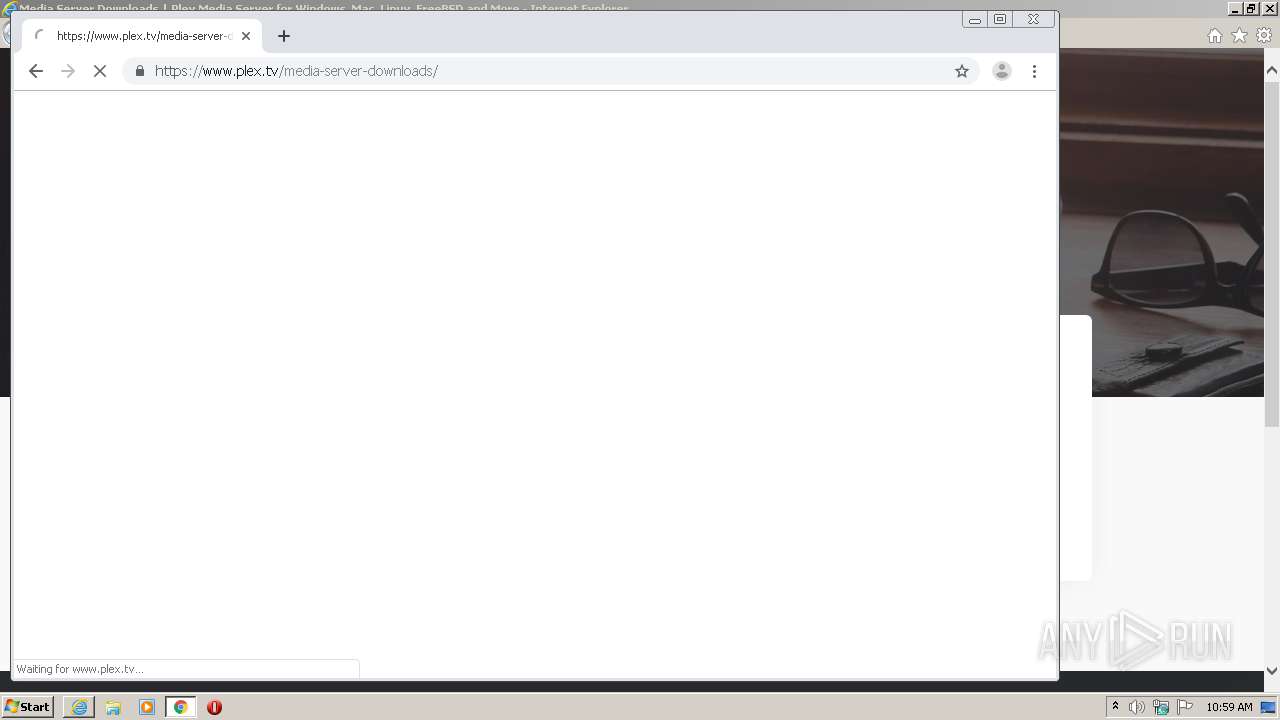
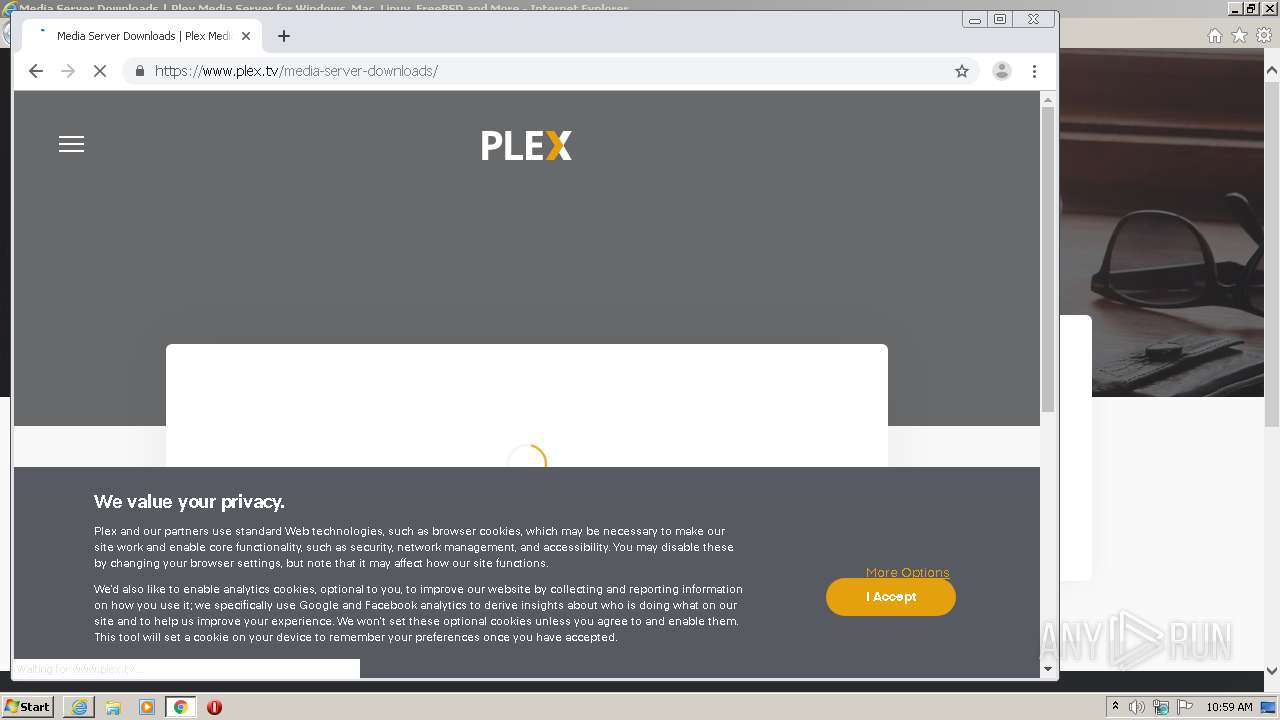
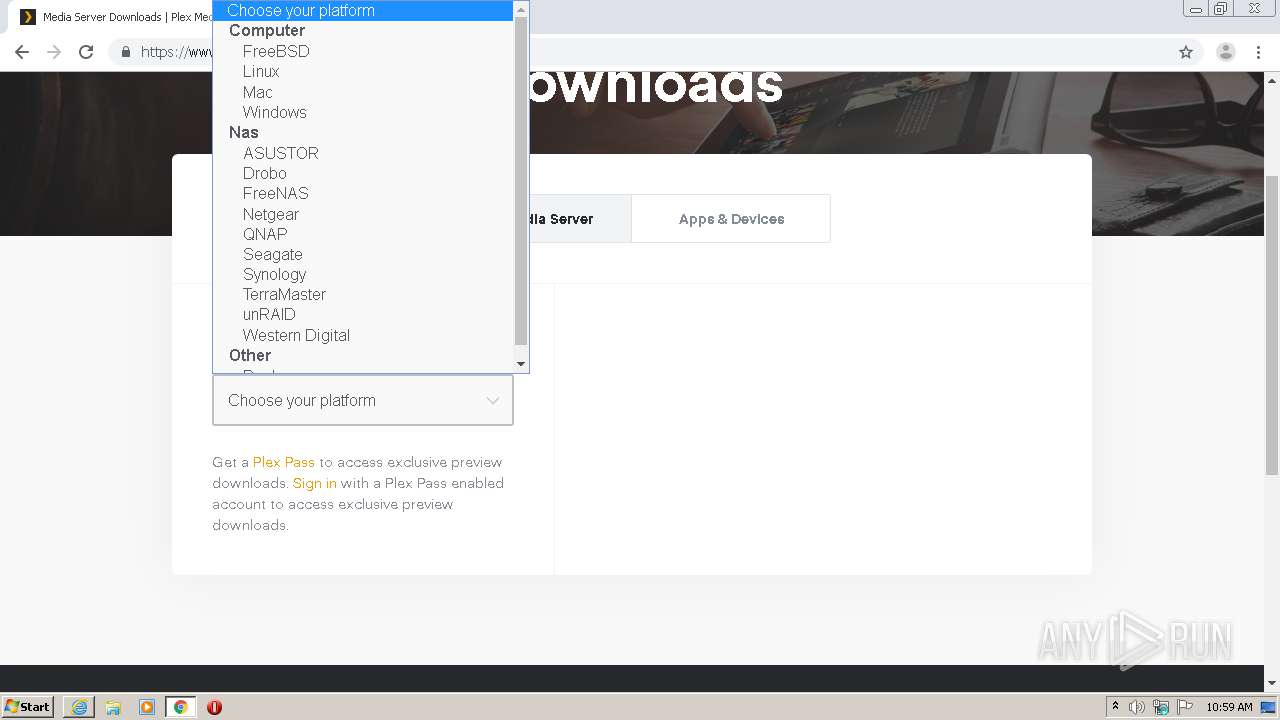
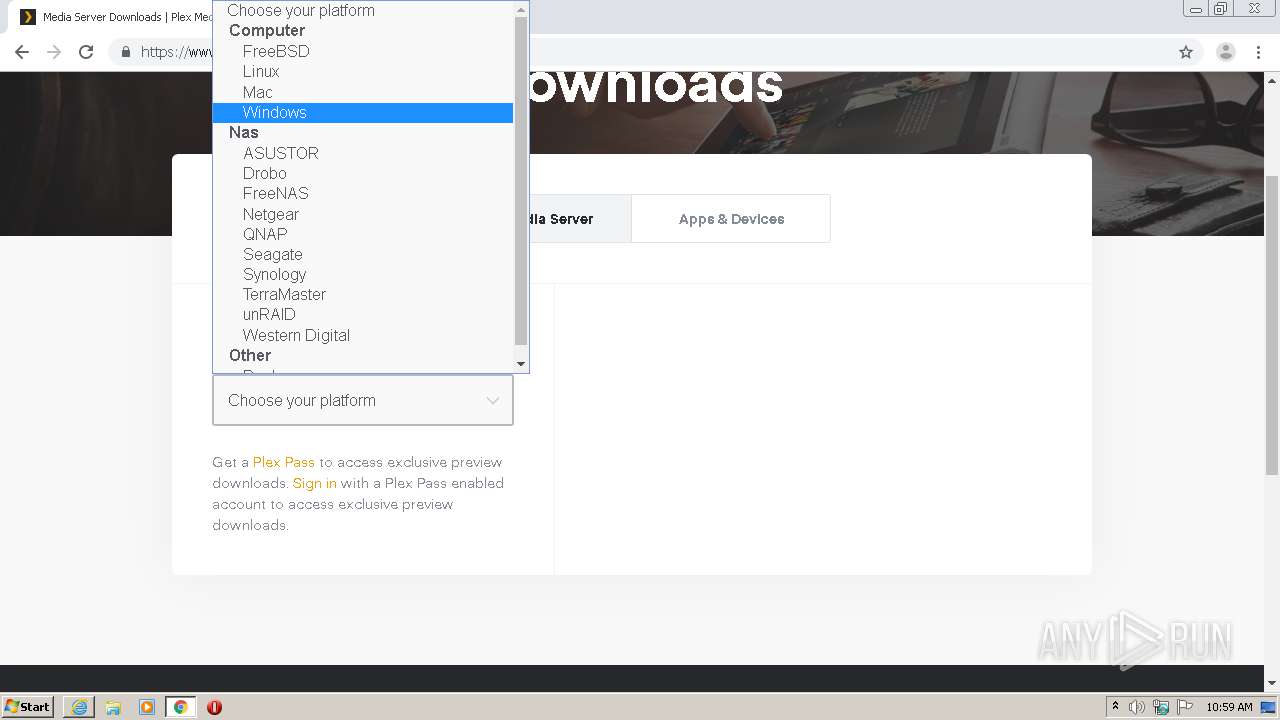
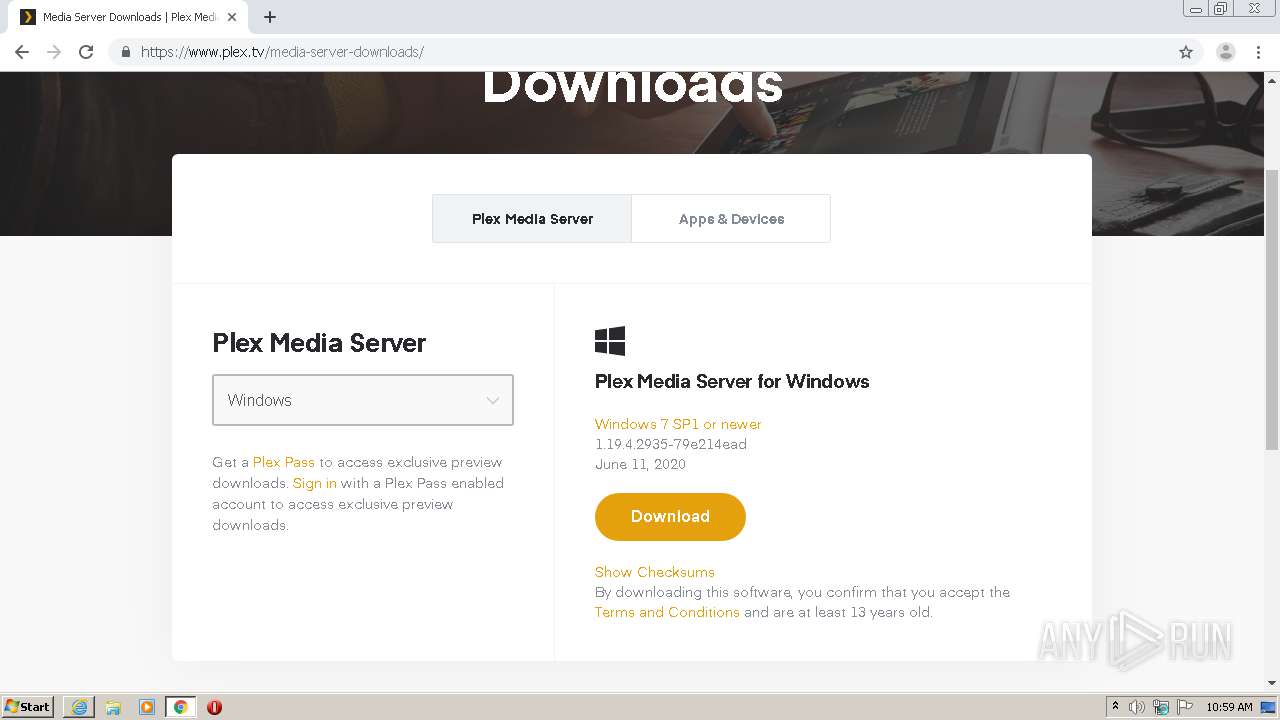
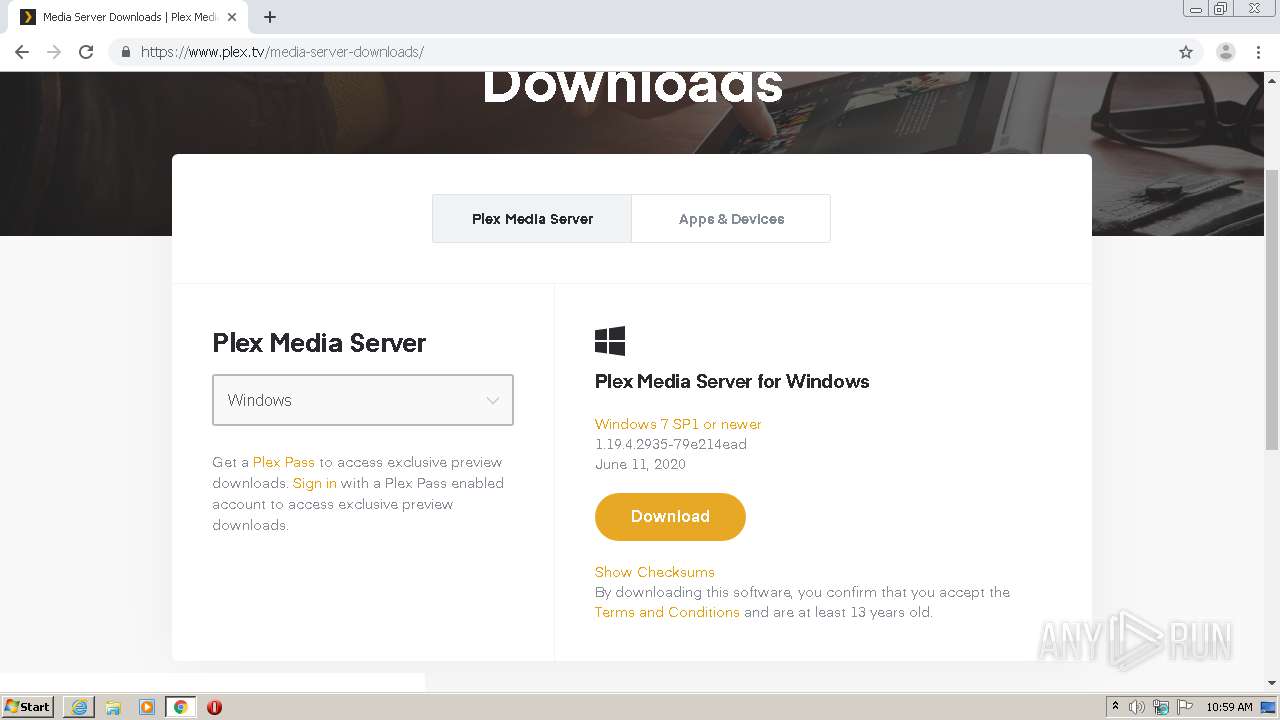
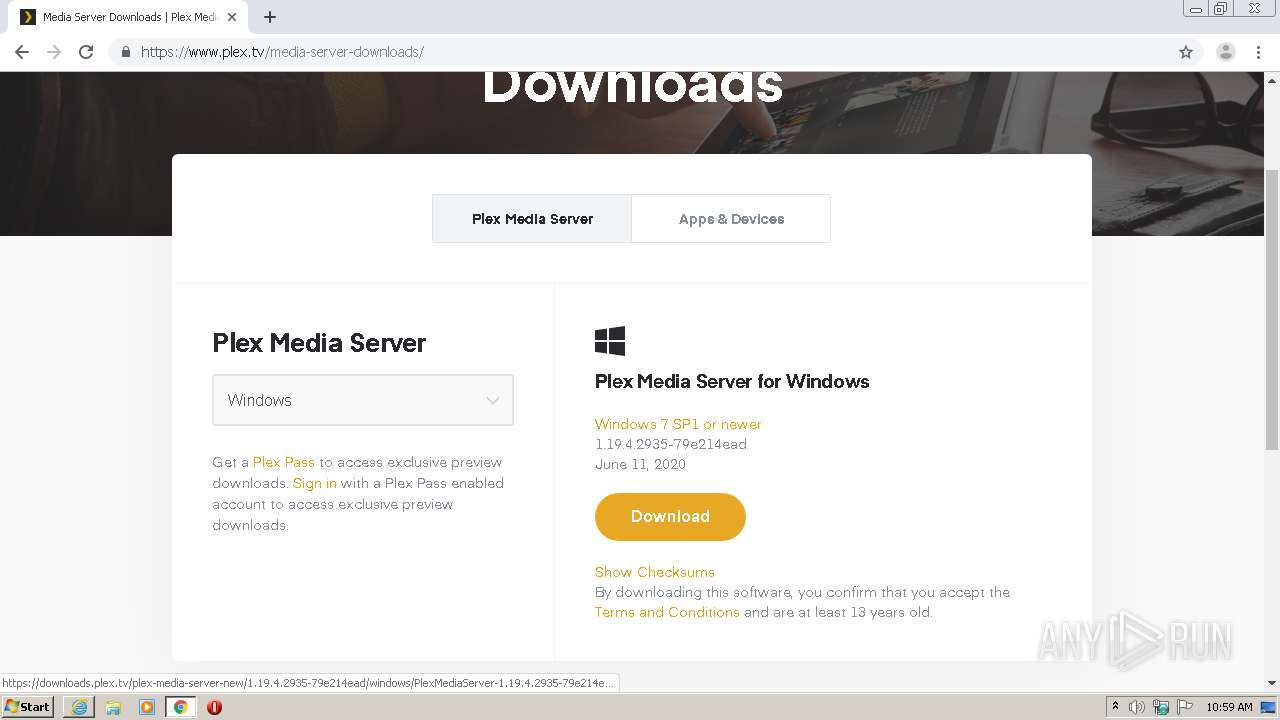
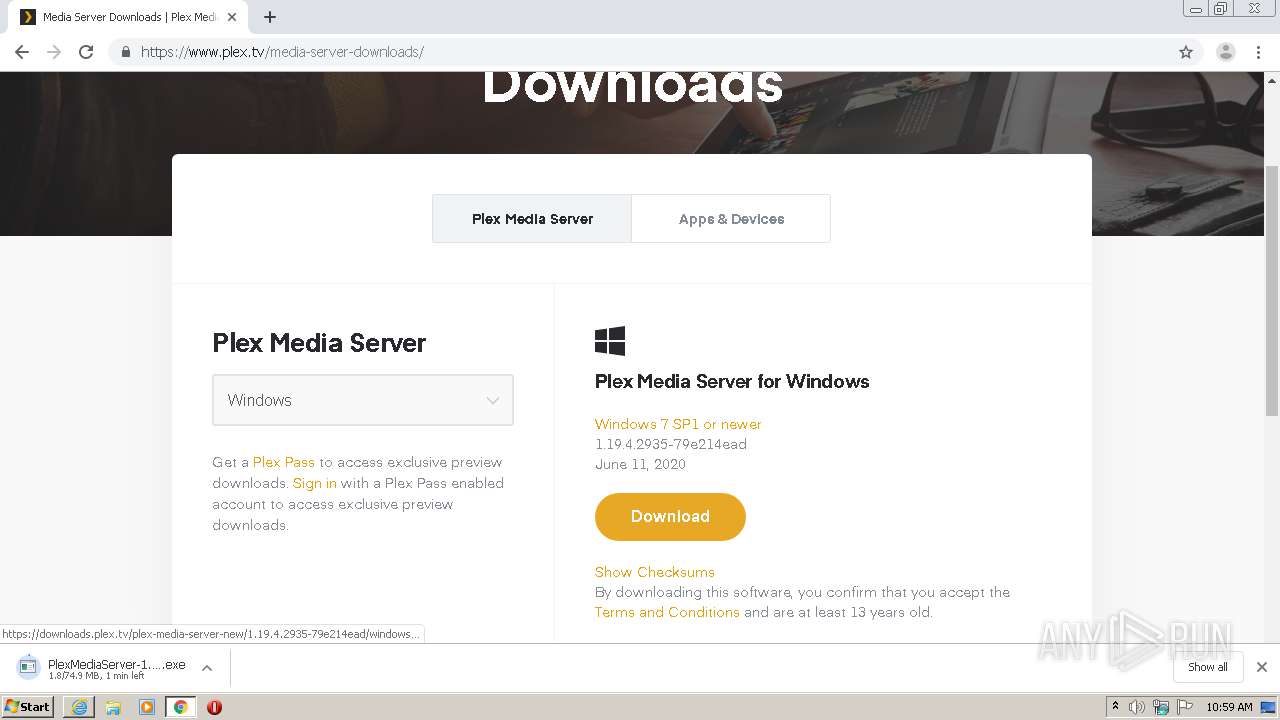
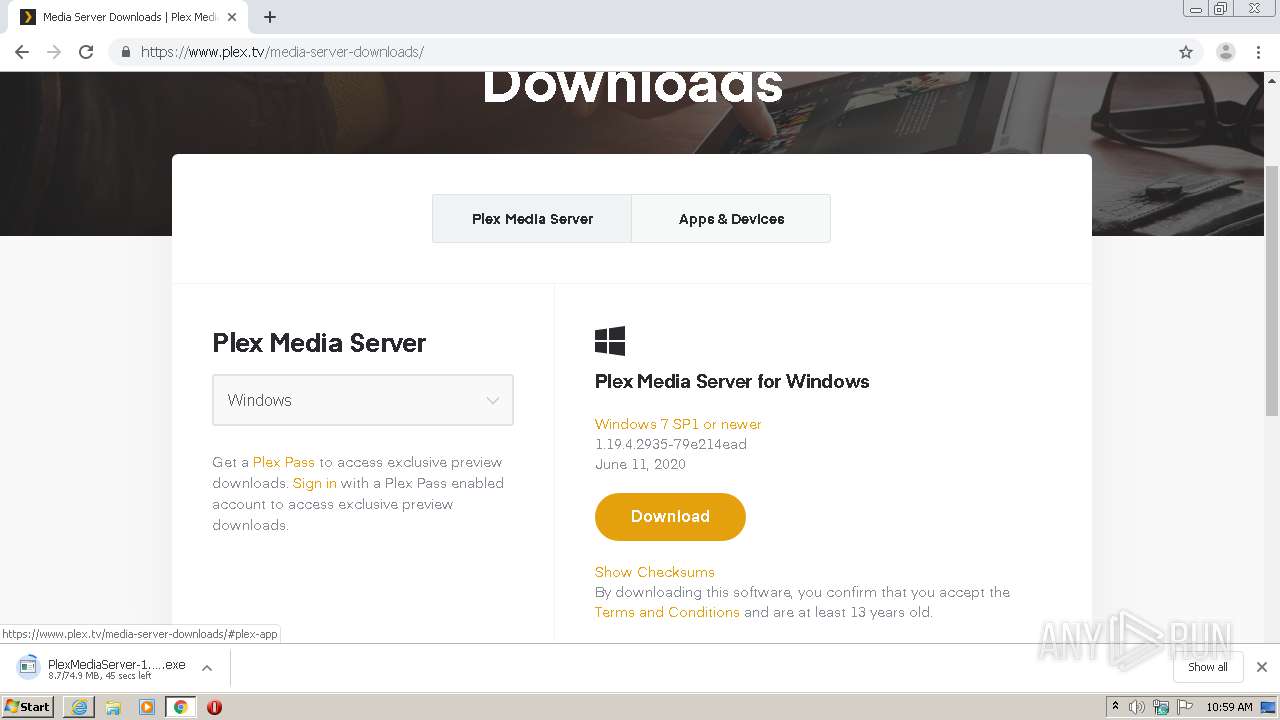
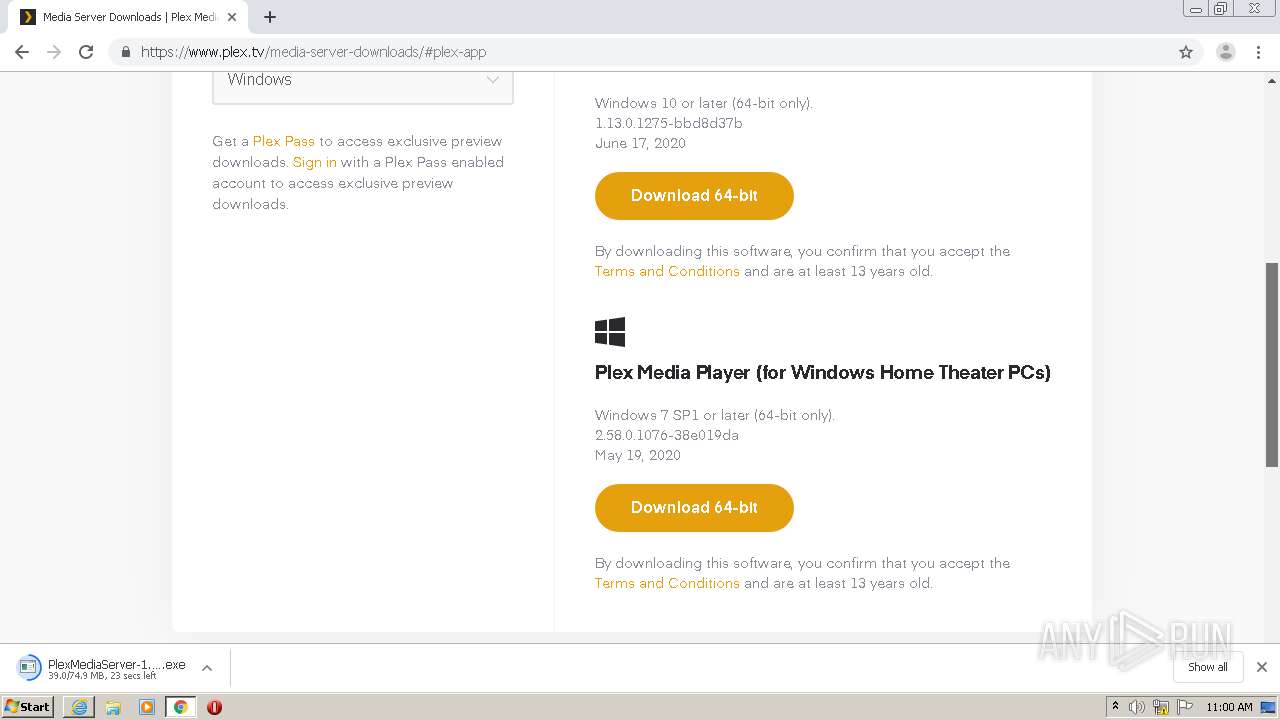
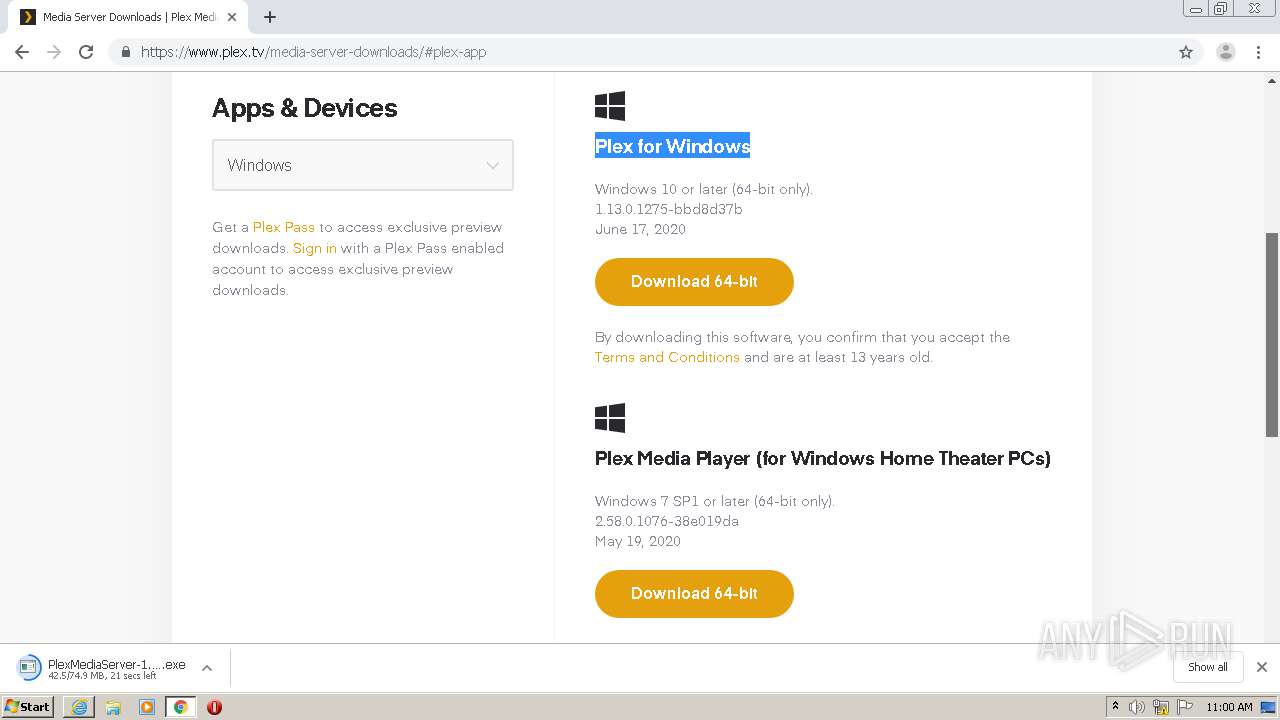
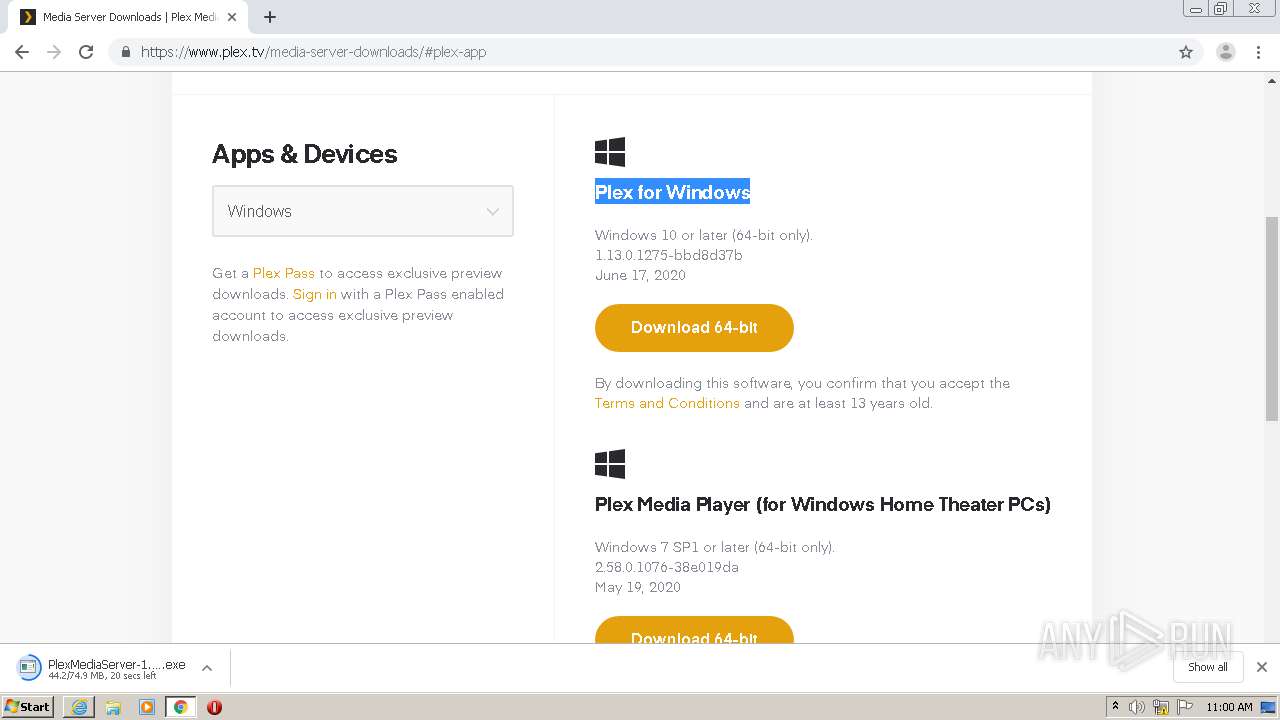
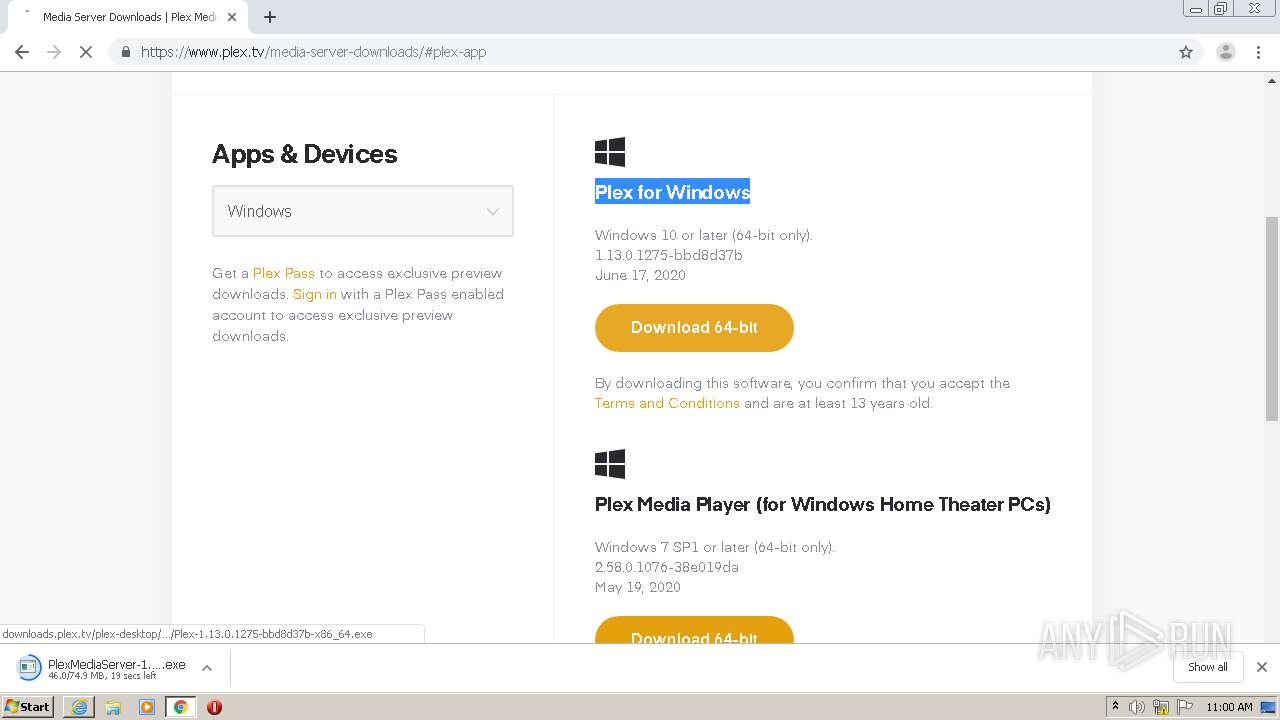
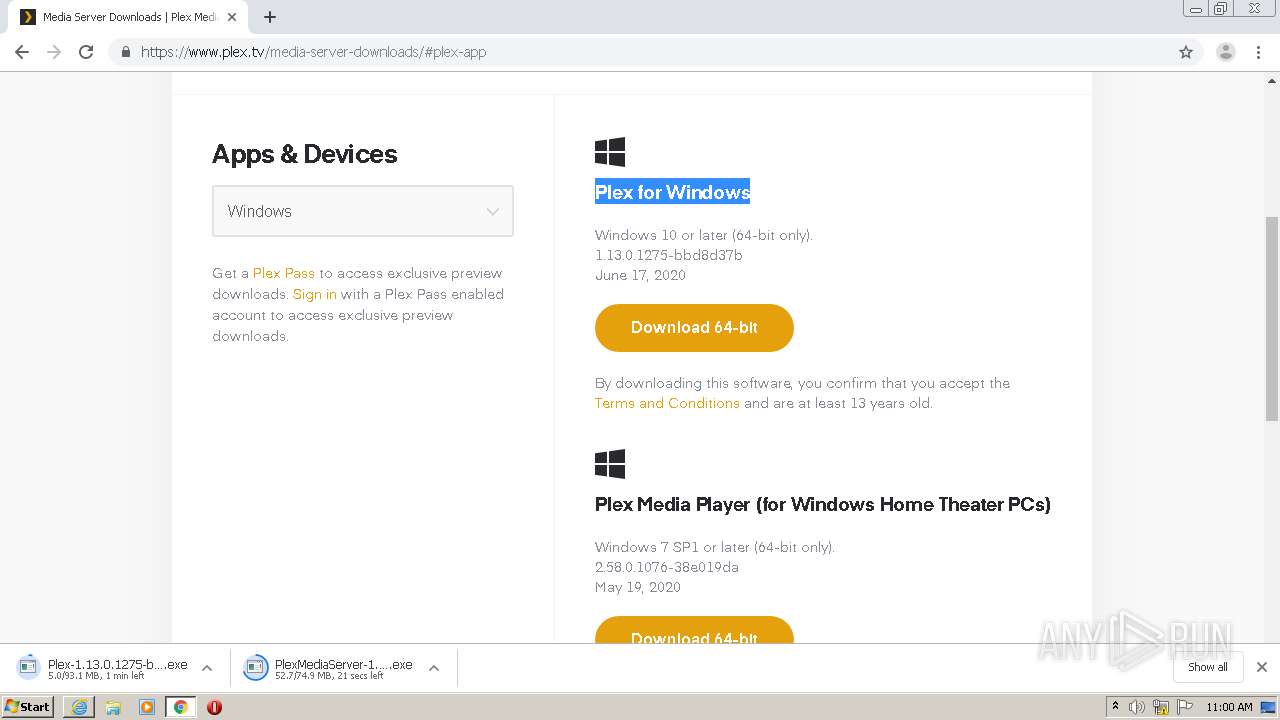
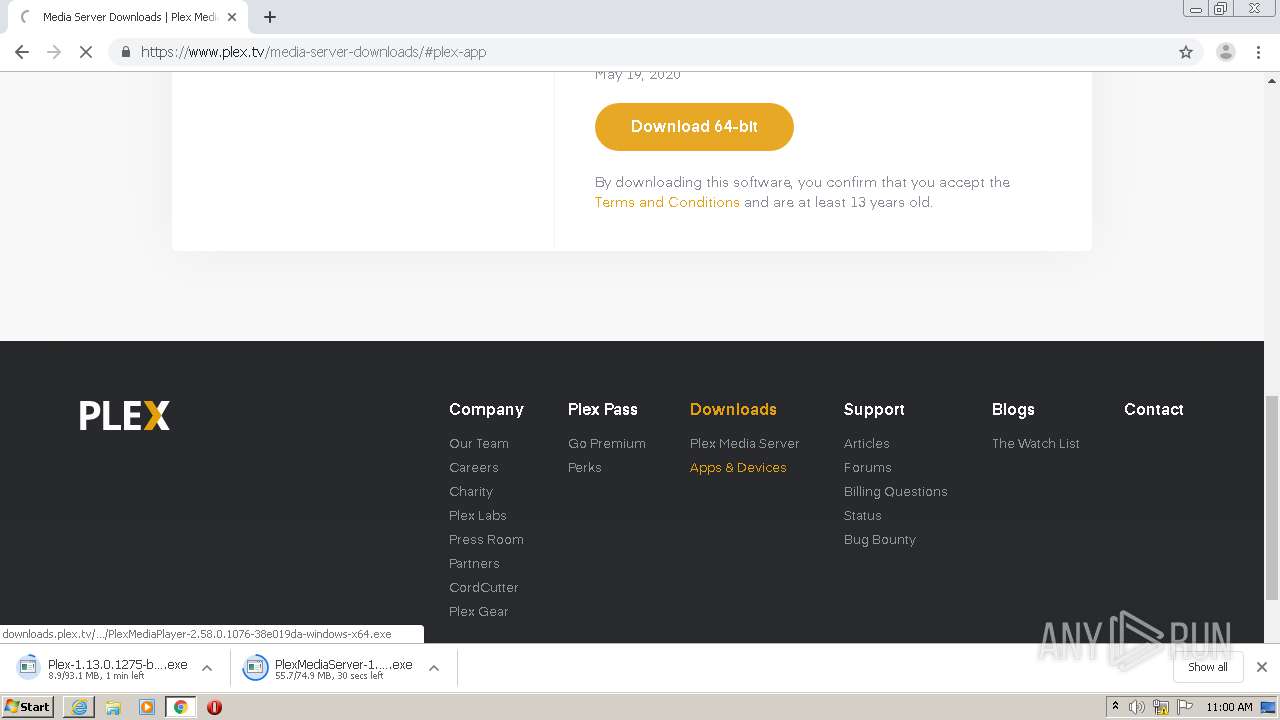
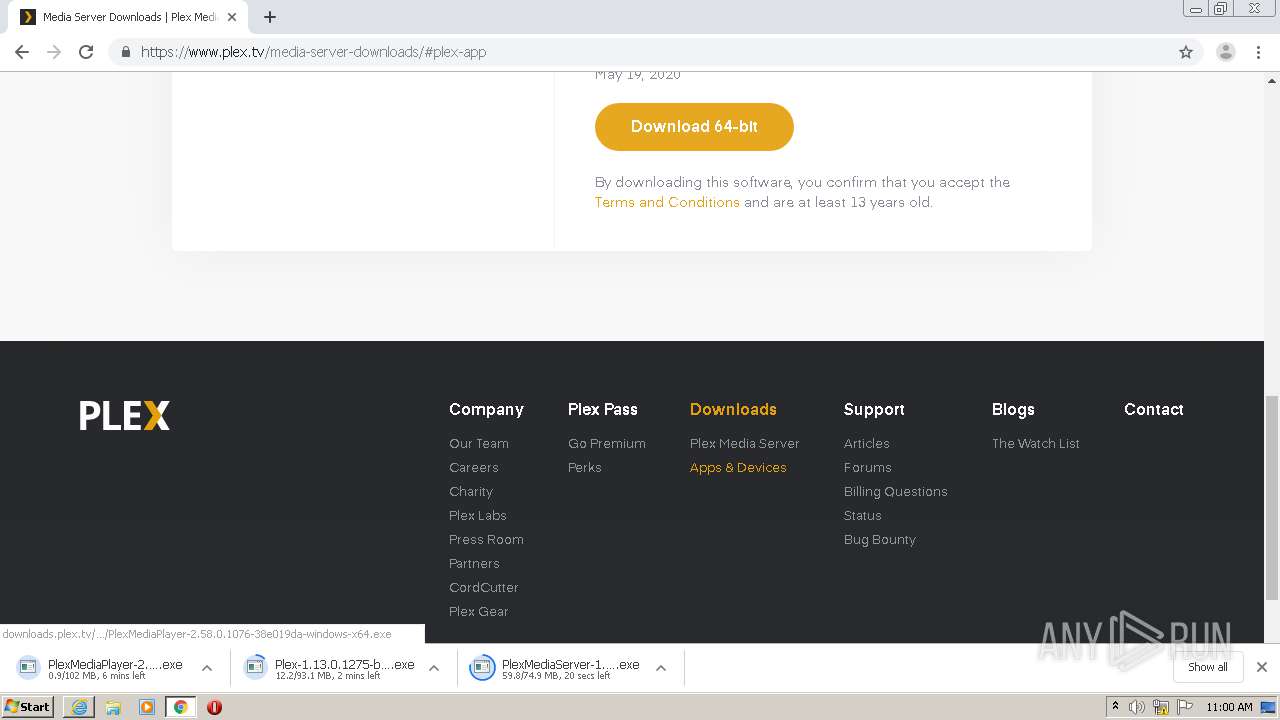
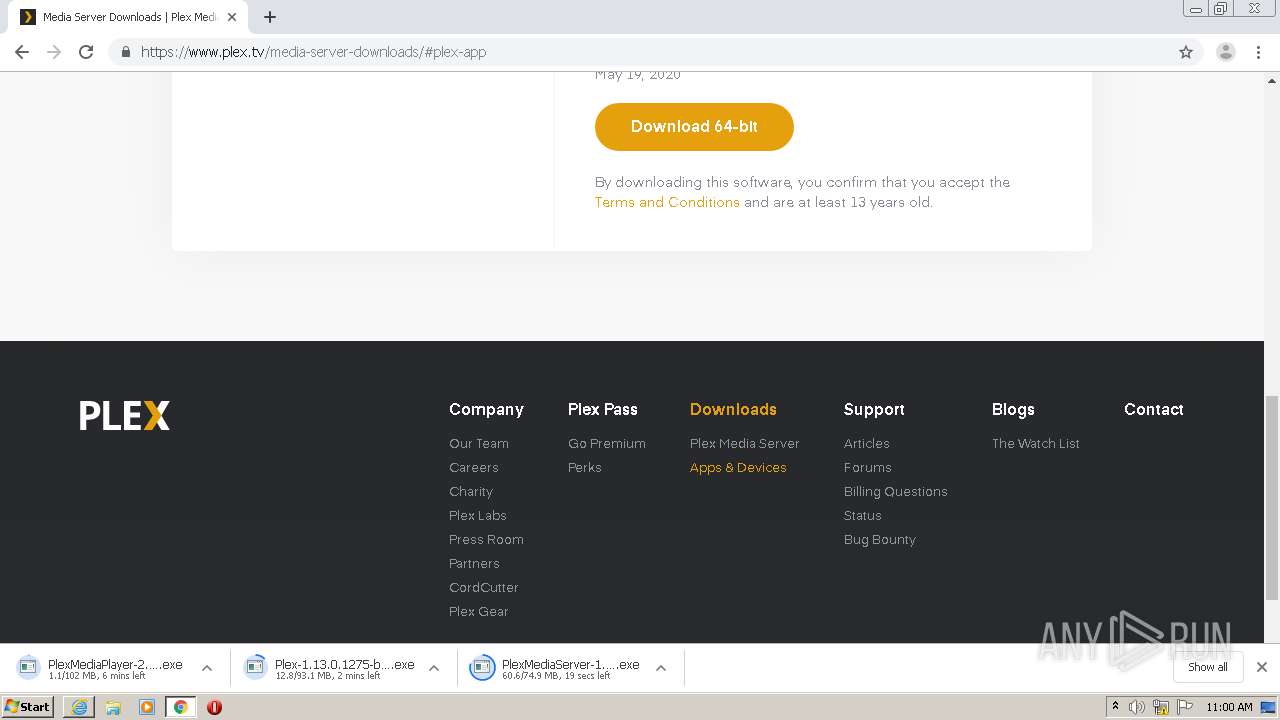
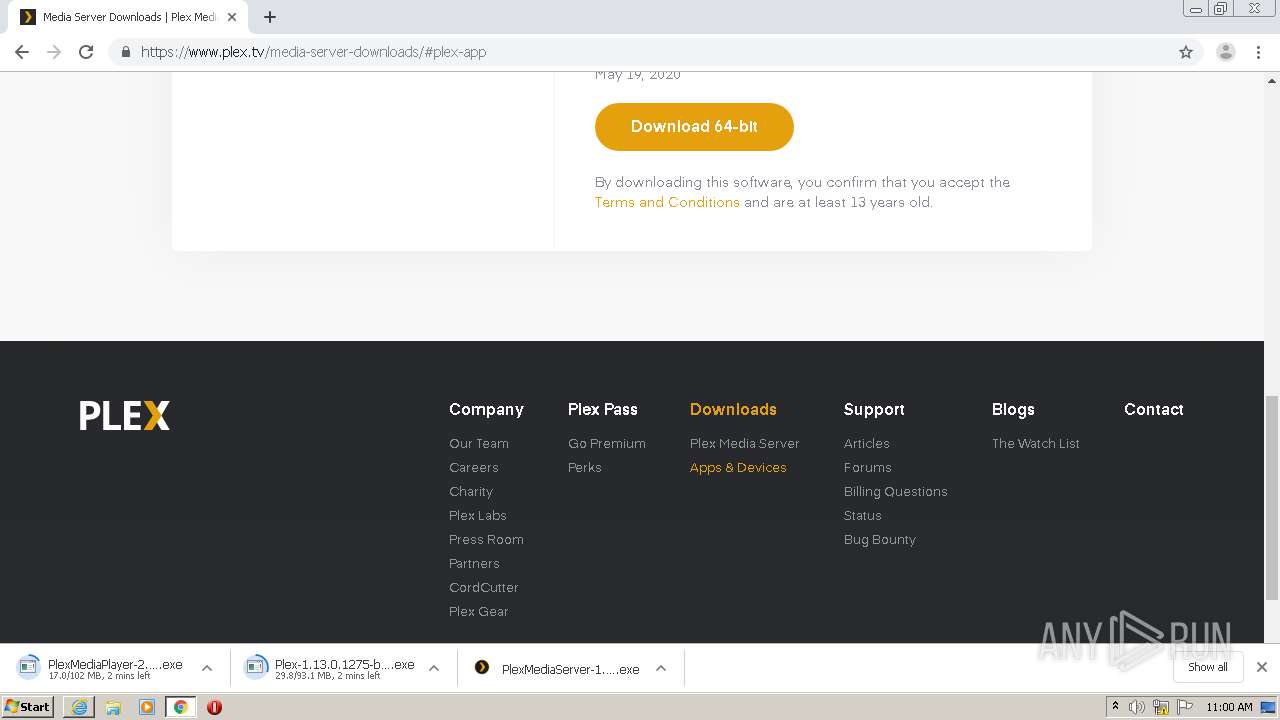
| URL: | https://www.plex.tv/media-server-downloads/ |
| Full analysis: | https://app.any.run/tasks/cee468f4-e18f-4053-8aaa-541a401a7499 |
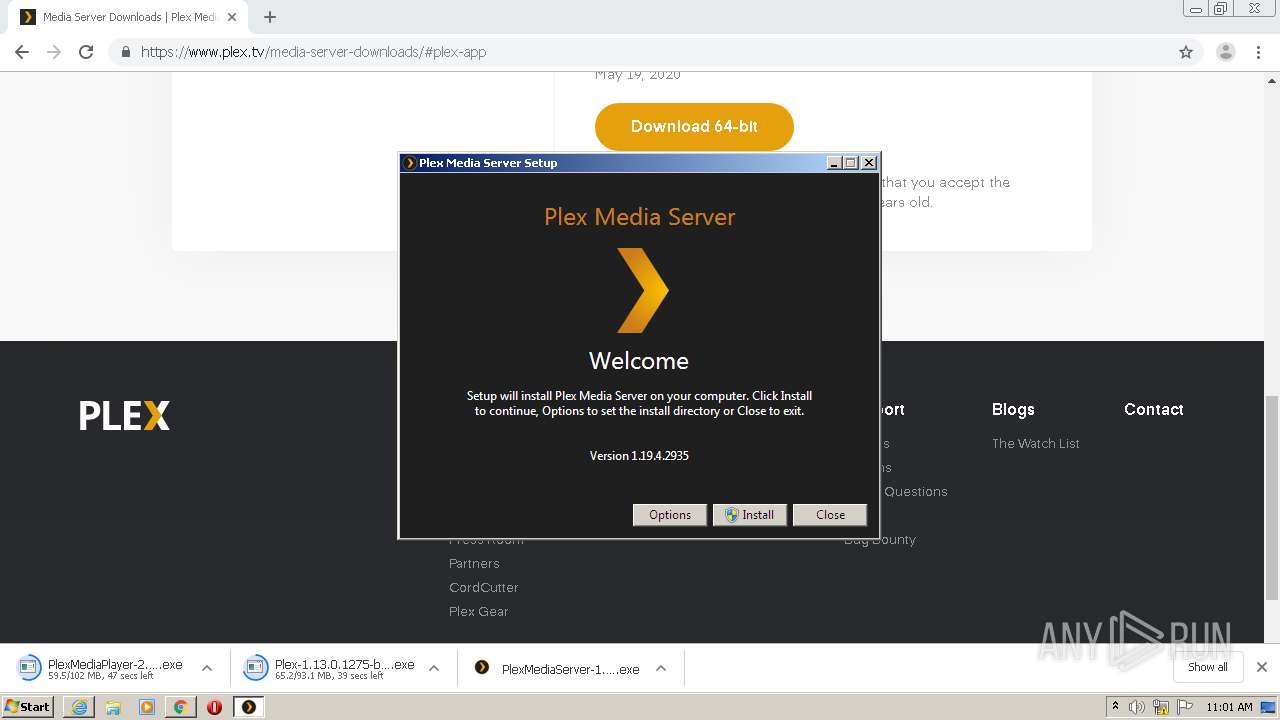
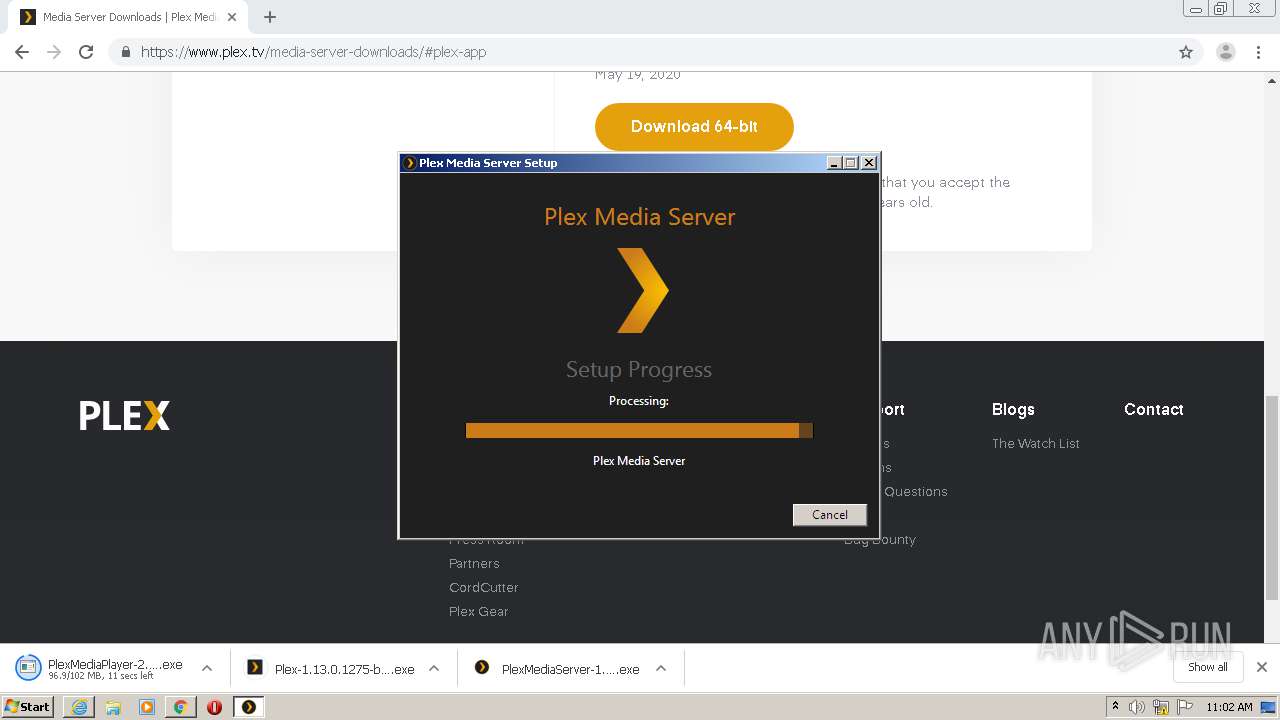
| Verdict: | Malicious activity |
| Analysis date: | July 06, 2020, 09:58:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BFF529E8E3533C808AE48DA063F5C55F |
| SHA1: | B0960820C7ABA62E176AF5E9763F4F7CAC2FE833 |
| SHA256: | 910BAB6826E152469FD77EF785FE0536D748F28532504152F0802966B36791E2 |
| SSDEEP: | 3:N8DSLMNpF6Kn:2OLevhn |
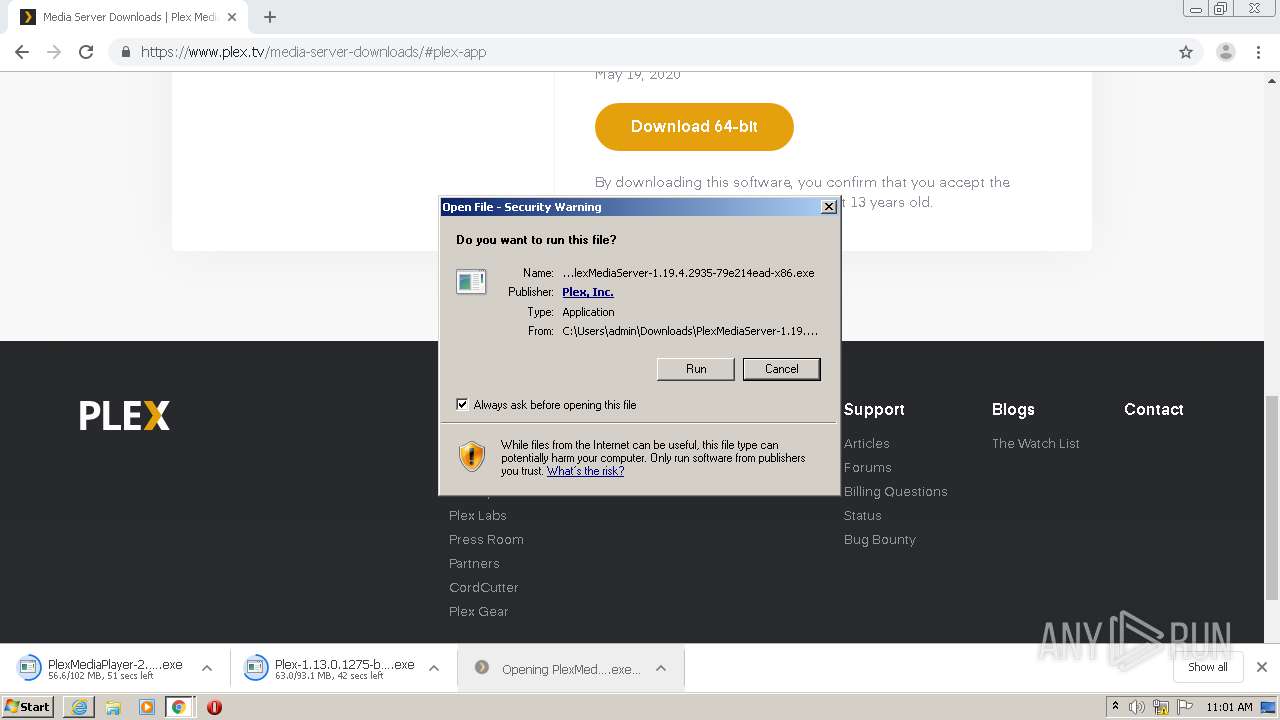
MALICIOUS
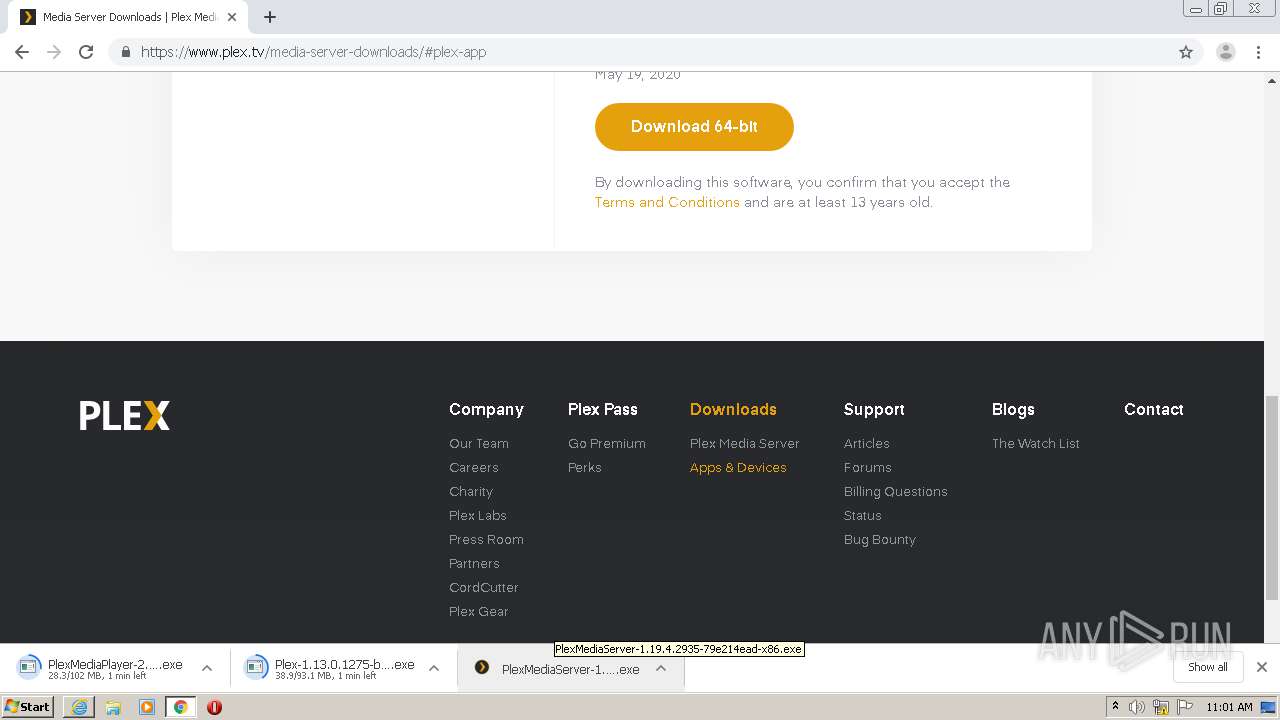
Application was dropped or rewritten from another process
- PlexMediaServer-1.19.4.2935-79e214ead-x86.exe (PID: 2076)
- PlexMediaServer-1.19.4.2935-79e214ead-x86.exe (PID: 4084)
- pms.exe (PID: 3828)
- vcredist_x86.exe (PID: 1520)
- VC_redist.x86.exe (PID: 2228)
- vcredist_x86.exe (PID: 648)
- VC_redist.x86.exe (PID: 2544)
- VC_redist.x86.exe (PID: 2732)
- VC_redist.x86.exe (PID: 1968)
- Plex Update Service.exe (PID: 3012)
- Plex Media Server.exe (PID: 2948)
- PlexScriptHost.exe (PID: 1076)
- CrashUploader.exe (PID: 2904)
- Plex Tuner Service.exe (PID: 3144)
- PlexScriptHost.exe (PID: 3336)
- PlexScriptHost.exe (PID: 2432)
- PlexScriptHost.exe (PID: 3272)
- PlexScriptHost.exe (PID: 2468)
- PlexScriptHost.exe (PID: 3776)
- PlexScriptHost.exe (PID: 3388)
- PlexScriptHost.exe (PID: 3772)
- PlexScriptHost.exe (PID: 3332)
- PlexScriptHost.exe (PID: 2740)
- PlexScriptHost.exe (PID: 3980)
- PlexScriptHost.exe (PID: 2428)
- PlexScriptHost.exe (PID: 5248)
- PlexScriptHost.exe (PID: 3988)
- PlexScriptHost.exe (PID: 5592)
- PlexScriptHost.exe (PID: 5596)
- PlexScriptHost.exe (PID: 5832)
Loads dropped or rewritten executable
- PlexMediaServer-1.19.4.2935-79e214ead-x86.exe (PID: 4084)
- vcredist_x86.exe (PID: 648)
- VC_redist.x86.exe (PID: 2732)
- Plex Update Service.exe (PID: 3012)
- Plex Media Server.exe (PID: 2948)
- PlexScriptHost.exe (PID: 1076)
- Plex Tuner Service.exe (PID: 3144)
- CrashUploader.exe (PID: 2904)
- PlexScriptHost.exe (PID: 3336)
- PlexScriptHost.exe (PID: 3272)
- PlexScriptHost.exe (PID: 2432)
- PlexScriptHost.exe (PID: 3388)
- PlexScriptHost.exe (PID: 3776)
- PlexScriptHost.exe (PID: 2468)
- PlexScriptHost.exe (PID: 3332)
- PlexScriptHost.exe (PID: 3772)
- PlexScriptHost.exe (PID: 2740)
- PlexScriptHost.exe (PID: 3988)
- PlexScriptHost.exe (PID: 3980)
- PlexScriptHost.exe (PID: 2428)
- PlexScriptHost.exe (PID: 5248)
- PlexScriptHost.exe (PID: 5596)
- PlexScriptHost.exe (PID: 5832)
- PlexScriptHost.exe (PID: 5592)
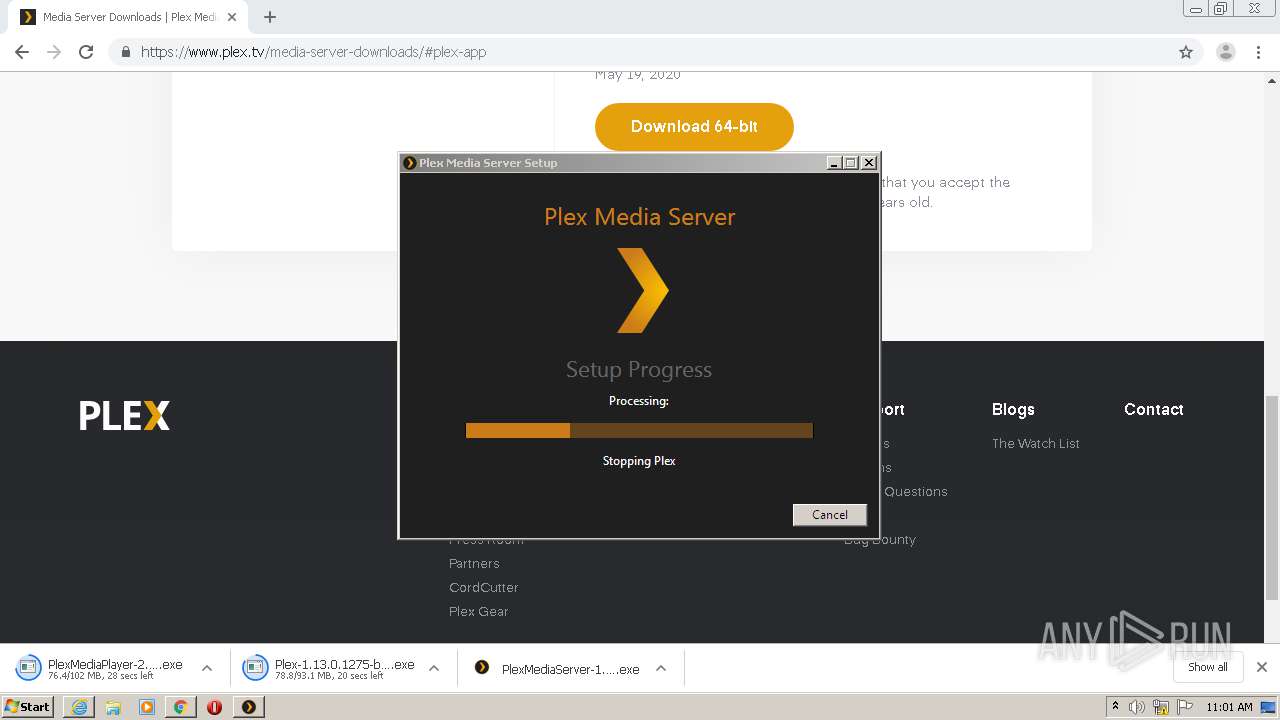
Changes the autorun value in the registry
- pms.exe (PID: 3828)
- VC_redist.x86.exe (PID: 2228)
Detects Cygwin installation
- msiexec.exe (PID: 3728)
Changes settings of System certificates
- msiexec.exe (PID: 3728)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3560)
Executable content was dropped or overwritten
- chrome.exe (PID: 3560)
- PlexMediaServer-1.19.4.2935-79e214ead-x86.exe (PID: 2076)
- PlexMediaServer-1.19.4.2935-79e214ead-x86.exe (PID: 4084)
- pms.exe (PID: 3828)
- vcredist_x86.exe (PID: 1520)
- vcredist_x86.exe (PID: 648)
- VC_redist.x86.exe (PID: 2228)
- msiexec.exe (PID: 3728)
- VC_redist.x86.exe (PID: 1968)
- VC_redist.x86.exe (PID: 2732)
Starts itself from another location
- PlexMediaServer-1.19.4.2935-79e214ead-x86.exe (PID: 4084)
- vcredist_x86.exe (PID: 648)
Executed as Windows Service
- vssvc.exe (PID: 3596)
- Plex Update Service.exe (PID: 3012)
Searches for installed software
- pms.exe (PID: 3828)
- VC_redist.x86.exe (PID: 2228)
Creates files in the program directory
- pms.exe (PID: 3828)
- VC_redist.x86.exe (PID: 2228)
Creates a software uninstall entry
- pms.exe (PID: 3828)
- VC_redist.x86.exe (PID: 2228)
- VC_redist.x86.exe (PID: 1968)
Creates files in the Windows directory
- vcredist_x86.exe (PID: 1520)
- vcredist_x86.exe (PID: 648)
- msiexec.exe (PID: 3728)
- VC_redist.x86.exe (PID: 2732)
- Plex Update Service.exe (PID: 3012)
Application launched itself
- VC_redist.x86.exe (PID: 2732)
Removes files from Windows directory
- VC_redist.x86.exe (PID: 2732)
- vcredist_x86.exe (PID: 648)
- vcredist_x86.exe (PID: 1520)
Loads Python modules
- Plex Media Server.exe (PID: 2948)
- PlexScriptHost.exe (PID: 1076)
- PlexScriptHost.exe (PID: 2432)
- PlexScriptHost.exe (PID: 3336)
- PlexScriptHost.exe (PID: 3272)
- PlexScriptHost.exe (PID: 3388)
- PlexScriptHost.exe (PID: 3776)
- PlexScriptHost.exe (PID: 2468)
- PlexScriptHost.exe (PID: 3332)
- PlexScriptHost.exe (PID: 2740)
- PlexScriptHost.exe (PID: 3772)
- PlexScriptHost.exe (PID: 3980)
- PlexScriptHost.exe (PID: 2428)
- PlexScriptHost.exe (PID: 3988)
- PlexScriptHost.exe (PID: 5248)
- PlexScriptHost.exe (PID: 5596)
- PlexScriptHost.exe (PID: 5832)
- PlexScriptHost.exe (PID: 5592)
Changes the autorun value in the registry
- msiexec.exe (PID: 3728)
Adds / modifies Windows certificates
- msiexec.exe (PID: 3728)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3208)
- iexplore.exe (PID: 2808)
- chrome.exe (PID: 3560)
- iexplore.exe (PID: 3296)
Creates files in the user directory
- iexplore.exe (PID: 2808)
- iexplore.exe (PID: 3208)
Reads internet explorer settings
- iexplore.exe (PID: 2808)
- iexplore.exe (PID: 3296)
Manual execution by user
- chrome.exe (PID: 3560)
Application launched itself
- chrome.exe (PID: 3560)
- iexplore.exe (PID: 3208)
- msiexec.exe (PID: 3728)
Reads the hosts file
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3436)
Changes internet zones settings
- iexplore.exe (PID: 3208)
Reads settings of System Certificates
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3436)
- msiexec.exe (PID: 3728)
- iexplore.exe (PID: 3208)
- PlexScriptHost.exe (PID: 1076)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3596)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 912)
- MsiExec.exe (PID: 3964)
- MsiExec.exe (PID: 3416)
- MsiExec.exe (PID: 3940)
Creates a software uninstall entry
- msiexec.exe (PID: 3728)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3728)
Creates files in the program directory
- msiexec.exe (PID: 3728)
Changes settings of System certificates
- iexplore.exe (PID: 3208)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
133
Monitored processes
71
Malicious processes
31
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,9706570433971270661,11194179298528618808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7722788047006393106 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | "C:\Windows\Temp\{6DB5C2B7-11AA-4DE3-A5E0-1274B5A5E7B6}\.cr\vcredist_x86.exe" -burn.clean.room="C:\ProgramData\Package Cache\AFA5BADCE64EE67290ADD24E0DC3D8210954AC6C\vcredist_x86.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 /install /quiet /norestart | C:\Windows\Temp\{6DB5C2B7-11AA-4DE3-A5E0-1274B5A5E7B6}\.cr\vcredist_x86.exe | vcredist_x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.24.28127 Exit code: 0 Version: 14.24.28127.4 Modules
| |||||||||||||||
| 696 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,9706570433971270661,11194179298528618808,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13358651959337712365 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3704 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,9706570433971270661,11194179298528618808,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14126396043460698249 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4328 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,9706570433971270661,11194179298528618808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8508192417371248917 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | C:\Windows\system32\MsiExec.exe -Embedding D9F10529036E5F632224744EA432C3A1 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,9706570433971270661,11194179298528618808,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3504249951040272089 --mojo-platform-channel-handle=3592 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Plex\Plex Media Server\PlexScriptHost.exe" "C:\Program Files\Plex\Plex Media Server\Resources\Plug-ins-79e214ead\Framework.bundle\Contents\Resources\Versions\2\Python\bootstrap.py" "C:\Program Files\Plex\Plex Media Server\Resources\Plug-ins-79e214ead\System.bundle" | C:\Program Files\Plex\Plex Media Server\PlexScriptHost.exe | Plex Media Server.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 2.7.17 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ee0a9d0,0x6ee0a9e0,0x6ee0a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\ProgramData\Package Cache\AFA5BADCE64EE67290ADD24E0DC3D8210954AC6C\vcredist_x86.exe" /install /quiet /norestart | C:\ProgramData\Package Cache\AFA5BADCE64EE67290ADD24E0DC3D8210954AC6C\vcredist_x86.exe | pms.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.24.28127 Exit code: 0 Version: 14.24.28127.4 Modules
| |||||||||||||||
Total events
13 583
Read events
3 564
Write events
7 988
Delete events
2 031
Modification events
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 544802818 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30823292 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3208) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
156
Suspicious files
161
Text files
2 588
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2808 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabD7F3.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarD7F4.tmp | — | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U5LXJ8BI.txt | text | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\media-server-downloads[1].htm | html | |
MD5:— | SHA256:— | |||
| 3208 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\app.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\plex.downloads.min[1].js | text | |
MD5:— | SHA256:— | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F02F5E6-DE8.pma | — | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\plex-pms-icon[1].jpg | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
108
DNS requests
58
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2808 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2808 | iexplore.exe | GET | 200 | 13.35.253.185:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2808 | iexplore.exe | GET | 200 | 143.204.208.173:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAZalrG1oyCUv4%2F%2BEUj7l%2Fw%3D | US | der | 471 b | whitelisted |
2808 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2808 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEAar2mu0dHehCAAAAABH74o%3D | US | der | 471 b | whitelisted |
2808 | iexplore.exe | GET | 200 | 143.204.208.127:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3436 | chrome.exe | GET | 200 | 173.194.150.185:80 | http://r3---sn-5goeen7d.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvY2Y1QUFXUjZlVjI5UldyLVpDTFJFcEx6QQ/7719.805.0.2_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=Nf&mip=196.244.192.14&mm=28&mn=sn-5goeen7d&ms=nvh&mt=1594029494&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 823 Kb | whitelisted |
3208 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2808 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.com/root.crl | US | der | 1.03 Kb | whitelisted |
2808 | iexplore.exe | GET | 200 | 13.35.253.198:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2808 | iexplore.exe | 104.18.157.41:443 | www.plex.tv | Cloudflare Inc | US | shared |
2808 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2808 | iexplore.exe | 151.101.1.132:443 | cdn.transifex.com | Fastly | US | suspicious |
2808 | iexplore.exe | 216.58.212.136:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2808 | iexplore.exe | 172.217.22.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2808 | iexplore.exe | 104.18.20.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3436 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3436 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3208 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3436 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.plex.tv |
| unknown |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.transifex.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |