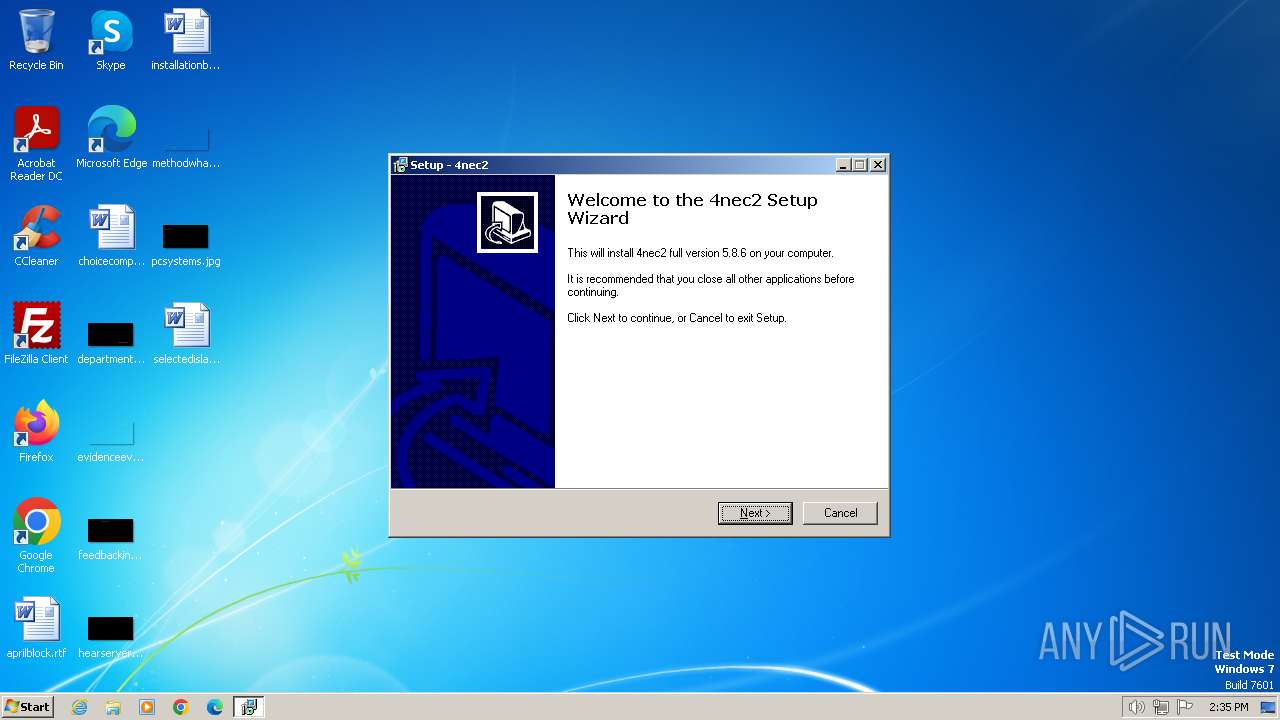
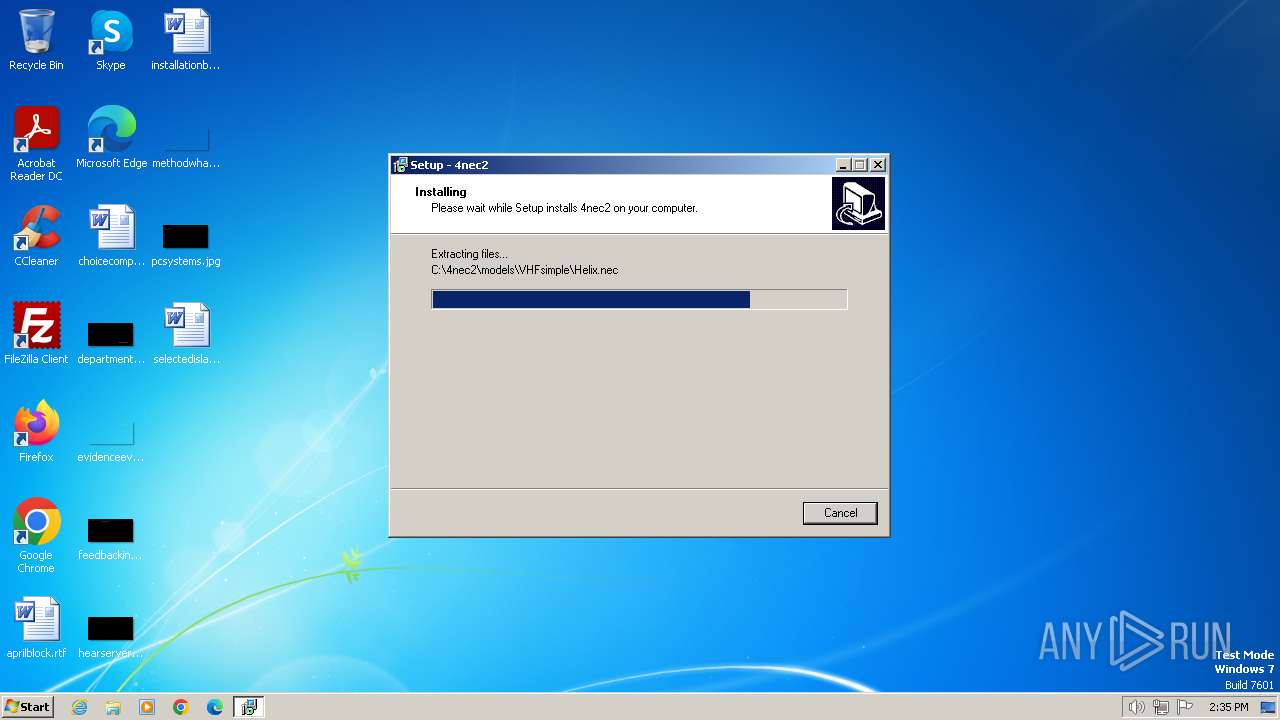
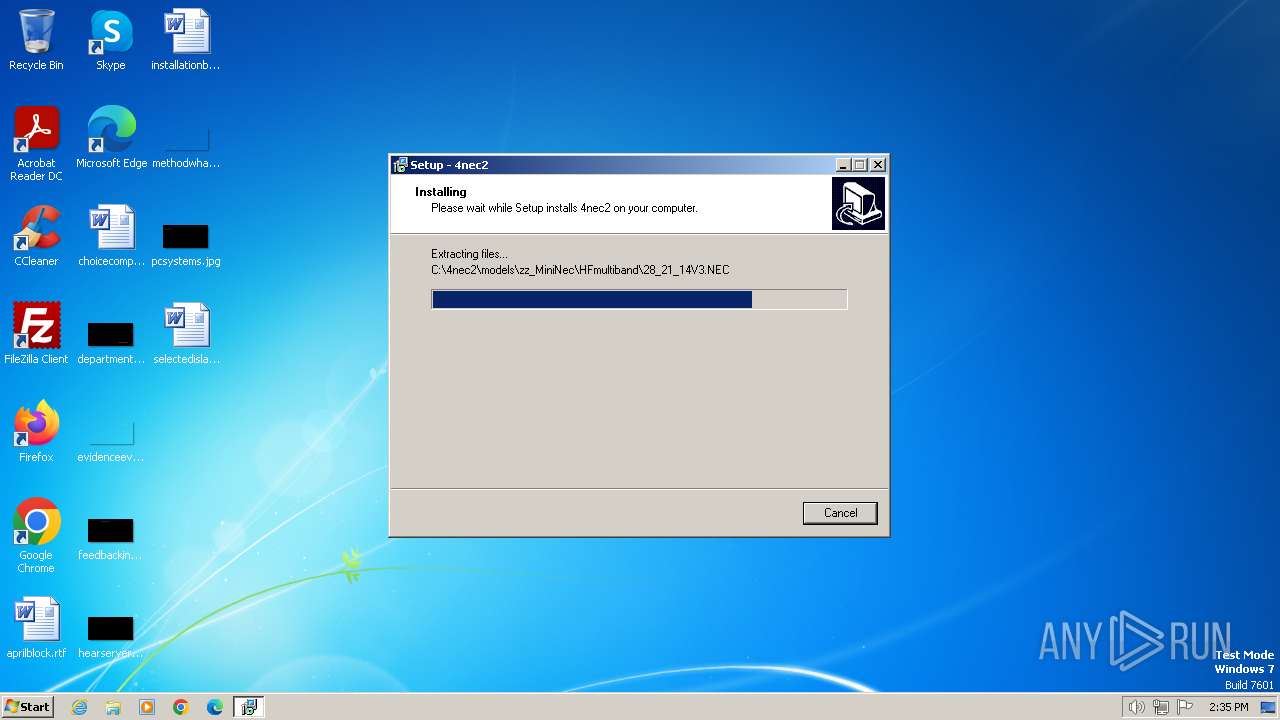
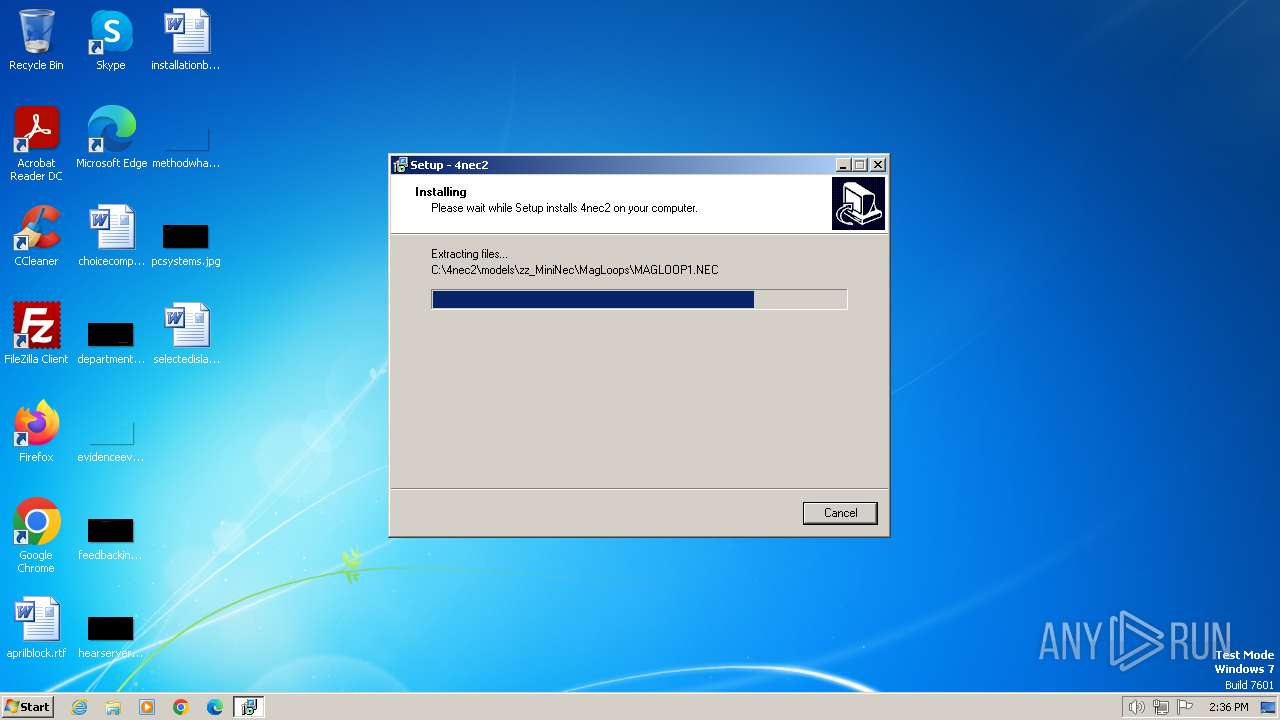
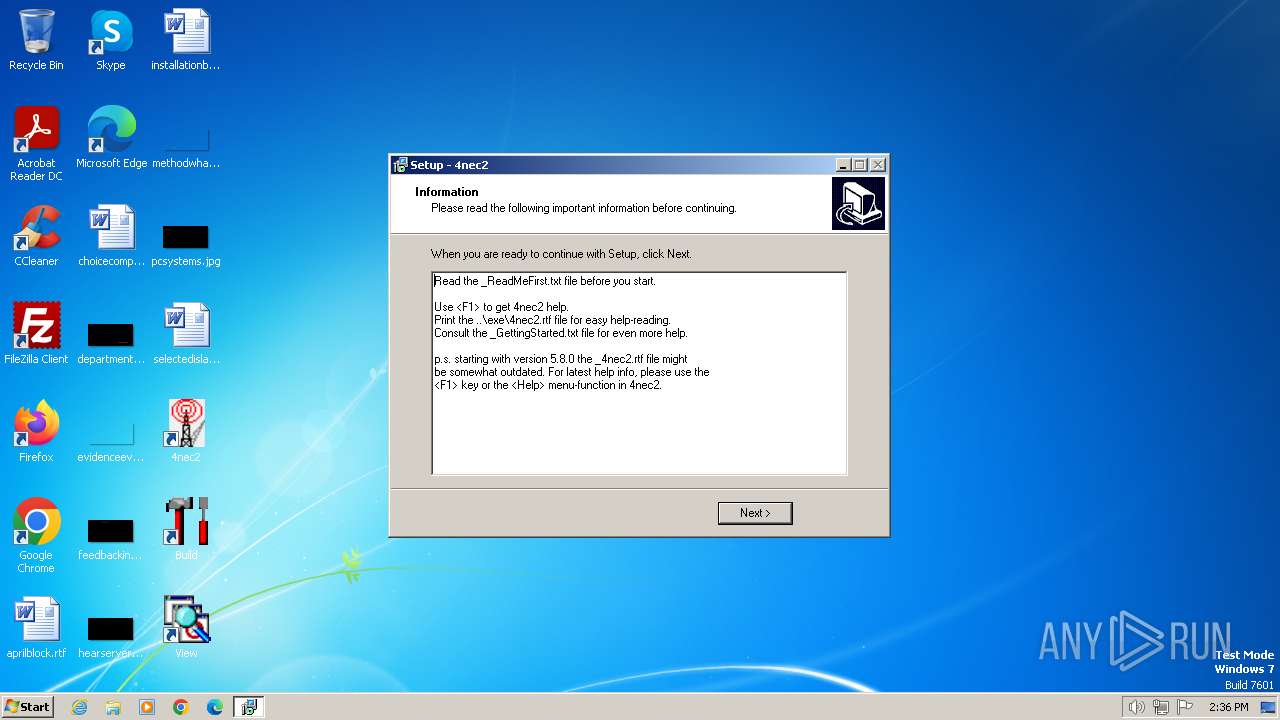
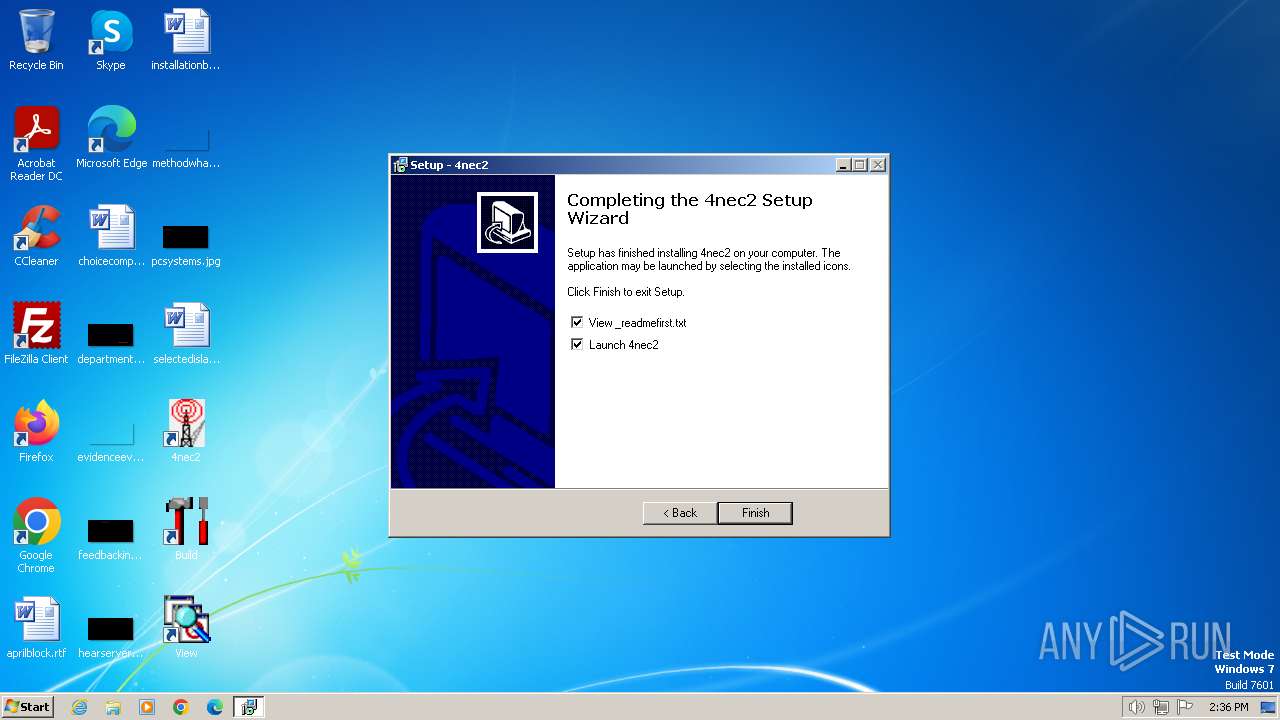
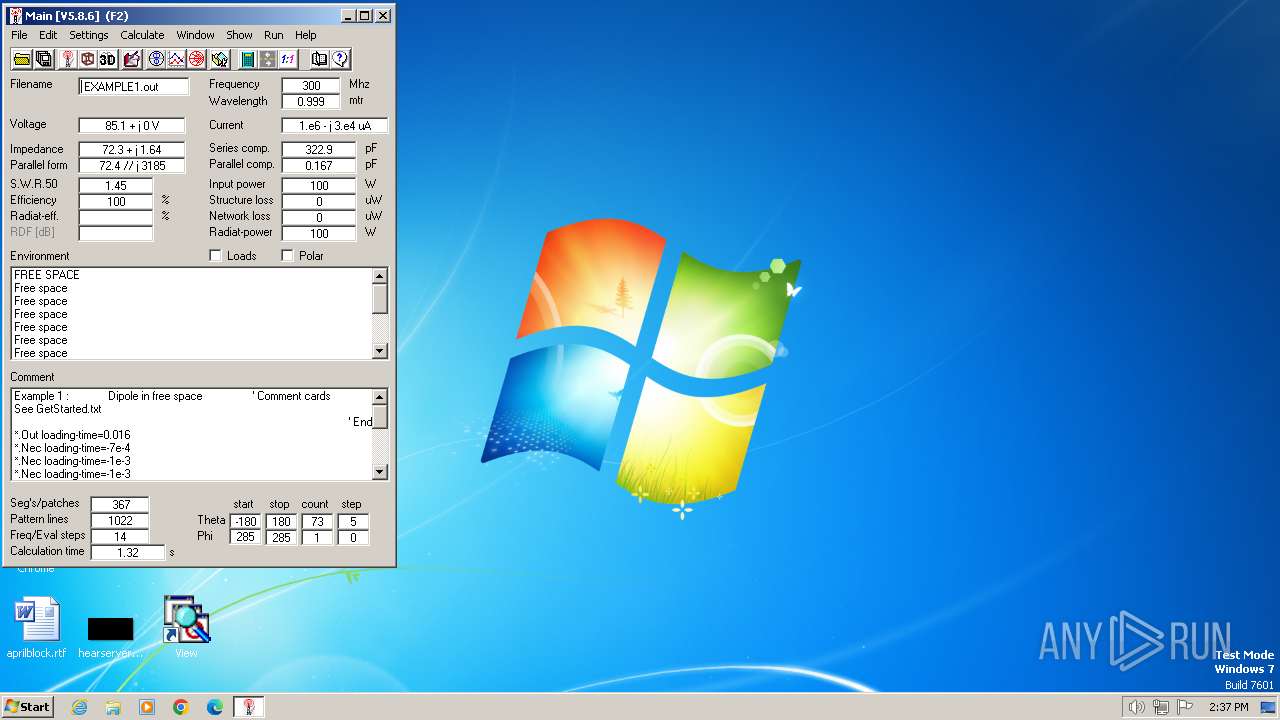
| File name: | Setup_4nec2.exe |
| Full analysis: | https://app.any.run/tasks/fd550806-9dfc-44ed-9a60-683725f64eb8 |
| Verdict: | Malicious activity |
| Analysis date: | January 21, 2024, 14:35:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D811164DD44E1982941E4731743974F8 |
| SHA1: | 3CA7C41D577CCB91C377450CBFF8D29866F811CF |
| SHA256: | 912D95968694FE1454F6111529BEB8012DFBF51A7D7AAF2FCDC375F17F079E27 |
| SSDEEP: | 98304:0E0s3kIksqHwdubFDcYZ6uK/vYhoVk8PJfvekVYZ69azcPNa2ZaMGX5nqMgsKbpN:mXf8tRYgH |
MALICIOUS
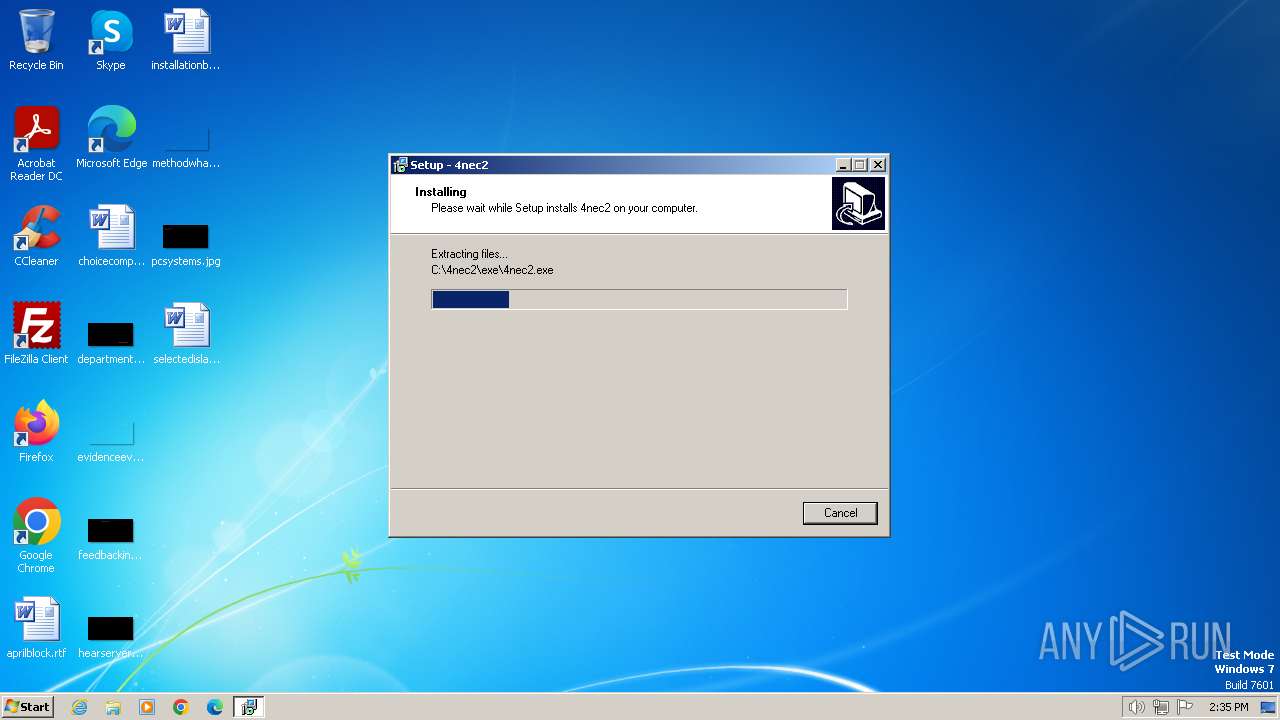
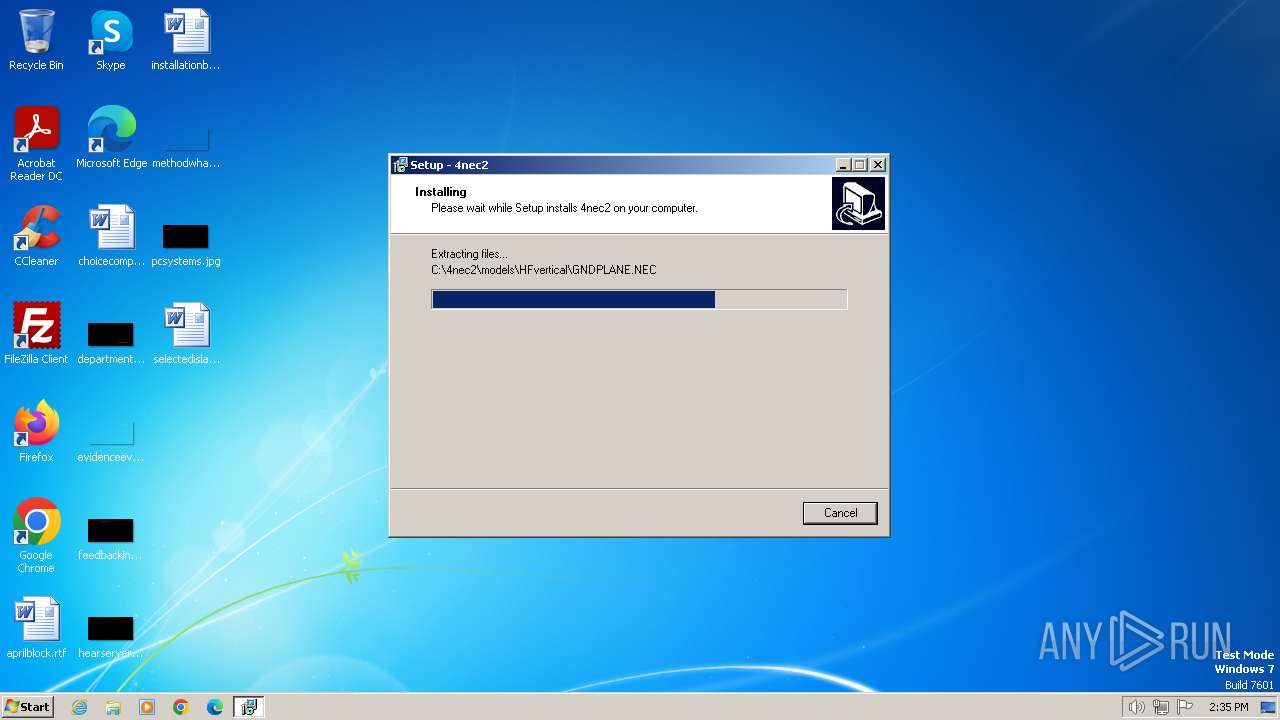
Drops the executable file immediately after the start
- Setup_4nec2.exe (PID: 2184)
- Setup_4nec2.exe (PID: 2024)
- Setup_4nec2.tmp (PID: 2016)
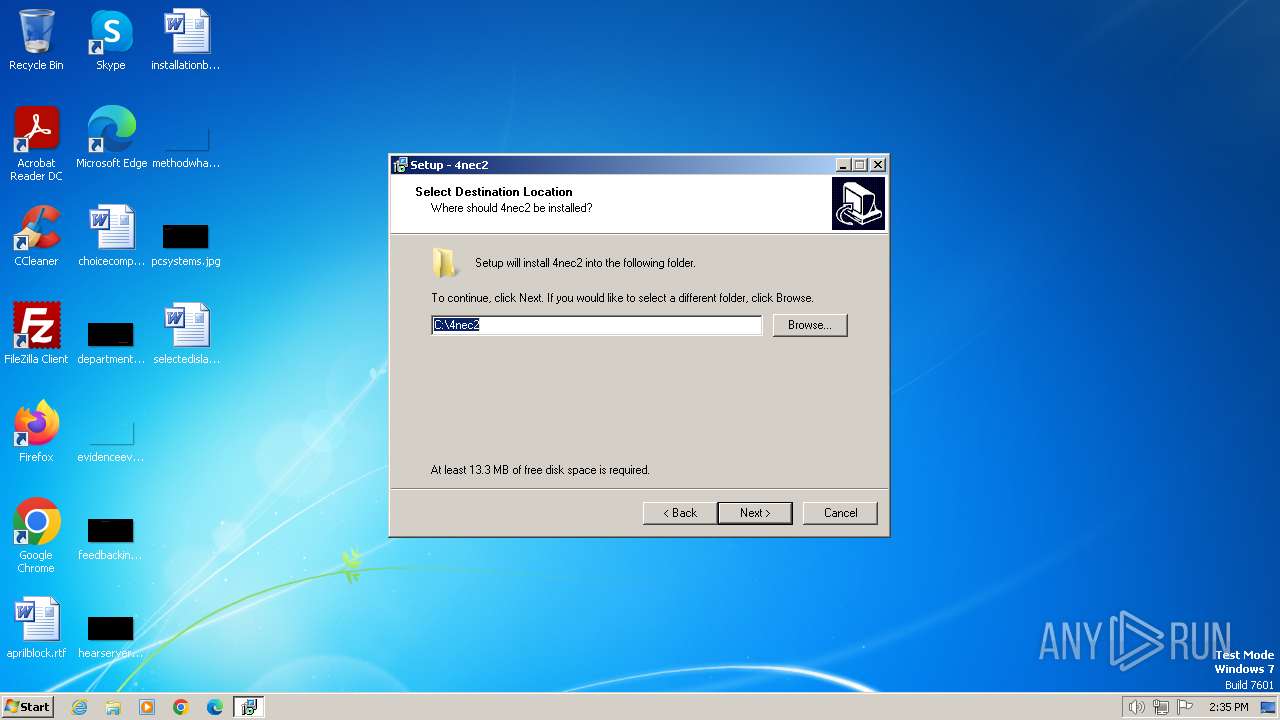
Creates a writable file in the system directory
- Setup_4nec2.tmp (PID: 2016)
Registers / Runs the DLL via REGSVR32.EXE
- Setup_4nec2.tmp (PID: 2016)
SUSPICIOUS
Executable content was dropped or overwritten
- Setup_4nec2.exe (PID: 2184)
- Setup_4nec2.exe (PID: 2024)
- Setup_4nec2.tmp (PID: 2016)
Process drops legitimate windows executable
- Setup_4nec2.tmp (PID: 2016)
Reads the Windows owner or organization settings
- Setup_4nec2.tmp (PID: 2016)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 1864)
Start notepad (likely ransomware note)
- Setup_4nec2.tmp (PID: 116)
Starts CMD.EXE for commands execution
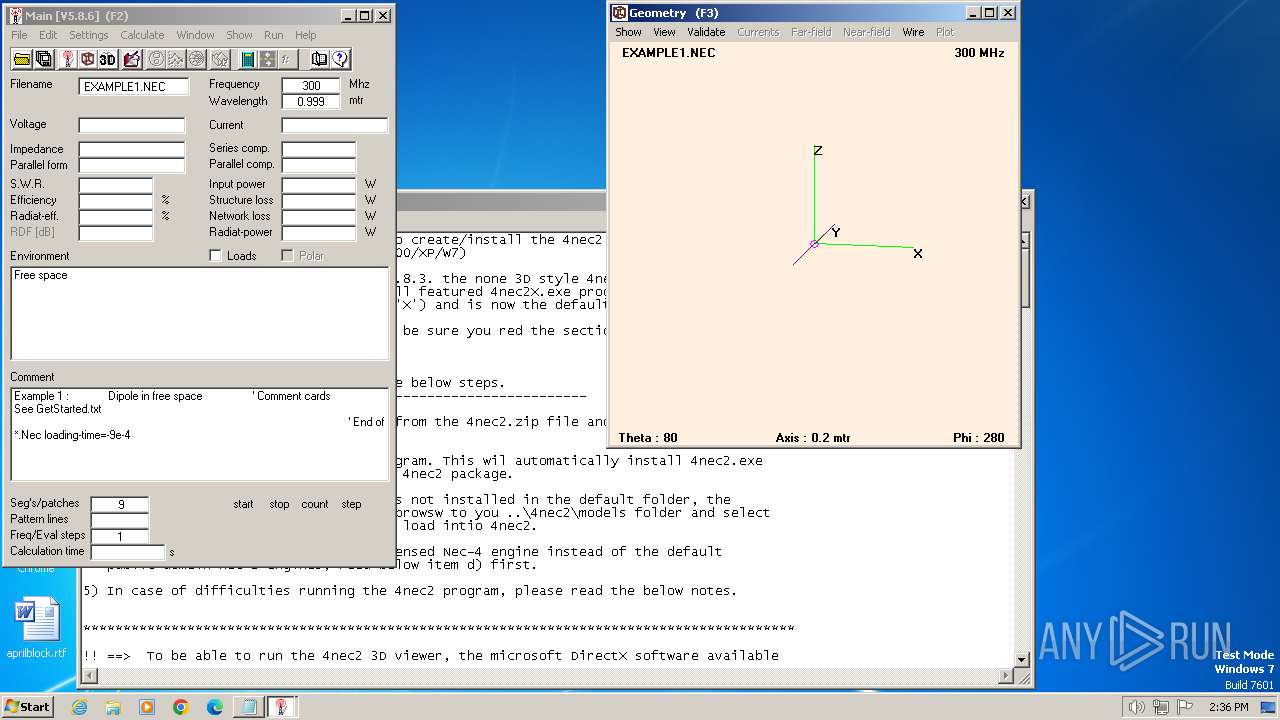
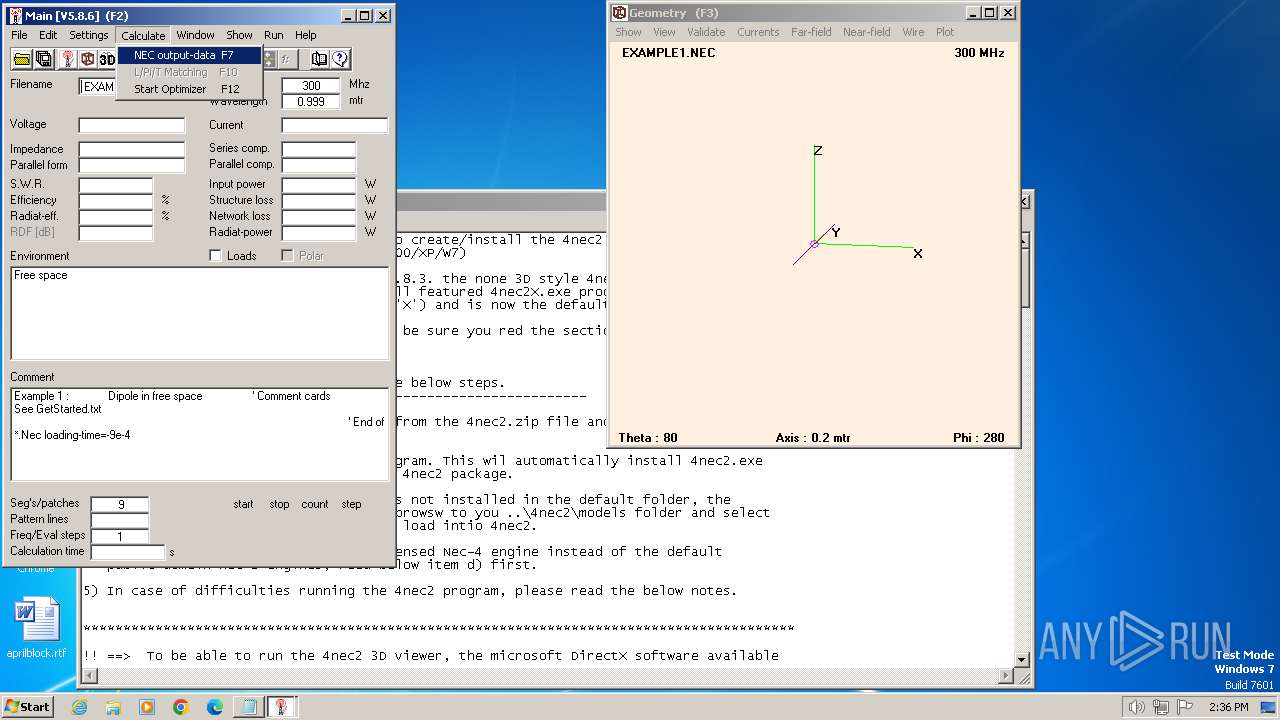
- 4nec2.exe (PID: 1808)
Executing commands from a ".bat" file
- 4nec2.exe (PID: 1808)
INFO
Checks supported languages
- Setup_4nec2.exe (PID: 2184)
- Setup_4nec2.tmp (PID: 116)
- Setup_4nec2.exe (PID: 2024)
- Setup_4nec2.tmp (PID: 2016)
- nec2dxs1K5.exe (PID: 376)
- 4nec2.exe (PID: 1808)
- nec2dxs1K5.exe (PID: 1728)
- nec2dxs1K5.exe (PID: 188)
- nec2dxs1K5.exe (PID: 2056)
- nec2dxs1K5.exe (PID: 2624)
- nec2dxs1K5.exe (PID: 2736)
- nec2dxs1K5.exe (PID: 2808)
- nec2dxs1K5.exe (PID: 2388)
- nec2dxs1K5.exe (PID: 1984)
- nec2dxs1K5.exe (PID: 2316)
- nec2dxs1K5.exe (PID: 2780)
- nec2dxs1K5.exe (PID: 2908)
- nec2dxs1K5.exe (PID: 2536)
- nec2dxs1K5.exe (PID: 2496)
- nec2dxs1K5.exe (PID: 2176)
Reads the computer name
- Setup_4nec2.tmp (PID: 116)
- Setup_4nec2.tmp (PID: 2016)
Create files in a temporary directory
- Setup_4nec2.exe (PID: 2184)
- Setup_4nec2.exe (PID: 2024)
- Setup_4nec2.tmp (PID: 2016)
- 4nec2.exe (PID: 1808)
Creates files in the program directory
- Setup_4nec2.tmp (PID: 2016)
Reads the machine GUID from the registry
- 4nec2.exe (PID: 1808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9b24 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
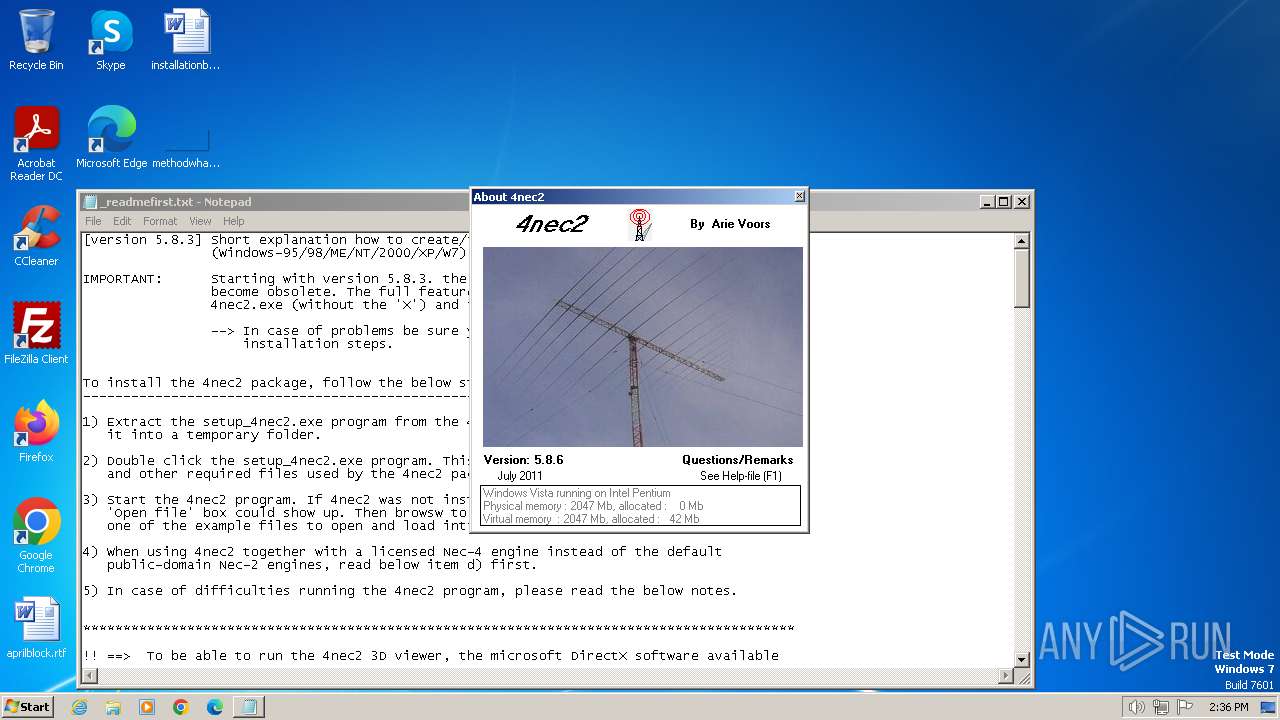
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | 4nec2@gmx.net (Use "4nec2 modeller" as the subject) |
| FileDescription: | 4nec2 Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | 4nec2 |
| ProductVersion: |
Total processes
91
Monitored processes
40
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\is-9MJEQ.tmp\Setup_4nec2.tmp" /SL5="$301AA,3960781,54272,C:\Users\admin\AppData\Local\Temp\Setup_4nec2.exe" | C:\Users\admin\AppData\Local\Temp\is-9MJEQ.tmp\Setup_4nec2.tmp | — | Setup_4nec2.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.50.0.0 Modules
| |||||||||||||||
| 188 | Nec2dXS1k5.exe | C:\4nec2\exe\nec2dxs1K5.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 376 | Nec2dXS1k5.exe | C:\4nec2\exe\nec2dxs1K5.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 584 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\Tabctl32.ocx" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 848 | C:\Windows\system32\cmd.exe /c ""C:\4nec2\exe\4nec2.bat" gen Nec2dXS1k5 NOW" | C:\Windows\System32\cmd.exe | — | 4nec2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 876 | C:\Windows\system32\cmd.exe /c ""C:\4nec2\exe\4nec2.bat" gen Nec2dXS1k5 NOW" | C:\Windows\System32\cmd.exe | — | 4nec2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1216 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\dx8vb.dll" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1572 | C:\Windows\system32\cmd.exe /c ""C:\4nec2\exe\4nec2.bat" gen Nec2dXS1k5 NOW" | C:\Windows\System32\cmd.exe | — | 4nec2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1632 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\Msflxgrd.ocx" | C:\Windows\System32\regsvr32.exe | — | Setup_4nec2.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | Nec2dXS1k5.exe | C:\4nec2\exe\nec2dxs1K5.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 968
Read events
1 954
Write events
9
Delete events
5
Modification events
| (PID) Process: | (1632) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{6262D3A0-531B-11CF-91F6-C2863C385E30} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1632) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{6319EEA0-531B-11CF-91F6-C2863C385E30} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1632) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{275DBBA0-805A-11CF-91F7-C2863C385E30} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1632) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{2334D2B1-713E-11CF-8AE5-00AA00C00905}\TypeLib |
| Operation: | write | Name: | Version |
Value: 2.0 | |||
| (PID) Process: | (1632) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{2334D2B3-713E-11CF-8AE5-00AA00C00905}\TypeLib |
| Operation: | write | Name: | Version |
Value: 2.0 | |||
| (PID) Process: | (584) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{BDC217C5-ED16-11CD-956C-0000C04E4C0A} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (584) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{7DA06D40-54A0-11CF-A521-0080C77A7786} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (584) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{2334D2B1-713E-11CF-8AE5-00AA00C00905}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (584) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{2334D2B3-713E-11CF-8AE5-00AA00C00905}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.0 | |||
| (PID) Process: | (1864) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{D5DE8D20-5BB8-11D1-A1E3-00A0C90F2731}\InProcServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
Executable files
46
Suspicious files
30
Text files
1 174
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2016 | Setup_4nec2.tmp | C:\Users\admin\AppData\Local\Temp\is-7LHEF.tmp\_isetup\_shfoldr.dll | executable | |
MD5:92DC6EF532FBB4A5C3201469A5B5EB63 | SHA256:9884E9D1B4F8A873CCBD81F8AD0AE257776D2348D027D811A56475E028360D87 | |||
| 2184 | Setup_4nec2.exe | C:\Users\admin\AppData\Local\Temp\is-9MJEQ.tmp\Setup_4nec2.tmp | executable | |
MD5:ED69E64731547EBA52476A2D2A2F7882 | SHA256:427FA988A8A8C63393693FFEB61DDEC195F000220EE55FD5112EC91682E933B0 | |||
| 2016 | Setup_4nec2.tmp | C:\Users\admin\AppData\Local\Temp\is-7LHEF.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\is-PI8R9.tmp | executable | |
MD5:FBA1DE70F5BB8544A9753957F269F897 | SHA256:87931B032A78E11A4DD491E21A66A9F24DF3FFBBEF61B5672BFE286E3903953B | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\is-ERV6I.tmp | text | |
MD5:5708F56F2AEE9D5AF652EF754C1A695B | SHA256:E8AA45B87EF665E097048232B5697324D6CAB206B70B7BE14A2D313060EFE4C7 | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\_Info.txt | text | |
MD5:FF5EAFFB8D9035D6ED18123AB54251BF | SHA256:74EB723197B34CFBBA65933717B4FA0A6308B8A18A6183C700878EDB218453B0 | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\_Out_of_env_space.txt | text | |
MD5:5708F56F2AEE9D5AF652EF754C1A695B | SHA256:E8AA45B87EF665E097048232B5697324D6CAB206B70B7BE14A2D313060EFE4C7 | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\is-SKLV7.tmp | text | |
MD5:B844164FAD30916854B95FC433772D19 | SHA256:37C311824E81821CB2C5D68C6692C37BA64F5AEFF6793DD3C9E1ACD902DFF7A3 | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\is-LF8FL.tmp | text | |
MD5:208A3AF8352E14DB32306E4A95FB1406 | SHA256:6A756FCFE40677048091098A302C880C24979AAA1A6416233FCC2F69148C00D7 | |||
| 2016 | Setup_4nec2.tmp | C:\4nec2\is-FV3QP.tmp | document | |
MD5:C0BAF5358FC6CC4CFDFE1EDE512D68EB | SHA256:CDE6E5890BBD4DB74B2002387B9BF3CAEA23A81D9F91858471CF9437873F781D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |