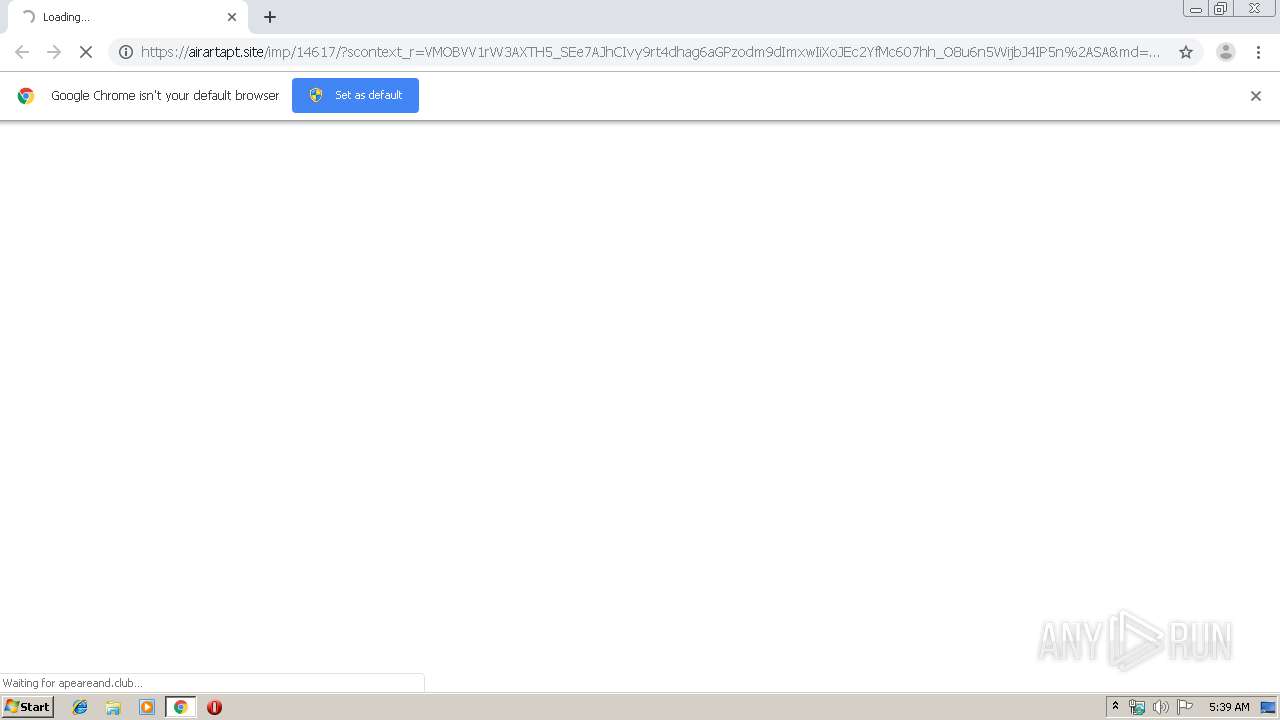
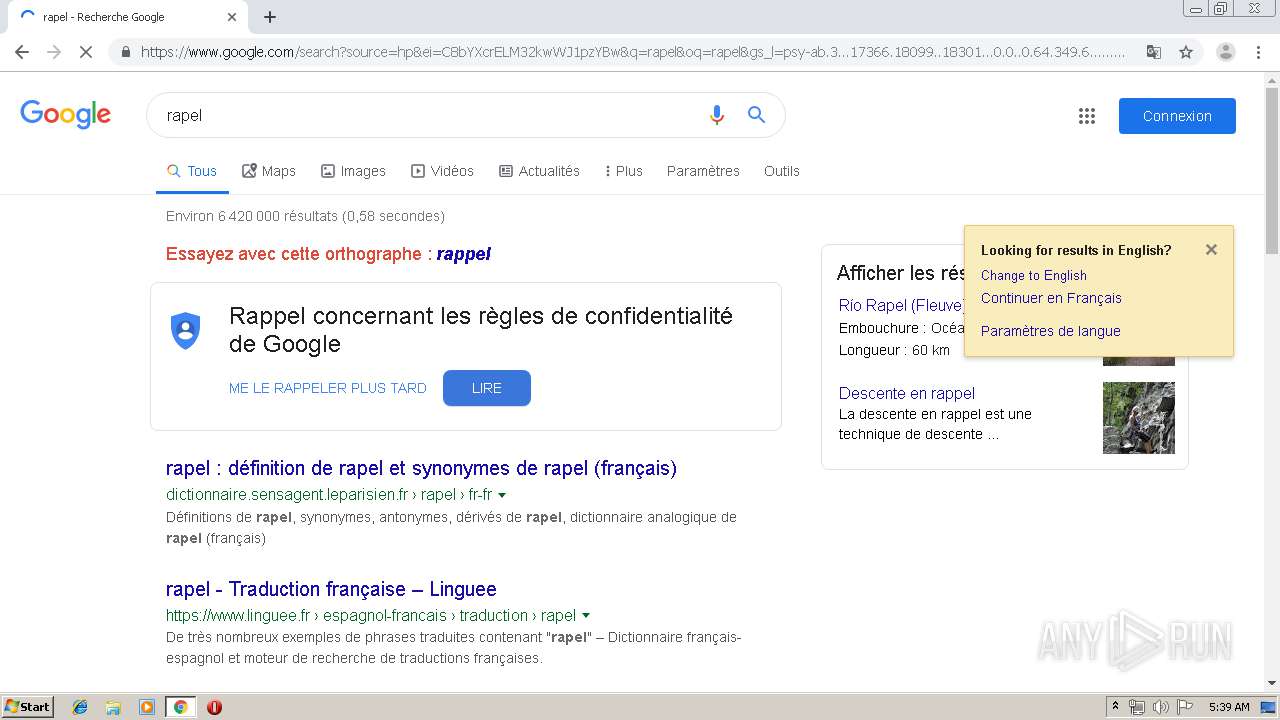
| URL: | https://airartapt.site/imp/14617/?scontext_r=VMOBVV1rW3AXTH5_SEe7AJhCIvy9rt4dhag6aGPzodm9dImxwIiXoJEc2YfMc607hh_O8u6n5WijbJ4IP5n%2ASA&md=7JSYiojNzQDLiMnI6ISMzYjN4djN4ICLiImI6ISMzYjN4ZTN0ICLiInI6ICa0RHczpzLv0WYj1CdvJncl5GdtQ2b35GbvFGZu4WZ09iIsICaiojMxEDOsICbiojIwRXLCJlIsICdioTM4ADLionI6gTNyEDLismI6ITf |
| Full analysis: | https://app.any.run/tasks/56076ba7-e23f-4018-ac0b-f4a3fe368290 |
| Verdict: | Malicious activity |
| Analysis date: | November 23, 2019, 05:38:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C9438999A48960A9895A05BA6D0BD003 |
| SHA1: | C142685D8AB475C362A80711DE7631A2EAA6E8E9 |
| SHA256: | 90B43BAF2E66DD7040F55321994F7B47F08C50A11786CF78907B2E03A2D9EAAE |
| SSDEEP: | 6:2hRWmg0pUAgBNHLas8/wIWQrQue6cP+RNBi9U/fp36ni1IYGD:23gcUAxcIEuaP+NBi9piyD |
MALICIOUS
No malicious indicators.SUSPICIOUS
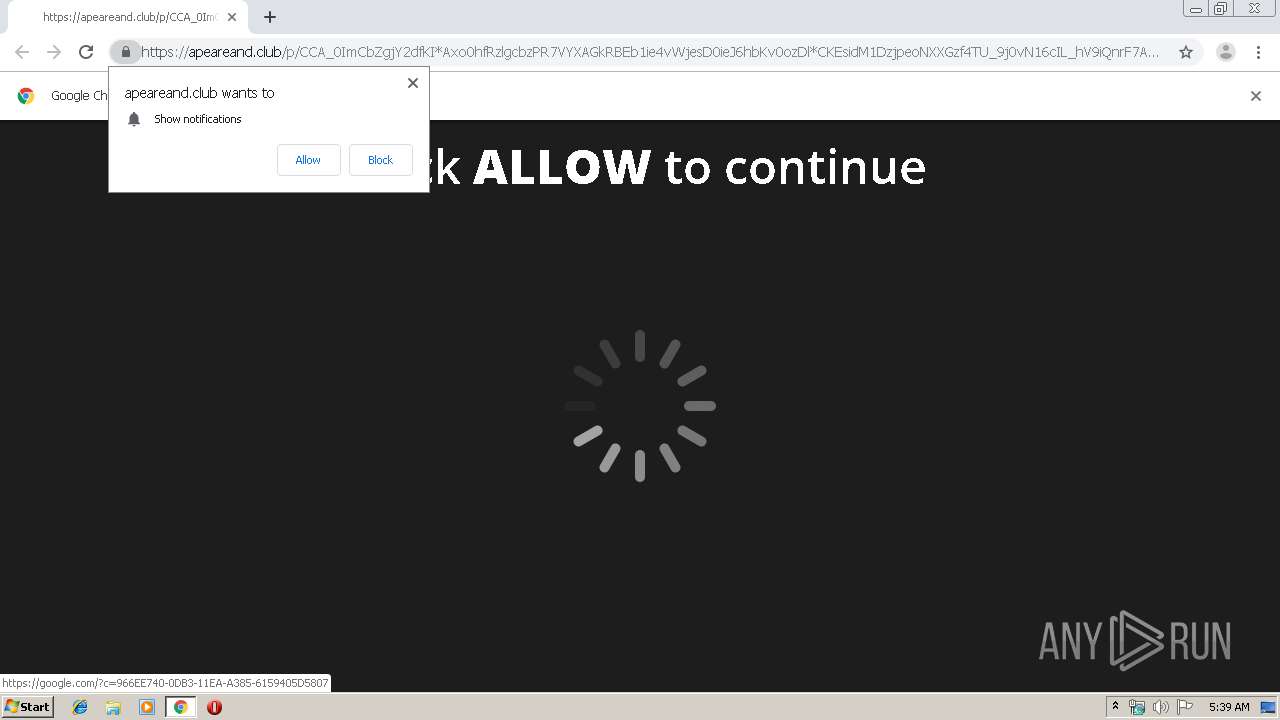
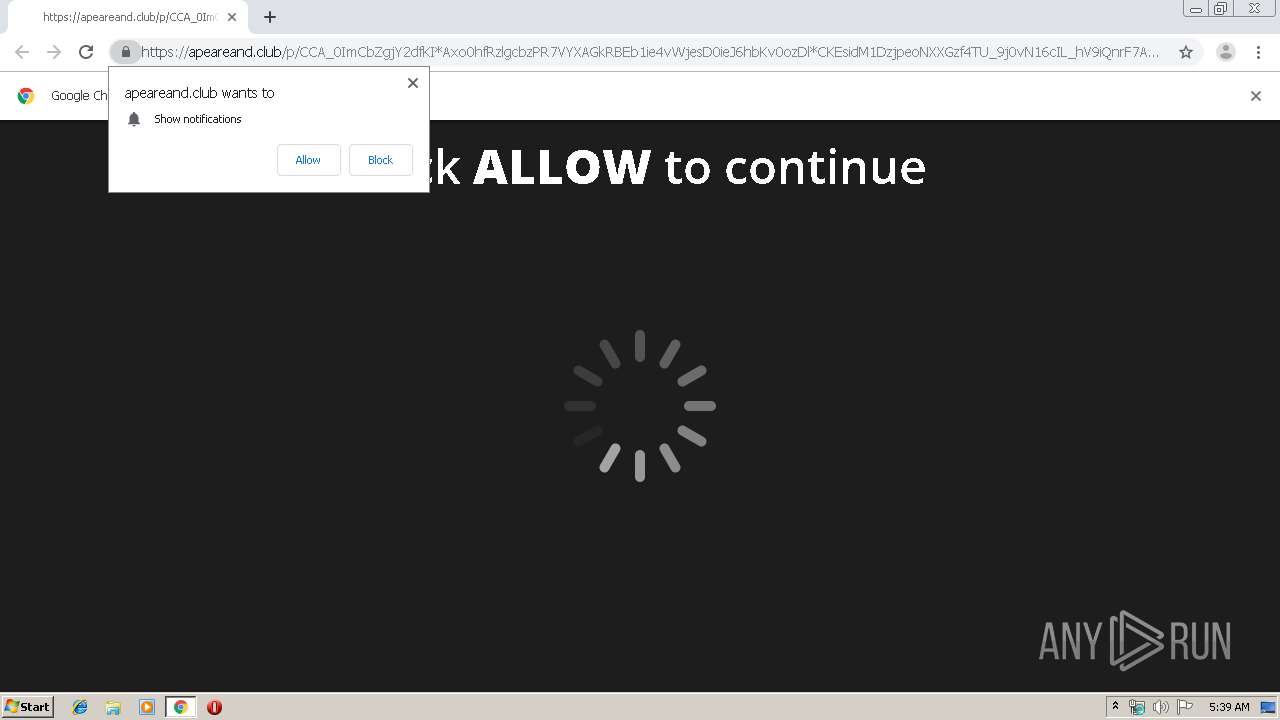
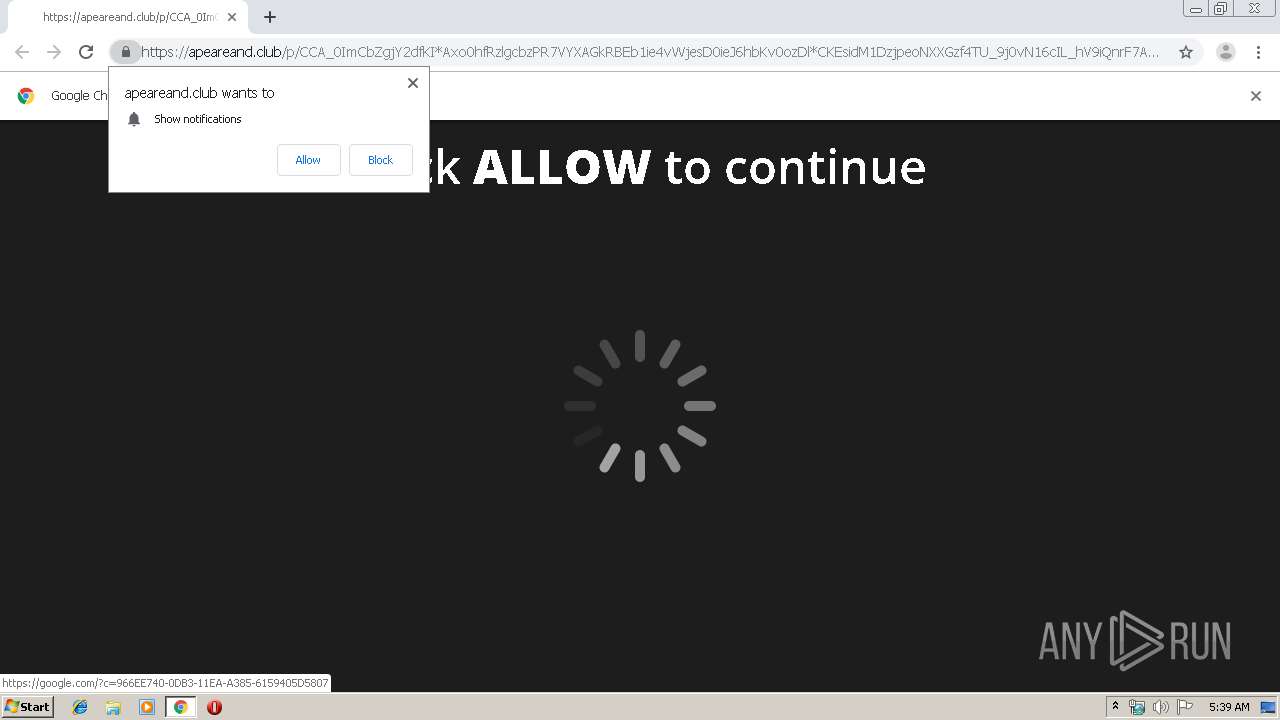
Modifies files in Chrome extension folder
- chrome.exe (PID: 532)
INFO
Reads the hosts file
- chrome.exe (PID: 532)
- chrome.exe (PID: 2112)
Reads settings of System Certificates
- chrome.exe (PID: 2112)
Application launched itself
- chrome.exe (PID: 532)
Creates files in the user directory
- chrome.exe (PID: 532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
50
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14479025470228021111 --renderer-client-id=41 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11851999112932933007 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5677882313976222348 --mojo-platform-channel-handle=3984 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://airartapt.site/imp/14617/?scontext_r=VMOBVV1rW3AXTH5_SEe7AJhCIvy9rt4dhag6aGPzodm9dImxwIiXoJEc2YfMc607hh_O8u6n5WijbJ4IP5n%2ASA&md=7JSYiojNzQDLiMnI6ISMzYjN4djN4ICLiImI6ISMzYjN4ZTN0ICLiInI6ICa0RHczpzLv0WYj1CdvJncl5GdtQ2b35GbvFGZu4WZ09iIsICaiojMxEDOsICbiojIwRXLCJlIsICdioTM4ADLionI6gTNyEDLismI6ITf" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16173901473030977941 --mojo-platform-channel-handle=4752 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7190326545807840750 --mojo-platform-channel-handle=3512 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=12892138398005774205 --mojo-platform-channel-handle=4596 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8941578523529551433 --renderer-client-id=46 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5876 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5166442354542513089 --mojo-platform-channel-handle=4416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,7147081294062879578,14128116837692931282,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14202692887775618203 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
718
Read events
596
Write events
117
Delete events
5
Modification events
| (PID) Process: | (2136) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 532-13218961153894250 |
Value: 259 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (532) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
255
Text files
1 907
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2d97ace4-b2fe-4cb6-8f11-97a26c1bfc16.tmp | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a841.TMP | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 532 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a841.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 579
TCP/UDP connections
170
DNS requests
142
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2112 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
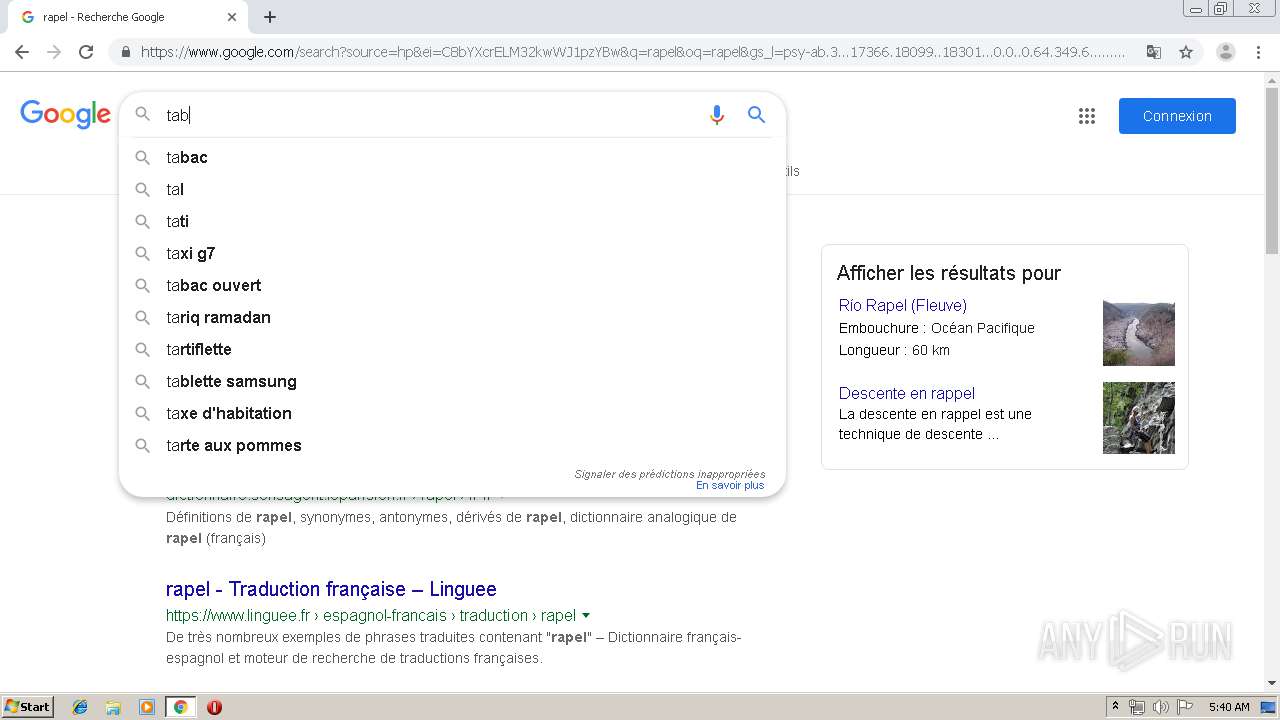
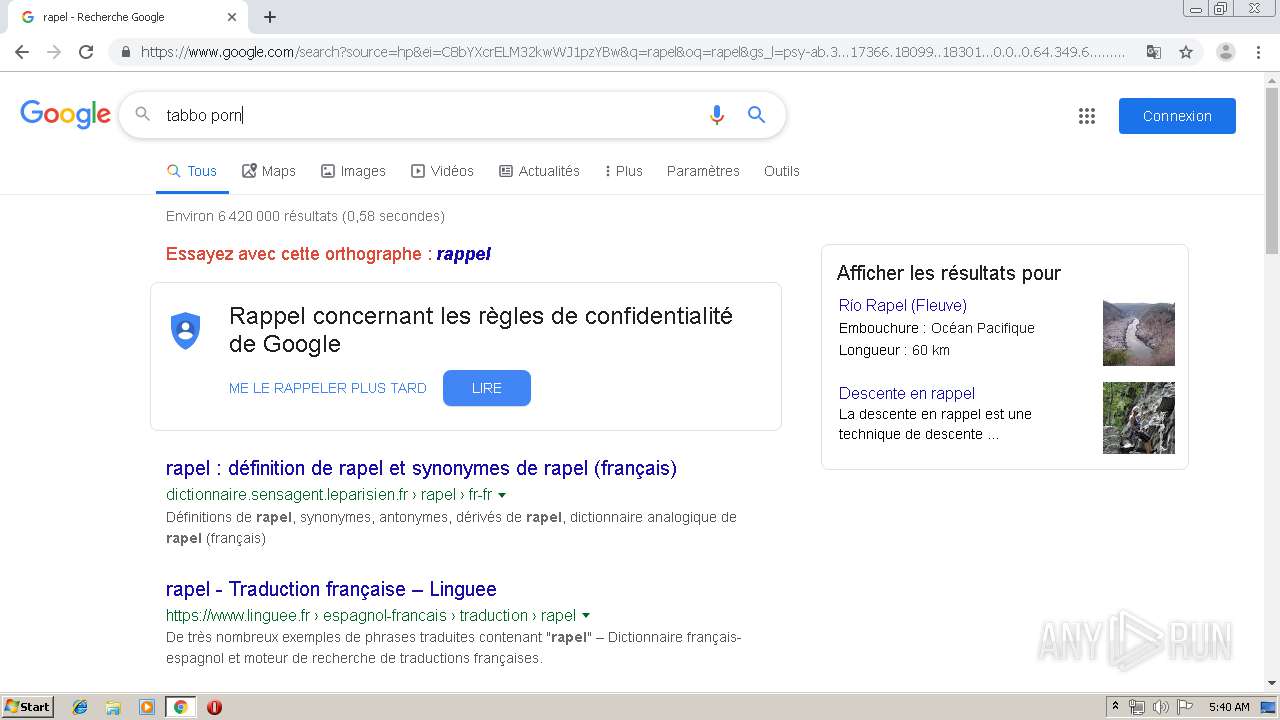
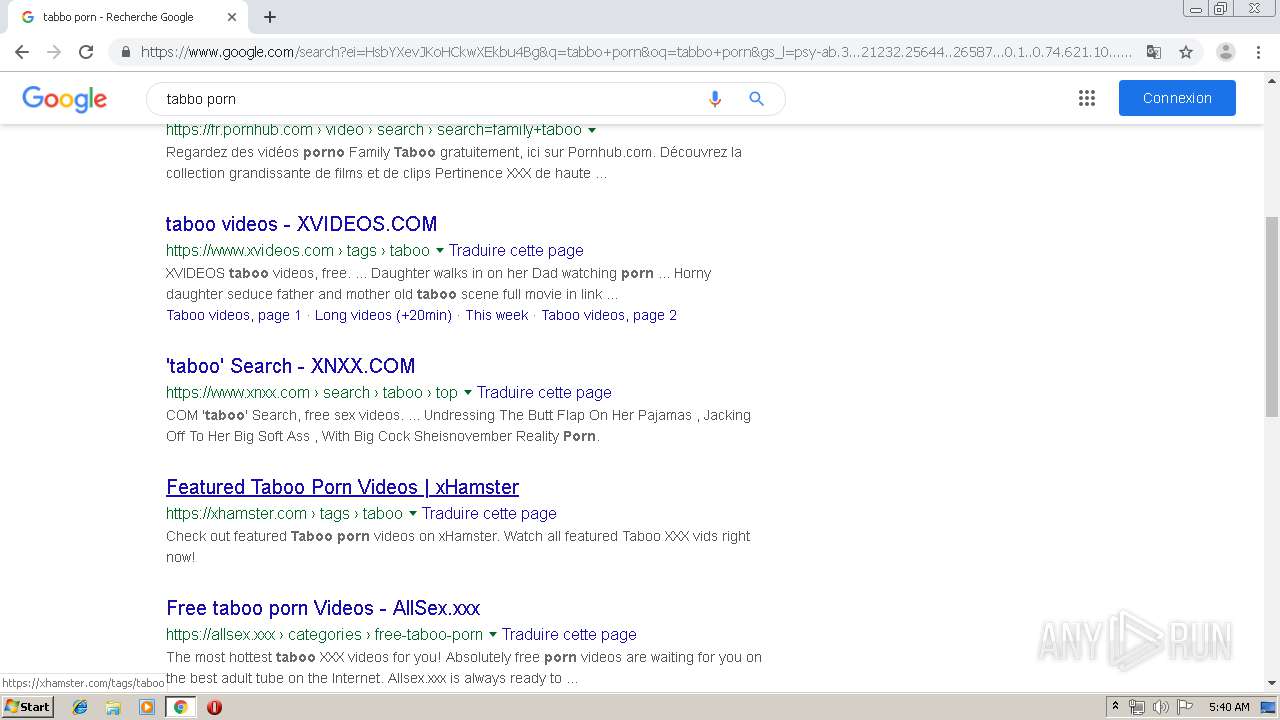
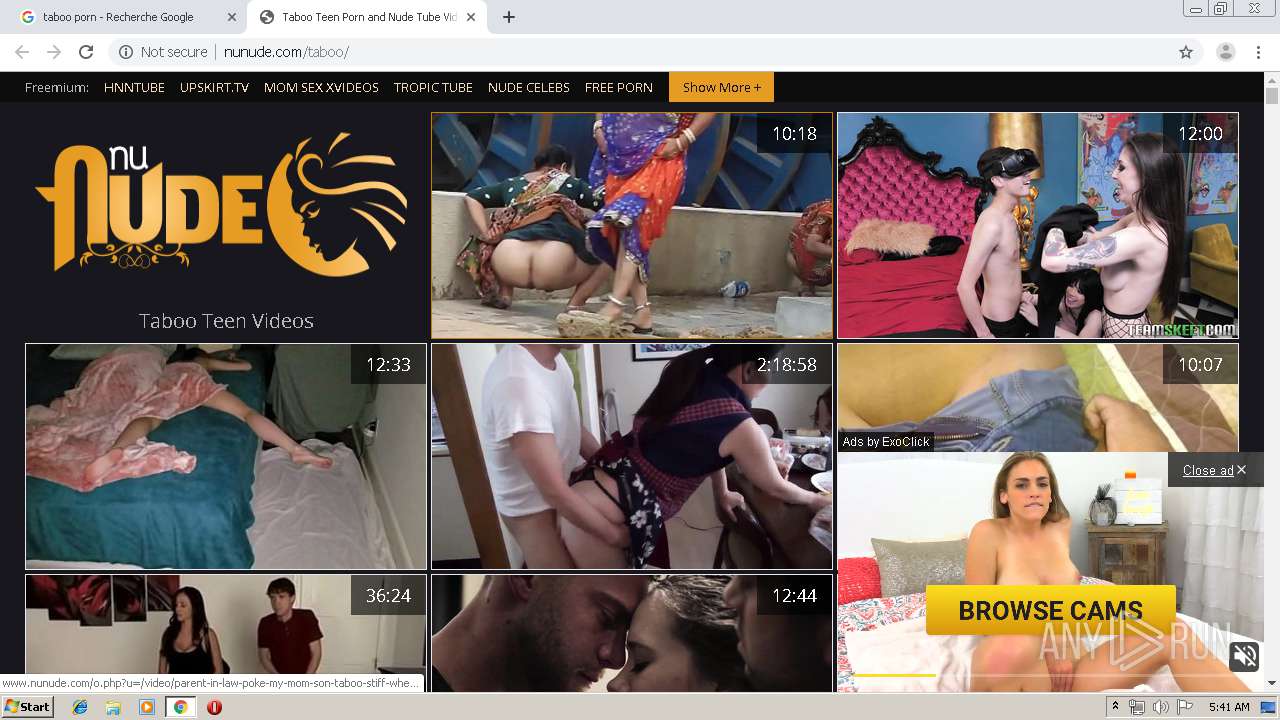
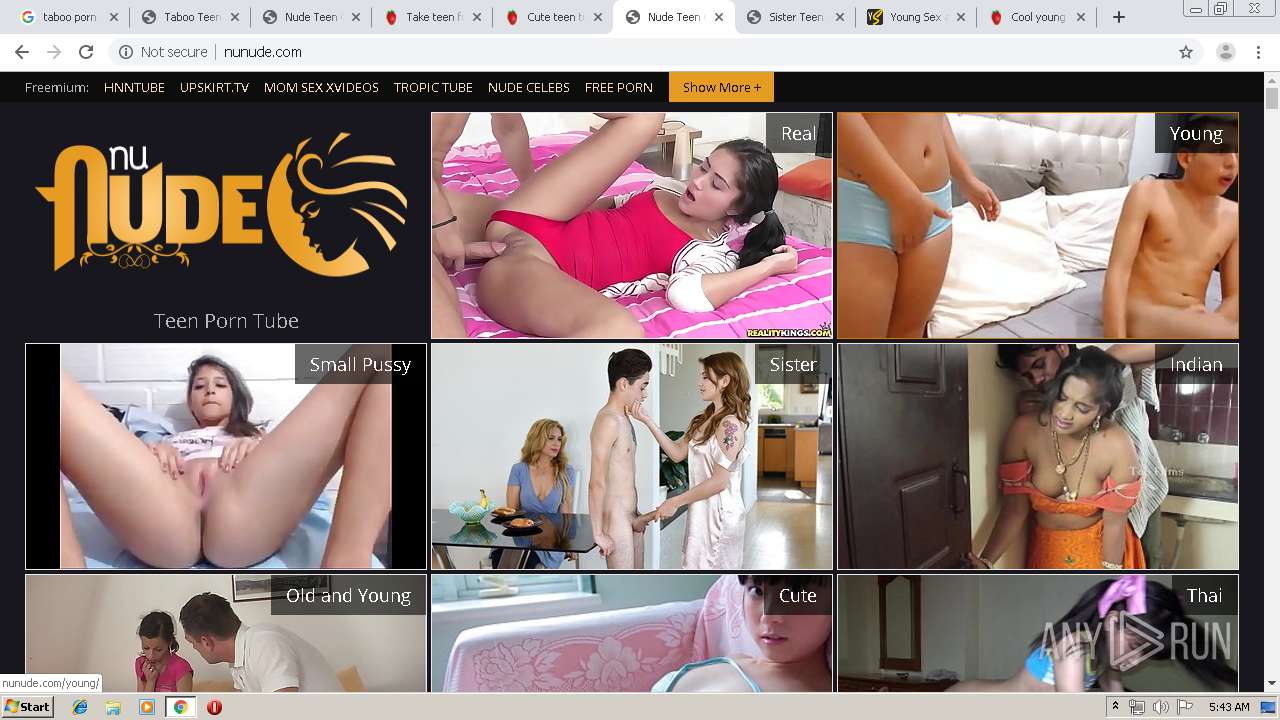
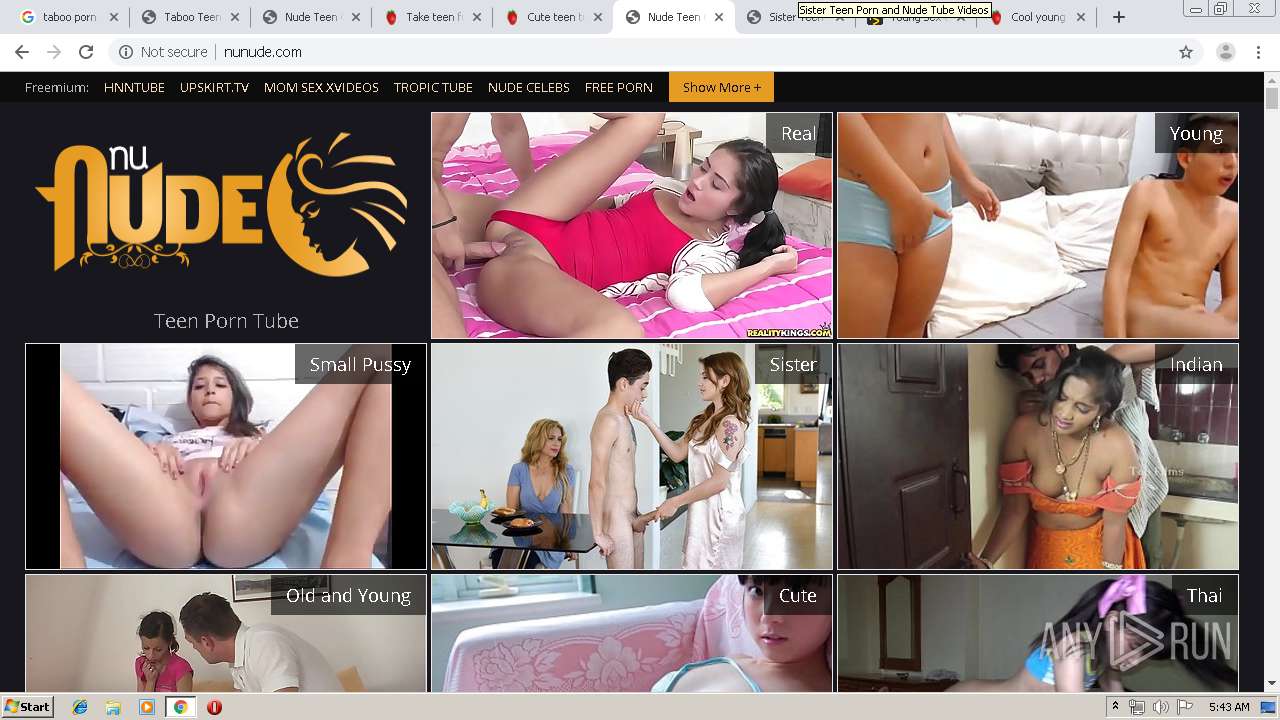
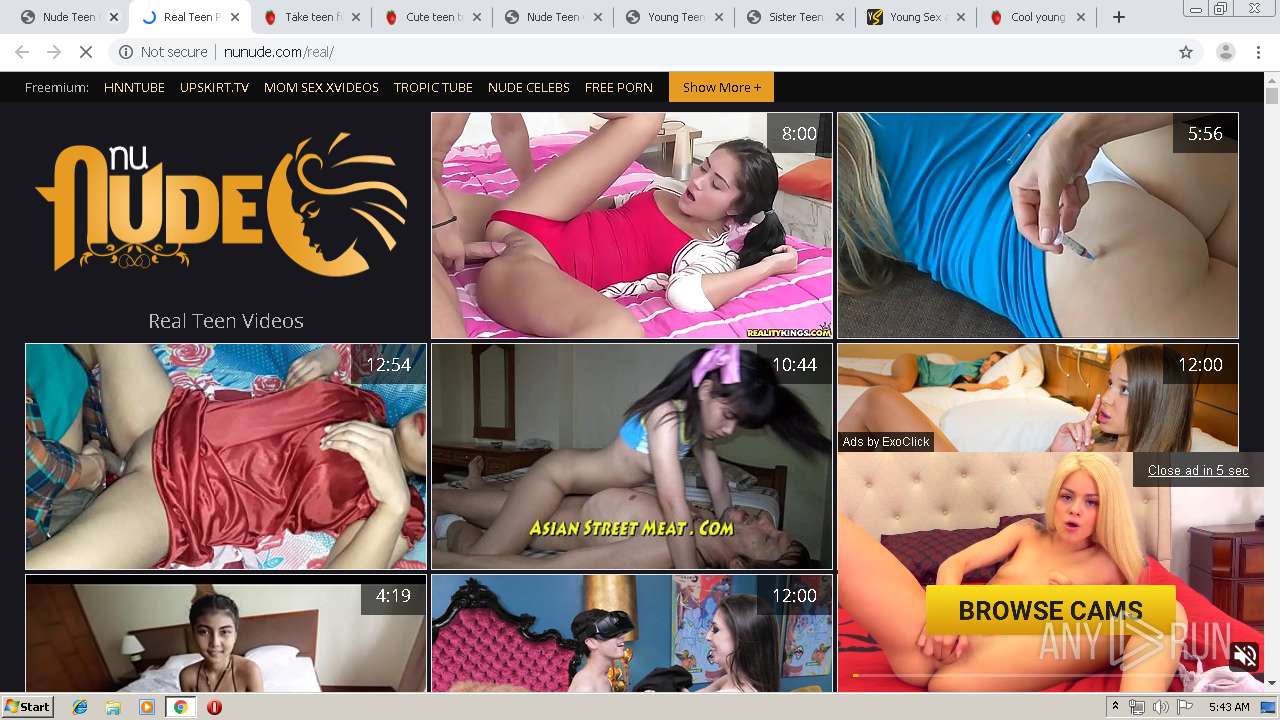
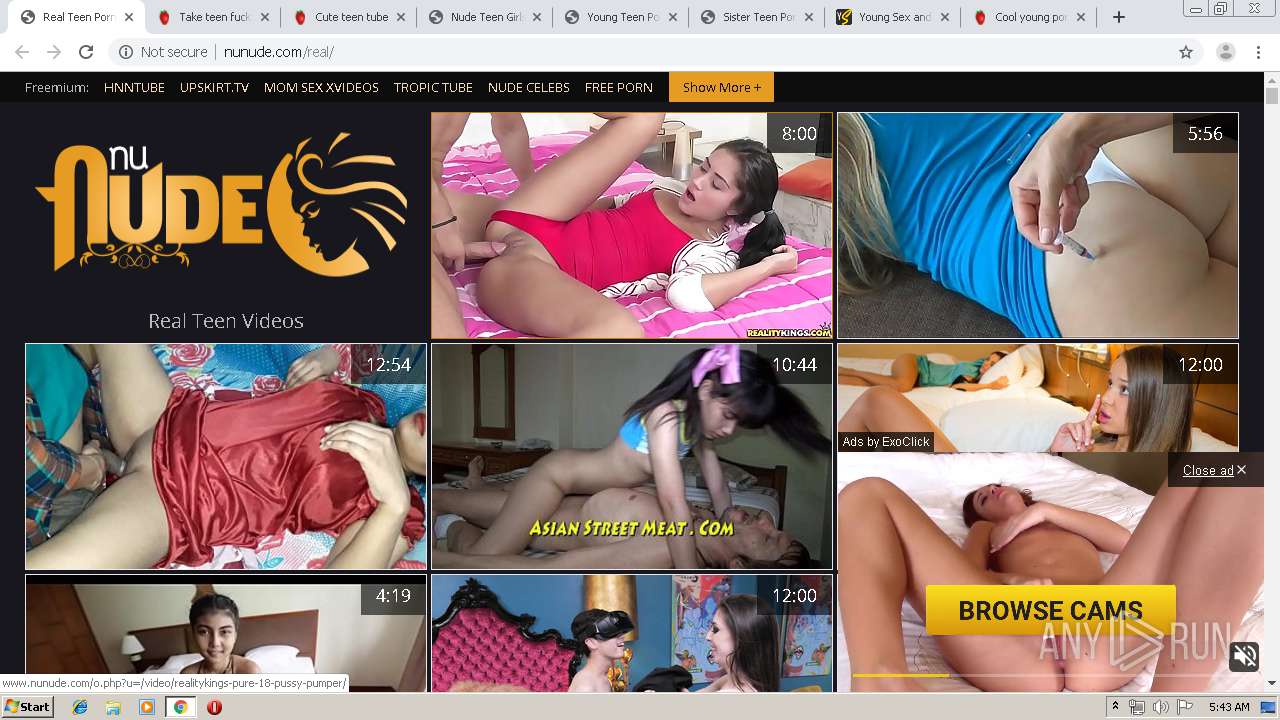
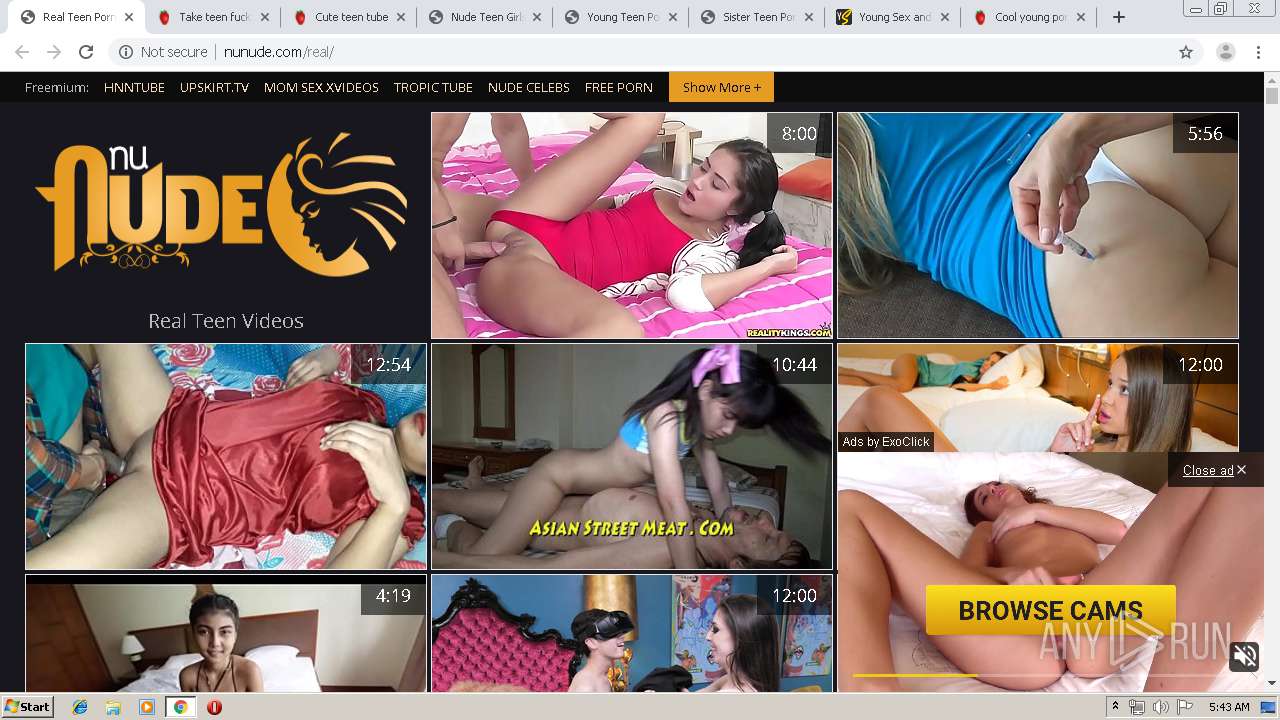
2112 | chrome.exe | GET | 200 | 162.254.191.3:80 | http://nunude.com/taboo/ | US | html | 32.0 Kb | unknown |
2112 | chrome.exe | GET | 200 | 136.243.49.118:80 | http://a.o333o.com/api/spots/98144?p=1 | DE | html | 897 b | suspicious |
2112 | chrome.exe | GET | 200 | 136.243.49.118:80 | http://a.o333o.com/api/spots/98144?p=1 | DE | html | 897 b | suspicious |
2112 | chrome.exe | GET | 200 | 136.243.49.118:80 | http://a.o333o.com/api/spots/98144?p=1 | DE | html | 897 b | suspicious |
2112 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://cdn.o333o.com/asg_embed.js | US | text | 11.9 Kb | suspicious |
2112 | chrome.exe | GET | 200 | 162.254.191.3:80 | http://nunude.com/images/icon.png | US | image | 3.88 Kb | unknown |
2112 | chrome.exe | GET | 200 | 162.254.191.3:80 | http://nunude.com/nunude.png | US | image | 38.2 Kb | unknown |
2112 | chrome.exe | GET | 200 | 136.243.49.118:80 | http://a.o333o.com/api/spots/98144?p=1 | DE | html | 897 b | suspicious |
2112 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://cdn.o333o.com/logo16x16.png | US | image | 583 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2112 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 142.91.159.108:443 | airartapt.site | — | NL | suspicious |
2112 | chrome.exe | 142.91.159.219:443 | apeareand.club | — | NL | suspicious |
2112 | chrome.exe | 213.196.48.68:443 | images.babyboomboomads.com | Servers.com, Inc. | NL | unknown |
2112 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 62.210.24.88:443 | balvalur.com | Online S.a.s. | FR | unknown |
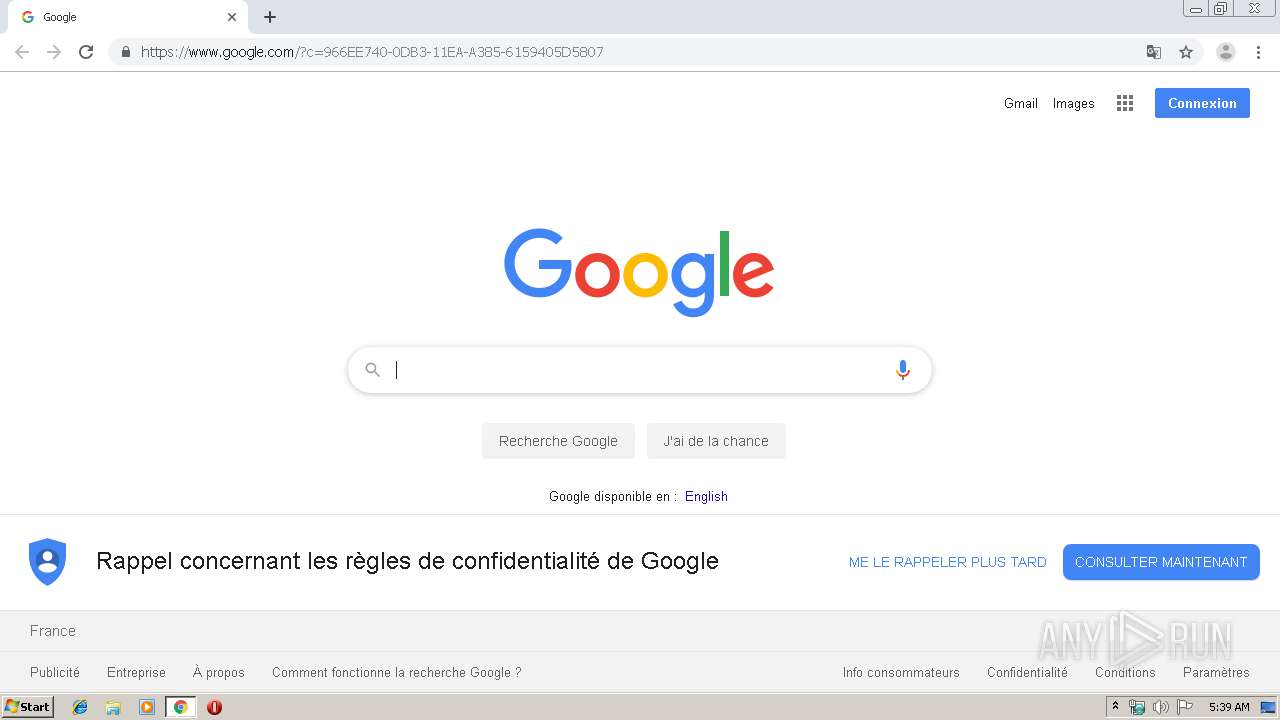
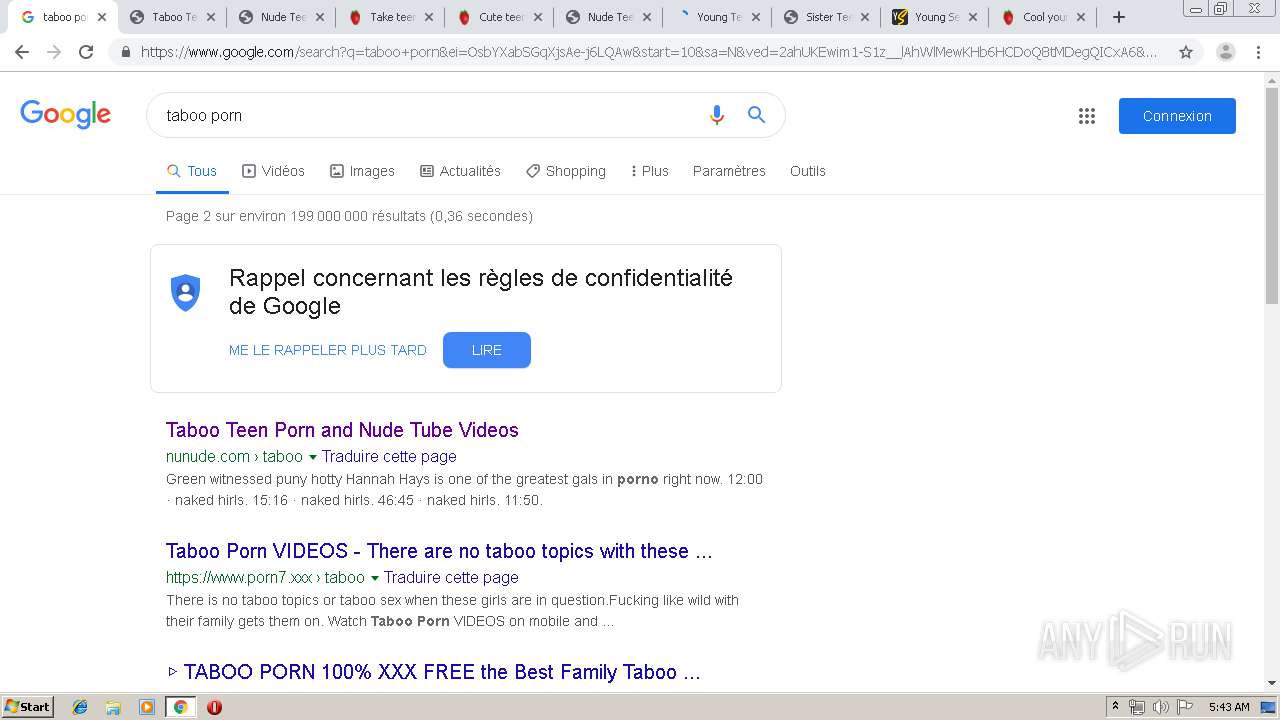
2112 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2112 | chrome.exe | 172.217.22.67:443 | www.google.fr | Google Inc. | US | whitelisted |
2112 | chrome.exe | 216.58.205.238:443 | ogs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
airartapt.site |
| suspicious |
accounts.google.com |
| shared |
apeareand.club |
| suspicious |
fonts.googleapis.com |
| whitelisted |
images.babyboomboomads.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
balvalur.com |
| suspicious |
www.google.com |
| malicious |
android.clients.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2112 | chrome.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |