| File name: | PL2W_defaultpl2w_1.0.0.877.exe |
| Full analysis: | https://app.any.run/tasks/bc127630-4e64-424c-88a0-320412e6b7e7 |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2025, 09:01:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | E646E4E5EFE9E362FAD177027879D233 |
| SHA1: | 69D705A252C4609042C3A8167611FD0A5BC0A368 |
| SHA256: | 918D8162E7DB92EBBF06066FDD3D904785A1404F807FF6168998CEFA7D19D392 |
| SSDEEP: | 98304:DJ8eFncxm/KkW1ESISVeGsXQffvhwobWEqWmwo6/Kmf5mIZFQKvOiDNtdiZNPDBV:DHZ9aUbWV44YglWFL41W |
MALICIOUS
No malicious indicators.SUSPICIOUS
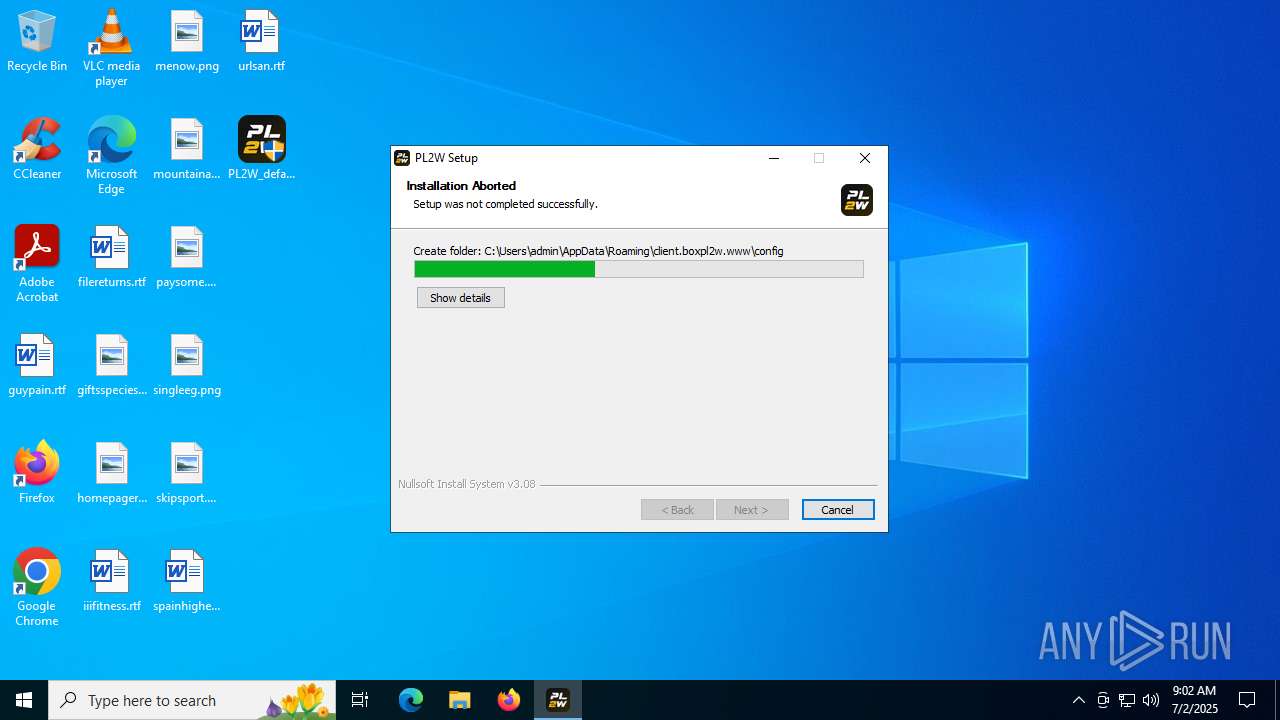
The process creates files with name similar to system file names
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
Malware-specific behavior (creating "System.dll" in Temp)
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 4768)
- MicrosoftEdgeUpdate.exe (PID: 2792)
Executable content was dropped or overwritten
- MicrosoftEdgeWebview2Setup.exe (PID: 4768)
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
Process drops legitimate windows executable
- MicrosoftEdgeUpdate.exe (PID: 2792)
- MicrosoftEdgeWebview2Setup.exe (PID: 4768)
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
Disables SEHOP
- MicrosoftEdgeUpdate.exe (PID: 2792)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 2792)
There is functionality for taking screenshot (YARA)
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
INFO
Checks supported languages
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
- MicrosoftEdgeWebview2Setup.exe (PID: 4768)
- MicrosoftEdgeUpdate.exe (PID: 2792)
The sample compiled with english language support
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
- MicrosoftEdgeUpdate.exe (PID: 2792)
- MicrosoftEdgeWebview2Setup.exe (PID: 4768)
Create files in a temporary directory
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
Reads the computer name
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
- MicrosoftEdgeUpdate.exe (PID: 2792)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 2792)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 2792)
- wermgr.exe (PID: 6892)
- slui.exe (PID: 4512)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 2792)
- wermgr.exe (PID: 6892)
- slui.exe (PID: 4512)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 2792)
Creates files or folders in the user directory
- PL2W_defaultpl2w_1.0.0.877.exe (PID: 1208)
Creates files in the program directory
- MicrosoftEdgeWebview2Setup.exe (PID: 4768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.877 |
| ProductVersionNumber: | 1.0.0.877 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | 2025-07-02 15:47:43 |
| FileDescription: | PL2W |
| FileVersion: | 0.0.877 |
| LegalCopyright: | - |
| ProductName: | PL2W |
| ProductVersion: | 0.0.877 |
Total processes
142
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1208 | "C:\Users\admin\Desktop\PL2W_defaultpl2w_1.0.0.877.exe" | C:\Users\admin\Desktop\PL2W_defaultpl2w_1.0.0.877.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: PL2W Version: 0.0.877 Modules
| |||||||||||||||
| 2792 | "C:\Program Files (x86)\Microsoft\Temp\EU86C4.tmp\MicrosoftEdgeUpdate.exe" /silent /install "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=prefers" | C:\Program Files (x86)\Microsoft\Temp\EU86C4.tmp\MicrosoftEdgeUpdate.exe | MicrosoftEdgeWebview2Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Exit code: 2147747592 Version: 1.3.187.39 Modules
| |||||||||||||||
| 4512 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4768 | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | PL2W_defaultpl2w_1.0.0.877.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Update Setup Exit code: 2147747592 Version: 1.3.187.39 Modules
| |||||||||||||||
| 6200 | "C:\Users\admin\Desktop\PL2W_defaultpl2w_1.0.0.877.exe" | C:\Users\admin\Desktop\PL2W_defaultpl2w_1.0.0.877.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PL2W Exit code: 3221226540 Version: 0.0.877 Modules
| |||||||||||||||
| 6892 | "C:\WINDOWS\system32\wermgr.exe" "-outproc" "0" "2792" "2308" "1980" "2328" "0" "0" "0" "0" "0" "0" "0" "0" | C:\Windows\SysWOW64\wermgr.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 033
Read events
12 999
Write events
32
Delete events
2
Modification events
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{950FD304-CB75-4BE8-B71E-87A642A87DEB} |
| Operation: | write | Name: | PersistedPingString |
Value: <?xml version="1.0" encoding="UTF-8"?><request protocol="3.0" updater="Omaha" updaterversion="1.3.187.39" shell_version="1.3.147.37" ismachine="1" sessionid="{441E0B56-3443-4743-8A49-7CFE4A890744}" userid="{FD984739-A122-4DB0-BE5B-46E3E09D84E4}" installsource="otherinstallcmd" requestid="{950FD304-CB75-4BE8-B71E-87A642A87DEB}" dedup="cr" domainjoined="0"><hw logical_cpus="4" physmemory="4" disk_type="2" sse="1" sse2="1" sse3="1" ssse3="1" sse41="1" sse42="1" avx="1"/><os platform="win" version="10.0.19045.4046" sp="" arch="x64" product_type="48" is_wip="0" is_in_lockdown_mode="0"/><oem product_manufacturer="DELL" product_name="DELL"/><exp etag=""r452t1+k2Tgq/HXzjvFNBRhopBWR9sbjXxqeUDH9uX0=""/><app appid="{F3C4FE00-EFD5-403B-9569-398A20F1BA4A}" version="1.3.195.43" nextversion="1.3.187.39" lang="" brand="" client=""><event eventtype="2" eventresult="1" errorcode="0" extracode1="0" system_uptime_ticks="15429383823" install_time_ms="249"/></app></request> | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{950FD304-CB75-4BE8-B71E-87A642A87DEB} |
| Operation: | write | Name: | PersistedPingTime |
Value: 133959205395389290 | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\MicrosoftEdgeUpdate.exe |
| Operation: | write | Name: | DisableExceptionChainValidation |
Value: 0 | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\proxy |
| Operation: | write | Name: | source |
Value: auto | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\PersistedPings\{950FD304-CB75-4BE8-B71E-87A642A87DEB} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | \REGISTRY\A\{5b6b3d98-7e28-047b-105f-ac53b6db97af}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | \REGISTRY\A\{5b6b3d98-7e28-047b-105f-ac53b6db97af}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6892) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | ClockTimeSeconds |
Value: 9DF5646800000000 | |||
| (PID) Process: | (6892) wermgr.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\IdentityCRL\ClockData |
| Operation: | write | Name: | TickCount |
Value: 6291170000000000 | |||
| (PID) Process: | (2792) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\UsageStats\Daily\Timings |
| Operation: | write | Name: | setup_lock_acquire_ms |
Value: 0400000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
205
Suspicious files
0
Text files
8
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1208 | PL2W_defaultpl2w_1.0.0.877.exe | C:\Users\admin\AppData\Local\Temp\nsr6023.tmp\LangDLL.dll | executable | |
MD5:68B287F4067BA013E34A1339AFDB1EA8 | SHA256:18E8B40BA22C7A1687BD16E8D585380BC2773FFF5002D7D67E9485FCC0C51026 | |||
| 4768 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU86C4.tmp\MicrosoftEdgeUpdateComRegisterShell64.exe | executable | |
MD5:F87A4644FD6DC581EF7B67062FDB55BA | SHA256:1C2FD257DFC2C3967F7AFC0EE726319CB6EAA0F1DB86C34F97D703CE7BDCB5EB | |||
| 4768 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU86C4.tmp\psmachine_64.dll | executable | |
MD5:3C00E3683C341CAA12A7F05301E28C1E | SHA256:99EDC437426A41758D1A42D53D512931A5E8CAAF26A700FDFDBAC4CFE3F2EA69 | |||
| 1208 | PL2W_defaultpl2w_1.0.0.877.exe | C:\Users\admin\AppData\Local\Temp\nsr6023.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
| 1208 | PL2W_defaultpl2w_1.0.0.877.exe | C:\Users\admin\AppData\Local\Temp\nsr6023.tmp\nsDialogs.dll | executable | |
MD5:6C3F8C94D0727894D706940A8A980543 | SHA256:56B96ADD1978B1ABBA286F7F8982B0EFBE007D4A48B3DED6A4D408E01D753FE2 | |||
| 1208 | PL2W_defaultpl2w_1.0.0.877.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | executable | |
MD5:C06E9135C420469715D4310BFB3C1B33 | SHA256:34EFCE66F80CCDF56EC4697D323922CA751C783099B9E0D1A38EEC054776182F | |||
| 1208 | PL2W_defaultpl2w_1.0.0.877.exe | C:\Users\admin\AppData\Local\Temp\nsr6023.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 1208 | PL2W_defaultpl2w_1.0.0.877.exe | C:\Users\admin\AppData\Local\Temp\nsr6023.tmp\StartMenu.dll | executable | |
MD5:D070F3275DF715BF3708BEFF2C6C307D | SHA256:42DD4DDA3249A94E32E20F76EAFFAE784A5475ED00C60EF0197C8A2C1CCD2FB7 | |||
| 4768 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU86C4.tmp\MicrosoftEdgeUpdateBroker.exe | executable | |
MD5:4581E69B900350D2CCA651CADCDC2D5F | SHA256:7DC397674C2A27180C62047F74ECCA70D5BA494F9BE521BC50A20D88650AB03C | |||
| 4768 | MicrosoftEdgeWebview2Setup.exe | C:\Program Files (x86)\Microsoft\Temp\EU86C4.tmp\MicrosoftEdgeUpdate.exe | executable | |
MD5:D80D6C8774203980BEB027E2192F7DF0 | SHA256:41587C47ED8B365599332D5E321437A6DFCA746EDFC782A231F5D0D4174B5CB8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
48
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
4400 | RUXIMICS.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
4400 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
— | — | POST | 400 | 20.190.160.132:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | GET | 304 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/EdgeUpdate/1.3.187.39?clientId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&appChannel_edgeupdate=6&appConsentState_edgeupdate=0&appDayOfInstall_edgeupdate=0&appInactivityBadgeApplied_edgeupdate=0&appInactivityBadgeCleared_edgeupdate=0&appInactivityBadgeDuration_edgeupdate=0&appInstallTimeDiffSec_edgeupdate=0&appIsPinnedSystem_edgeupdate=false&appLastLaunchCount_edgeupdate=0&appLastLaunchTime_edgeupdate=0&appLastLaunchTimeJson_edgeupdate=0&appLastLaunchTimeDaysAgo_edgeupdate=0&appVersion_edgeupdate=1.3.187.39&appUpdateCheckIsUpdateDisabled_edgeupdate=false&appUpdatesAllowedForMeteredNetworks_edgeupdate=false&hwDiskType=2&hwHasSsse3=true&hwLogicalCpus=4&hwPhysmemory=4&isCTADevice=false&isMsftDomainJoined=false&oemProductManufacturer=DELL&oemProductName=DELL&osArch=x64&osIsDefaultNetworkConnectionMetered=false&osIsInLockdownMode=false&osIsWIP=false&osPlatform=win&osProductType=48&osVersion=10.0.19045.4046&requestCheckPeriodSec=-1&requestDomainJoined=false&requestInstallSource=otherinstallcmd&requestIsMachine=true&requestOmahaShellVersion=1.3.147.37&requestOmahaVersion=1.3.187.39 | US | — | — | unknown |
— | — | GET | 304 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/EdgeUpdate/1.3.187.39?clientId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&appChannel_webview=5&appConsentState_webview=0&appDayOfInstall_webview=0&appInactivityBadgeApplied_webview=0&appInactivityBadgeCleared_webview=0&appInactivityBadgeDuration_webview=0&appInstallTimeDiffSec_webview=0&appIsPinnedSystem_webview=false&appLastLaunchCount_webview=0&appLastLaunchTime_webview=0&appLastLaunchTimeJson_webview=0&appLastLaunchTimeDaysAgo_webview=0&appUpdateCheckIsUpdateDisabled_webview=false&appUpdatesAllowedForMeteredNetworks_webview=false&hwDiskType=2&hwHasSsse3=true&hwLogicalCpus=4&hwPhysmemory=4&isCTADevice=false&isMsftDomainJoined=false&oemProductManufacturer=DELL&oemProductName=DELL&osArch=x64&osIsDefaultNetworkConnectionMetered=false&osIsInLockdownMode=false&osIsWIP=false&osPlatform=win&osProductType=48&osVersion=10.0.19045.4046&requestCheckPeriodSec=-1&requestDomainJoined=false&requestInstallSource=otherinstallcmd&requestIsMachine=true&requestOmahaShellVersion=1.3.147.37&requestOmahaVersion=1.3.187.39 | US | — | — | unknown |
— | — | POST | 200 | 20.190.160.14:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 16.7 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4400 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4400 | RUXIMICS.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4400 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |