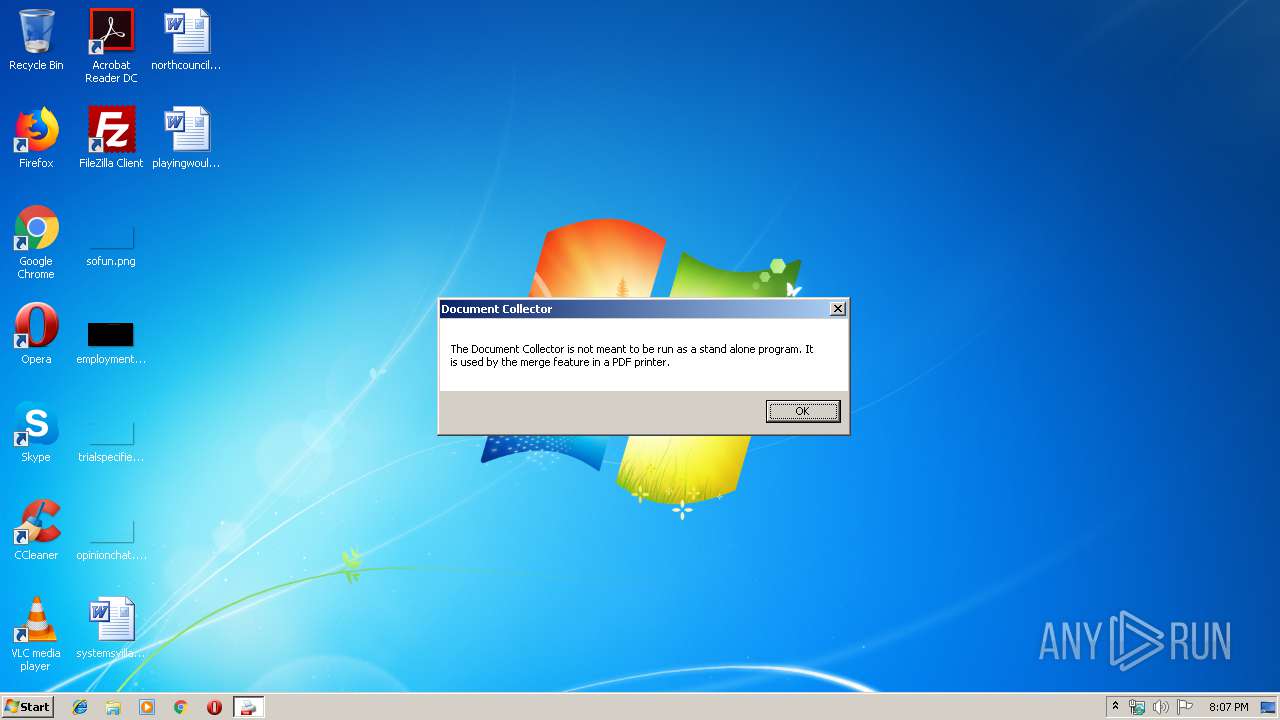
| File name: | DocumentCollector.exe |
| Full analysis: | https://app.any.run/tasks/b4cc5205-5066-4608-a86e-dd3f246a3a5c |
| Verdict: | No threats detected |
| Analysis date: | June 20, 2019, 19:07:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | FB5875C880C9C59B069ABC6C3BF5603D |
| SHA1: | F27DD31D7350929C990735F71176F6D7002FFE3D |
| SHA256: | 90D0BF3E8E662601E490C125BB0FA57390722CDA228379976C5049E559BBE8CE |
| SSDEEP: | 24576:76C6arshqfLOrcnQKnpQXnPpnrXKLSPozv9Cr2HK3emN8lLT6bQ8DtDpaABNKqpc:76arccnfeXhrXoSPMlCr2q3pGH8DDz8F |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
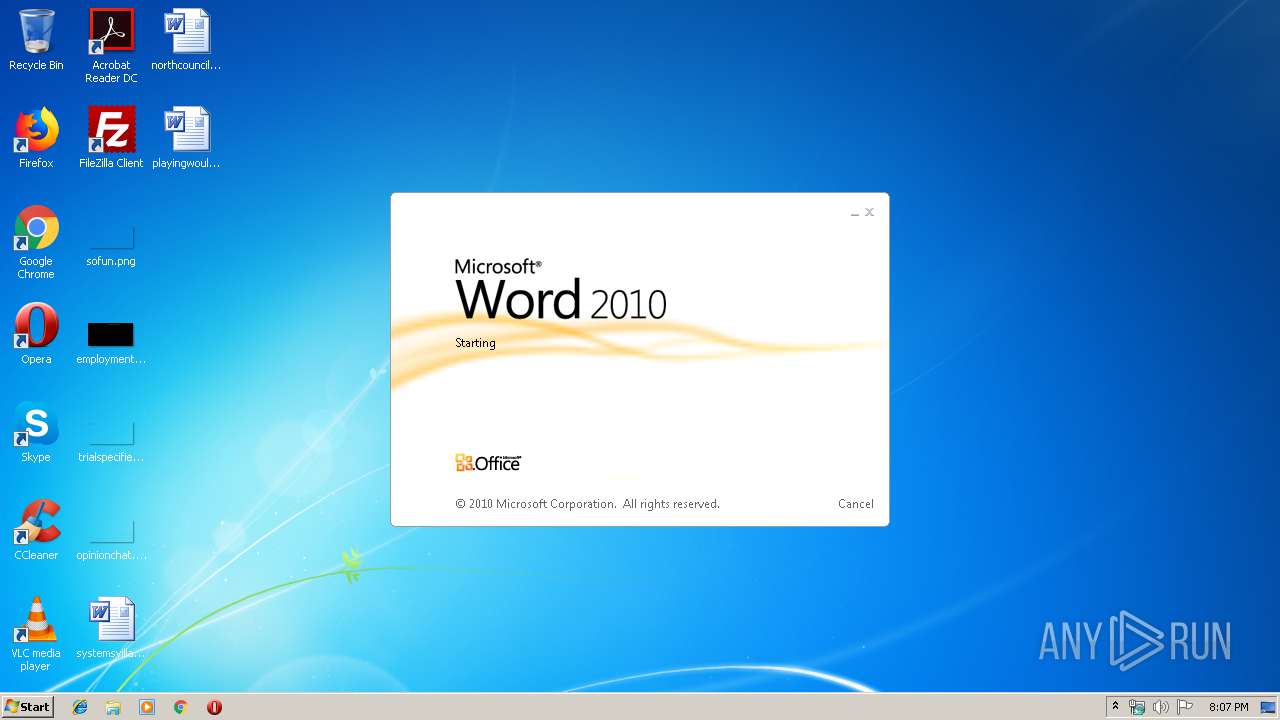
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3996)
Creates files in the user directory
- WINWORD.EXE (PID: 3996)
Manual execution by user
- WINWORD.EXE (PID: 3996)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:15 16:09:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 1500160 |
| InitializedDataSize: | 37376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1702fa |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.6985.29097 |
| ProductVersionNumber: | 1.0.6985.29097 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Document Collector |
| FileVersion: | 1.0.6985.29097 |
| InternalName: | DocumentCollector.exe |
| LegalCopyright: | Copyright 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | DocumentCollector.exe |
| ProductName: | Document Collector |
| ProductVersion: | 1.0.6985.29097 |
| AssemblyVersion: | 1.0.6985.29097 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Feb-2019 15:09:59 |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Document Collector |
| FileVersion: | 1.0.6985.29097 |
| InternalName: | DocumentCollector.exe |
| LegalCopyright: | Copyright 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | DocumentCollector.exe |
| ProductName: | Document Collector |
| ProductVersion: | 1.0.6985.29097 |
| Assembly Version: | 1.0.6985.29097 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 15-Feb-2019 15:09:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0016E300 | 0x0016E400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.98336 |
.reloc | 0x00172000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
.rsrc | 0x00174000 | 0x00008E58 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.11201 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00137 | 706 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.40478 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.44958 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.79862 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.38193 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 7.63389 | 10575 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.59288 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.99115 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.26018 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.84132 | 132 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3124 | "C:\Users\admin\AppData\Local\Temp\DocumentCollector.exe" | C:\Users\admin\AppData\Local\Temp\DocumentCollector.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Document Collector Exit code: 0 Version: 1.0.6985.29097 Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\playingwould.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
483
Read events
443
Write events
29
Delete events
11
Modification events
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?.$ |
Value: 3F2E24009C0F0000010000000000000000000000 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1322516511 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322516632 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1322516633 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 9C0F000084FB9A6E9B27D50100000000 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | h/$ |
Value: 682F24009C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | h/$ |
Value: 682F24009C0F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3996) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREBF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{BC7E3F7F-E1D3-4281-82CE-D5DB0A3323BE}.tmp | — | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{AFA70153-9387-491D-8385-4A45B85BE4D8}.tmp | — | |
MD5:— | SHA256:— | |||
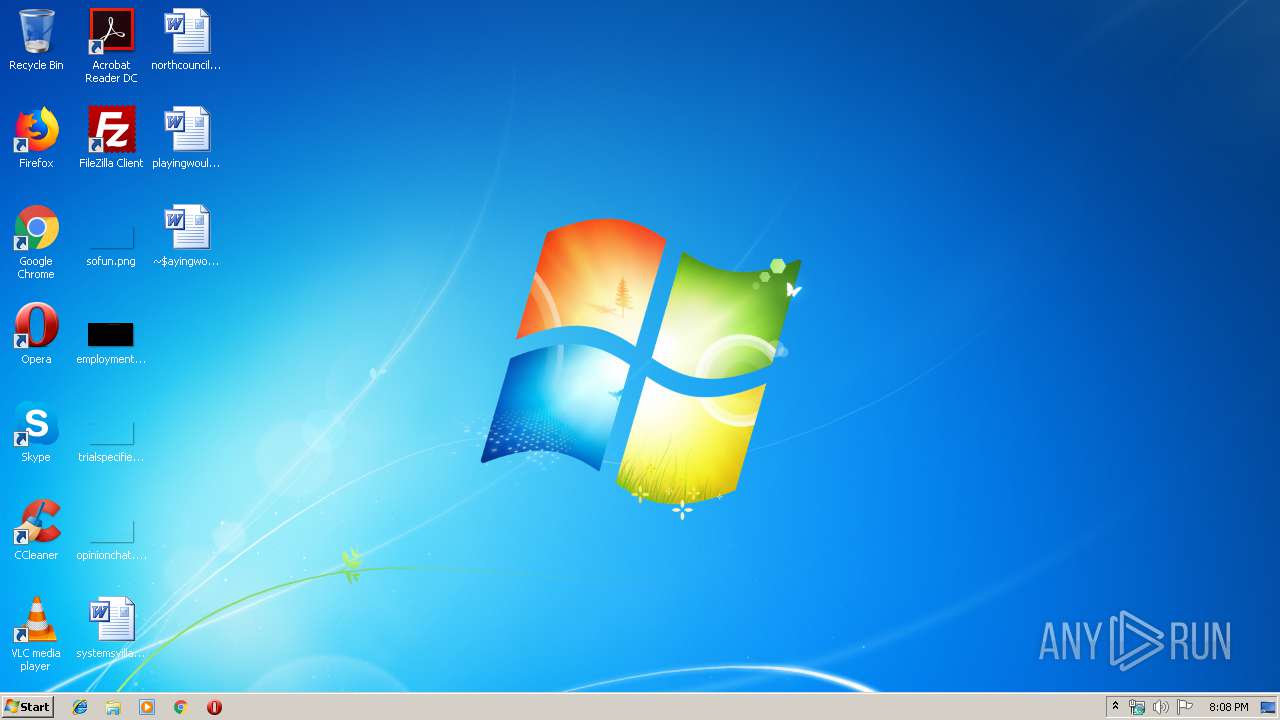
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\Desktop\~$ayingwould.rtf | pgc | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 3996 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\playingwould.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report