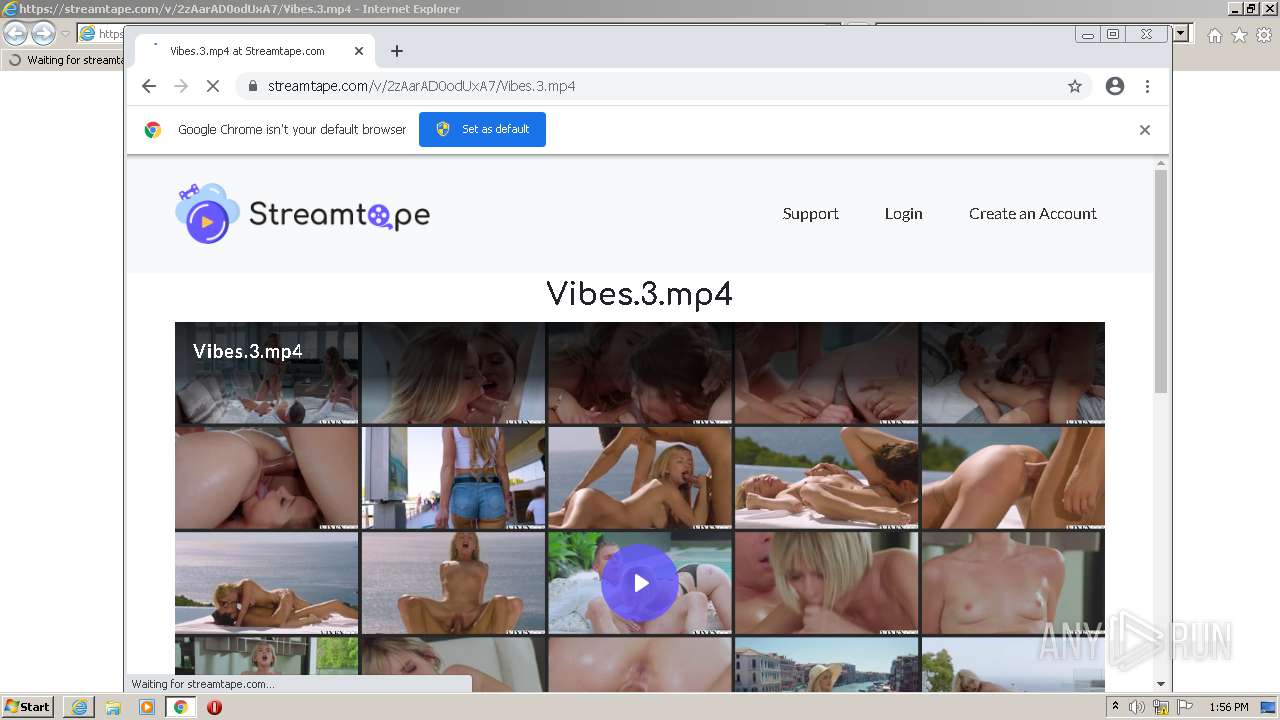
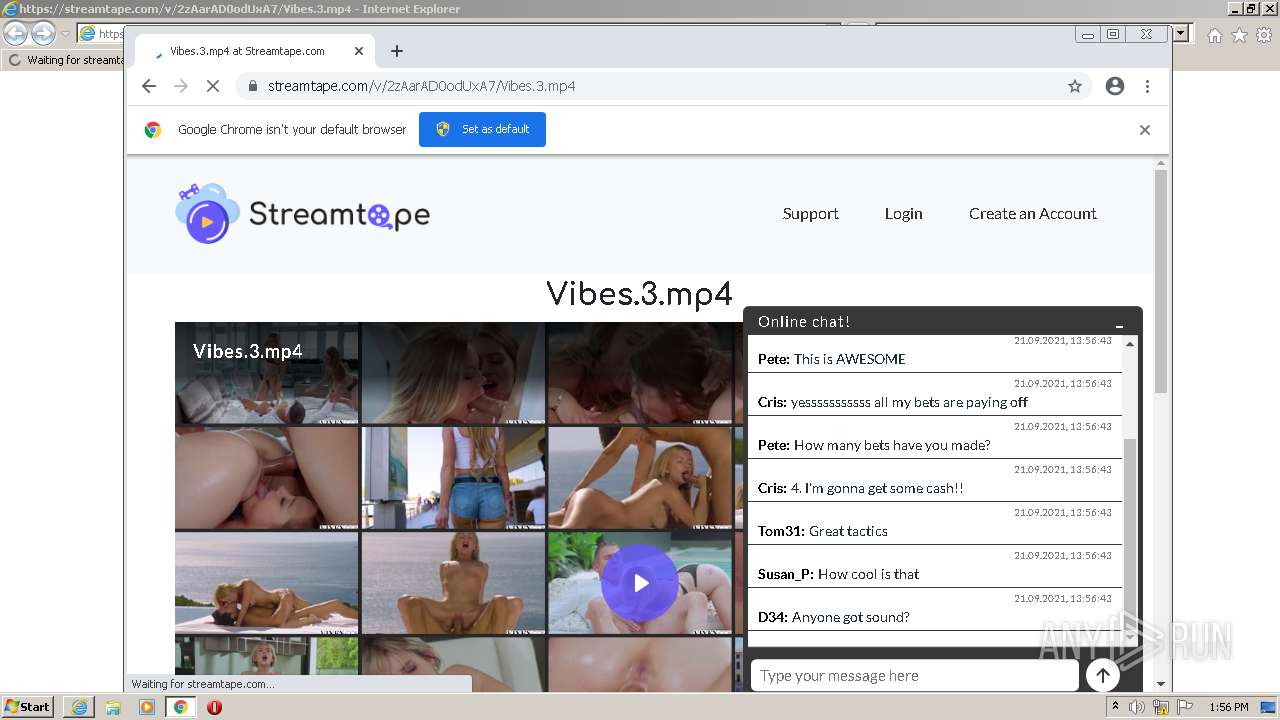
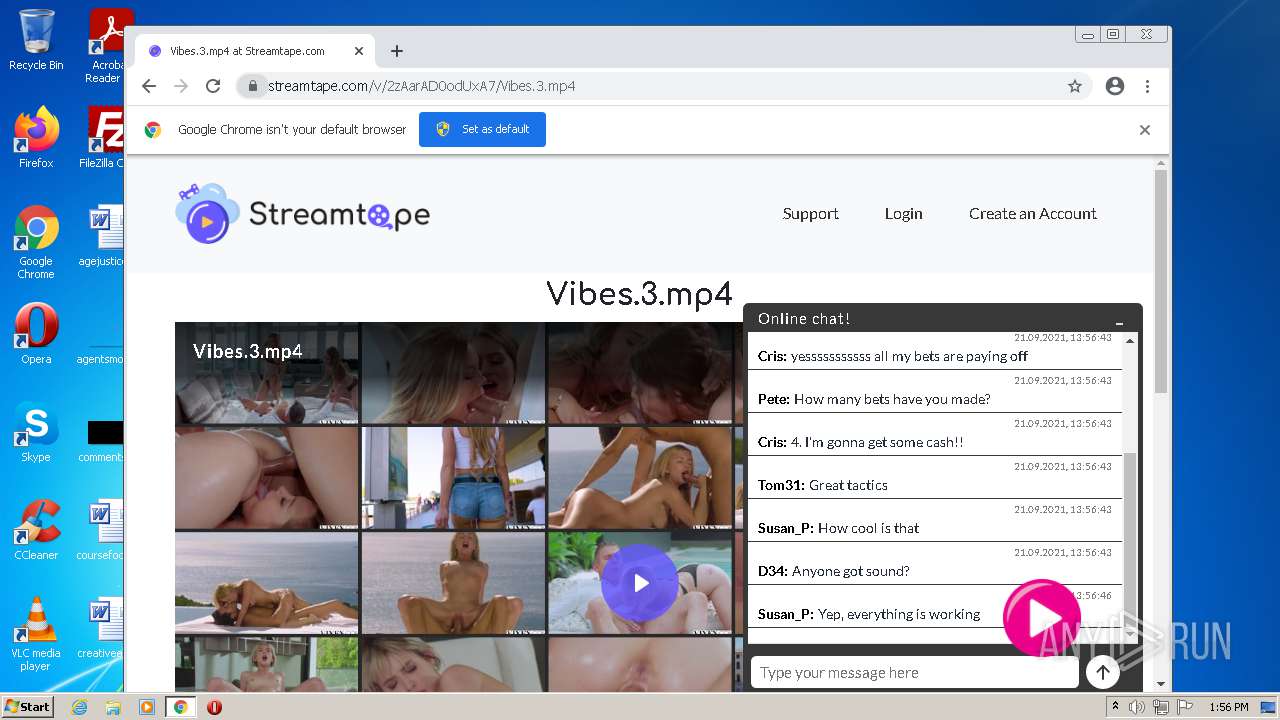
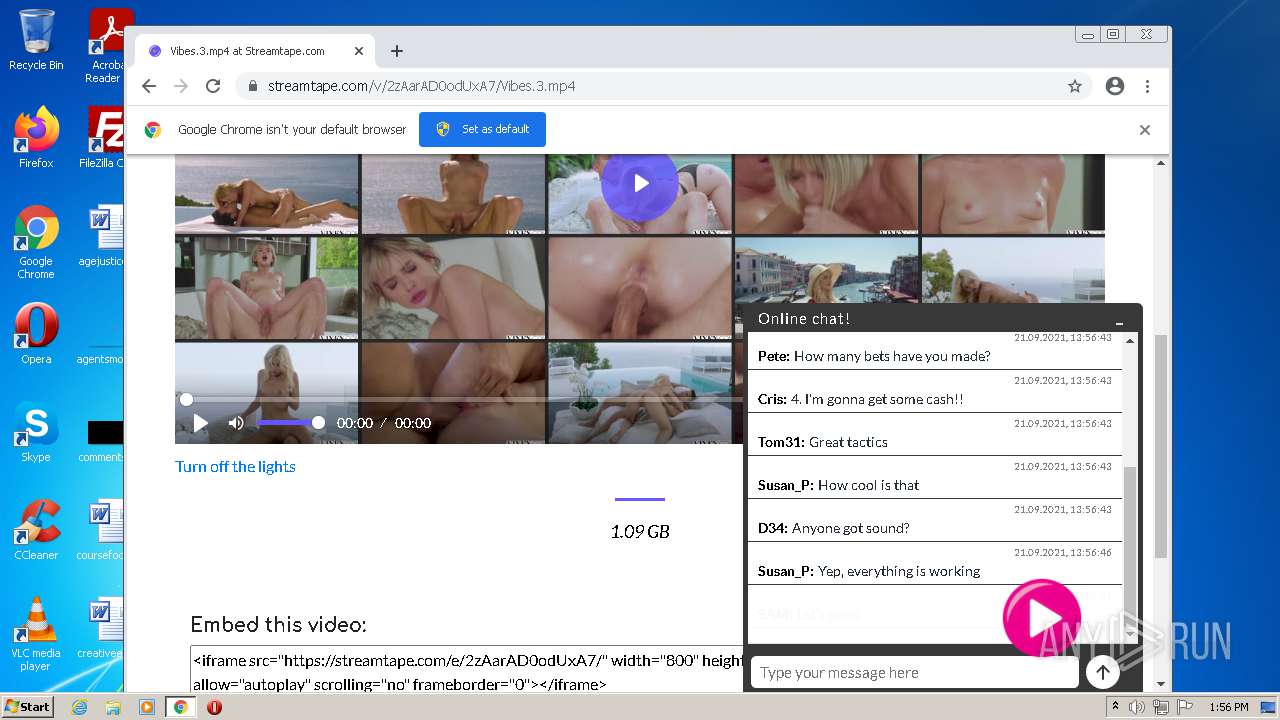
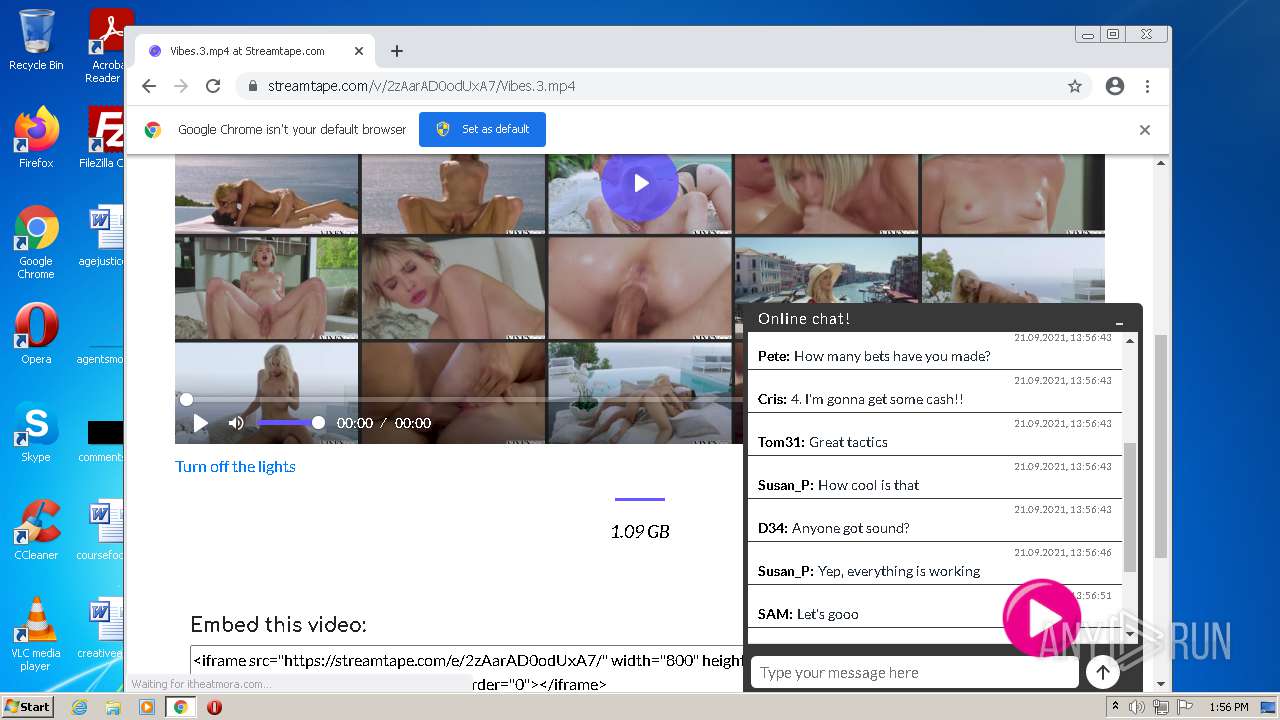
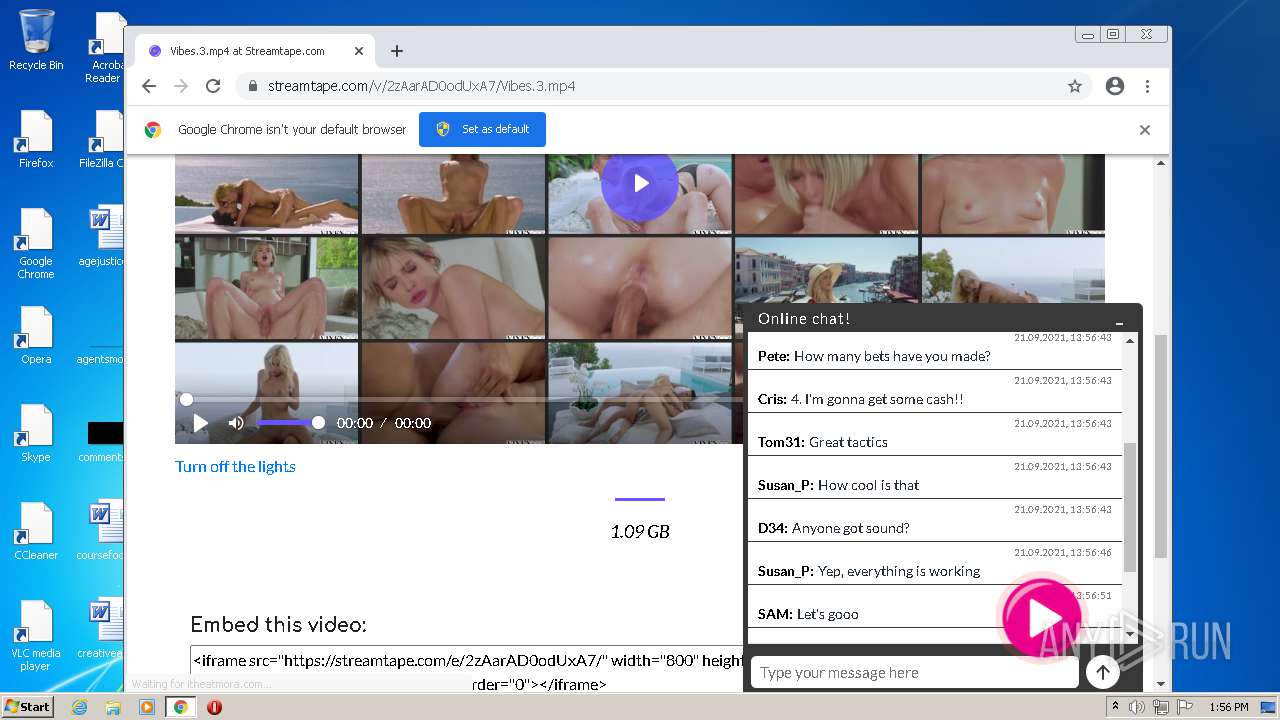
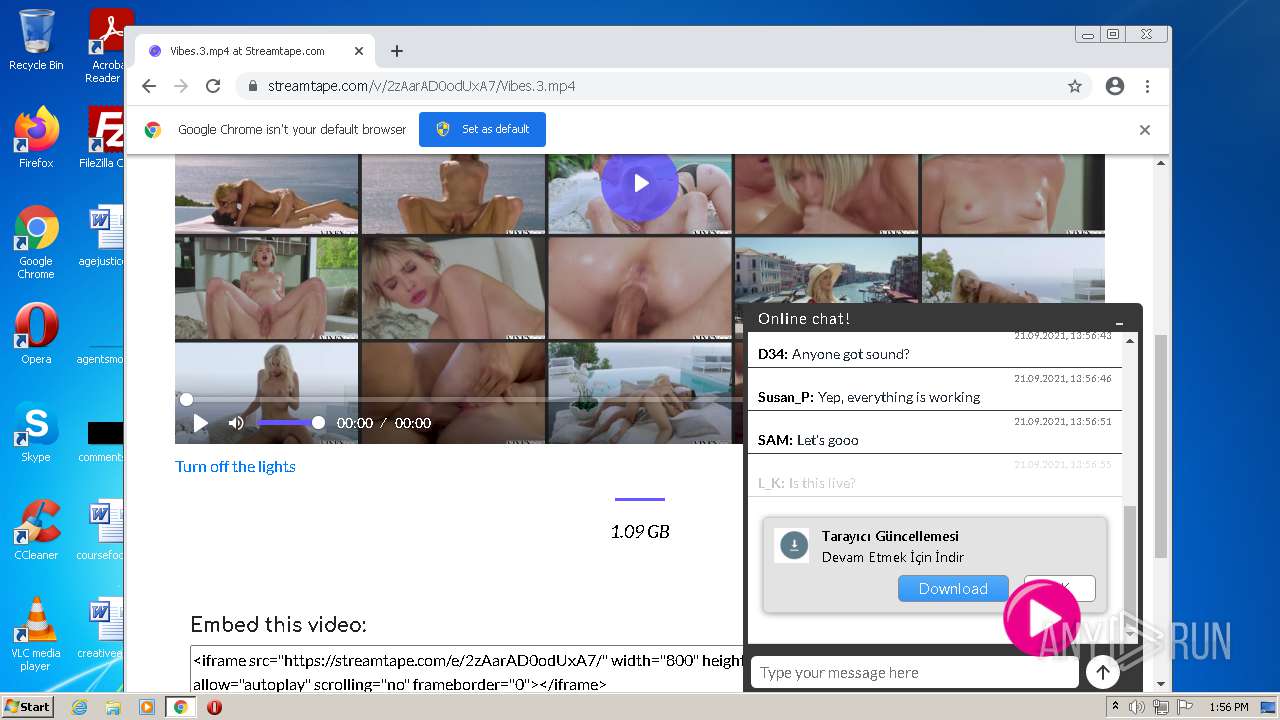
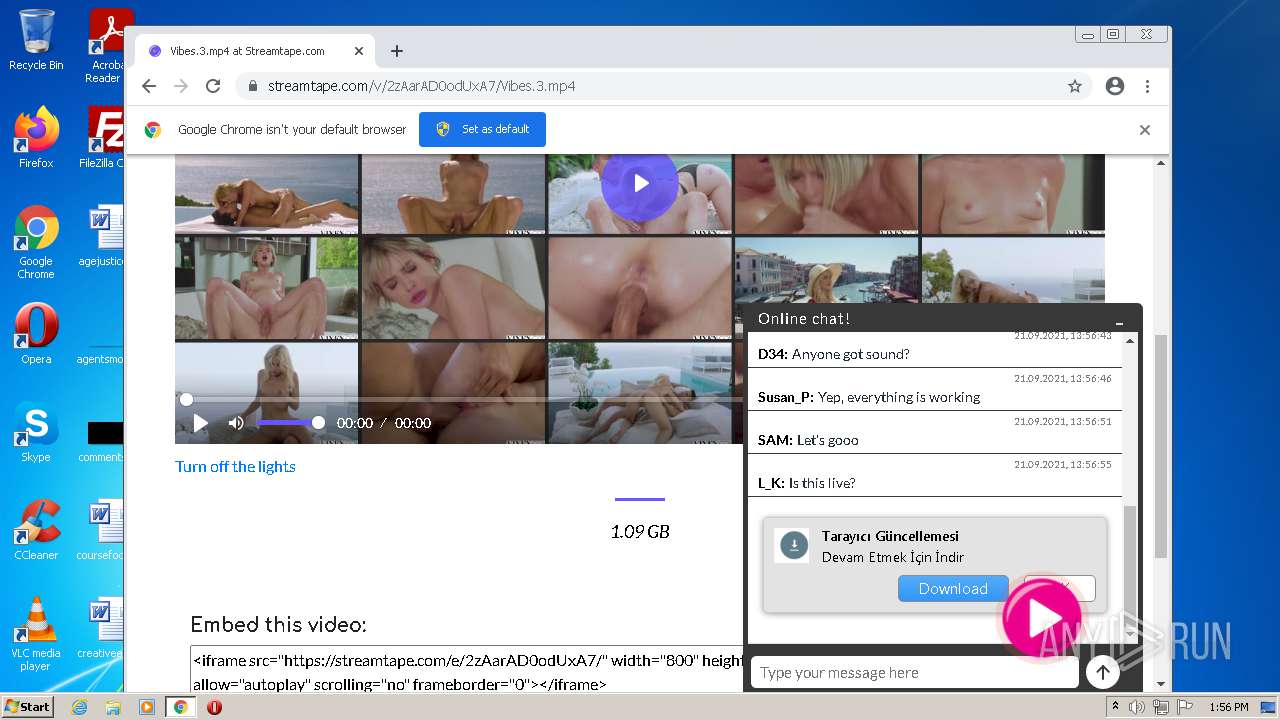
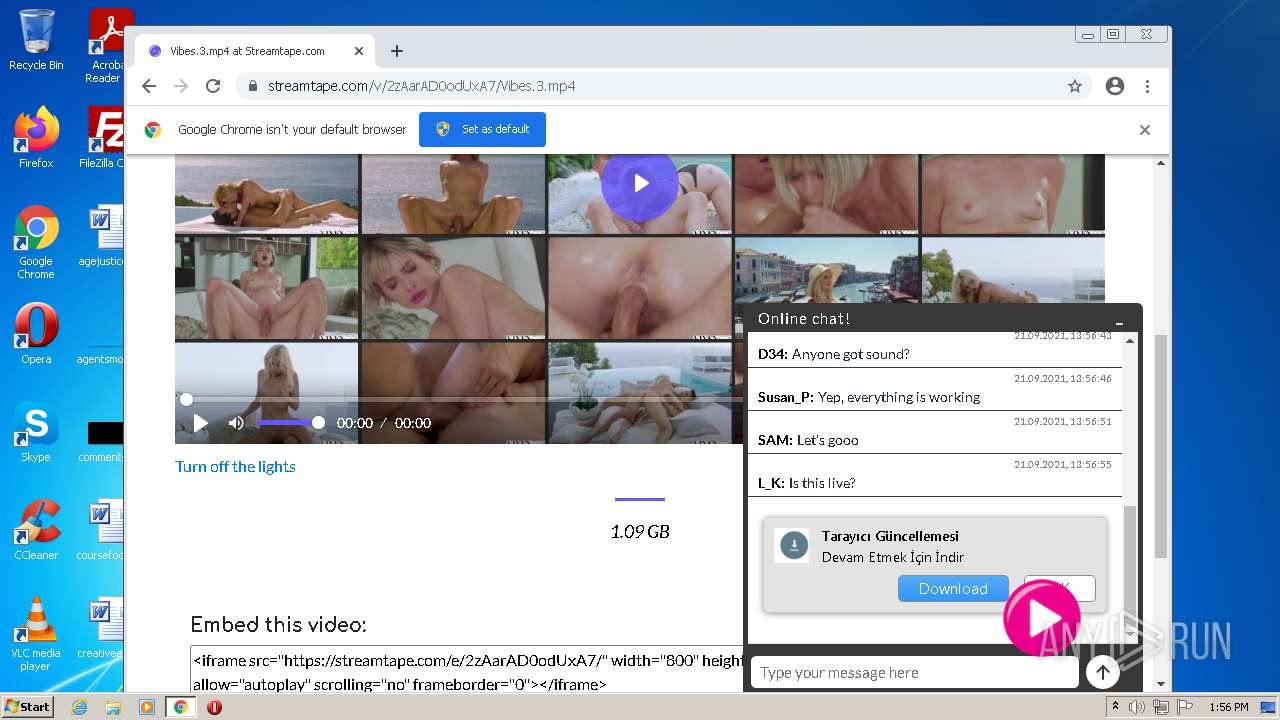
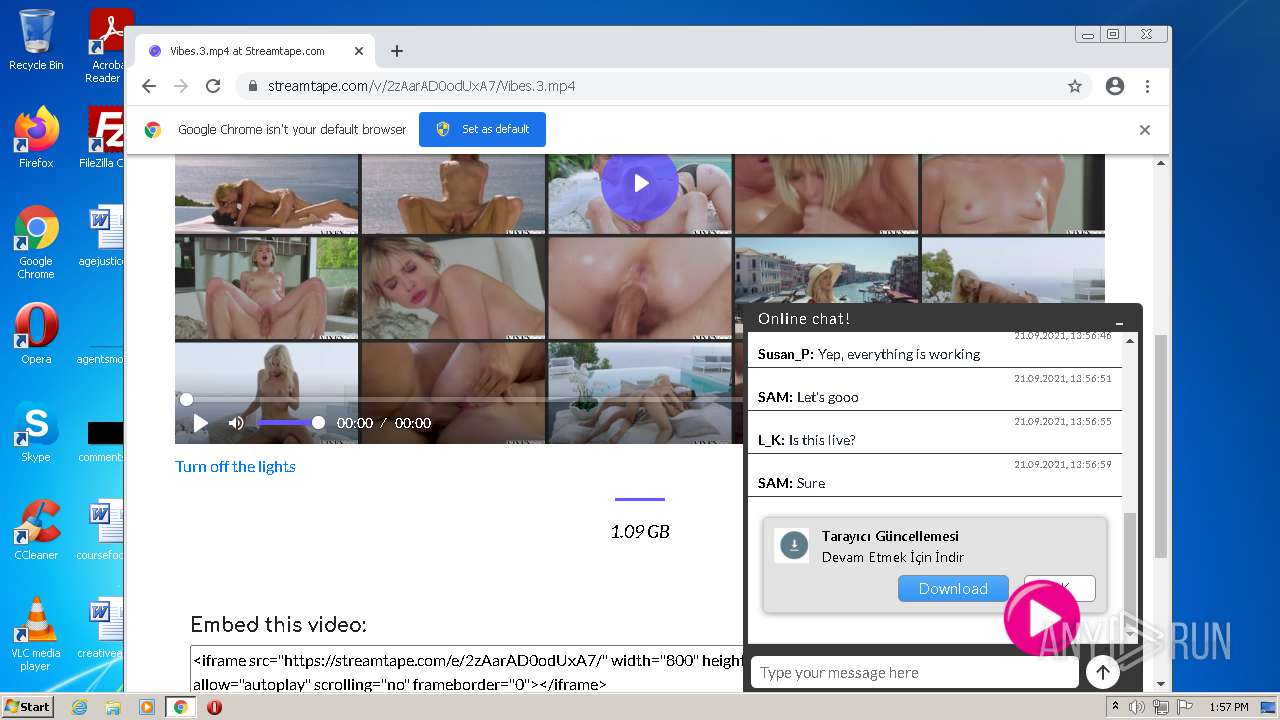
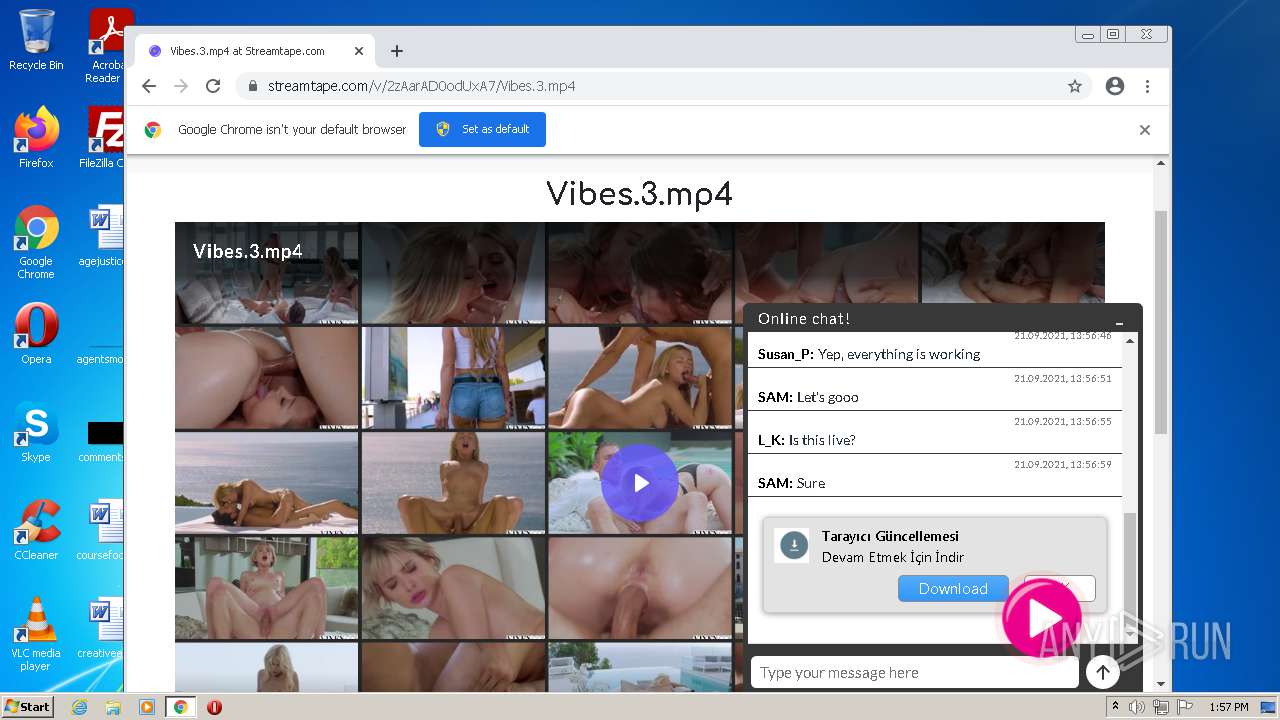
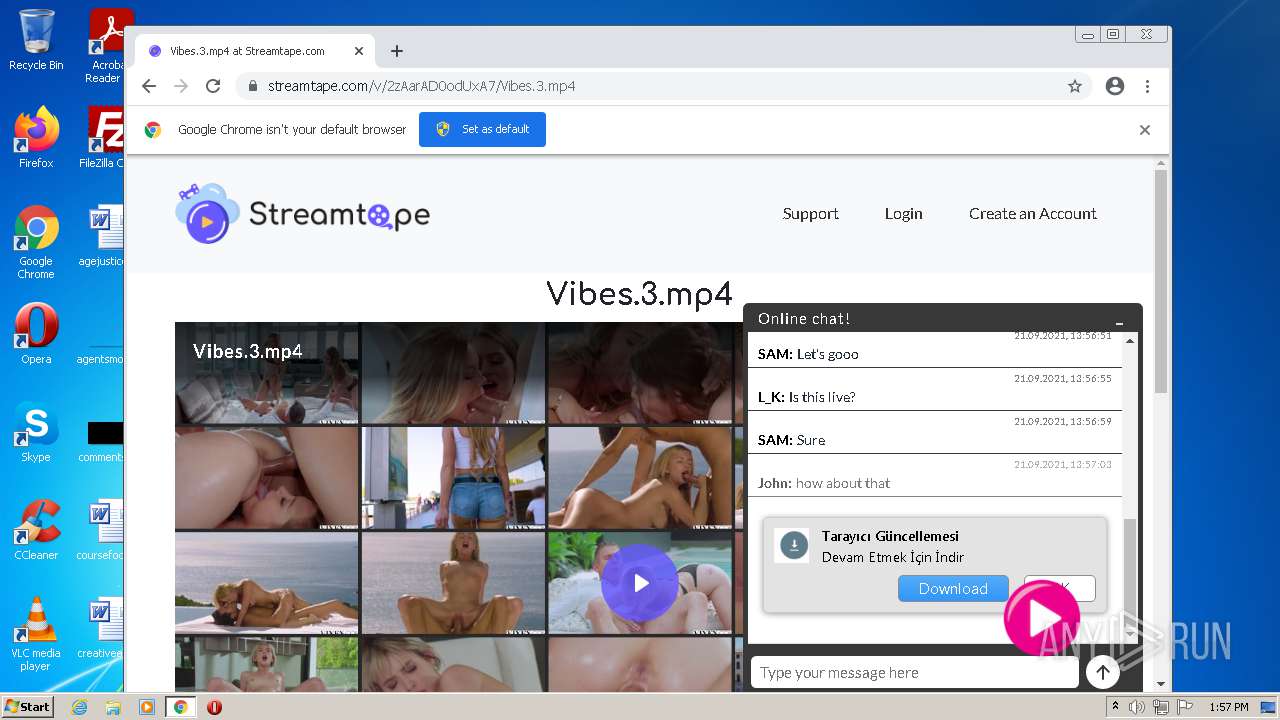
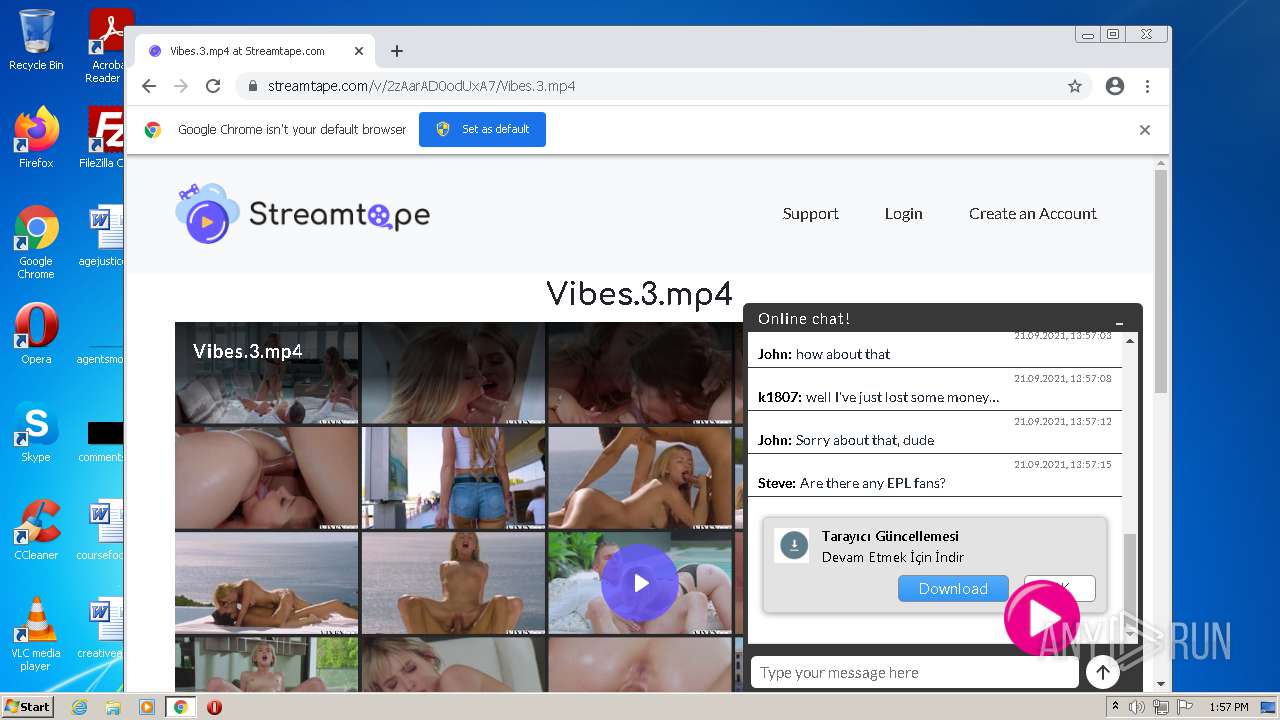
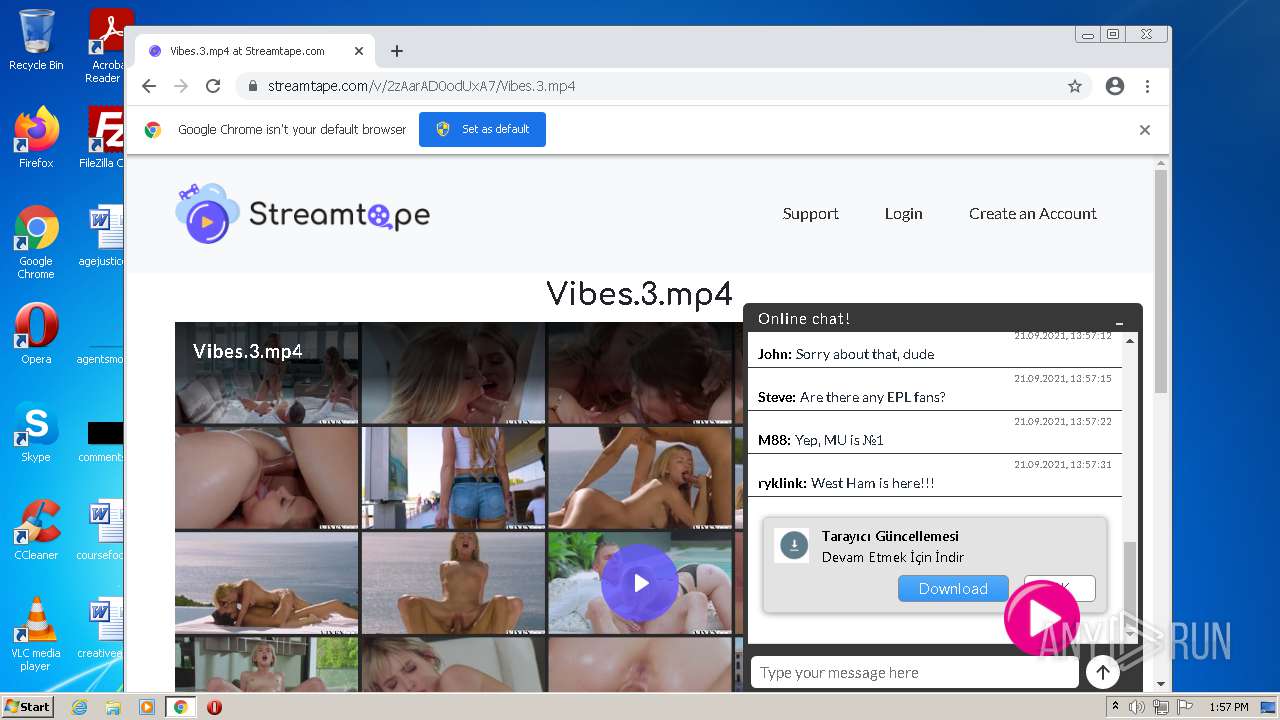
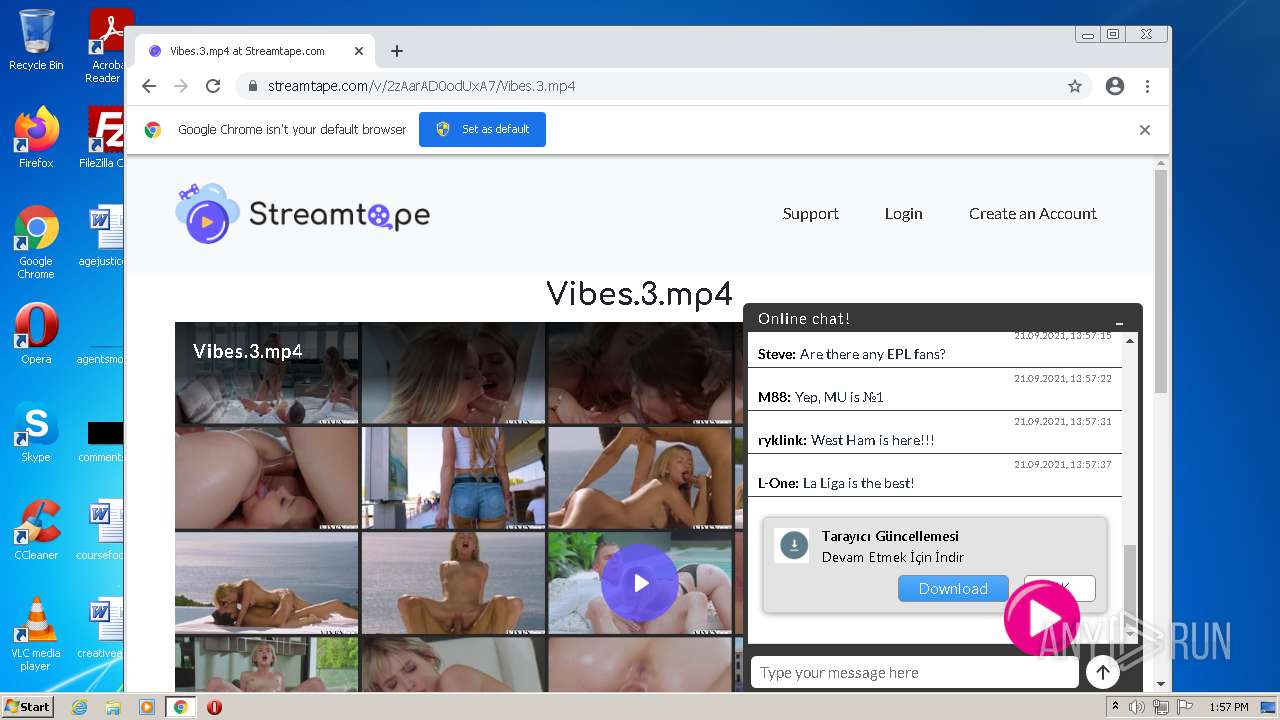
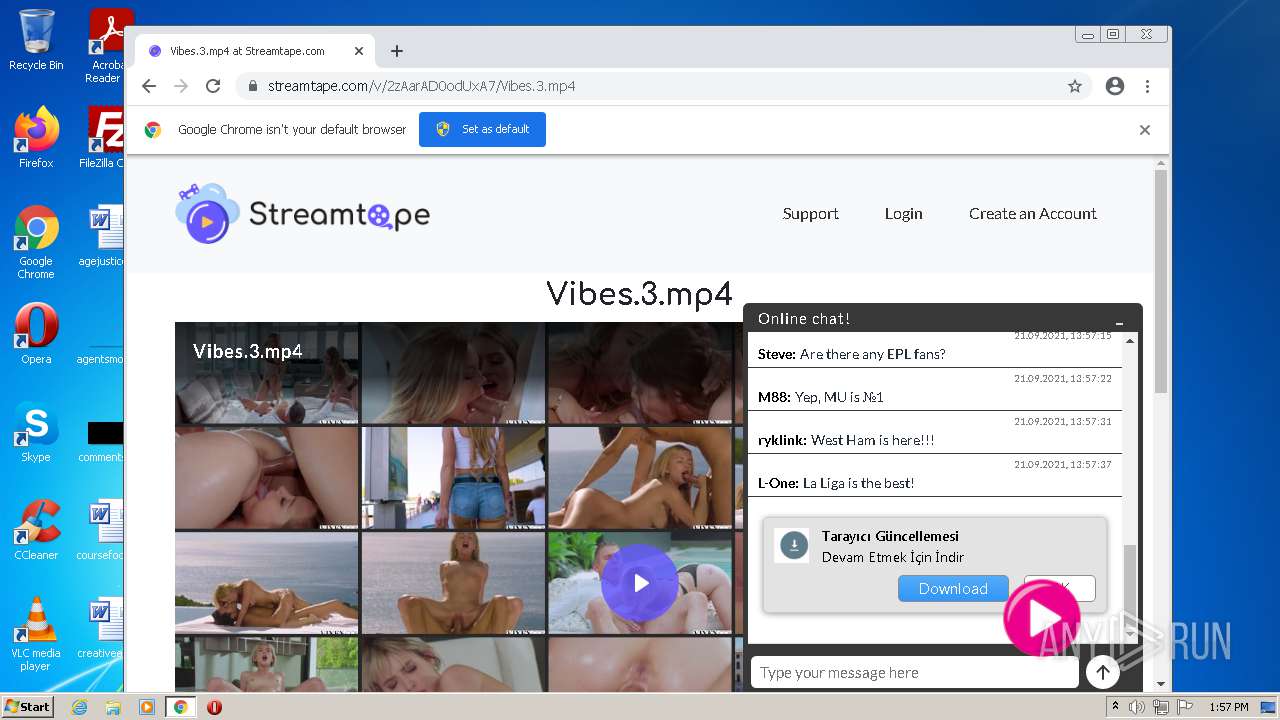
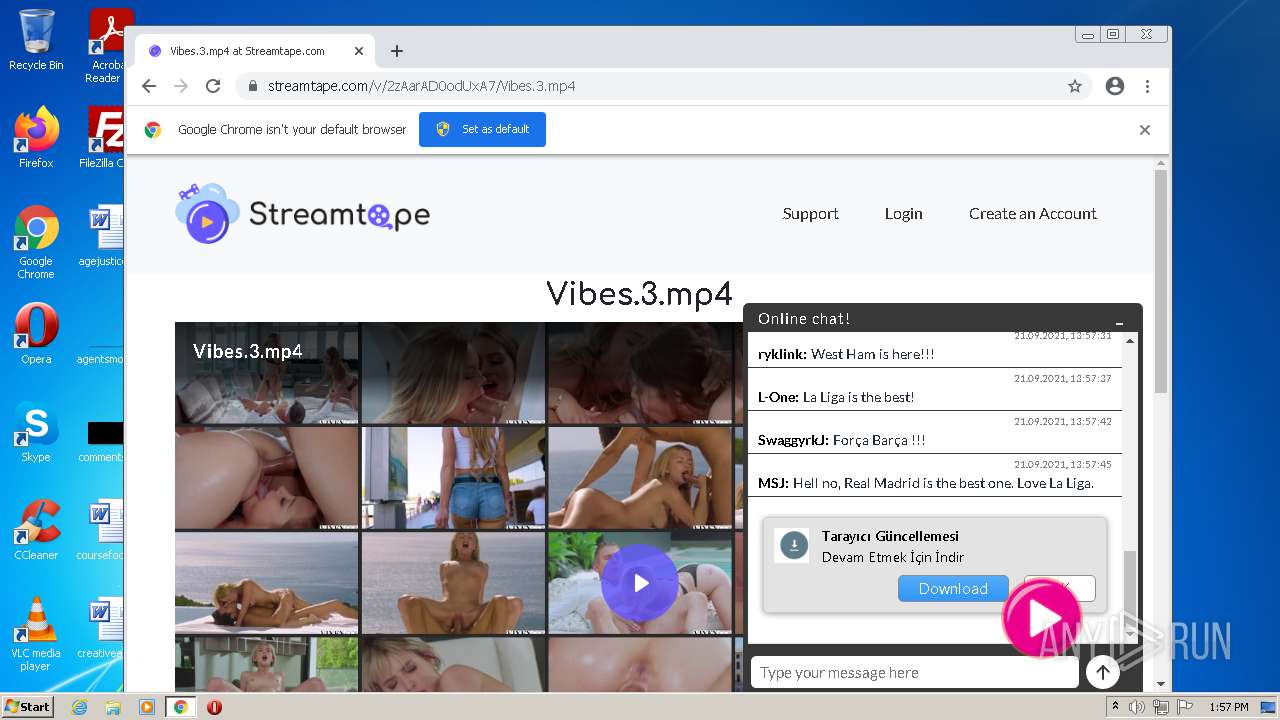
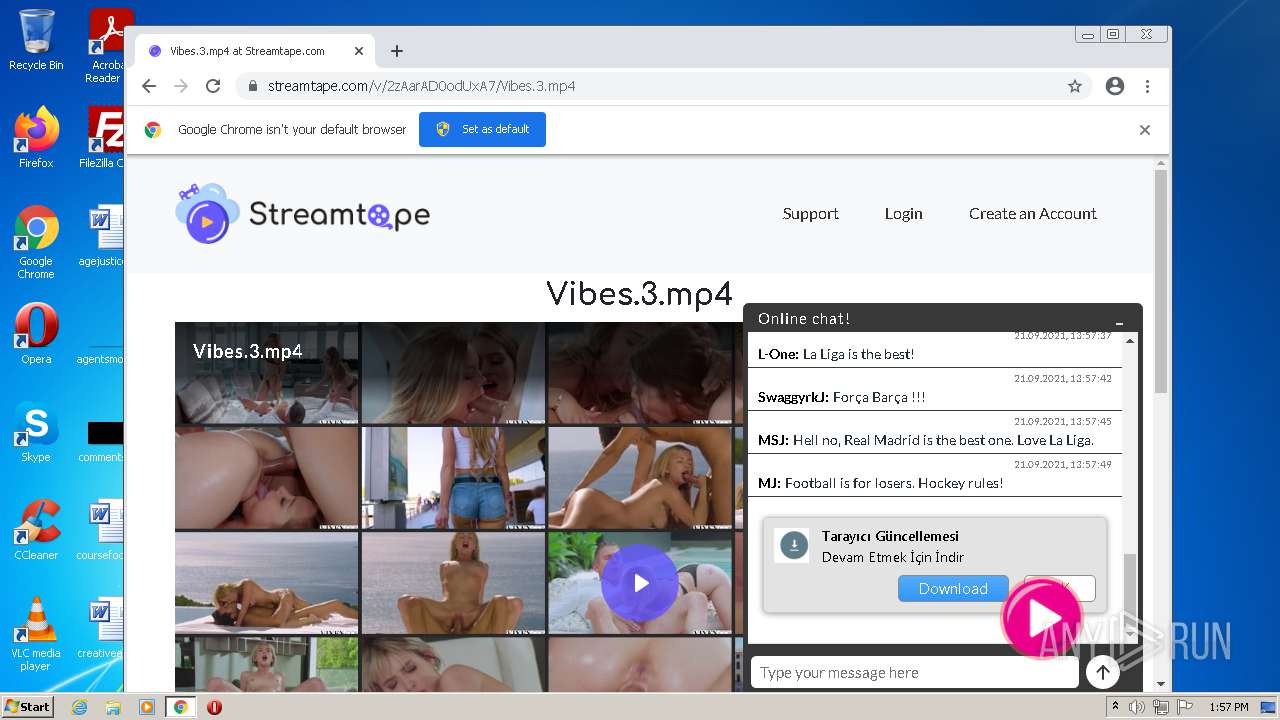
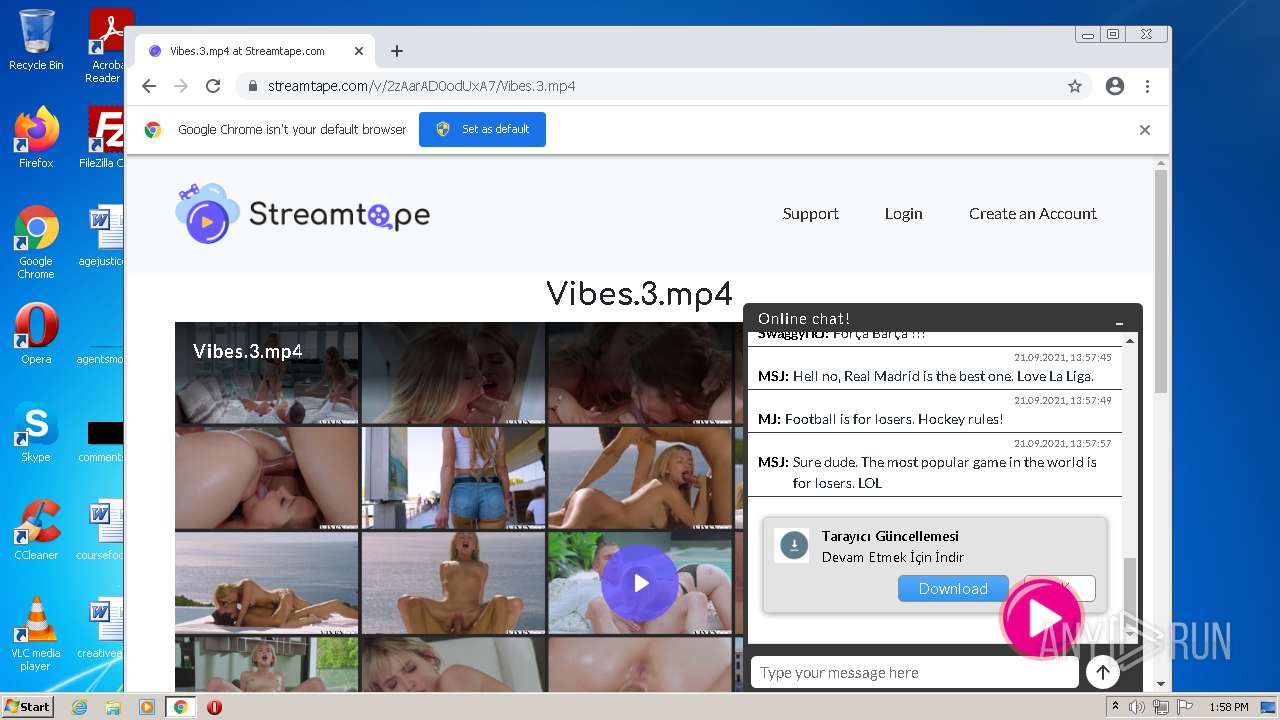
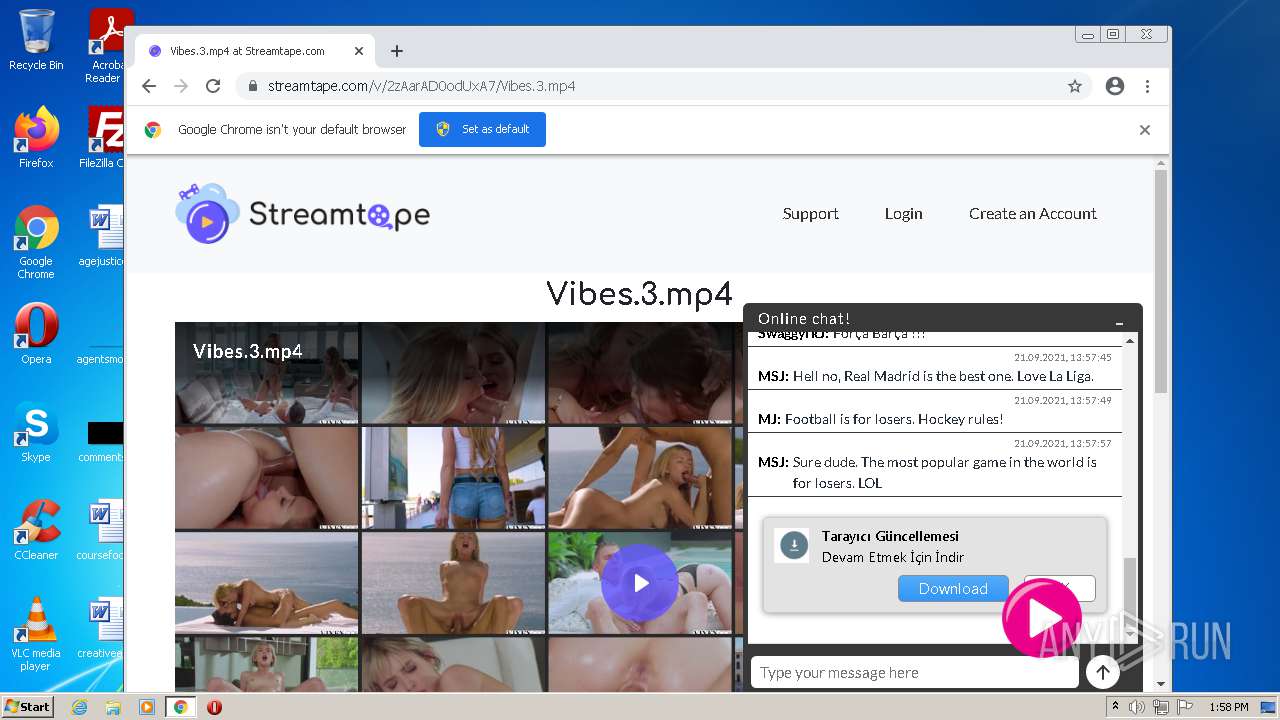
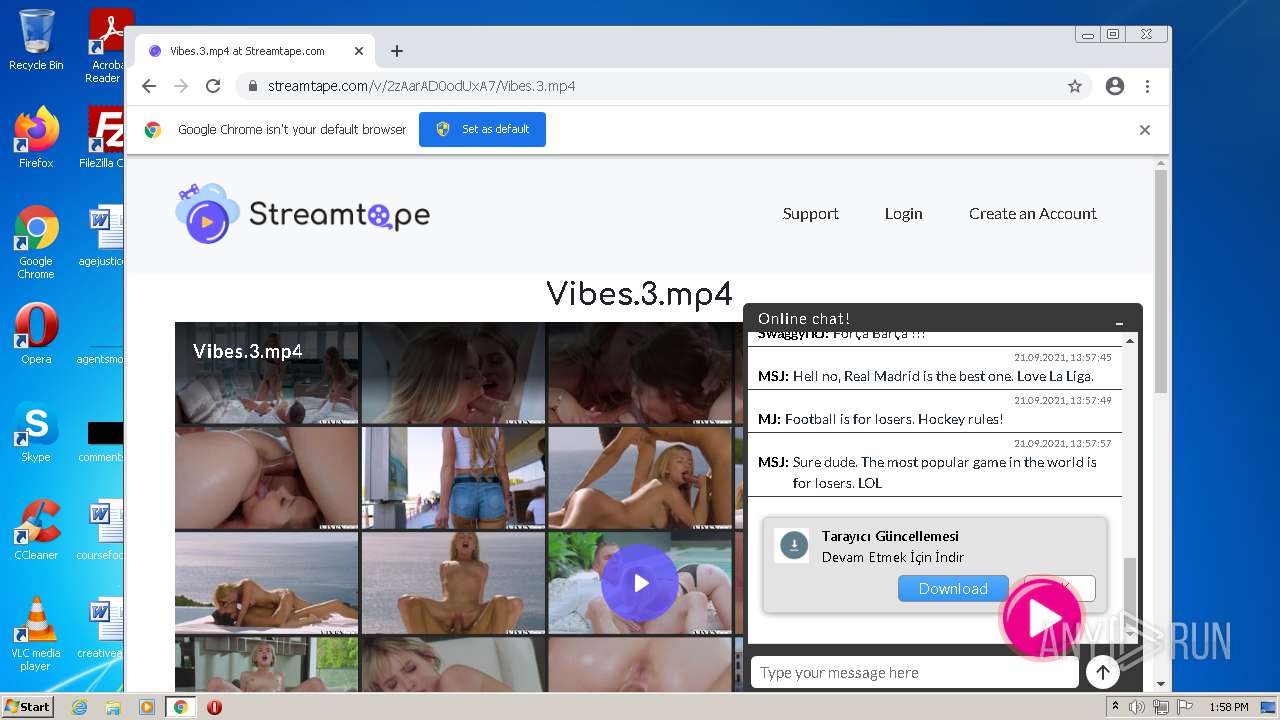
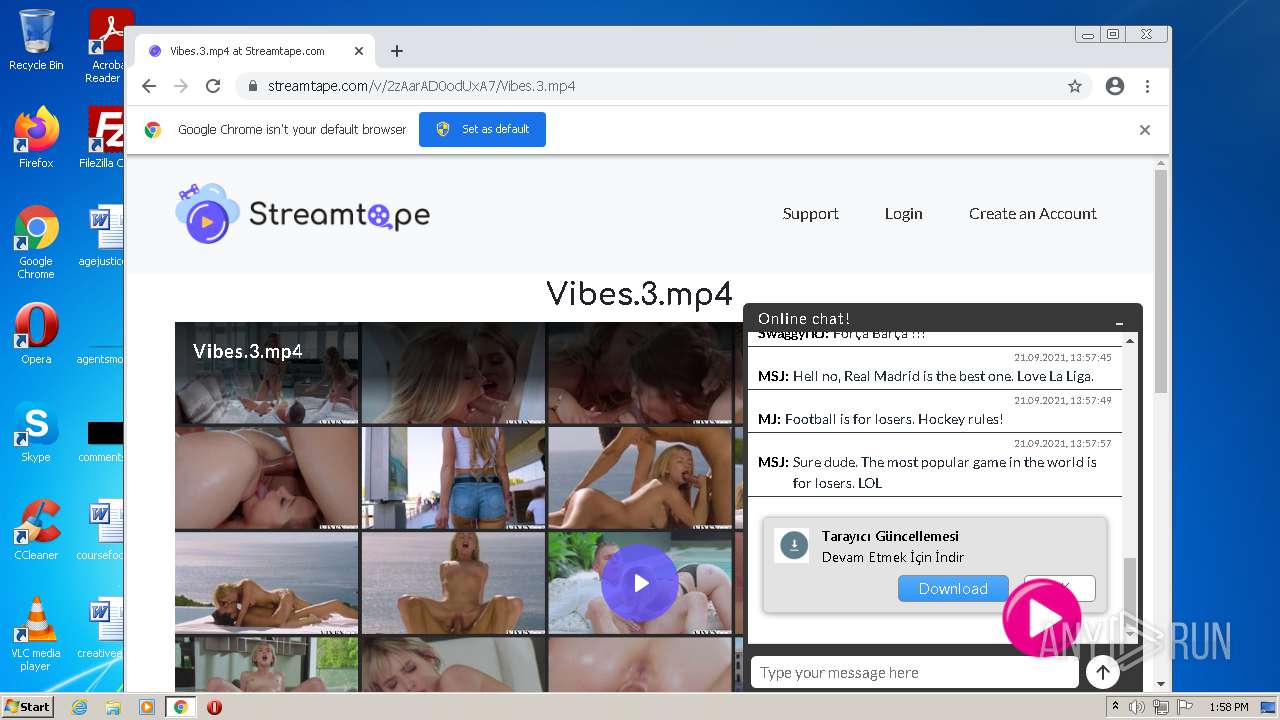
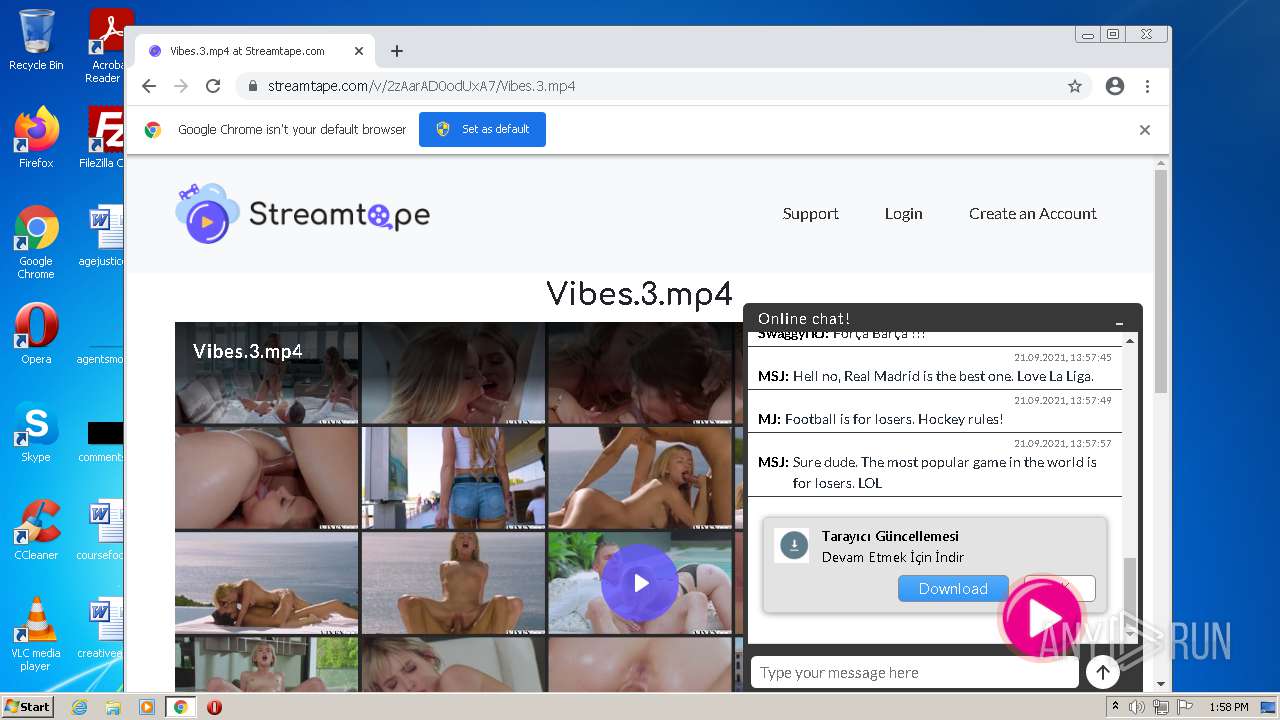
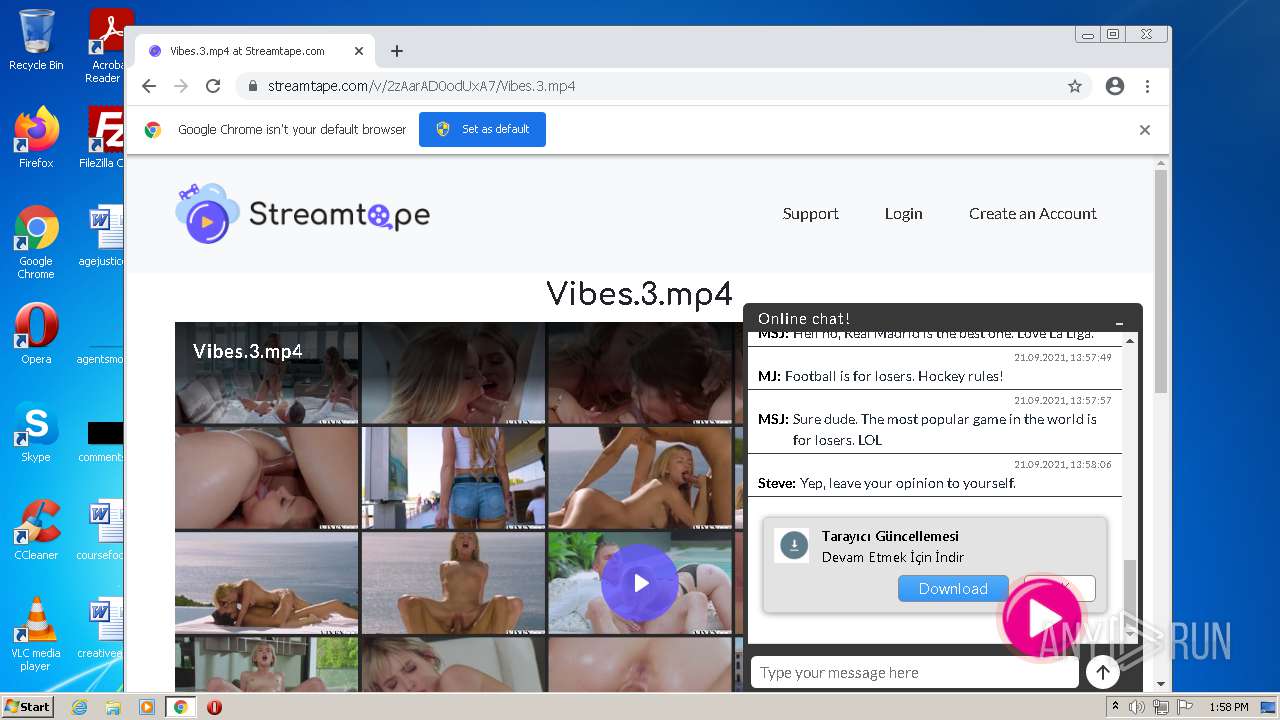
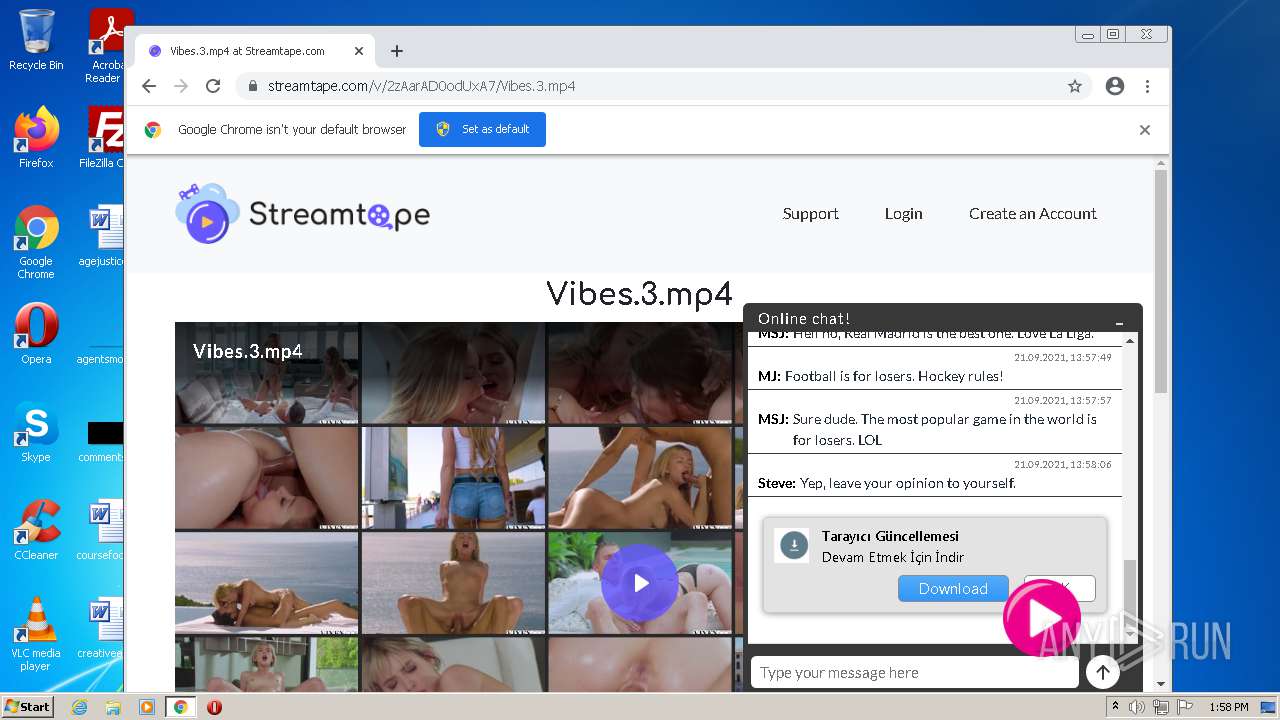
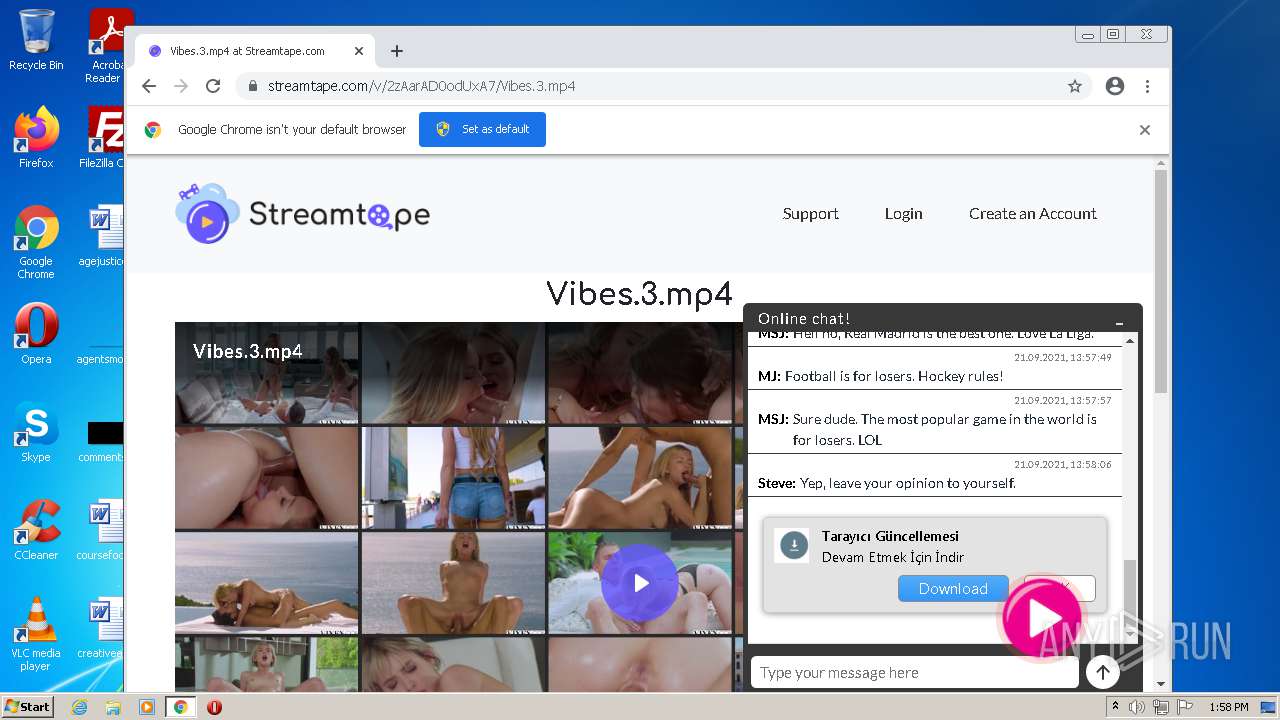
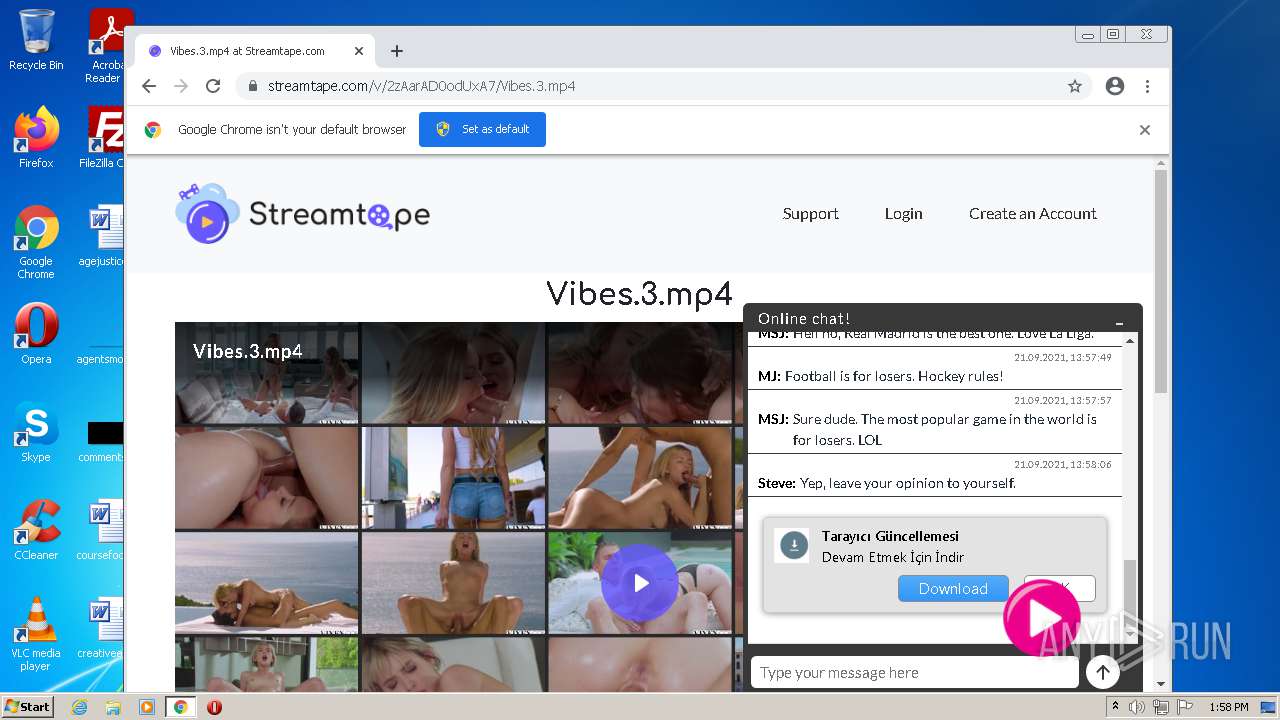
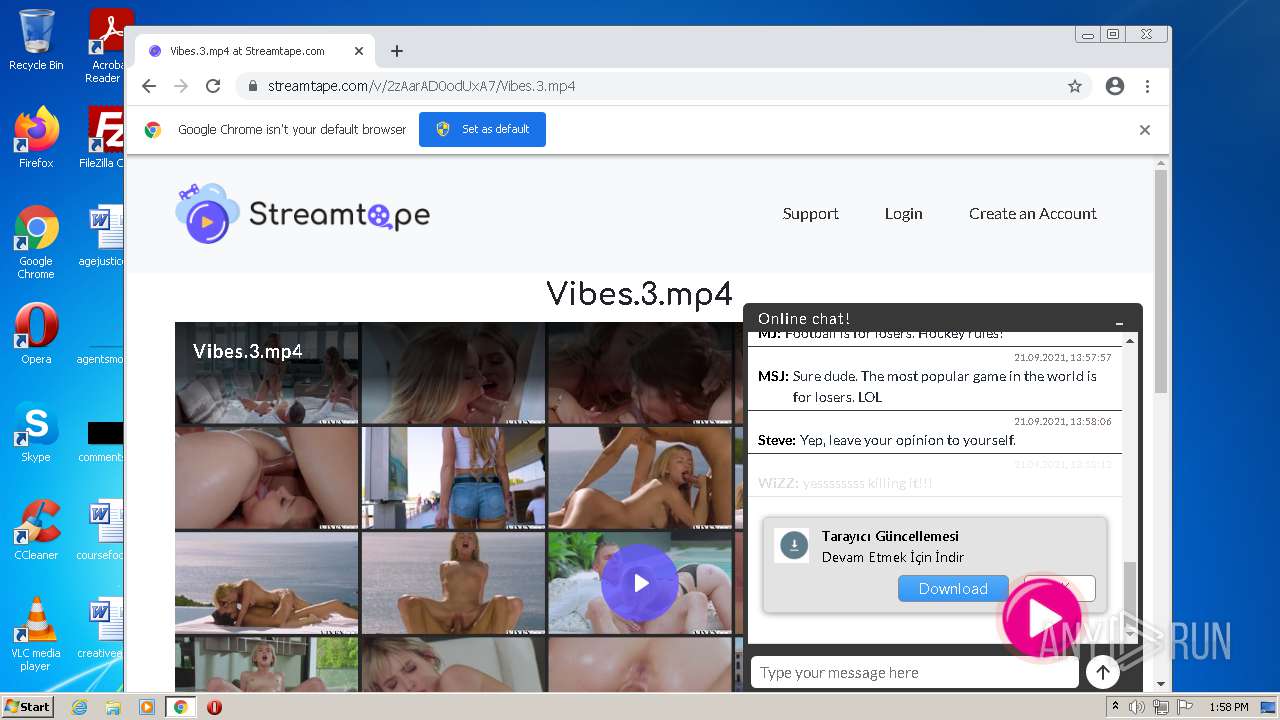
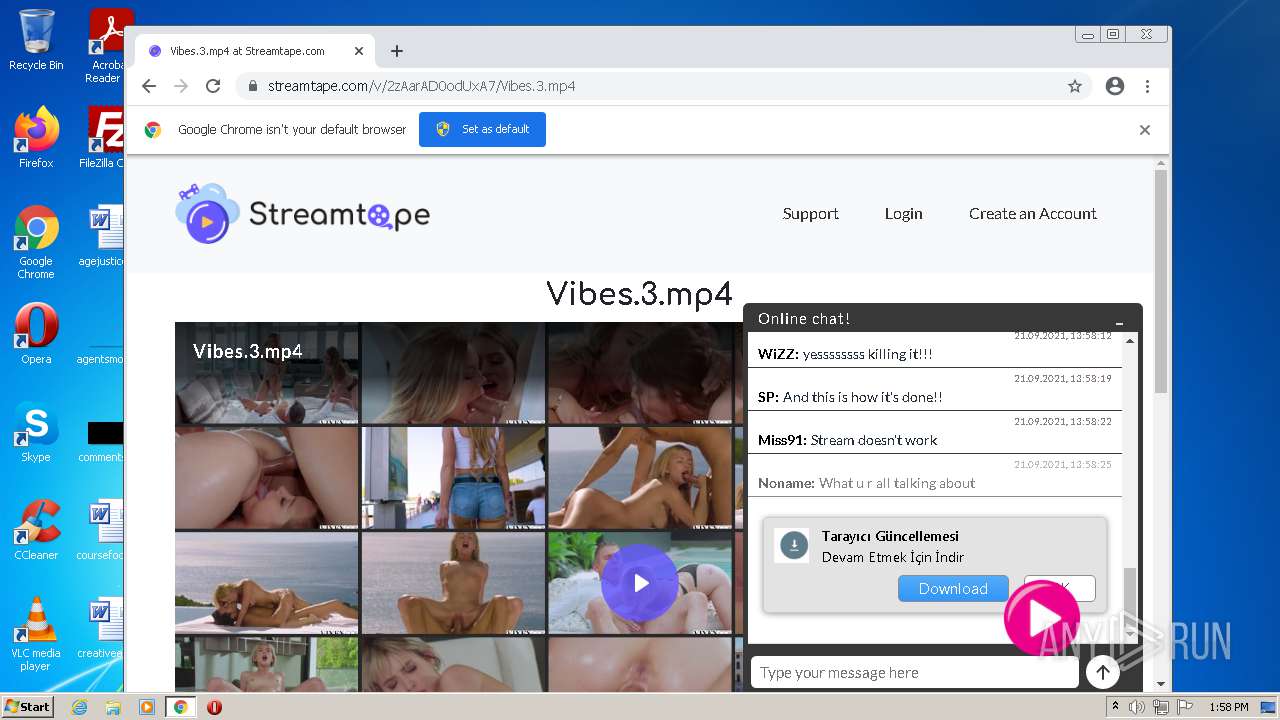
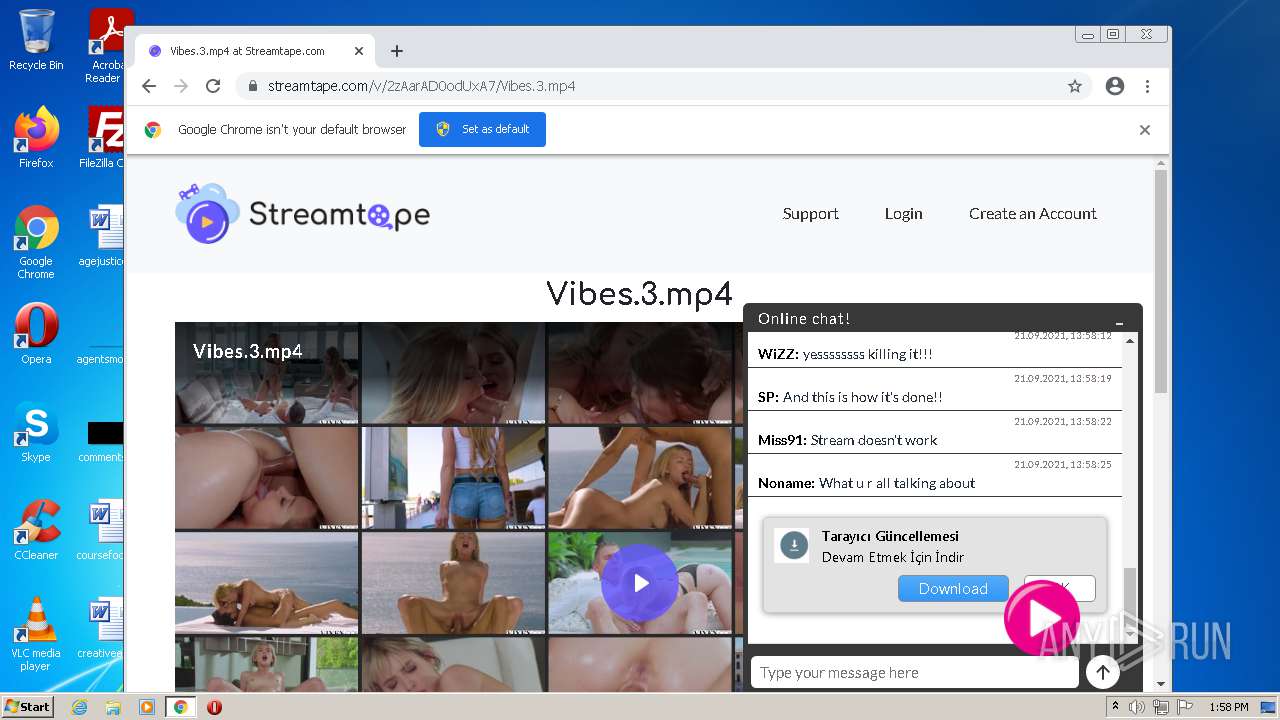
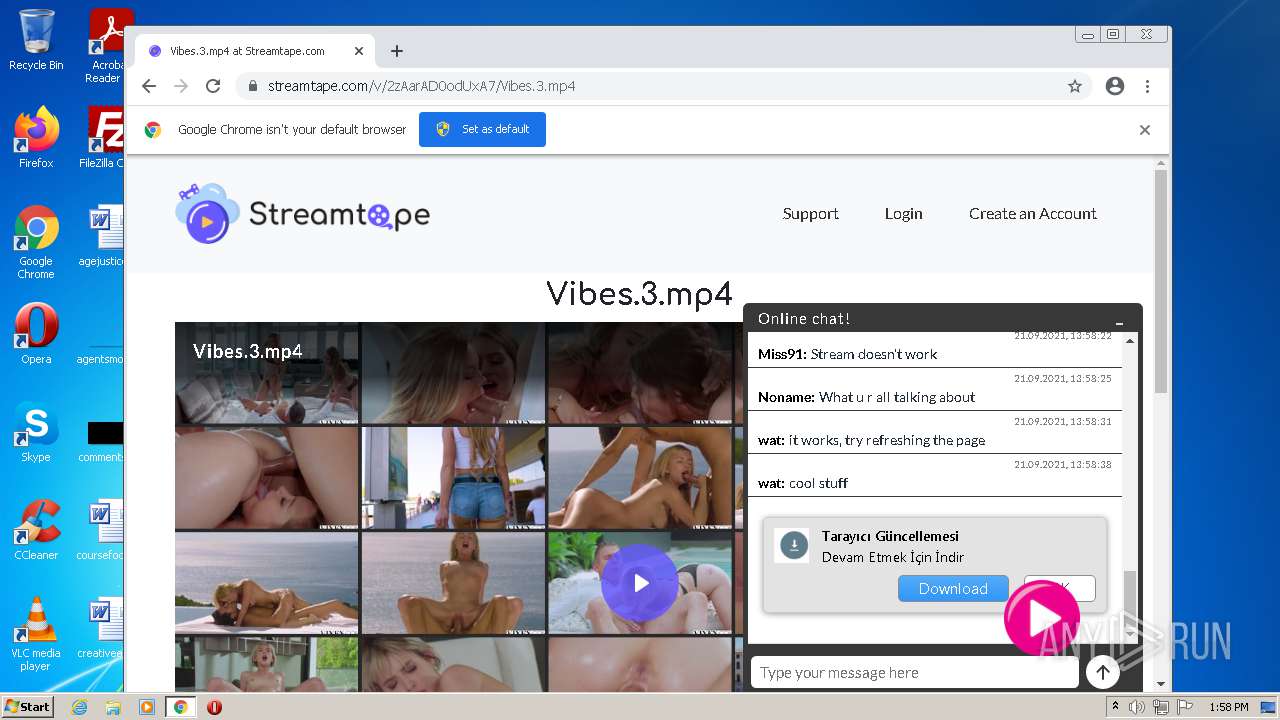
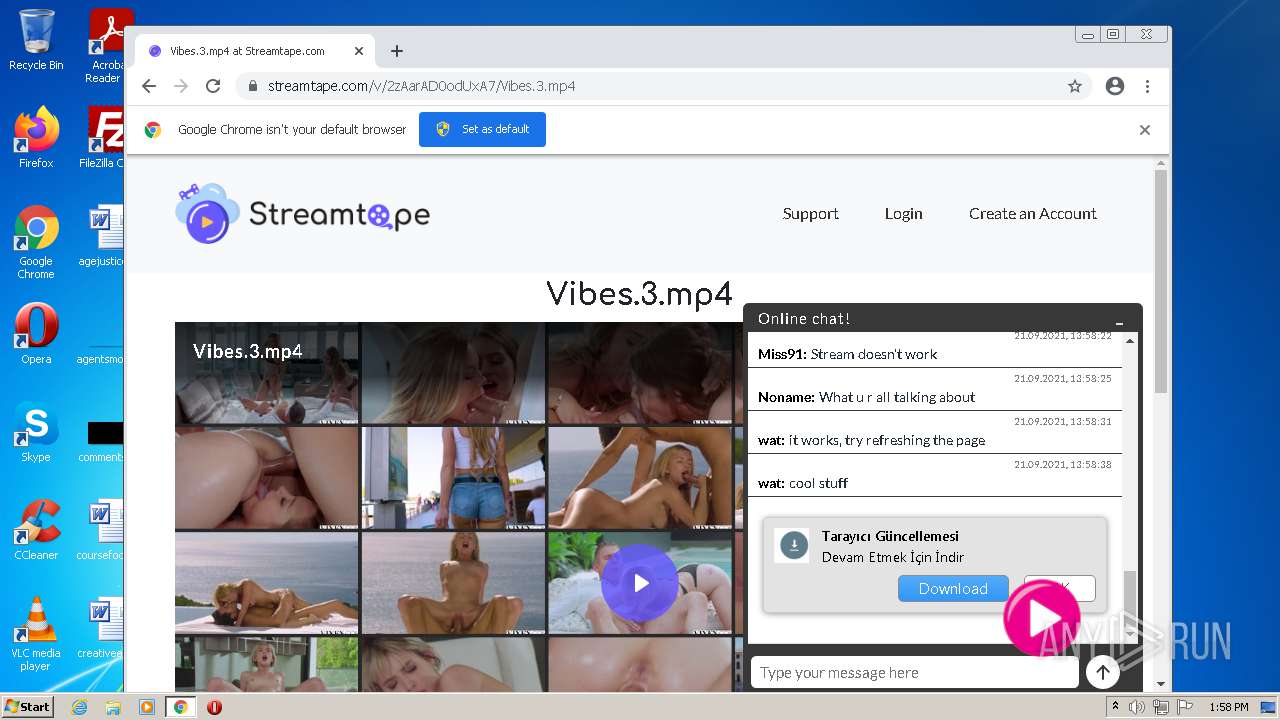
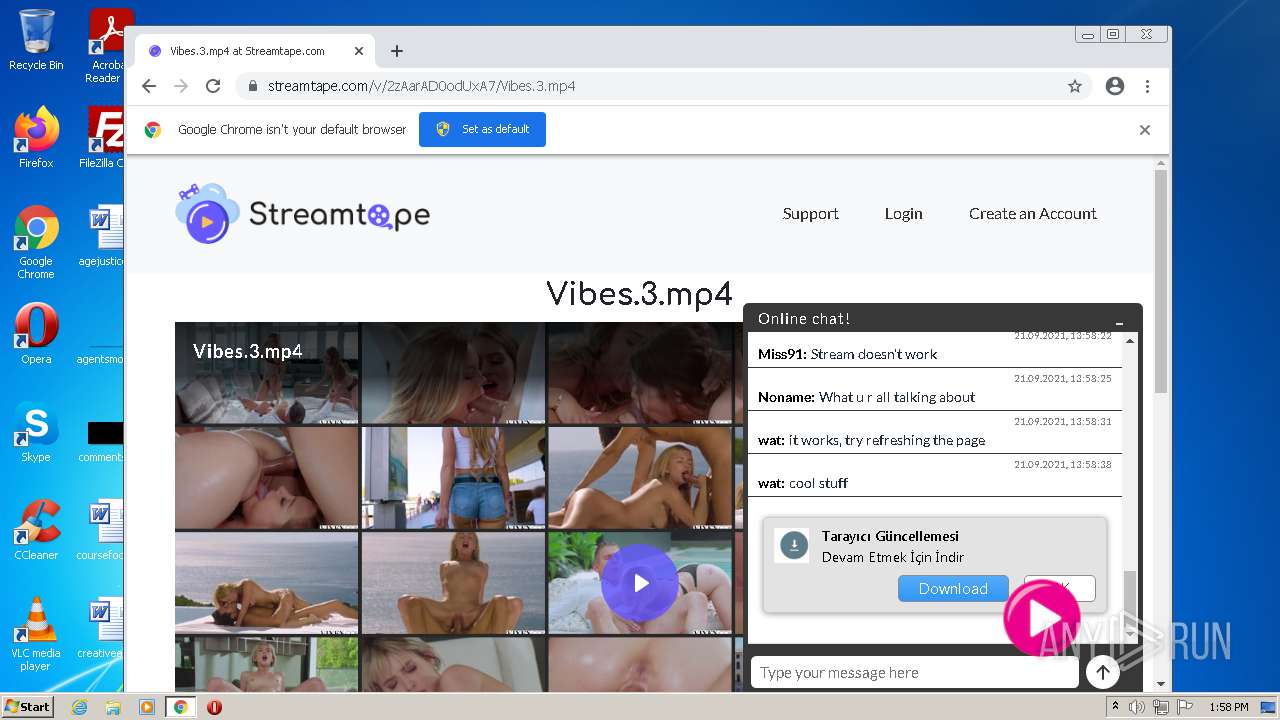
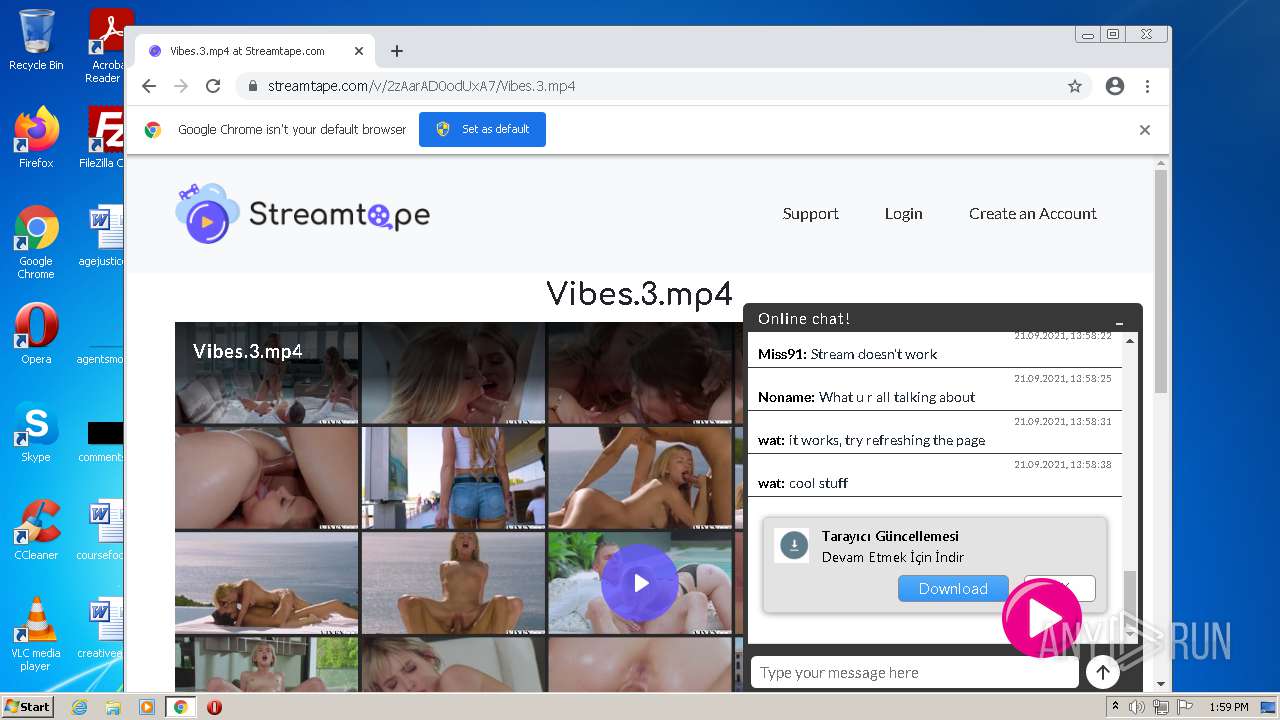
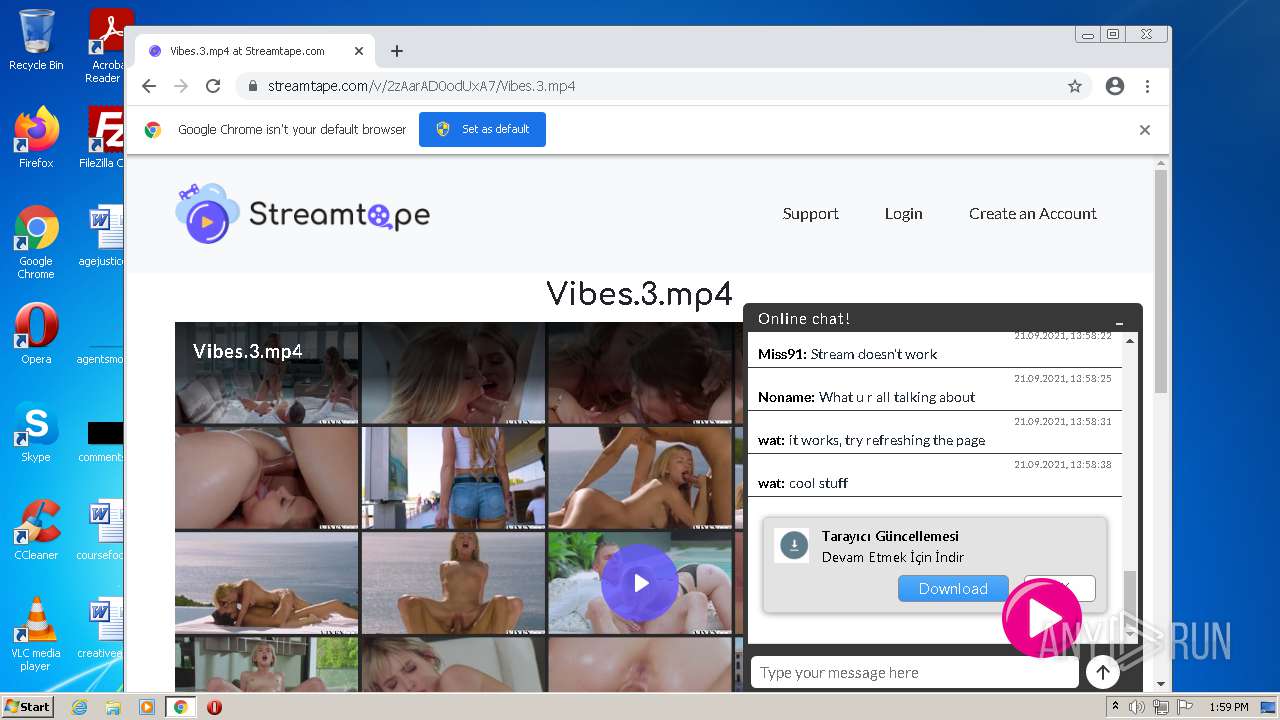
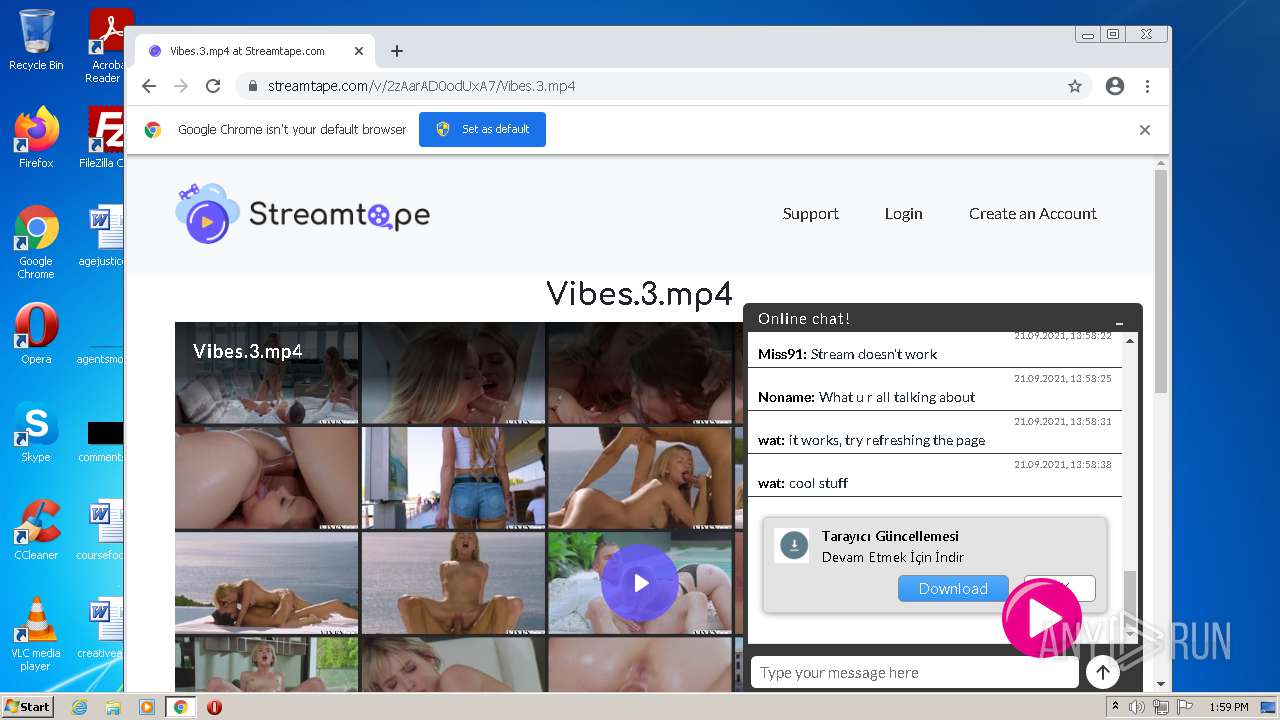
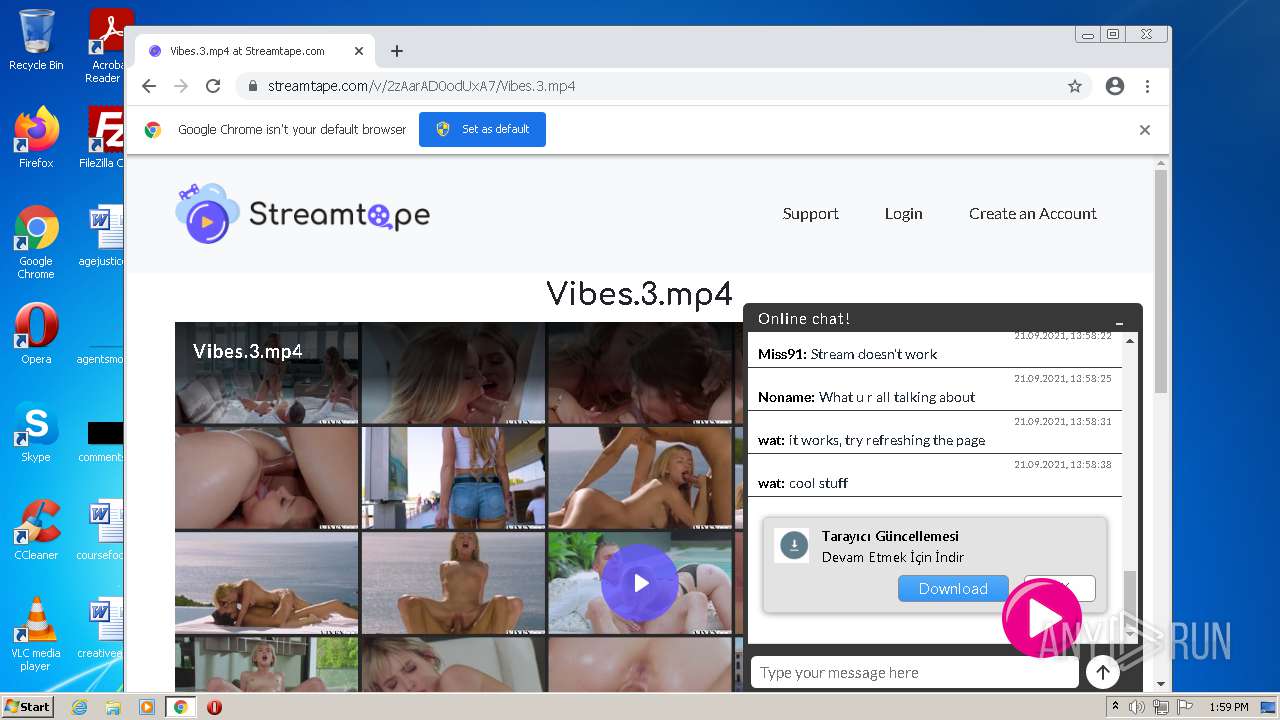
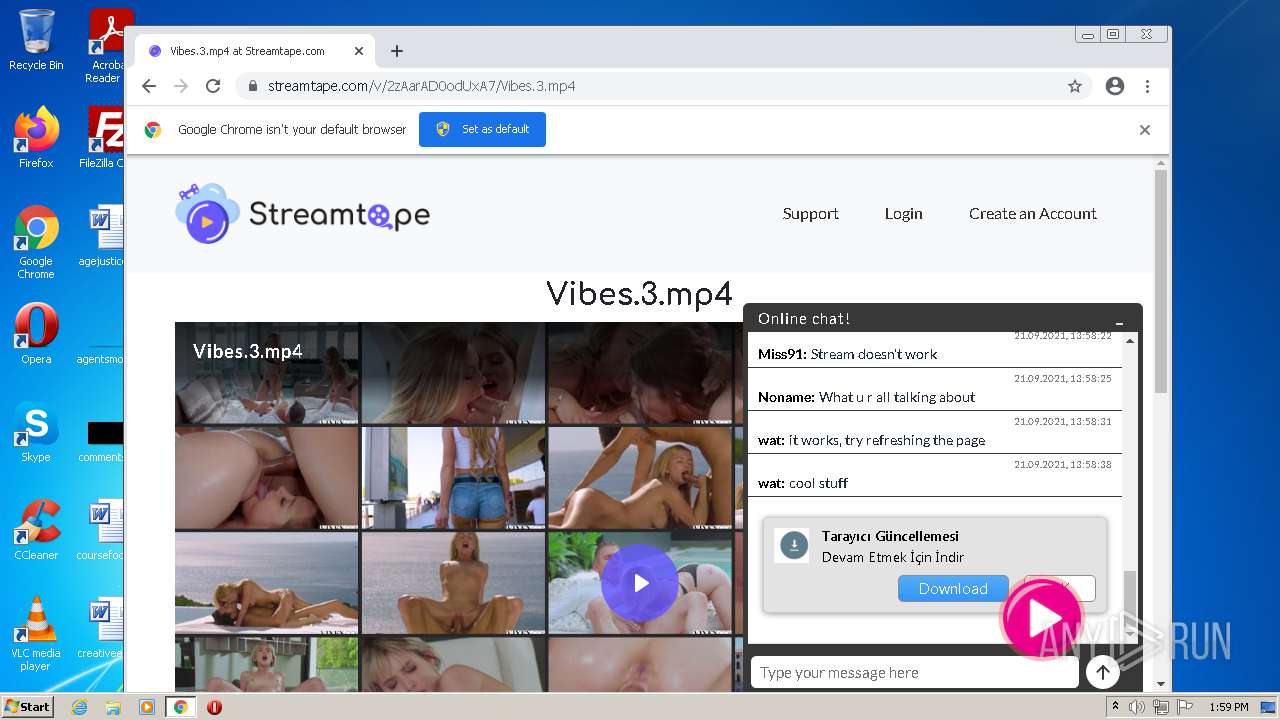
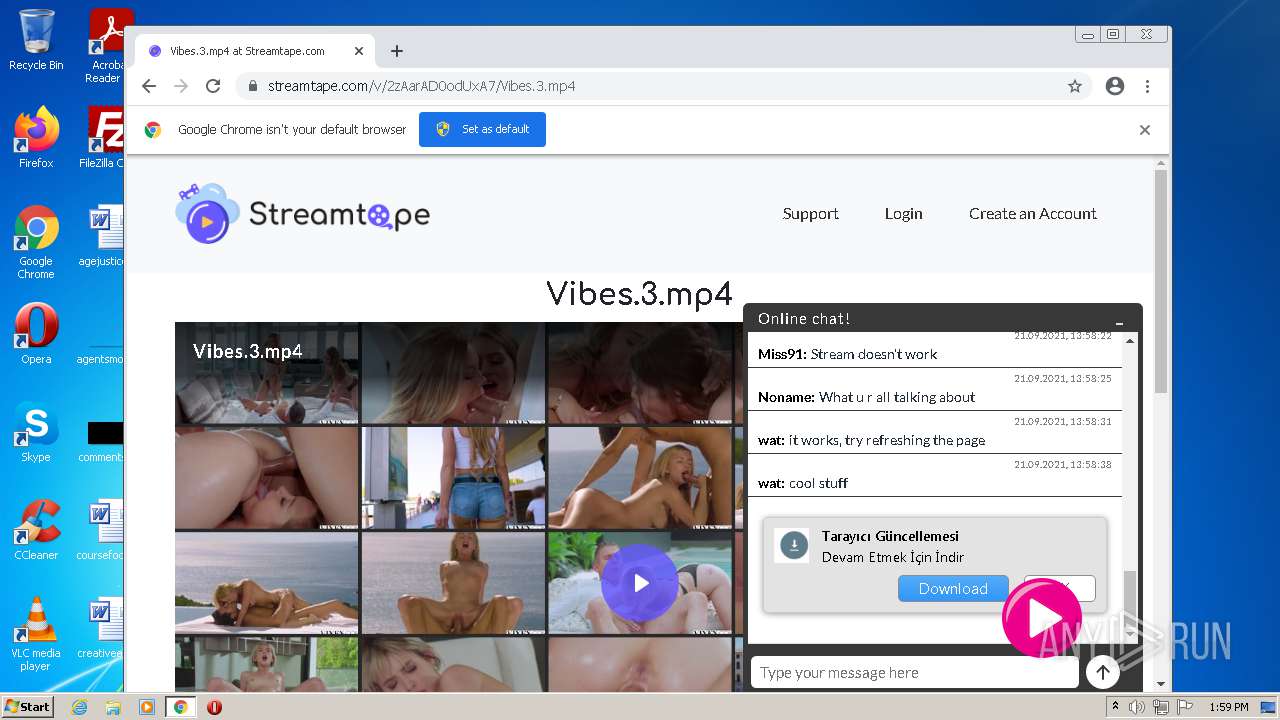
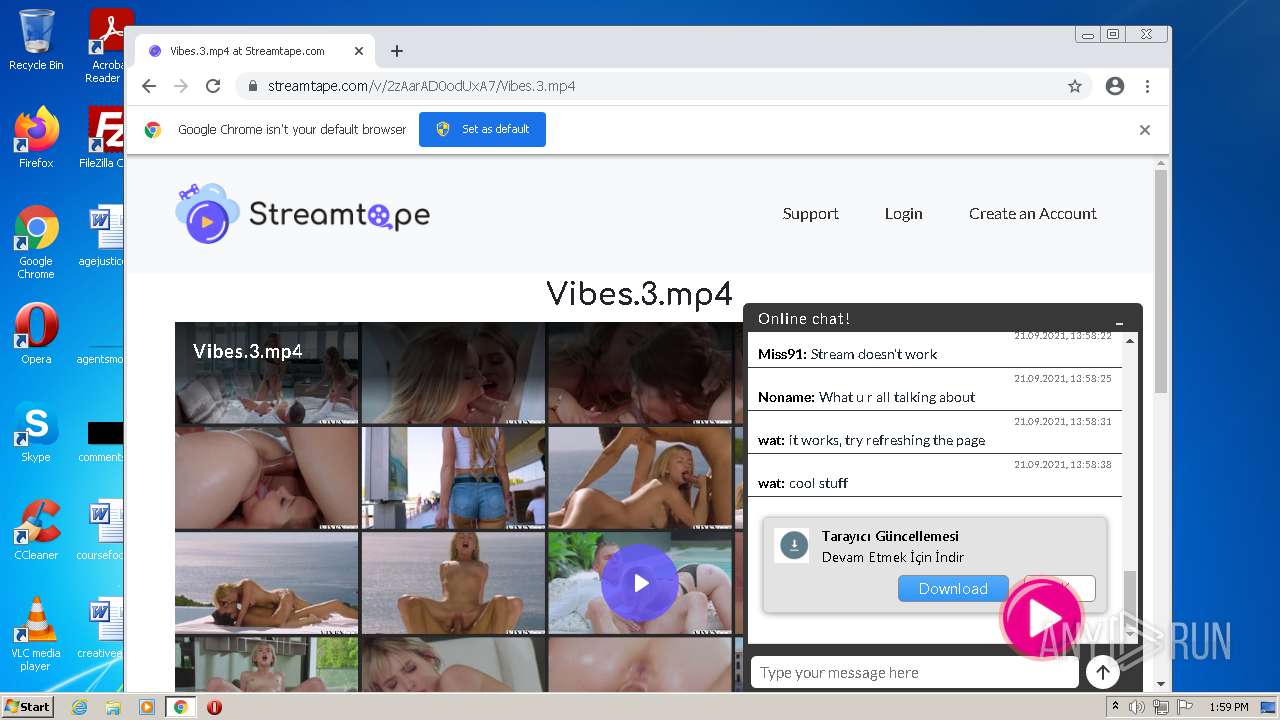
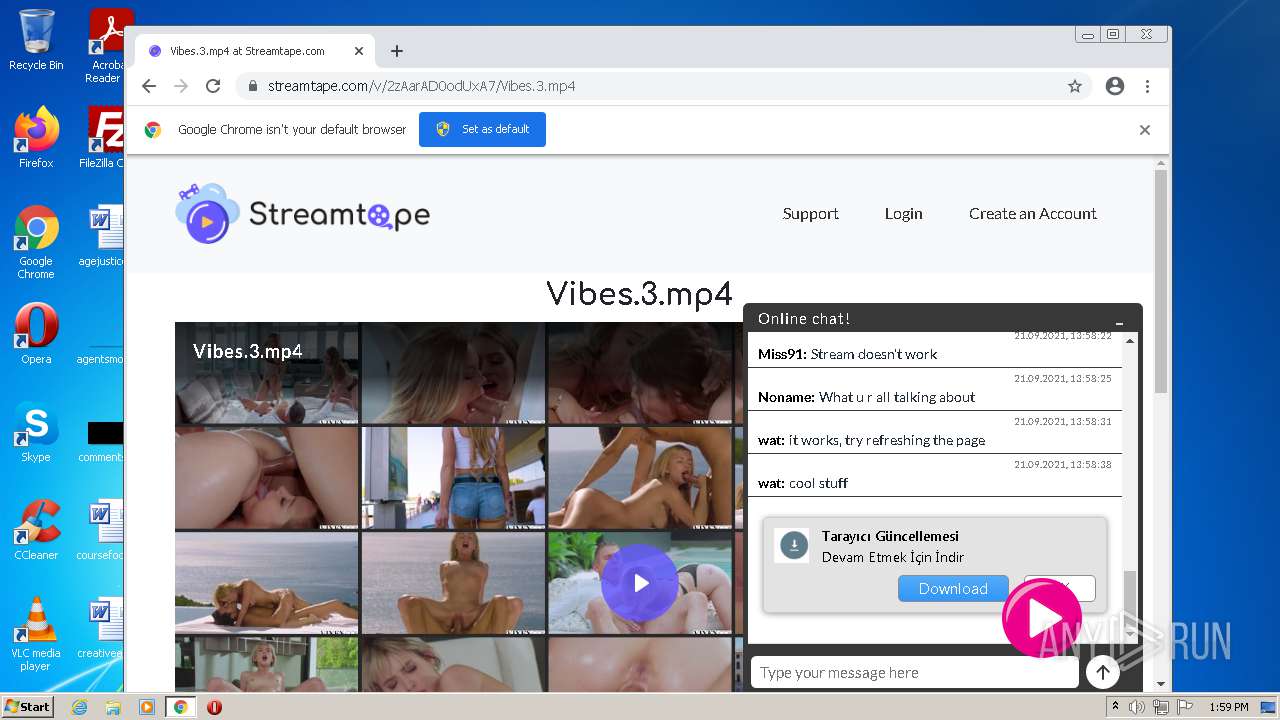
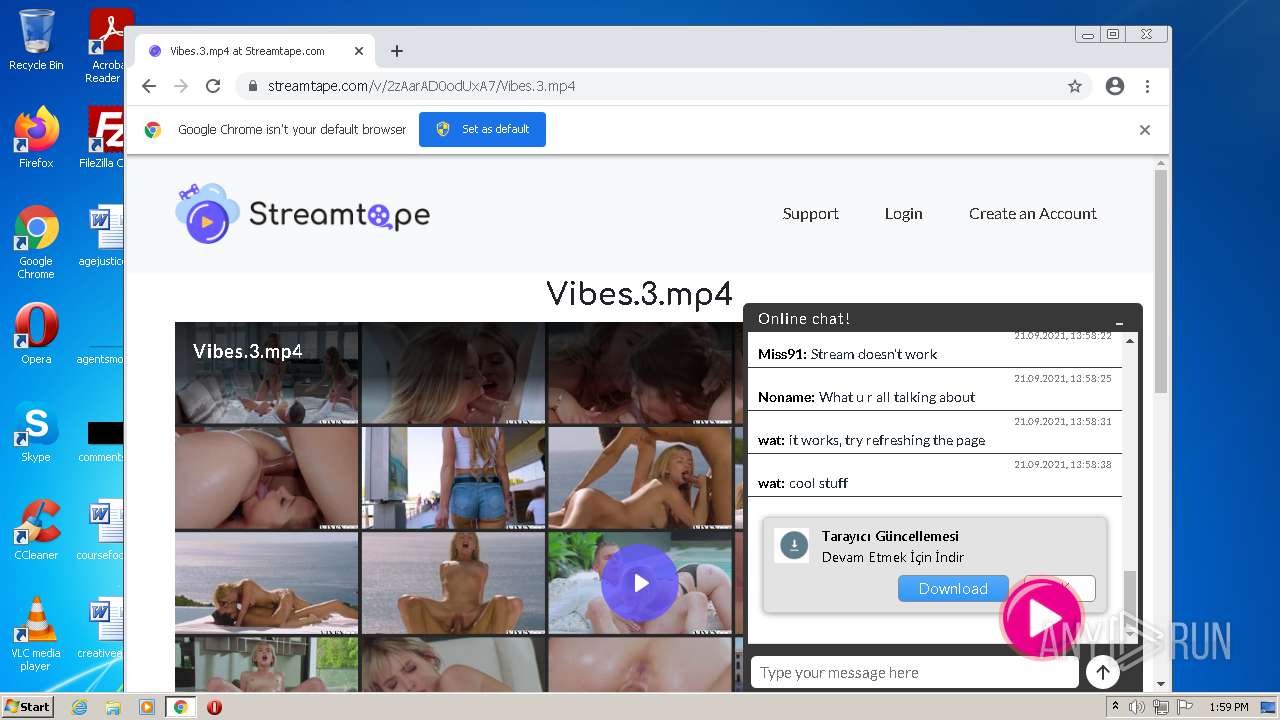
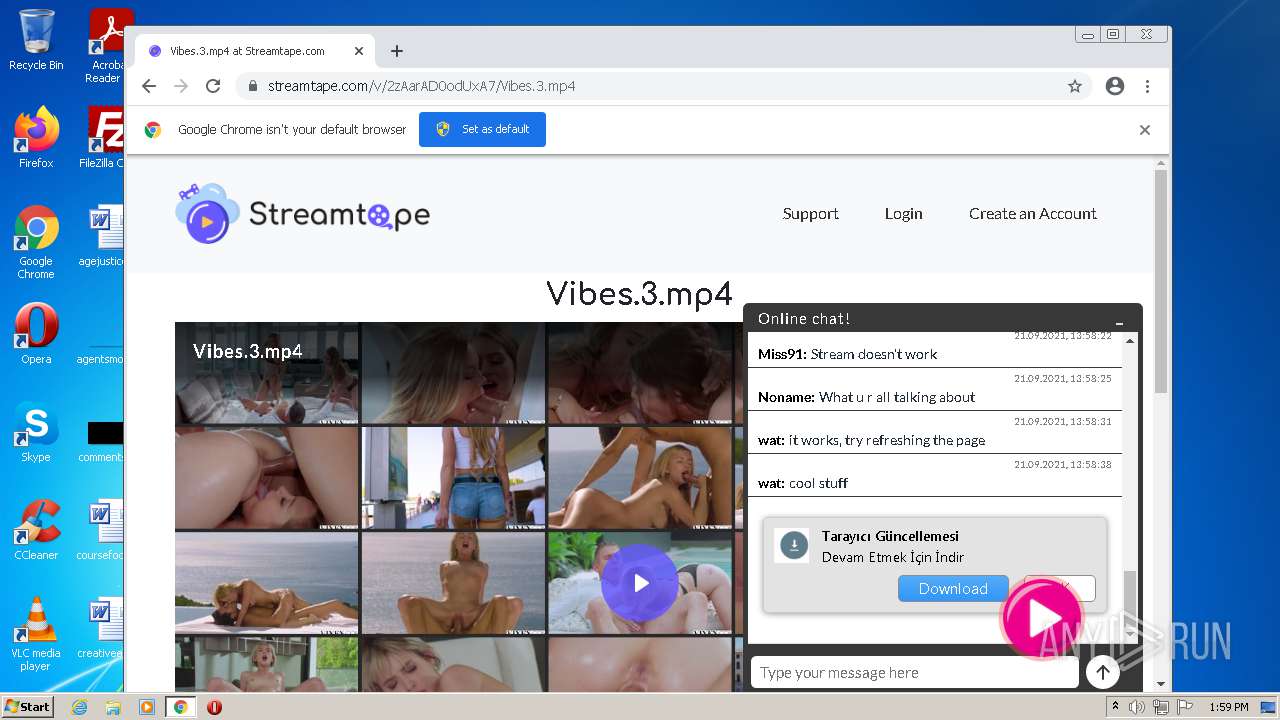
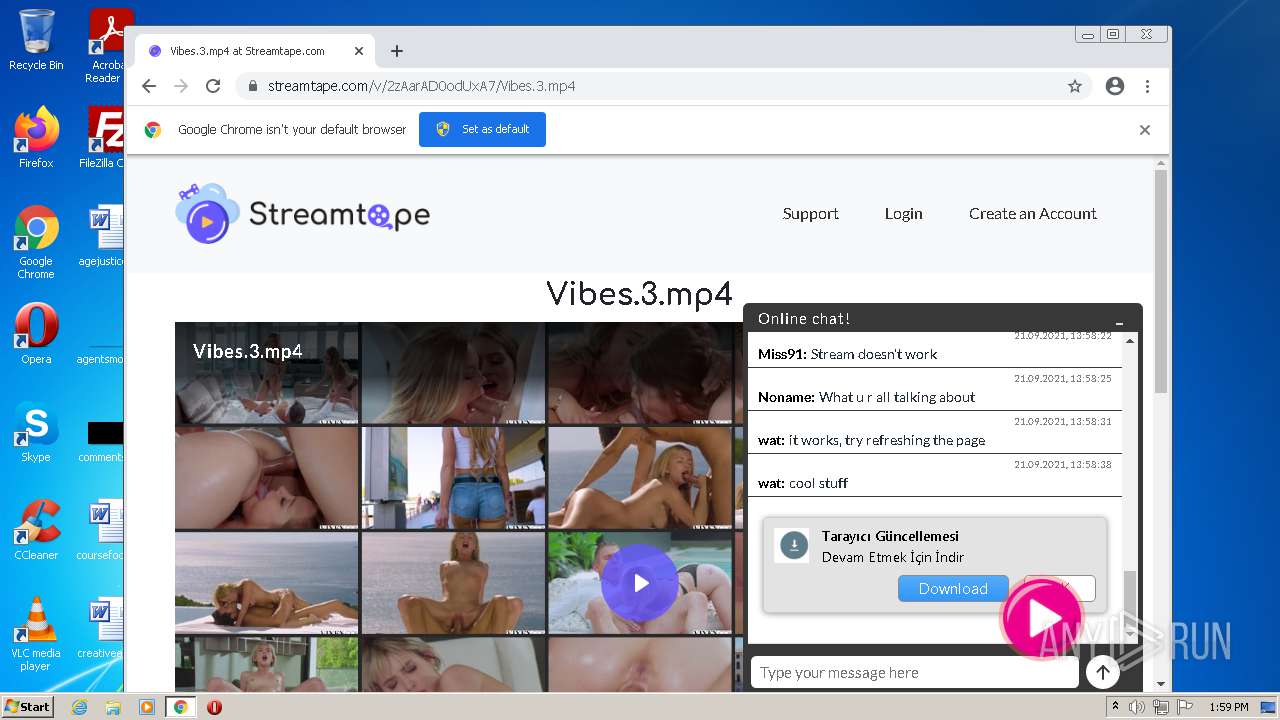
| URL: | https://streamtape.com/v/2zAarAD0odUxA7/Vibes.3.mp4 |
| Full analysis: | https://app.any.run/tasks/1ae84ffd-63cf-48fc-b7bb-133e52a67c5c |
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2021, 12:55:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 22D0751ED29432C48F8B611B0C1D77F8 |
| SHA1: | B51ADF3A636D1135C21C9D591B5E56A32CC4016E |
| SHA256: | 9131153D35997B8EB354C931C3EEB2D2DA3B1F96D5695D175387F3500B43E289 |
| SSDEEP: | 3:N8cRPAZ3TKXF0hVasHJ7:2cRPpXia81 |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2856)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3292)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1360)
Executable content was dropped or overwritten
- chrome.exe (PID: 2856)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2856)
INFO
Checks supported languages
- iexplore.exe (PID: 3156)
- iexplore.exe (PID: 3292)
- chrome.exe (PID: 1360)
- chrome.exe (PID: 2324)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 3124)
- chrome.exe (PID: 4036)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 1788)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 1028)
- chrome.exe (PID: 1608)
- chrome.exe (PID: 2856)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 280)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 956)
- chrome.exe (PID: 2436)
Reads the computer name
- iexplore.exe (PID: 3156)
- iexplore.exe (PID: 3292)
- chrome.exe (PID: 1360)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 1028)
- chrome.exe (PID: 956)
- chrome.exe (PID: 1608)
Changes internet zones settings
- iexplore.exe (PID: 3156)
Application launched itself
- iexplore.exe (PID: 3156)
- chrome.exe (PID: 1360)
Checks Windows Trust Settings
- iexplore.exe (PID: 3156)
- iexplore.exe (PID: 3292)
Reads settings of System Certificates
- iexplore.exe (PID: 3156)
- iexplore.exe (PID: 3292)
- chrome.exe (PID: 3928)
Reads internet explorer settings
- iexplore.exe (PID: 3292)
Manual execution by user
- chrome.exe (PID: 1360)
Reads the hosts file
- chrome.exe (PID: 1360)
- chrome.exe (PID: 3928)
Reads the date of Windows installation
- iexplore.exe (PID: 3156)
- chrome.exe (PID: 1608)
Creates files in the user directory
- iexplore.exe (PID: 3156)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3156)
Changes settings of System certificates
- iexplore.exe (PID: 3156)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=724 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1012 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1880 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6d42d988,0x6d42d998,0x6d42d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1056,14600459182487668234,6047650840057108246,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
20 309
Read events
20 049
Write events
249
Delete events
11
Modification events
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30912231 | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 219282750 | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30912232 | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3156) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
108
Text files
236
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6149D684-550.pma | — | |
MD5:— | SHA256:— | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:0B386E545EA55999453373429254B069 | SHA256:FE808D810397A0A06B233A06BCECDB5ABB699EB2B54D349C1485D7AFD7B802D6 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:8C75BE6598D552ECEFE50B149BB2BA53 | SHA256:E26D2A3B86B05AFCDCB09F84172E9FA9EDE1A24B4294916DDD573679539F3BC4 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:FCF8152EBE8211374074451B86E877E0 | SHA256:5E6C3666F70EF6E8AEC368F71C6E0B3DB69EF530C7D2D36C9CBE8E3DE60ED808 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:6E6E33B11BBFC3EDE577044EB9F43EEC | SHA256:7BC2B47C7B67604188BA9453AA9AC2E0833C4701ACE0A9CD37D9633F71404792 | |||
| 1360 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | binary | |
MD5:28DDDCCD31076112B375A6984A4F3FDC | SHA256:07F81705027EA89F5F766F2FADF98431DC29F062E0024A2D9C165DD2A12915EB | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:0062794FA62B22C483A3DBB6515F1770 | SHA256:65D41A45837BE14E343D8DAFB3D154DD9812D2F166045AAA9C3C5BB826E0D581 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6DFE.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
95
DNS requests
55
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | iexplore.exe | GET | 200 | 67.27.159.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?578500d736587b57 | US | compressed | 4.70 Kb | whitelisted |
3156 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3156 | iexplore.exe | GET | 200 | 67.27.159.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?58c0b4f734840f3d | US | compressed | 4.70 Kb | whitelisted |
3156 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lqlsk6mqjnfj2pe42zbq5tboou_2699/jflookgnkcckhobaglndicnbbgbonegd_2699_all_ay7b7jsxeop2v4i5fxamxepufa.crx3 | US | binary | 5.67 Kb | whitelisted |
3156 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
3928 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 47.0 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 5.39 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODNjQUFXN0xyYnNNZ1UyTjZEQjNiZzhuQQ/4.10.2209.0_oimompecagnajdejgnnjijobebaeigek.crx | US | binary | 12.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.64.140.6:443 | streamtape.com | Cloudflare Inc | US | unknown |
3156 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3156 | iexplore.exe | 67.27.159.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
3156 | iexplore.exe | 8.253.207.120:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3292 | iexplore.exe | 172.64.141.6:443 | streamtape.com | Cloudflare Inc | US | suspicious |
3156 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3156 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3292 | iexplore.exe | 172.64.140.6:443 | streamtape.com | Cloudflare Inc | US | unknown |
3928 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
streamtape.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
3928 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |