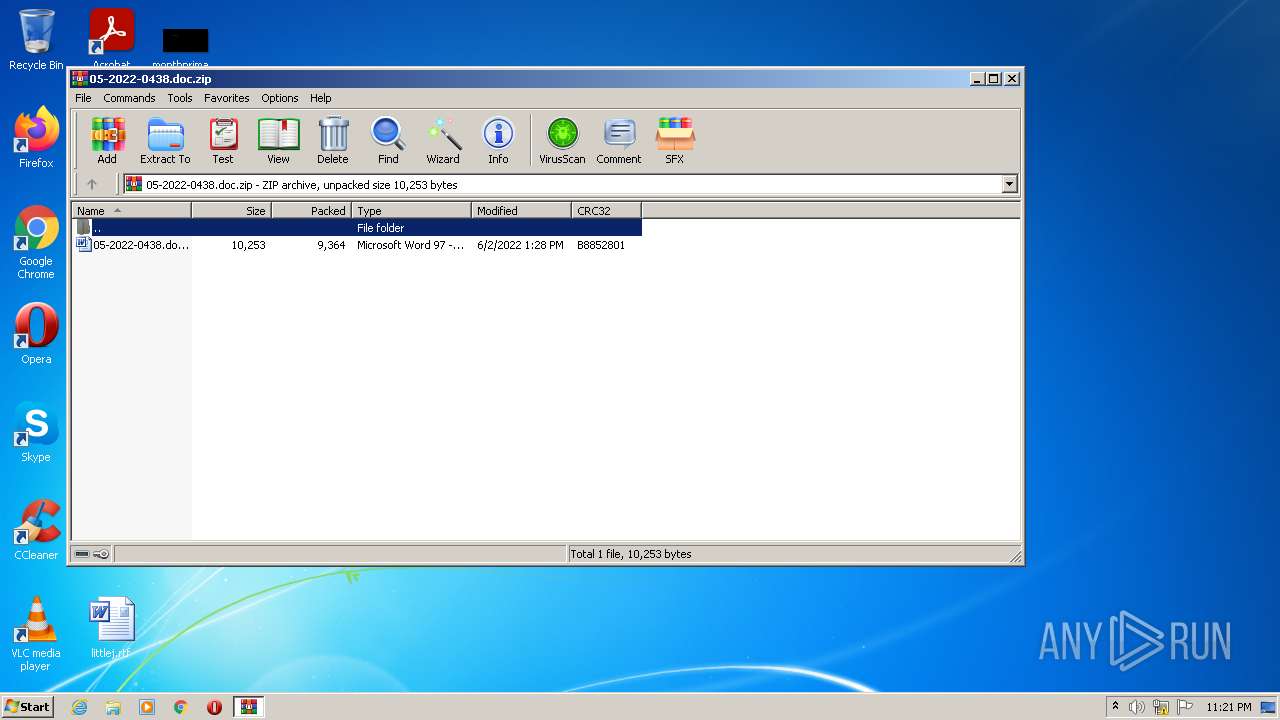
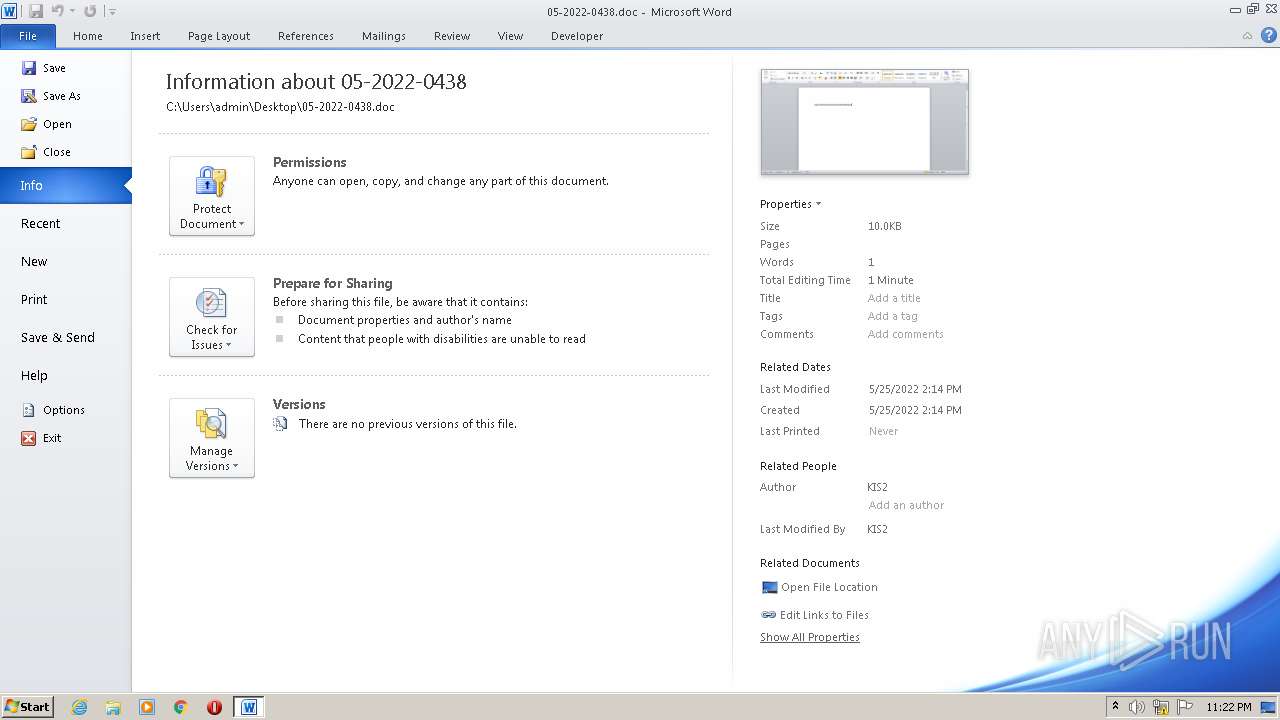
| File name: | 05-2022-0438.doc.zip |
| Full analysis: | https://app.any.run/tasks/bf12c6d0-f4d5-4629-bb47-333732699d60 |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 22:21:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 58A2A7ABF63694E01DEB961166C5663E |
| SHA1: | B22A5B27A8E93C440189E321082D3EB625BC8453 |
| SHA256: | 90A1A94F5F9EFCE66697129BD4267B5E5102EEC7446D51B769882360AE035B19 |
| SSDEEP: | 192:dfbGLkotEJOklSYTlRyZLsQgeWzkSfGeosi/oPCQh8TNxpr1yxw+1UUQ/t:dTGLkCEJOklllRyZLhgFzkSf2H2cr1yW |
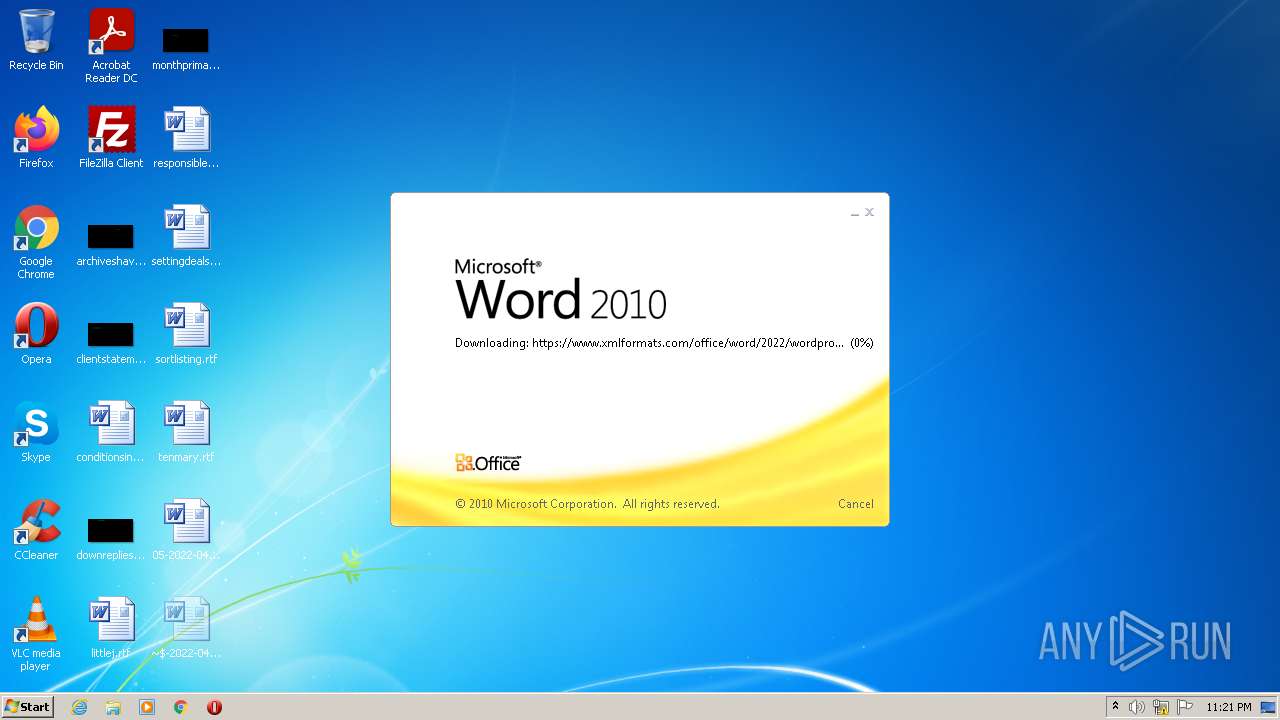
MALICIOUS
CVE-2022-30190 detected
- WINWORD.EXE (PID: 3188)
SUSPICIOUS
Reads default file associations for system extensions
- WinRAR.exe (PID: 1124)
- WINWORD.EXE (PID: 3188)
Reads the computer name
- WinRAR.exe (PID: 1124)
Checks supported languages
- WinRAR.exe (PID: 1124)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3188)
Reads the computer name
- WINWORD.EXE (PID: 3188)
Checks supported languages
- WINWORD.EXE (PID: 3188)
Manual execution by user
- WINWORD.EXE (PID: 3188)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
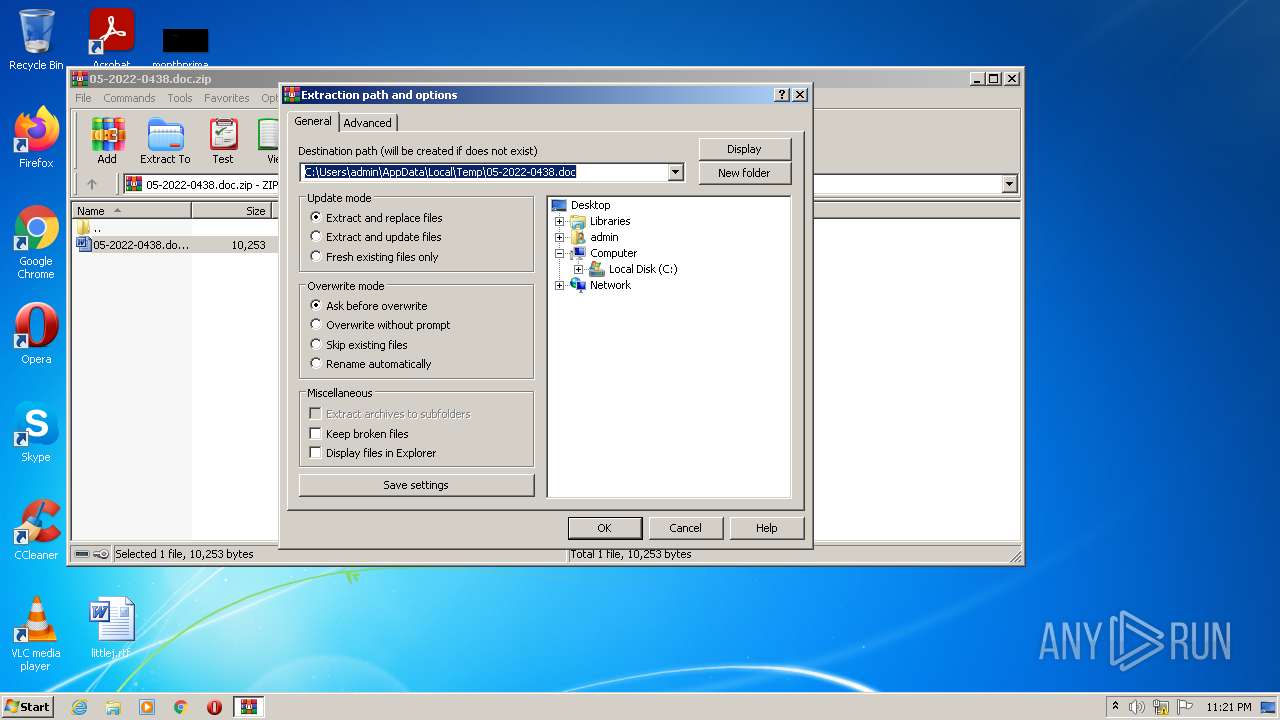
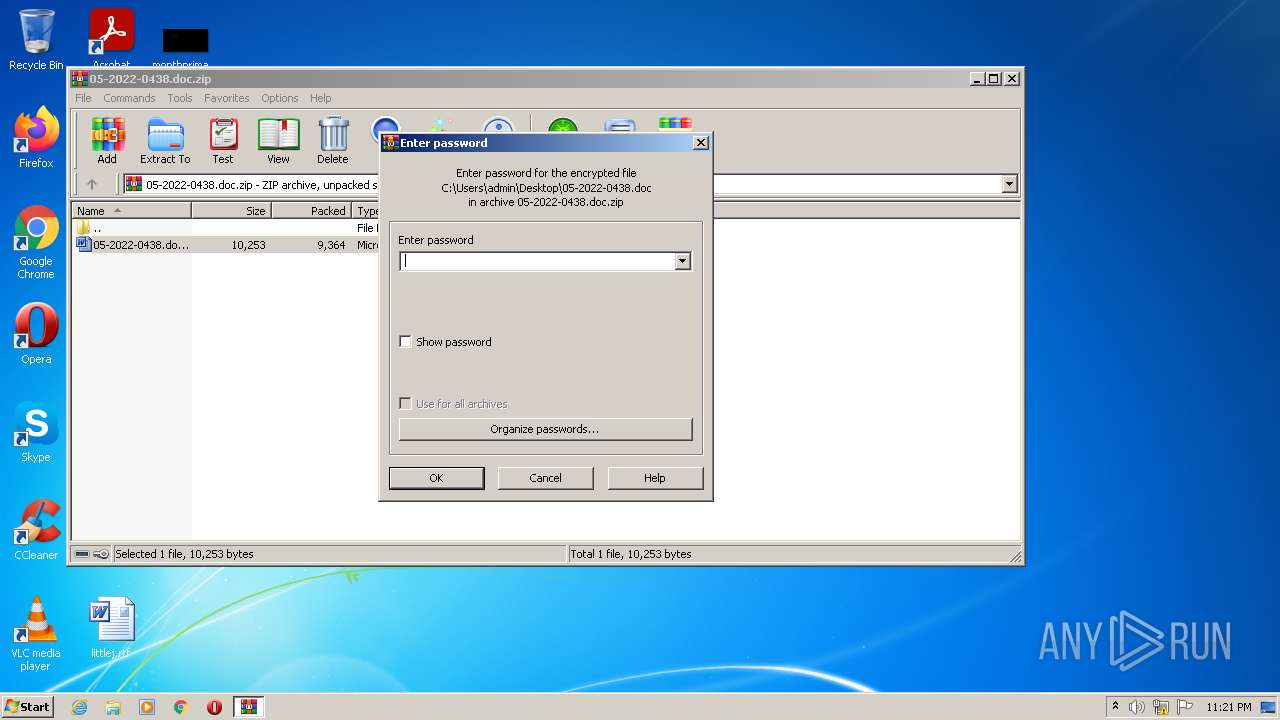
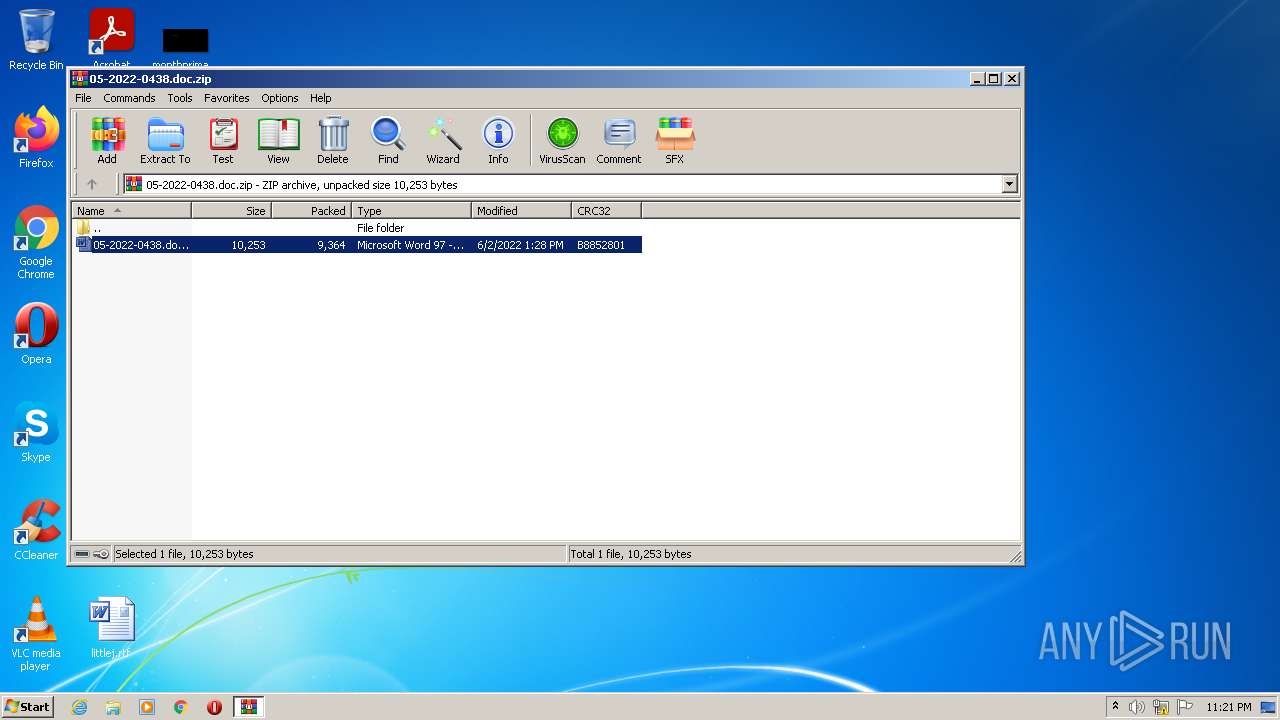
| 1124 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\05-2022-0438.doc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\05-2022-0438.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 748
Read events
3 987
Write events
620
Delete events
141
Modification events
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\05-2022-0438.doc.zip | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1124) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
0
Suspicious files
9
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRF415.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\FSD-{BD7561BF-76BE-4B40-A34D-79A1F8D356F9}.FSD | binary | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\Desktop\~$-2022-0438.doc | pgc | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{08C64D7B-396E-4285-AB68-83B41547F3D0} | binary | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSF-{0E1EEE64-E8C6-4E2A-9759-63CF07FD8988}.FSF | binary | |
MD5:D471A0BB5F0B8A9AC834E0172491B7F9 | SHA256:418B6AE0A39787583DCD77DA0ED040F8C3DDA03410E71D04C235EE6E736F298F | |||
| 1124 | WinRAR.exe | C:\Users\admin\Desktop\05-2022-0438.doc | document | |
MD5:52945AF1DEF85B171870B31FA4782E52 | SHA256:4A24048F81AFBE9FB62E7A6A49ADBD1FAF41F266B5F9FEECDCEB567AEC096784 | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\05-2022-0438.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\14.0\OfficeFileCache\LocalCacheFileEditManager\FSD-CNRY.FSD | binary | |
MD5:— | SHA256:— | |||
| 3188 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\{1C0AE668-5221-41C1-B9EA-5D86A075E0D1} | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.xmlformats.com |
| malicious |