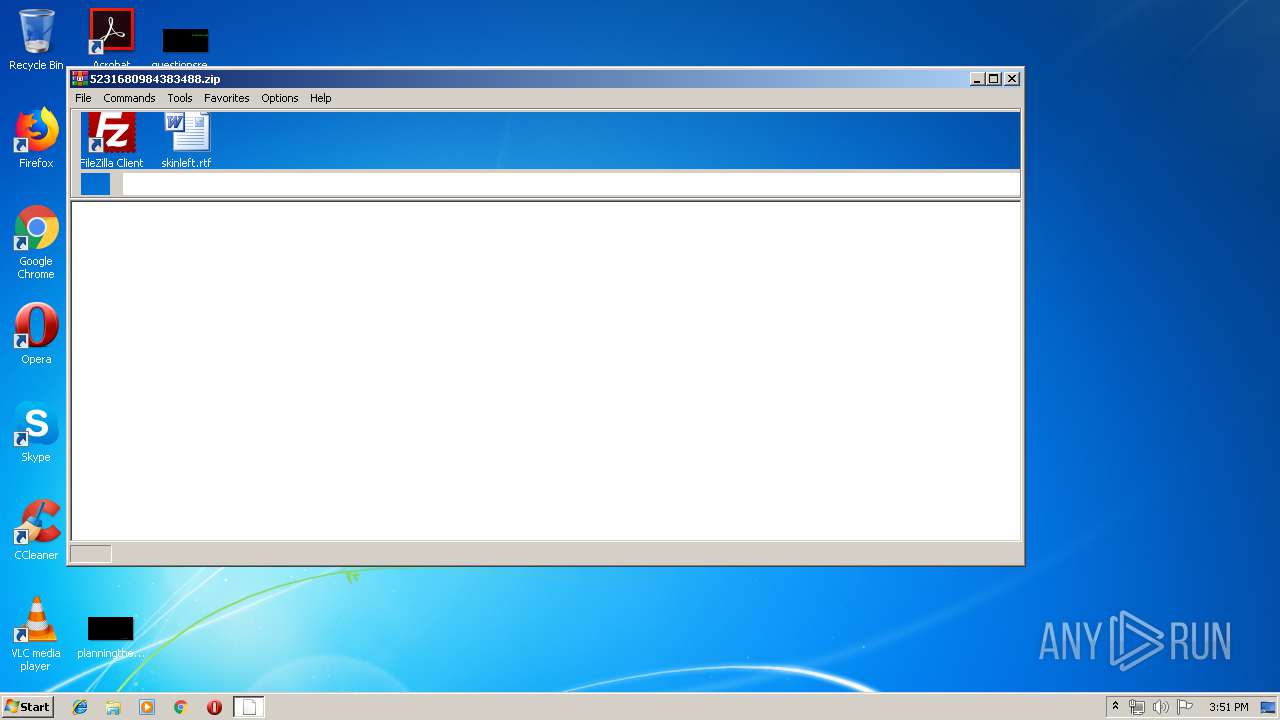
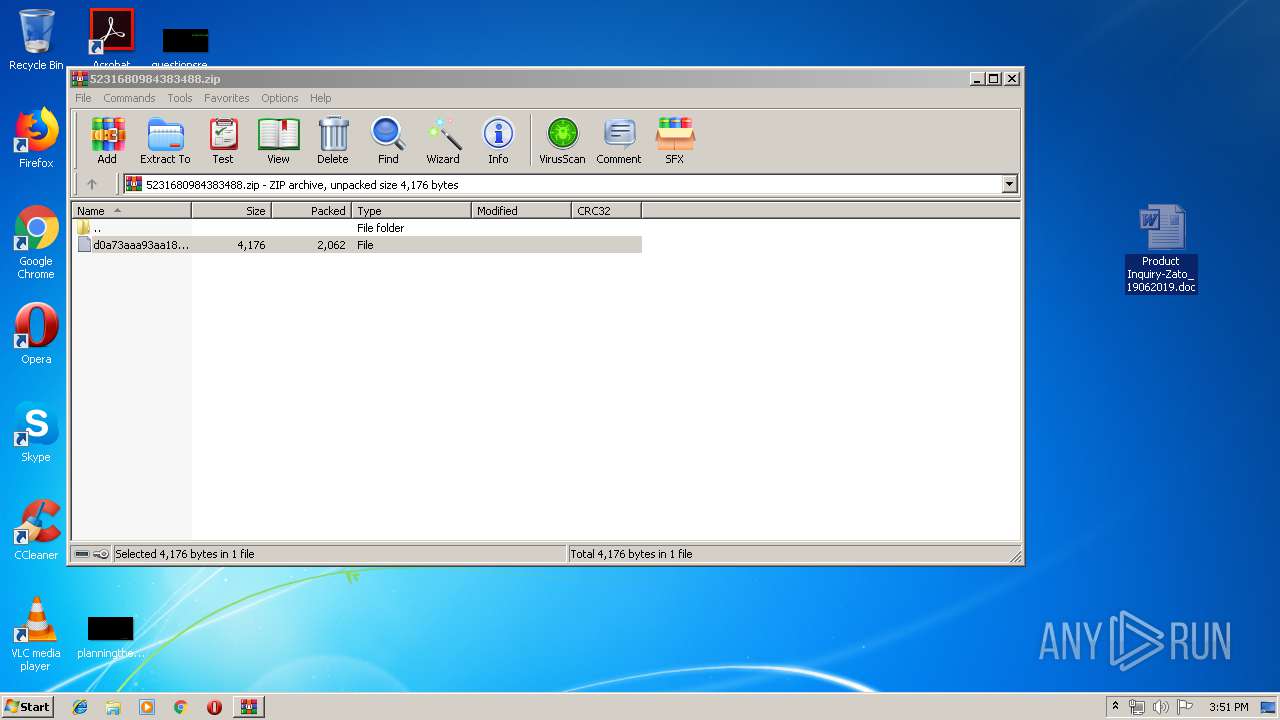
| File name: | 5231680984383488.zip |
| Full analysis: | https://app.any.run/tasks/a85c3d42-4d8b-4c09-9c9e-f7dfa03a0085 |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2019, 14:51:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | D3FE3B7F359F49E682803EE9C77DB3F1 |
| SHA1: | 07557E9C61D03444D620BA9A4FF29034D10E9060 |
| SHA256: | 910D8547E144C17FA9211C47F4986C2B06B4A9716DAEAAE85E6BEE18FCCF8593 |
| SSDEEP: | 48:9skGYBUXufDiytFCK5LyYoYrDcAv9+dHGVoNbusgbJ3KenO:OPdeNvRmY5kdHtusgbJaenO |
MALICIOUS
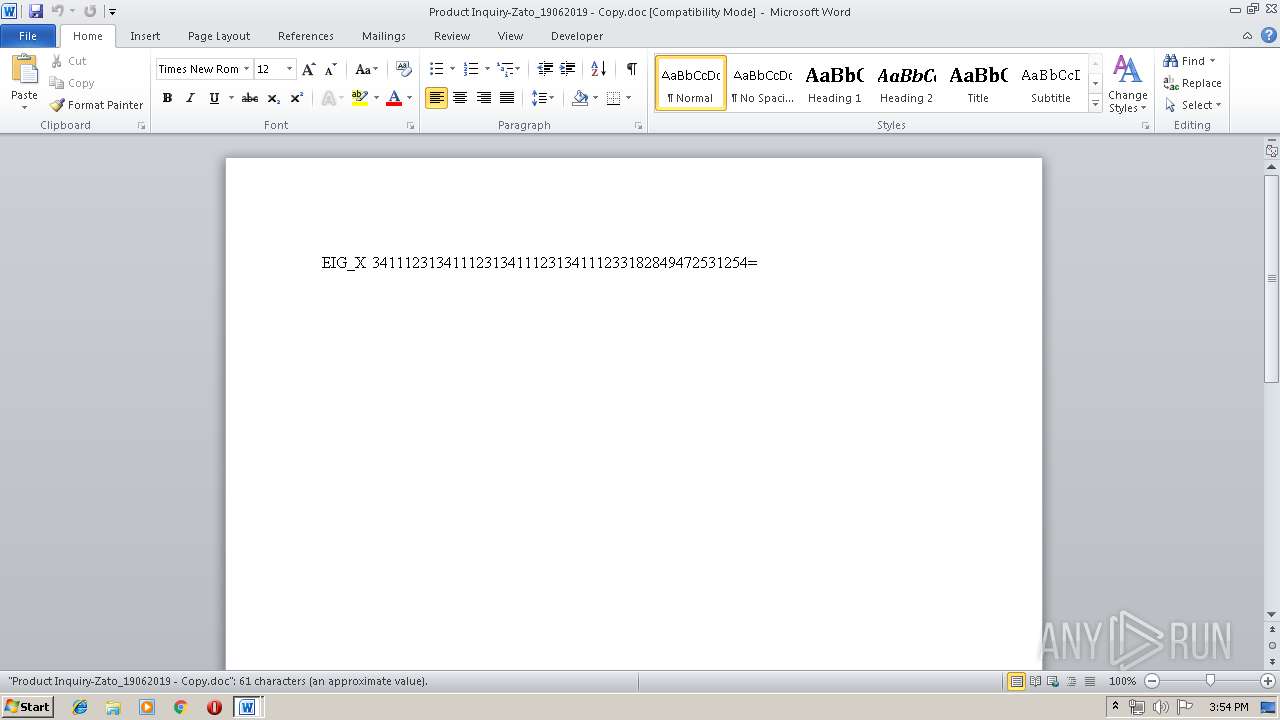
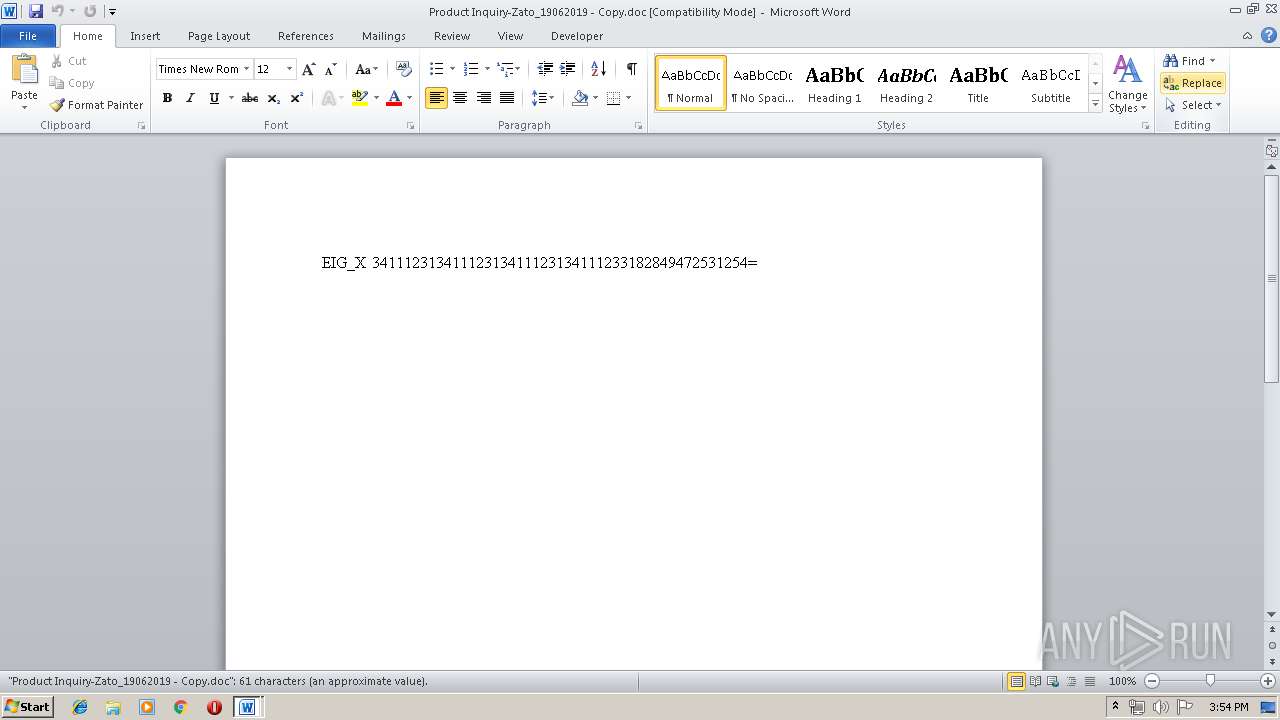
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 1696)
- EQNEDT32.EXE (PID: 1424)
Application was dropped or rewritten from another process
- fjhrekdml;sa.exe (PID: 572)
- fjhrekdml;sa.exe (PID: 2520)
Actions looks like stealing of personal data
- RegAsm.exe (PID: 3060)
- RegAsm.exe (PID: 1372)
SUSPICIOUS
Executed via COM
- EQNEDT32.EXE (PID: 1696)
- EQNEDT32.EXE (PID: 1424)
Executable content was dropped or overwritten
- EQNEDT32.EXE (PID: 1696)
- EQNEDT32.EXE (PID: 1424)
Creates files in the user directory
- EQNEDT32.EXE (PID: 1696)
INFO
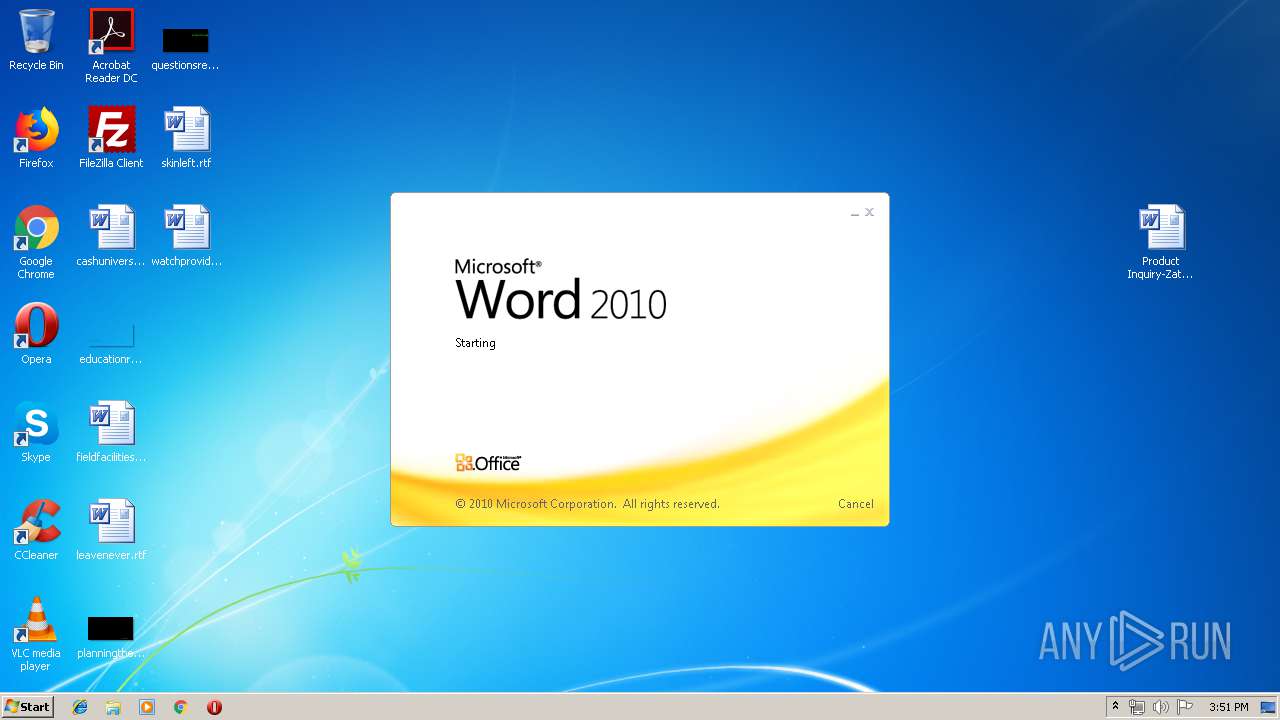
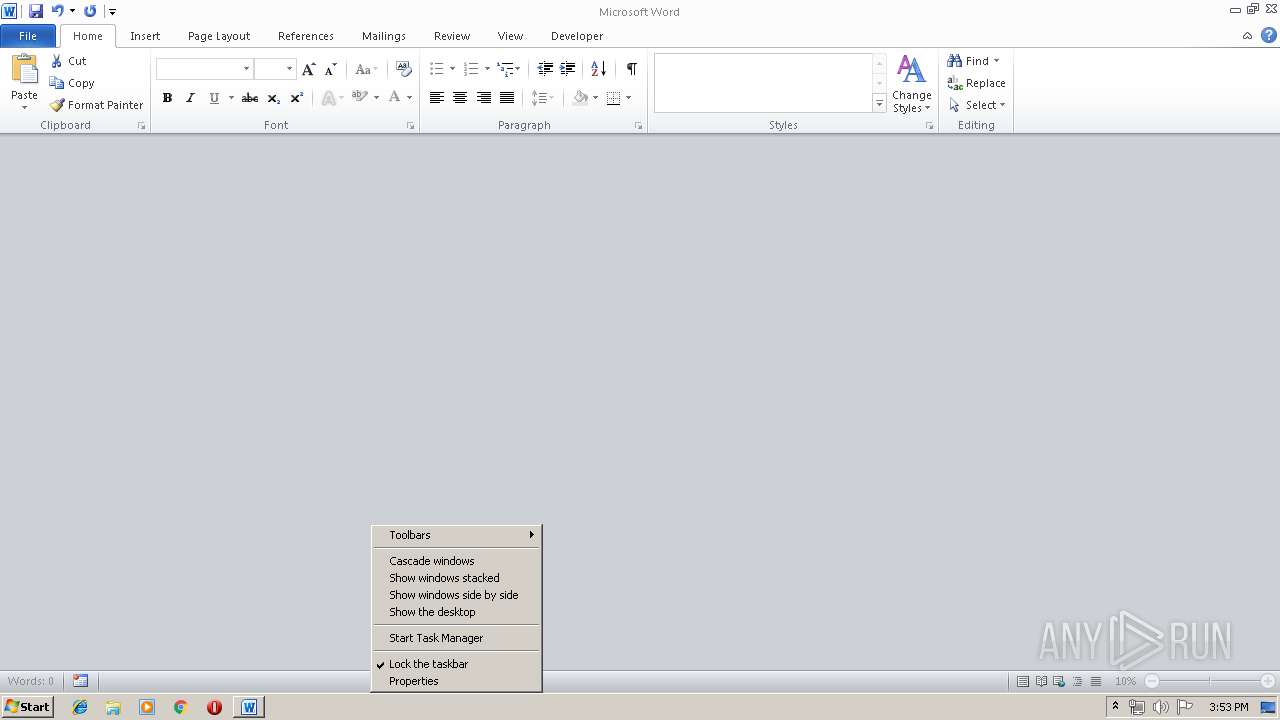
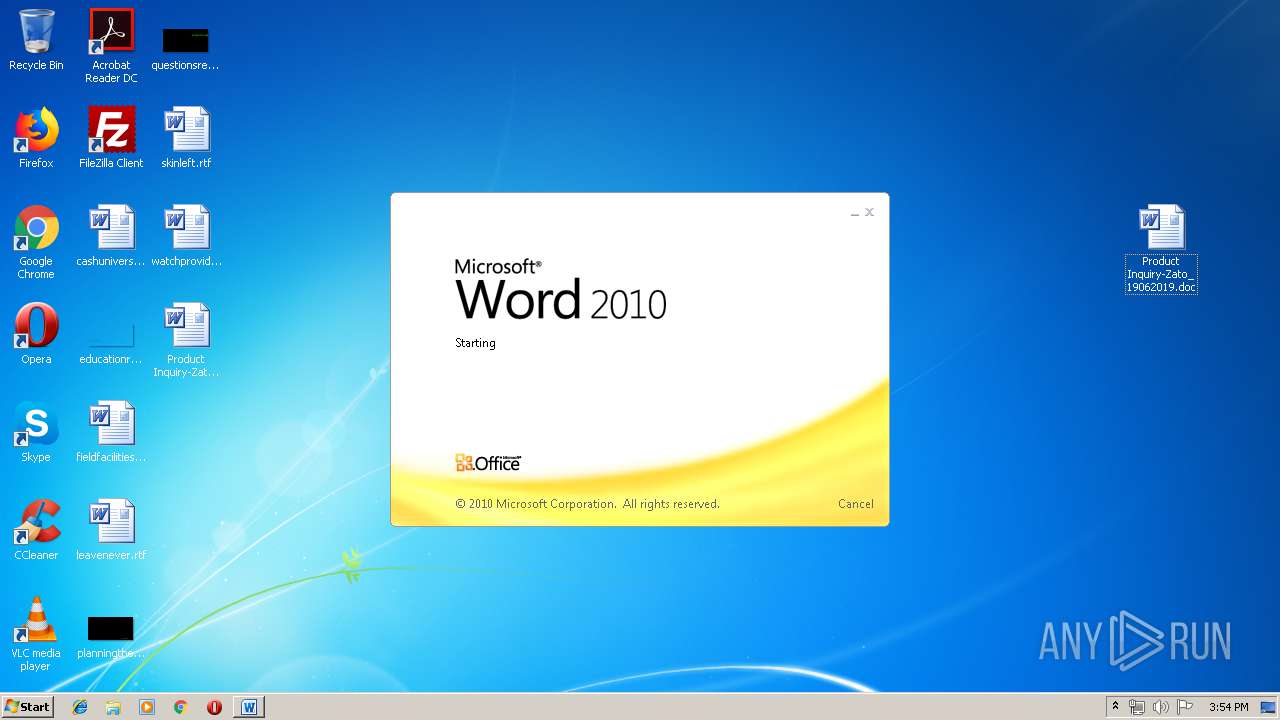
Manual execution by user
- WINWORD.EXE (PID: 3276)
- WINWORD.EXE (PID: 3712)
- WINWORD.EXE (PID: 124)
Creates files in the user directory
- WINWORD.EXE (PID: 3276)
- WINWORD.EXE (PID: 124)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3276)
- WINWORD.EXE (PID: 3712)
- WINWORD.EXE (PID: 124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
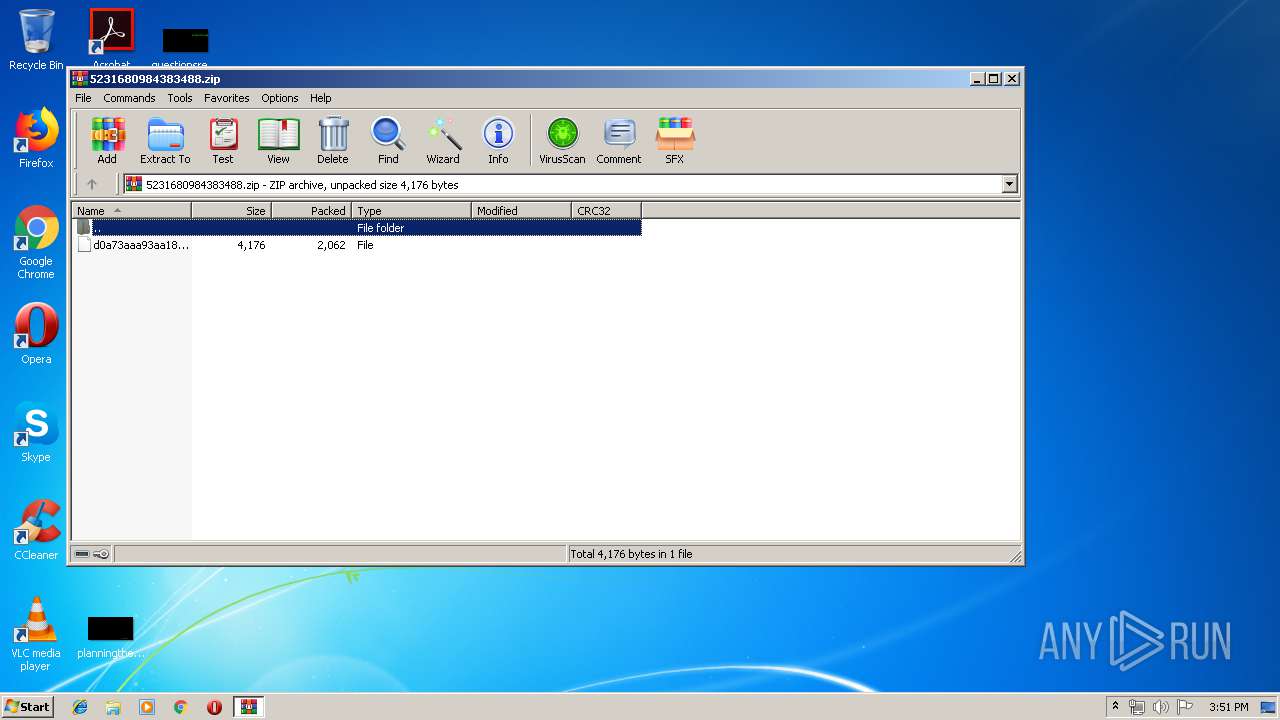
| ZipRequiredVersion: | 20 |
|---|---|
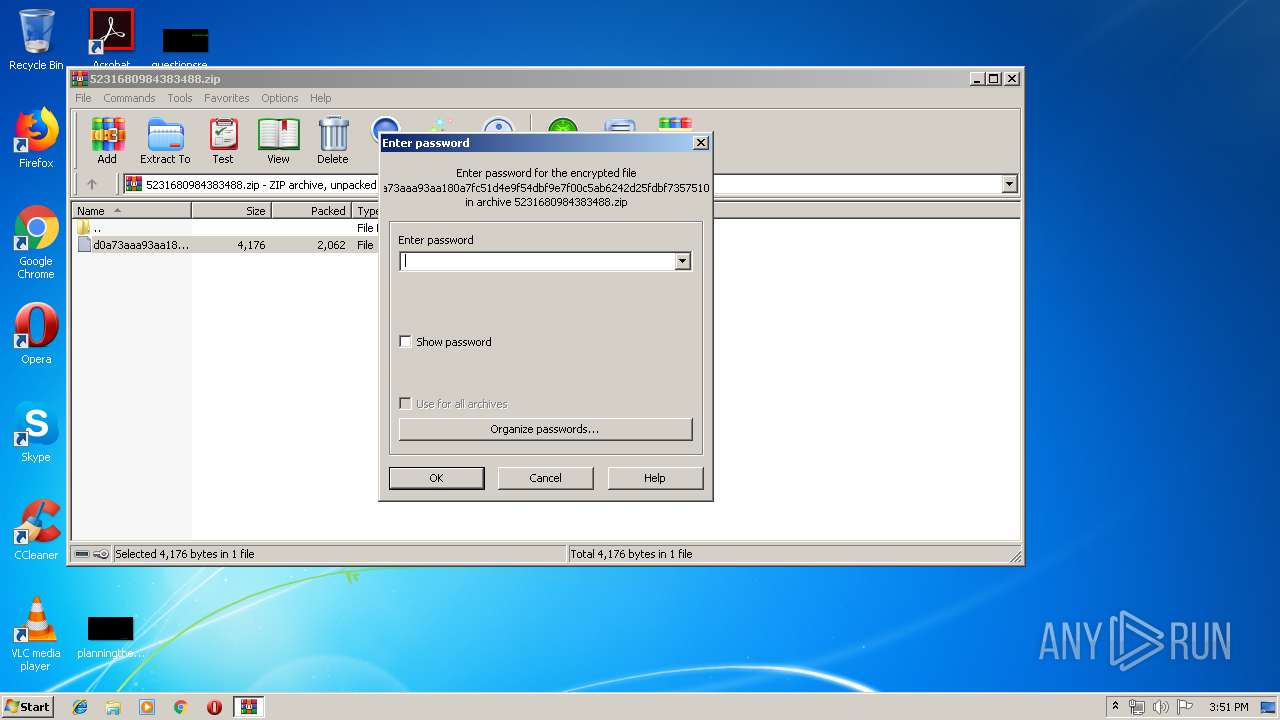
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0x00000000 |
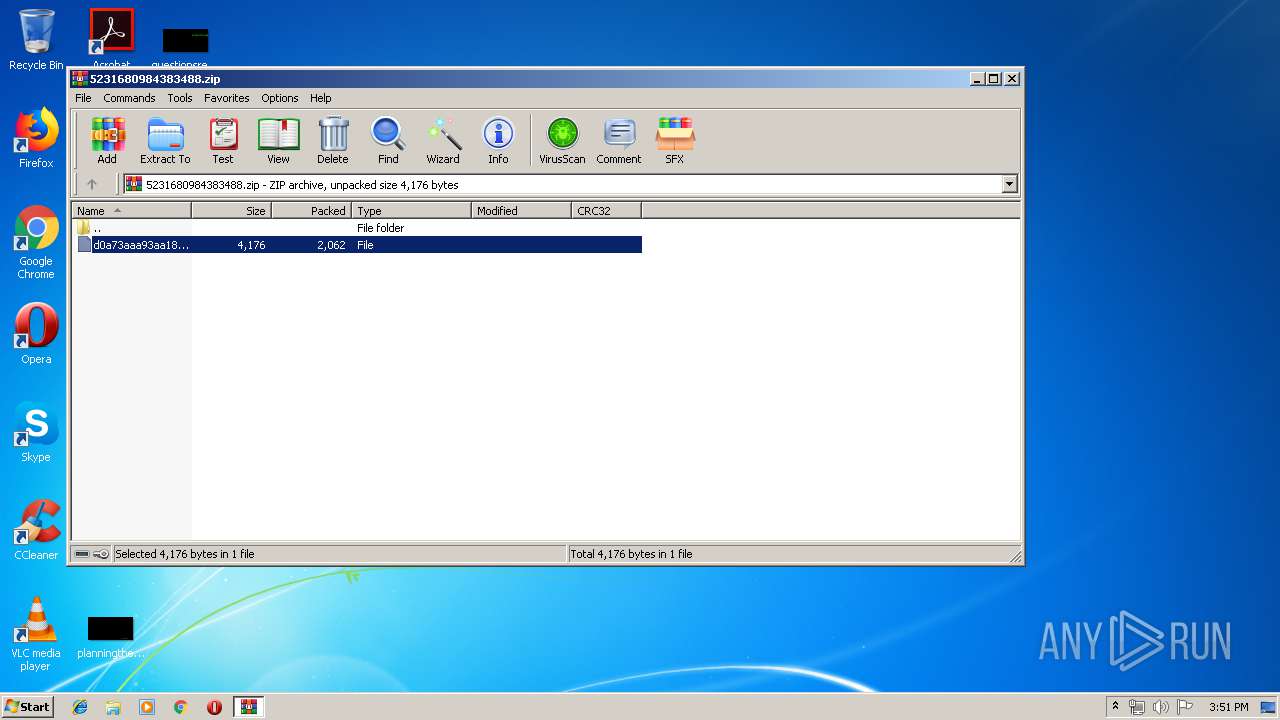
| ZipCompressedSize: | 2062 |
| ZipUncompressedSize: | 4176 |
| ZipFileName: | d0a73aaa93aa180a7fc51d4e9f54dbf9e7f00c5ab6242d25fdbf73575107a709 |
Total processes
47
Monitored processes
10
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Product Inquiry-Zato_19062019 - Copy.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 572 | "C:\Users\admin\AppData\Roaming\fjhrekdml;sa.exe" | C:\Users\admin\AppData\Roaming\fjhrekdml;sa.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1372 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | fjhrekdml;sa.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 1696 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 2520 | "C:\Users\admin\AppData\Roaming\fjhrekdml;sa.exe" | C:\Users\admin\AppData\Roaming\fjhrekdml;sa.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3060 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | fjhrekdml;sa.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 4294967295 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
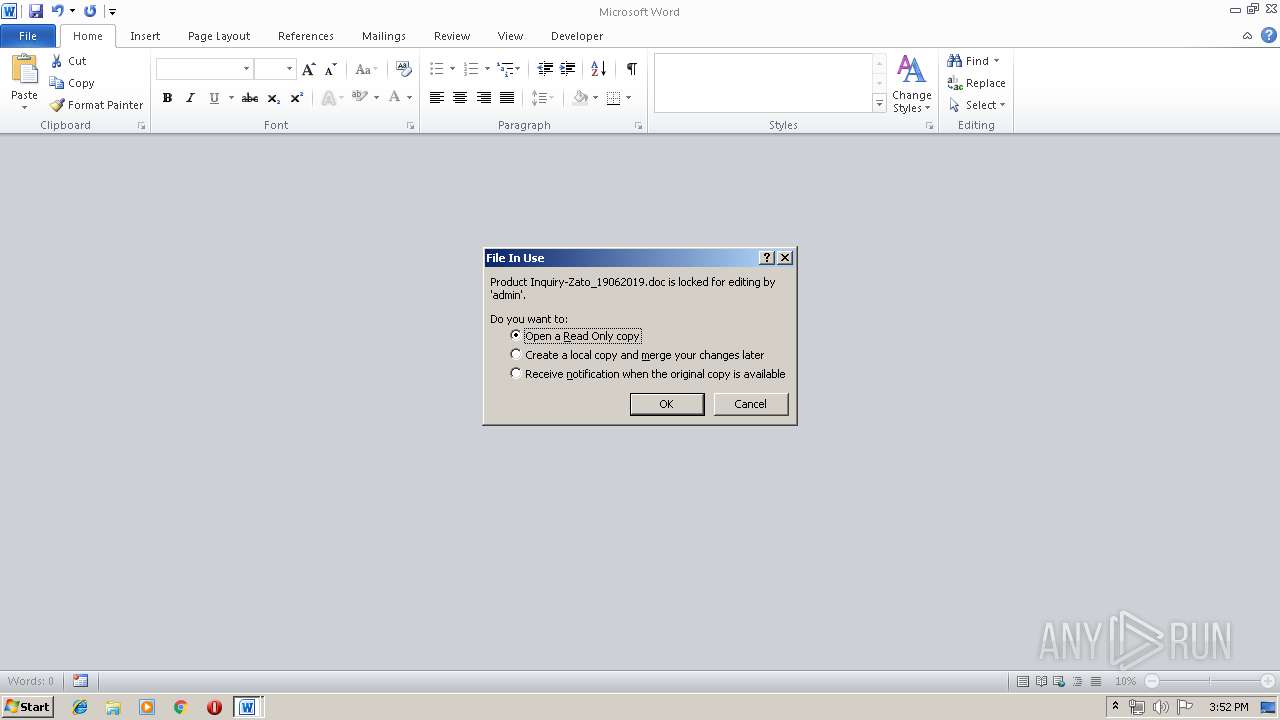
| 3276 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Product Inquiry-Zato_19062019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3564 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\5231680984383488.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3712 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\Product Inquiry-Zato_19062019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 471
Read events
2 008
Write events
443
Delete events
20
Modification events
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\5231680984383488.zip | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3564) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3276) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | f7f81a39-5f63-5b42-9efd-1f13b5431005gt;! |
Value: 243E2100CC0C0000010000000000000000000000 | |||
Executable files
4
Suspicious files
0
Text files
4
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3564 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3564.38460\d0a73aaa93aa180a7fc51d4e9f54dbf9e7f00c5ab6242d25fdbf73575107a709 | — | |
MD5:— | SHA256:— | |||
| 3276 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7274.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2BF0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRC0000.tmp | — | |
MD5:— | SHA256:— | |||
| 3712 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{4C1D888D-2752-4BF5-88FB-875F277E9BA4}.tmp | — | |
MD5:— | SHA256:— | |||
| 124 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6EF0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3276 | WINWORD.EXE | C:\Users\admin\Desktop\~$oduct Inquiry-Zato_19062019.doc | pgc | |
MD5:— | SHA256:— | |||
| 1696 | EQNEDT32.EXE | C:\Users\admin\AppData\Roaming\fjhrekdml;sa.exe | executable | |
MD5:— | SHA256:— | |||
| 3276 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 124 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Product Inquiry-Zato_19062019 - Copy.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
3
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1696 | EQNEDT32.EXE | 112.213.89.40:443 | tfvn.com.vn | SUPERDATA | VN | malicious |
1424 | EQNEDT32.EXE | 112.213.89.40:443 | tfvn.com.vn | SUPERDATA | VN | malicious |
3060 | RegAsm.exe | 198.54.122.60:587 | mail.privateemail.com | Namecheap, Inc. | US | suspicious |
1372 | RegAsm.exe | 198.54.122.60:587 | mail.privateemail.com | Namecheap, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tfvn.com.vn |
| unknown |
mail.privateemail.com |
| malicious |
Threats
1 ETPRO signatures available at the full report