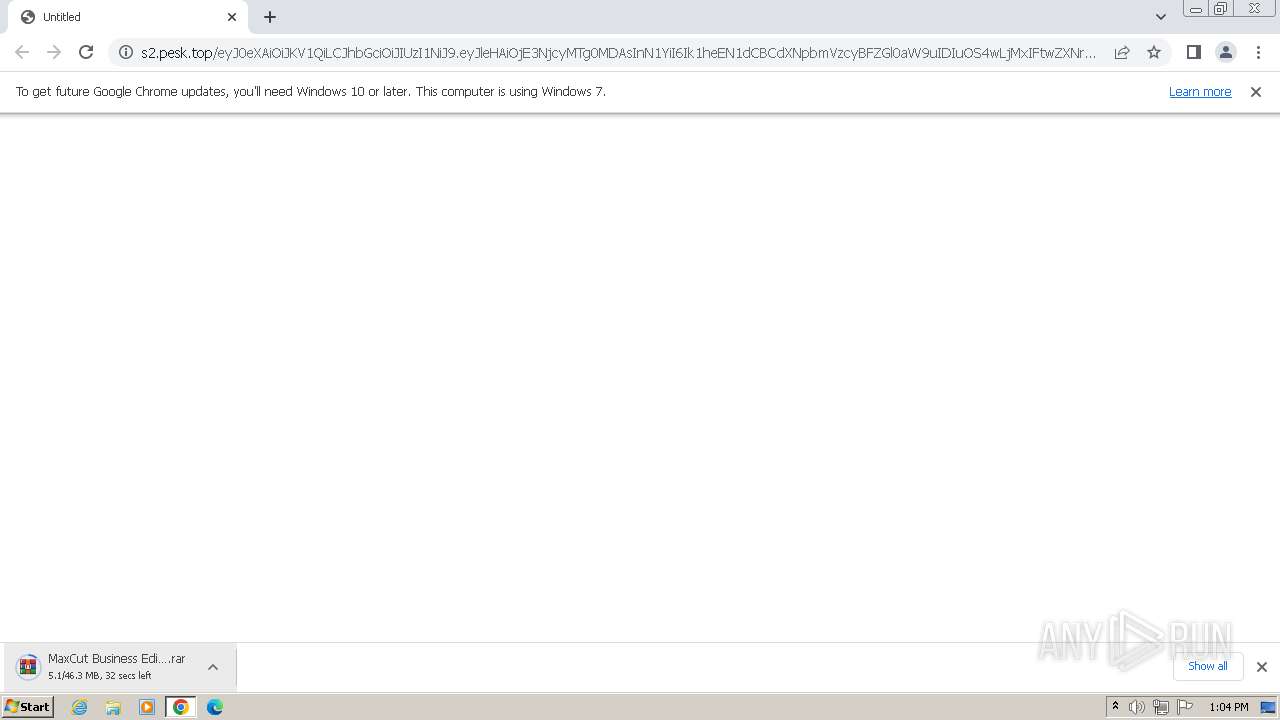
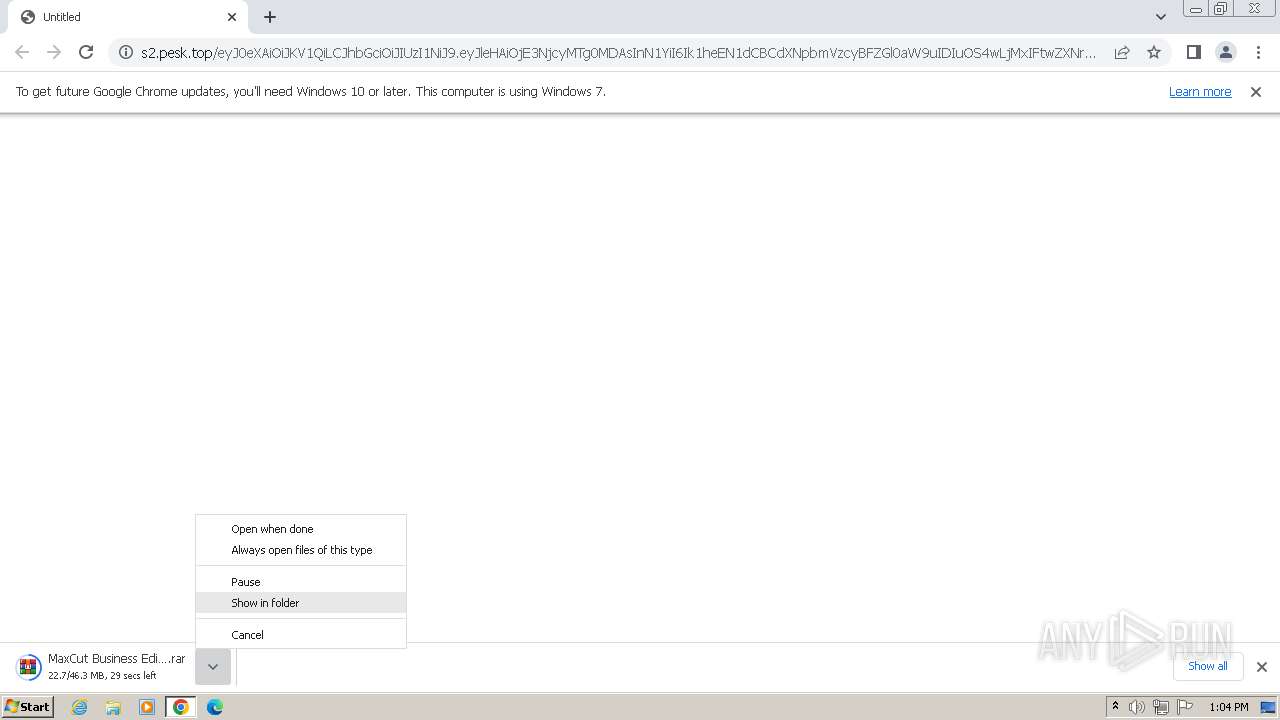
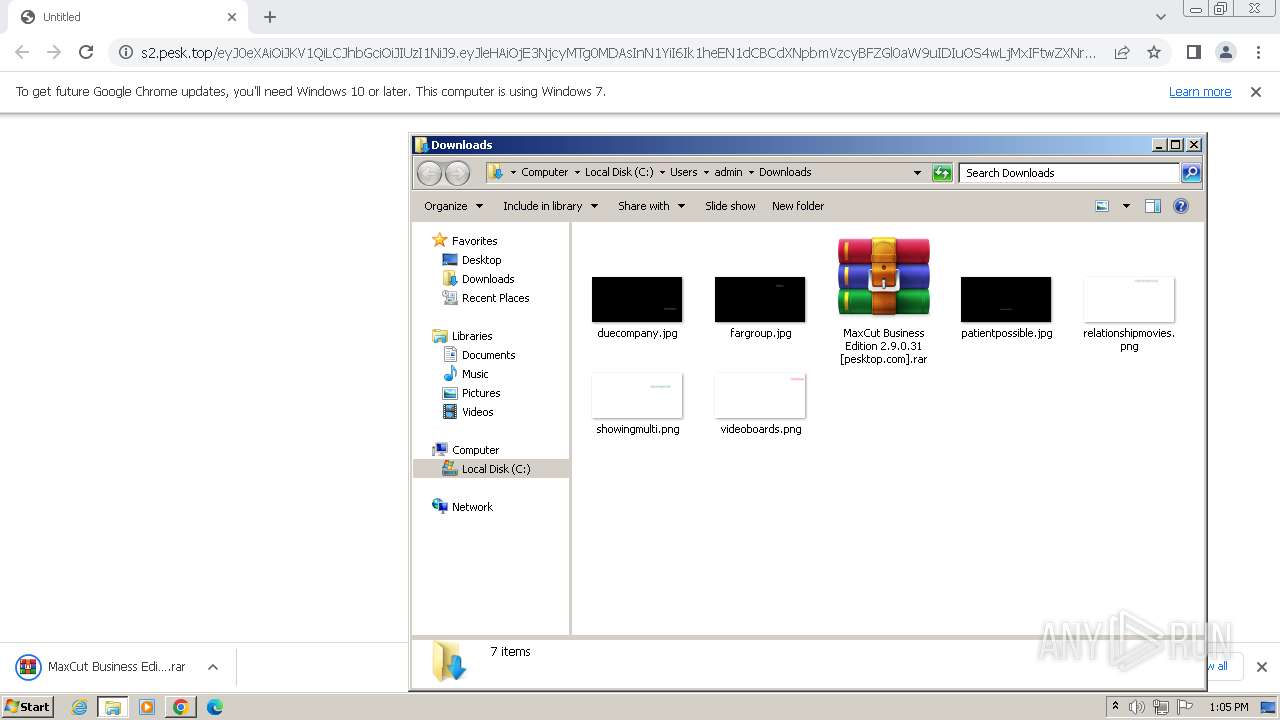
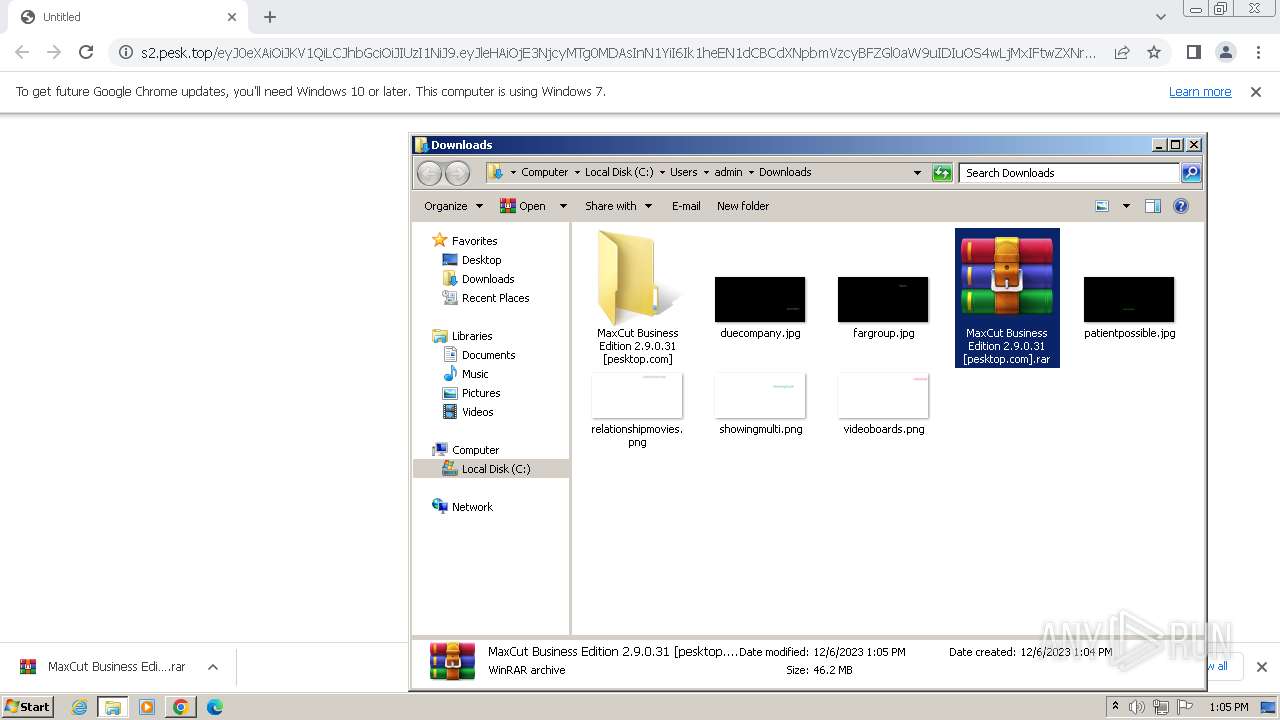
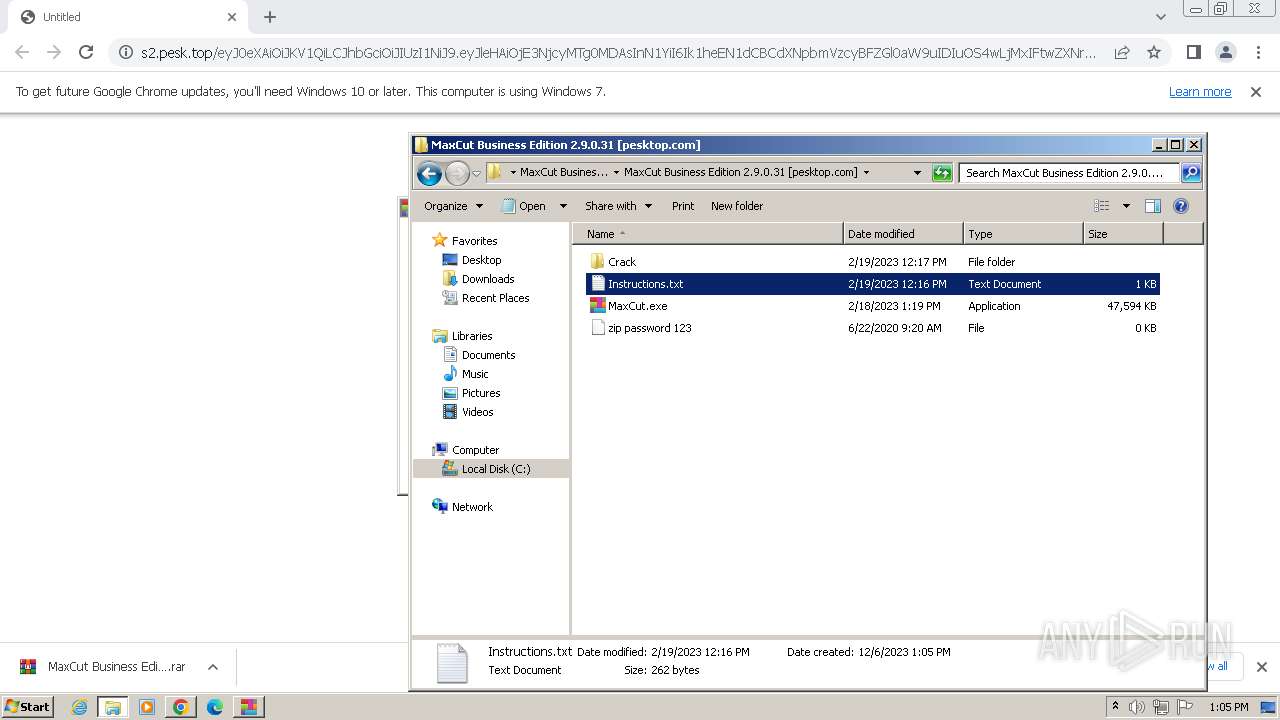
| URL: | https://s2.pesk.top/eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJleHAiOjE3NjcyMTg0MDAsInN1YiI6Ik1heEN1dCBCdXNpbmVzcyBFZGl0aW9uIDIuOS4wLjMxIFtwZXNrdG9wLmNvbV0ucmFyIiwic291cmNlIjoiaHR0cHM6XC9cL3Blc2t0b3AuY29tXC8ifQ.7IHgeBPIF_aBJmtKIvgmPdwb45FwBANelQ_VgcfECj4 |
| Full analysis: | https://app.any.run/tasks/adfa02fd-f15e-4da7-b45f-34c3480f1d8f |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2023, 13:04:07 |
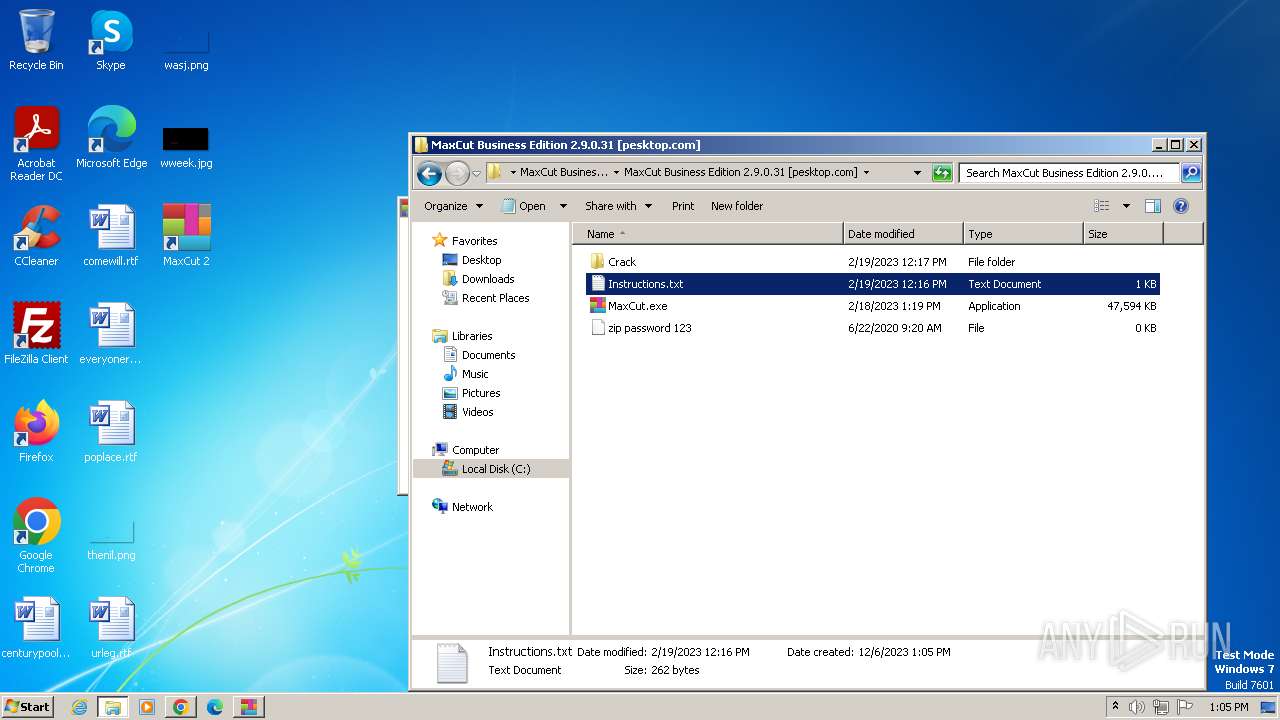
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F5EE9C280B1B11CCBC776CA7C39E04E7 |
| SHA1: | 7CC91DC6EC54740D62552FF3F5C9F514F39E4402 |
| SHA256: | 9113DBDA7070378FBB1594C2C55F88DA1E85CE8AB93A55FF8A9E1486F5B9DE34 |
| SSDEEP: | 6:2AtnYVAK7r48ebj7yD+OPLQshsjPoqG+KC/nx1ec:2cYVAKXnk74+qG+C/Wc |
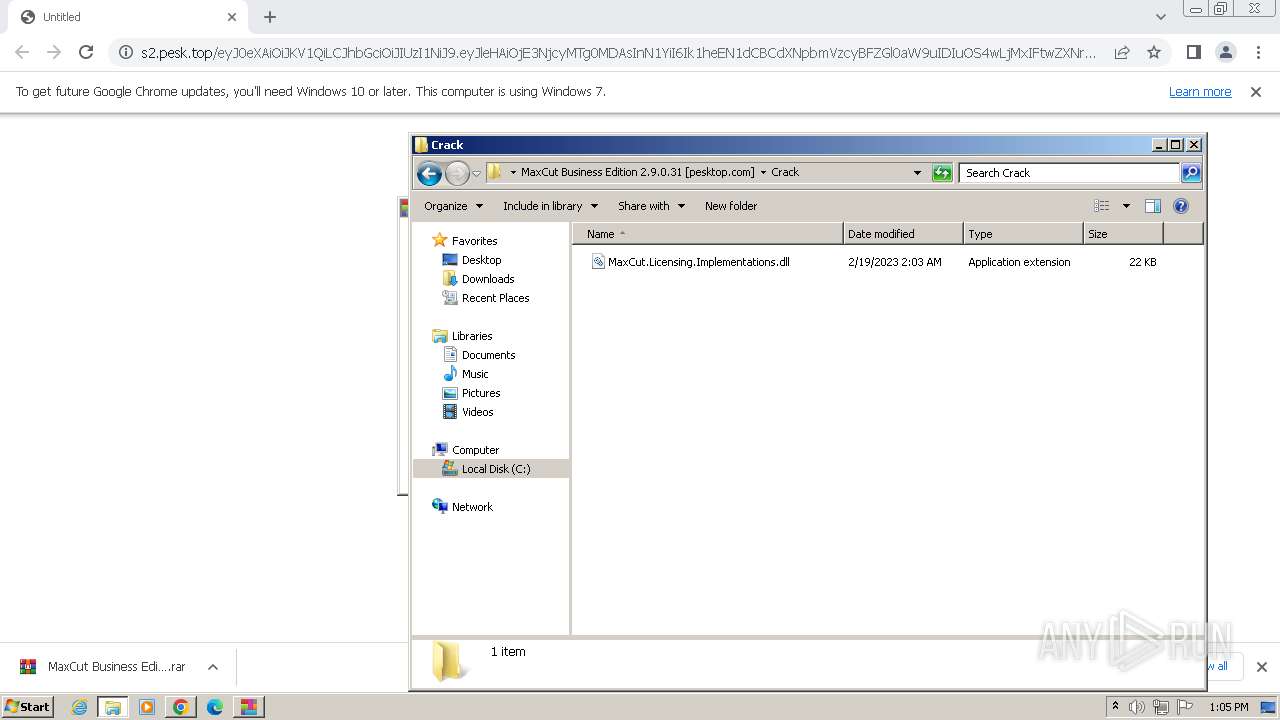
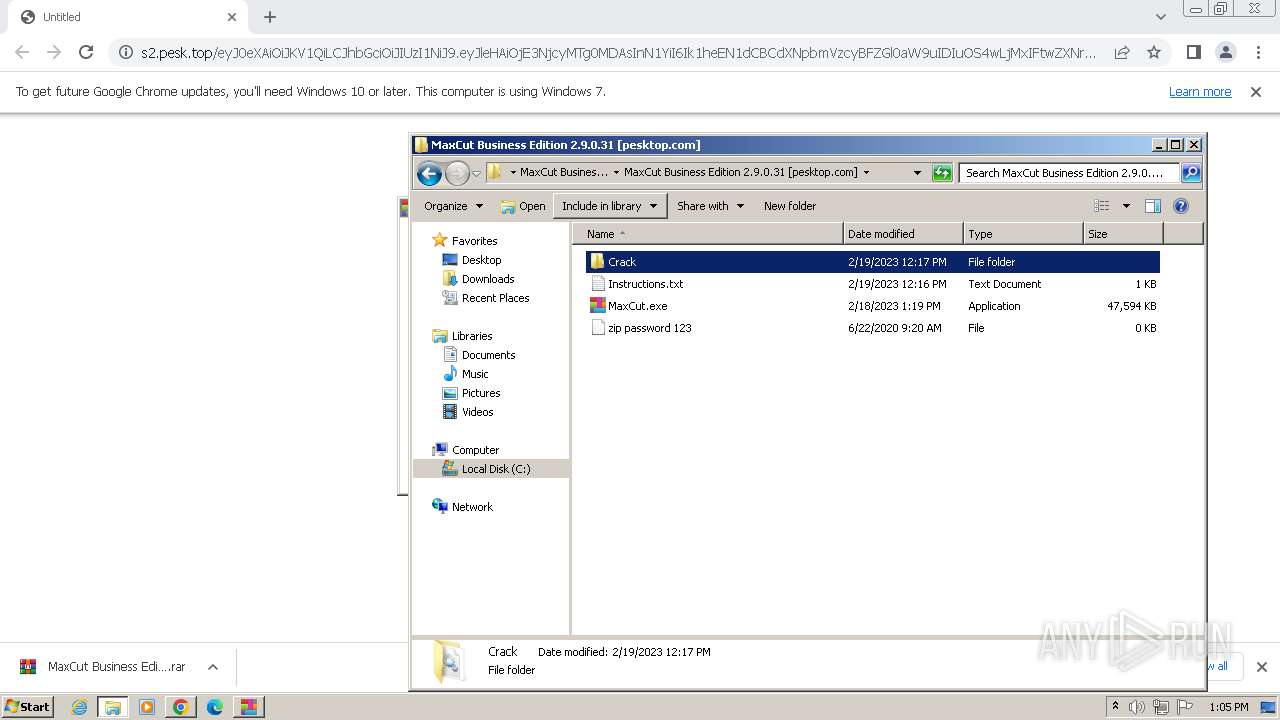
MALICIOUS
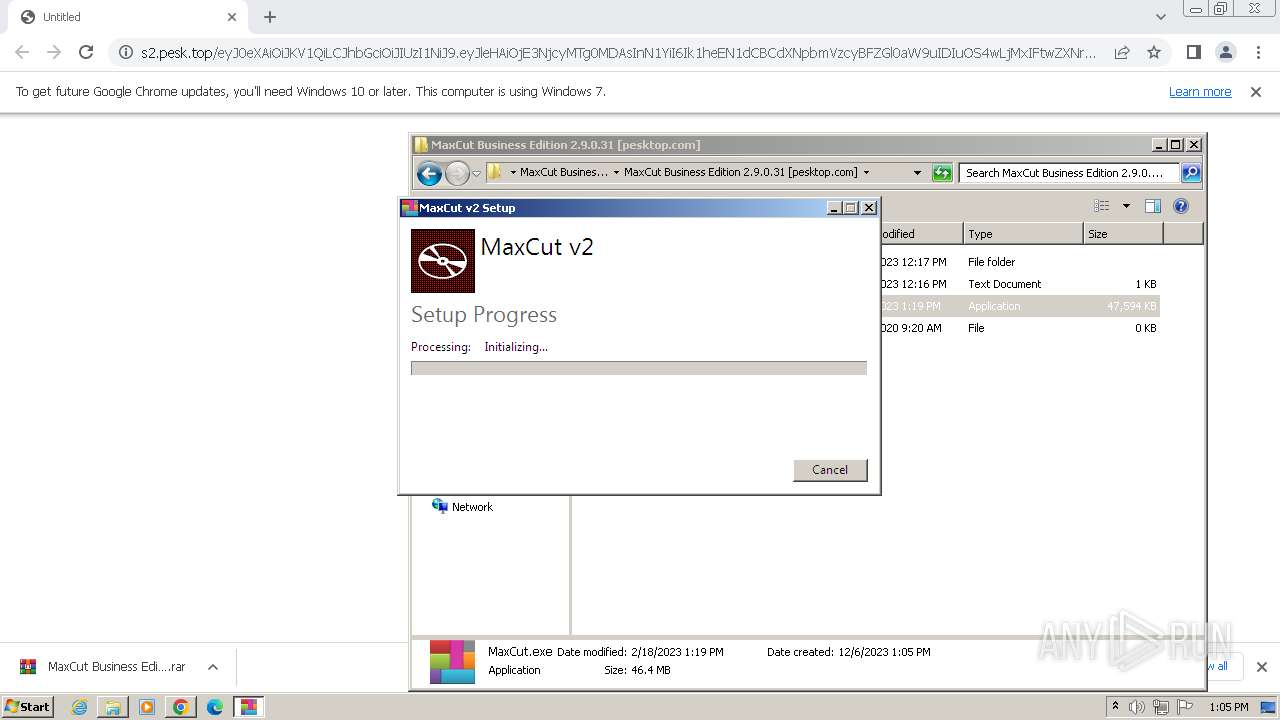
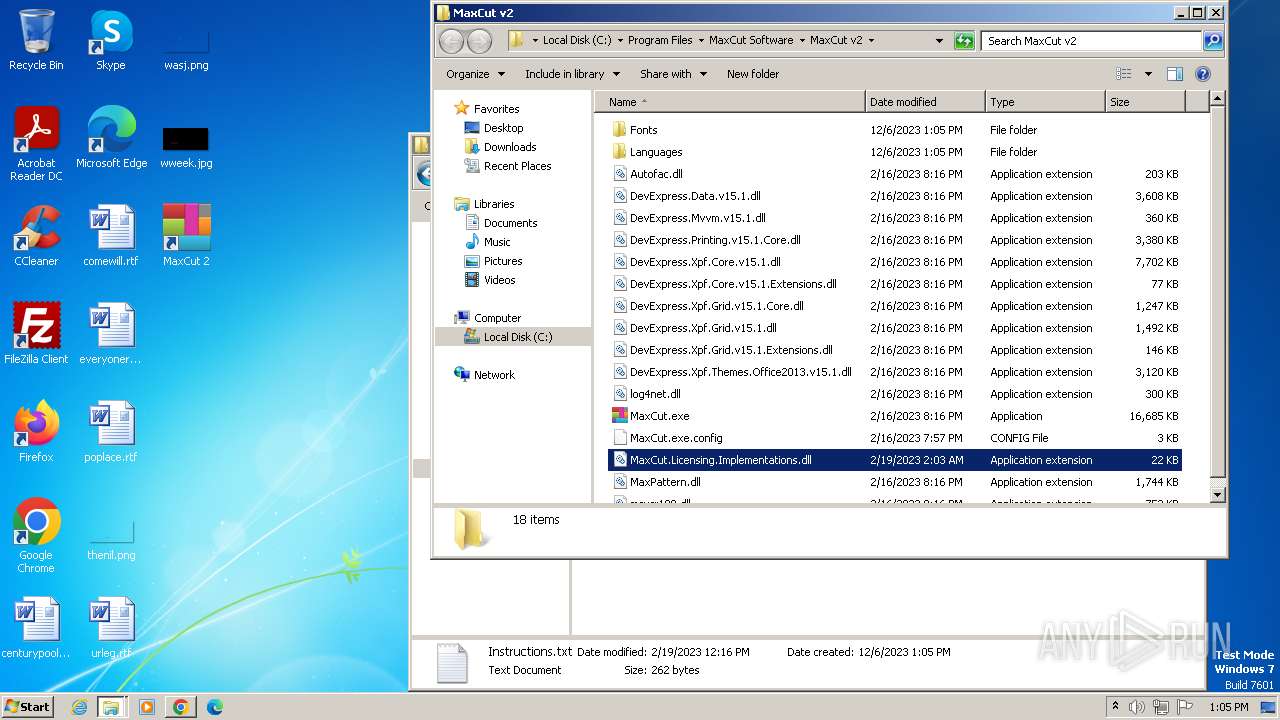
Drops the executable file immediately after the start
- MaxCut.exe (PID: 2576)
- MaxCut.exe (PID: 2776)
- MaxCutSetup.exe (PID: 4040)
- msiexec.exe (PID: 3336)
SUSPICIOUS
Process drops legitimate windows executable
- chrome.exe (PID: 1556)
- msiexec.exe (PID: 3336)
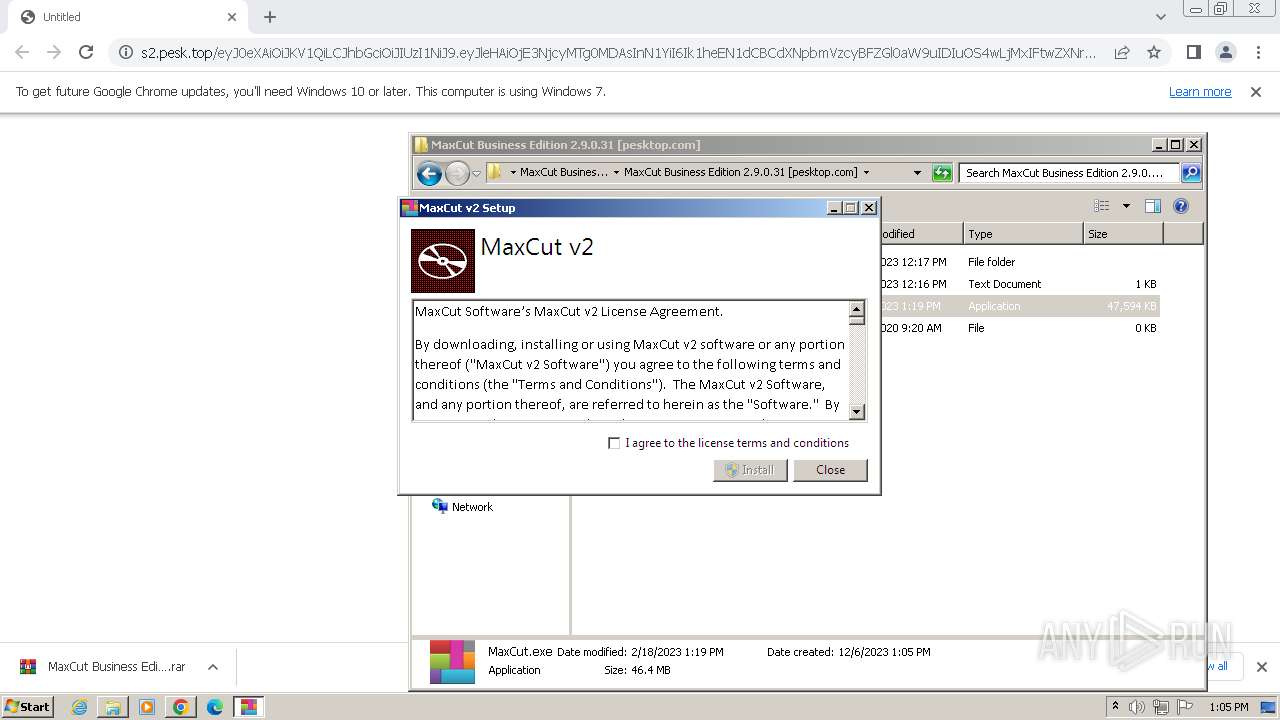
Searches for installed software
- MaxCut.exe (PID: 2776)
- MaxCutSetup.exe (PID: 4040)
Starts itself from another location
- MaxCut.exe (PID: 2776)
Reads the Internet Settings
- MaxCut.exe (PID: 2776)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
Executes as Windows Service
- VSSVC.exe (PID: 2912)
Checks Windows Trust Settings
- msiexec.exe (PID: 3336)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 3336)
Adds/modifies Windows certificates
- msiexec.exe (PID: 3336)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 3428)
The process drops C-runtime libraries
- msiexec.exe (PID: 3336)
Creates a software uninstall entry
- MaxCutSetup.exe (PID: 4040)
Reads settings of System Certificates
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
Process requests binary or script from the Internet
- MaxCut.exe (PID: 824)
INFO
Application launched itself
- chrome.exe (PID: 1556)
- msiexec.exe (PID: 3336)
Reads the computer name
- wmpnscfg.exe (PID: 900)
- MaxCutSetup.exe (PID: 4040)
- msiexec.exe (PID: 3336)
- msiexec.exe (PID: 3428)
- msiexec.exe (PID: 3096)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
- MaxCut.exe (PID: 2776)
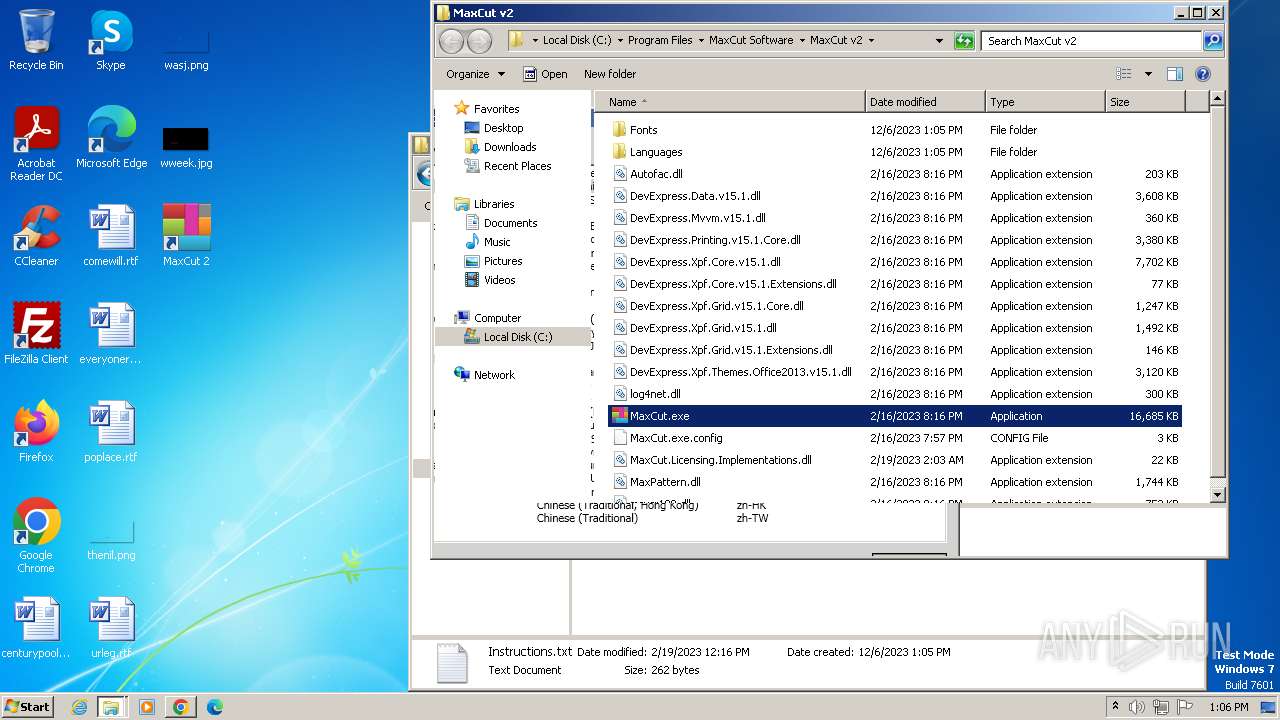
Checks supported languages
- wmpnscfg.exe (PID: 900)
- MaxCut.exe (PID: 2576)
- MaxCut.exe (PID: 2776)
- MaxCutSetup.exe (PID: 4040)
- msiexec.exe (PID: 3336)
- msiexec.exe (PID: 3428)
- msiexec.exe (PID: 3096)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
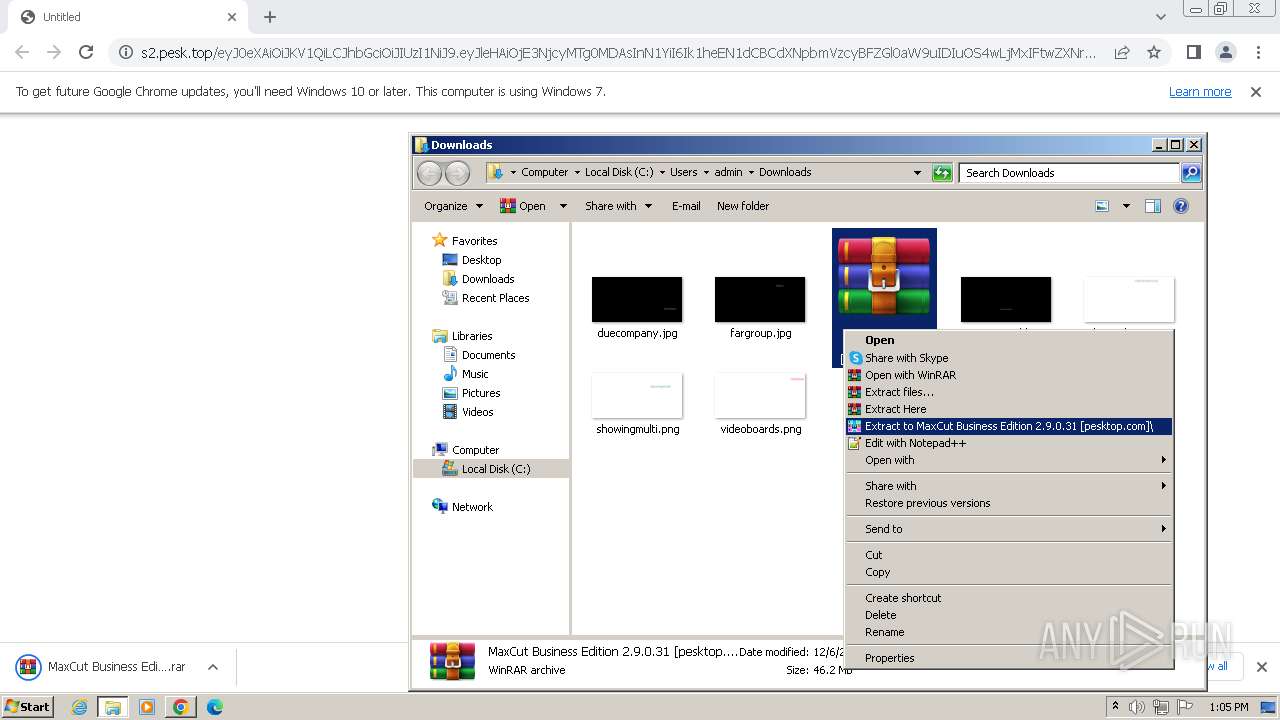
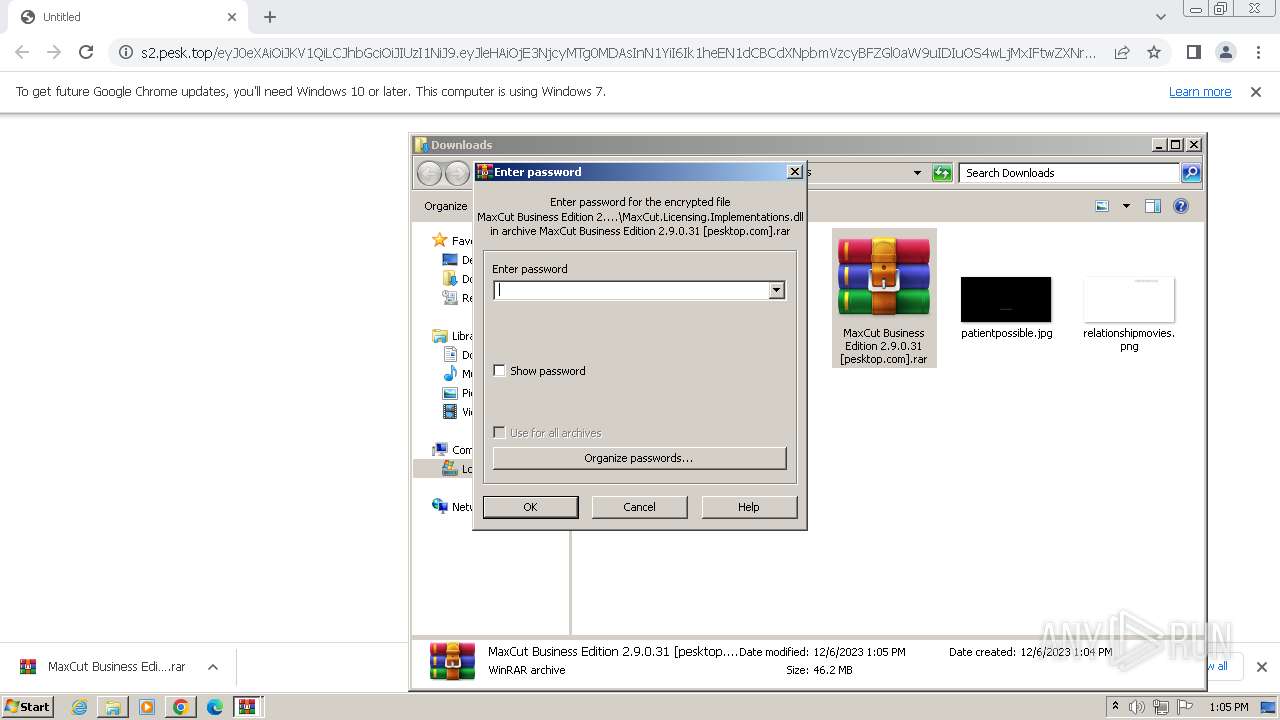
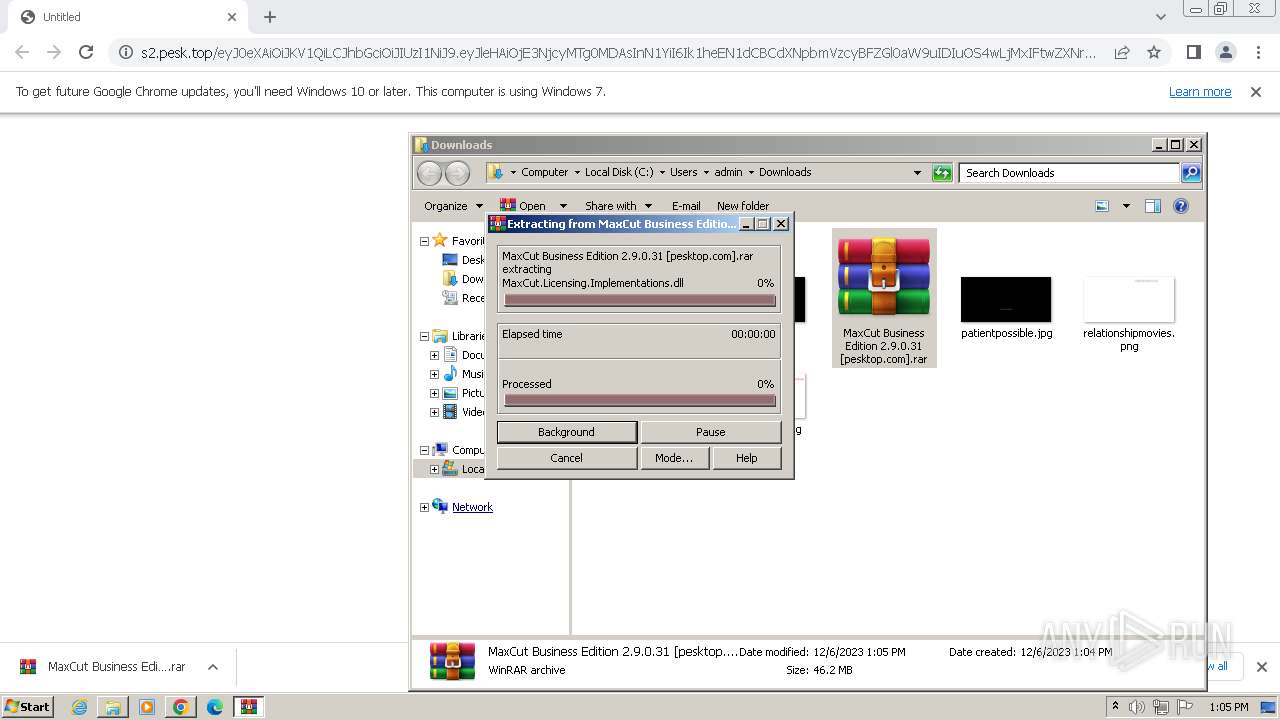
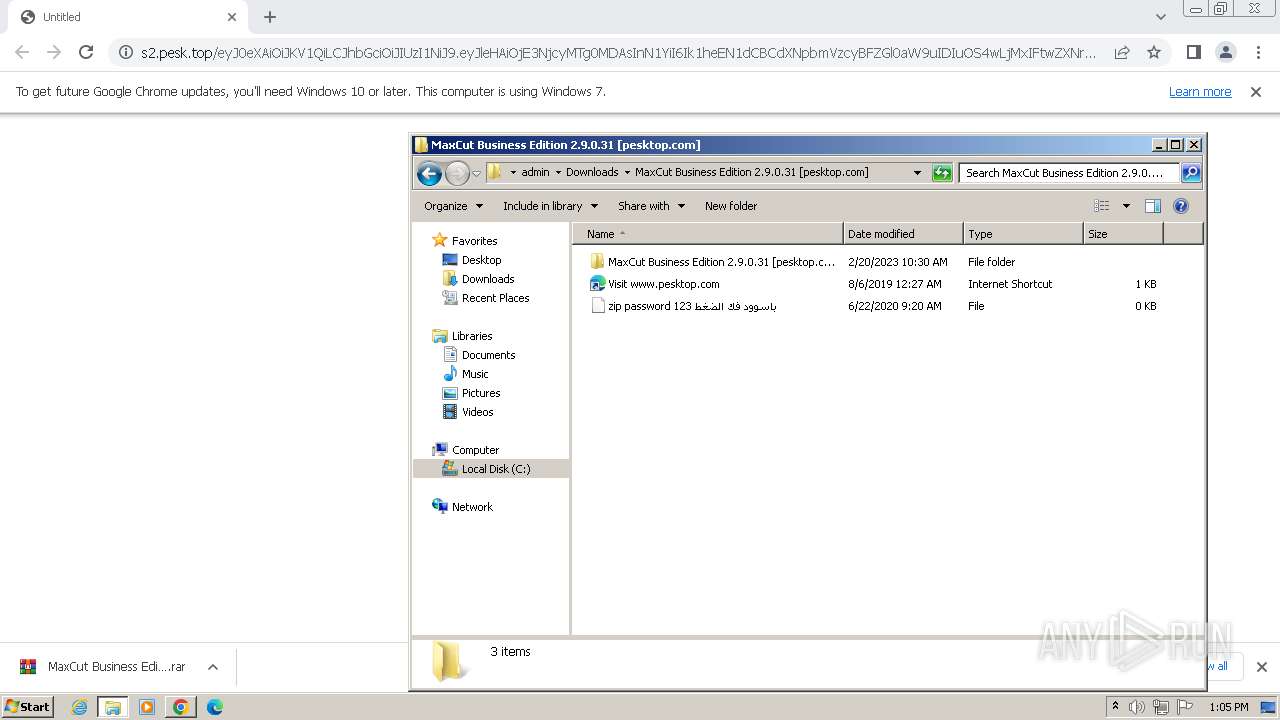
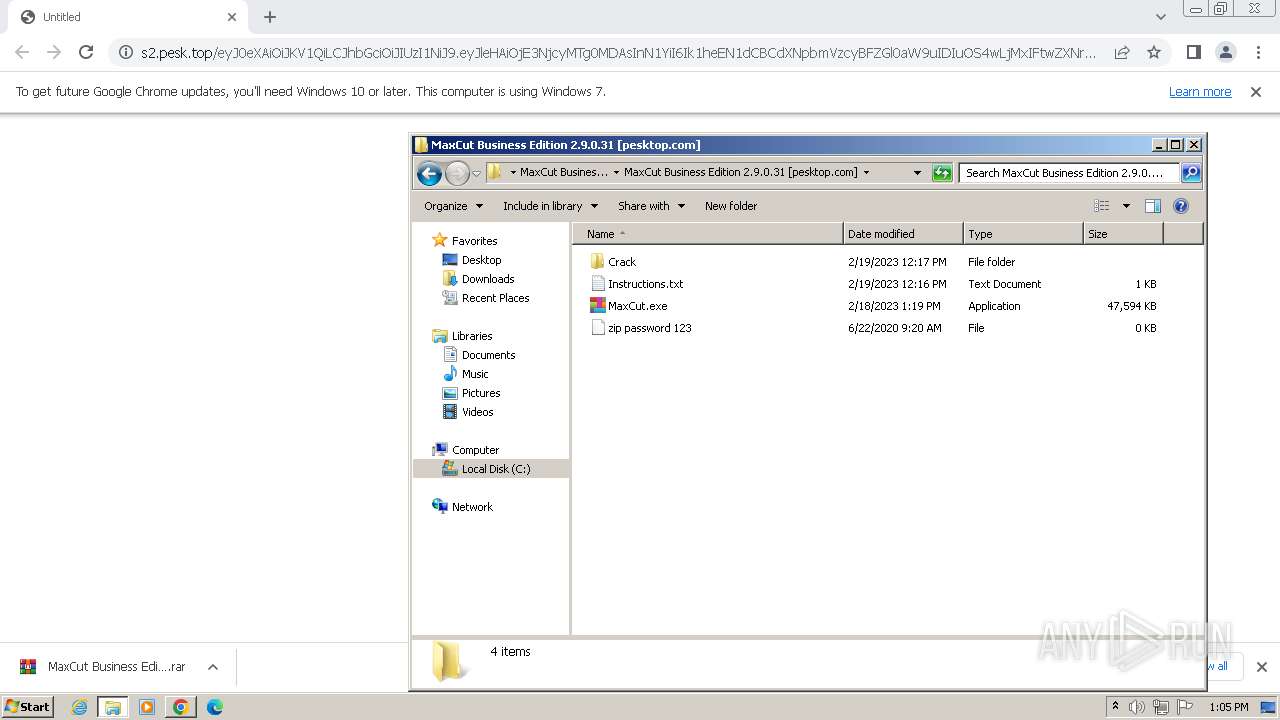
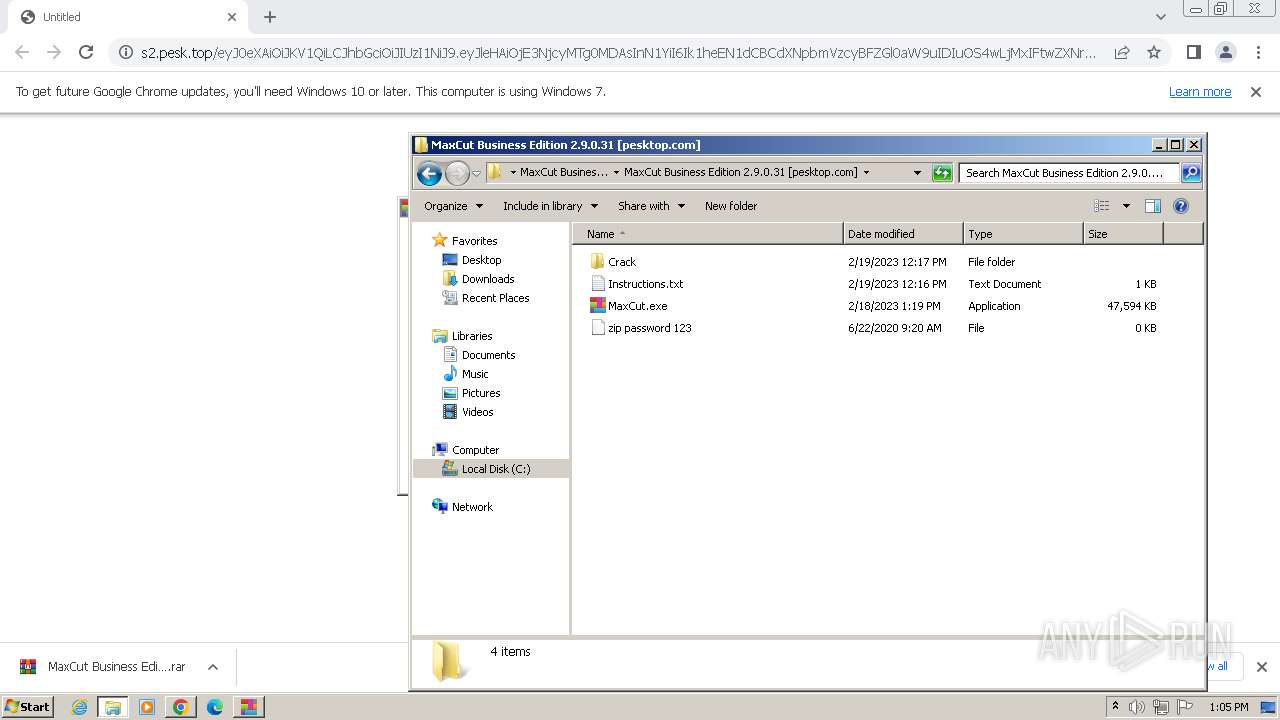
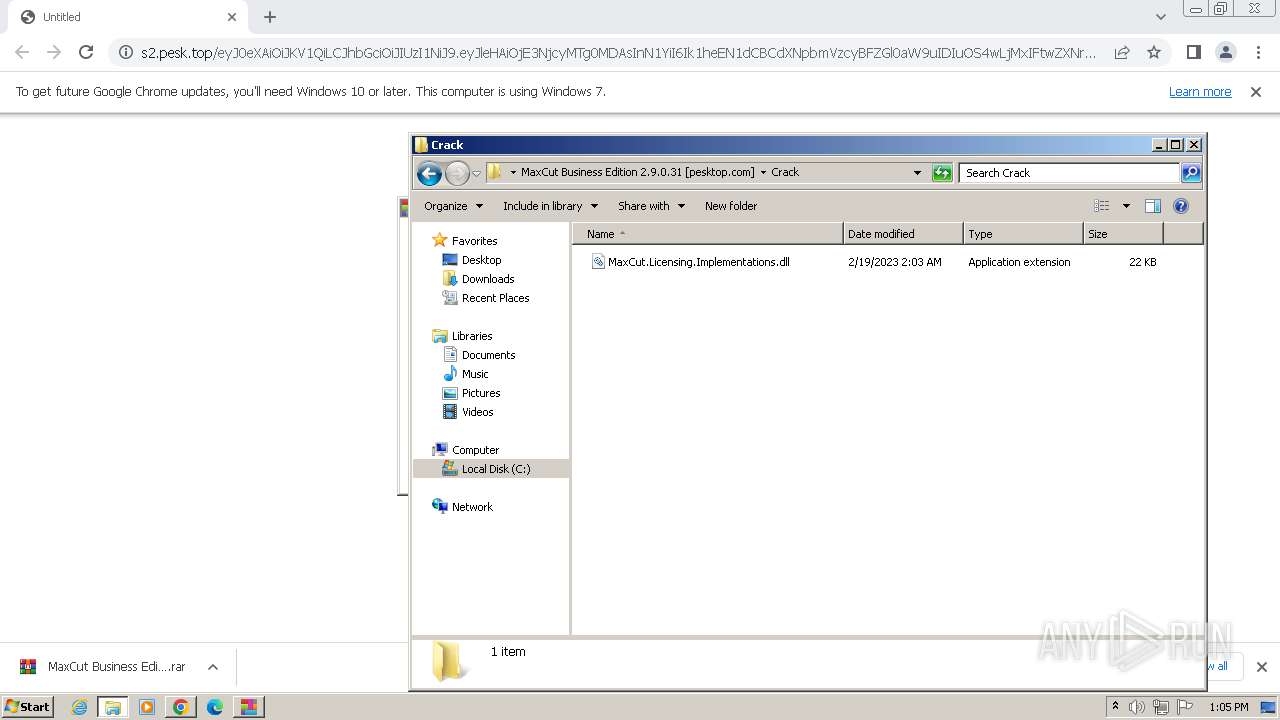
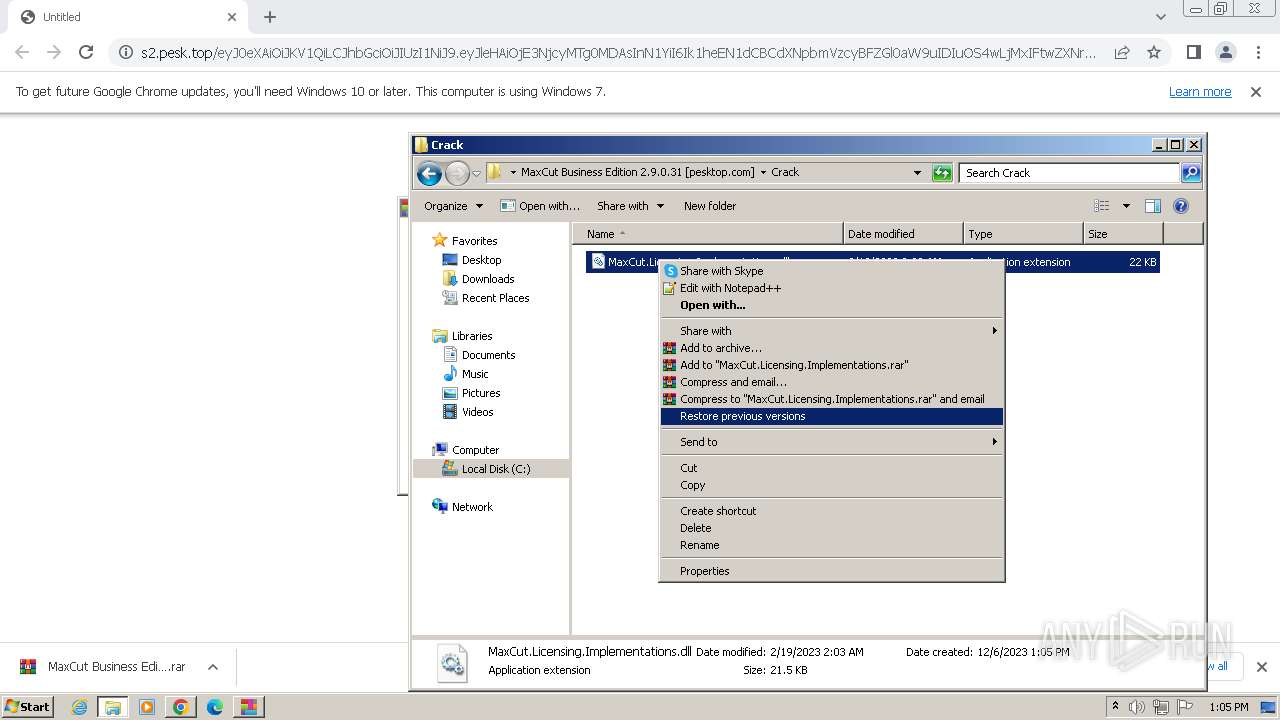
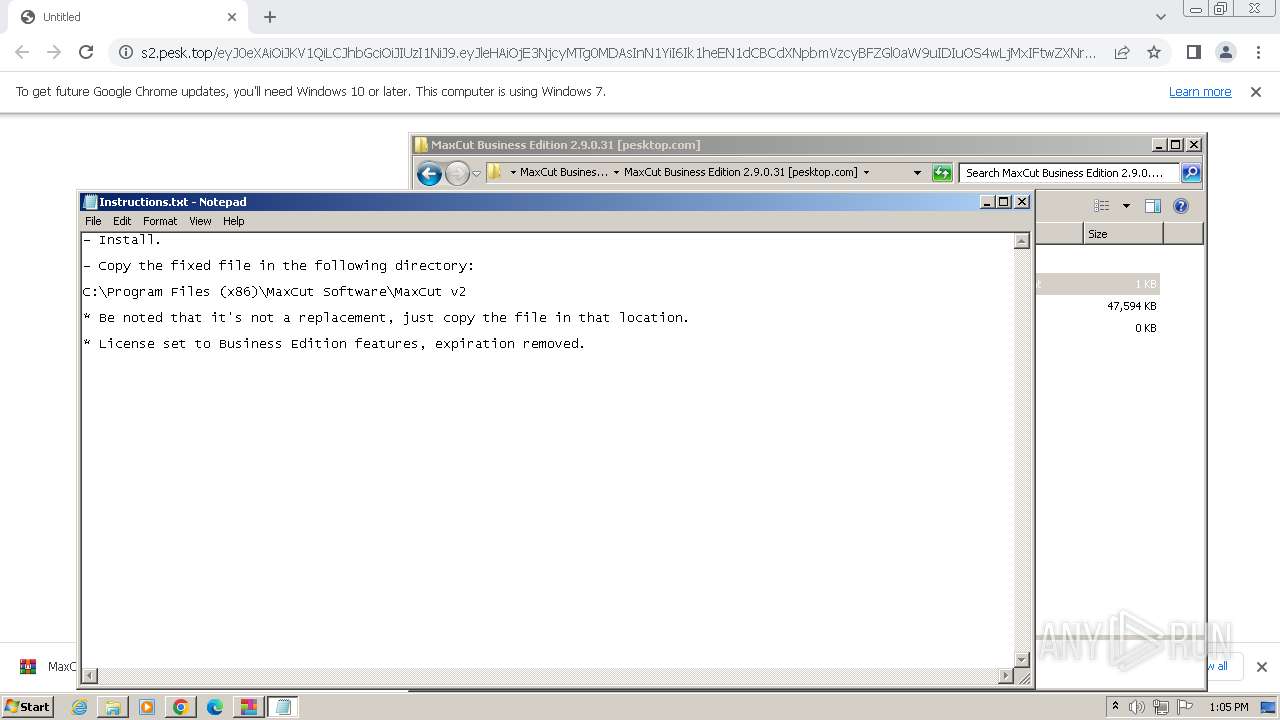
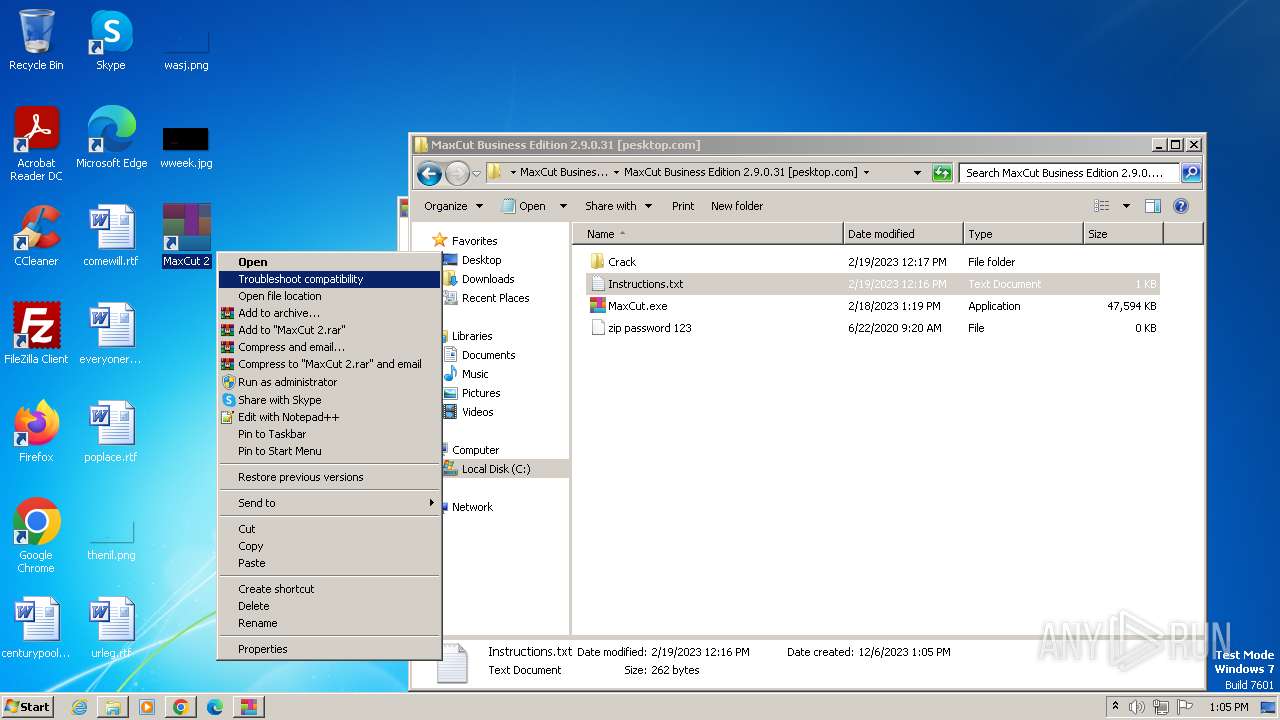
Manual execution by a user
- wmpnscfg.exe (PID: 900)
- WinRAR.exe (PID: 3152)
- MaxCut.exe (PID: 2576)
- notepad.exe (PID: 1600)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
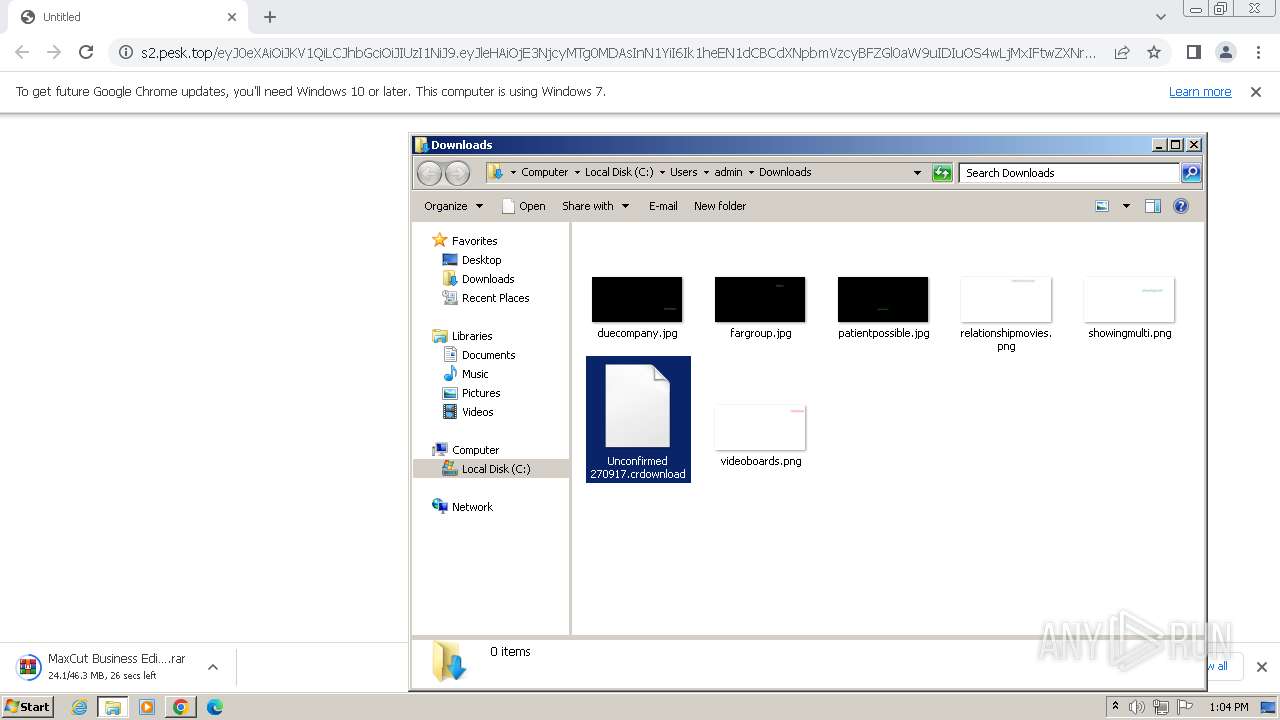
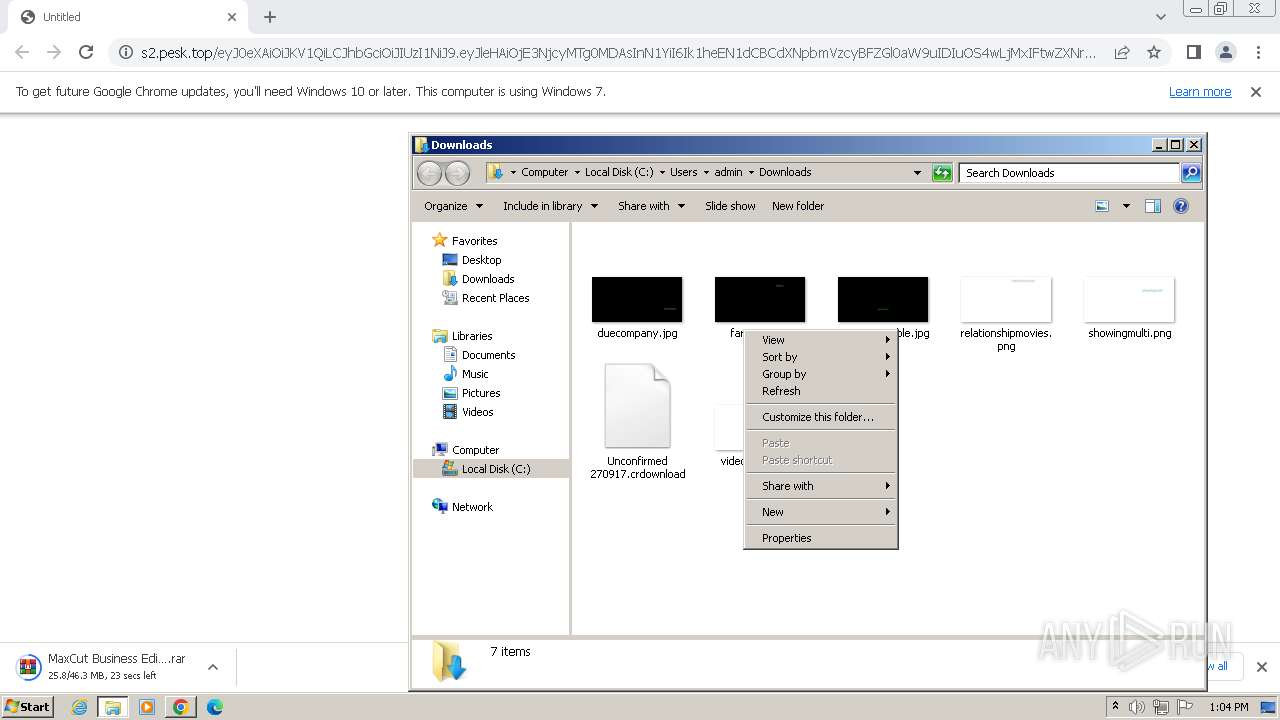
The process uses the downloaded file
- chrome.exe (PID: 2808)
- chrome.exe (PID: 3728)
- chrome.exe (PID: 2472)
- chrome.exe (PID: 3704)
- WinRAR.exe (PID: 3152)
Drops the executable file immediately after the start
- chrome.exe (PID: 1556)
- WinRAR.exe (PID: 3152)
- rundll32.exe (PID: 1328)
- rundll32.exe (PID: 3844)
- rundll32.exe (PID: 2380)
- rundll32.exe (PID: 1636)
- rundll32.exe (PID: 1952)
- dllhost.exe (PID: 948)
- chrome.exe (PID: 3172)
- chrome.exe (PID: 1816)
Create files in a temporary directory
- MaxCut.exe (PID: 2576)
- MaxCutSetup.exe (PID: 4040)
- msiexec.exe (PID: 3336)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 2776)
Reads the machine GUID from the registry
- MaxCut.exe (PID: 2776)
- MaxCutSetup.exe (PID: 4040)
- msiexec.exe (PID: 3336)
- msiexec.exe (PID: 3428)
- msiexec.exe (PID: 3096)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
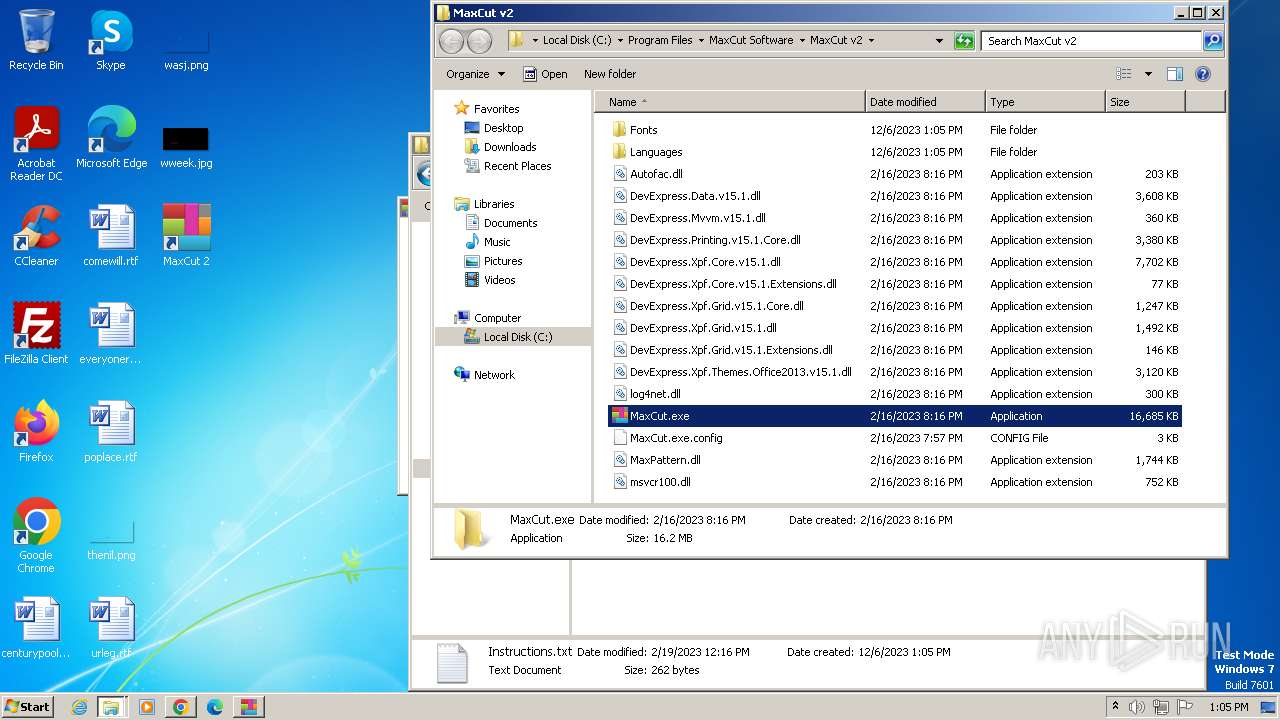
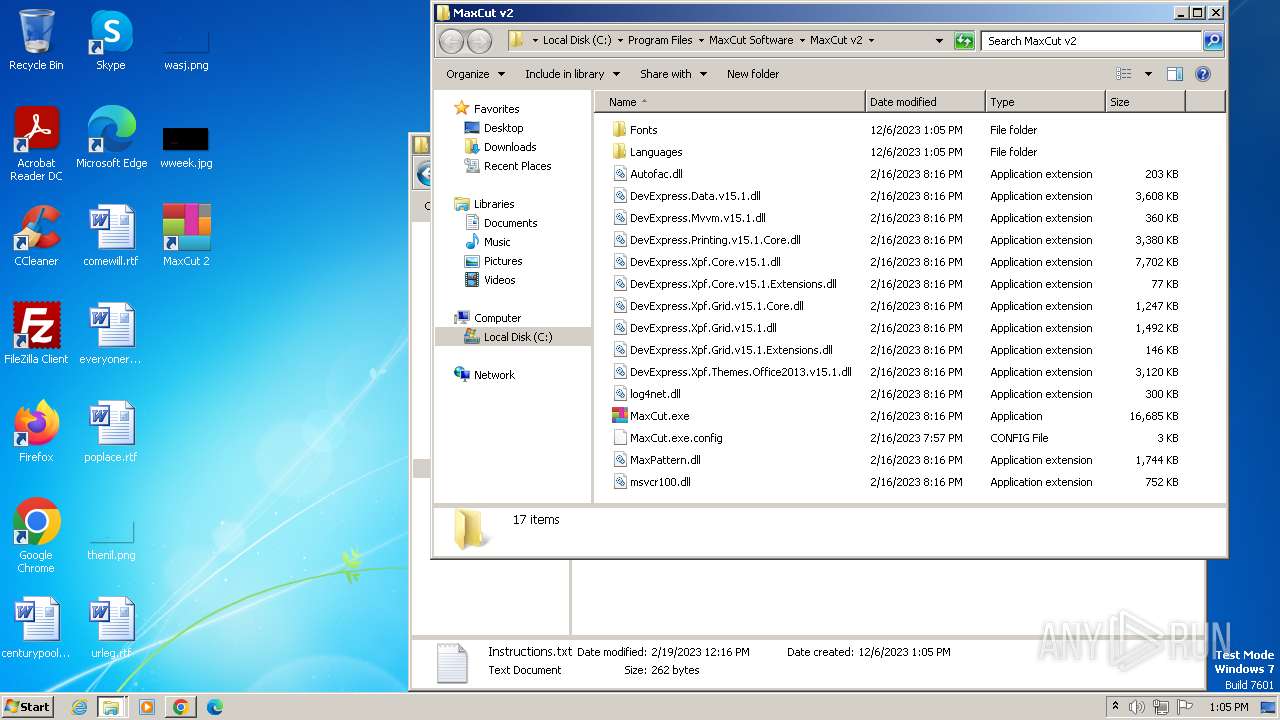
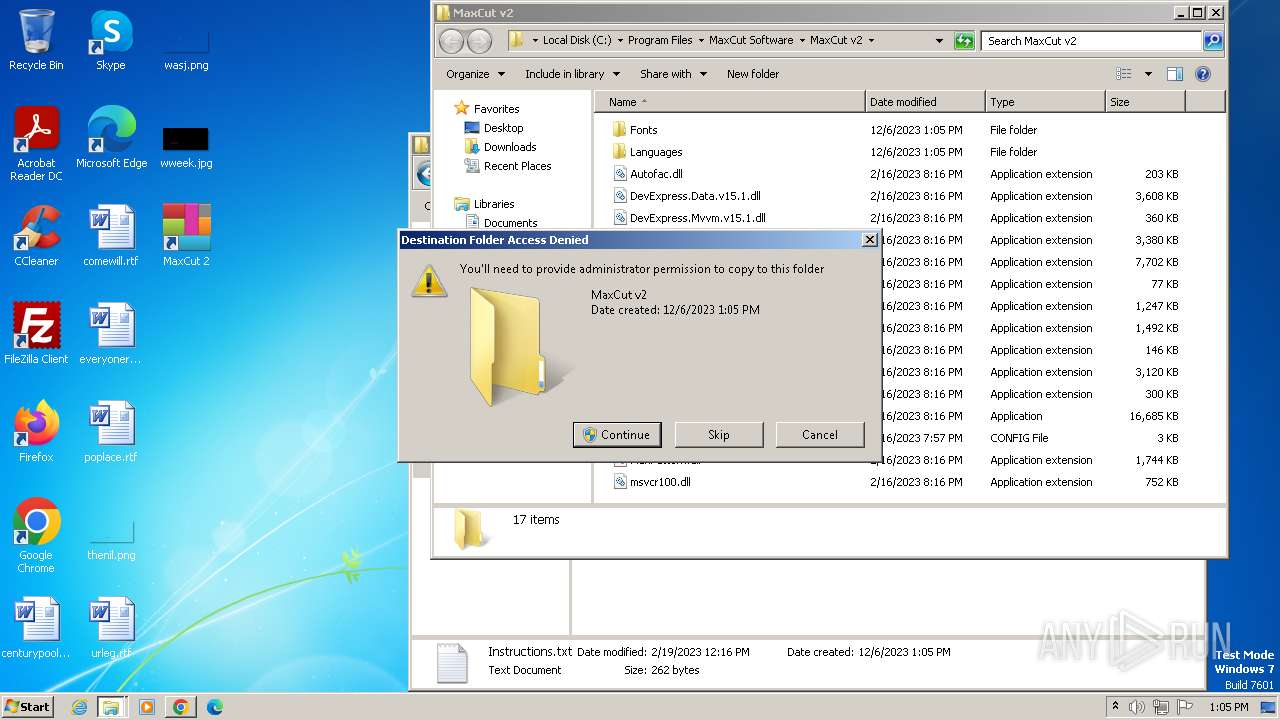
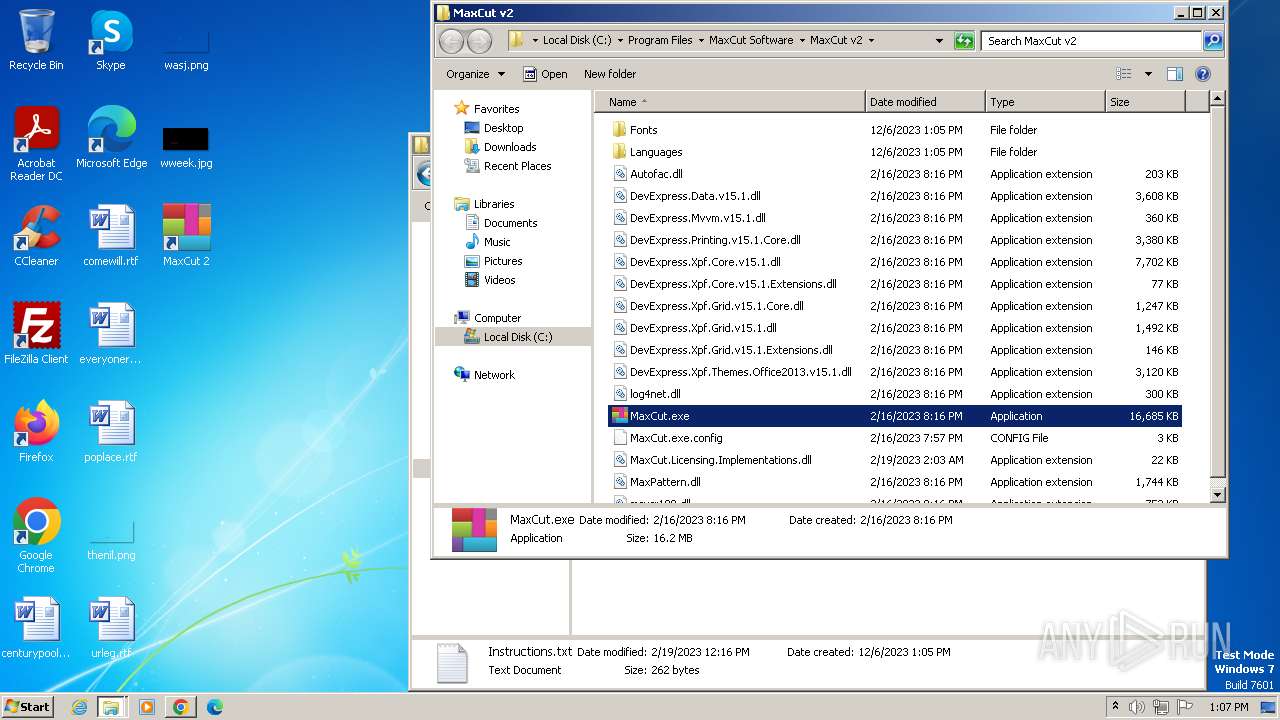
Creates files in the program directory
- MaxCutSetup.exe (PID: 4040)
- dllhost.exe (PID: 948)
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
Reads Environment values
- MaxCut.exe (PID: 824)
- MaxCut.exe (PID: 3884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
98
Monitored processes
47
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3536 --field-trial-handle=1088,i,11269331173937500977,1908815433233384982,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1476 --field-trial-handle=1088,i,11269331173937500977,1908815433233384982,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgACAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1128 --field-trial-handle=1088,i,11269331173937500977,1908815433233384982,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
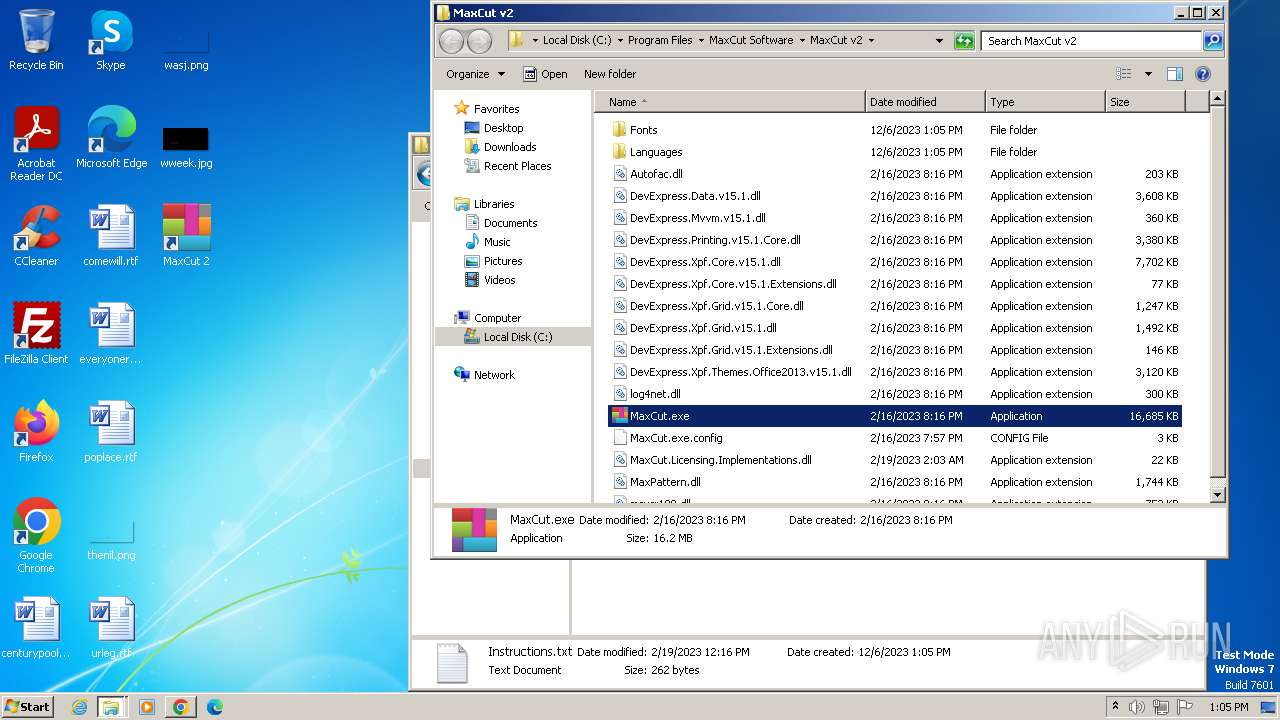
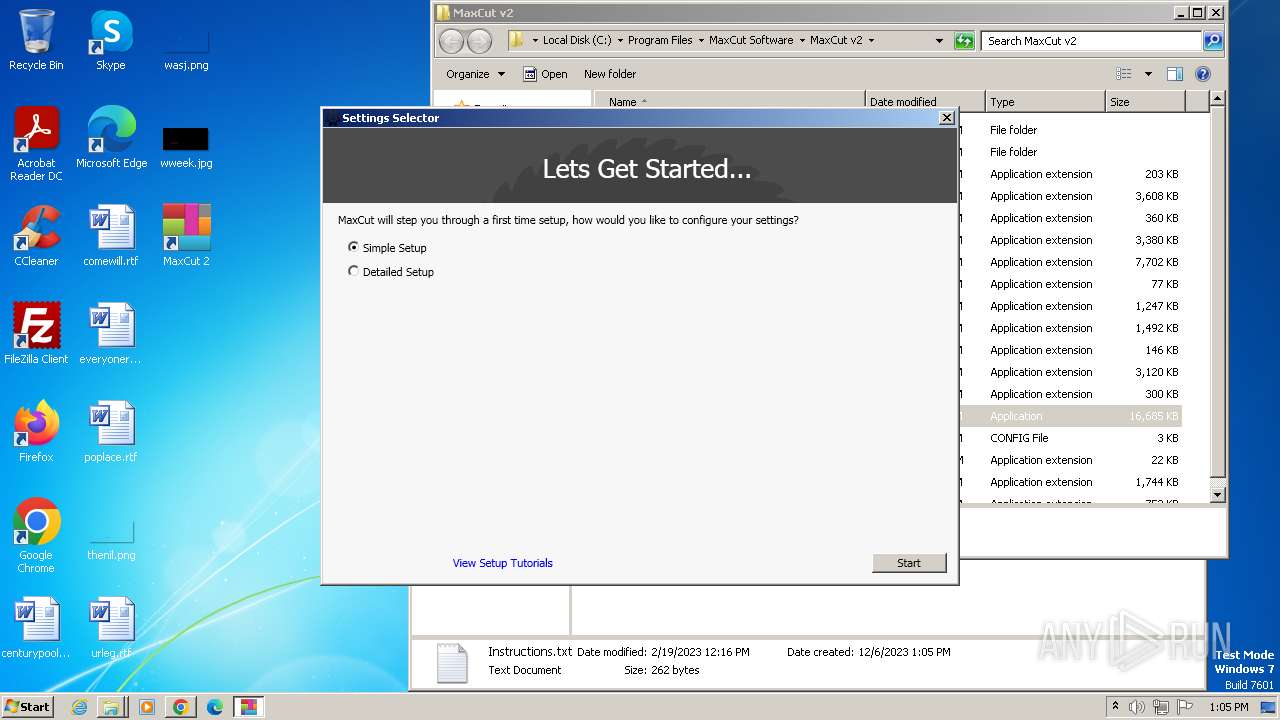
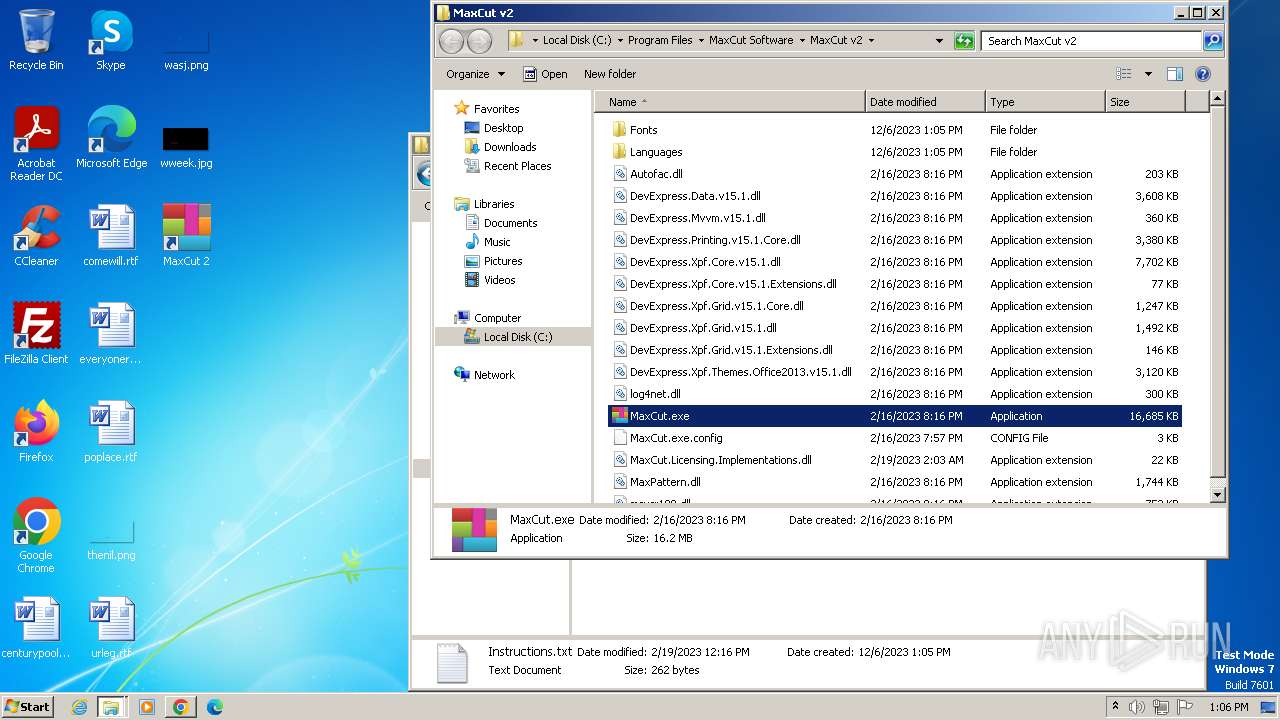
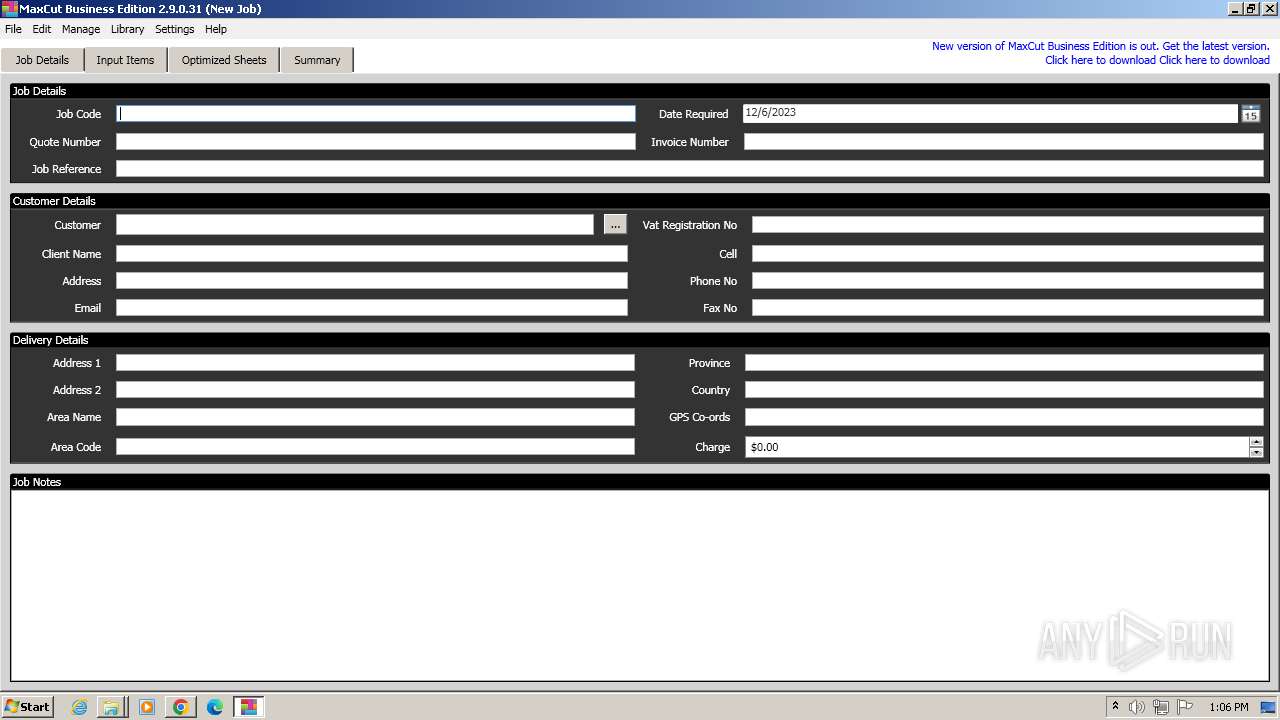
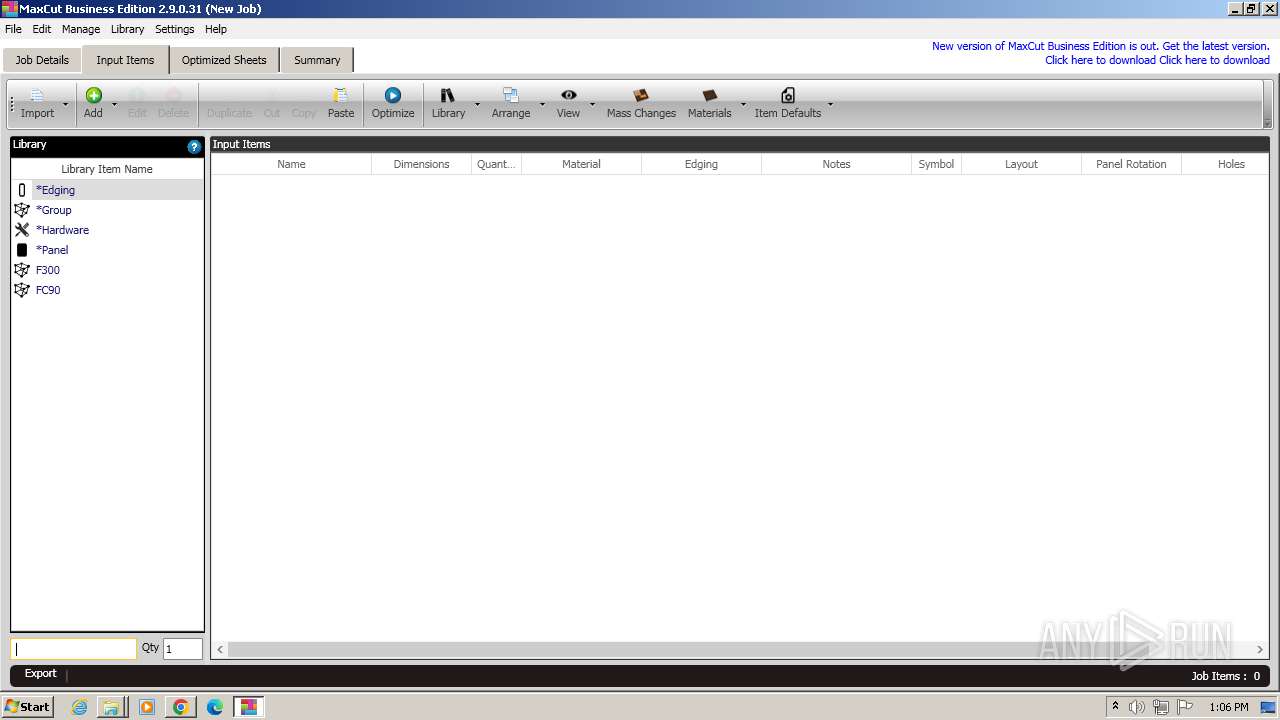
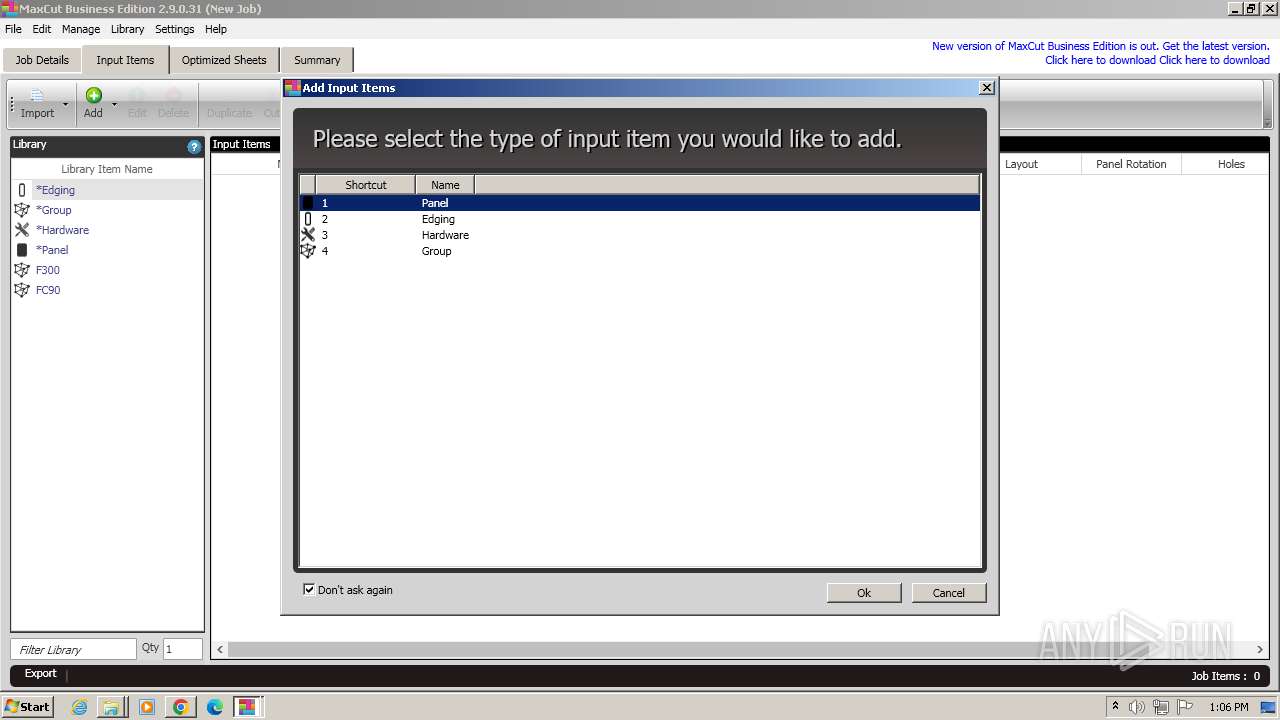
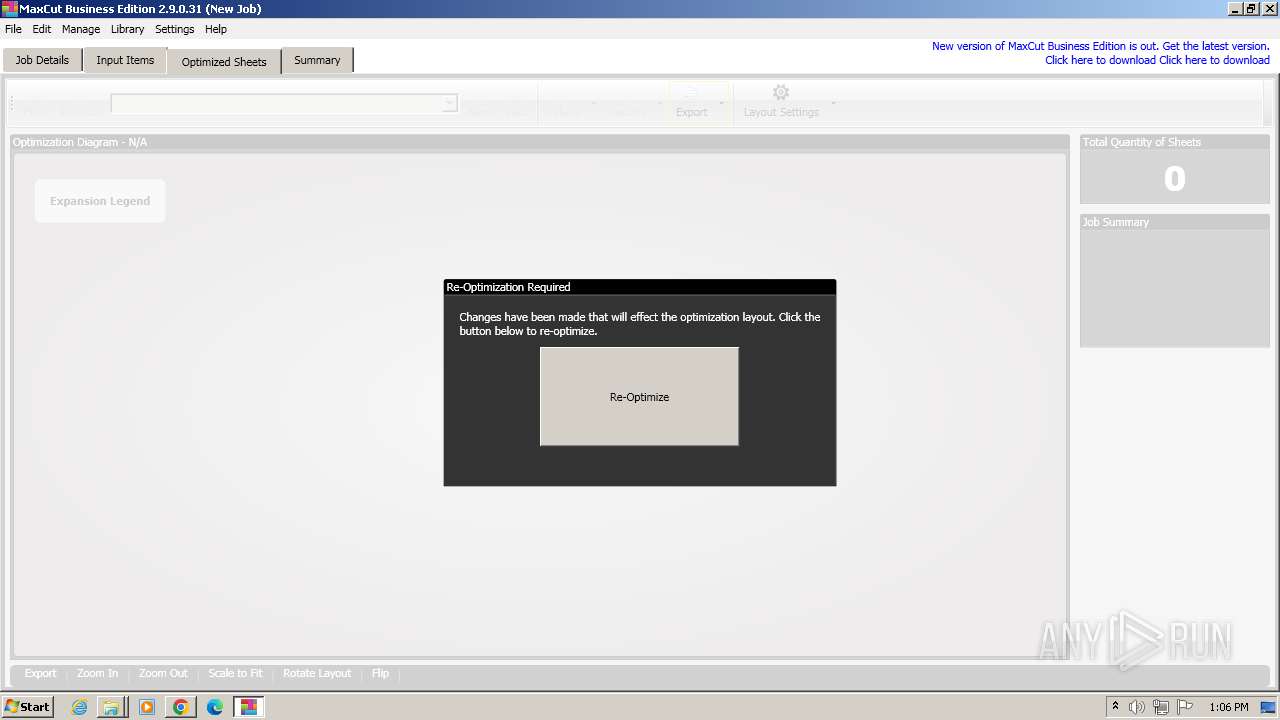
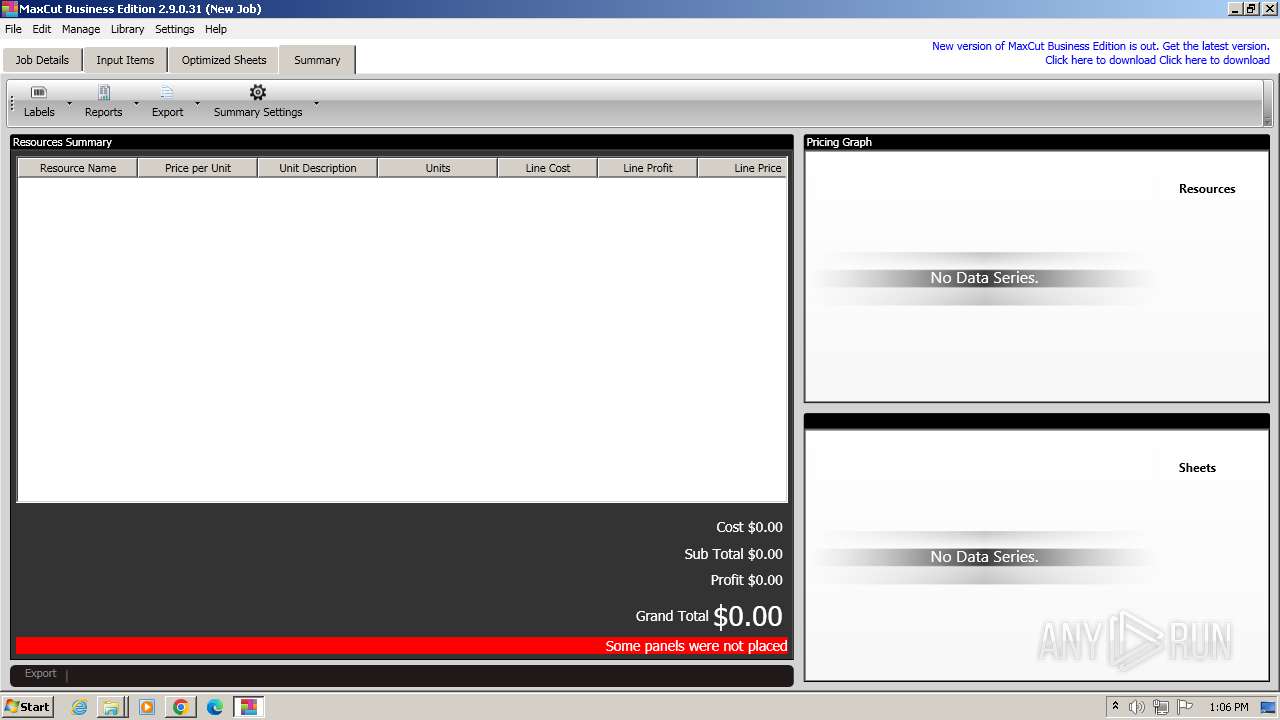
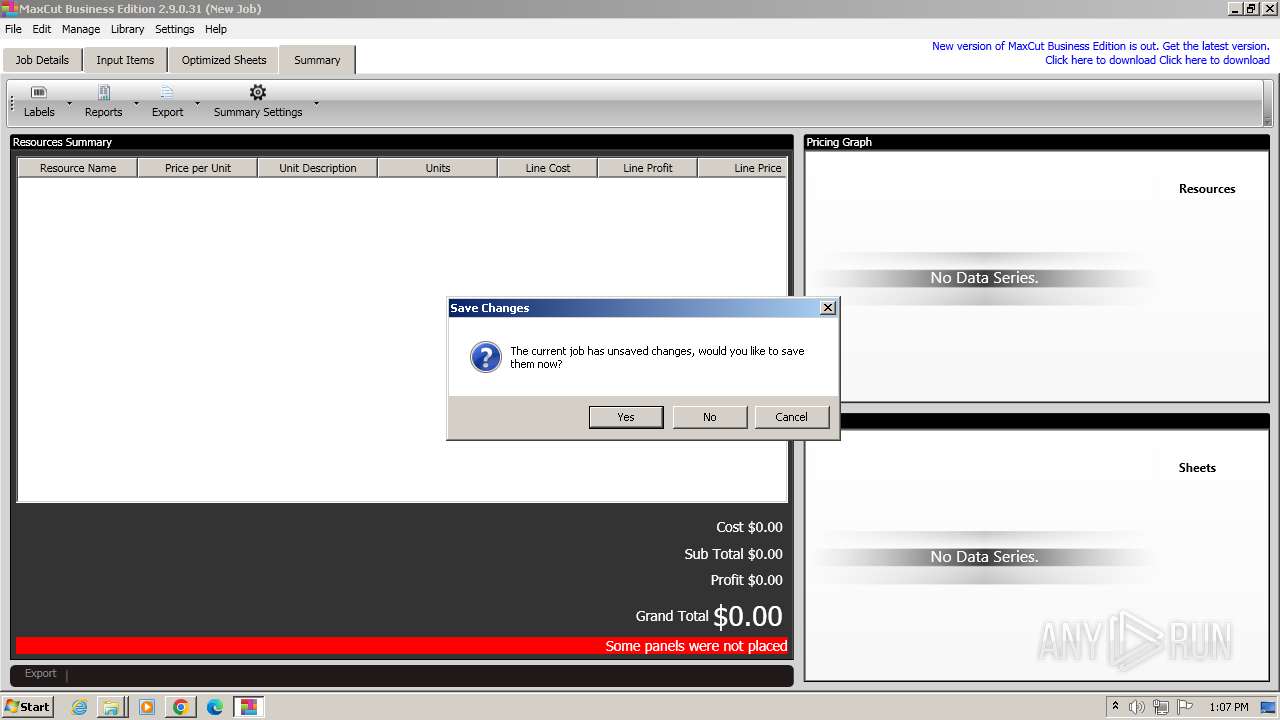
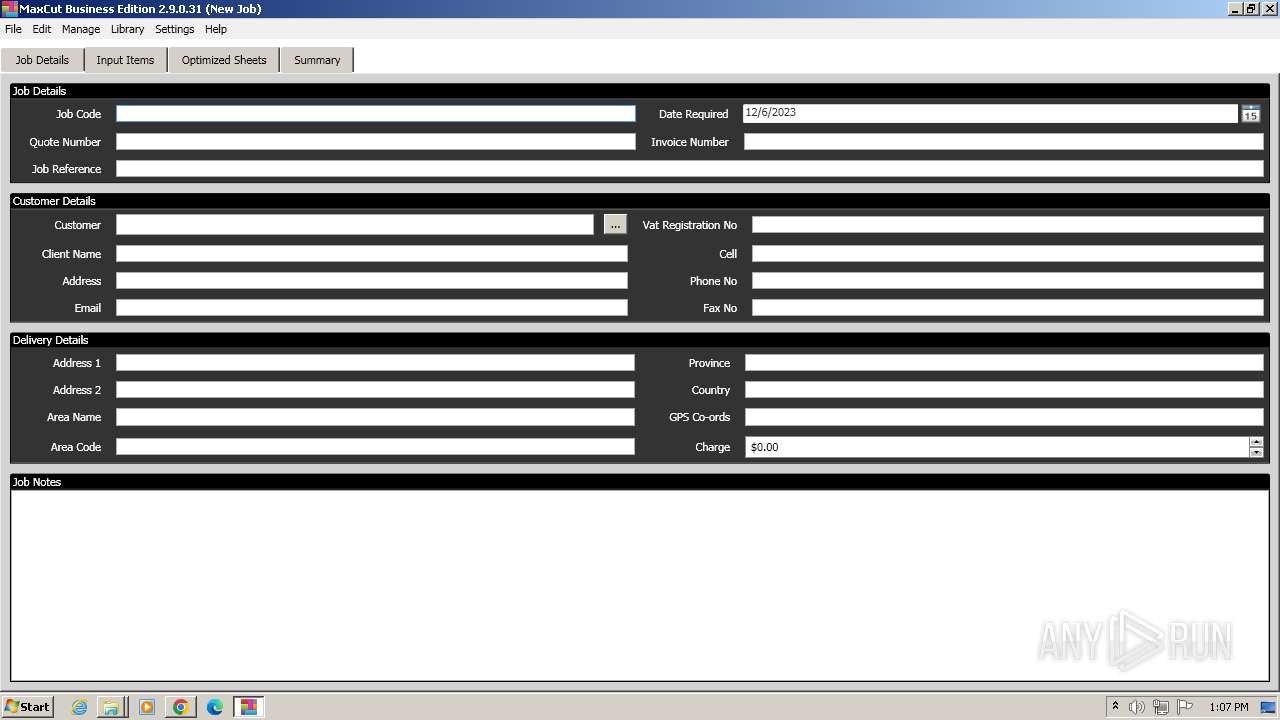
| 824 | "C:\Program Files\MaxCut Software\MaxCut v2\MaxCut.exe" | C:\Program Files\MaxCut Software\MaxCut v2\MaxCut.exe | explorer.exe | ||||||||||||
User: admin Company: MaxCut Software Ltd Integrity Level: MEDIUM Description: MaxCut Exit code: 0 Version: 2.9.0.31 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=2760 --field-trial-handle=1088,i,11269331173937500977,1908815433233384982,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1328 | rundll32.exe "C:\Windows\Installer\MSI2EEA.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_2240281 1 MaxCut.CustomActions!MaxCut.BackupMaterials.CustomActions.MigrateToMaxCutSoftwareDataDirectory | C:\Windows\System32\rundll32.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://s2.pesk.top/eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJleHAiOjE3NjcyMTg0MDAsInN1YiI6Ik1heEN1dCBCdXNpbmVzcyBFZGl0aW9uIDIuOS4wLjMxIFtwZXNrdG9wLmNvbV0ucmFyIiwic291cmNlIjoiaHR0cHM6XC9cL3Blc2t0b3AuY29tXC8ifQ.7IHgeBPIF_aBJmtKIvgmPdwb45FwBANelQ_VgcfECj4" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1600 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\MaxCut Business Edition 2.9.0.31 [pesktop.com]\MaxCut Business Edition 2.9.0.31 [pesktop.com]\Instructions.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
23 454
Read events
23 276
Write events
163
Delete events
15
Modification events
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
| (PID) Process: | (1556) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_enableddate |
Value: 0 | |||
Executable files
105
Suspicious files
155
Text files
78
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF210157.TMP | — | |
MD5:— | SHA256:— | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:9F941EA08DBDCA2EB3CFA1DBBBA6F5DC | SHA256:127F71DF0D2AD895D4F293E62284D85971AE047CA15F90B87BF6335898B0B655 | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF2103d7.TMP | — | |
MD5:— | SHA256:— | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF210157.TMP | text | |
MD5:513218482935B0D388C0A990D868387A | SHA256:8E39CBAAF4AACC3A01AFA74EA8C30FB24FE69A22B8B30728AFB1614FD68809D9 | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:43550DBA2277BE44F5F842196E084145 | SHA256:D19055342C06316F8B80D0B029BD233A3E48AD4C591953AF7B712ADA7F68F403 | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old~RF210270.TMP | text | |
MD5:8268A4D53A6A9432A8266584CBD7D624 | SHA256:F785C42945CFE320C52C763837CD41541A8CAAB3E5FD567999EED5343CF0FD7A | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF210166.TMP | text | |
MD5:E91E138A25FD7E5BCA5E60111F39C91A | SHA256:B1F7E3537A31A4B847F862858E5D2581993CC9372F19ABF19EA2A9185FE42A4F | |||
| 1556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
51
TCP/UDP connections
26
DNS requests
22
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | — | — | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 21.3 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 44.1 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 342 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 77.5 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 164 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 1.15 Mb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 672 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 692 Kb | unknown |
868 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adhioj45hzjkfunn7ccrbqyyhu3q_20230916.567854667.14/obedbbhbpmojnkanicioggnmelmoomoc_20230916.567854667.14_all_ENUS500000_lr7434qyx46lykosg2elaepqdi.crx3 | unknown | binary | 1.05 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1556 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2300 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
2300 | chrome.exe | 144.76.154.148:443 | s2.pesk.top | Hetzner Online GmbH | DE | unknown |
1556 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
2300 | chrome.exe | 142.250.186.100:443 | www.google.com | GOOGLE | US | whitelisted |
2300 | chrome.exe | 172.217.16.202:443 | optimizationguide-pa.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
s2.pesk.top |
| unknown |
www.google.com |
| whitelisted |
optimizationguide-pa.googleapis.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
activation.maxcut.co.za |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2300 | chrome.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |