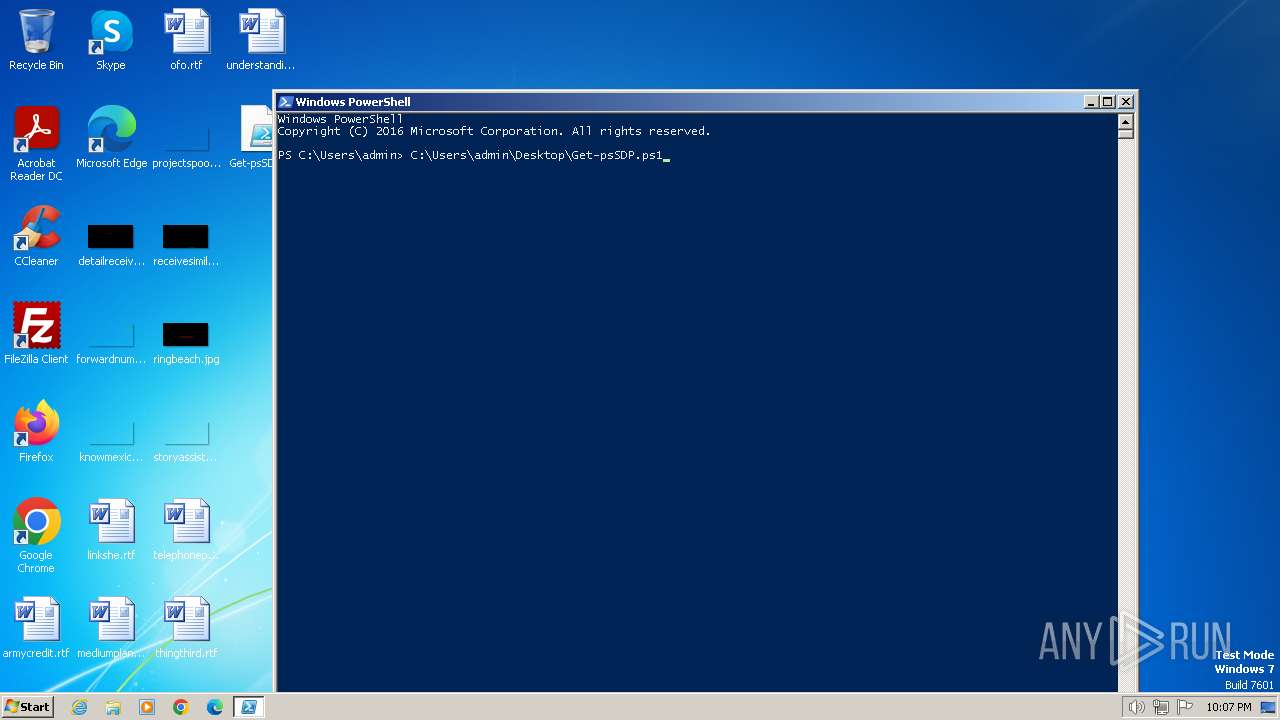
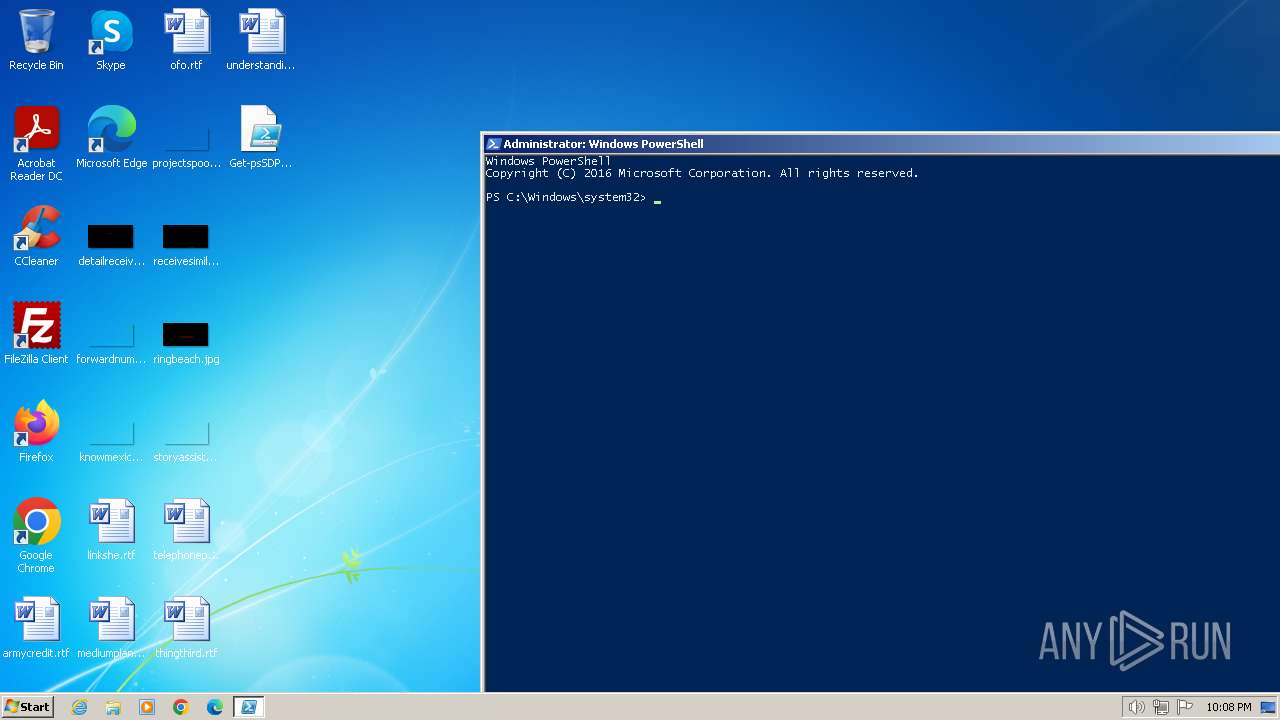
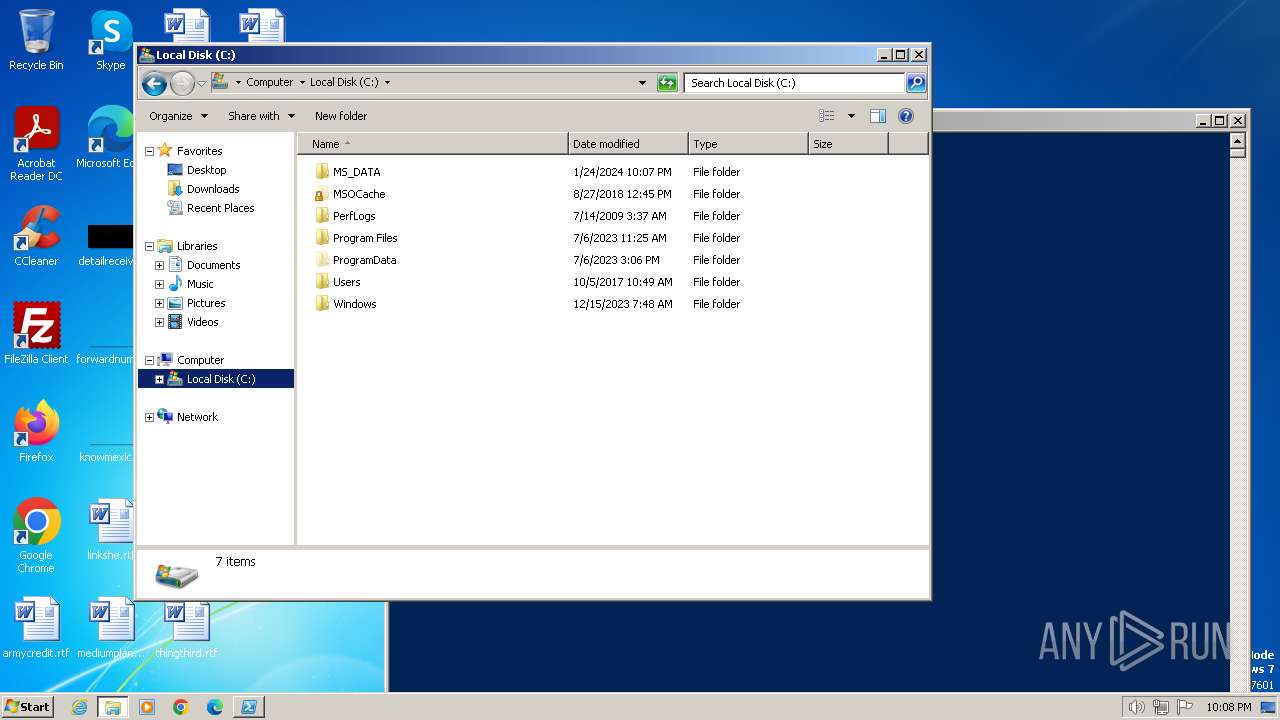
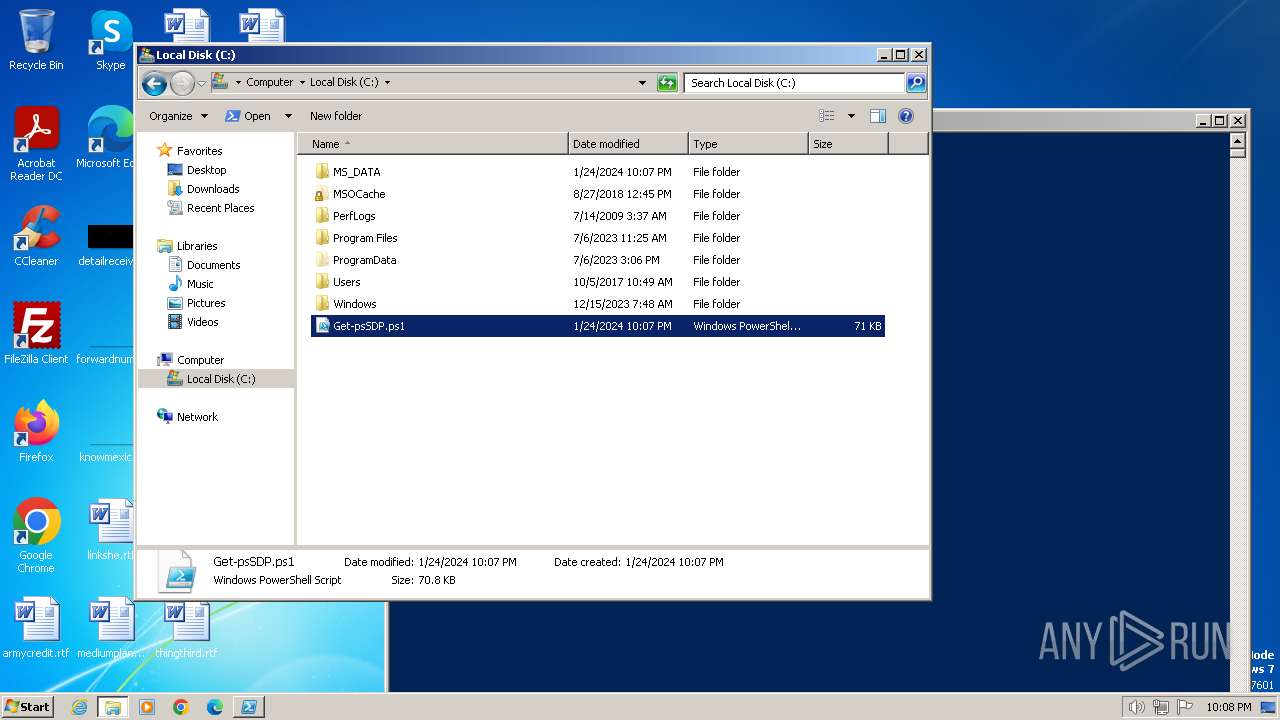
| File name: | Get-psSDP.ps1 |
| Full analysis: | https://app.any.run/tasks/198fffbb-2c97-4286-b451-fd0c4c0659f6 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2024, 22:05:57 |
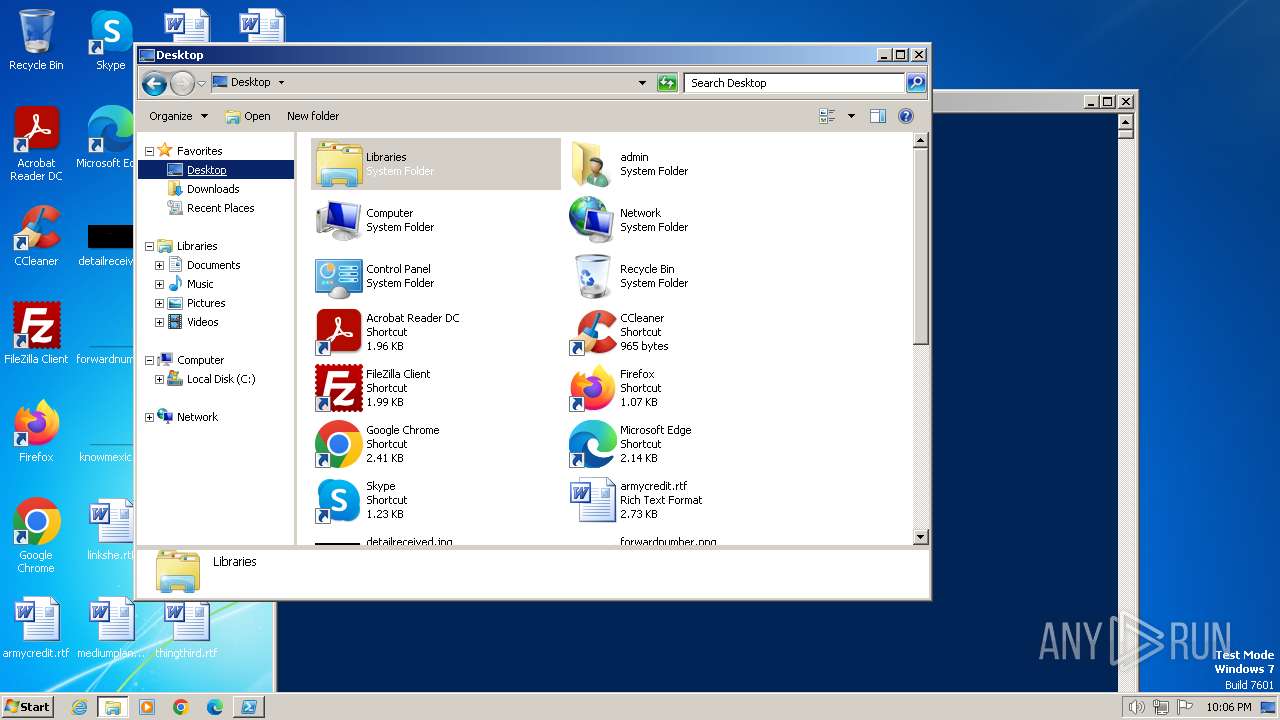
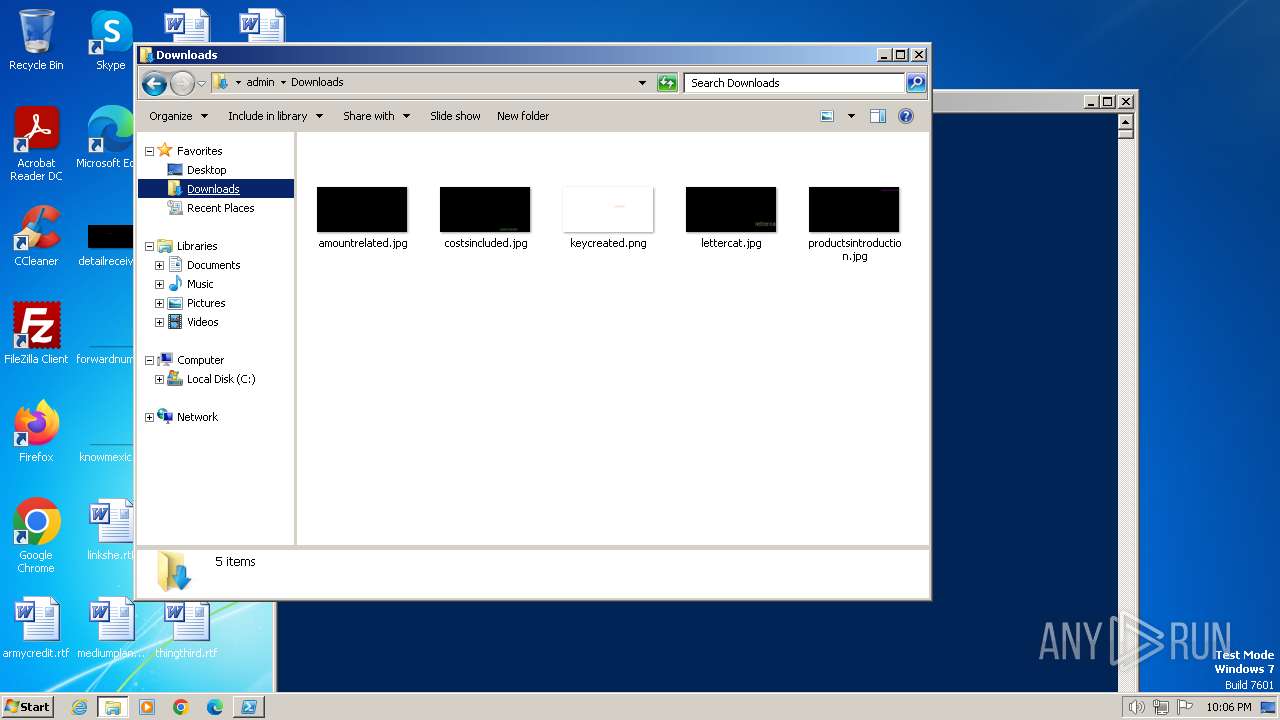
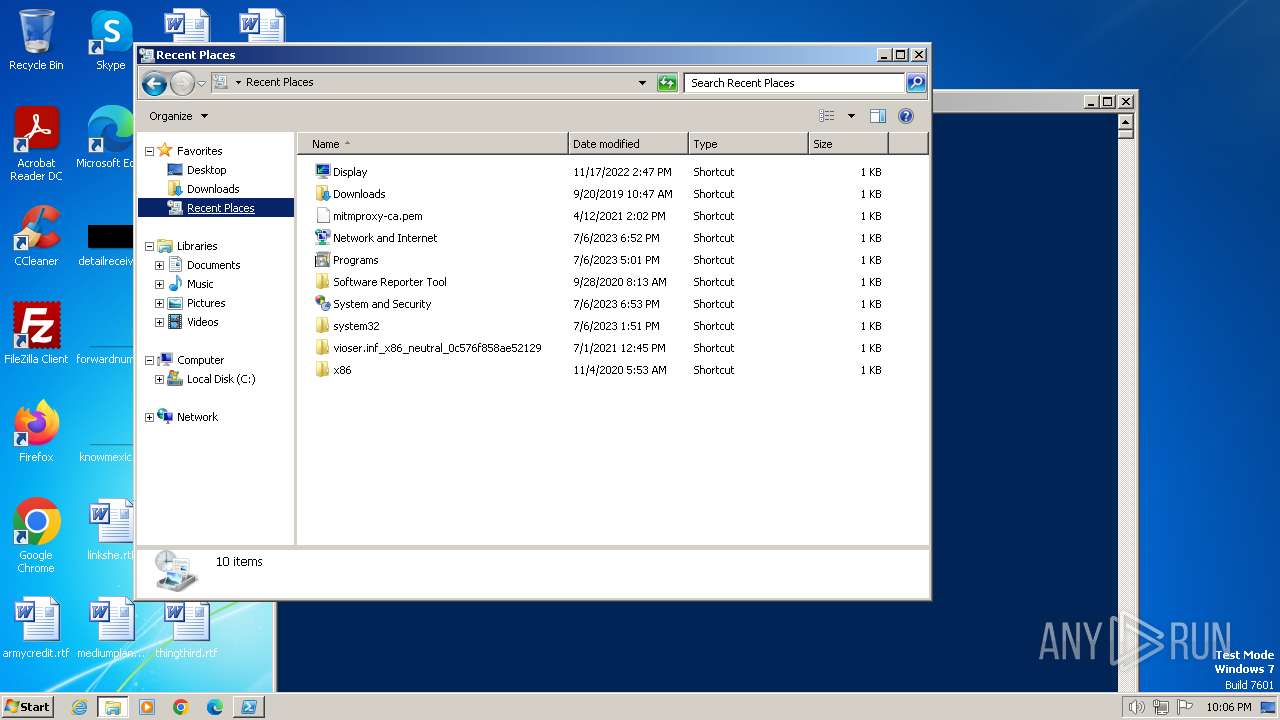
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | UTF-8 Unicode text, with very long lines, with CRLF line terminators |
| MD5: | C1D03A8CD8648379E8F484158CE7C2DE |
| SHA1: | 88BA5A8B72AC544CCE32B8FA55573EB510CA8A21 |
| SHA256: | 9130AEDF61BBD9B5BA049C7D0ED8A5DD70E4BD0B6EBD323576C780EF94178141 |
| SSDEEP: | 1536:+cd+SzUq+e54qaRMxRAEO1FD3luVFq6Wp:+cd+0Uo4qaixWEOnD3lph |
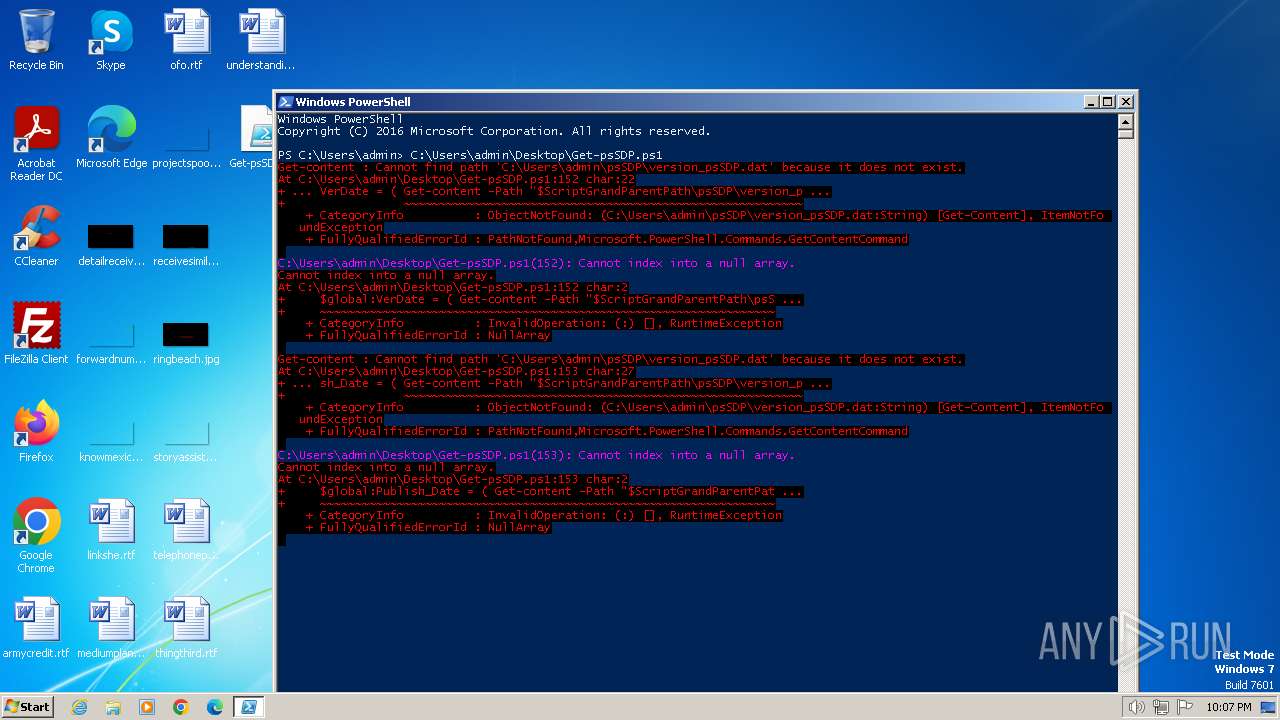
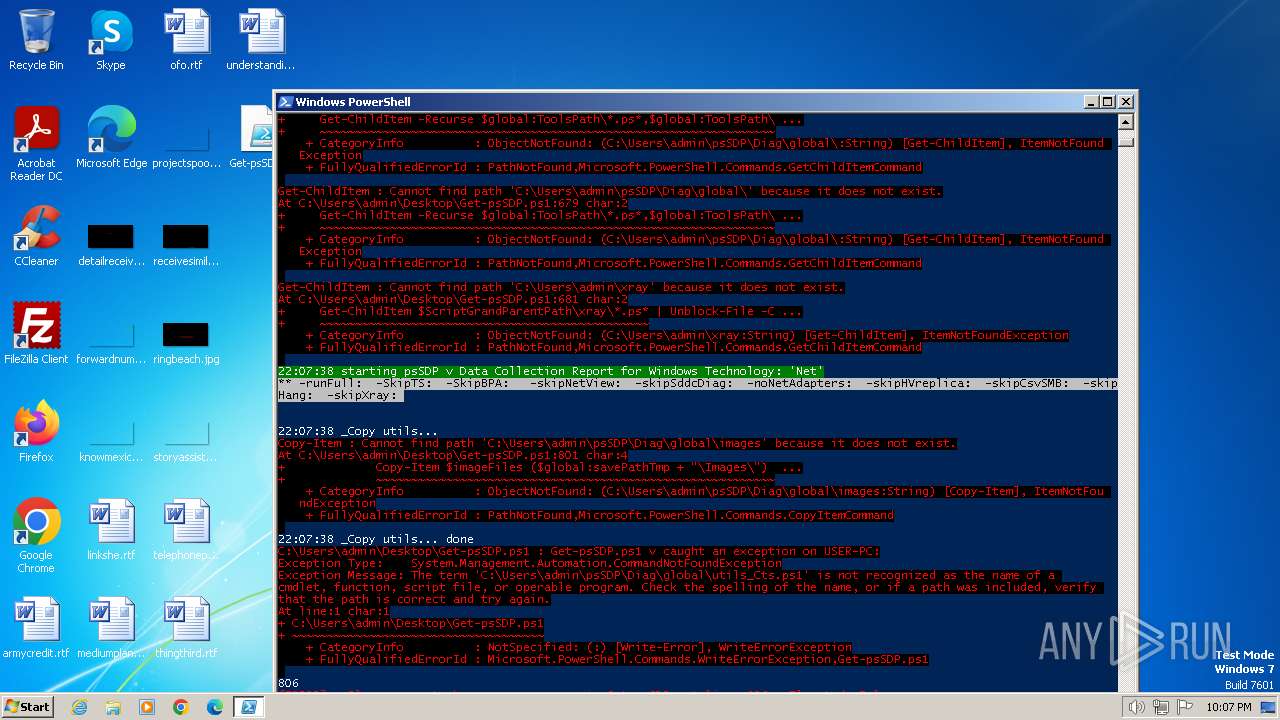
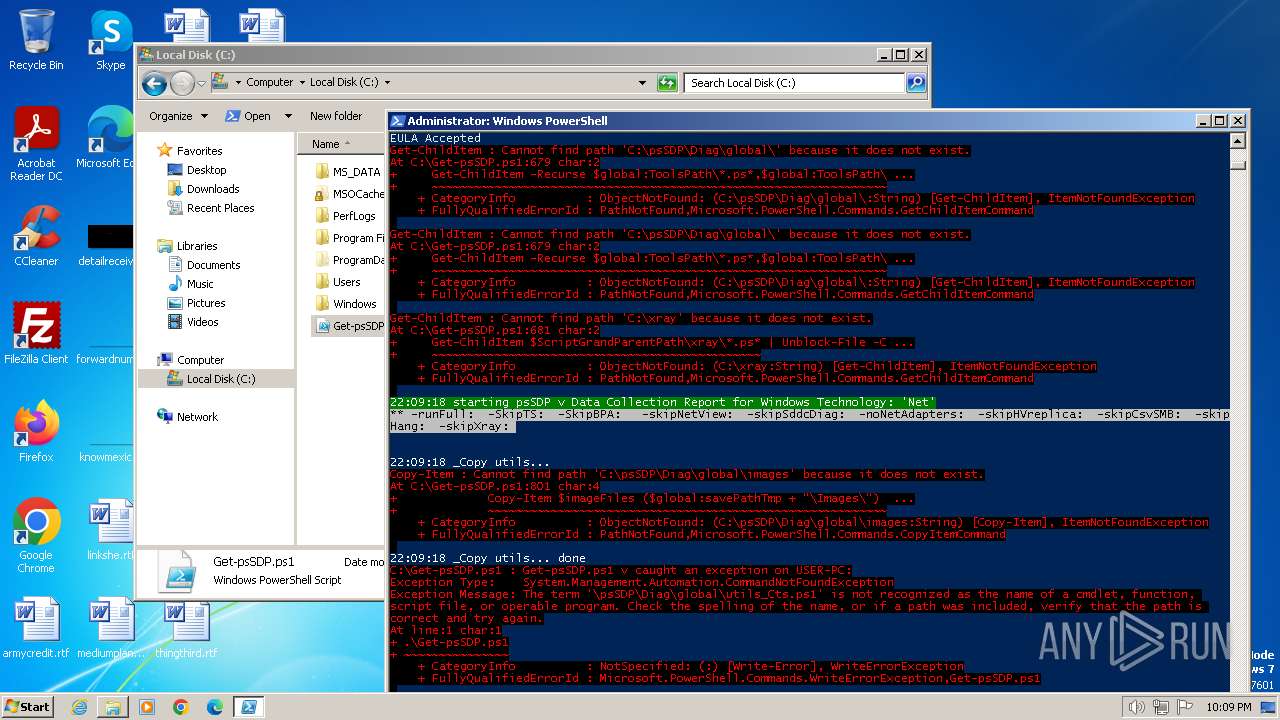
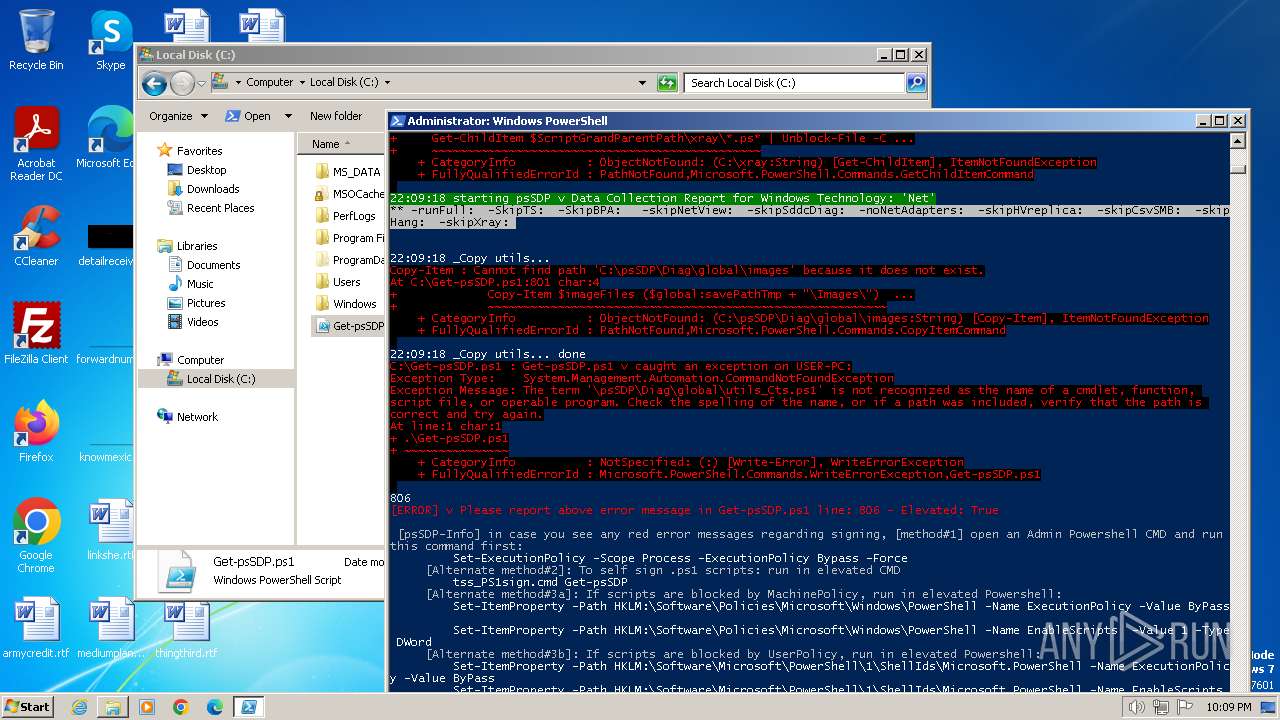
MALICIOUS
Starts Visual C# compiler
- powershell.exe (PID: 3072)
- powershell.exe (PID: 3504)
Drops the executable file immediately after the start
- csc.exe (PID: 3216)
- csc.exe (PID: 4064)
SUSPICIOUS
Reads the Internet Settings
- powershell.exe (PID: 3072)
- powershell.exe (PID: 3504)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3072)
Uses .NET C# to load dll
- powershell.exe (PID: 3072)
- powershell.exe (PID: 3504)
Executable content was dropped or overwritten
- csc.exe (PID: 3216)
- csc.exe (PID: 4064)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2900)
- csc.exe (PID: 3216)
- cvtres.exe (PID: 2840)
- csc.exe (PID: 4064)
- cvtres.exe (PID: 3792)
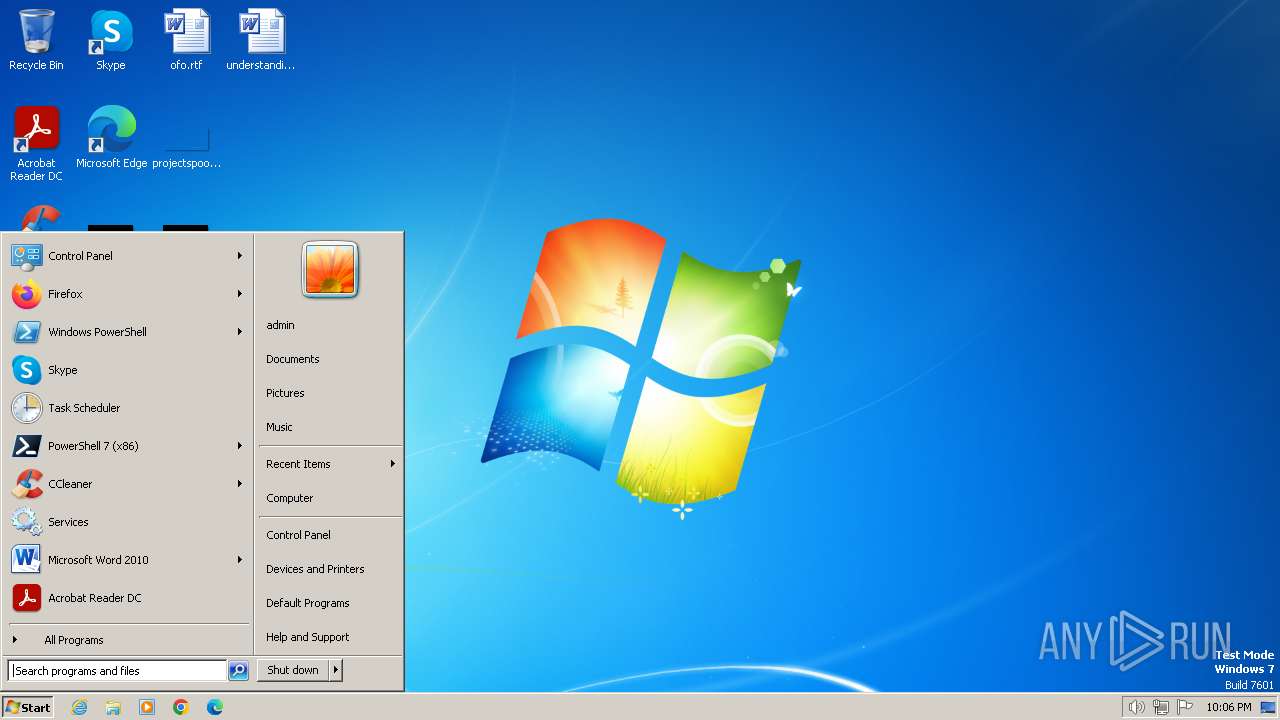
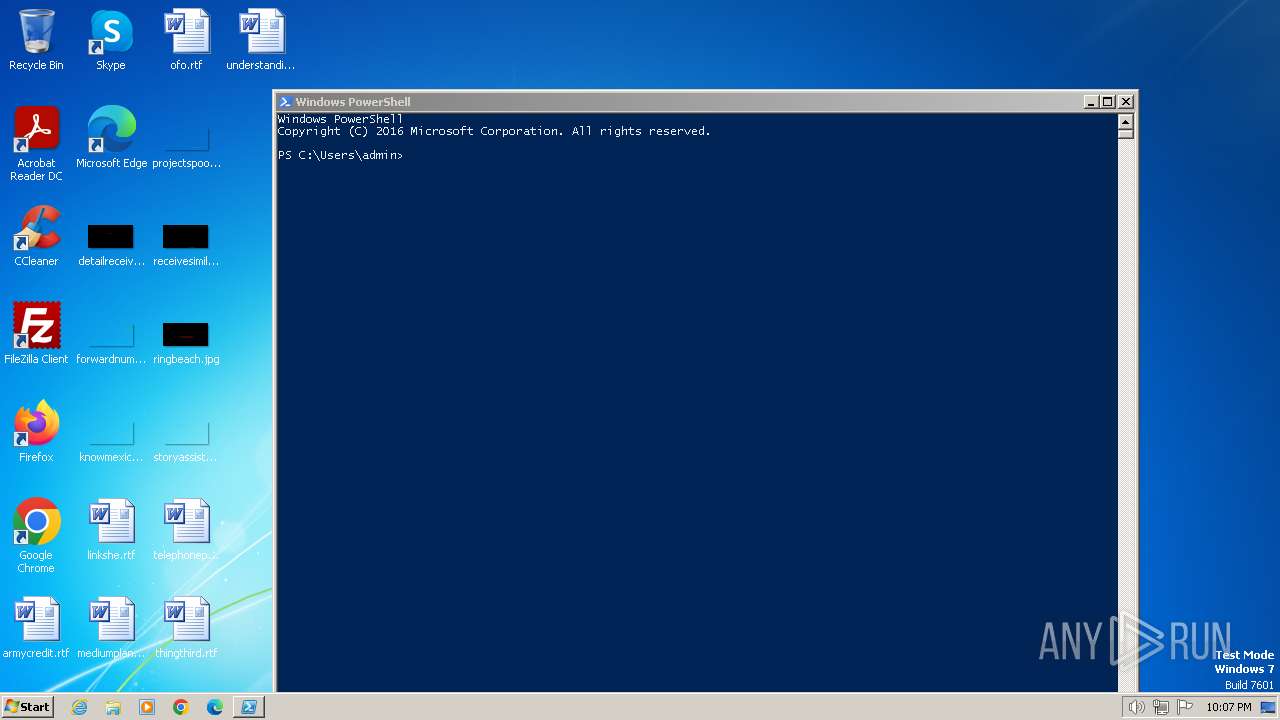
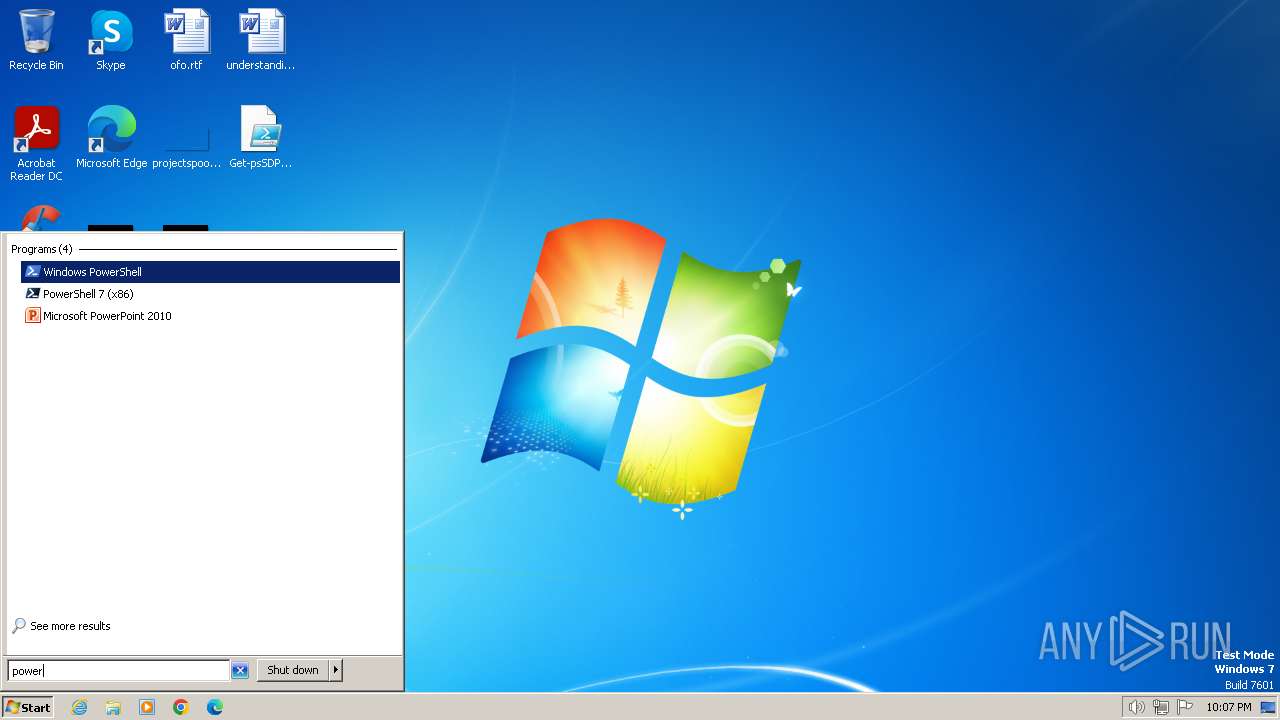
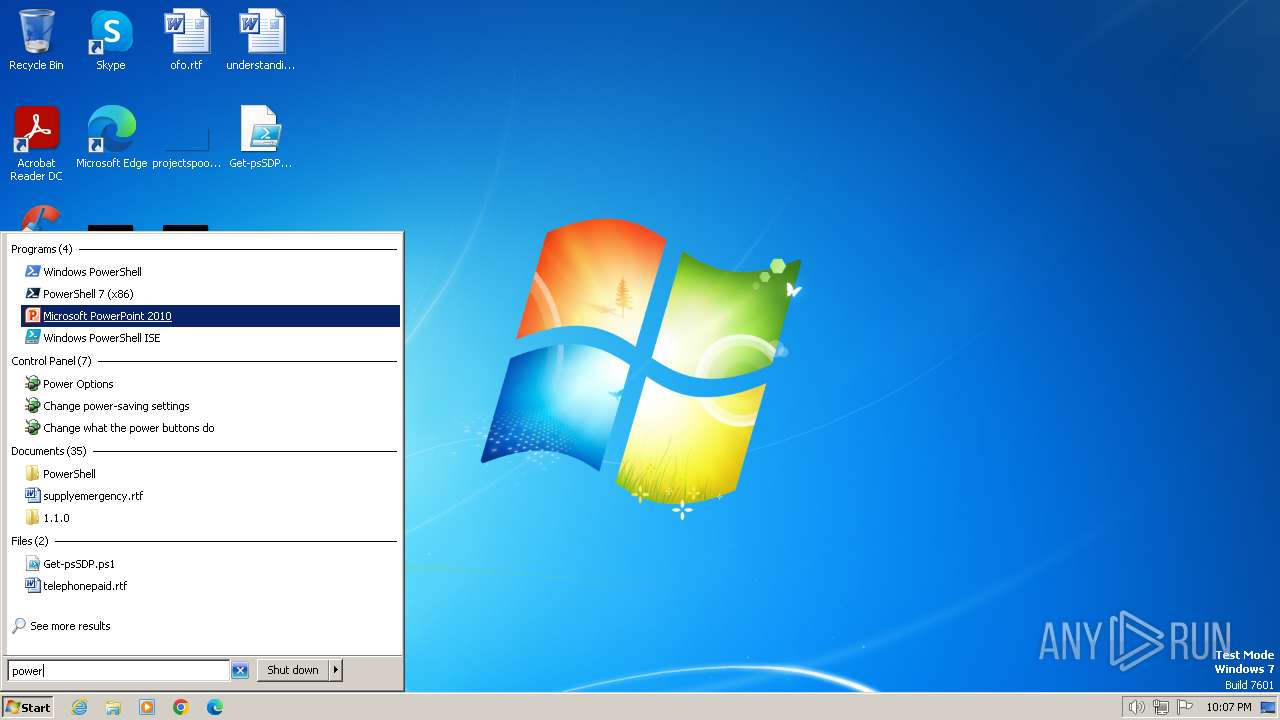
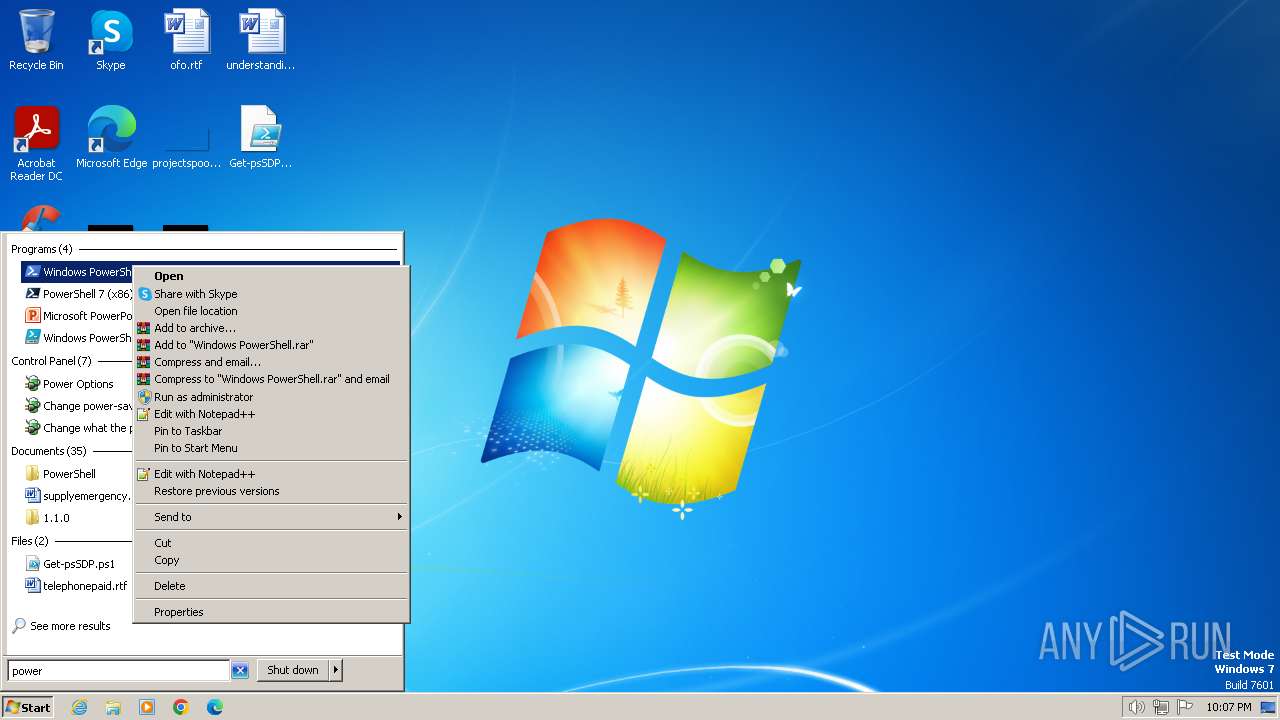
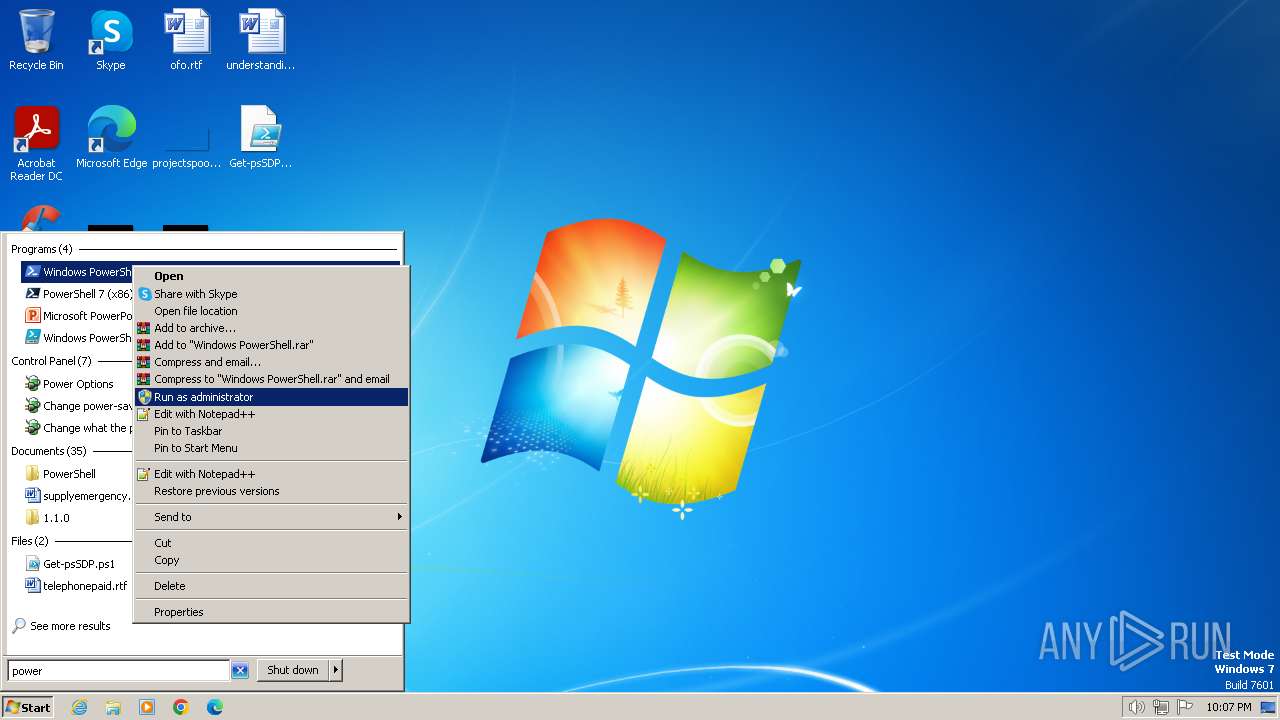
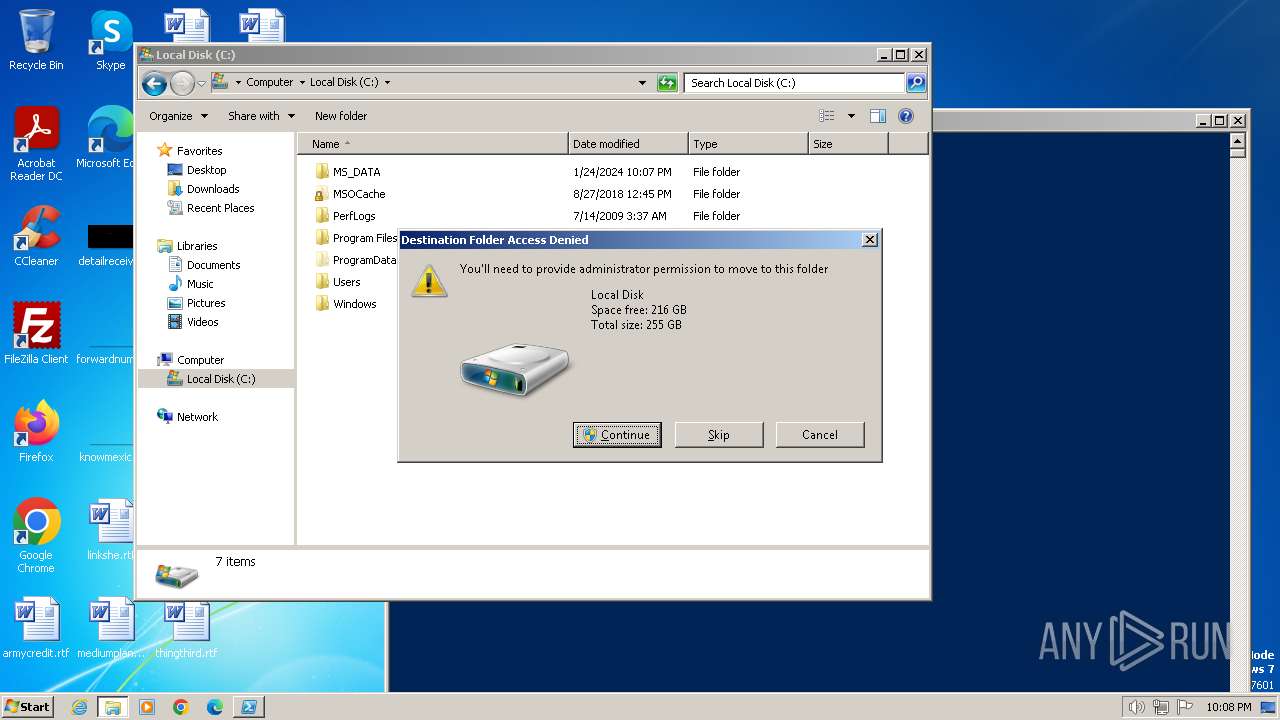
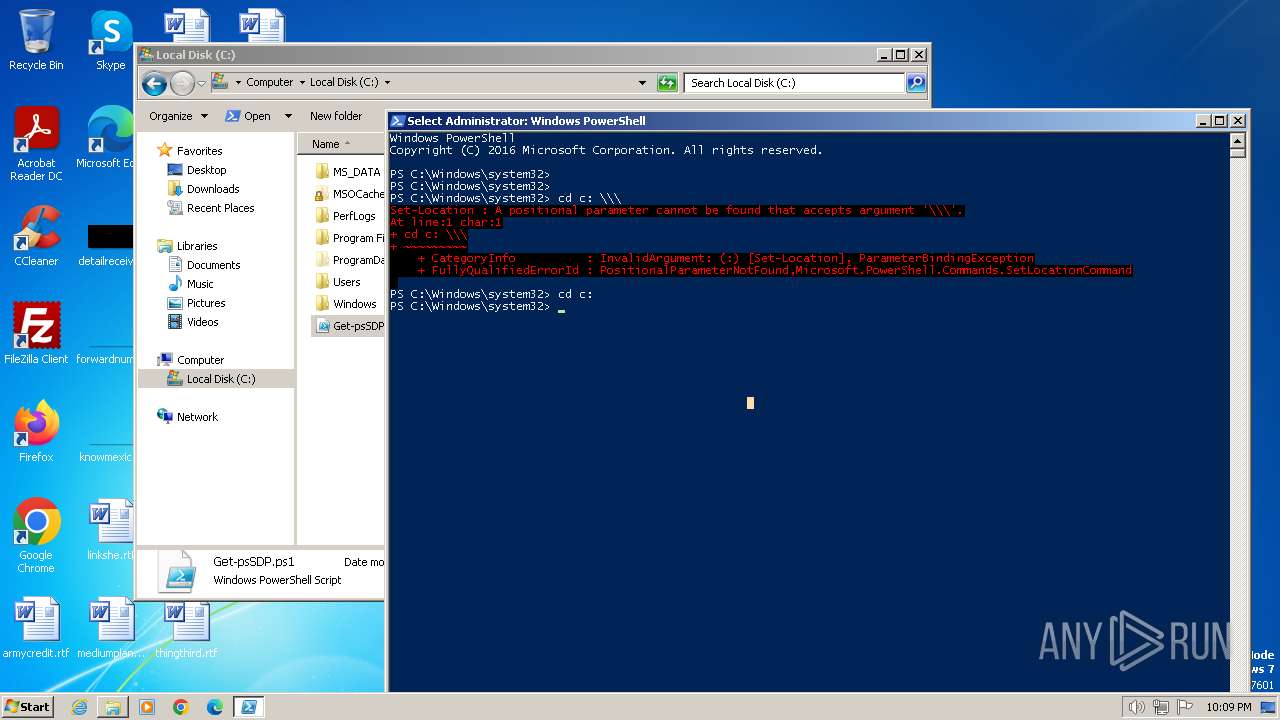
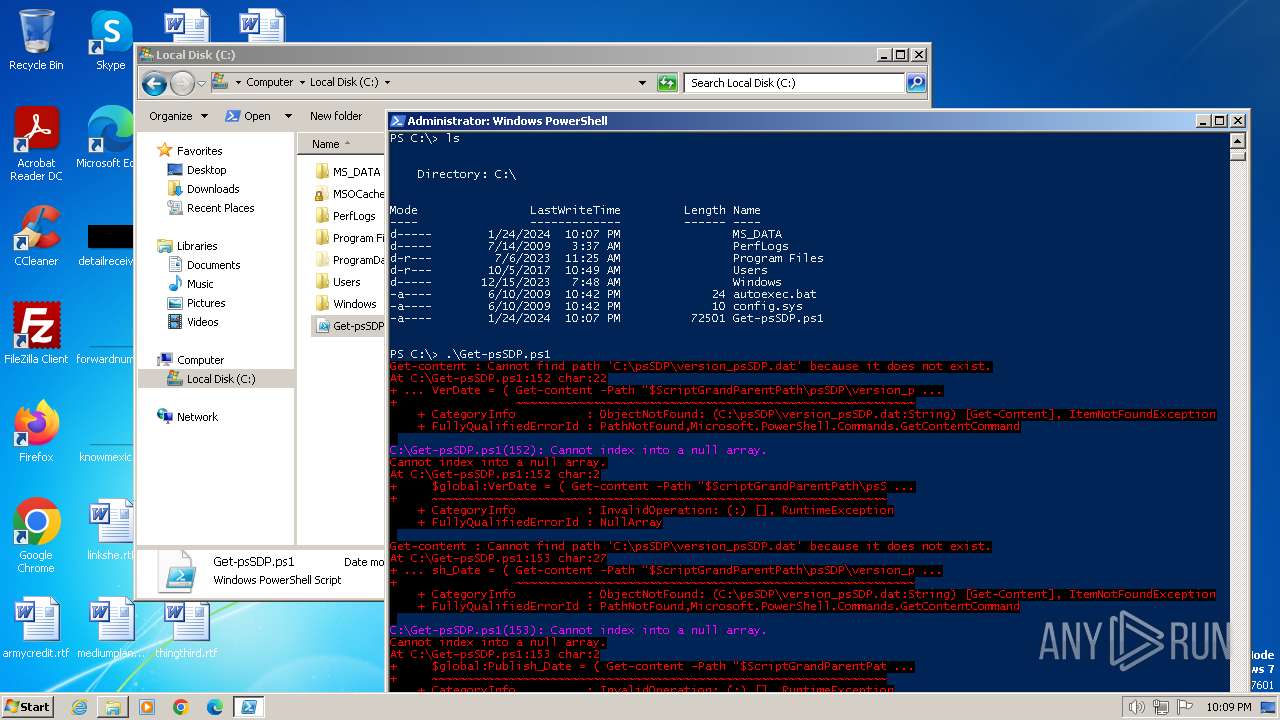
Manual execution by a user
- wmpnscfg.exe (PID: 2900)
- explorer.exe (PID: 3040)
- powershell.exe (PID: 3072)
- powershell.exe (PID: 3504)
- explorer.exe (PID: 1656)
Reads the machine GUID from the registry
- csc.exe (PID: 3216)
- cvtres.exe (PID: 2840)
- csc.exe (PID: 4064)
- cvtres.exe (PID: 3792)
Create files in a temporary directory
- cvtres.exe (PID: 2840)
- csc.exe (PID: 3216)
- csc.exe (PID: 4064)
- cvtres.exe (PID: 3792)
Application launched itself
- iexplore.exe (PID: 2628)
- iexplore.exe (PID: 2052)
Reads the computer name
- wmpnscfg.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
Total processes
63
Monitored processes
13
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1656 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1904 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2628 CREDAT:144385 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
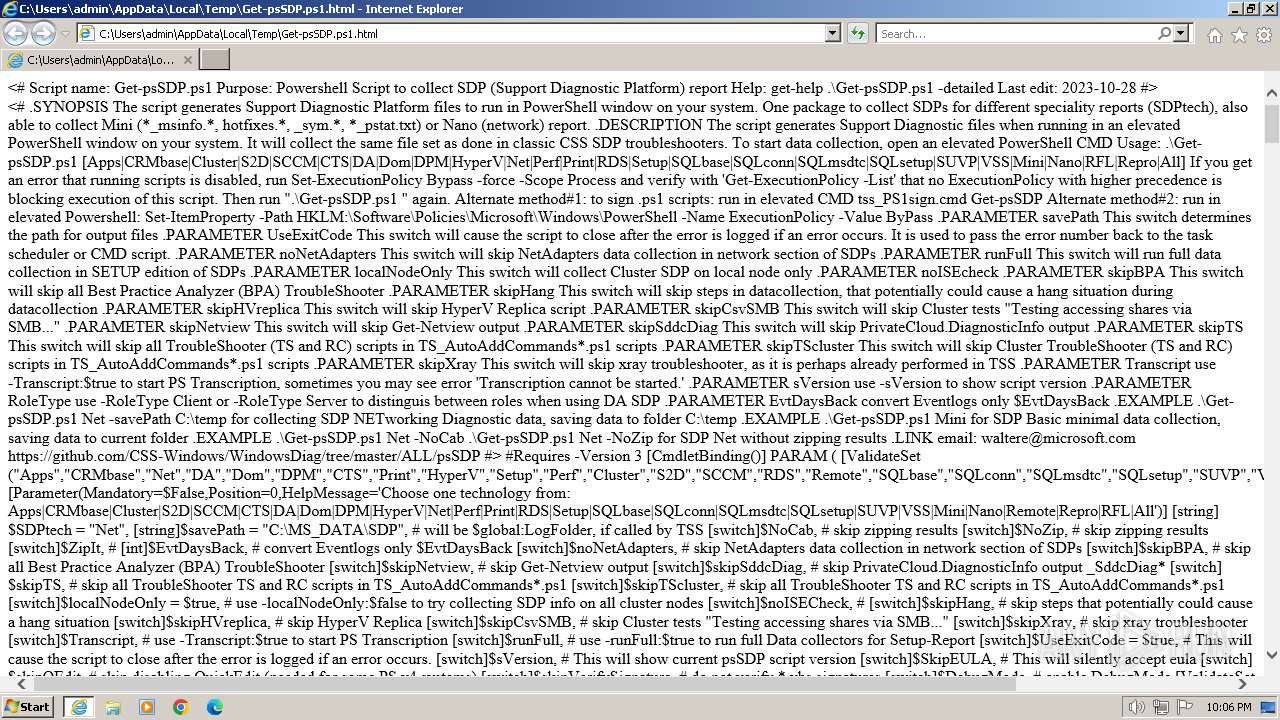
| 2628 | "C:\Program Files\Internet Explorer\iexplore.exe" "C:\Users\admin\AppData\Local\Temp\Get-psSDP.ps1.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2628 CREDAT:333057 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2840 | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESD7DB.tmp" "c:\Users\admin\AppData\Local\Temp\CSC4BA8298C95843608DAD6B668239793B.TMP" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.10.25028.0 built by: VCTOOLSD15RTM Modules
| |||||||||||||||
| 2900 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3040 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
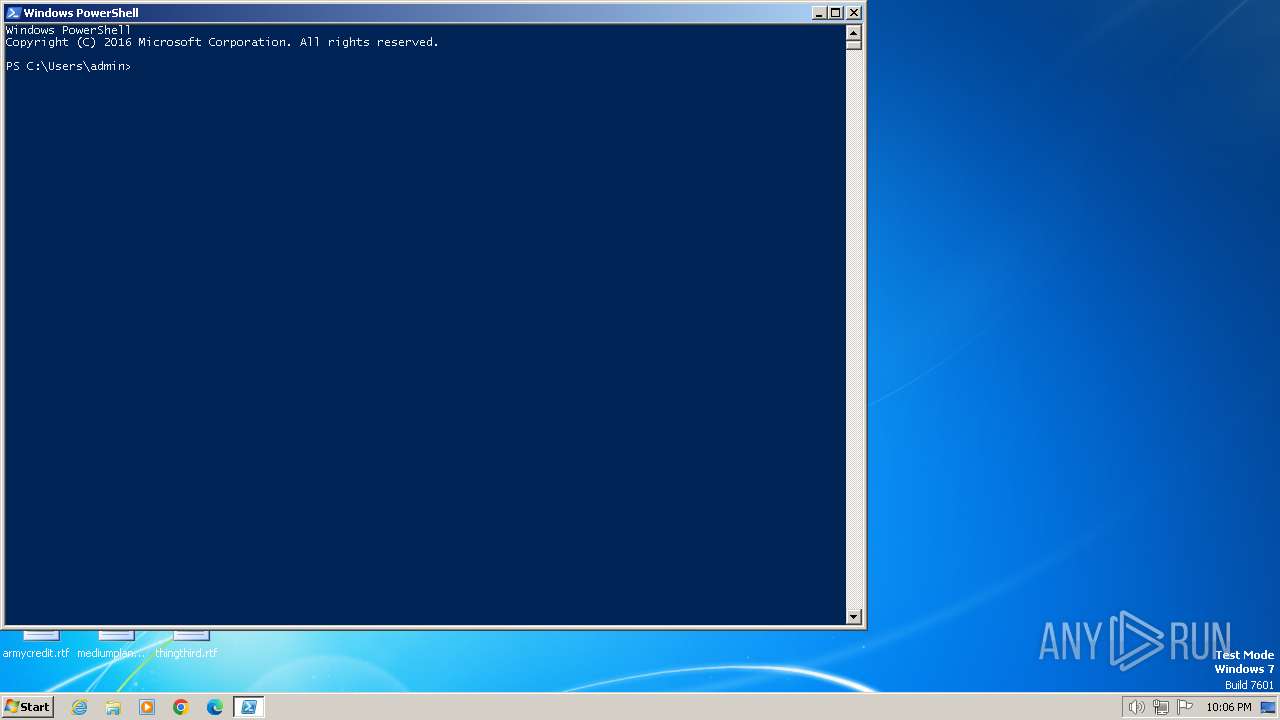
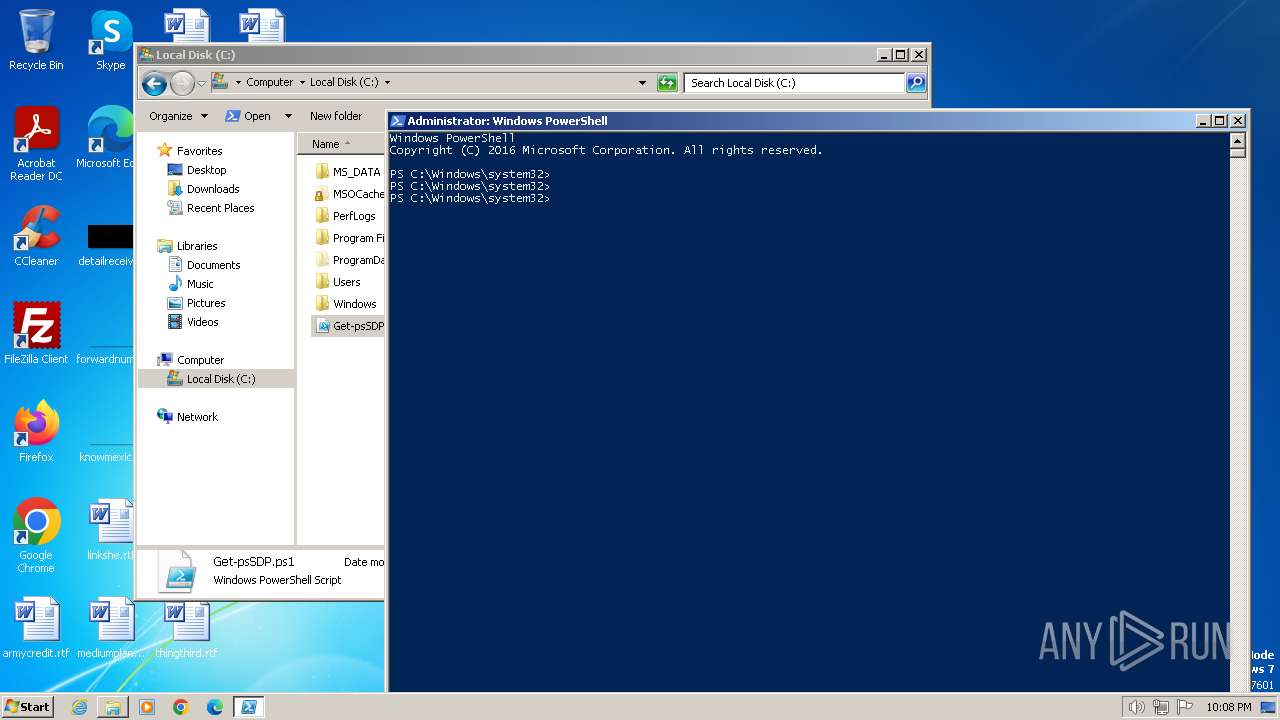
| 3072 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3216 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\gkswniy2.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
Total events
18 678
Read events
18 431
Write events
240
Delete events
7
Modification events
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2628) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
2
Suspicious files
32
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2628 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | der | |
MD5:7479499E2B80691CB5B19FD35BDFB2FE | SHA256:3FBF8523AC3F281B824092D0E89124AB62C6968478C4F2BE5E5532880DD14576 | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:BDBAAE4813F9454DDD15D9FB79720BAA | SHA256:FA3DDF24C57E191148052C705B381771833147EB2BC0D2D340525D793C344787 | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFAD7499E329F34FB4.TMP | binary | |
MD5:BCB17F72E21FAAF9D30A67596E8CDBEA | SHA256:9CE413E47EE2DA315B75830C95DE1C439DD25622D26F03ED823A2B6E836802E9 | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{C3C231F3-BB04-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:EDB2B5ACB439C57F0F3EBB2F41472A7C | SHA256:53C95A9E1B8B4E83533686494DAA342FB7C0DD1027680720511B3D384C1F620F | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF14f357.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF03F87E4105006FE2.TMP | binary | |
MD5:FE5A6E06DA58FEB29A7383F3703A855C | SHA256:37FB7C0CDBB261EADD2F6E52EDD4AA1B142436CC0B787045D42ED6885783DBEA | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{C3C231F5-BB04-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:EE5668F3F722478E9D5F079E983BA1B3 | SHA256:46A2589F45454D97875FFFFED604786AAAA8F336400B1D59278966C2FC0F0BFE | |||
| 3072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:67BC9011476C87B42100EDEB9660C156 | SHA256:1332A0F6F56E228FD1BF8D1756BBA448C457E74C26A8E2DDA9F0BA80BE65F1BC | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{C3C231F6-BB04-11EE-AE0A-12A9866C77DE}.dat | binary | |
MD5:F9001B79E76179EA32D74C47DCF51C71 | SHA256:2EC6FB11228F0F30AB45008B3517FE10BC39AAAF15E529D515E3F3B12B0EC7D2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
13
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2628 | iexplore.exe | GET | 304 | 2.22.242.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?7c5817e8f4cd7bad | unknown | — | — | unknown |
2628 | iexplore.exe | GET | 304 | 2.22.242.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?32db231de3ffc72c | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 23.53.41.250:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0754c686571bd23f | unknown | compressed | 65.2 Kb | unknown |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
2628 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 23.53.41.250:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?624d1ab720bef5f8 | unknown | compressed | 65.2 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2628 | iexplore.exe | 104.126.37.186:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2628 | iexplore.exe | 2.22.242.121:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2628 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2628 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 23.53.41.250:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |