| File name: | BackgroundHost64.exe |
| Full analysis: | https://app.any.run/tasks/1962a9b4-7137-4065-a37a-2b837de1d70f |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2020, 19:58:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 66184C0FB9A2CBB25E1EB232CF4B1544 |
| SHA1: | FB910146317206EDB9E895B2A880D75C85B5C5B2 |
| SHA256: | 90EC655F776ED099822D44410D5BDBD3913FBE4968189FC7361ED636E91F4B46 |
| SSDEEP: | 49152:NNpN9f9Kg4l+SwGzk2gZO4ra1vJAy7nXvTMHBHW//Y9kZf/tApaZ:NLjlKX+SwKkXaVCy7n/gM3WkZf1gy |
MALICIOUS
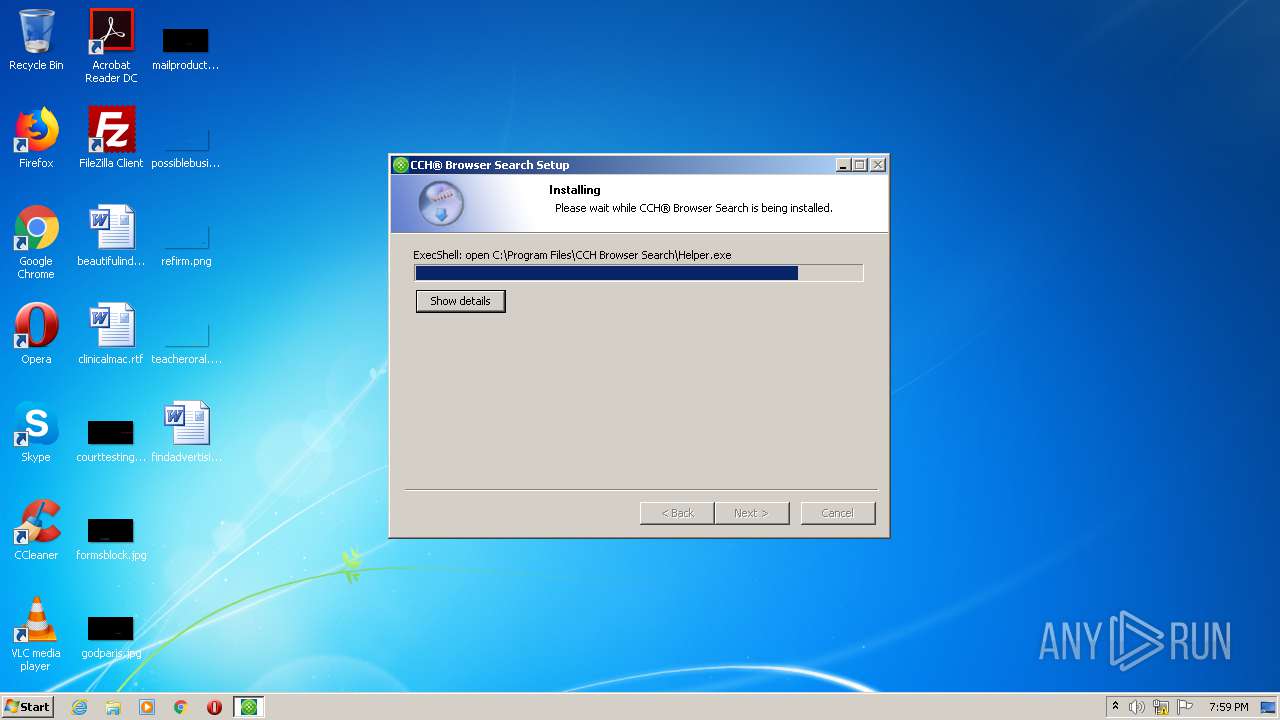
Drops executable file immediately after starts
- BackgroundHost64.exe (PID: 2244)
Loads dropped or rewritten executable
- BackgroundHost64.exe (PID: 2244)
- BackgroundHost64.exe (PID: 2564)
- regsvr32.exe (PID: 1856)
- regsvr32.exe (PID: 2080)
- regsvr32.exe (PID: 1456)
- iexplore.exe (PID: 2936)
- regsvr32.exe (PID: 2544)
Application was dropped or rewritten from another process
- BackgroundHost.exe (PID: 2204)
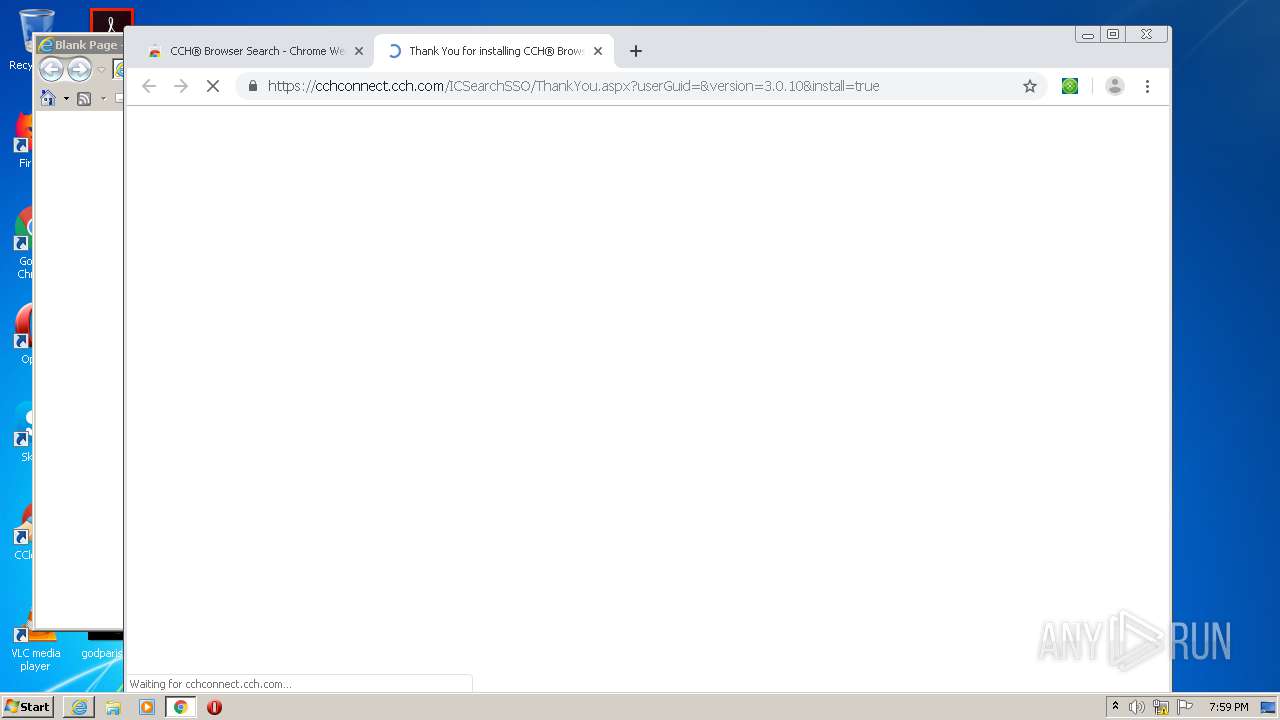
- icschrome.exe (PID: 1024)
- icschrome.exe (PID: 3608)
- icschrome.exe (PID: 3160)
- icschrome.exe (PID: 896)
Registers / Runs the DLL via REGSVR32.EXE
- BackgroundHost64.exe (PID: 2244)
Actions looks like stealing of personal data
- BackgroundHost64.exe (PID: 2564)
SUSPICIOUS
Executable content was dropped or overwritten
- BackgroundHost64.exe (PID: 2244)
- BackgroundHost64.exe (PID: 2564)
Application launched itself
- BackgroundHost64.exe (PID: 2564)
Drops a file with too old compile date
- BackgroundHost64.exe (PID: 2244)
- BackgroundHost64.exe (PID: 2564)
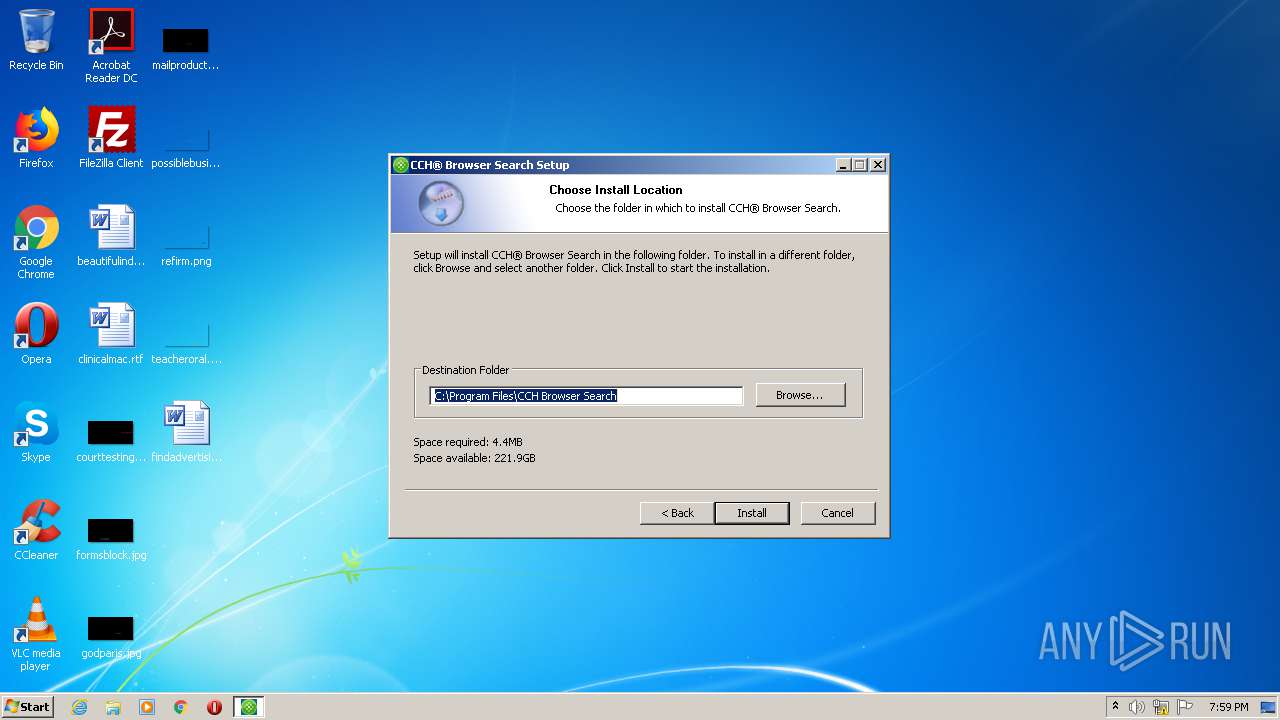
Creates a directory in Program Files
- BackgroundHost64.exe (PID: 2244)
Drops a file that was compiled in debug mode
- BackgroundHost64.exe (PID: 2244)
- BackgroundHost64.exe (PID: 2564)
Uses TASKKILL.EXE to kill Browsers
- BackgroundHost64.exe (PID: 2564)
- BackgroundHost64.exe (PID: 2244)
Creates files in the program directory
- BackgroundHost64.exe (PID: 2244)
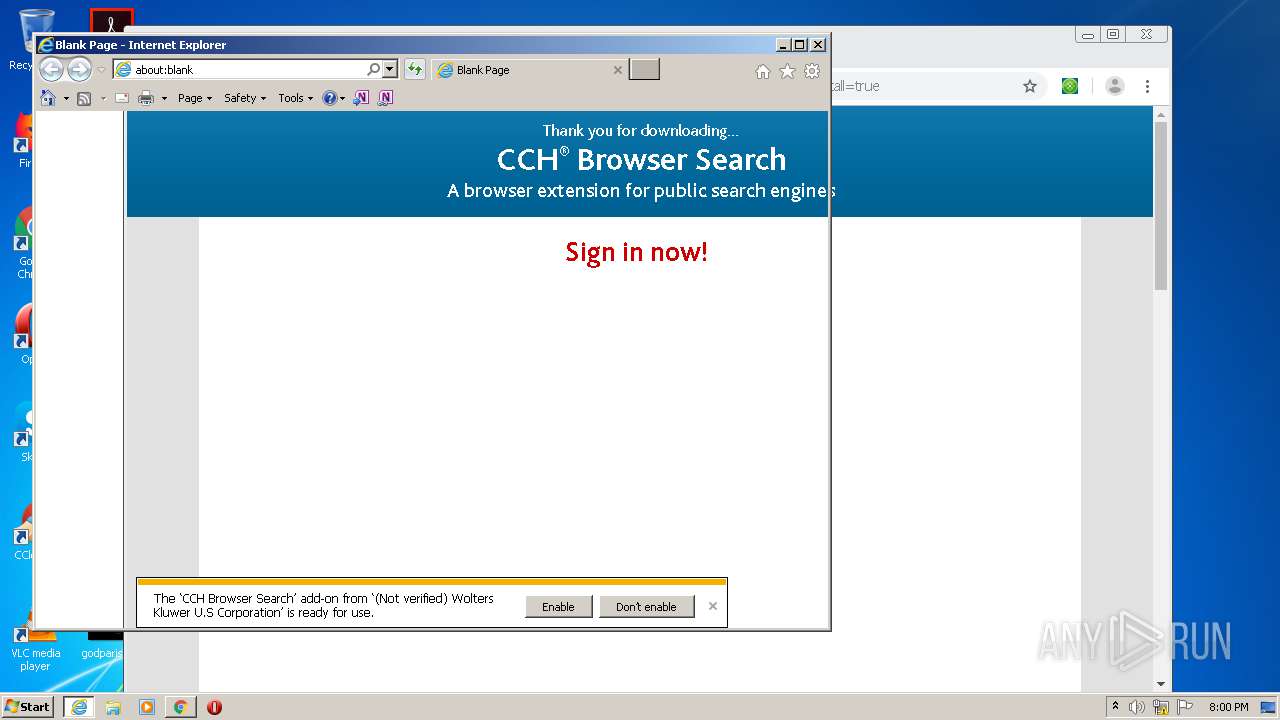
Changes IE settings (feature browser emulation)
- BackgroundHost.exe (PID: 2204)
Creates COM task schedule object
- regsvr32.exe (PID: 1456)
- regsvr32.exe (PID: 2080)
- regsvr32.exe (PID: 2544)
Creates files in the user directory
- BackgroundHost64.exe (PID: 2564)
Creates a software uninstall entry
- BackgroundHost64.exe (PID: 2244)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3712)
Starts CMD.EXE for commands execution
- chrome.exe (PID: 3712)
INFO
Reads the hosts file
- chrome.exe (PID: 3712)
- chrome.exe (PID: 1448)
Changes settings of System certificates
- chrome.exe (PID: 1448)
- iexplore.exe (PID: 2936)
Reads settings of System Certificates
- chrome.exe (PID: 1448)
- iexplore.exe (PID: 2936)
Manual execution by user
- iexplore.exe (PID: 2936)
Application launched itself
- chrome.exe (PID: 3712)
- iexplore.exe (PID: 2936)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3712)
Adds / modifies Windows certificates
- chrome.exe (PID: 1448)
- iexplore.exe (PID: 2936)
Reads internet explorer settings
- iexplore.exe (PID: 2872)
Changes internet zones settings
- iexplore.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23040 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30cb |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.35 |
| ProductVersionNumber: | 2.0.0.35 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
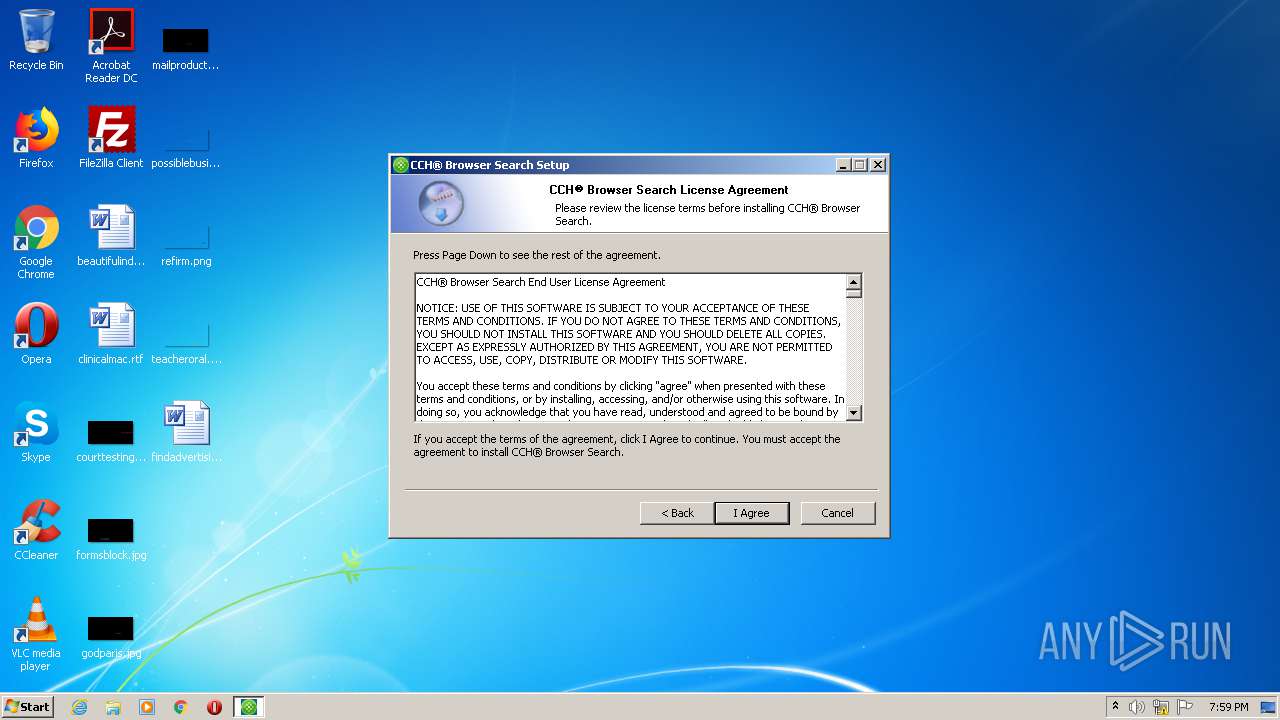
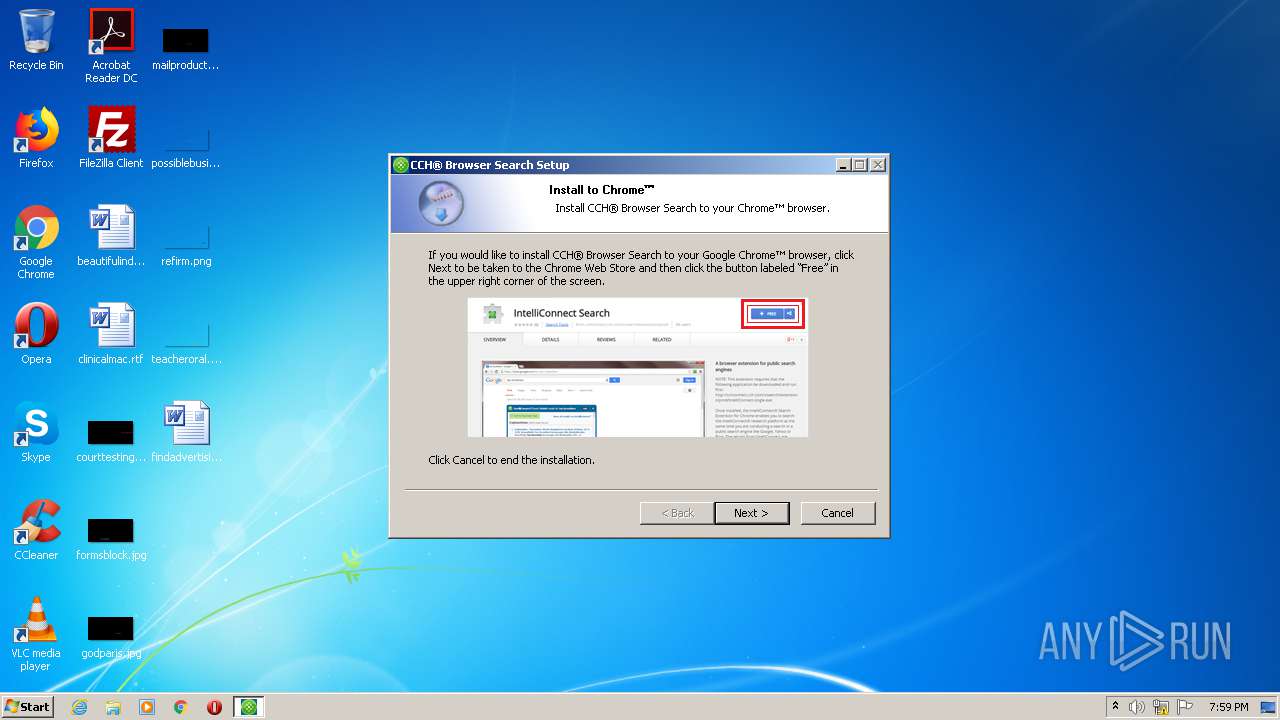
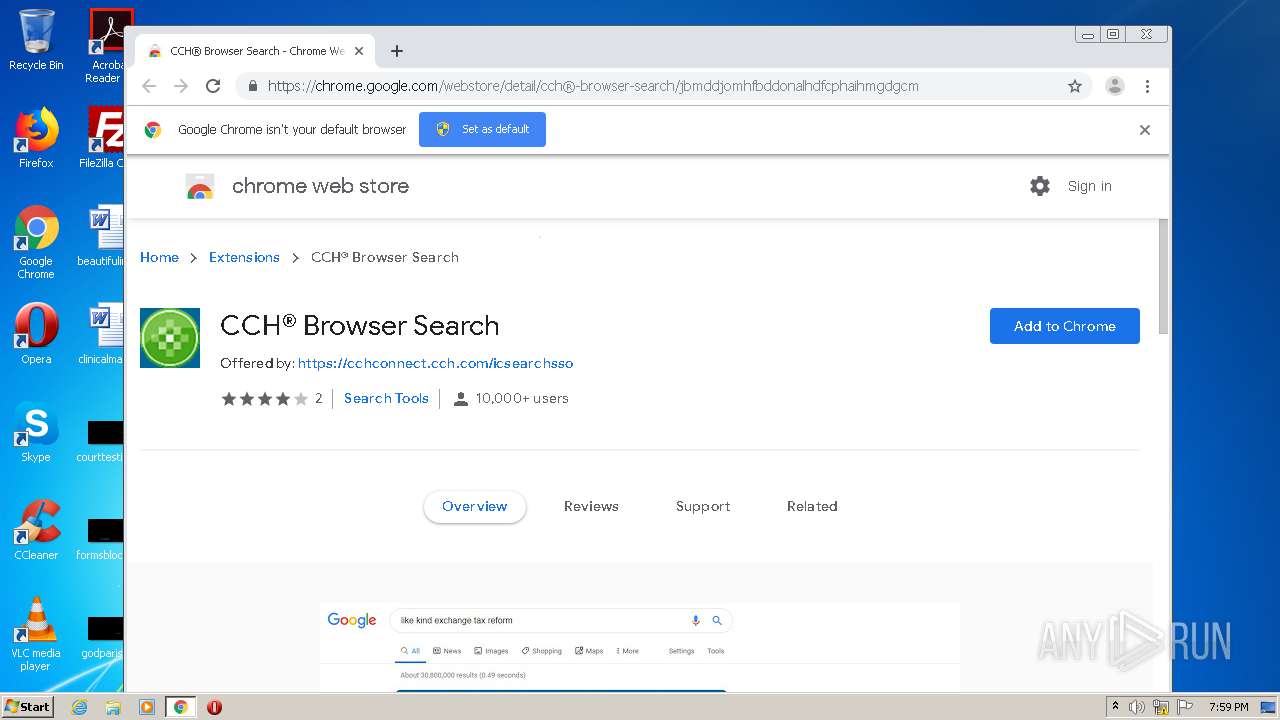
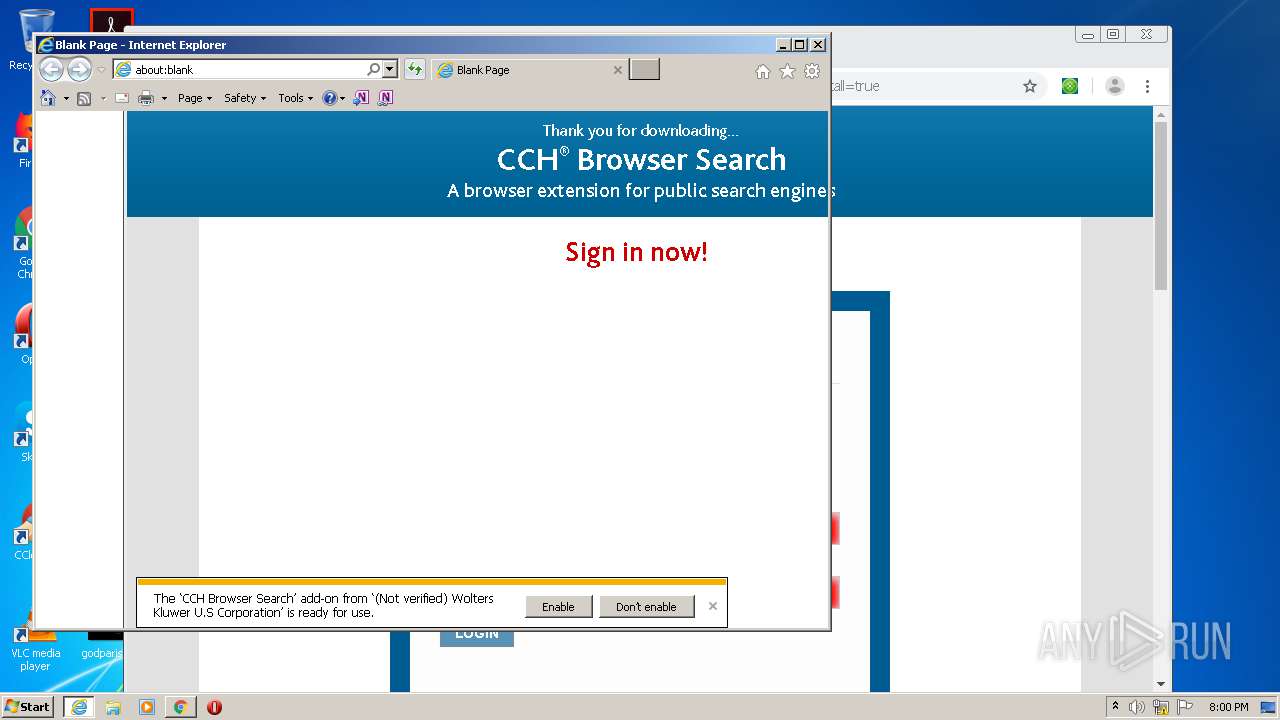
| Comments: | CCH® Browser Search |
| CompanyName: | Wolters Kluwer |
| FileDescription: | CCH® Browser Search |
| FileVersion: | 2.0.0.35 |
| InternalName: | CCH® Browser Search |
| LegalCopyright: | Wolters Kluwer |
| LegalTrademarks: | CCH® Browser Search is a Trademark of Wolters Kluwer |
| OriginalFileName: | CCHBrowserSearch.single.exe |
| ProductName: | CCH® Browser Search |
| ProductVersion: | 2.0.0.35 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:41 |
| Detected languages: |
|
| Comments: | CCH® Browser Search |
| CompanyName: | Wolters Kluwer |
| FileDescription: | CCH® Browser Search |
| FileVersion: | 2.0.0.35 |
| InternalName: | CCH® Browser Search |
| LegalCopyright: | Wolters Kluwer |
| LegalTrademarks: | CCH® Browser Search is a Trademark of Wolters Kluwer |
| OriginalFilename: | CCHBrowserSearch.single.exe |
| ProductName: | CCH® Browser Search |
| ProductVersion: | 2.0.0.35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000058D2 | 0x00005A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4331 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.17976 |
.data | 0x00009000 | 0x0001AF78 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.6178 |
.ndata | 0x00024000 | 0x0001A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003E000 | 0x000195A8 | 0x00019600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.05923 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22437 | 947 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.11297 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 6.18748 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 6.10259 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 5.72204 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.60989 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.67385 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
111
Monitored processes
60
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | C:\Windows\system32\cmd.exe /d /c "C:\Program Files\CCH Browser Search\icschrome.exe" chrome-extension://jbmddjomhfbddonalhdfcphaihmgdgcm/ --parent-window=0 < \\.\pipe\chrome.nativeMessaging.in.88ee5a5c3a460dab > \\.\pipe\chrome.nativeMessaging.out.88ee5a5c3a460dab | C:\Windows\system32\cmd.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13051515822500552863,17741900905429802618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13535134818392795804 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3712 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 656 | C:\Windows\system32\regsvr32 /s "C:\Program Files\CCH Browser Search\ButtonSite64.dll" | C:\Windows\system32\regsvr32.exe | — | BackgroundHost64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 3 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13051515822500552863,17741900905429802618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10778918818985037471 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,13051515822500552863,17741900905429802618,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10647846438777828407 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13051515822500552863,17741900905429802618,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2533719933051747731 --mojo-platform-channel-handle=4356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\CCH Browser Search\icschrome.exe" chrome-extension://jbmddjomhfbddonalhdfcphaihmgdgcm/ --parent-window=0 | C:\Program Files\CCH Browser Search\icschrome.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\CCH Browser Search\icschrome.exe" chrome-extension://jbmddjomhfbddonalhdfcphaihmgdgcm/ --parent-window=0 | C:\Program Files\CCH Browser Search\icschrome.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,13051515822500552863,17741900905429802618,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9580929627026978898 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Windows\system32\taskkill.exe" /F /IM chrome.exe | C:\Windows\system32\taskkill.exe | — | BackgroundHost64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 839
Read events
1 164
Write events
664
Delete events
11
Modification events
| (PID) Process: | (2244) BackgroundHost64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2244) BackgroundHost64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2244) BackgroundHost64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\LowRegistry\IntelliConnect |
| Operation: | write | Name: | InstallUpdate |
Value: msie;firefox | |||
| (PID) Process: | (2564) BackgroundHost64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2564) BackgroundHost64.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1856) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\{19975B78-1907-4DD6-A437-4C48120F46A4} |
| Operation: | write | Name: | (default) |
Value: AddonsFramework | |||
| (PID) Process: | (1856) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\AppID\AddonsFramework.DLL |
| Operation: | write | Name: | AppID |
Value: {19975B78-1907-4DD6-A437-4C48120F46A4} | |||
| (PID) Process: | (1856) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{A69B74FD-9808-4CA6-B661-9173F35E53D1}\1.0 |
| Operation: | write | Name: | (default) |
Value: AddonsFramework 1.0 Type Library | |||
| (PID) Process: | (1856) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{A69B74FD-9808-4CA6-B661-9173F35E53D1}\1.0\FLAGS |
| Operation: | write | Name: | (default) |
Value: 0 | |||
| (PID) Process: | (1856) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{A69B74FD-9808-4CA6-B661-9173F35E53D1}\1.0\0\win32 |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\CCH Browser Search\AddonsFramework.Typelib.dll | |||
Executable files
25
Suspicious files
28
Text files
443
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\help_page.ini | text | |
MD5:— | SHA256:— | |||
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\point3.bmp | image | |
MD5:C40116495FFE9323790490BBBF7B86A8 | SHA256:43FA37545463C3B0A32EE2410C51F0CDB673B91B9096C955C19CDB968B993C8B | |||
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\chrome.bmp | image | |
MD5:E098D25DB4D4AB013E8379455C7D114F | SHA256:EE27275A2888D0B48E20EA7C6A0B620894DA1527A982AD97528772690A7DA1C6 | |||
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\UAC.dll | executable | |
MD5:29858669D7DA388D1E62B4FD5337AF12 | SHA256:C24C005DAA7F5578C4372B38D1BE6BE5E27EF3BA2CDB9B67FEE15CAC406EBA62 | |||
| 2244 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nsq3B7D.tmp\license.txt | text | |
MD5:7512C098BB3C0E110F97EF1474A8B9C3 | SHA256:C0F60154DE667B2DC5C28C6E9124973E8BB6CC2588EFB6B098EA95C73CD97E5F | |||
| 2244 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nsq3B7D.tmp\UAC.dll | executable | |
MD5:29858669D7DA388D1E62B4FD5337AF12 | SHA256:C24C005DAA7F5578C4372B38D1BE6BE5E27EF3BA2CDB9B67FEE15CAC406EBA62 | |||
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\UserInfo.dll | executable | |
MD5:D41CF0E4D88C60408F3D5B97F49D40C0 | SHA256:2DBDB3ABD5652302254466AEFA0F40048832F2A39FBB8A63C97FDA8116021FF9 | |||
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 2564 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nso3785.tmp\point1.bmp | image | |
MD5:879F49CA8E617DC5B52D7116B3764FFB | SHA256:E227167BFDD688A730EF5256653D570D636AA11AAD443D1E308A1C5518FA4CEF | |||
| 2244 | BackgroundHost64.exe | C:\Users\admin\AppData\Local\Temp\nsq3B7D.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
54
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2936 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
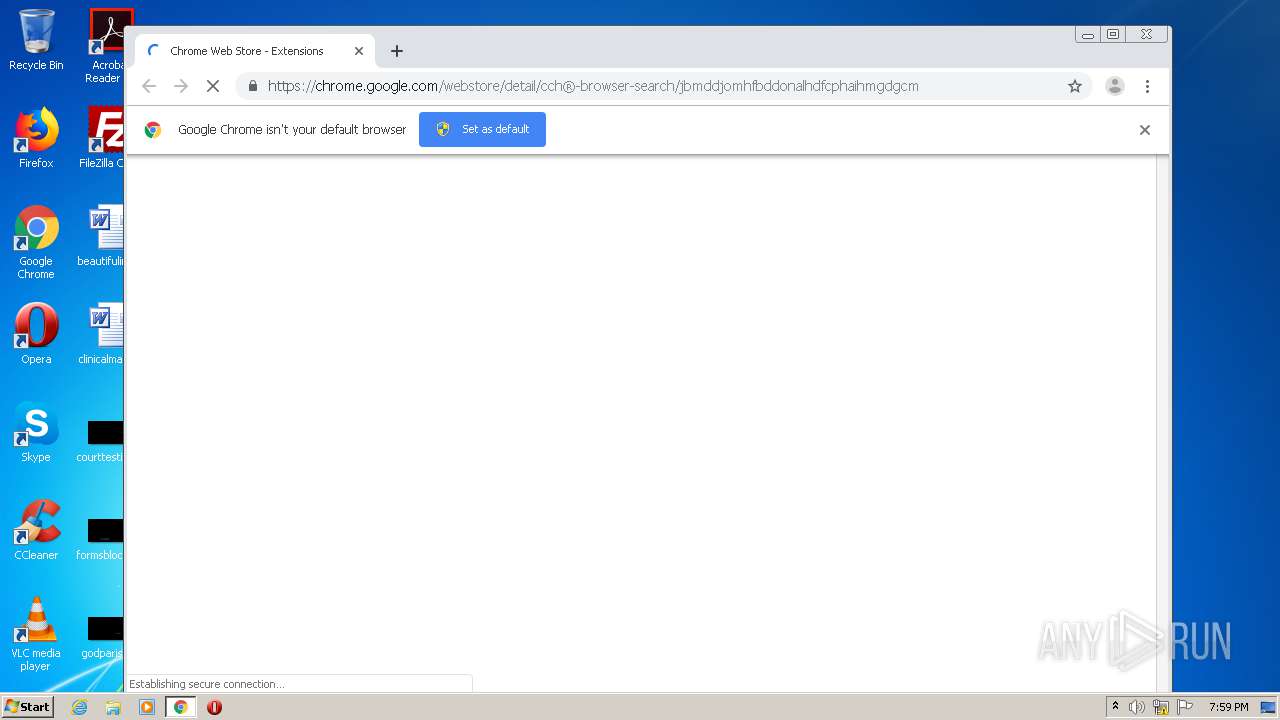
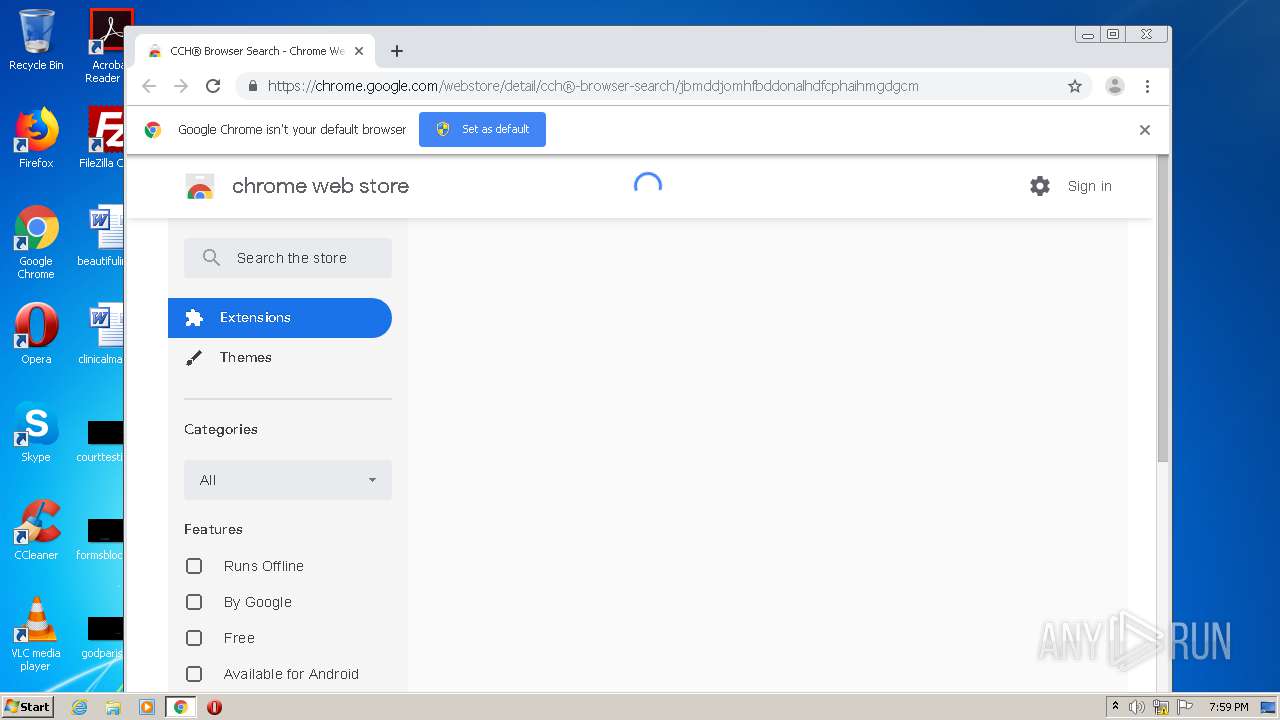
1448 | chrome.exe | 172.217.16.174:443 | chrome.google.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 216.58.212.168:443 | ssl.google-analytics.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 216.58.212.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 172.217.16.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1448 | chrome.exe | 142.250.13.154:443 | stats.g.doubleclick.net | Google Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chrome.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.gstatic.com |
| whitelisted |
ssl.google-analytics.com |
| whitelisted |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |