| download: | download |
| Full analysis: | https://app.any.run/tasks/b9b0e482-121b-4a64-9a1e-7cda27ee3d93 |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 13:26:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0D83A645018D9C2CD6AD9D00FF721636 |
| SHA1: | 5703E0C3CC6CA954CA08A0AAE0884C932CDDC991 |
| SHA256: | 90CFABF6F24FD6298A1F11E7DE6A101406B952642F303CCE54AE58F35FF546AA |
| SSDEEP: | 12288:Z7ytnLW49hHtzjOeop+57nPY9FPVFL0XnGurJz+0KIfg2fZ:py84PJOg7PY9FPHyGu9+0F9Z |
MALICIOUS
Connects to CnC server
- IEXPLORE.EXE (PID: 3852)
SUSPICIOUS
Reads internet explorer settings
- download.exe (PID: 3112)
Creates files in the user directory
- download.exe (PID: 3112)
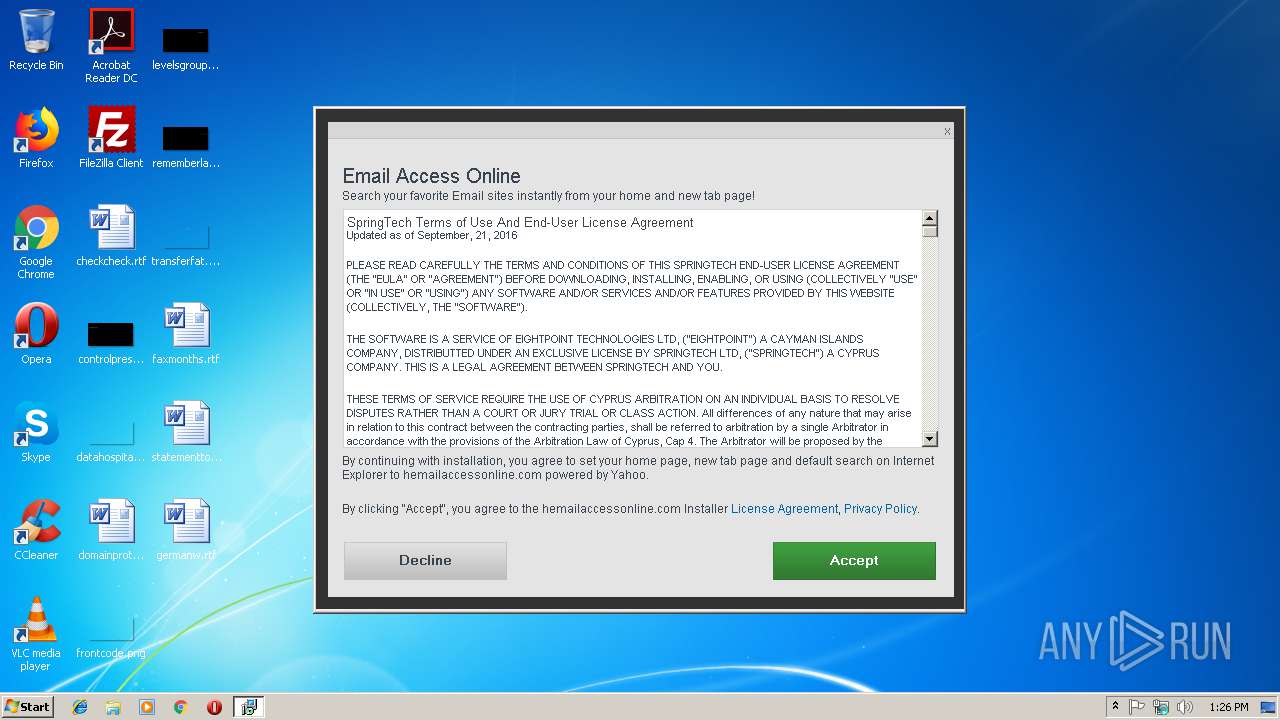
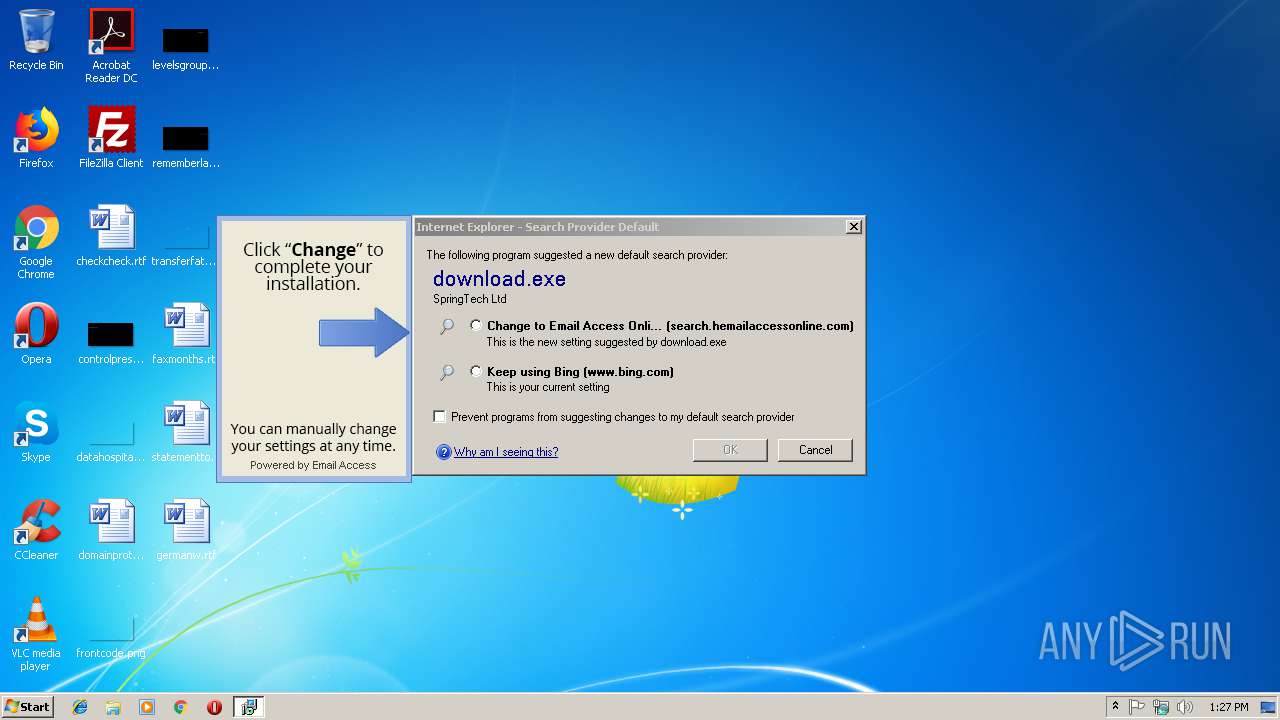
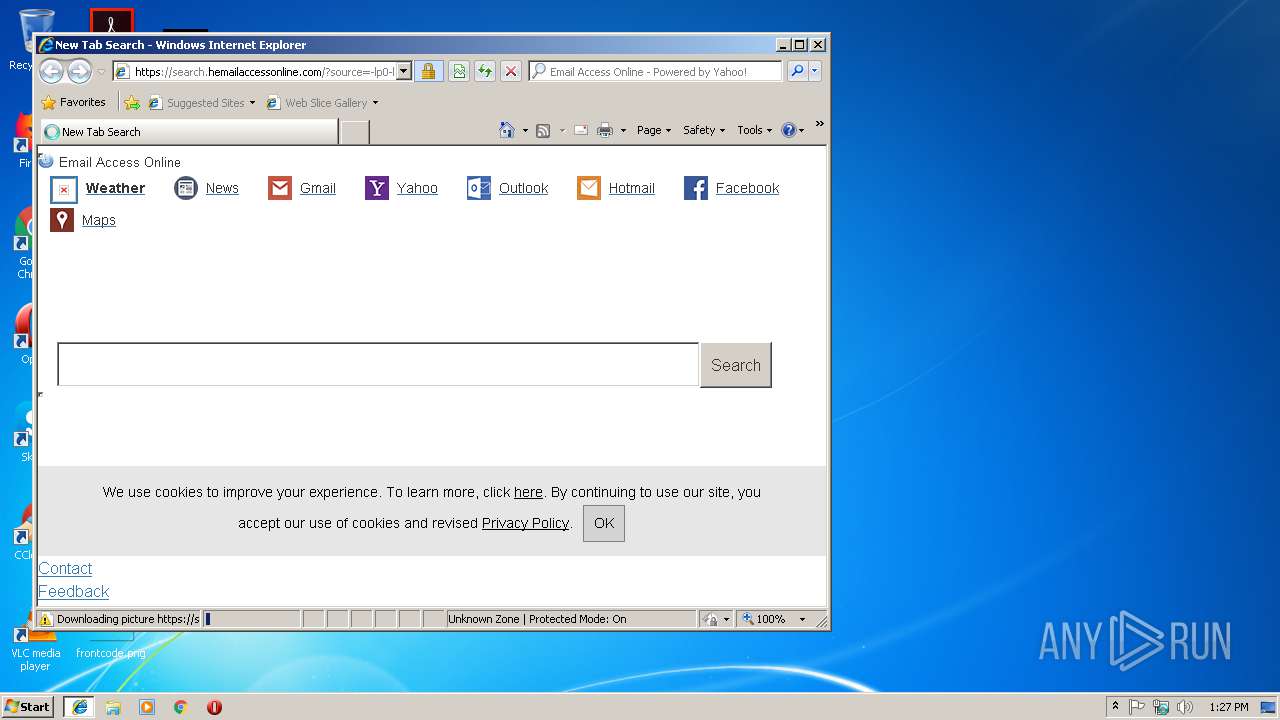
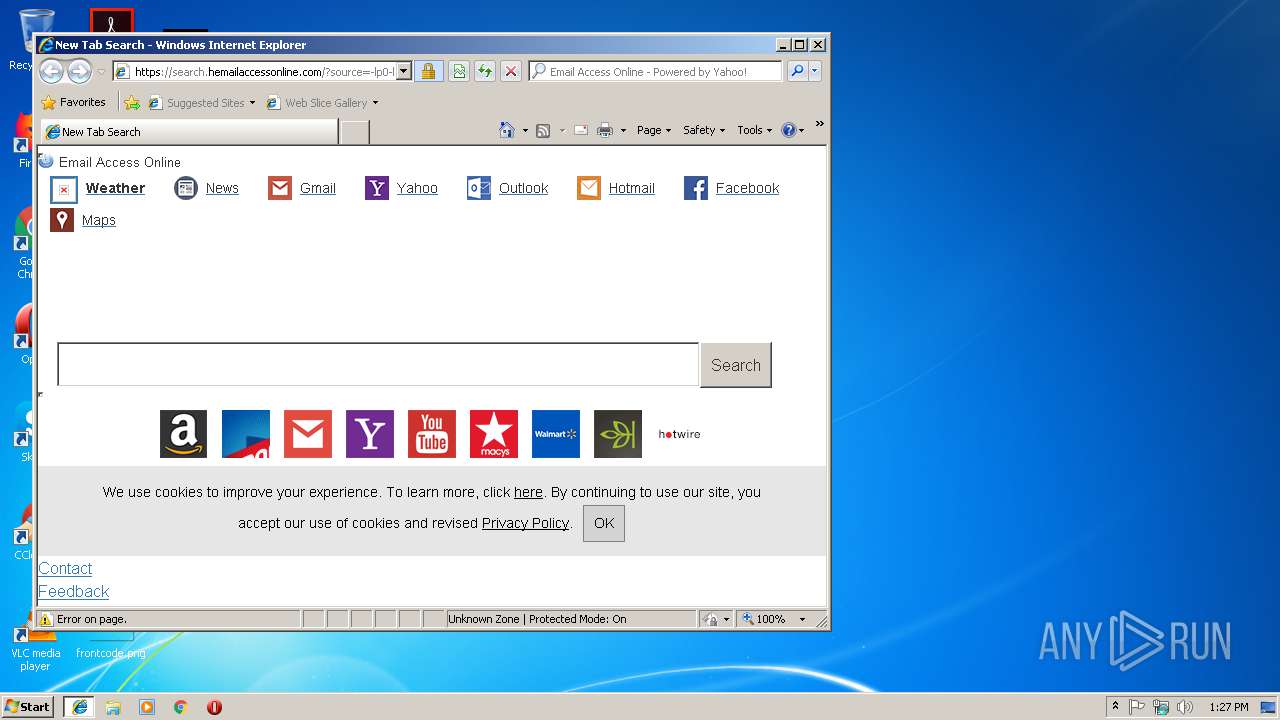
Changes the started page of IE
- download.exe (PID: 3112)
Executable content was dropped or overwritten
- download.exe (PID: 3112)
Starts Internet Explorer
- download.exe (PID: 3112)
Creates a software uninstall entry
- download.exe (PID: 3112)
INFO
Application launched itself
- IEXPLORE.EXE (PID: 3368)
Reads Internet Cache Settings
- IEXPLORE.EXE (PID: 3852)
Changes internet zones settings
- IEXPLORE.EXE (PID: 3368)
Creates files in the user directory
- IEXPLORE.EXE (PID: 3852)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 3852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:11 16:00:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.11 |
| CodeSize: | 273920 |
| InitializedDataSize: | 856064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x213d9 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.4.0.3 |
| ProductVersionNumber: | 4.4.0.3 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | SpringTech Ltd. |
| FileVersion: | 4, 4, 0, 3 |
| InternalName: | IEInstaller |
| LegalCopyright: | Copyright (C) 2017 SpringTech Ltd. |
| OriginalFileName: | IEInstaller |
| ProductName: | IEInstaller |
| ProductVersion: | 4, 4, 0, 3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-May-2018 14:00:34 |
| Detected languages: |
|
| CompanyName: | SpringTech Ltd. |
| FileVersion: | 4, 4, 0, 3 |
| InternalName: | IEInstaller |
| LegalCopyright: | Copyright (C) 2017 SpringTech Ltd. |
| OriginalFilename: | IEInstaller |
| ProductName: | IEInstaller |
| ProductVersion: | 4, 4, 0, 3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-May-2018 14:00:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00042CC7 | 0x00042E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64236 |
.rdata | 0x00044000 | 0x000168B4 | 0x00016A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.24493 |
.data | 0x0005B000 | 0x00002CC4 | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.10743 |
.AESeal | 0x0005E000 | 0x00001983 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.9412 |
.rsrc | 0x00060000 | 0x000B1C78 | 0x000B1E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.525 |
.reloc | 0x00112000 | 0x00003E7C | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55532 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3298 | 822 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 4.02252 | 3752 | UNKNOWN | English - United States | RT_ICON |
6 | 3.62911 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.25755 | 296 | UNKNOWN | English - United States | RT_ICON |
8 | 3.47151 | 1384 | UNKNOWN | English - United States | RT_ICON |
9 | 3.91708 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 3.91366 | 2216 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WININET.dll |
Total processes
32
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3112 | "C:\Users\admin\AppData\Local\Temp\download.exe" | C:\Users\admin\AppData\Local\Temp\download.exe | explorer.exe | ||||||||||||
User: admin Company: SpringTech Ltd. Integrity Level: MEDIUM Exit code: 0 Version: 4, 4, 0, 3 Modules
| |||||||||||||||
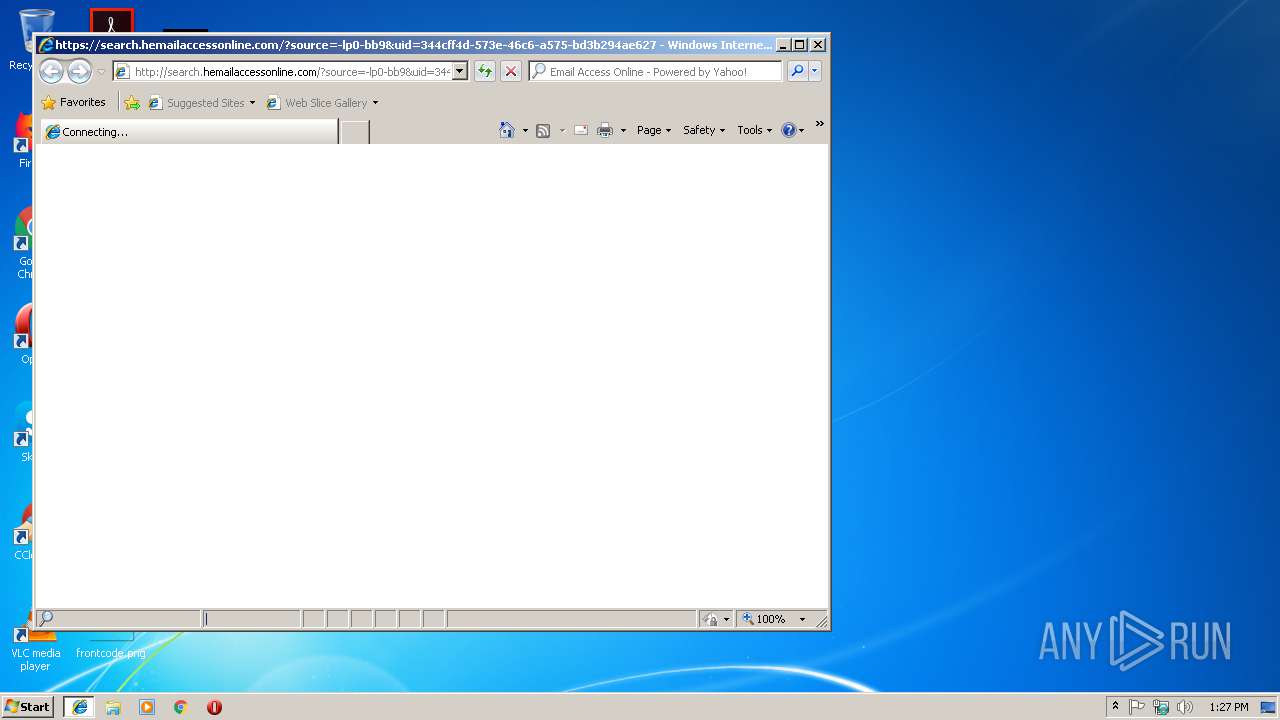
| 3368 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" http://search.hemailaccessonline.com/?source=-lp0-bb9&uid=344cff4d-573e-46c6-a575-bd3b294ae627&uc=20190111&ap=appfocus1&i_id=email_spt__1.30 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | — | download.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3852 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" SCODEF:3368 CREDAT:71937 | C:\Program Files\Internet Explorer\IEXPLORE.EXE | IEXPLORE.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
553
Read events
460
Write events
93
Delete events
0
Modification events
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3112) download.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\download_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
5
Text files
22
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabDF45.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarDF46.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabDFA4.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarDFA5.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\CabE072.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Temp\Low\TarE073.tmp | — | |
MD5:— | SHA256:— | |||
| 3852 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\search_hemailaccessonline_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3112 | download.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\script[1] | text | |
MD5:— | SHA256:— | |||
| 3112 | download.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\styles[1] | text | |
MD5:— | SHA256:— | |||
| 3112 | download.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\grey-btn[1] | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
15
DNS requests
10
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3112 | download.exe | GET | 200 | 23.22.198.205:80 | http://www.springtechdld.com/ies/api.cgi?act=getConfig&id=ZG93bmxvYWQuZXhl&rf=1&proto=1 | US | — | — | shared |
3852 | IEXPLORE.EXE | GET | 200 | 2.16.186.56:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 55.2 Kb | whitelisted |
3112 | download.exe | GET | 200 | 52.206.203.181:80 | http://imp.hemailaccessonline.com/impression.do?implementation_id=email_spt__1.30&source=-lp0-bb9&sub_id=20190111&traffic_source=appfocus1&user_id=344cff4d-573e-46c6-a575-bd3b294ae627&useragent=Mozilla%2F5.0+(Windows+NT+10.0%3B+WOW64%3B+Trident%2F7.0%3B+rv%3A11.0)+like+Gecko&subid2=8.0.7601.17514&event=ex_set_ds | US | image | 109 b | malicious |
3112 | download.exe | GET | 200 | 52.206.203.181:80 | http://imp.hemailaccessonline.com/impression.do?implementation_id=email_spt__1.30&source=-lp0-bb9&sub_id=20190111&traffic_source=appfocus1&user_id=344cff4d-573e-46c6-a575-bd3b294ae627&useragent=Mozilla%2F5.0+(Windows+NT+10.0%3B+WOW64%3B+Trident%2F7.0%3B+rv%3A11.0)+like+Gecko&subid2=8.0.7601.17514&event=ex_installed | US | image | 109 b | malicious |
3112 | download.exe | GET | 200 | 52.206.203.181:80 | http://imp.hemailaccessonline.com/impression.do?implementation_id=email_spt__1.30&source=-lp0-bb9&sub_id=20190111&traffic_source=appfocus1&user_id=344cff4d-573e-46c6-a575-bd3b294ae627&useragent=Mozilla%2F5.0+(Windows+NT+10.0%3B+WOW64%3B+Trident%2F7.0%3B+rv%3A11.0)+like+Gecko&subid2=8.0.7601.17514&event=ex_set_hp | US | image | 109 b | malicious |
3112 | download.exe | GET | 200 | 52.206.203.181:80 | http://imp.hemailaccessonline.com/impression.do?implementation_id=email_spt__1.30&source=-lp0-bb9&sub_id=20190111&traffic_source=appfocus1&user_id=344cff4d-573e-46c6-a575-bd3b294ae627&useragent=Mozilla%2F5.0+(Windows+NT+10.0%3B+WOW64%3B+Trident%2F7.0%3B+rv%3A11.0)+like+Gecko&subid2=8.0.7601.17514&event=ex_executed | US | image | 109 b | malicious |
3112 | download.exe | POST | 200 | 23.22.198.205:80 | http://www.springtechdld.com/advplatform/api.cgi?act=postStat | US | — | — | shared |
3112 | download.exe | GET | 200 | 52.206.203.181:80 | http://imp.hemailaccessonline.com/impression.do?implementation_id=email_spt__1.30&source=-lp0-bb9&sub_id=20190111&traffic_source=appfocus1&user_id=344cff4d-573e-46c6-a575-bd3b294ae627&useragent=Mozilla%2F5.0+(Windows+NT+10.0%3B+WOW64%3B+Trident%2F7.0%3B+rv%3A11.0)+like+Gecko&subid2=8.0.7601.17514&event=ex_shown | US | image | 109 b | malicious |
3852 | IEXPLORE.EXE | GET | 200 | 143.204.208.222:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
3852 | IEXPLORE.EXE | GET | 302 | 52.1.166.42:80 | http://search.hemailaccessonline.com/?source=-lp0-bb9&uid=344cff4d-573e-46c6-a575-bd3b294ae627&uc=20190111&ap=appfocus1&i_id=email_spt__1.30 | US | html | 274 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3852 | IEXPLORE.EXE | 23.8.4.219:443 | imp.mt48.net | Akamai International B.V. | NL | whitelisted |
3852 | IEXPLORE.EXE | 52.22.199.136:443 | imp.hemailaccessonline.com | Amazon.com, Inc. | US | malicious |
3112 | download.exe | 23.22.198.205:80 | www.springtechdld.com | Amazon.com, Inc. | US | malicious |
3112 | download.exe | 52.206.203.181:80 | imp.hemailaccessonline.com | Amazon.com, Inc. | US | malicious |
3852 | IEXPLORE.EXE | 52.1.166.42:443 | search.hemailaccessonline.com | Amazon.com, Inc. | US | malicious |
3852 | IEXPLORE.EXE | 52.1.166.42:80 | search.hemailaccessonline.com | Amazon.com, Inc. | US | malicious |
3852 | IEXPLORE.EXE | 143.204.208.222:80 | x.ss2.us | — | US | suspicious |
3852 | IEXPLORE.EXE | 2.16.186.56:80 | www.download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
3852 | IEXPLORE.EXE | 52.50.109.222:443 | appfocus.go2cloud.org | Amazon.com, Inc. | IE | suspicious |
3852 | IEXPLORE.EXE | 143.204.208.39:443 | d3ff8olul1r3ot.cloudfront.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.springtechdld.com |
| shared |
imp.hemailaccessonline.com |
| unknown |
search.hemailaccessonline.com |
| unknown |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
appfocus.go2cloud.org |
| shared |
d3ff8olul1r3ot.cloudfront.net |
| shared |
imp.mt48.net |
| whitelisted |
imp.onesearch.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3112 | download.exe | A Network Trojan was detected | ET MALWARE MALWARE W32/WinWrapper.Adware User-Agent |
3112 | download.exe | A Network Trojan was detected | ET MALWARE MALWARE W32/WinWrapper.Adware User-Agent |
1 ETPRO signatures available at the full report