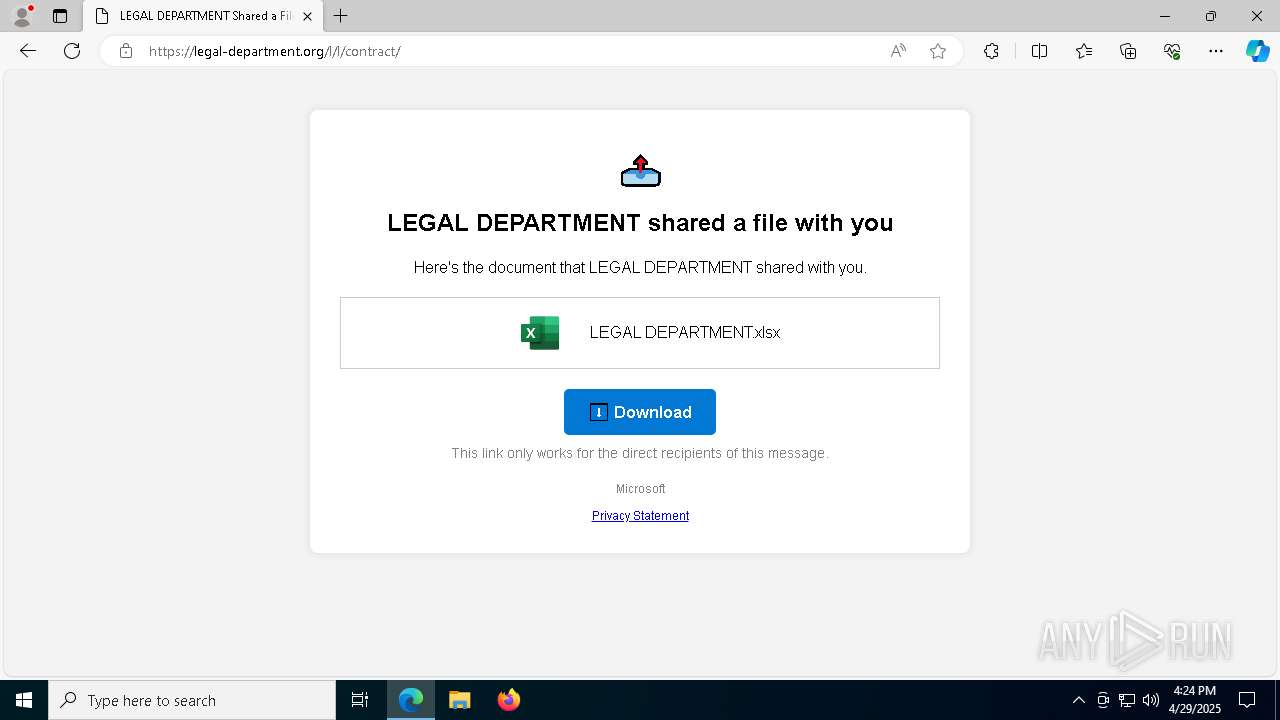
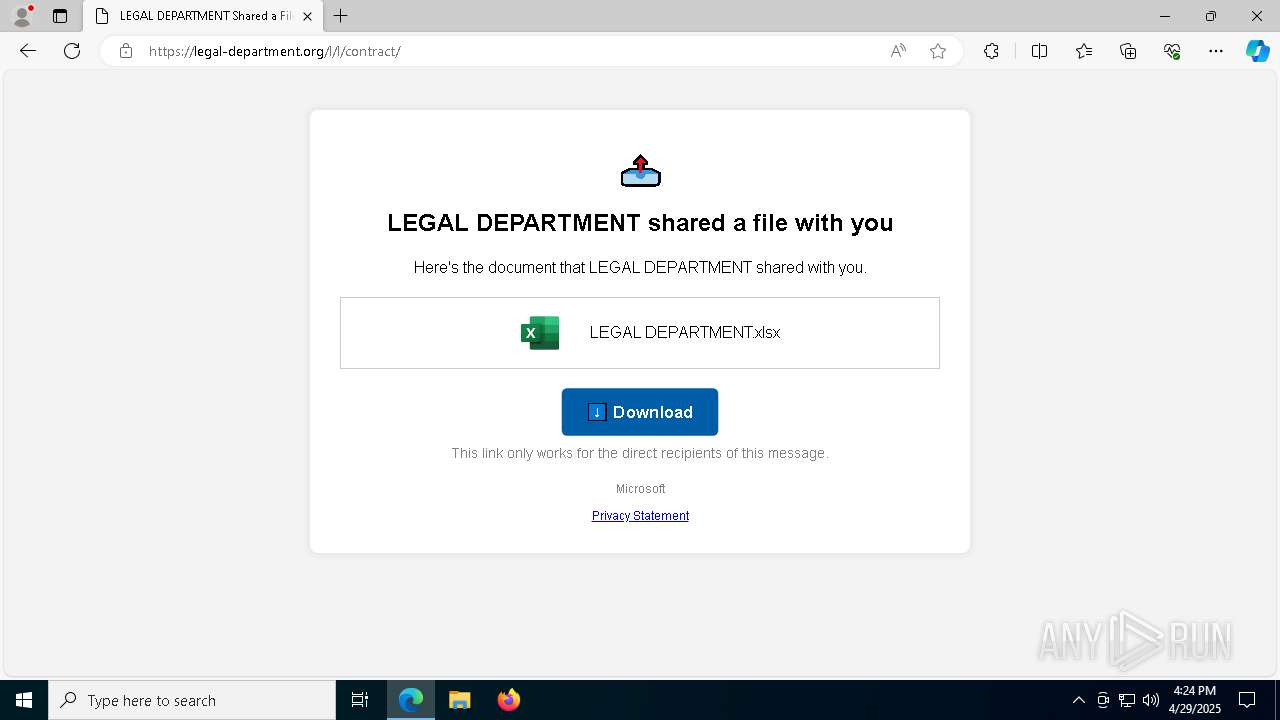
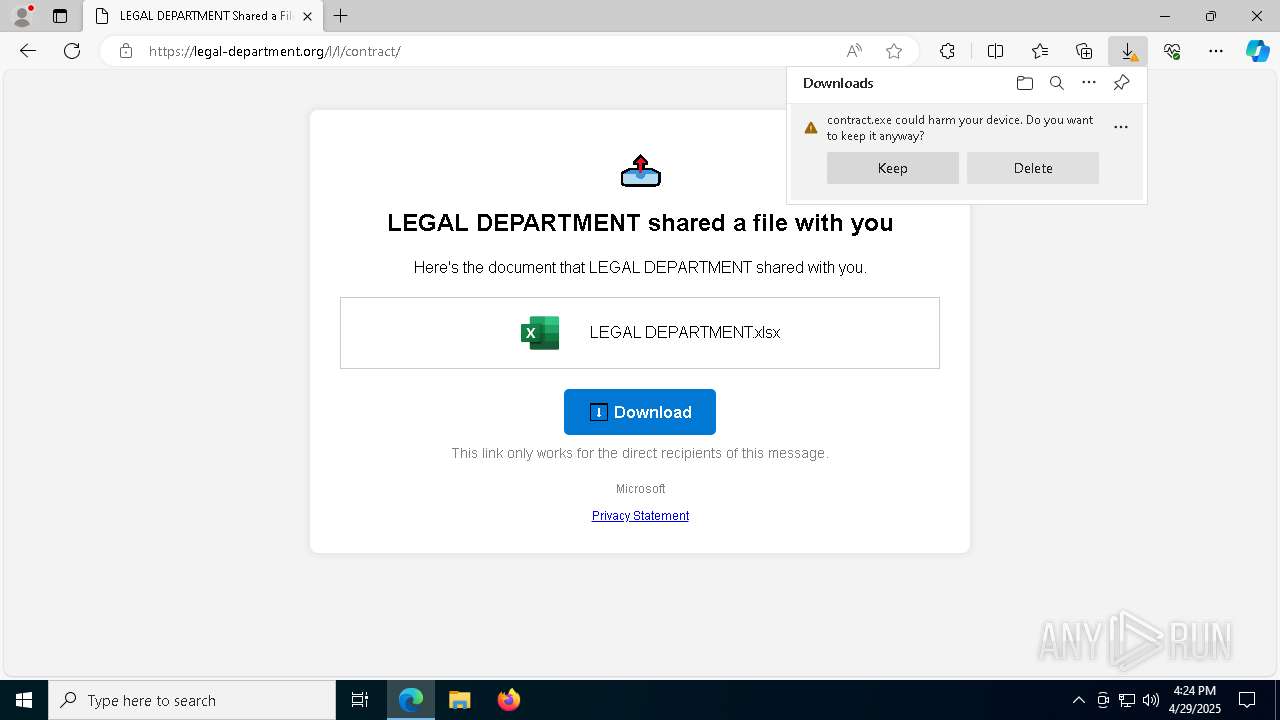
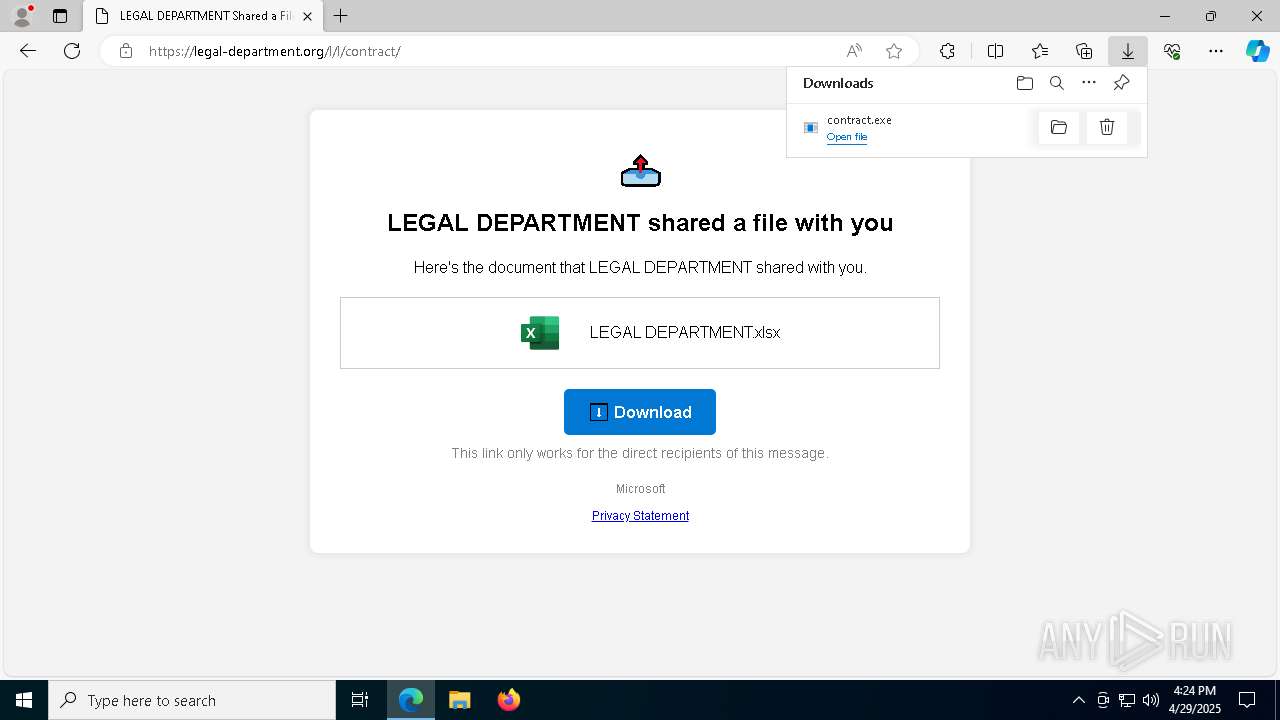
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 3024)
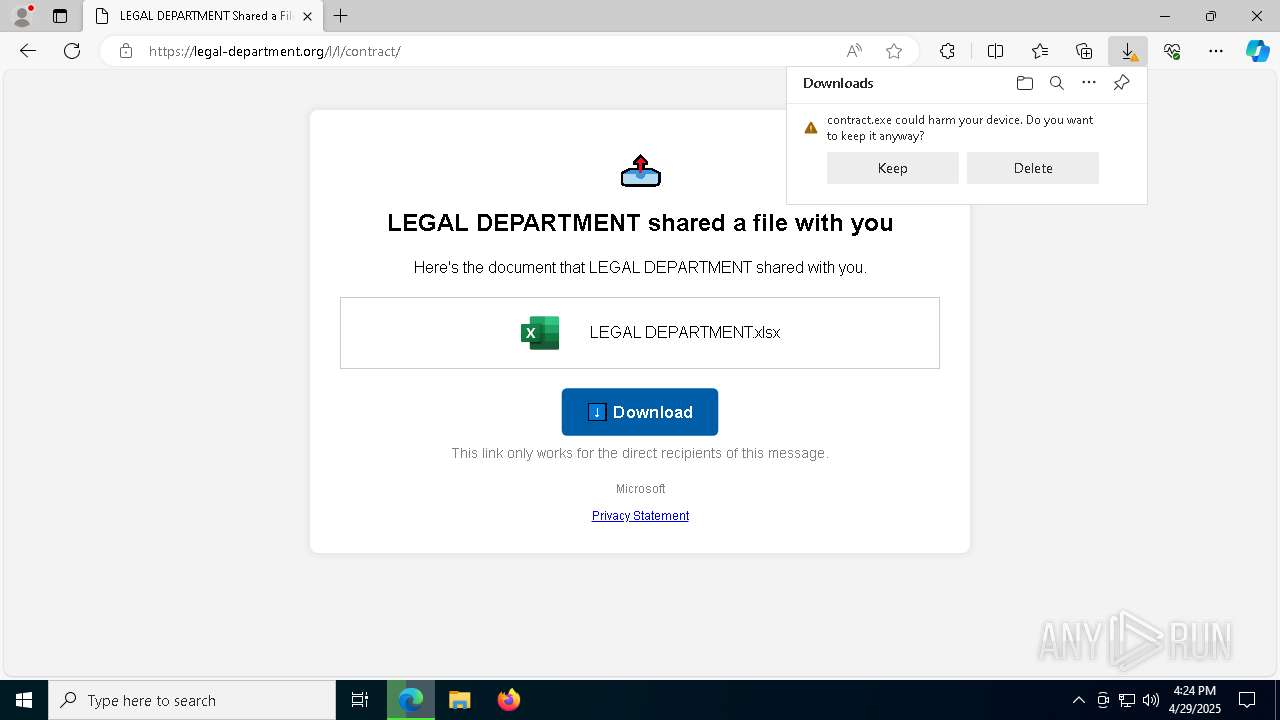
SUSPICIOUS
Reads security settings of Internet Explorer
- contract.exe (PID: 5228)
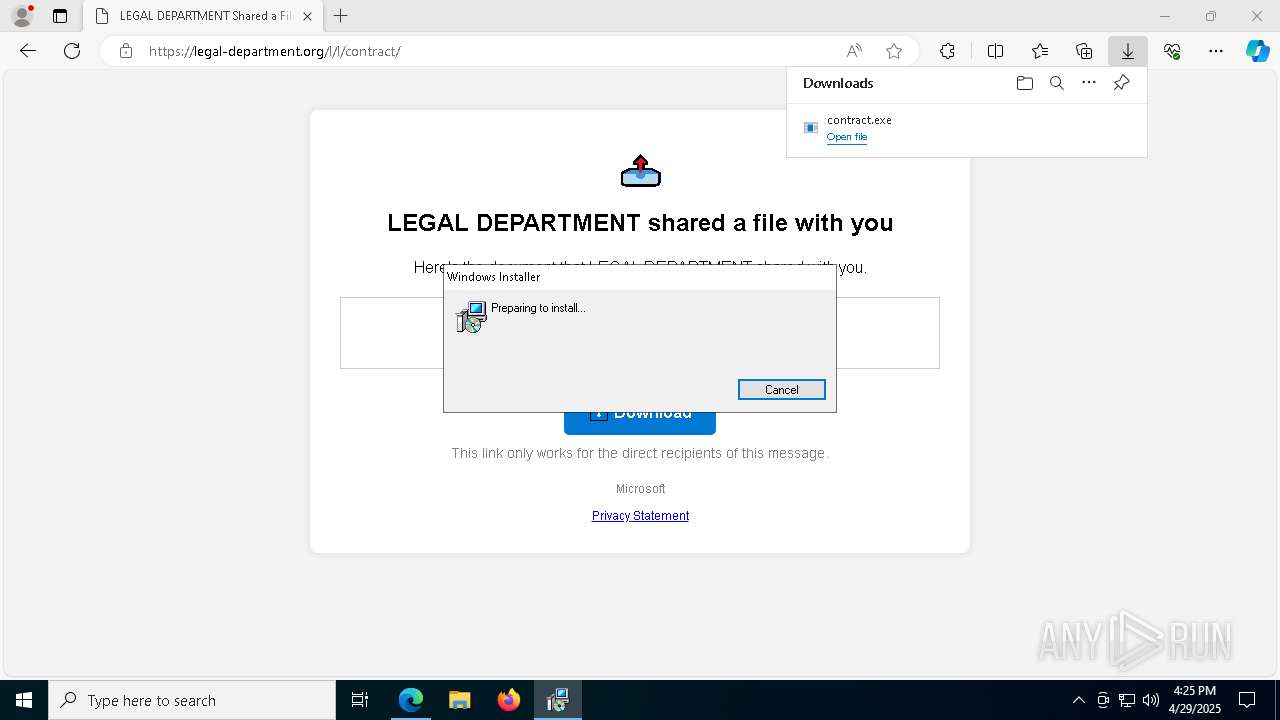
Executable content was dropped or overwritten
- rundll32.exe (PID: 3304)
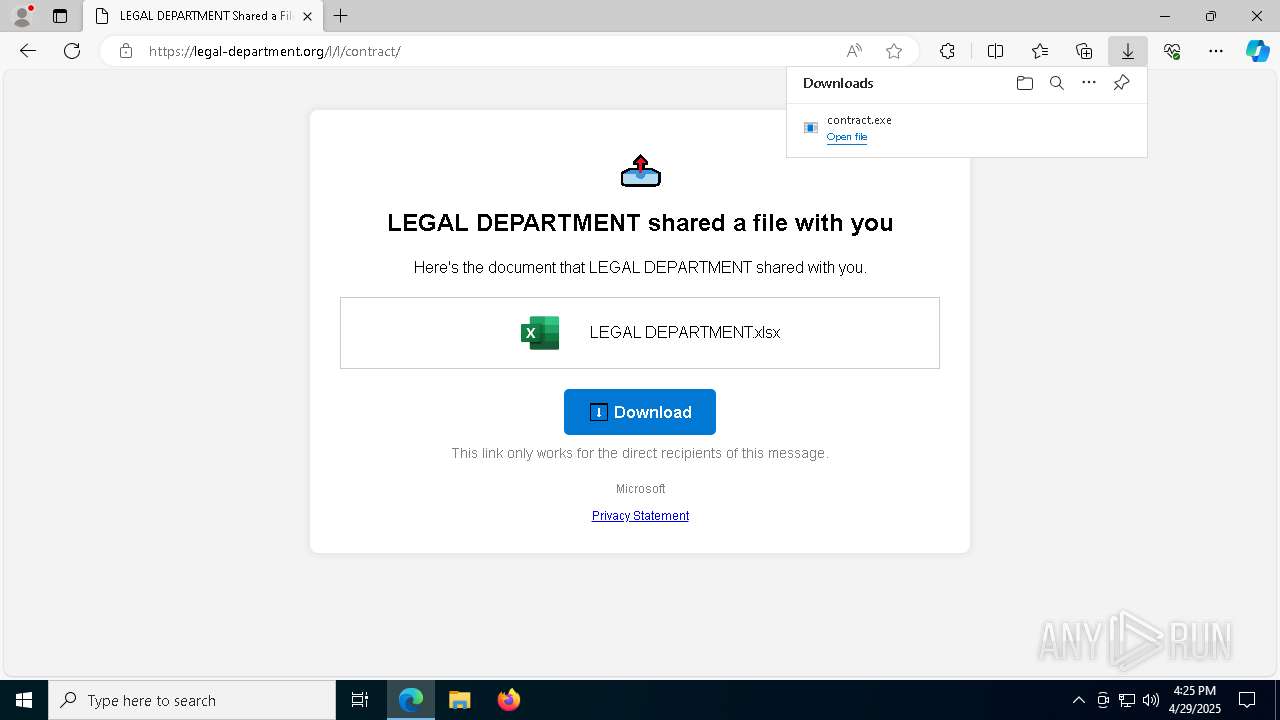
Executes as Windows Service
- VSSVC.exe (PID: 472)
- ScreenConnect.ClientService.exe (PID: 3024)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 3024)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 3024)
INFO
Reads the computer name
- identity_helper.exe (PID: 4120)
- contract.exe (PID: 5228)
- msiexec.exe (PID: 6728)
- msiexec.exe (PID: 2340)
Checks supported languages
- identity_helper.exe (PID: 4120)
- contract.exe (PID: 5228)
- msiexec.exe (PID: 6728)
- msiexec.exe (PID: 2340)
Reads Environment values
- identity_helper.exe (PID: 4120)
Create files in a temporary directory
- contract.exe (PID: 5228)
- rundll32.exe (PID: 3304)
Executable content was dropped or overwritten
- msedge.exe (PID: 7356)
- msiexec.exe (PID: 668)
- msiexec.exe (PID: 6728)
Application launched itself
- msedge.exe (PID: 7356)
Reads the machine GUID from the registry
- contract.exe (PID: 5228)
Process checks computer location settings
- contract.exe (PID: 5228)
CONNECTWISE has been detected
- msiexec.exe (PID: 668)
Manages system restore points
- SrTasks.exe (PID: 6344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
183
Monitored processes
50
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 472 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\25.2.4.9229\190838e8cdfd3642\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | contract.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 812 | C:\Windows\syswow64\MsiExec.exe -Embedding B6E0567319180E9E75DC625C9FD601A0 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6940 --field-trial-handle=2400,i,143018517843723648,113369146081649441,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=6552 --field-trial-handle=2400,i,143018517843723648,113369146081649441,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | C:\Windows\syswow64\MsiExec.exe -Embedding 18BE9B61C08703BCA0188D3C2A36D0AC | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2096 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6364 --field-trial-handle=2400,i,143018517843723648,113369146081649441,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6708 --field-trial-handle=2400,i,143018517843723648,113369146081649441,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6528 --field-trial-handle=2400,i,143018517843723648,113369146081649441,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2340 | C:\Windows\syswow64\MsiExec.exe -Embedding 9794EA07D4AC53E175CD5D44BE6F4173 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 515
Read events
10 220
Write events
278
Delete events
17
Modification events
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D75F388583922F00 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D4512F8583922F00 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 23A3718583922F00 | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\655872 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {ED1711E0-3066-4C1C-81C1-6047289DC581} | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\655872 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {FAEB14B1-D84E-4079-A8EC-67580F7C14FA} | |||
| (PID) Process: | (7356) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\655872 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D619315F-2C34-4BA5-94BE-B1DFF9C2FA27} | |||
Executable files
30
Suspicious files
231
Text files
48
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb43.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bb53.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb53.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bb82.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb91.TMP | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7356 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
66
DNS requests
67
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2384 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
2384 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7668 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7356 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7668 | msedge.exe | 52.18.252.197:443 | click.pstmrk.it | AMAZON-02 | IE | whitelisted |
7668 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
click.pstmrk.it |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
7668 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (short .gy) |
7668 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] WEB Link Shortener (.short .gy) |
7668 | msedge.exe | Misc activity | INFO [ANY.RUN] Possible short link service (short .gy) |
7668 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7668 | msedge.exe | Misc activity | ET HUNTING Telegram API Domain in DNS Lookup |
7668 | msedge.exe | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2196 | svchost.exe | Misc activity | ET REMOTE_ACCESS Observed DNS Query to Known ScreenConnect/ConnectWise Remote Desktop Service Domain |
3024 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |