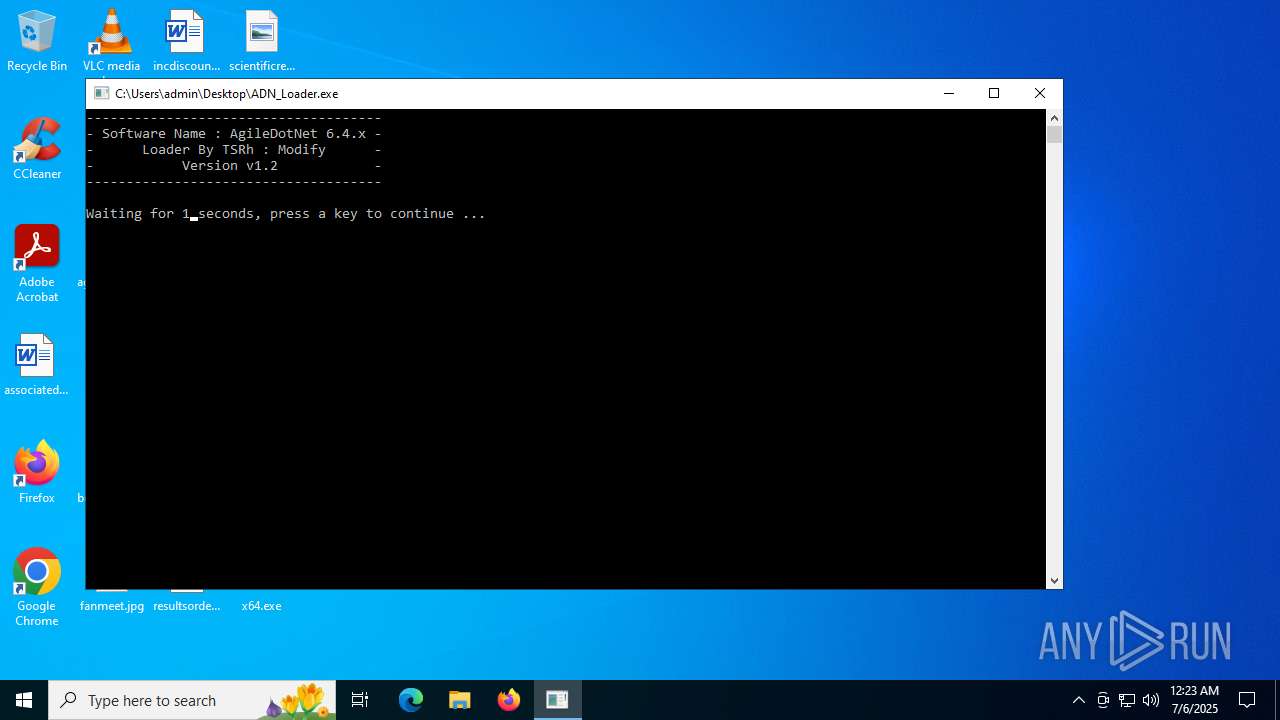
| File name: | ADN_Loader.exe |
| Full analysis: | https://app.any.run/tasks/5b4d38a5-c4b8-4c8e-90c1-827615e88fc2 |
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2025, 00:23:28 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 3 sections |
| MD5: | F84BE7679082F463405D2C3EDB6C893D |
| SHA1: | E766E3B88DF18BD1D4451DCA890FAB601C9B5EDA |
| SHA256: | 918B30A5EA8A1A492499D9435798558062781C8806F840C6DD7A1B01E9B61A8B |
| SSDEEP: | 3072:W1YPvwue7Ur+vhLpDNL+p05QiYMeB+qP6nW:2YPvwuxr+vhLW05QiYMeB+qP6W |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- ADN_Loader.exe (PID: 4400)
Executing commands from a ".bat" file
- ADN_Loader.exe (PID: 4400)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5556)
Executable content was dropped or overwritten
- ADN_Loader.exe (PID: 4400)
The process executes via Task Scheduler
- updater.exe (PID: 6764)
Application launched itself
- updater.exe (PID: 6764)
INFO
Checks supported languages
- ADN_Loader.exe (PID: 4400)
- x64.exe (PID: 4920)
- updater.exe (PID: 6764)
- updater.exe (PID: 6748)
Create files in a temporary directory
- ADN_Loader.exe (PID: 4400)
Checks proxy server information
- slui.exe (PID: 2128)
Reads the software policy settings
- slui.exe (PID: 2128)
Reads the computer name
- updater.exe (PID: 6764)
Process checks whether UAC notifications are on
- updater.exe (PID: 6764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win64 Executable (74.5) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (22.1) |
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2017:01:18 11:02:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 2.5 |
| CodeSize: | 86016 |
| InitializedDataSize: | 4096 |
| UninitializedDataSize: | 172032 |
| EntryPoint: | 0x3ed00 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
Total processes
142
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2128 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | "C:\Users\admin\Desktop\ADN_Loader.exe" | C:\Users\admin\Desktop\ADN_Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4692 | "C:\Users\admin\Desktop\ADN_Loader.exe" | C:\Users\admin\Desktop\ADN_Loader.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4804 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ADN_Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | timeout 3 | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4920 | "C:\Users\admin\Desktop\x64.exe" 24\10\2500 "C:\Users\admin\Desktop\AgileDotNet.exe" | C:\Users\admin\Desktop\x64.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 5116 | reg query HKEY_LOCAL_MACHINE\Software\imotech | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5556 | "C:\WINDOWS\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\5D23.tmp\5D24.bat C:\Users\admin\Desktop\ADN_Loader.exe" | C:\Windows\System32\cmd.exe | — | ADN_Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6748 | reg query HKEY_CURRENT_USER\Software\imotech | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6748 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --crash-handler --system "--database=C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\Crashpad" --url=https://clients2.google.com/cr/report --annotation=prod=Update4 --annotation=ver=134.0.6985.0 "--attachment=C:\Program Files (x86)\Google\GoogleUpdater\updater.log" --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x111c460,0x111c46c,0x111c478 | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
Total events
3 633
Read events
3 633
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4400 | ADN_Loader.exe | C:\Users\admin\AppData\Local\Temp\5D23.tmp\5D24.bat | text | |
MD5:07828F5CF65C79388F1C97543BD7D386 | SHA256:163556CE238E1634EC7F73FA71F498D3C71C71D269170625FAC1051BD8DDF268 | |||
| 4400 | ADN_Loader.exe | C:\Users\admin\Desktop\x64.exe | executable | |
MD5:B05AC25A3943C03A93748B945D4E5769 | SHA256:B30CB11EF8C7BC78CFACFA1F257A147114450074C2BBC00AA67B9781A73FEB14 | |||
| 4400 | ADN_Loader.exe | C:\Users\admin\Desktop\x86.exe | executable | |
MD5:63D605F8F25F0F588565FE8AB6BA2576 | SHA256:600F34375052FF602837D8D419AE82BD2EE3AB8088BDB7979103E2143F8E0D4D | |||
| 6748 | updater.exe | C:\Program Files (x86)\Google\GoogleUpdater\updater.log | text | |
MD5:F91D204101C7903C24750196F92229A8 | SHA256:495EEED577CB762737DEB0D9E532A7DBB39FCA2274803FECA7FD713582086C9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
19
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1520 | RUXIMICS.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1520 | RUXIMICS.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1520 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1520 | RUXIMICS.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1520 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |