| File name: | Instal.exe |
| Full analysis: | https://app.any.run/tasks/45d0a55c-84d3-4094-afd7-513db3bf249a |
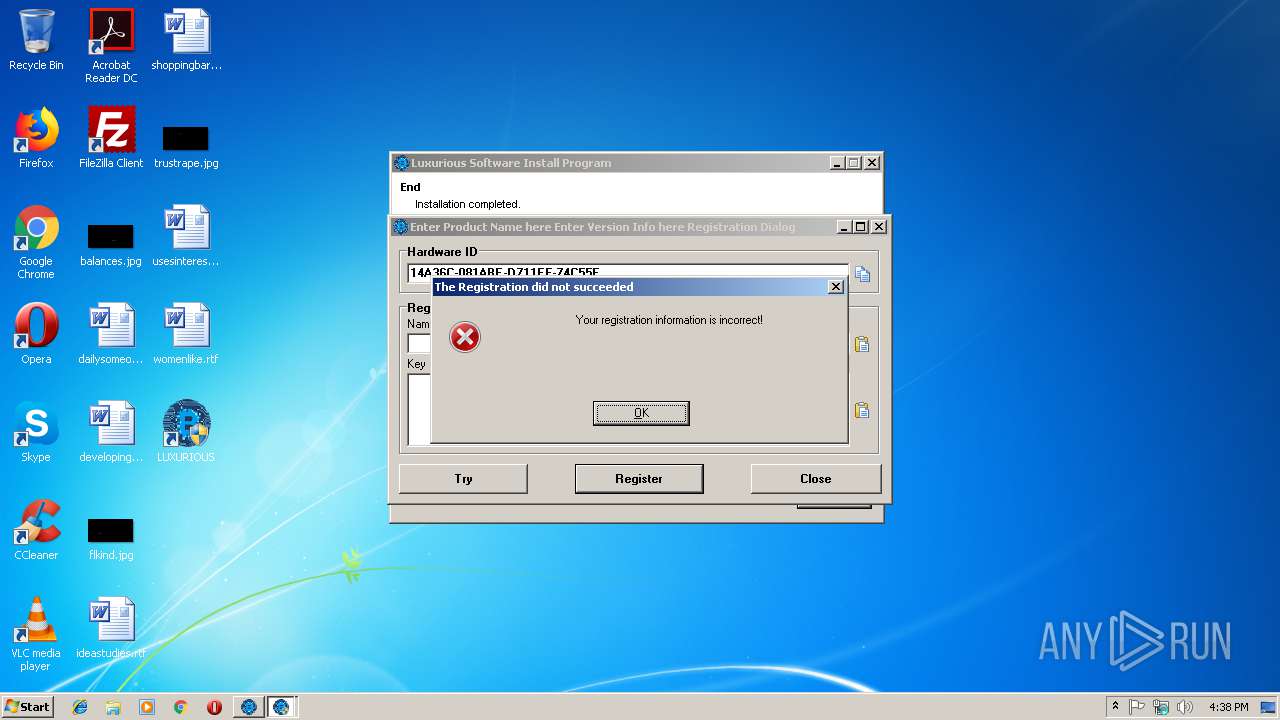
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 16:37:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8460BCDFD7531772B52C13D575CF0411 |
| SHA1: | 317CD5846D8236B4506CB7E7CBA2CE91325366E0 |
| SHA256: | 91012F115D486515AEC66F2304CEAF55899A4086347EFBC04D32755FB0D32082 |
| SSDEEP: | 98304:oRPLDcgPvAXijJdYMQ3UDC+5s9LHtAfOo0y0s:gPfAi3YMqqVsAR0s |
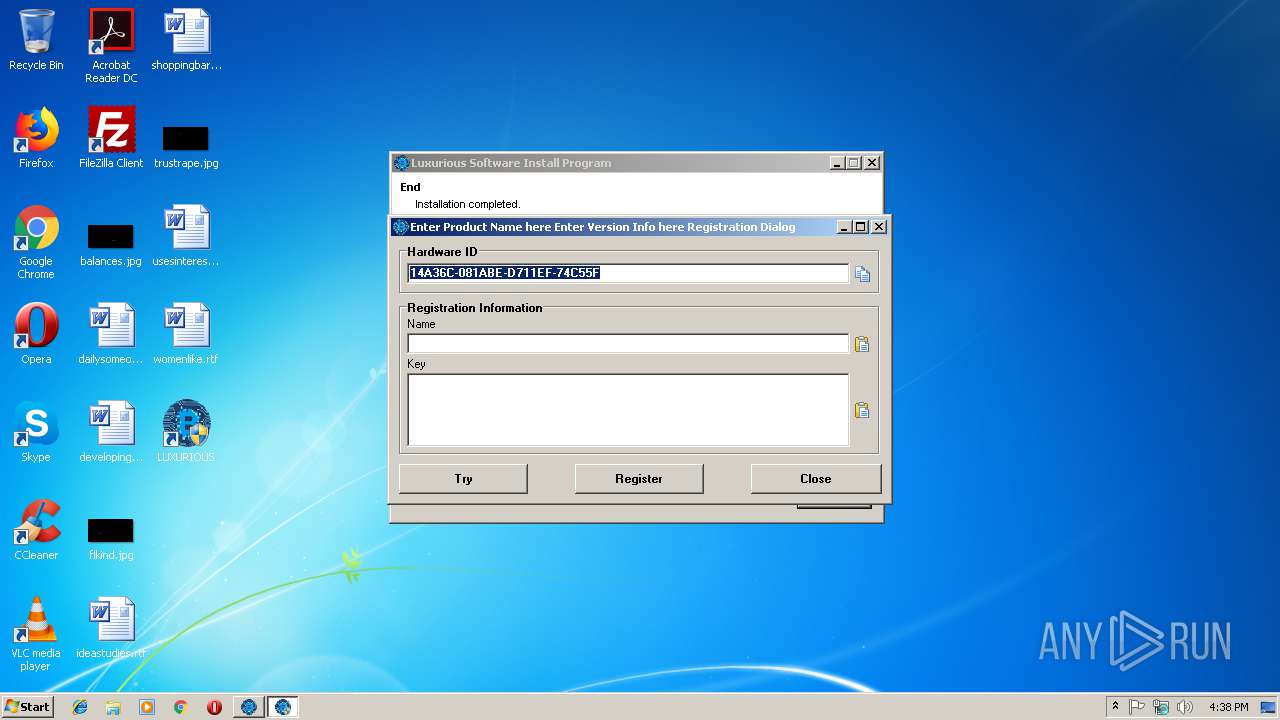
MALICIOUS
Application was dropped or rewritten from another process
- Luxurious Demo.exe (PID: 2140)
- Luxurious Demo.exe (PID: 2140)
SUSPICIOUS
Executable content was dropped or overwritten
- Instal.exe (PID: 1816)
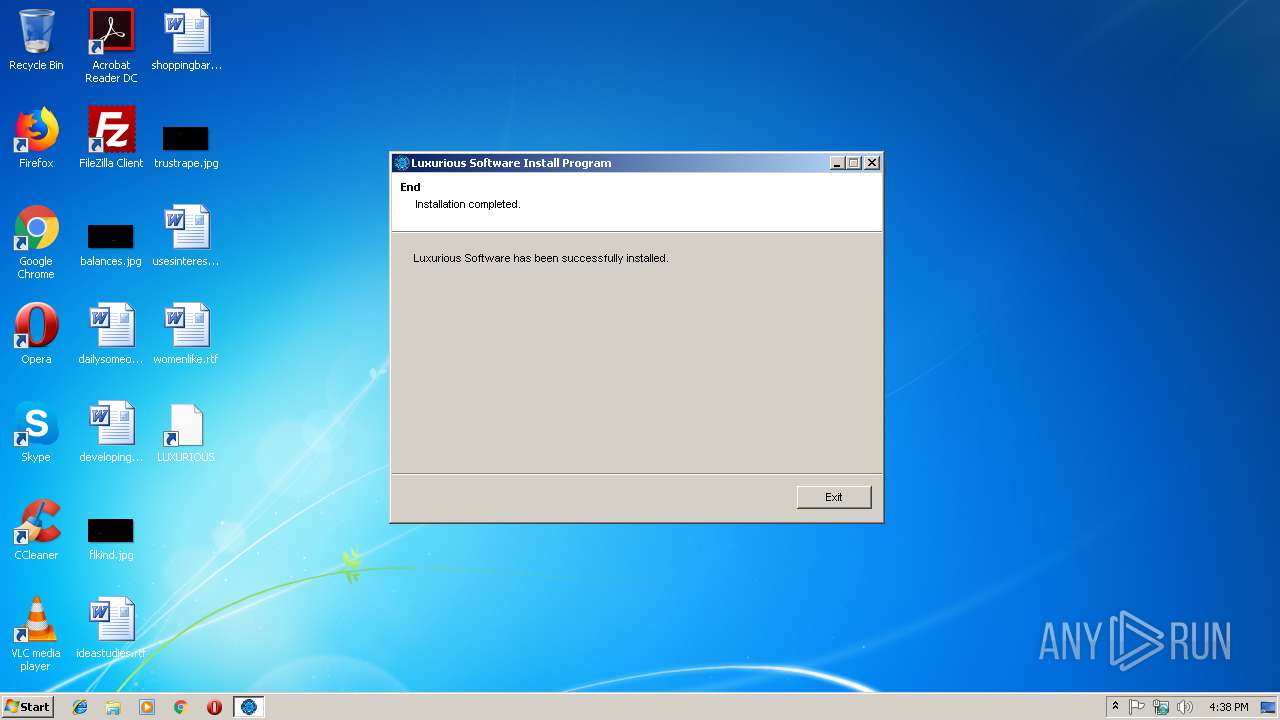
Creates files in the program directory
- Instal.exe (PID: 1816)
Creates a software uninstall entry
- Instal.exe (PID: 1816)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (33) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (23.9) |
| .exe | | | Win64 Executable (generic) (21.2) |
| .scr | | | Windows screen saver (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:10:02 17:38:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 139264 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c502 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.45 |
| ProductVersionNumber: | 2.0.0.45 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2,0,0,45 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
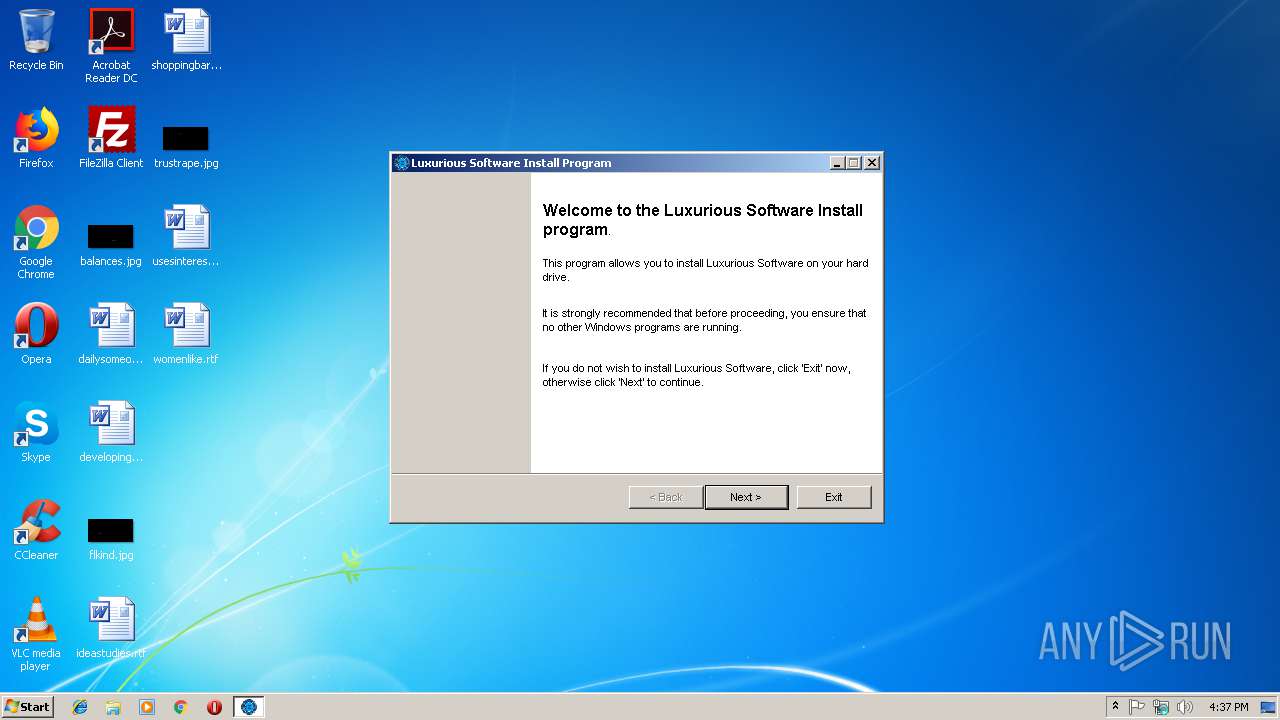
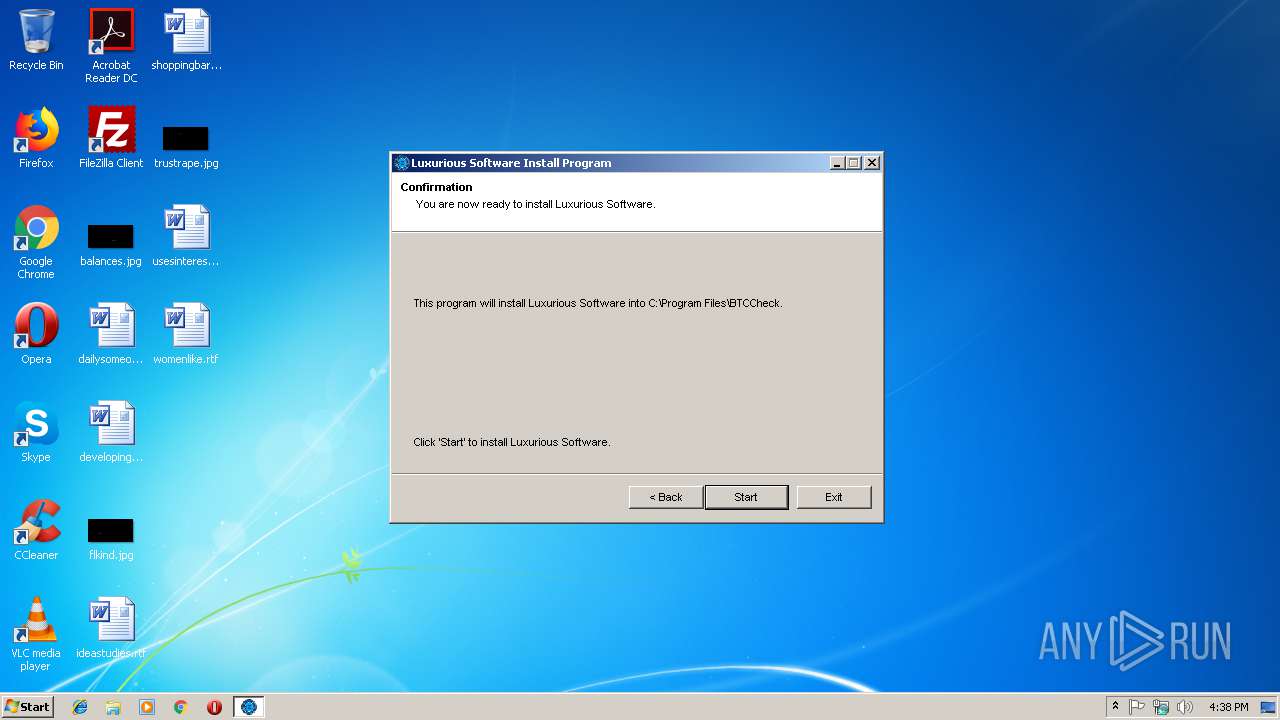
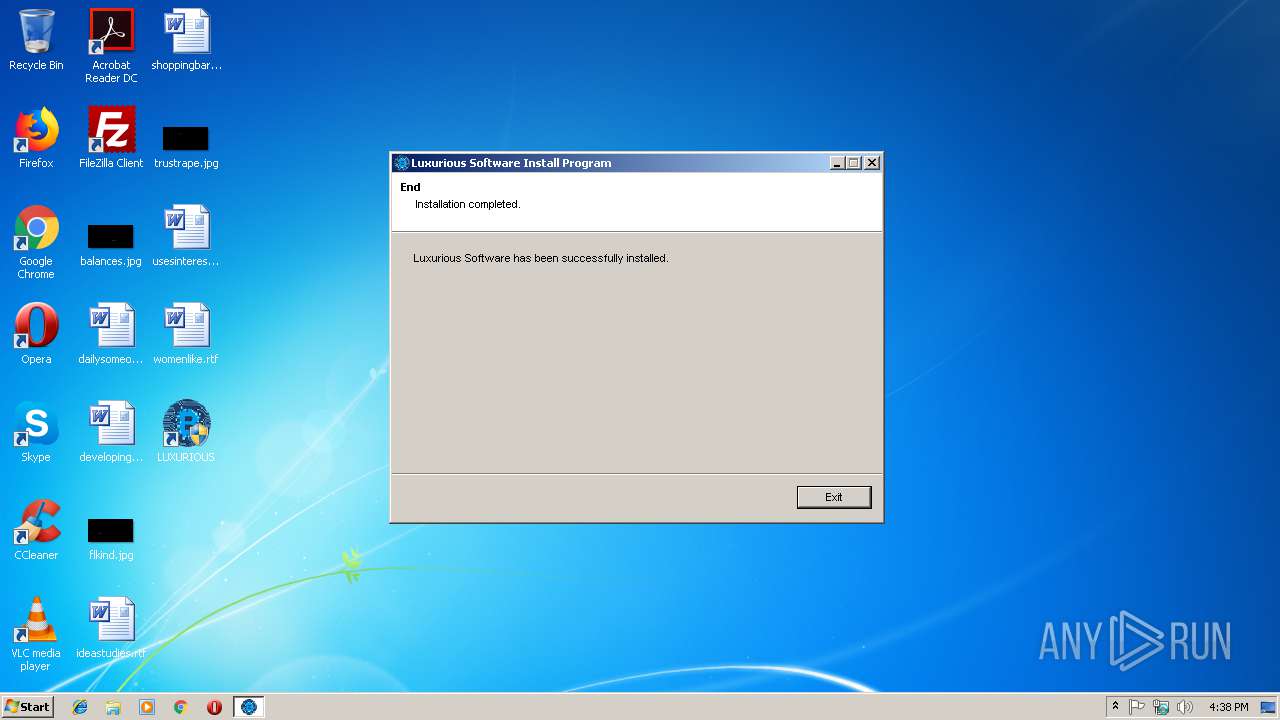
| ProductName: | Luxurious Software Install Program |
| ProductVersion: | 2,0,0,45 |
| SpecialBuild: | - |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
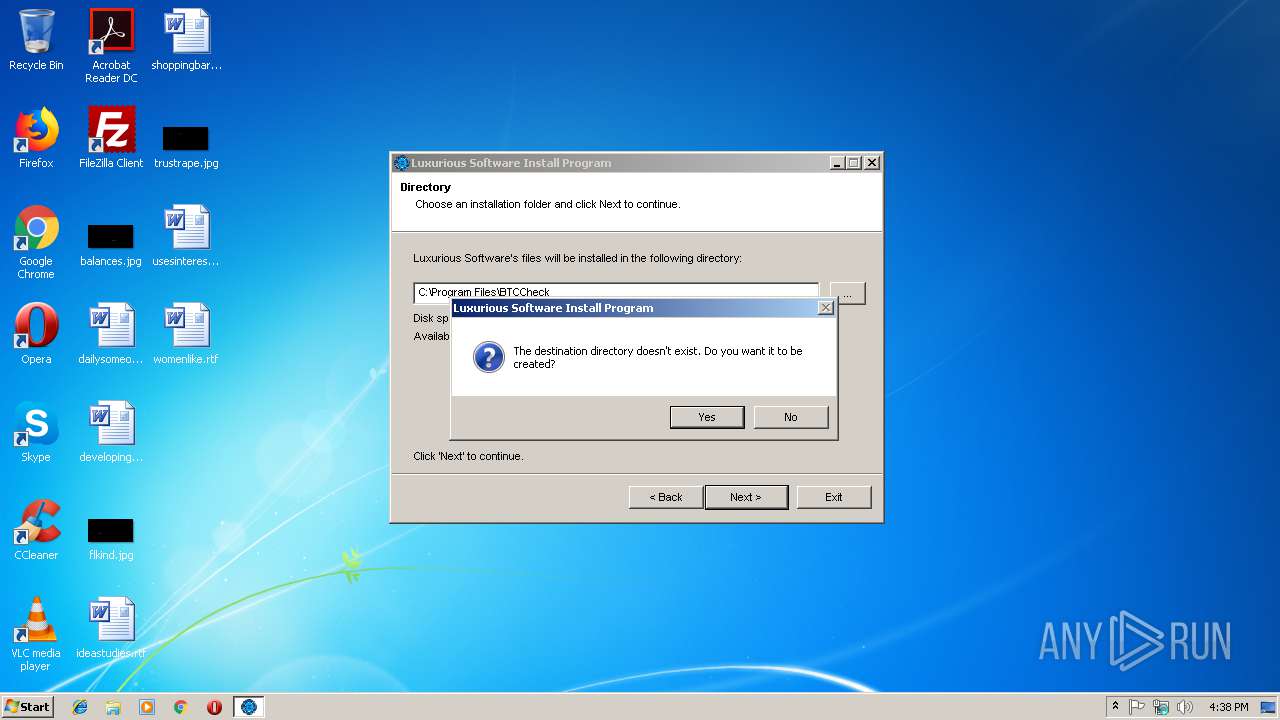
| 1816 | "C:\Users\admin\AppData\Local\Temp\Instal.exe" | C:\Users\admin\AppData\Local\Temp\Instal.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2,0,0,45 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\BTCCheck\Luxurious Demo.exe" | C:\Program Files\BTCCheck\Luxurious Demo.exe | — | explorer.exe | |||||||||||
User: admin Company: Luxurious Integrity Level: MEDIUM Description: Luxurious Demo Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\BTCCheck\Luxurious Demo.exe" | C:\Program Files\BTCCheck\Luxurious Demo.exe | explorer.exe | ||||||||||||
User: admin Company: Luxurious Integrity Level: HIGH Description: Luxurious Demo Exit code: 27355795 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3724 | "C:\Users\admin\AppData\Local\Temp\Instal.exe" | C:\Users\admin\AppData\Local\Temp\Instal.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2,0,0,45 Modules
| |||||||||||||||
Total events
168
Read events
166
Write events
2
Delete events
0
Modification events
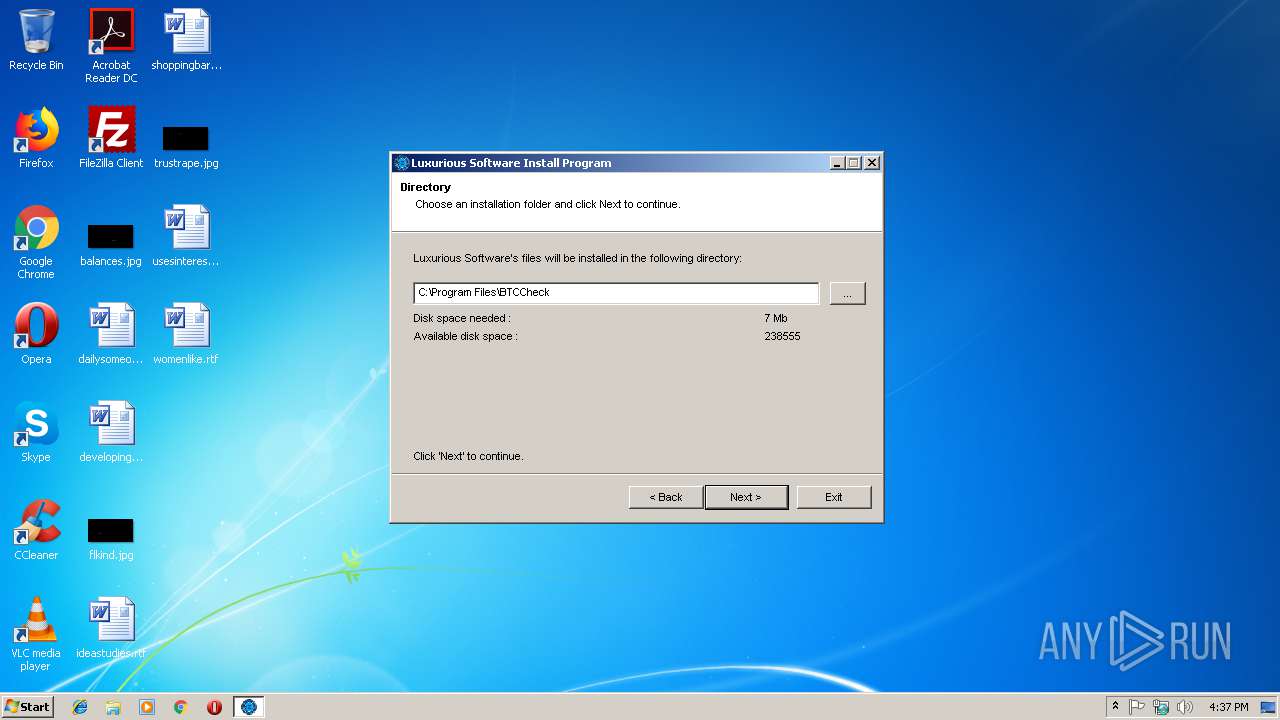
| (PID) Process: | (1816) Instal.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luxurious Software |
| Operation: | write | Name: | DisplayName |
Value: Luxurious Software | |||
| (PID) Process: | (1816) Instal.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luxurious Software |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\BTCCheck\Uninstal.exe | |||
Executable files
7
Suspicious files
0
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1816 | Instal.exe | C:\Program Files\BTCCheck\Uninstal.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\BouncyCastle.Crypto.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\Bunifu_UI_v1.5.3.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\Luxurious Demo.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\Luxurious Demo.exe.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\MaterialSkin.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\s.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\xNet.$A | — | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Users\Public\Desktop\LUXURIOUS.lnk | lnk | |
MD5:— | SHA256:— | |||
| 1816 | Instal.exe | C:\Program Files\BTCCheck\xNet.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report