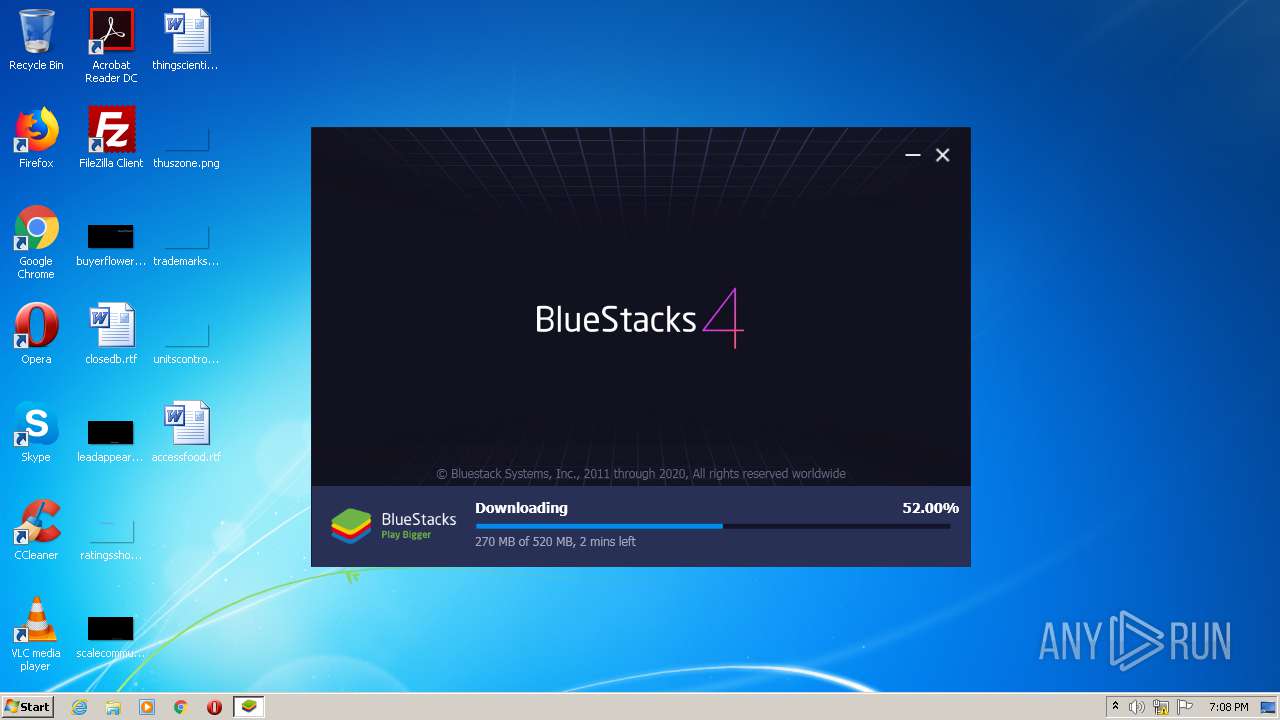
| File name: | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe |
| Full analysis: | https://app.any.run/tasks/5ac1d0ed-88f1-4a89-843b-70eb3989d434 |
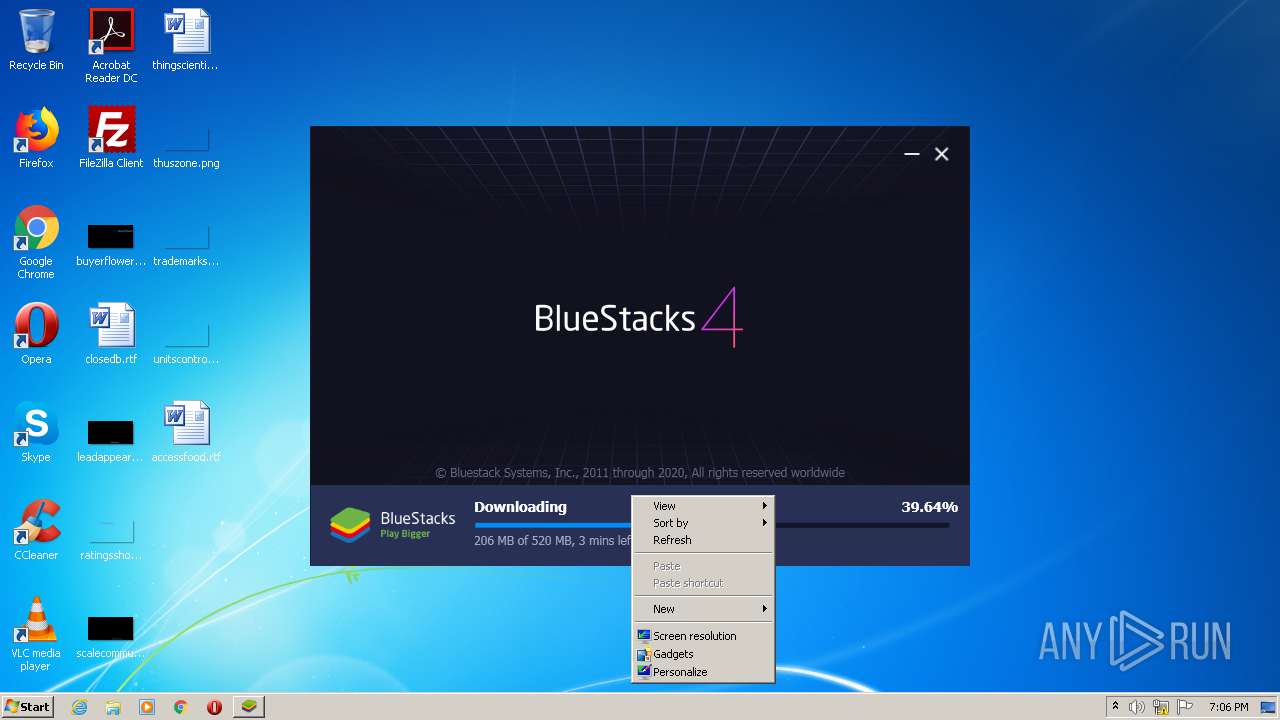
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2020, 19:03:12 |
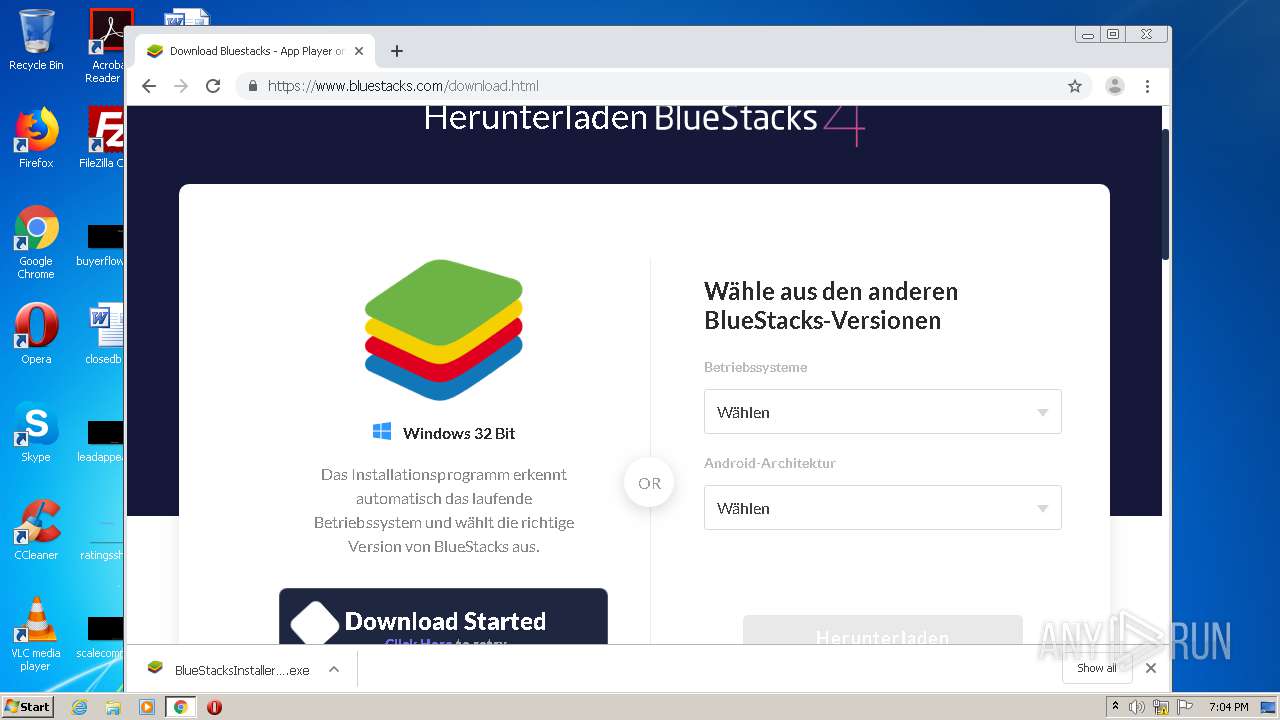
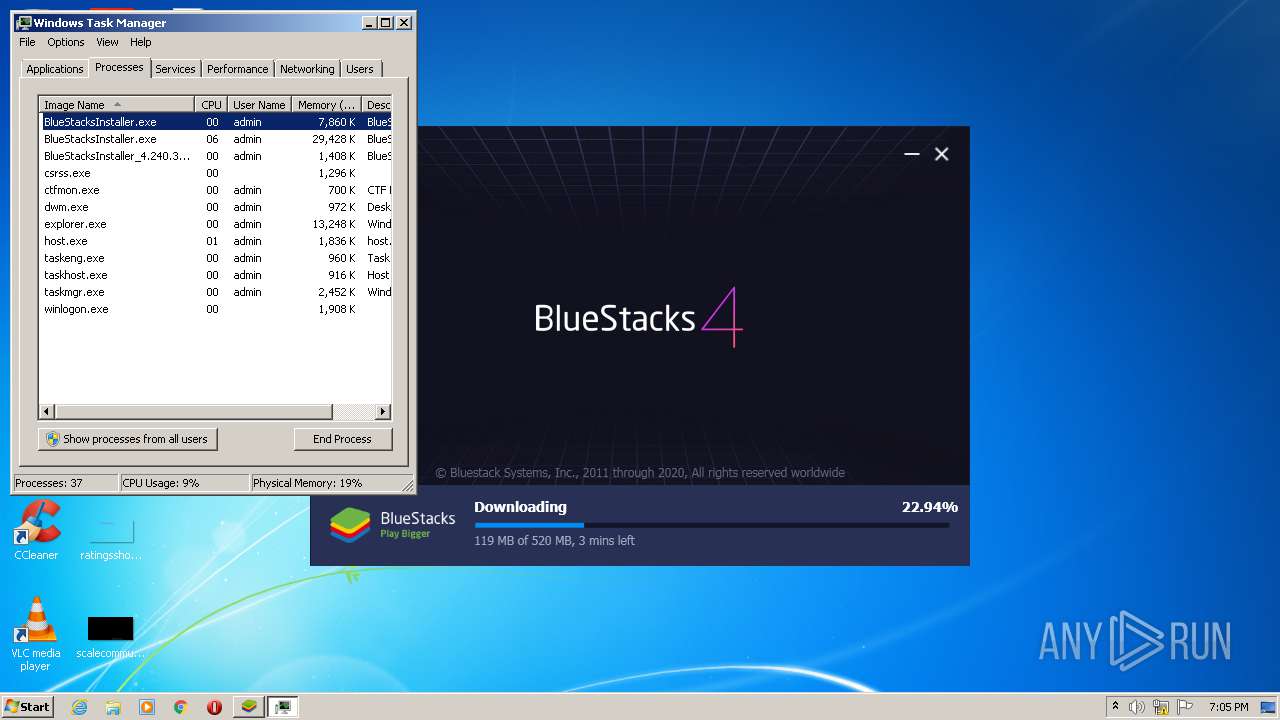
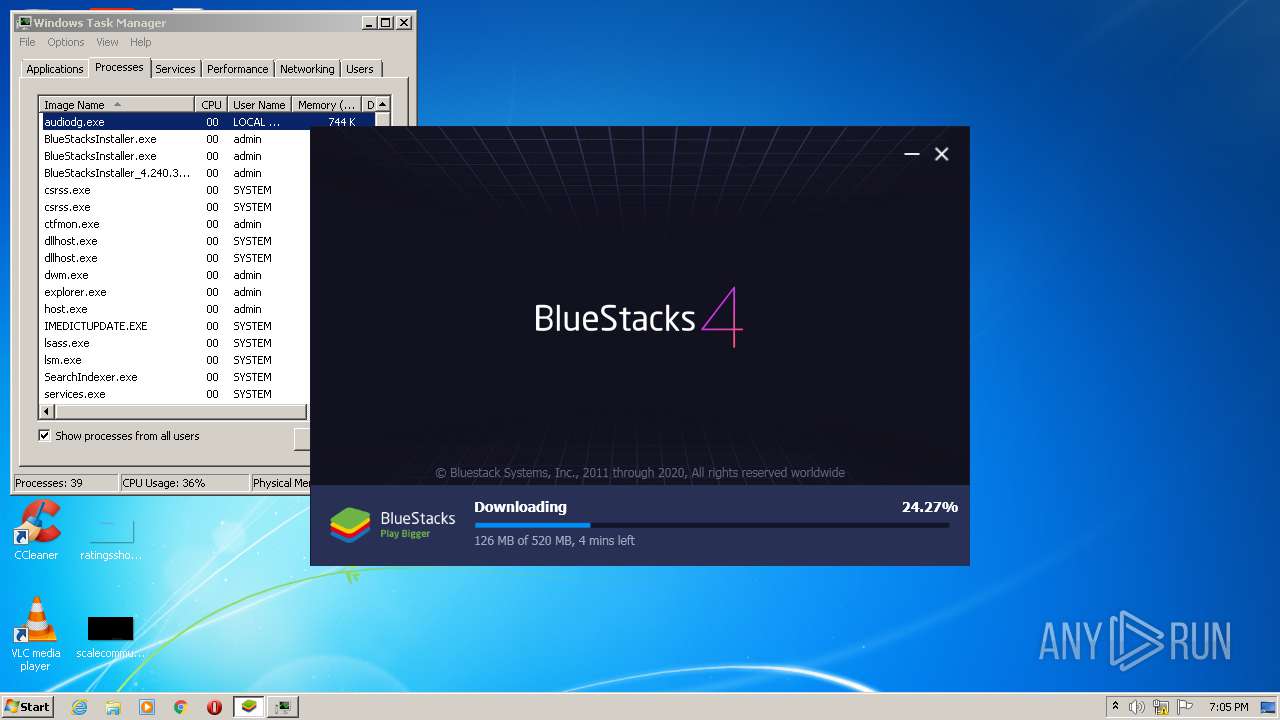
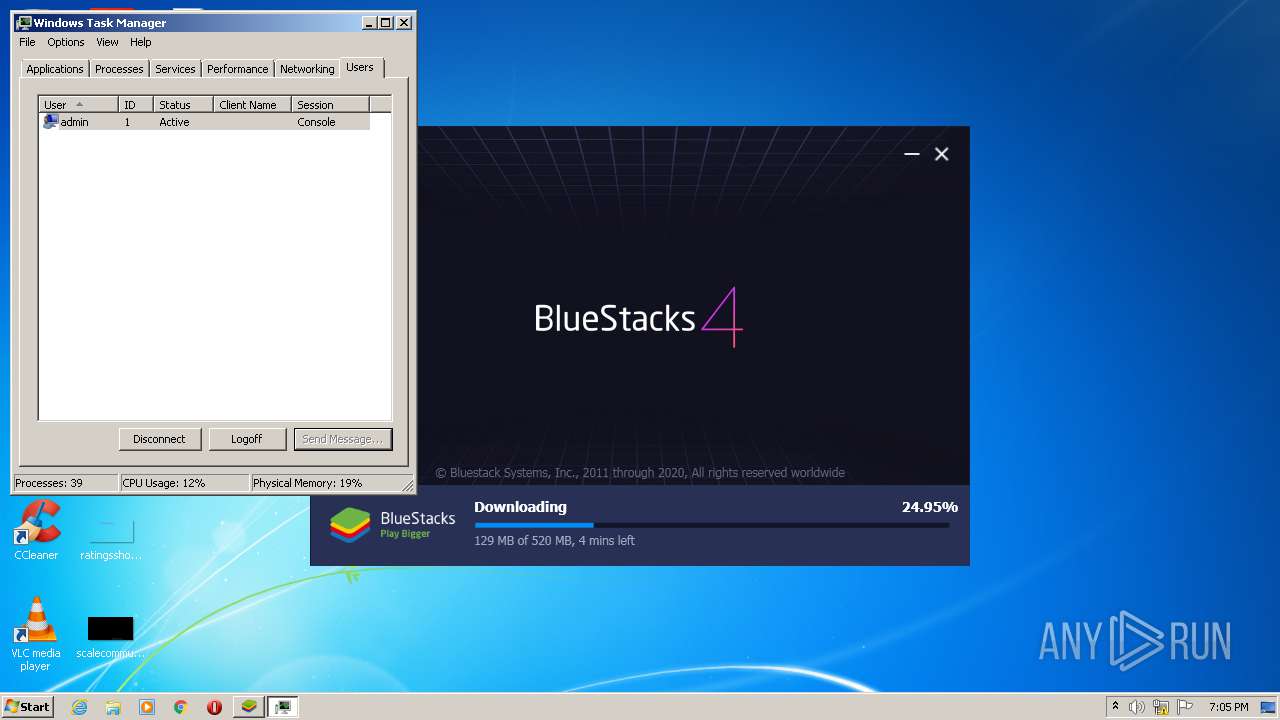
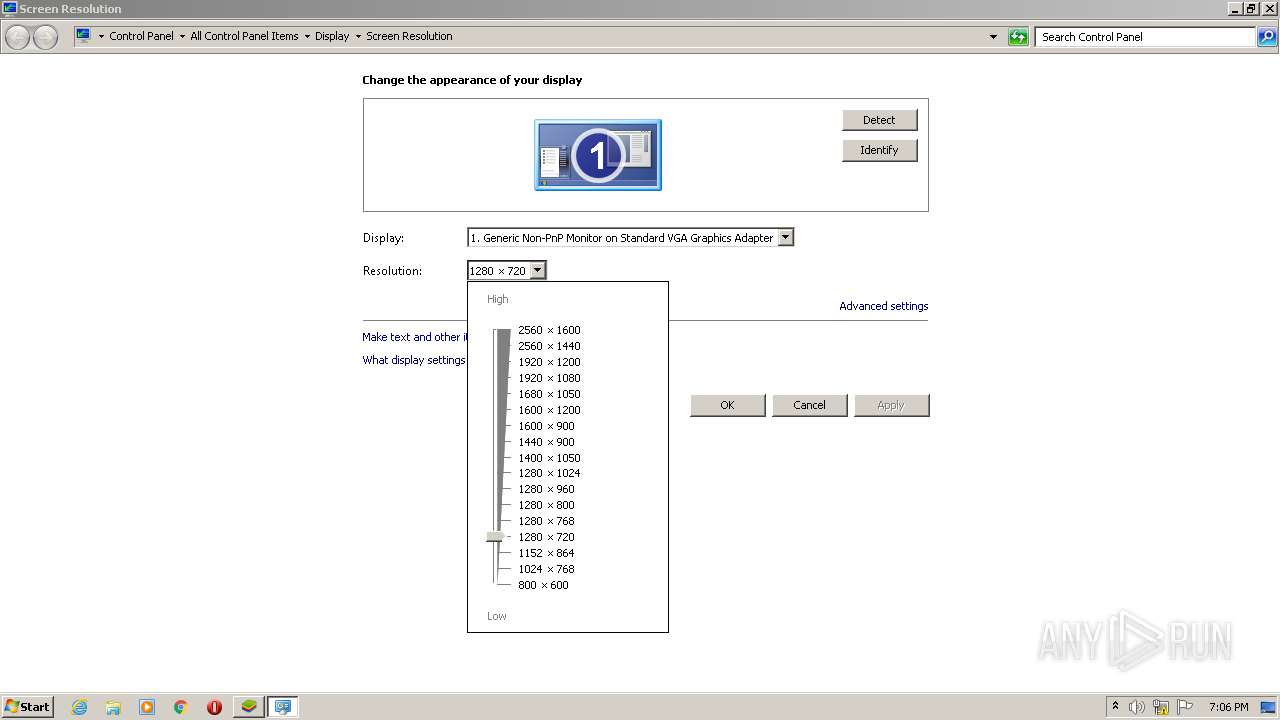
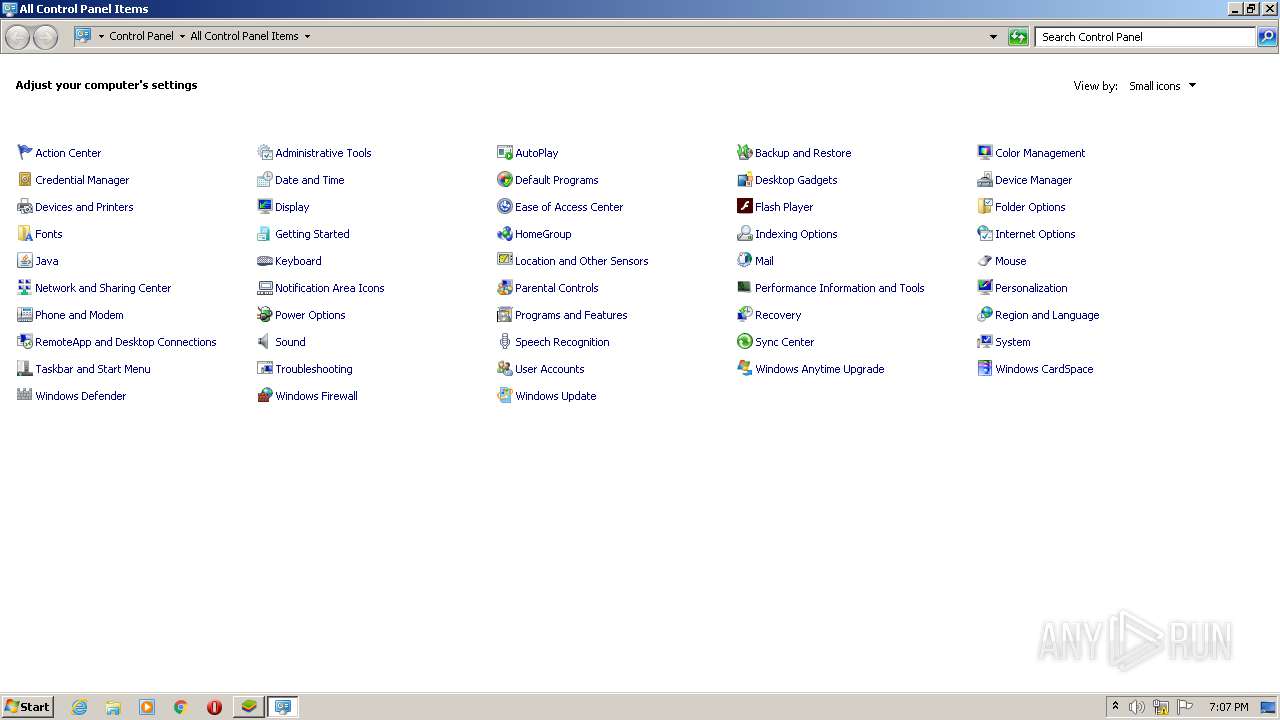
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 011E5D3F14FCE23F00F43B958BD74D90 |
| SHA1: | 138CAADB352BE7E6F7184266319A92DE34378B4F |
| SHA256: | 91405AA0B9DD7C256255096D7A20C182E55D36A837DDE3320BF10CFC604F1001 |
| SSDEEP: | 24576:ZcVkKS/WtWrnngnnnKnanxNpZb67JBVzSKDzzma/EO6O34gezvf0xiLsZpR46l1:ZcB6WErnngnnnKnanzbo5FDzBsO6ij0K |
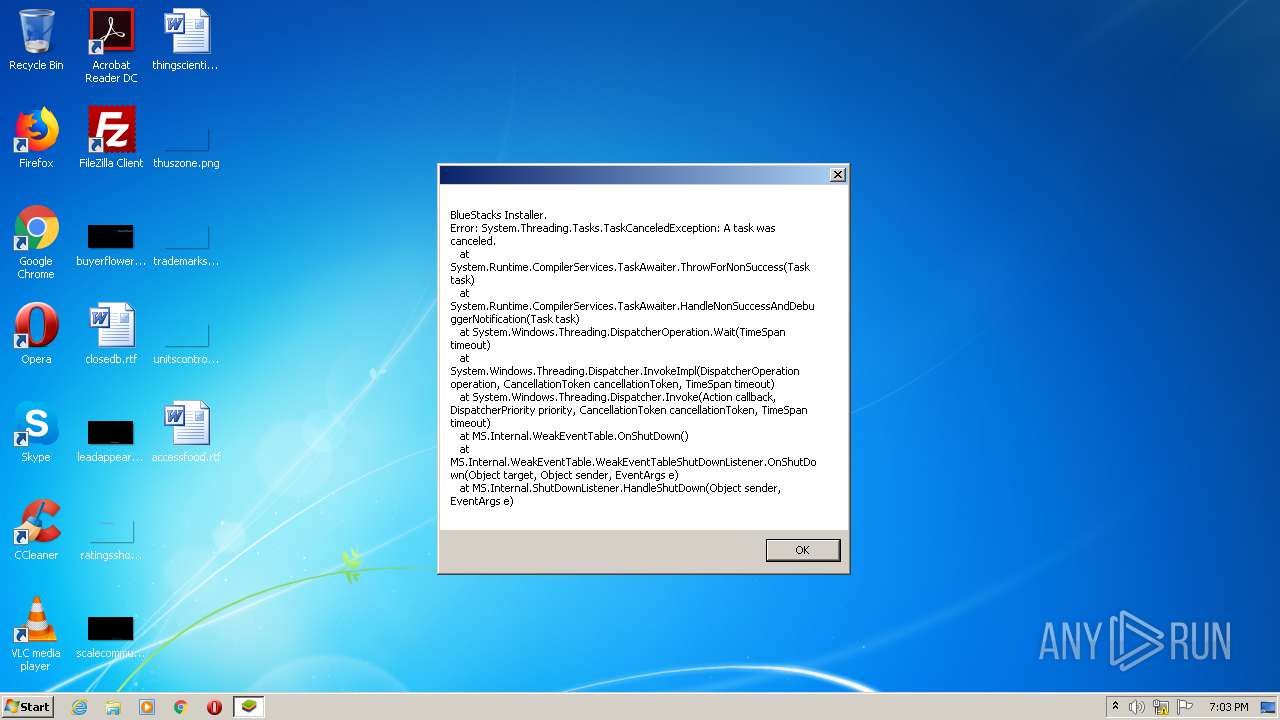
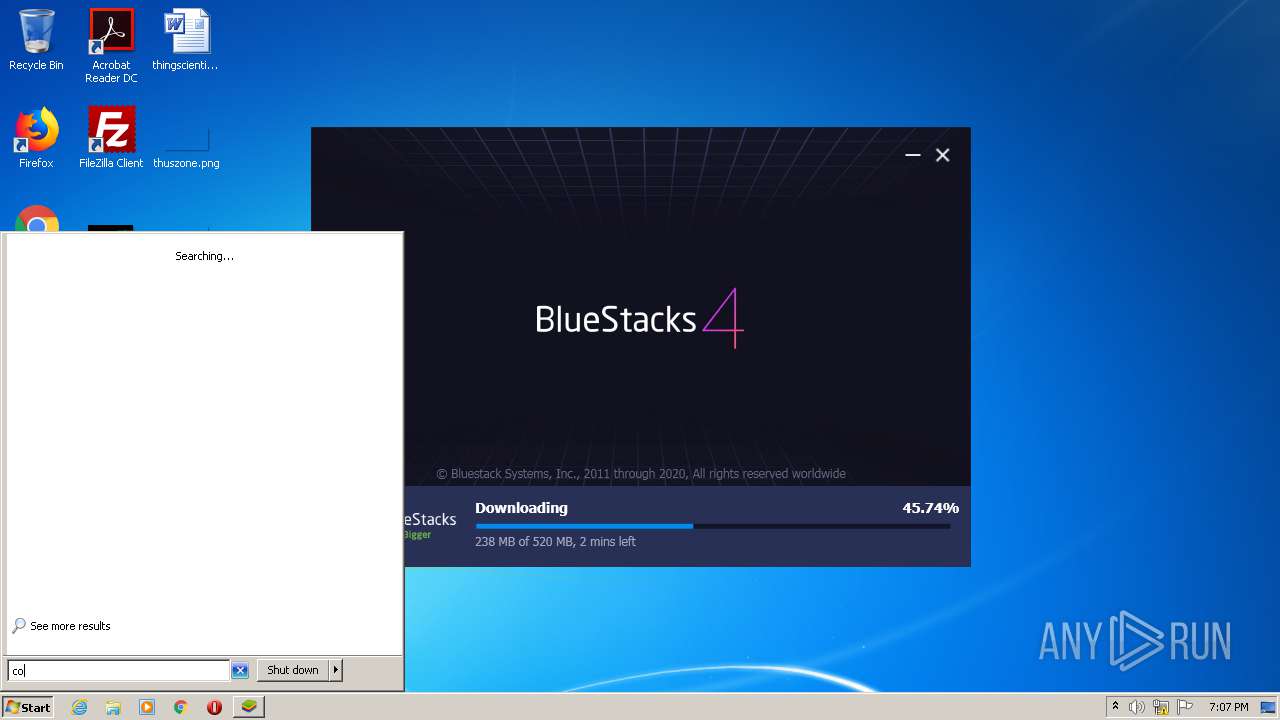
MALICIOUS
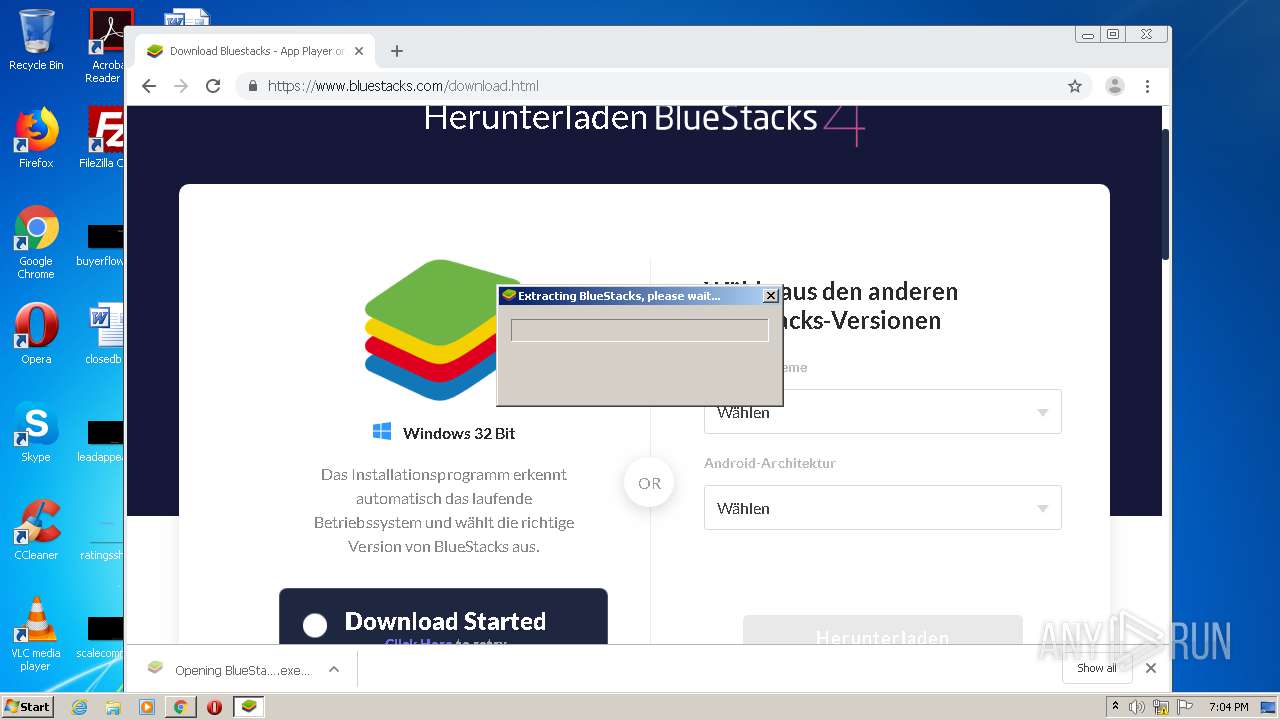
Drops executable file immediately after starts
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 2216)
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 3508)
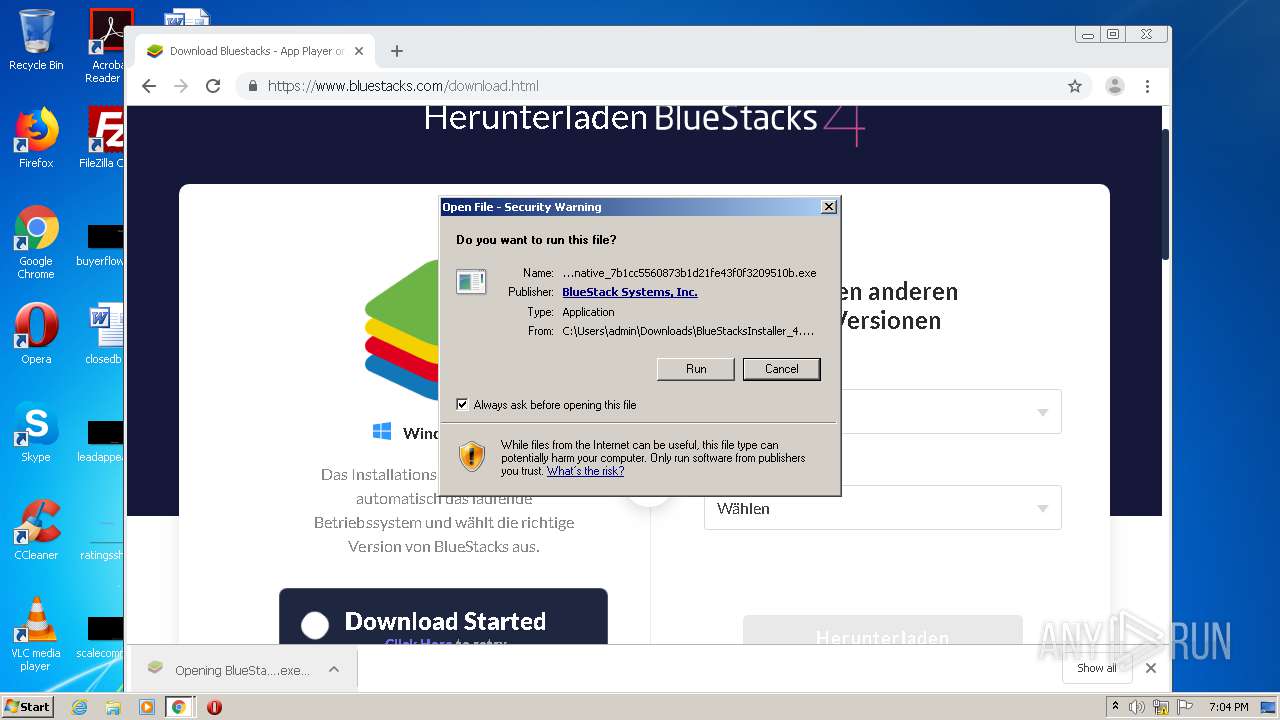
- BlueStacksInstaller_4.240.30.1002_native_7b1cc5560873b1d21fe43f0f3209510b.exe (PID: 2912)
Application was dropped or rewritten from another process
- BlueStacksInstaller.exe (PID: 2752)
- BlueStacksInstaller.exe (PID: 2444)
- BlueStacksInstaller.exe (PID: 2544)
- BlueStacksInstaller.exe (PID: 3156)
- BlueStacksInstaller.exe (PID: 2612)
Loads dropped or rewritten executable
- BlueStacksInstaller.exe (PID: 2752)
Changes settings of System certificates
- BlueStacksInstaller.exe (PID: 2752)
SUSPICIOUS
Executable content was dropped or overwritten
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 2216)
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 3508)
- BlueStacksInstaller.exe (PID: 2752)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3028)
- BlueStacksInstaller_4.240.30.1002_native_7b1cc5560873b1d21fe43f0f3209510b.exe (PID: 2912)
Drops a file with a compile date too recent
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 2216)
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 3508)
- BlueStacksInstaller_4.240.30.1002_native_7b1cc5560873b1d21fe43f0f3209510b.exe (PID: 2912)
Drops a file that was compiled in debug mode
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 2216)
- BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe (PID: 3508)
- BlueStacksInstaller_4.240.30.1002_native_7b1cc5560873b1d21fe43f0f3209510b.exe (PID: 2912)
Reads Environment values
- BlueStacksInstaller.exe (PID: 2752)
- BlueStacksInstaller.exe (PID: 2444)
- BlueStacksInstaller.exe (PID: 3156)
- BlueStacksInstaller.exe (PID: 2612)
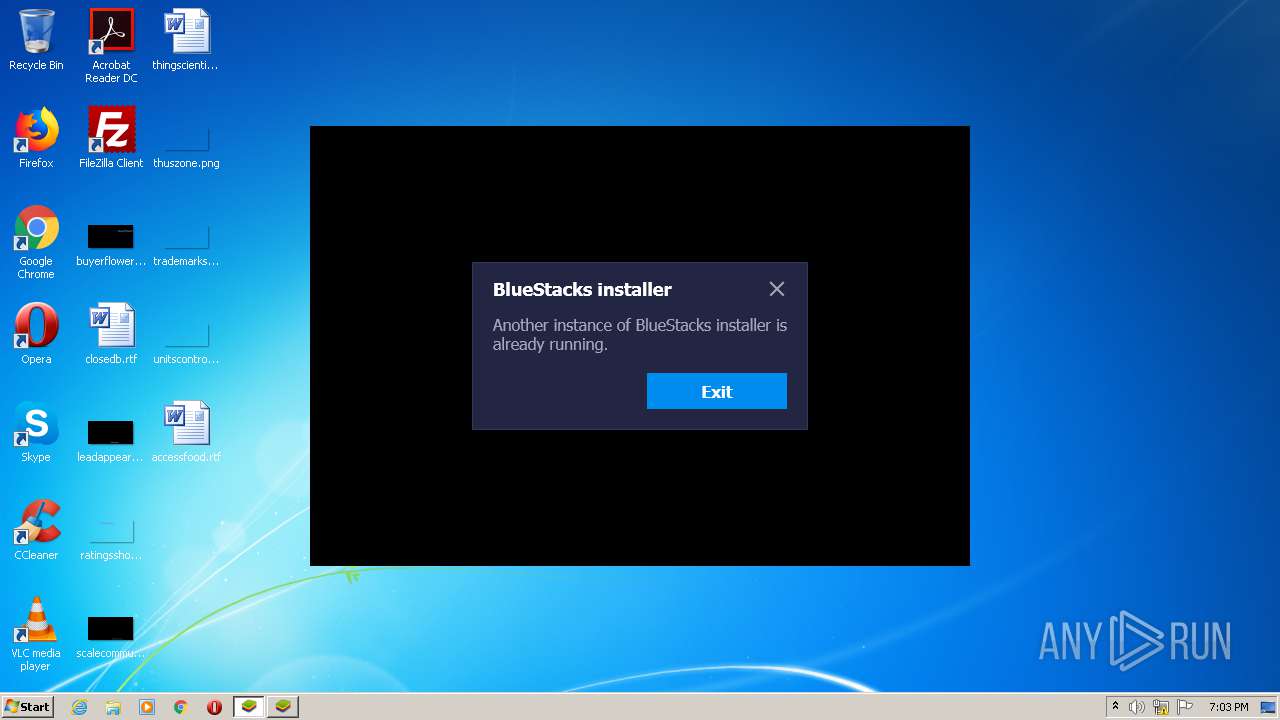
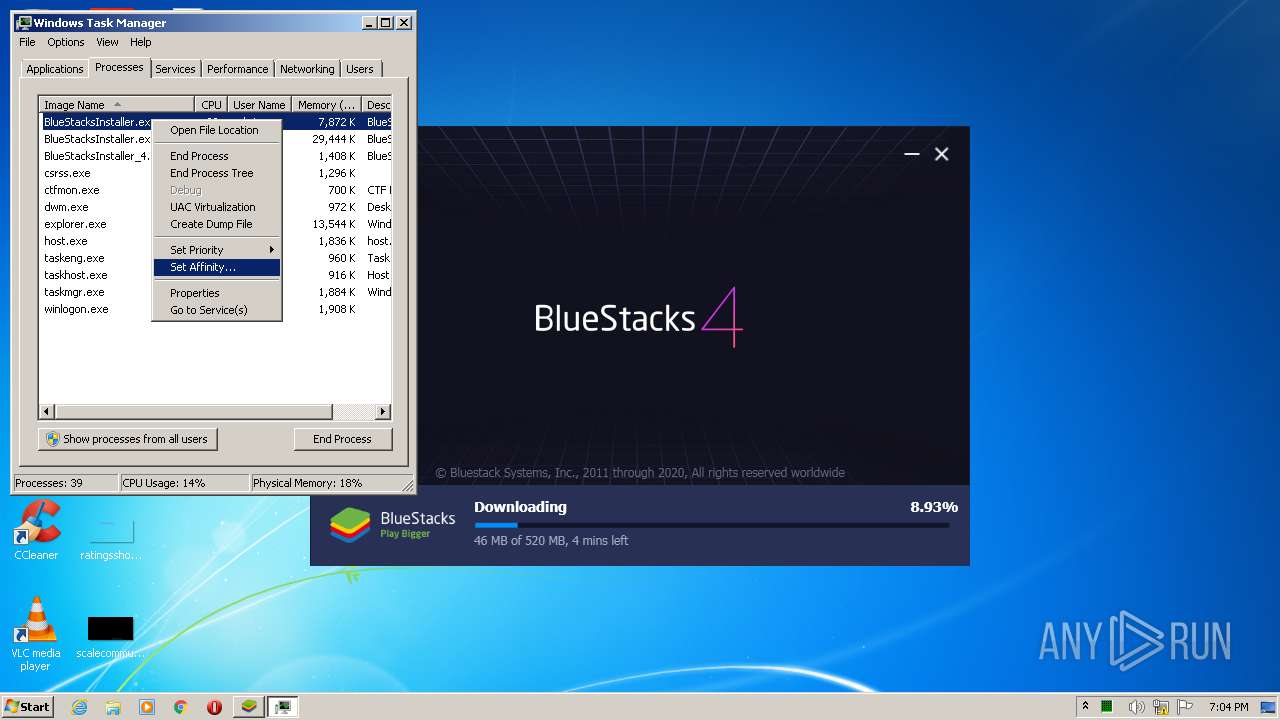
Application launched itself
- BlueStacksInstaller.exe (PID: 2444)
- BlueStacksInstaller.exe (PID: 2612)
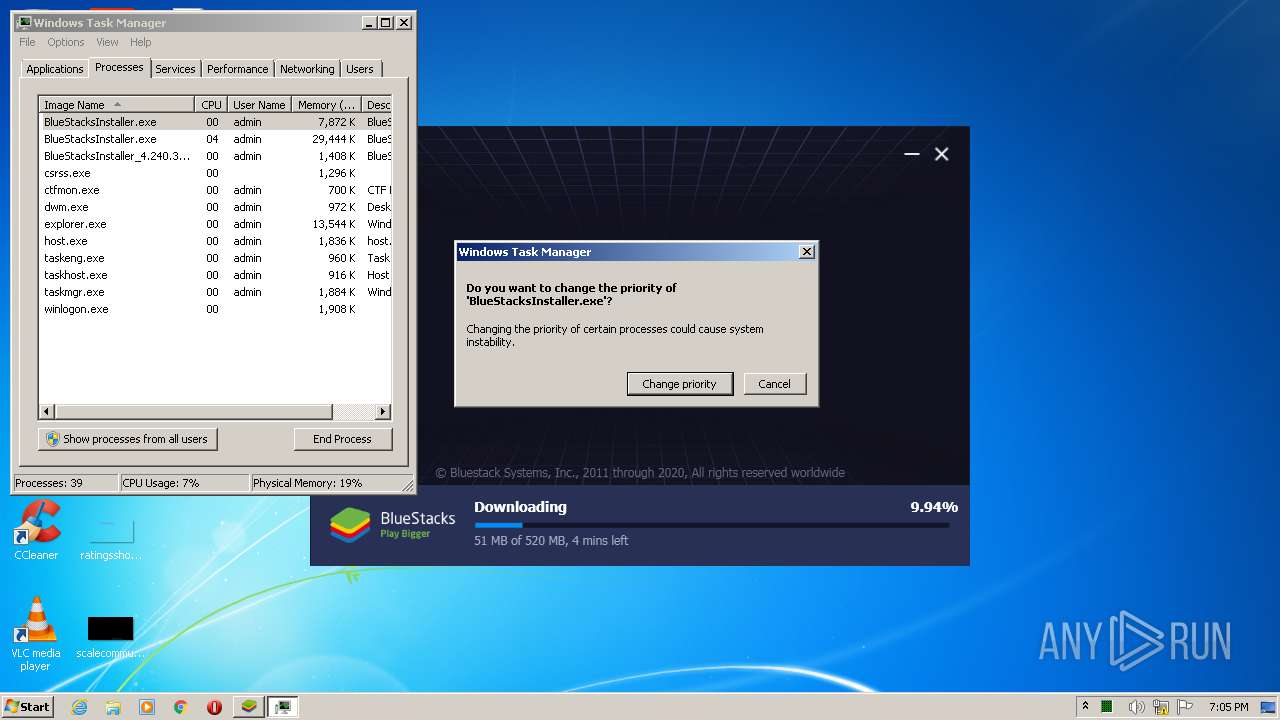
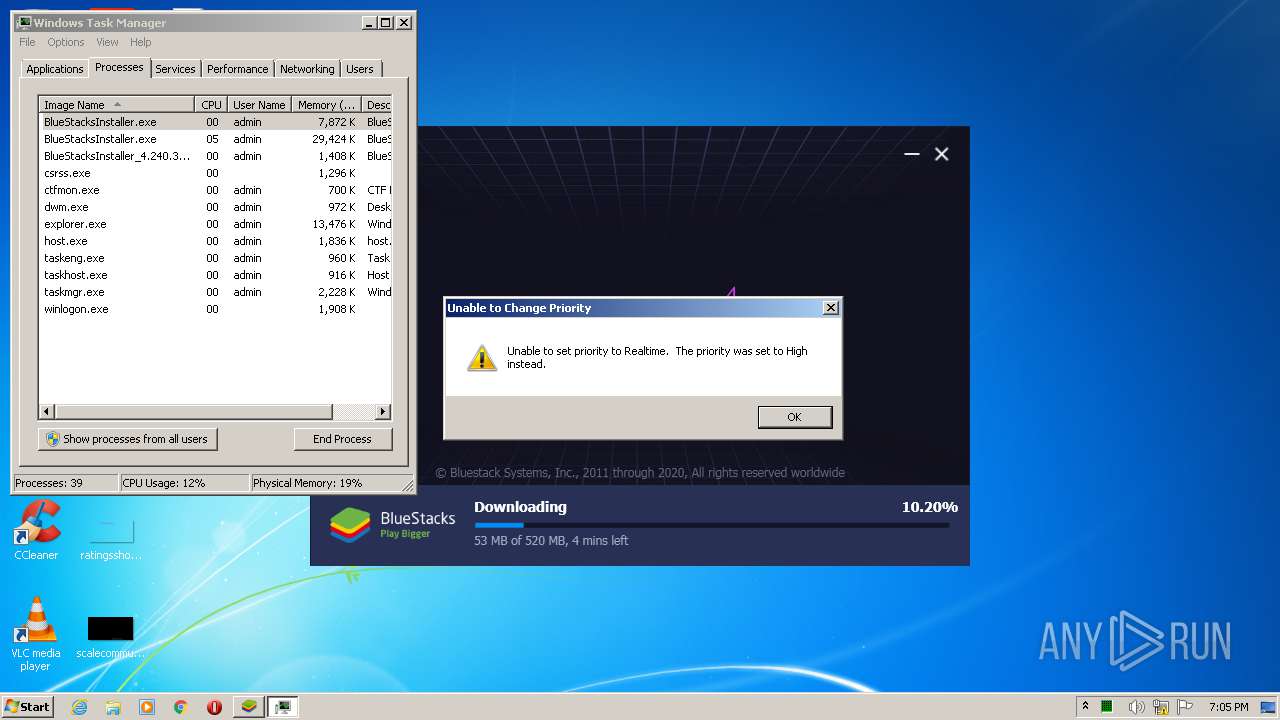
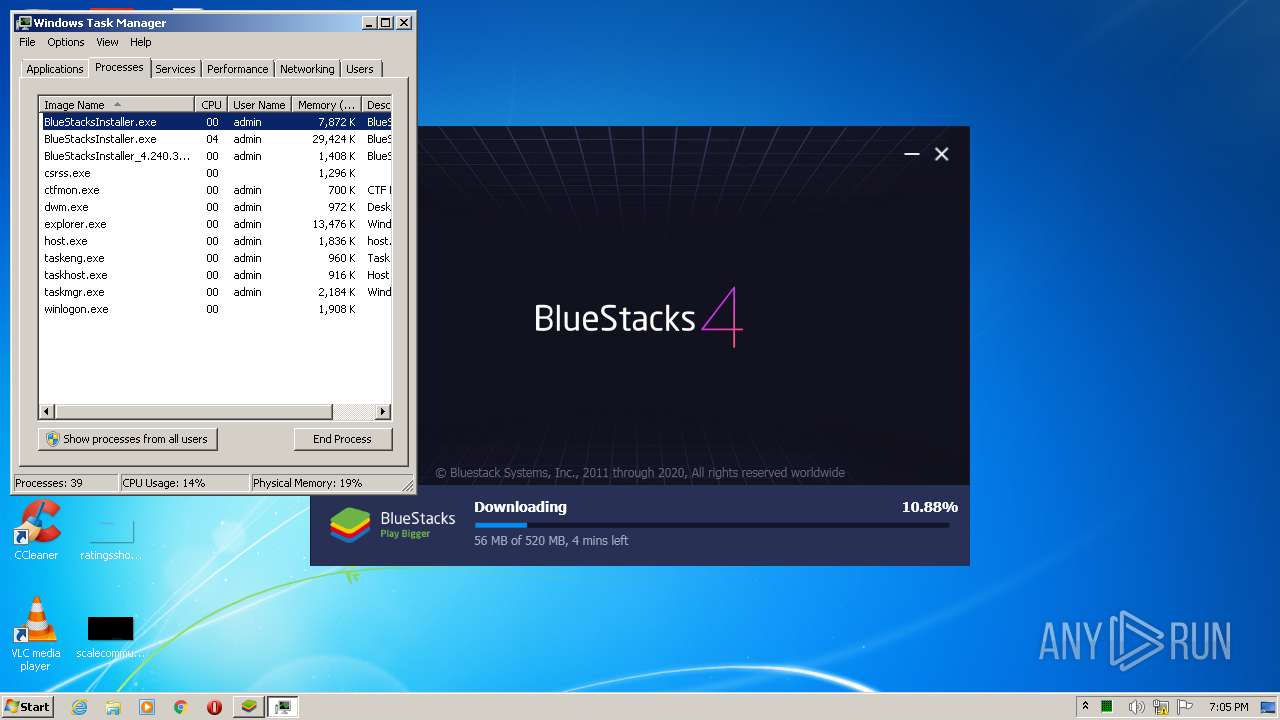
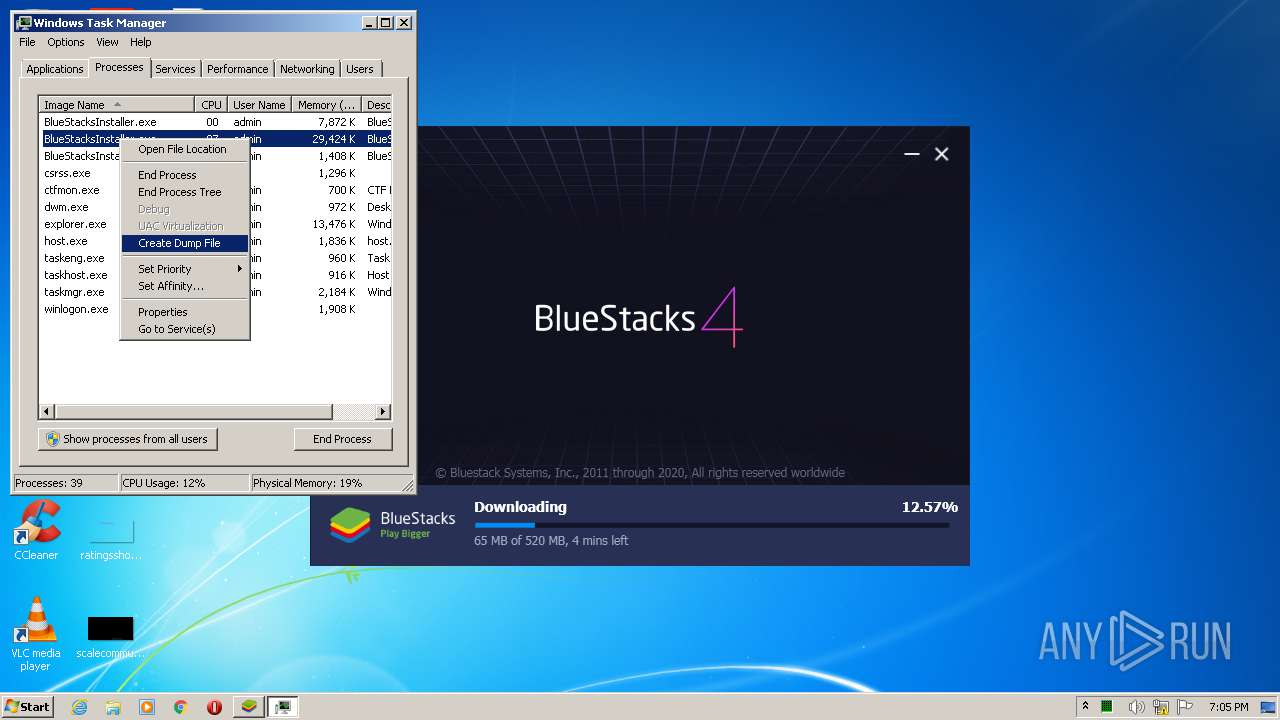
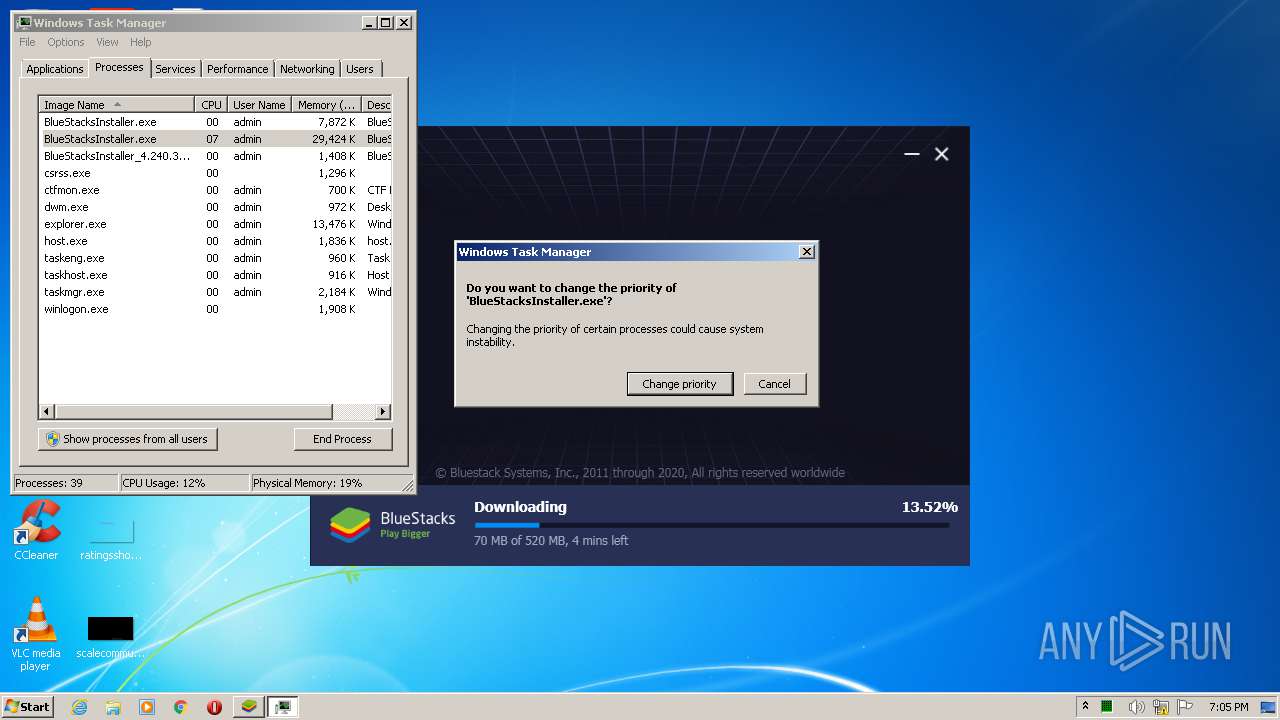
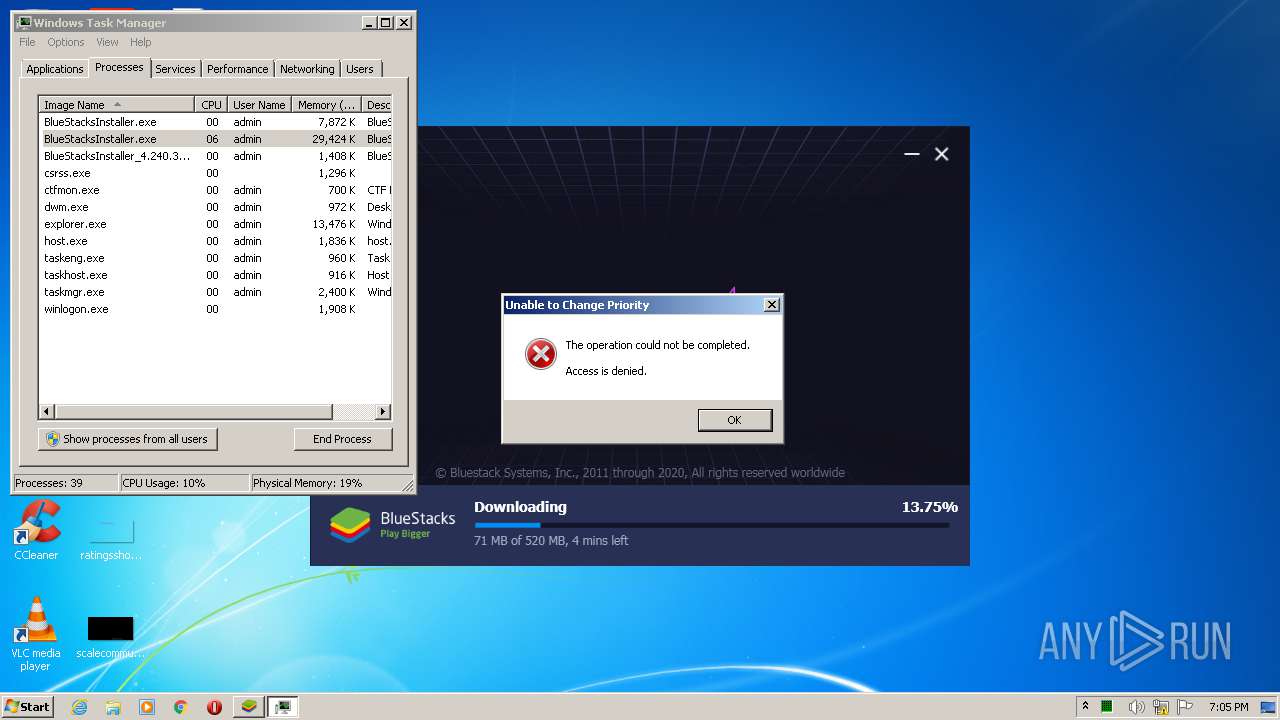
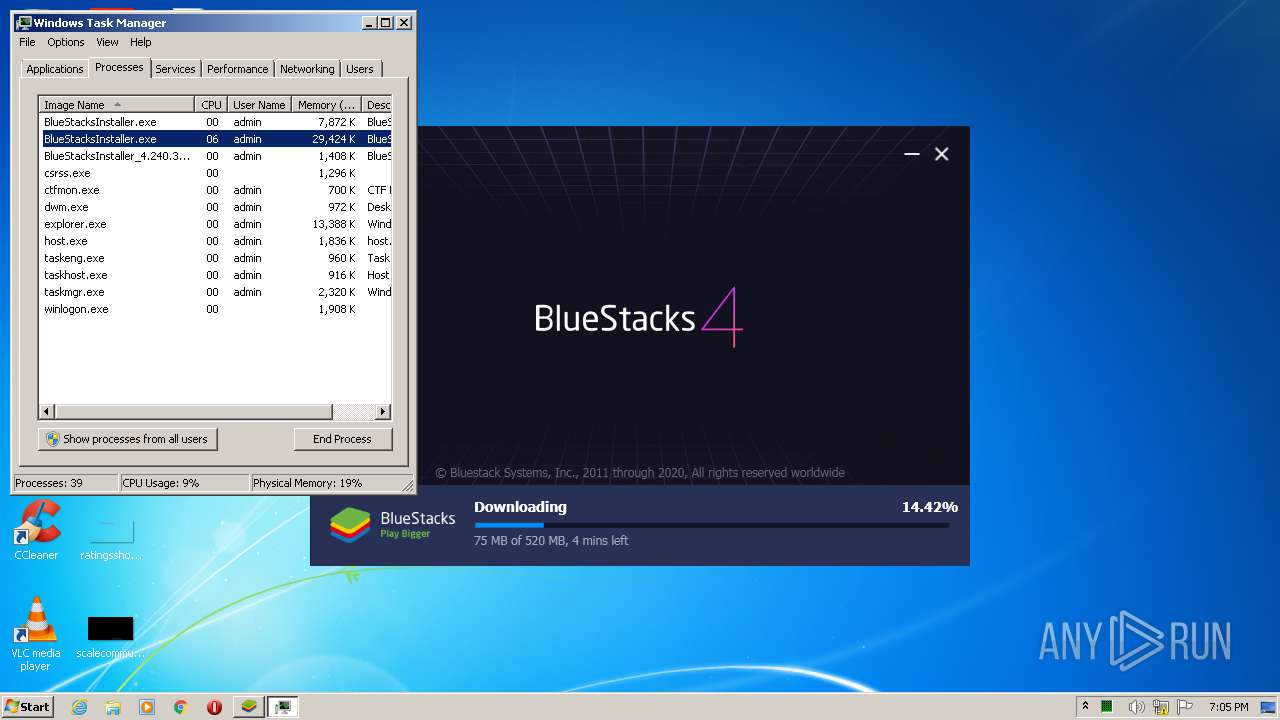
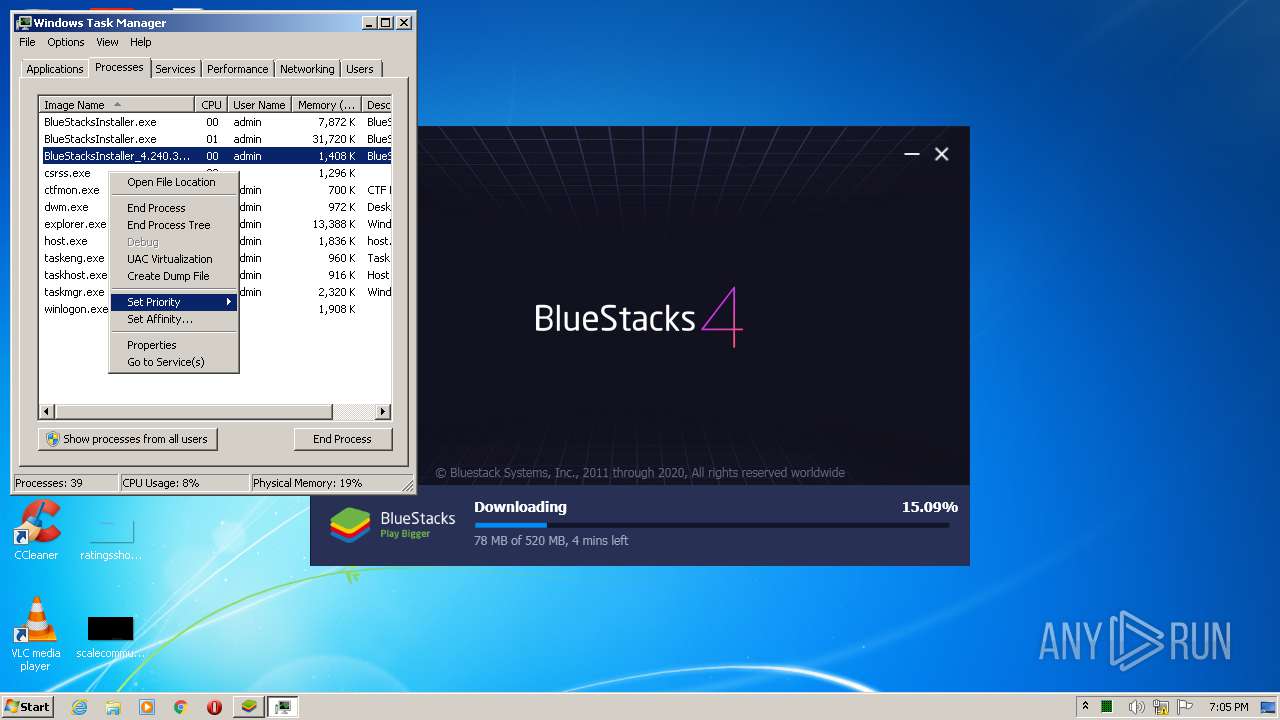
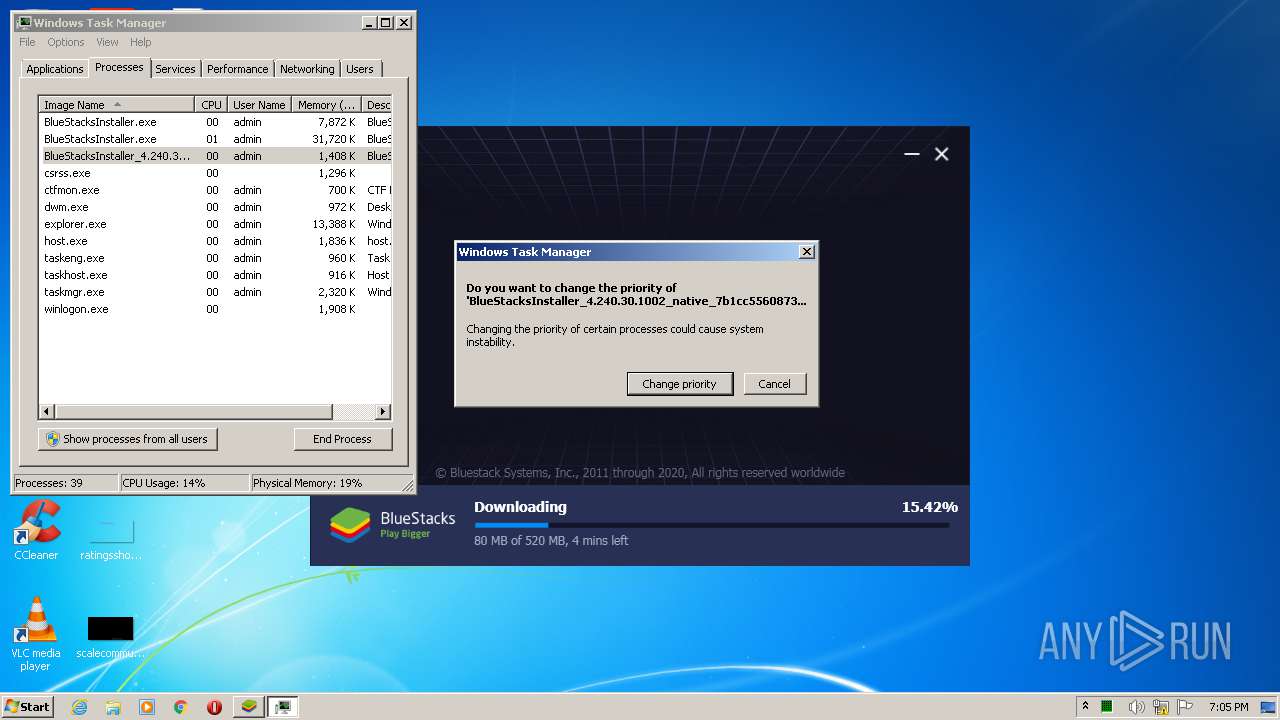
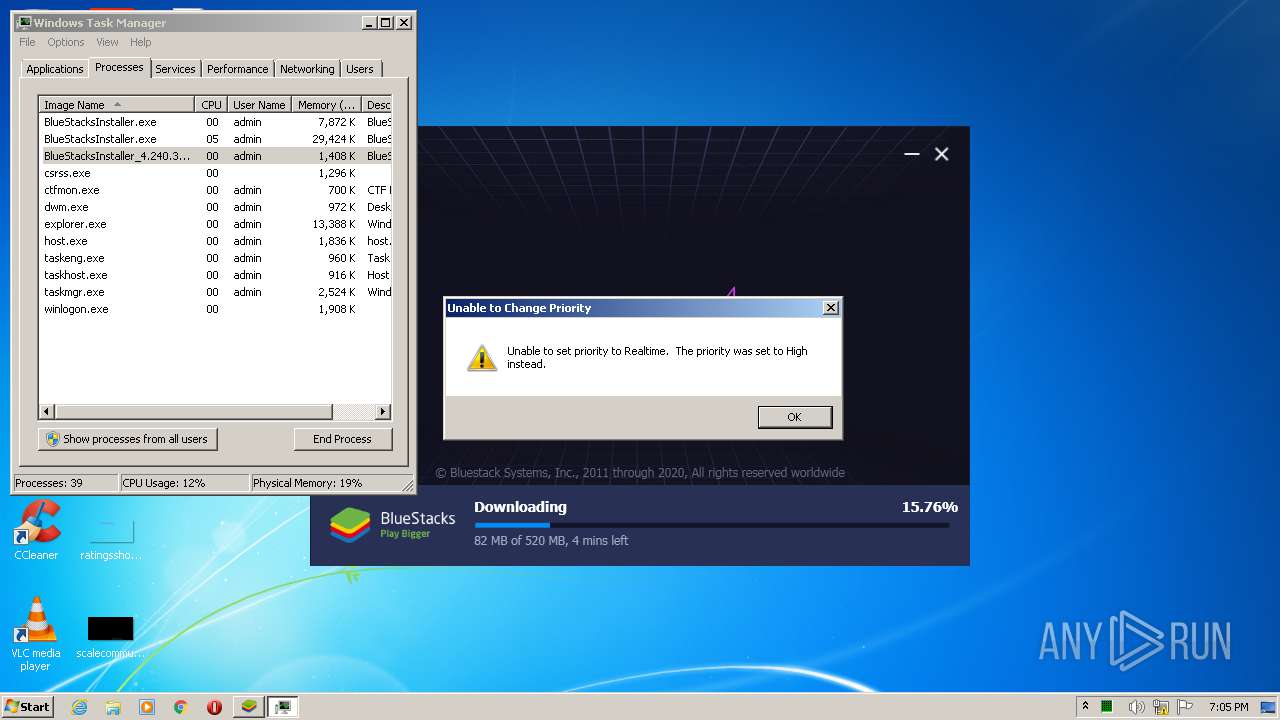
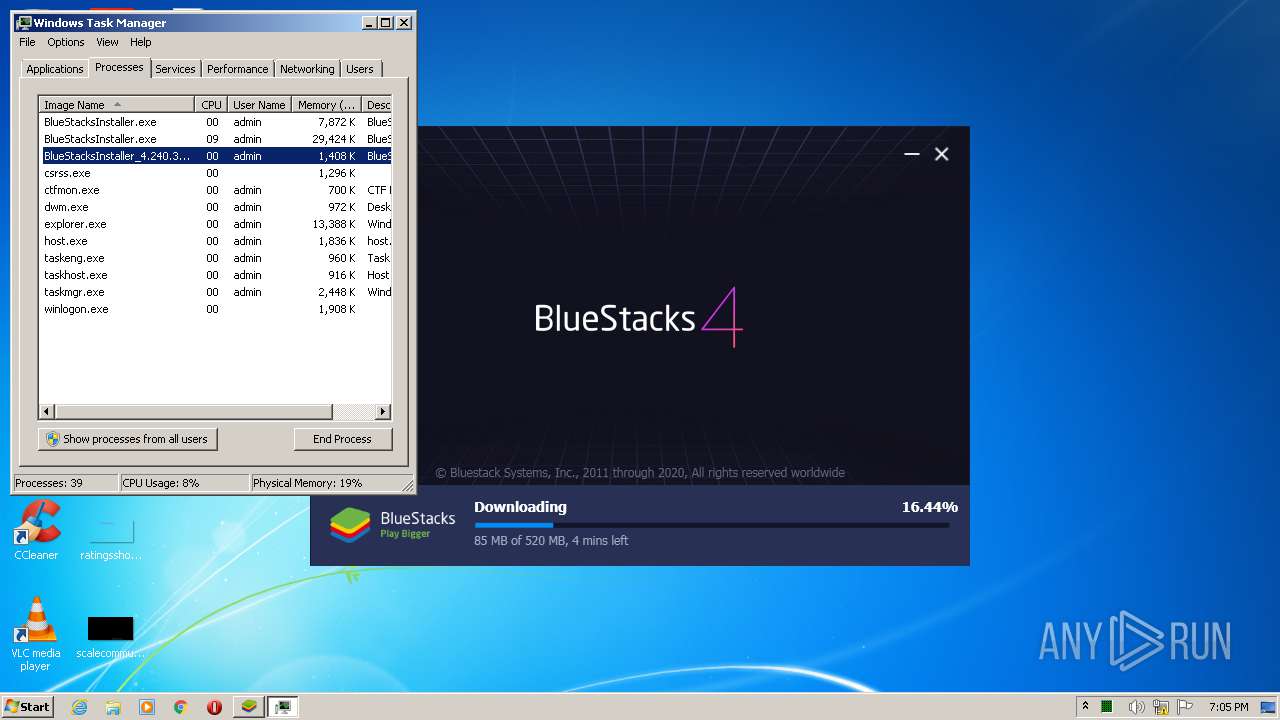
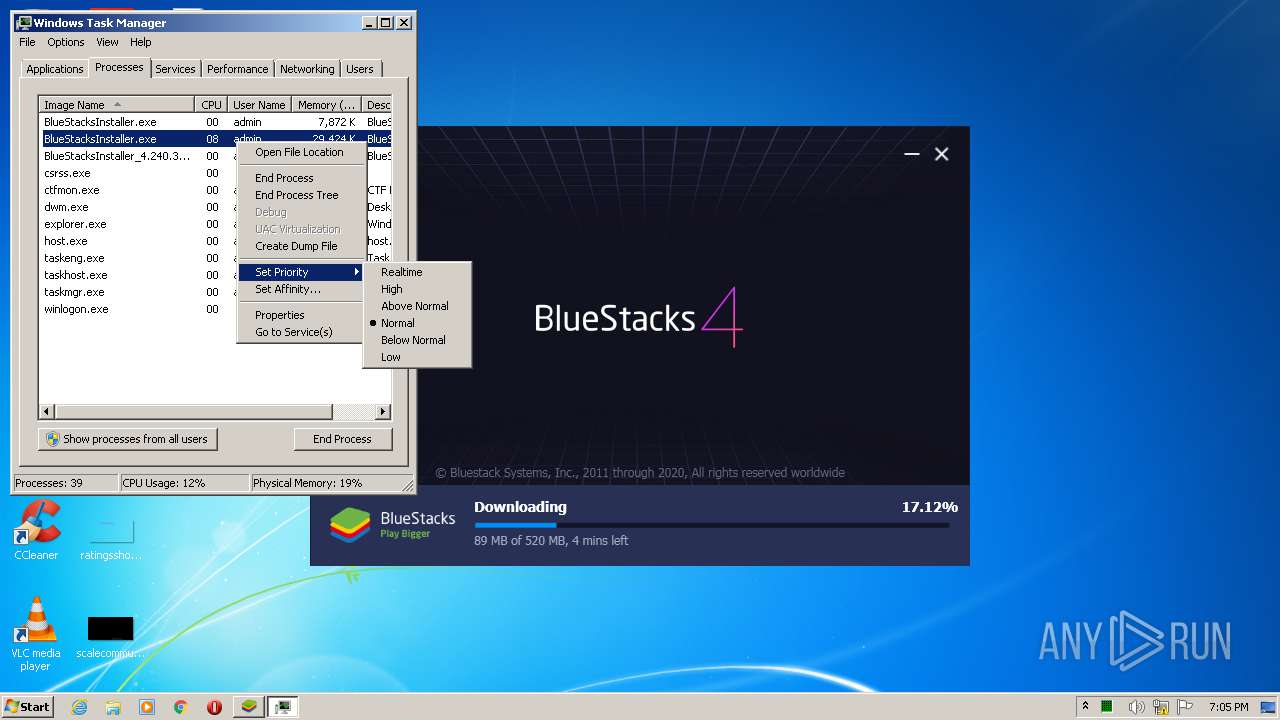
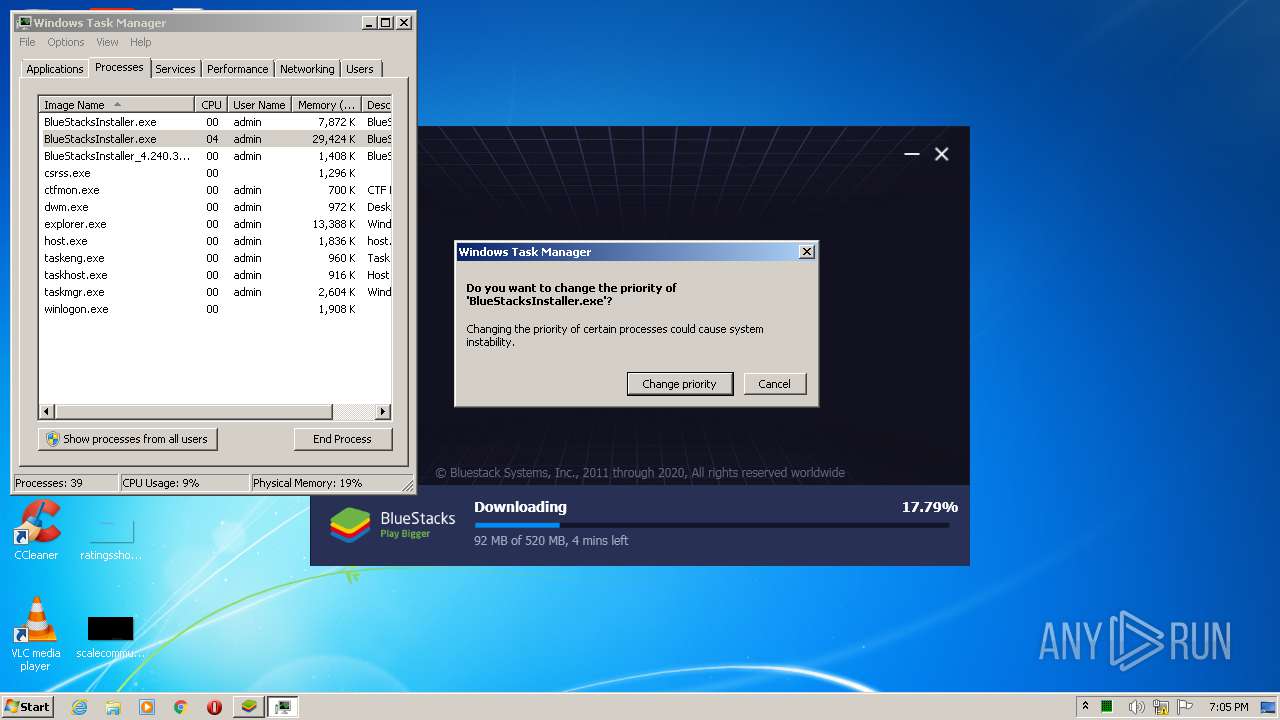
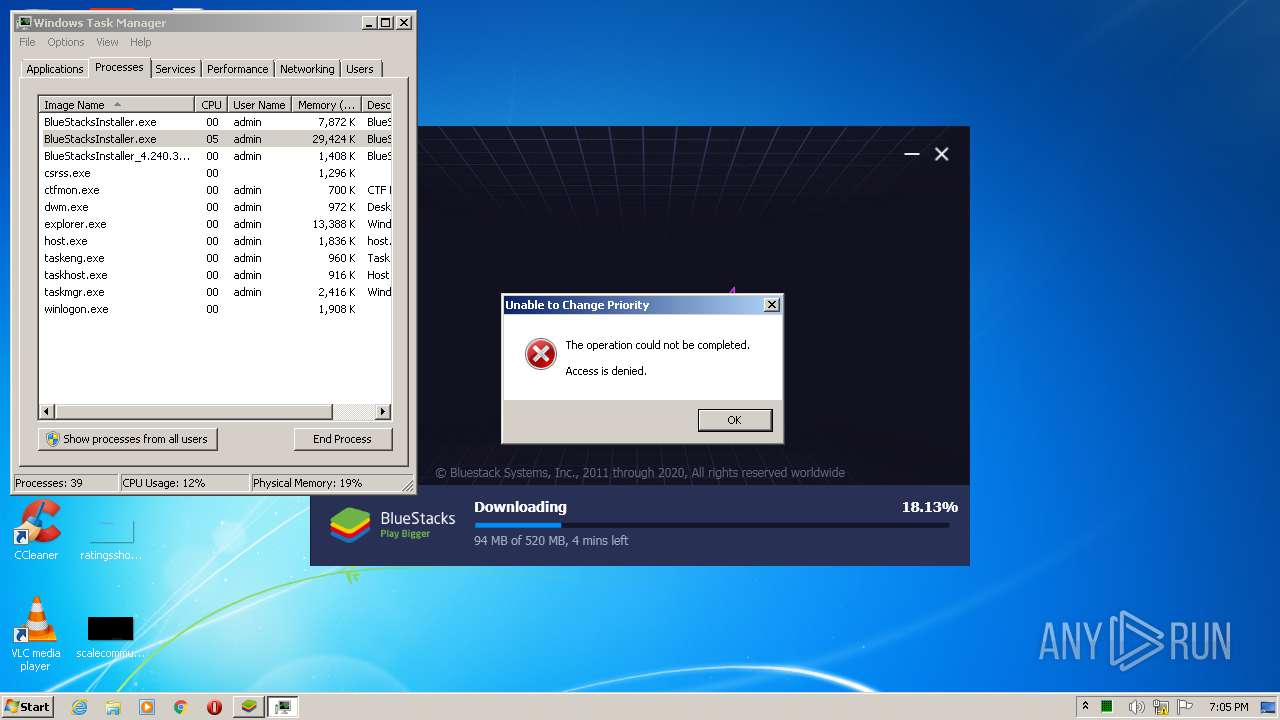
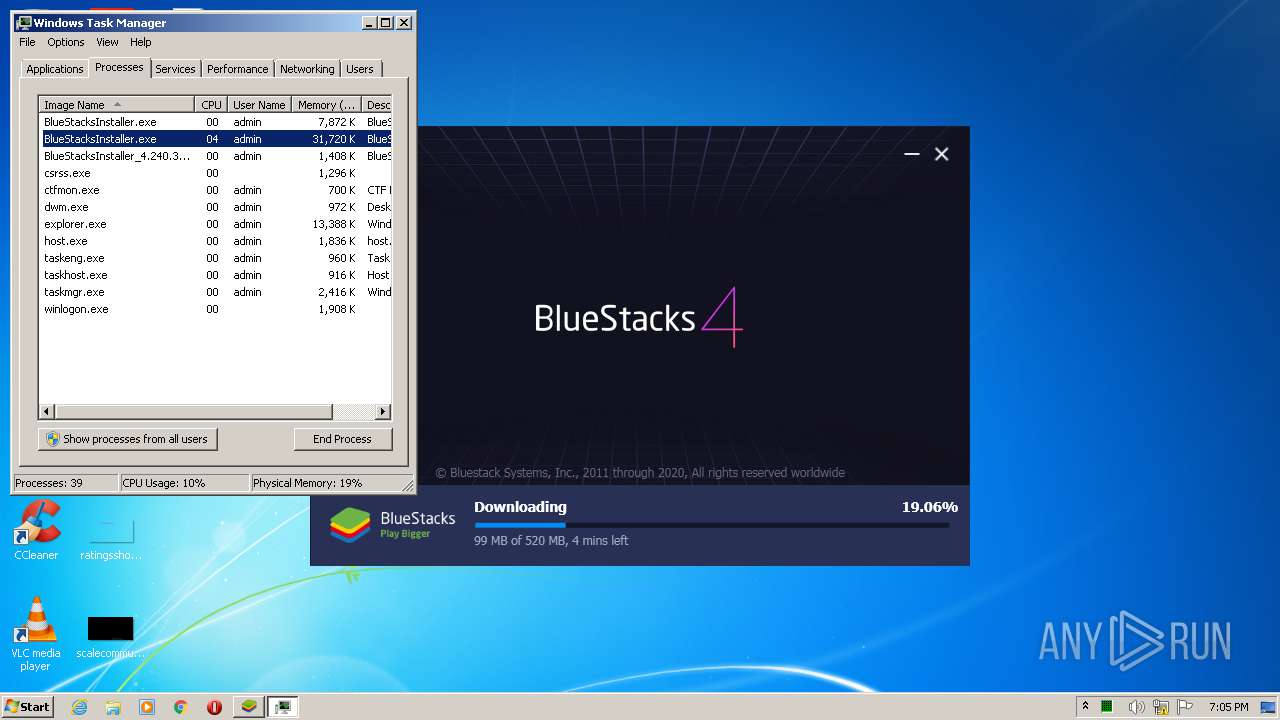
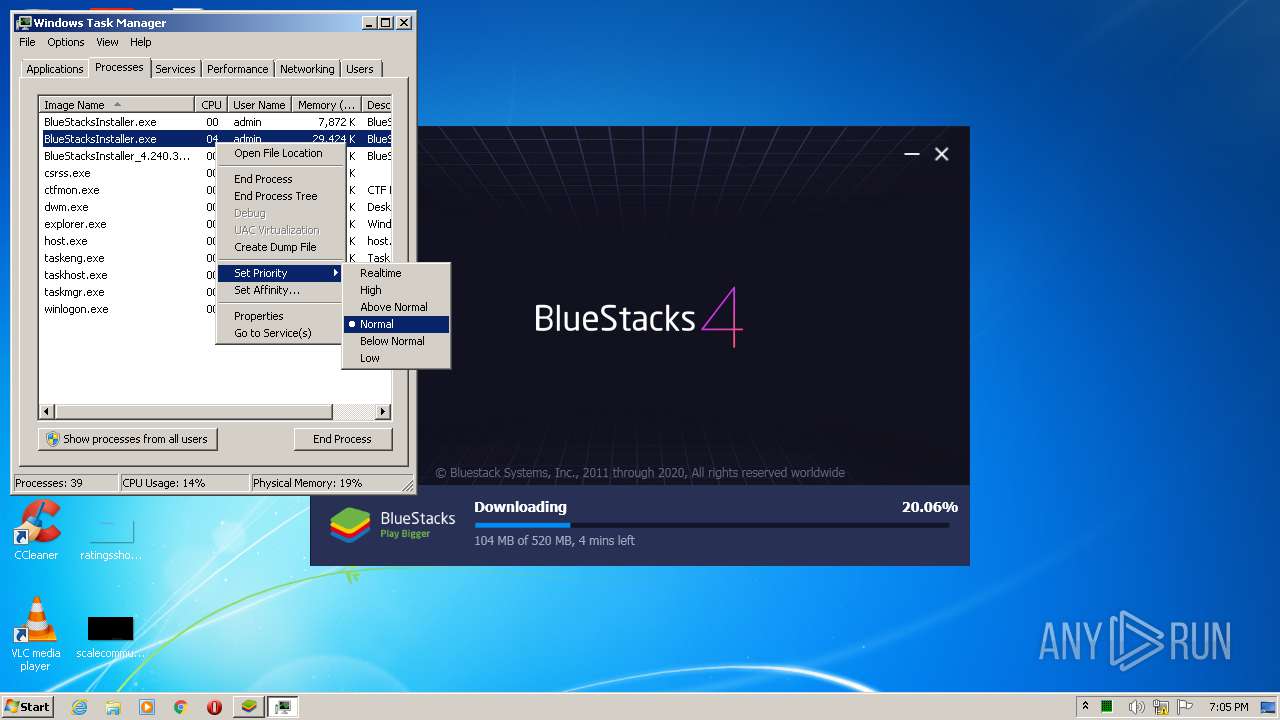
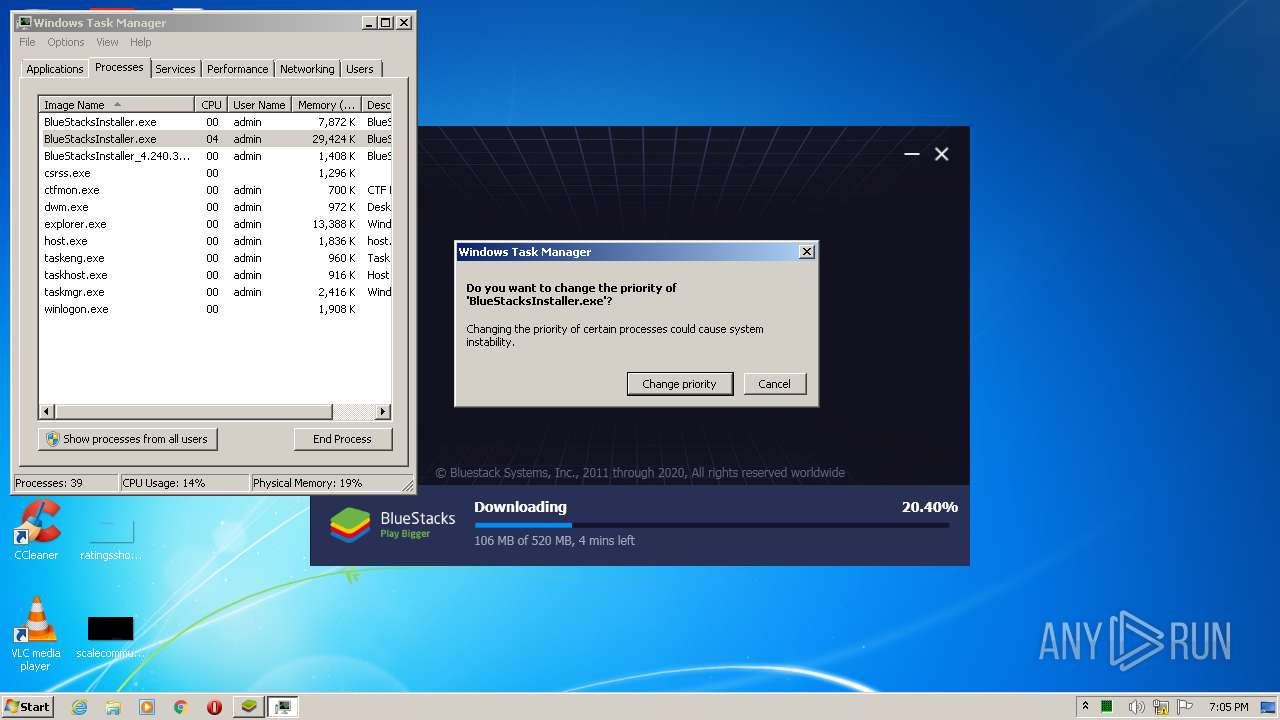
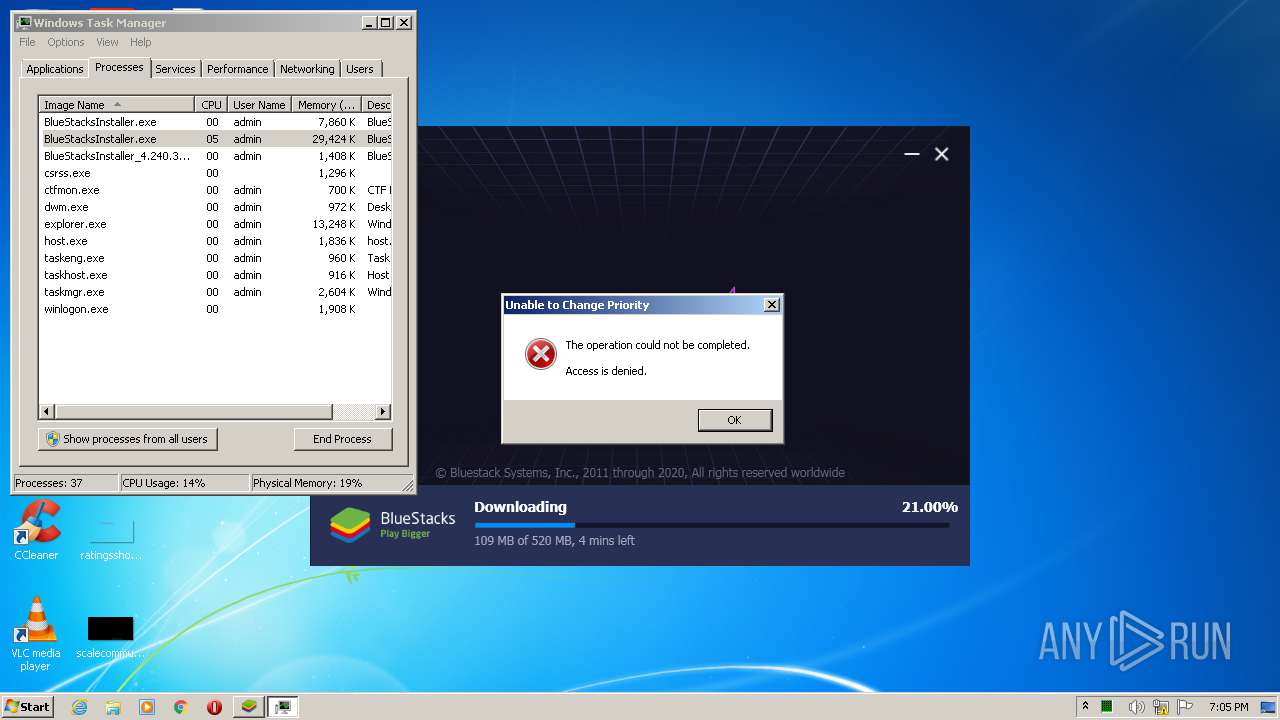
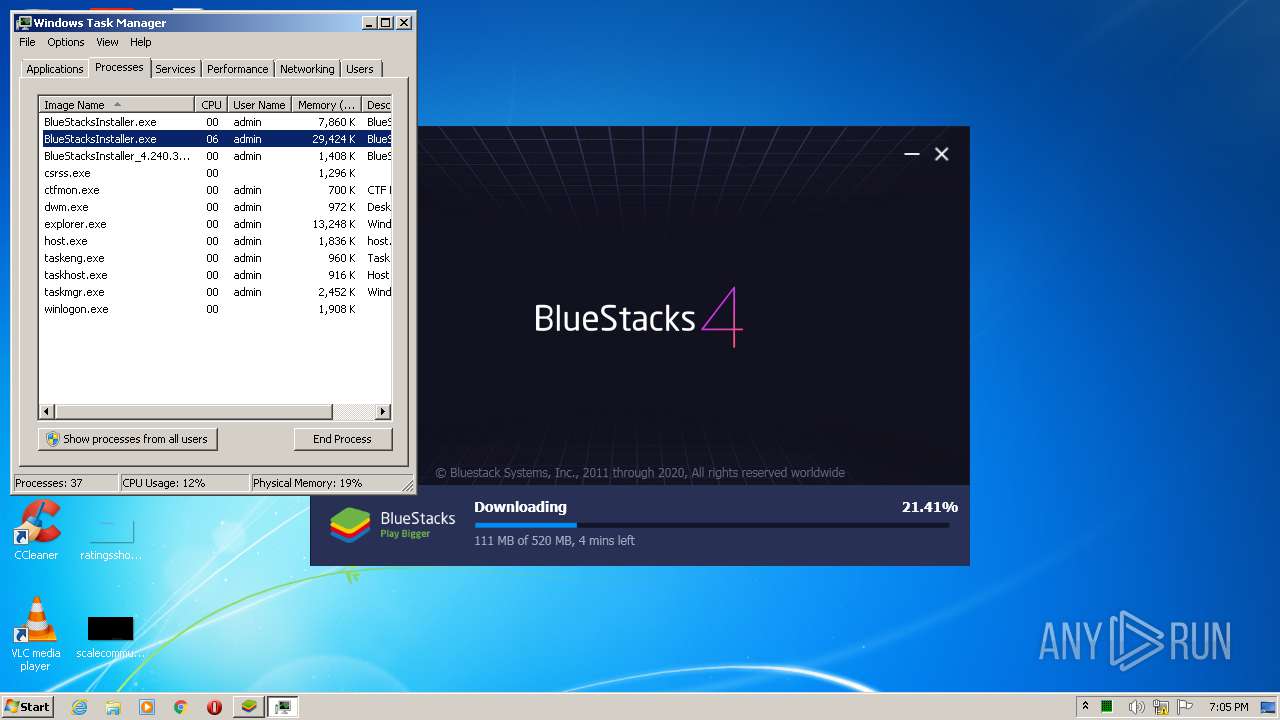
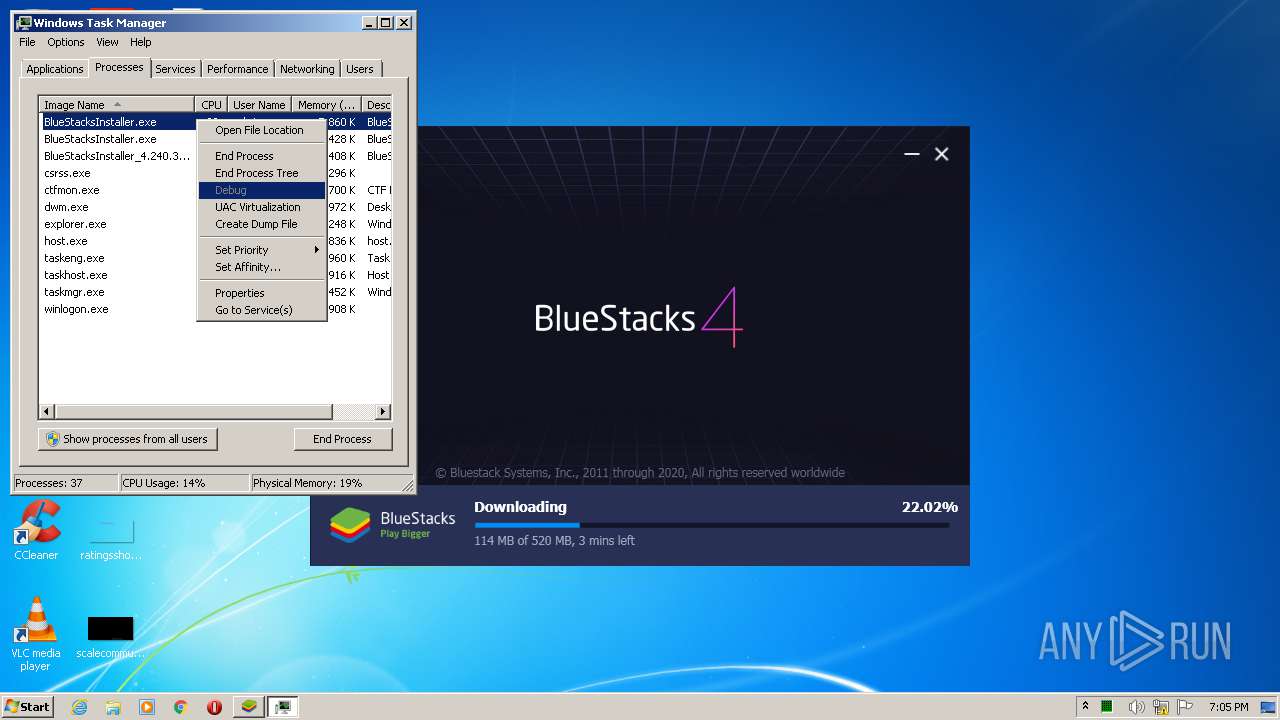
- taskmgr.exe (PID: 1392)
Adds / modifies Windows certificates
- BlueStacksInstaller.exe (PID: 2752)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3628)
INFO
Manual execution by user
- chrome.exe (PID: 3628)
- taskmgr.exe (PID: 1392)
- rundll32.exe (PID: 1780)
- rundll32.exe (PID: 3100)
- rundll32.exe (PID: 3248)
- rundll32.exe (PID: 1616)
- rundll32.exe (PID: 4076)
- rundll32.exe (PID: 2948)
Application launched itself
- chrome.exe (PID: 3628)
Reads the hosts file
- chrome.exe (PID: 3628)
- chrome.exe (PID: 3028)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3028)
Reads settings of System Certificates
- chrome.exe (PID: 3628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:21 17:00:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 104448 |
| InitializedDataSize: | 372224 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1910c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.0.0.0 |
| ProductVersionNumber: | 19.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
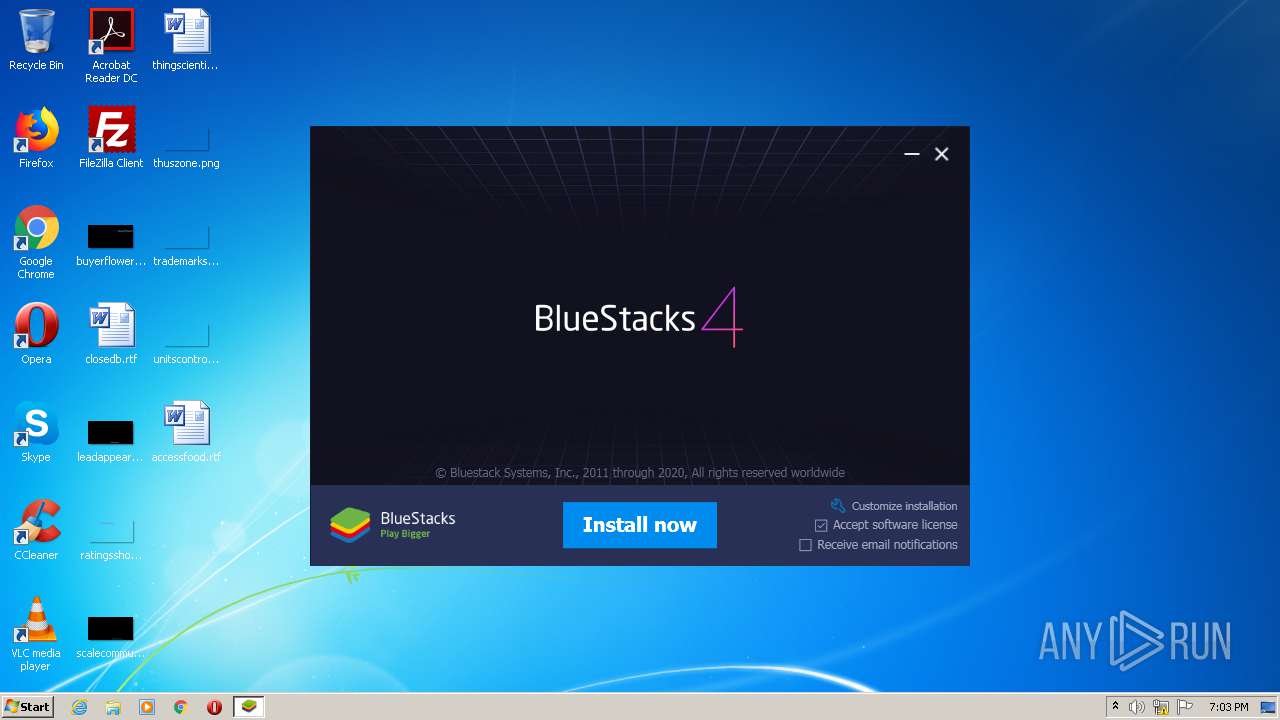
| CompanyName: | BlueStack Systems Inc. |
| FileDescription: | BlueStacks Installer |
| FileVersion: | 4 |
| InternalName: | BlueStacks Installer |
| LegalCopyright: | Copyright (c) BlueStack Systems Inc. |
| OriginalFileName: | BlueStacksInstaller.exe |
| ProductName: | BlueStacks Installer |
| ProductVersion: | 4 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Feb-2019 16:00:00 |
| Detected languages: |
|
| CompanyName: | BlueStack Systems Inc. |
| FileDescription: | BlueStacks Installer |
| FileVersion: | 4.00 |
| InternalName: | BlueStacks Installer |
| LegalCopyright: | Copyright (c) BlueStack Systems Inc. |
| OriginalFilename: | BlueStacksInstaller.exe |
| ProductName: | BlueStacks Installer |
| ProductVersion: | 4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Feb-2019 16:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00019745 | 0x00019800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63014 |
.rdata | 0x0001B000 | 0x00003A98 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39319 |
.data | 0x0001F000 | 0x000023F0 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.30023 |
.sxdata | 0x00022000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00023000 | 0x00056DB0 | 0x00056E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.08403 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02012 | 659 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.12778 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.47733 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.77612 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.18496 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
97 | 2.93146 | 144 | Latin 1 / Western European | English - United States | RT_DIALOG |
188 | 2.17822 | 84 | Latin 1 / Western European | English - United States | RT_STRING |
207 | 2.4279 | 108 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
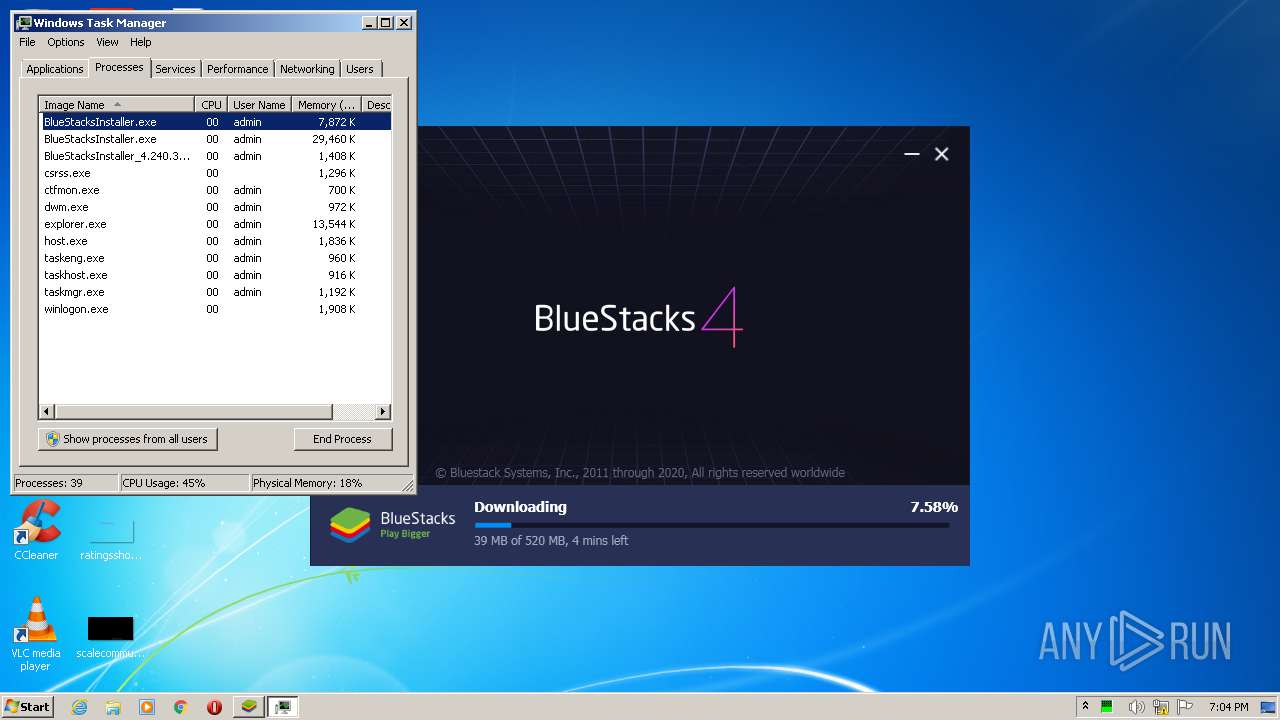
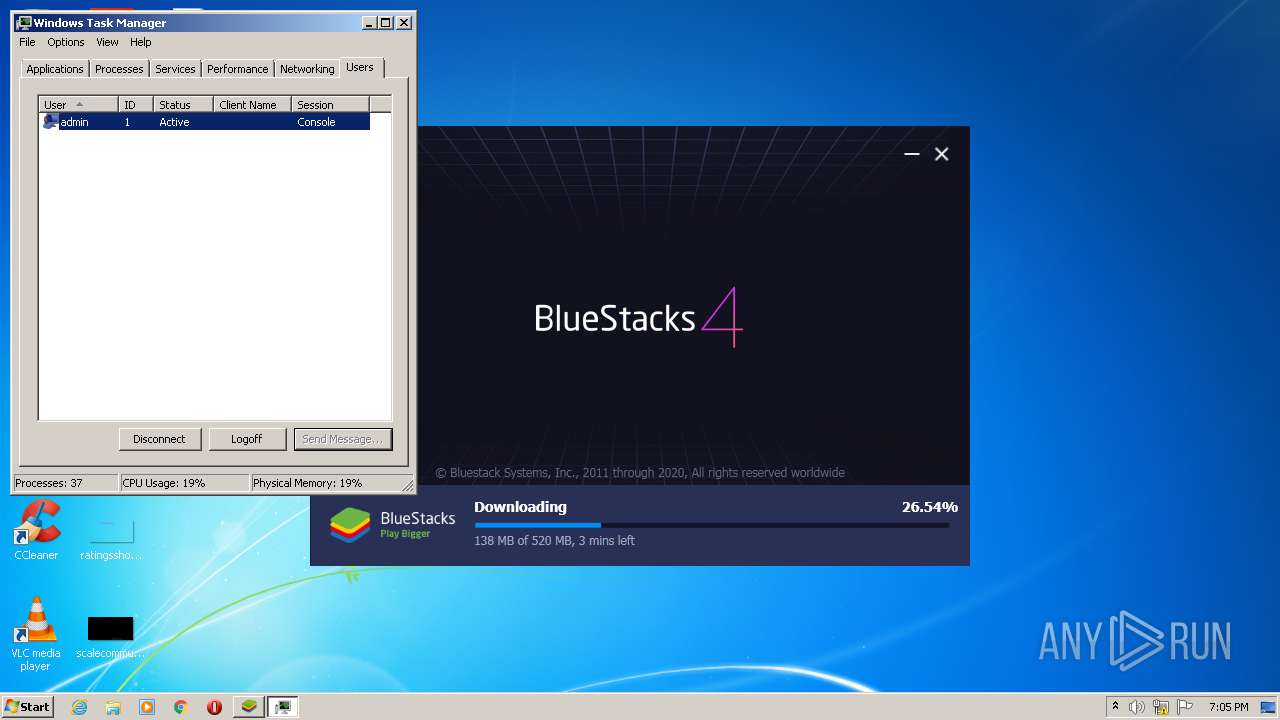
Total processes
97
Monitored processes
52
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8148611532721311529,16159575251196318888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=727735082713039528 --mojo-platform-channel-handle=2548 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8148611532721311529,16159575251196318888,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8058907739387316890 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,8148611532721311529,16159575251196318888,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2929283873064578727 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8148611532721311529,16159575251196318888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15845923924118845660 --mojo-platform-channel-handle=3872 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
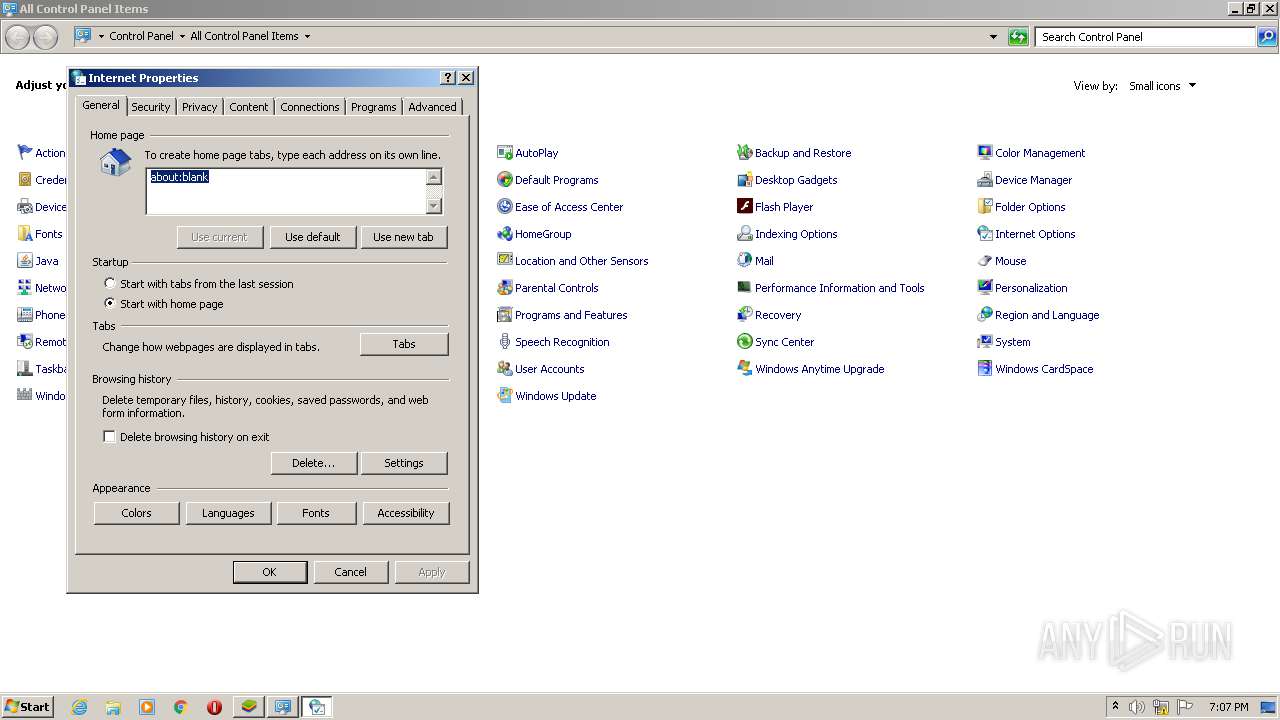
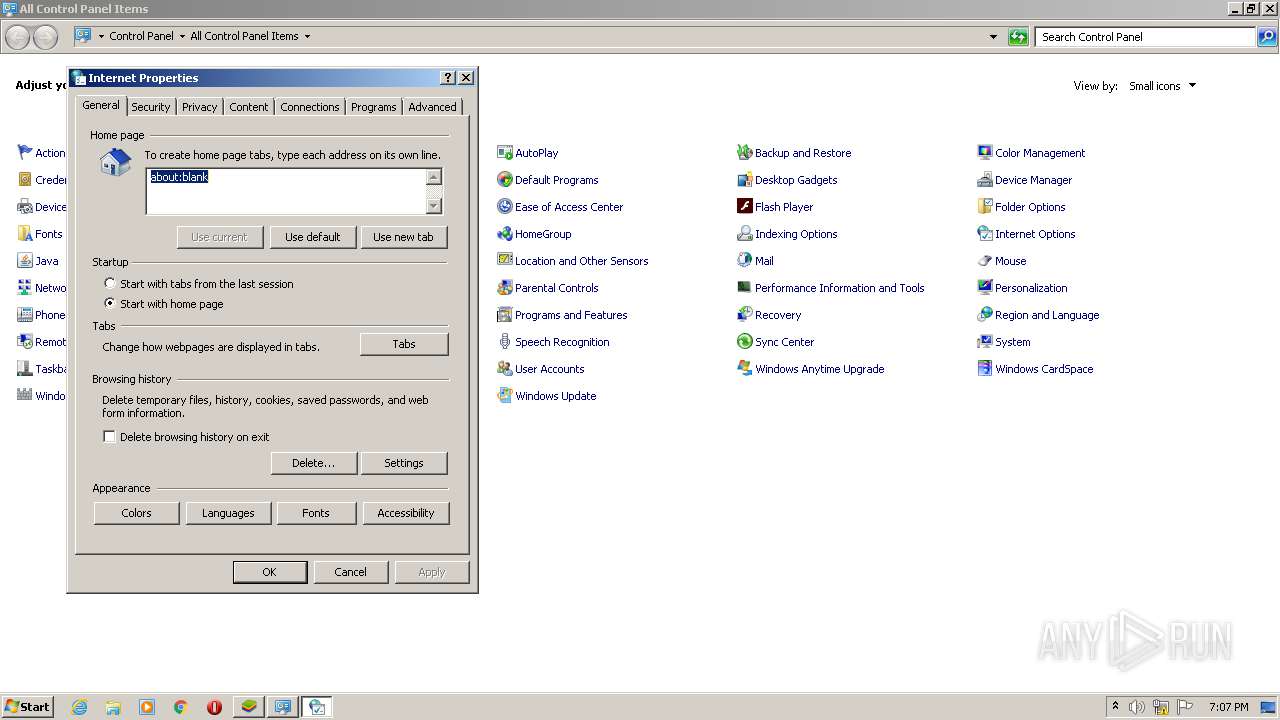
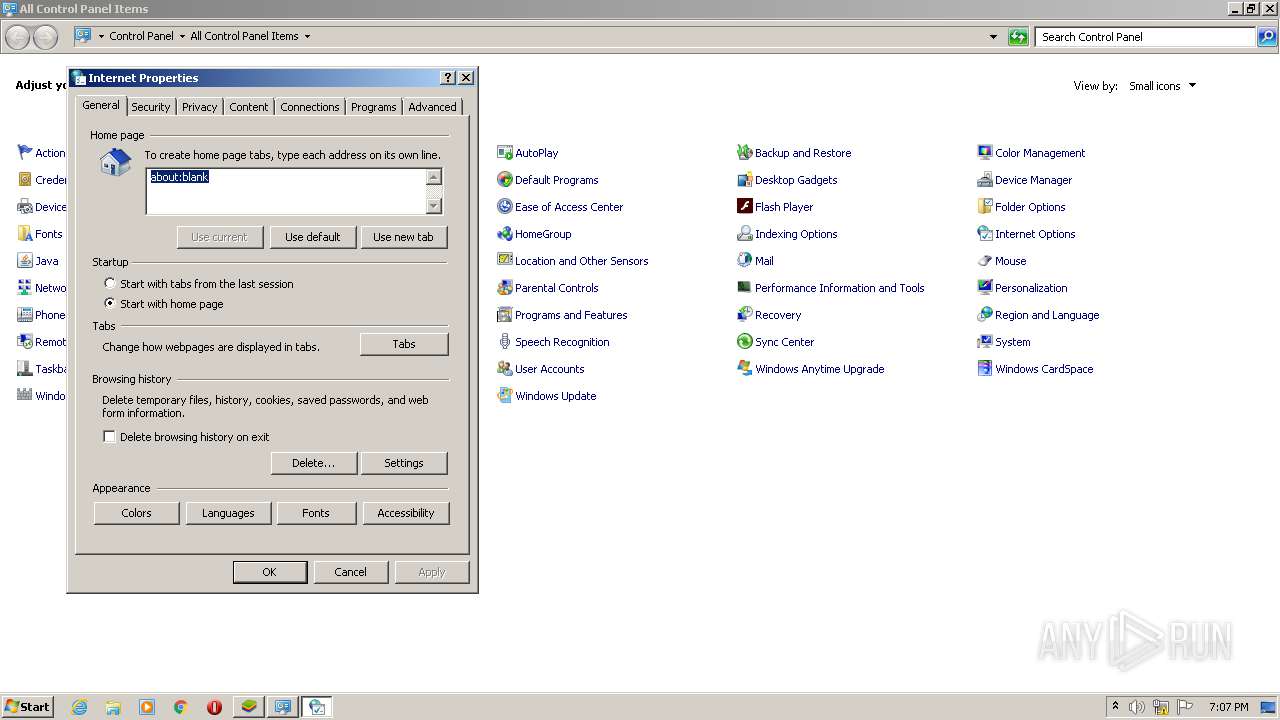
| 1616 | "C:\Windows\System32\rundll32.exe" C:\Windows\System32\shell32.dll,Control_RunDLL C:\Windows\System32\inetcpl.cpl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8148611532721311529,16159575251196318888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14368532708231253905 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,8148611532721311529,16159575251196318888,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13627712254095674608 --mojo-platform-channel-handle=4208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Windows\System32\rundll32.exe" C:\Windows\System32\shell32.dll,Control_RunDLL C:\Windows\System32\inetcpl.cpl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6c3fa9d0,0x6c3fa9e0,0x6c3fa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 465
Read events
3 267
Write events
193
Delete events
5
Modification events
| (PID) Process: | (2216) BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2216) BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_CURRENT_USER\Software\BlueStacksInstaller |
| Operation: | write | Name: | MachineID |
Value: 7313f563-0777-47e0-97eb-365f27ea5c1d | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_CURRENT_USER\Software\BlueStacksInstaller |
| Operation: | write | Name: | VersionMachineId_4.240.30.1002 |
Value: 34336652-4f8f-4937-a801-46f9b3973a7e | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BlueStacksInstaller_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BlueStacksInstaller_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BlueStacksInstaller_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BlueStacksInstaller_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BlueStacksInstaller_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2444) BlueStacksInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\BlueStacksInstaller_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
14
Suspicious files
89
Text files
336
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\BlueStacksInstaller.exe.config | xml | |
MD5:1B456D88546E29F4F007CD0BF1025703 | SHA256:D6D316584B63BB0D670A42F88B8F84E0DE0DB4275F1A342084DC383EBEB278EB | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.ar-IL.txt | text | |
MD5:9FB07E066CC2F213A64D35A97A8C2922 | SHA256:65E7B0F37B5E2AA805AC8D57969804D803430186F34E9703CA9FA09BA908EF90 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.en-US.txt | text | |
MD5:5D54C2B742889FE07B2C511A5D4A7693 | SHA256:F96CA4B320975C5F4B2C935F891CDCE12C8B9411614F3DB902023BE0428F549C | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.es-ES.txt | text | |
MD5:FB1819935E7031AA26CD5363D7FB06C0 | SHA256:12723B04B25736B4BA25D613DCCEE05E1EACD1DAC42DA75C497C84BE3B9355A2 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.pl-PL.txt | text | |
MD5:04E2A3F627E040985A0E80EC5E206306 | SHA256:CB601A100536A2E3C71CDC2CBBD4DB220C1787EFA8888FEC04CE3F2B982C5C27 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.ar-EG.txt | text | |
MD5:1B19F0DAF118F03B79C30FB22BDA884E | SHA256:EF08D46EAA87A179B56E3327BB65878F902446CC2BF419FA661F941962D5F1C5 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.de-DE.txt | text | |
MD5:0B733F60C9AF585C1B5B94605E50E862 | SHA256:BBE1237766E1B71181DD5052FFA2C45F457B0E351E0816C1C66624E052B43853 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.it-IT.txt | text | |
MD5:023A31D90379612D98521B53FBD7436E | SHA256:94CAB09EB0B4B6A648F1B3C149792881D884419386FEDE8F0FEFA85D3BA4A269 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.fr-FR.txt | text | |
MD5:568830BFD78398A1596E14B95E58AE5A | SHA256:6790DCEF71775352801721E2DB0146E676778E844BC6644FFA1DB0374F3AB4F2 | |||
| 2216 | BlueStacksInstaller_4.240.30.1002_native_51ccd2083bae0570102a4a87c2a2c3f2.exe | C:\Users\admin\AppData\Local\Temp\7zS8A82D6B5\Locales\i18n.pt-BR.txt | text | |
MD5:2684801FCE0B856F86B434D8EBB99057 | SHA256:61FC84CDE1719D0C927CC15C2EE5AD83CB292F36B1BEB072B473327A6F5C492B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
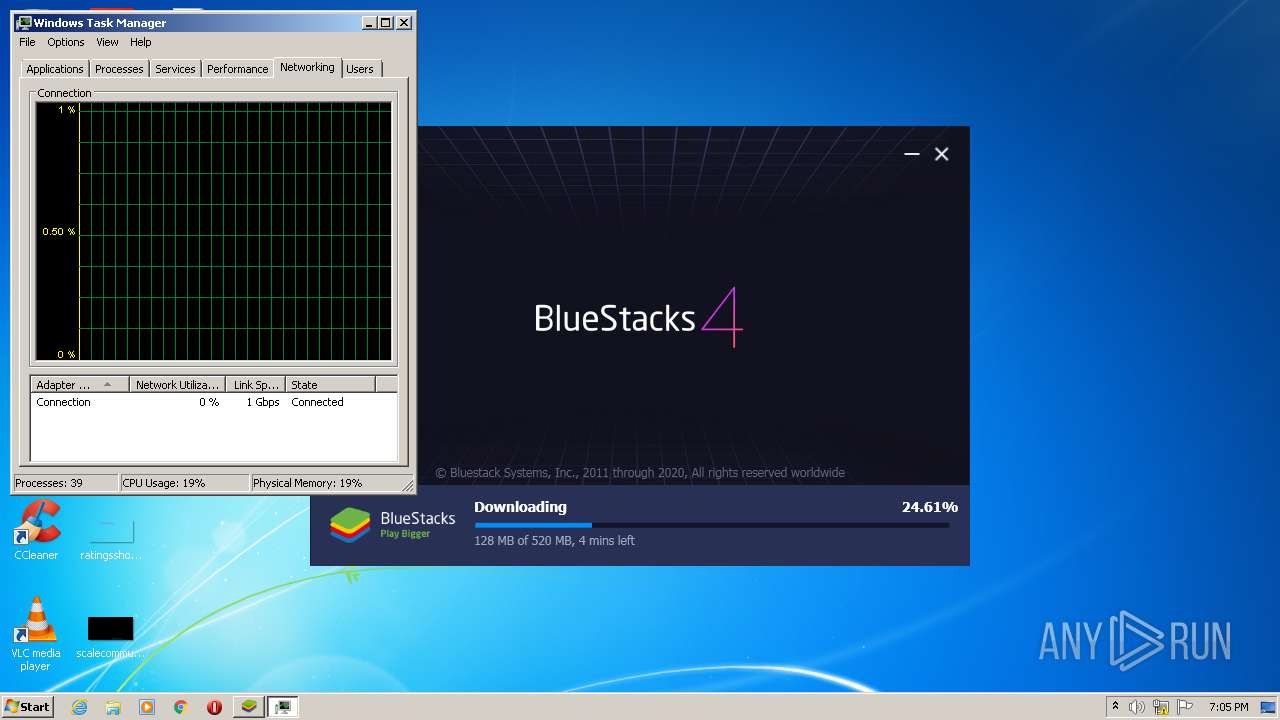
HTTP(S) requests
3
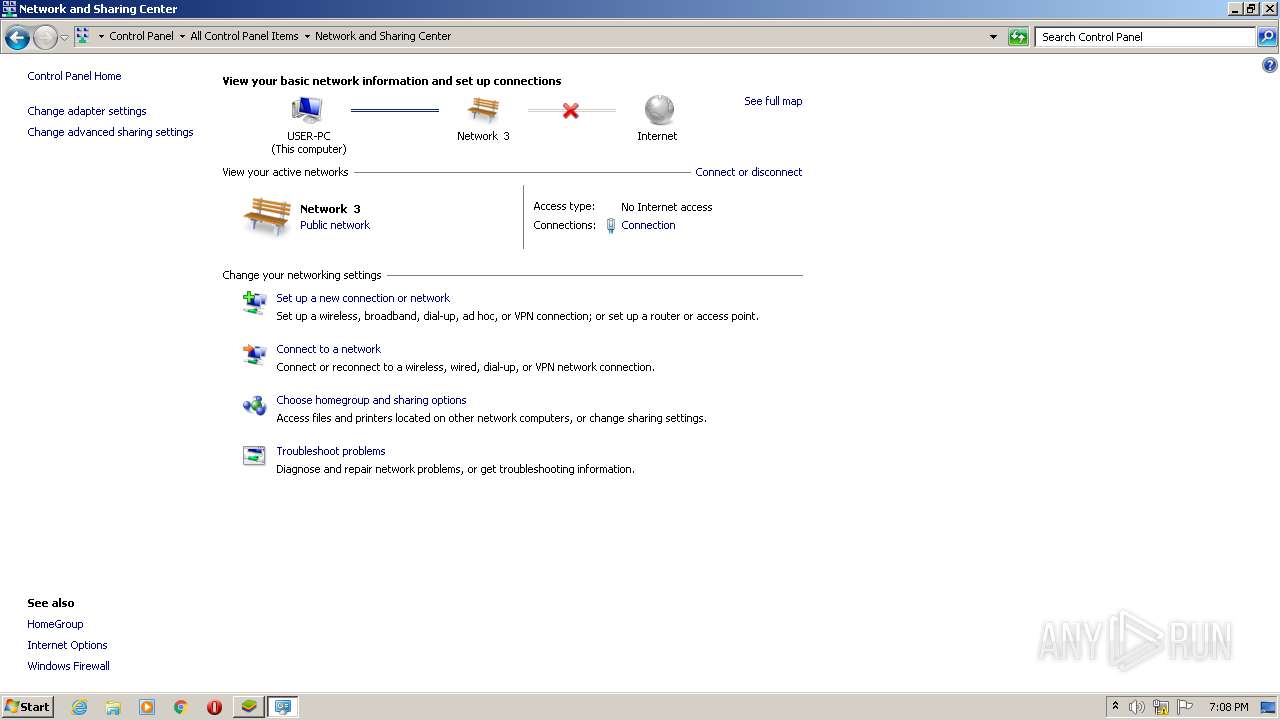
TCP/UDP connections
67
DNS requests
47
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
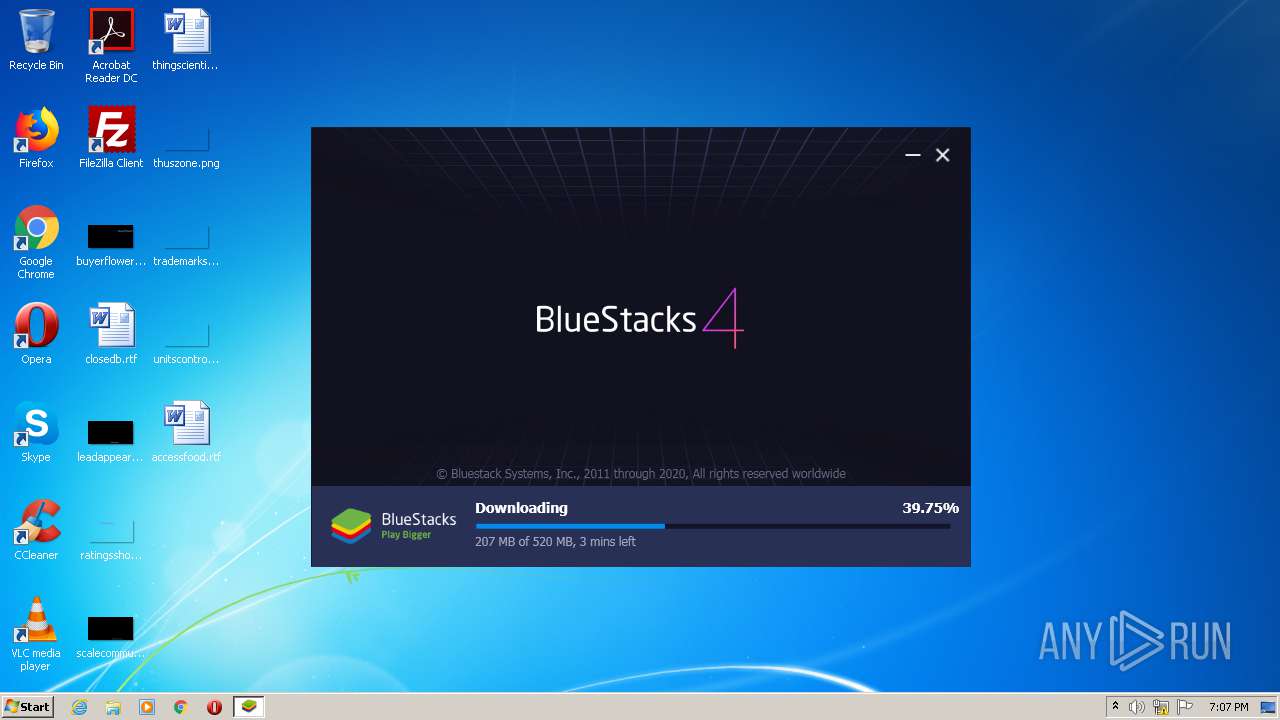
3156 | BlueStacksInstaller.exe | GET | — | 65.9.68.7:80 | http://cdn3.bluestacks.com/downloads/windows/bgp/4.240.30.1002/8c6ba9ef64cc2e5c31f0e855e519e5b3/x86/BlueStacks-Installer_4.240.30.1002_x86_native.exe?filename=BlueStacksInstaller_4.240.30.1002_native_7b1cc5560873b1d21fe43f0f3209510b.exe | US | — | — | shared |
3628 | chrome.exe | GET | 304 | 67.27.159.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
3628 | chrome.exe | GET | 200 | 67.27.159.126:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3028 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 172.217.22.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 172.217.23.163:443 | www.google.co.uk | Google Inc. | US | whitelisted |
2444 | BlueStacksInstaller.exe | 216.58.205.243:443 | cloud.bluestacks.com | Google Inc. | US | whitelisted |
2752 | BlueStacksInstaller.exe | 216.58.205.243:443 | cloud.bluestacks.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 216.58.212.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3028 | chrome.exe | 142.250.74.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cloud.bluestacks.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3156 | BlueStacksInstaller.exe | Potential Corporate Privacy Violation | AV POLICY HTTP request for .exe file with no User-Agent |
3156 | BlueStacksInstaller.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
3156 | BlueStacksInstaller.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3156 | BlueStacksInstaller.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |