| File name: | Nitro Tool.exe |
| Full analysis: | https://app.any.run/tasks/c4c1f7a6-1dd0-4482-8bf6-dbbd1cd003db |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 07:17:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 1DB3A28F988EE4747D7C6015A17AD08A |
| SHA1: | 99A6A48D7BE0BD2E8912B29EDEEA9A2486683095 |
| SHA256: | 90A9165F4085C1A3BCE18D0A26304B9A4F2758D803F760D4FFFFBBC5016C1DB3 |
| SSDEEP: | 196608:b0HrHXzCneX38DXDQ9jtbYPvbJQlHHO2SvhAH8CSBfSyVkb+8/LKXY:oHM0MDTQ9jkJQlnPydW |
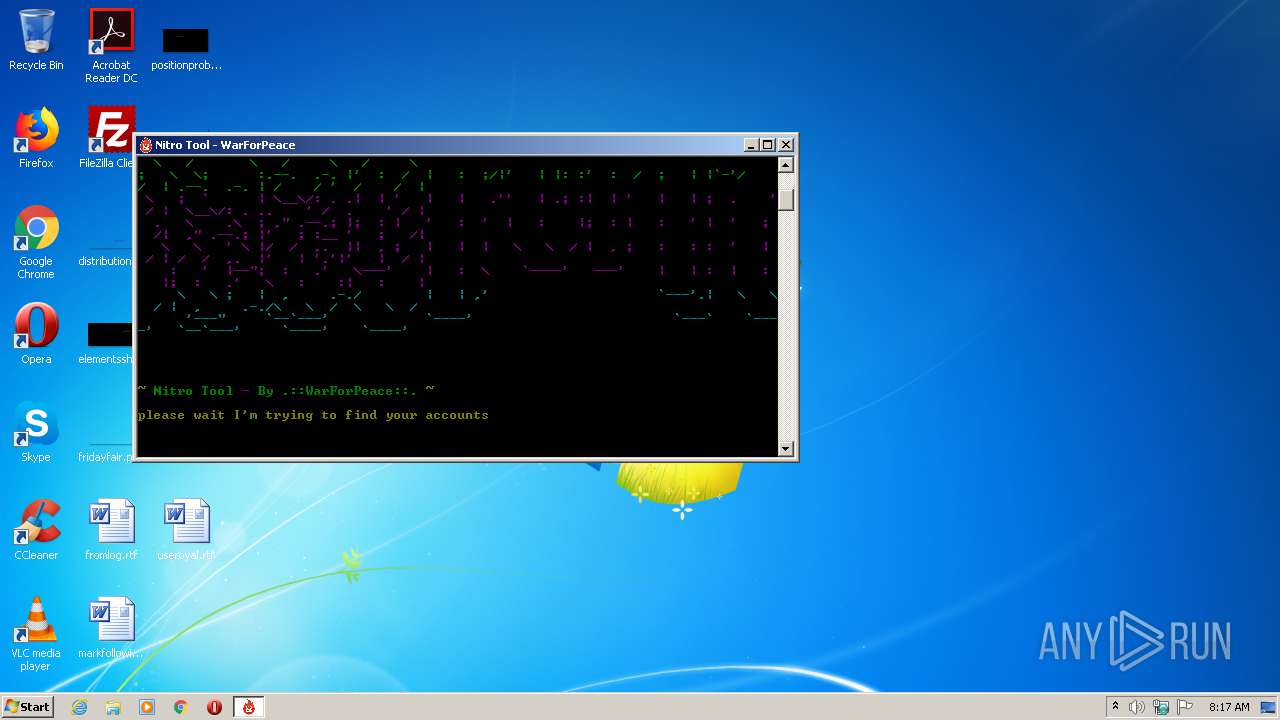
MALICIOUS
Loads dropped or rewritten executable
- Nitro Tool.exe (PID: 2712)
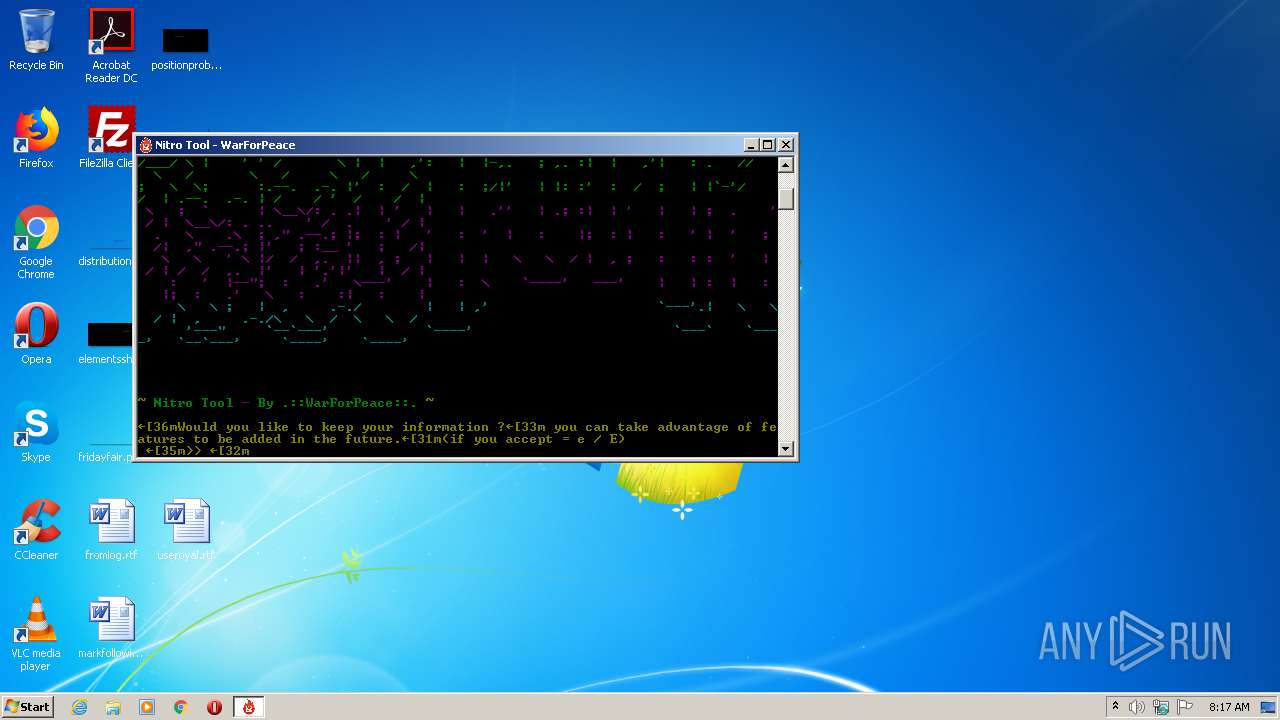
Actions looks like stealing of personal data
- Nitro Tool.exe (PID: 2712)
SUSPICIOUS
Executable content was dropped or overwritten
- Nitro Tool.exe (PID: 964)
Application launched itself
- Nitro Tool.exe (PID: 964)
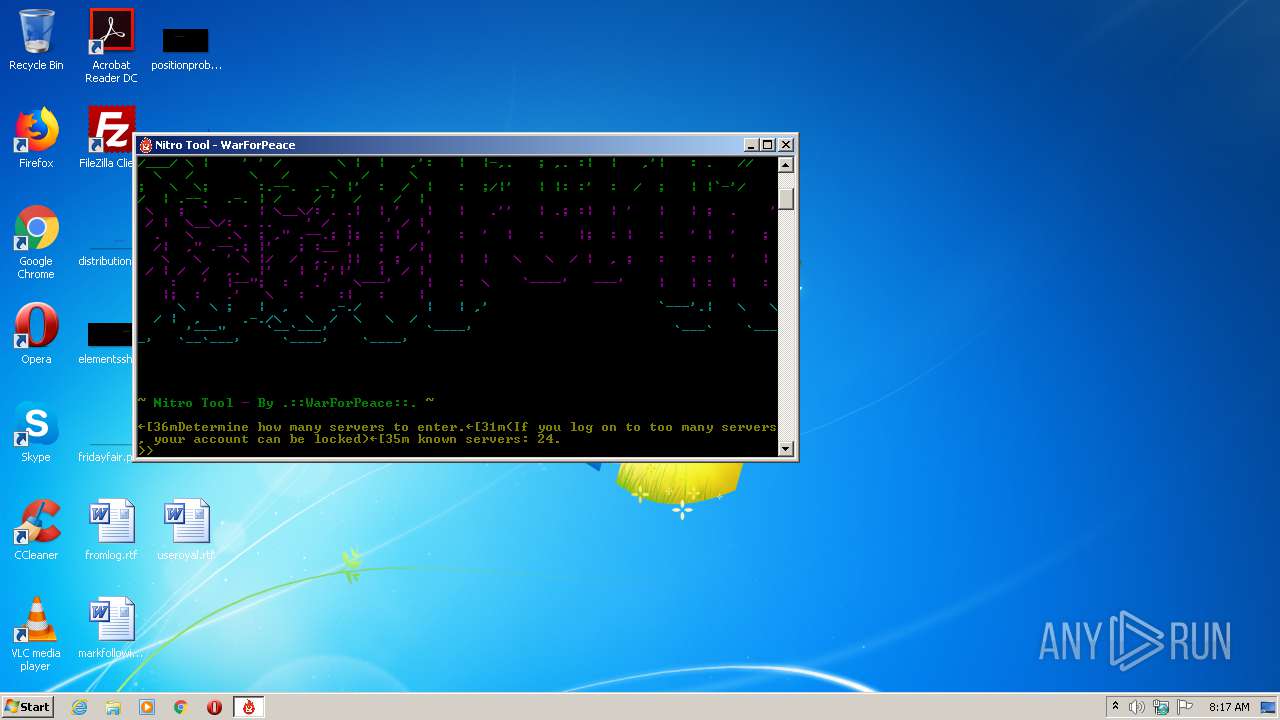
Starts CMD.EXE for commands execution
- Nitro Tool.exe (PID: 2712)
Loads Python modules
- Nitro Tool.exe (PID: 2712)
INFO
Dropped object may contain Bitcoin addresses
- Nitro Tool.exe (PID: 964)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:01:05 13:16:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128512 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x7a6a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 05-Jan-2020 12:16:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 05-Jan-2020 12:16:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F4D4 | 0x0001F600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6643 |
.rdata | 0x00021000 | 0x0000B19E | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.11204 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.93811 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.86299 |
.rsrc | 0x0003D000 | 0x00015344 | 0x00015400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.65336 |
.reloc | 0x00053000 | 0x000017D4 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65456 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 1.51664 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.3041 | 1033 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.05629 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
WS2_32.dll |
Total processes
41
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Nitro Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
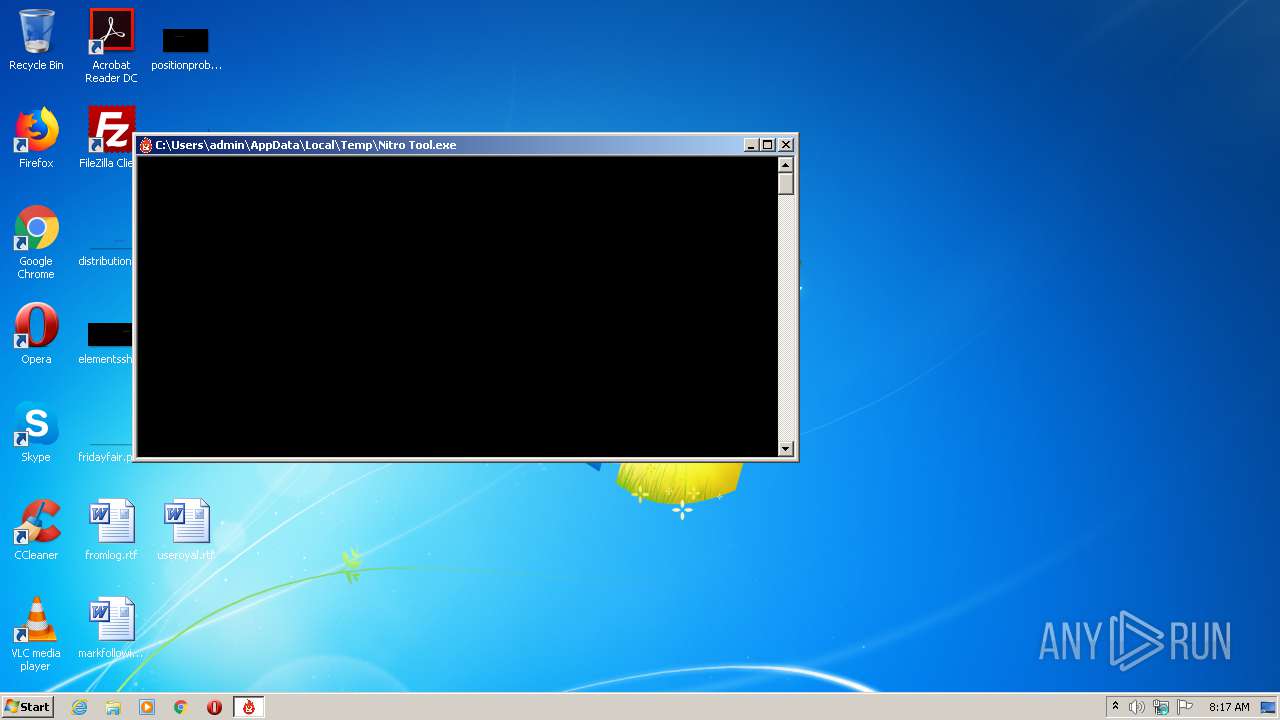
| 964 | "C:\Users\admin\AppData\Local\Temp\Nitro Tool.exe" | C:\Users\admin\AppData\Local\Temp\Nitro Tool.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1380 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Nitro Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2120 | C:\Windows\system32\cmd.exe /c title Nitro Tool - WarForPeace | C:\Windows\system32\cmd.exe | — | Nitro Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2188 | C:\Windows\system32\cmd.exe /c title Nitro Tool - WarForPeace | C:\Windows\system32\cmd.exe | — | Nitro Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2712 | "C:\Users\admin\AppData\Local\Temp\Nitro Tool.exe" | C:\Users\admin\AppData\Local\Temp\Nitro Tool.exe | Nitro Tool.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3488 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | Nitro Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3984 | C:\Windows\system32\cmd.exe /c title Nitro Tool - WarForPeace | C:\Windows\system32\cmd.exe | — | Nitro Tool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
272
Read events
272
Write events
0
Delete events
0
Modification events
Executable files
30
Suspicious files
1
Text files
916
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\Nitro Tool.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_decimal.pyd | executable | |
MD5:8601C853146A4BE85238A57C9FD56865 | SHA256:2A57023D4F355E3857187C02577FA4641A4D1DFF195196B3C33B90322EDF9FD4 | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_hashlib.pyd | executable | |
MD5:05362ADD80824B06014645A7951337D8 | SHA256:20B3A3D3350B3D4D57911ECFDB15F77512A6E73C3BF72B410724F81C79A5B1AF | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_bz2.pyd | executable | |
MD5:0F75C236C4CCFEA1B16F132F6C139236 | SHA256:5DC26DCBF58CC7F5BFDEC0BADD5240D6724DB3E34010AAF35A31876FE4057158 | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\VCRUNTIME140.dll | executable | |
MD5:4C360F78DE1F5BAAA5F110E65FAC94B4 | SHA256:AD1B0992B890BFE88EF52D0A830873ACC0AECC9BD6E4FC22397DBCCF4D2B4E37 | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_queue.pyd | executable | |
MD5:BC5FCE7B8DE6CA765CBF79F9D0587164 | SHA256:A5DB4D041F40FB01761B5BAA907099DB89CF891B0DF0251D92DA2FBF9DC3897B | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_ctypes.pyd | executable | |
MD5:3A2E78784B929003A6BACEEBDB0EFA4D | SHA256:F205948B01B29CB244AE09C5B57FD4B6C8F356DFCD2F8CB49E7CFD177A748CF9 | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_ssl.pyd | executable | |
MD5:B9ECF769FC63A542A113CA1552DC7A7B | SHA256:E0BDB16CFFC7B5A19C5AF22D8A33D3C999D55A3117F2DA07ED3171CA9487927E | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_asyncio.pyd | executable | |
MD5:5435CE08F40FBE43230CAE8D3DFF232C | SHA256:79FDA30CBFC95DB2BA60646FF53DFF45B5ADD57C12241C4A82FA798CB3B543DF | |||
| 964 | Nitro Tool.exe | C:\Users\admin\AppData\Local\Temp\_MEI9642\_sqlite3.pyd | executable | |
MD5:EF20E3DD0FDB3104077A32941B085C83 | SHA256:759C1594FD1E4DFFE604711436F203727184479D6C01A95B752195047995FE33 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2712 | Nitro Tool.exe | 174.129.255.253:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2712 | Nitro Tool.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2712 | Nitro Tool.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
1 ETPRO signatures available at the full report