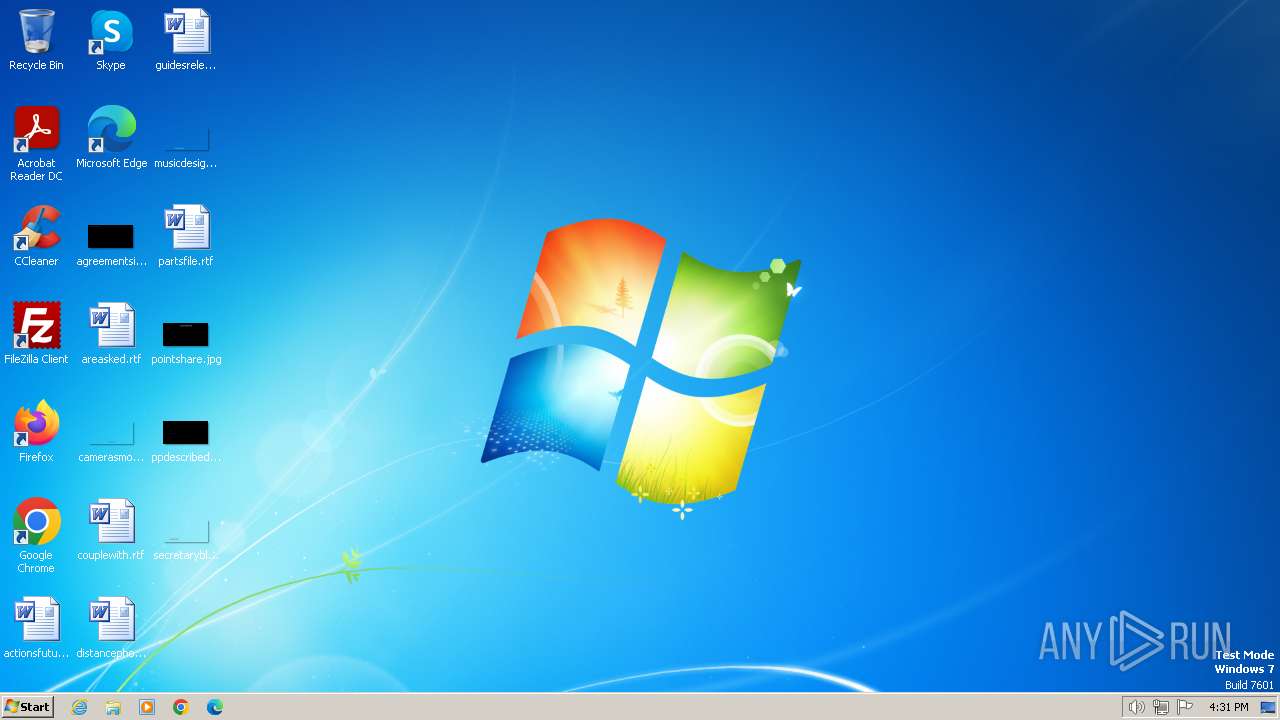
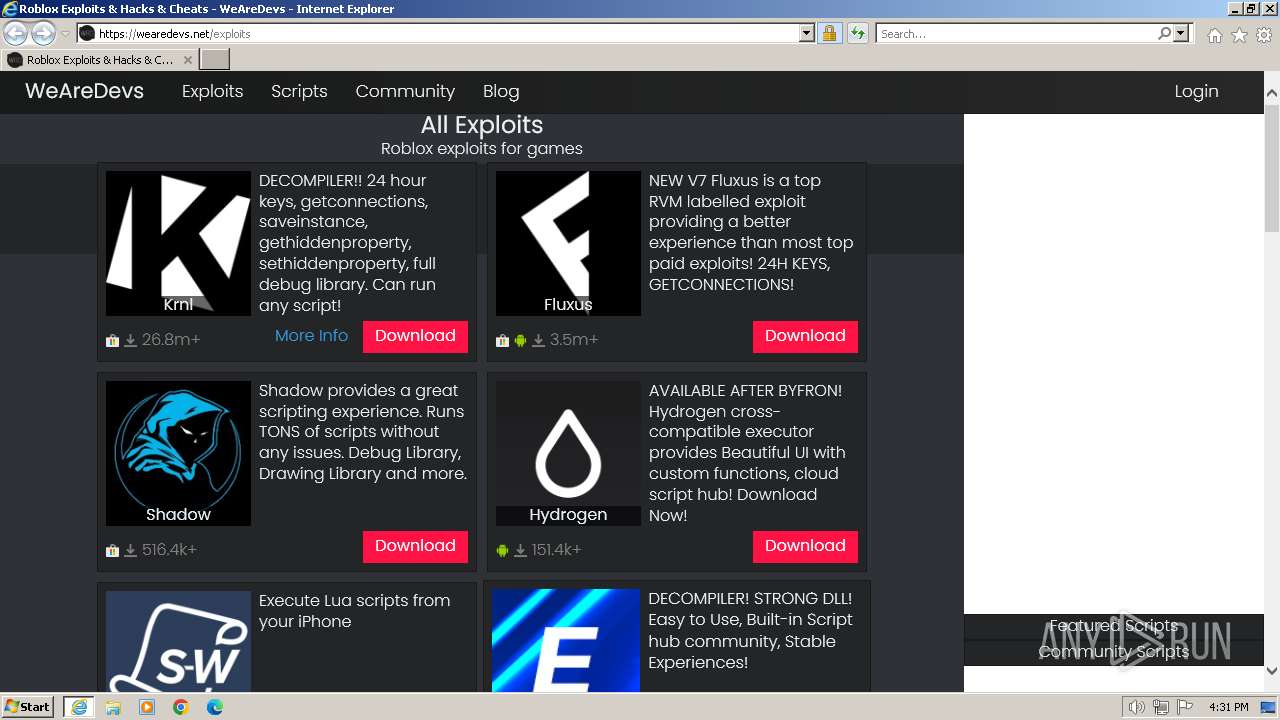
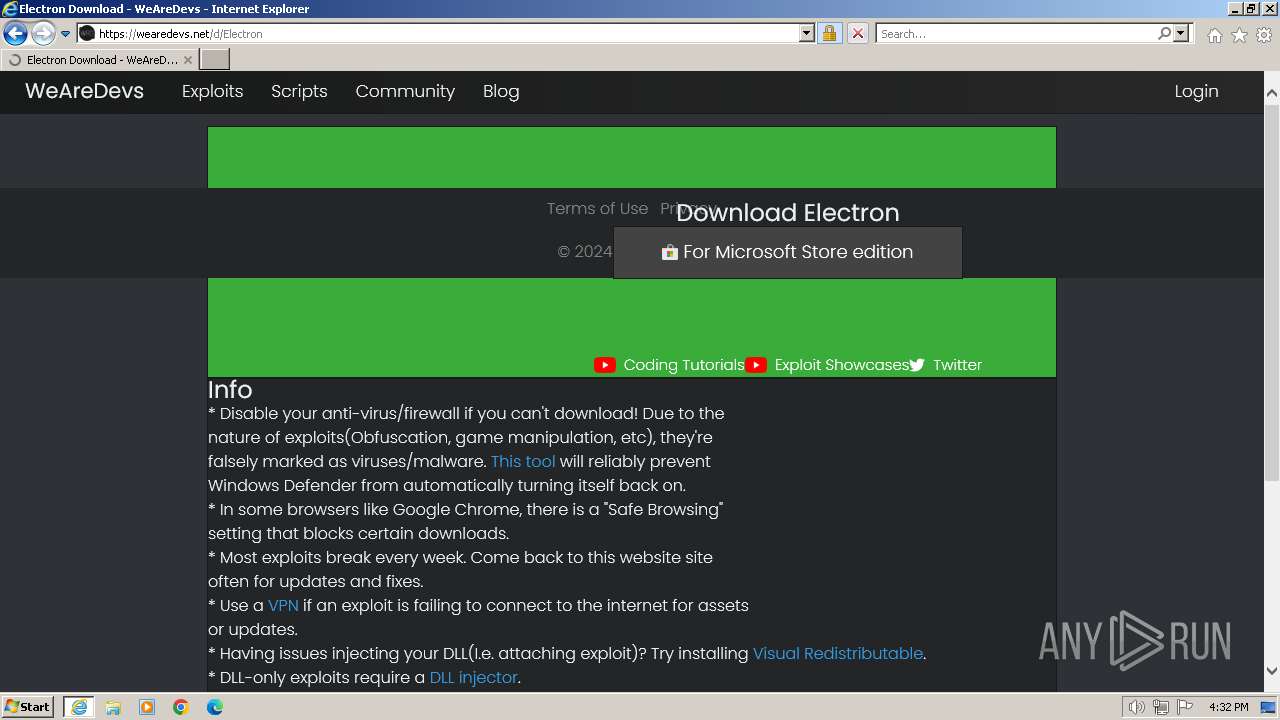
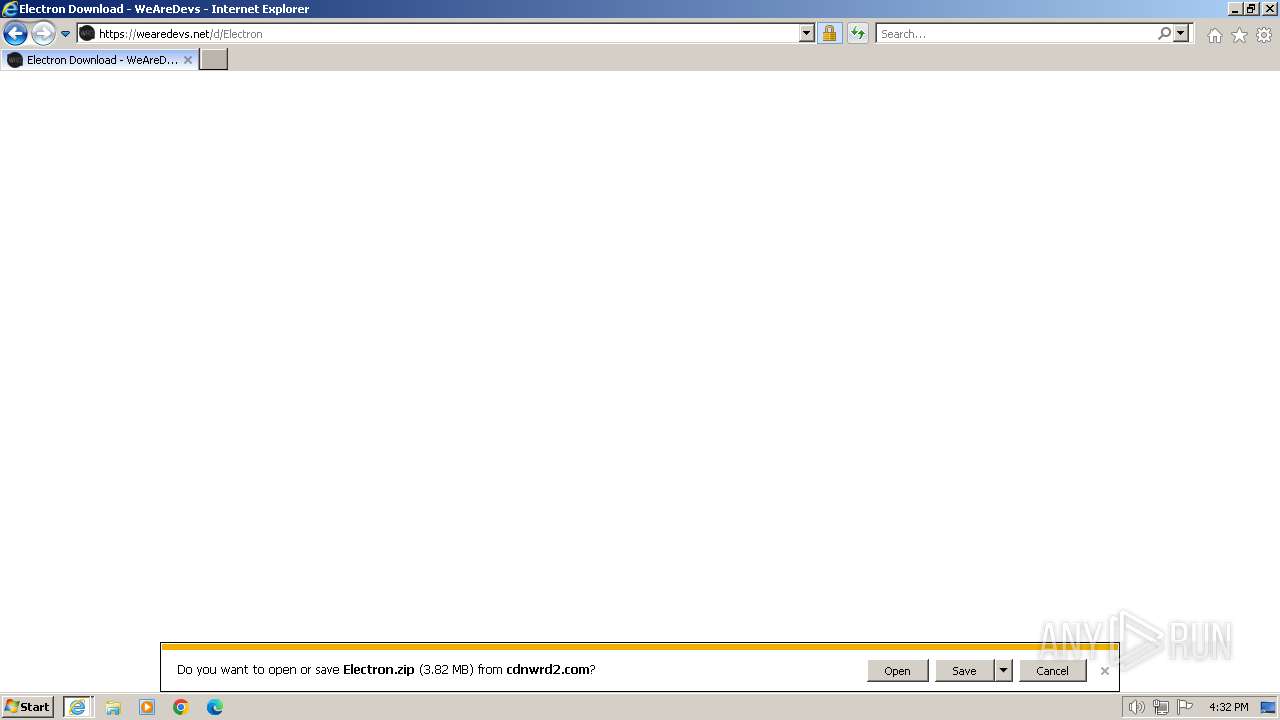
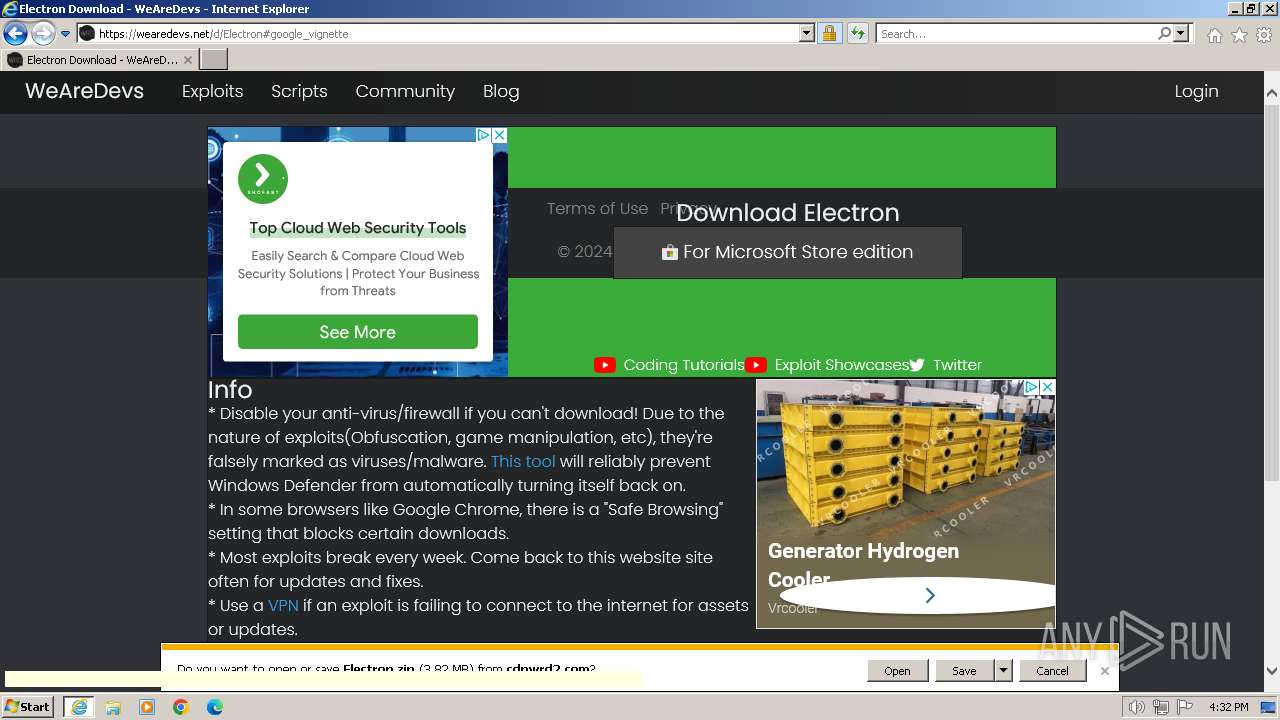
| URL: | www.wearedevs.net |
| Full analysis: | https://app.any.run/tasks/fb1ed74f-bde5-42da-a1a7-584e5bc41f50 |
| Verdict: | Malicious activity |
| Analysis date: | March 06, 2024, 16:31:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 99BA6C53E12C5EDD6C192B396EBD43E8 |
| SHA1: | F5217545A5049B426F4AFBE06BD590690BE74BAE |
| SHA256: | 909D71178124319601C382CDCA5630DA3F84D5FFC9D9A59E8A6075785F391AC5 |
| SSDEEP: | 3:Eepn:vn |
MALICIOUS
Drops the executable file immediately after the start
- Electron.exe (PID: 1544)
SUSPICIOUS
Reads the BIOS version
- Electron.exe (PID: 1544)
Process drops legitimate windows executable
- Electron.exe (PID: 1544)
Executable content was dropped or overwritten
- Electron.exe (PID: 1544)
INFO
Application launched itself
- iexplore.exe (PID: 3656)
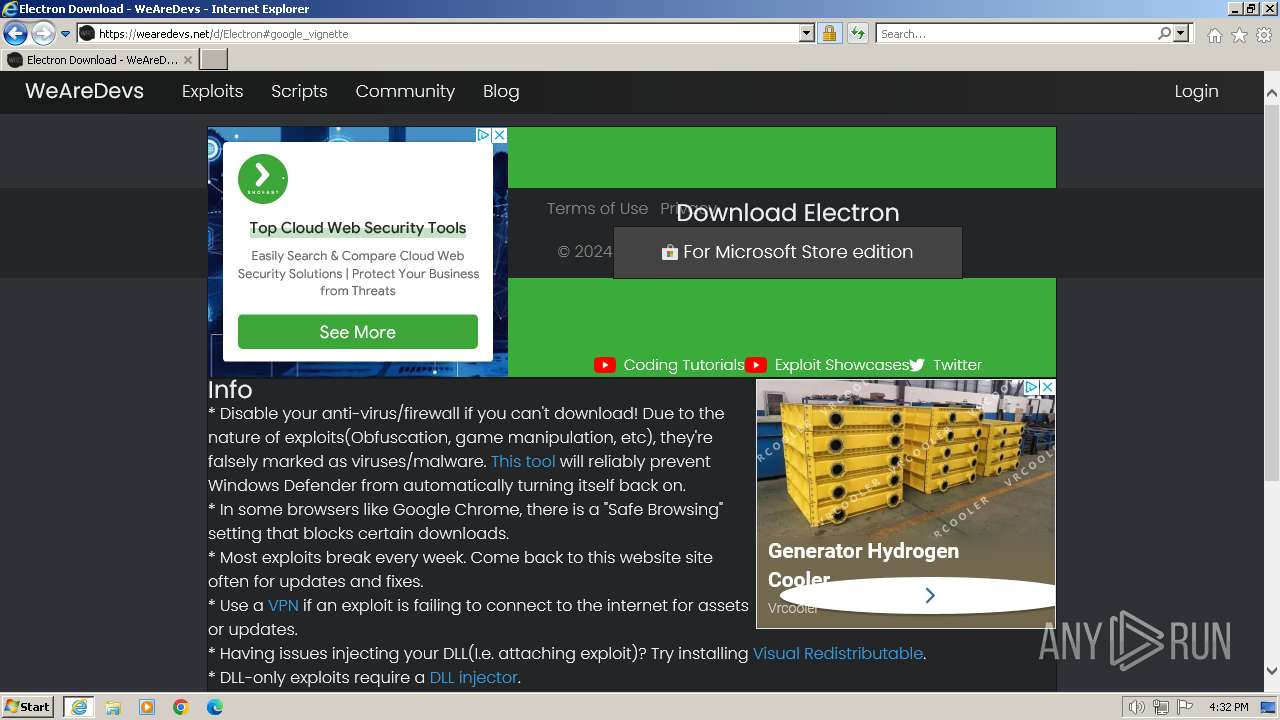
The process uses the downloaded file
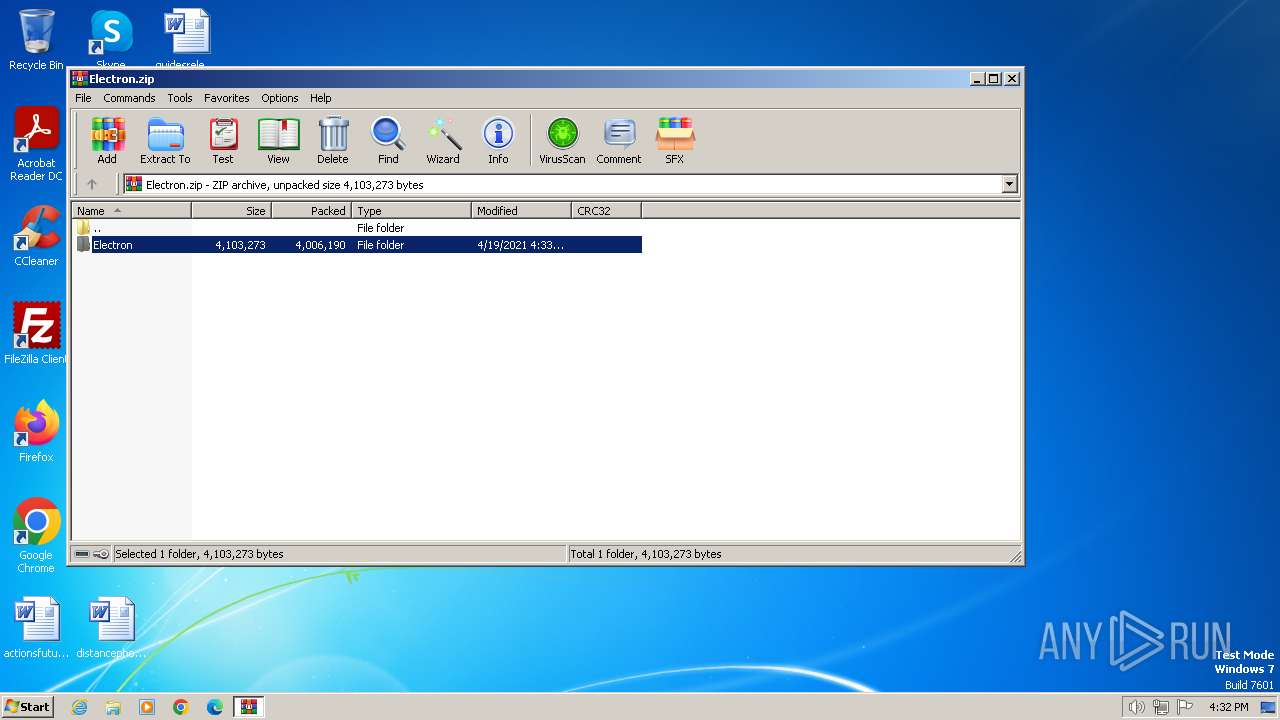
- WinRAR.exe (PID: 1336)
- iexplore.exe (PID: 3656)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 1336)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1336)
Manual execution by a user
- Electron.exe (PID: 3980)
- Electron.exe (PID: 1544)
Checks supported languages
- Electron.exe (PID: 1544)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3656)
Process checks whether UAC notifications are on
- Electron.exe (PID: 1544)
Reads the machine GUID from the registry
- Electron.exe (PID: 1544)
Reads the computer name
- Electron.exe (PID: 1544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
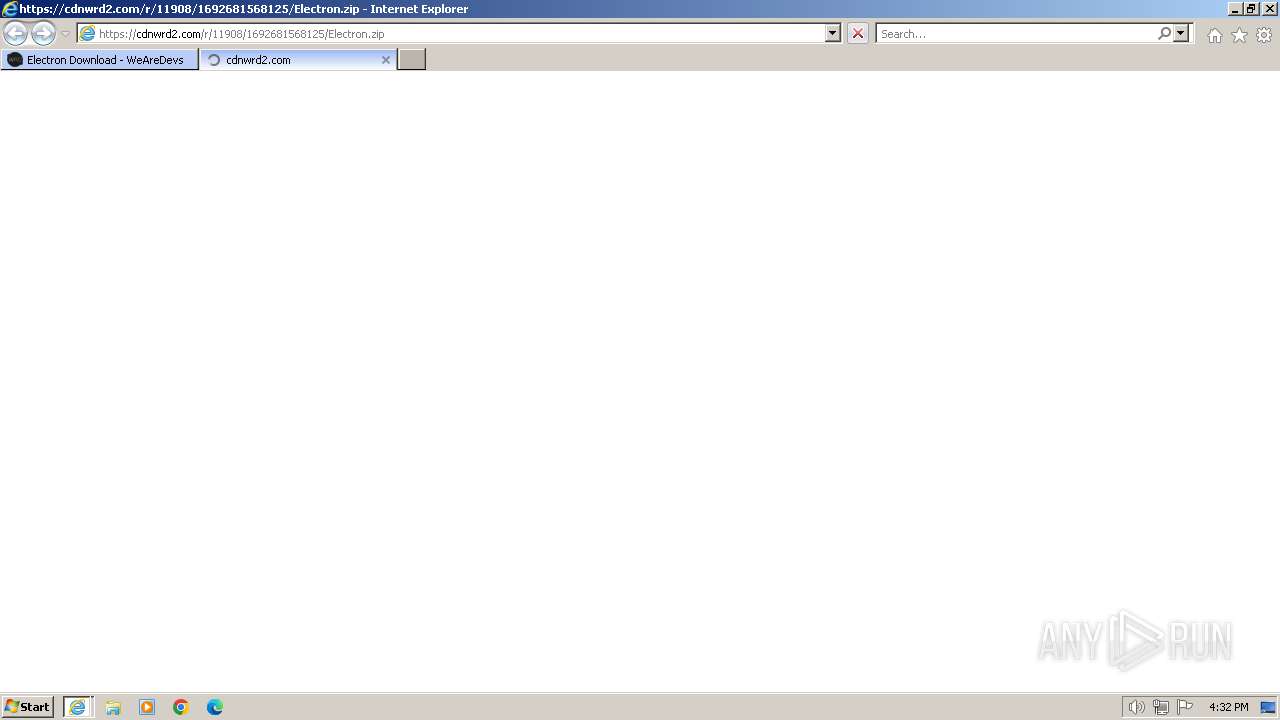
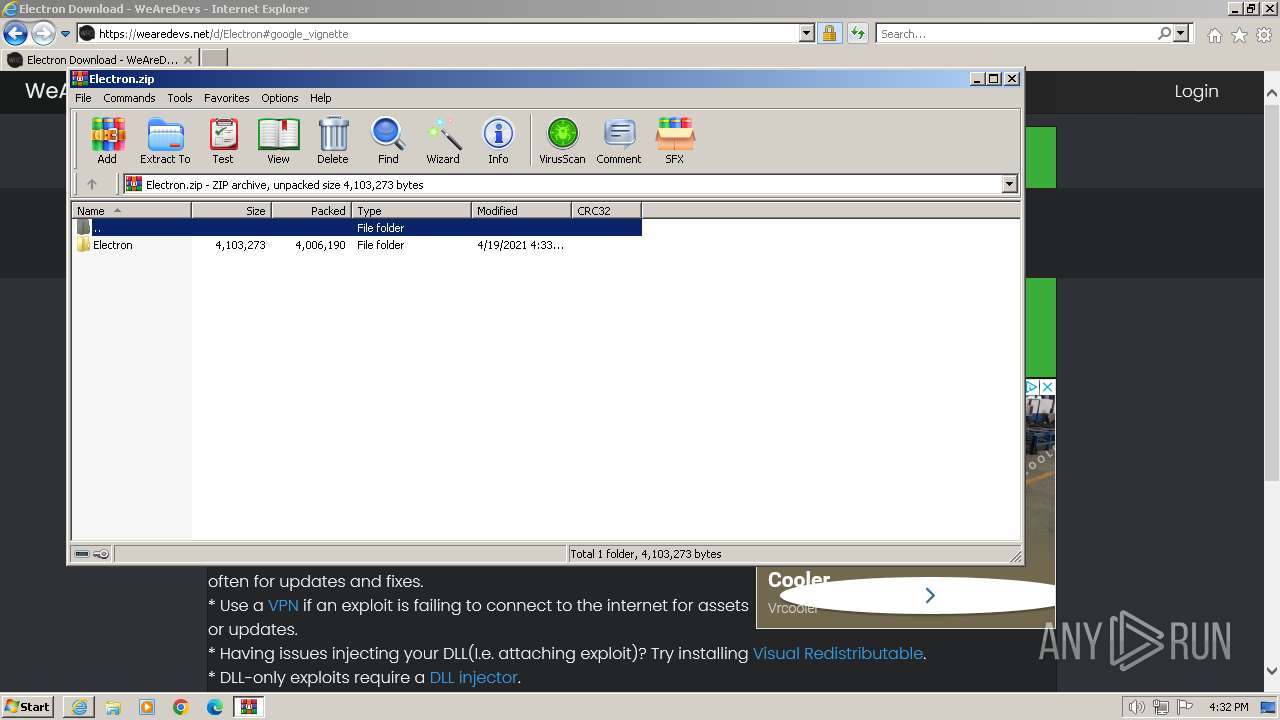
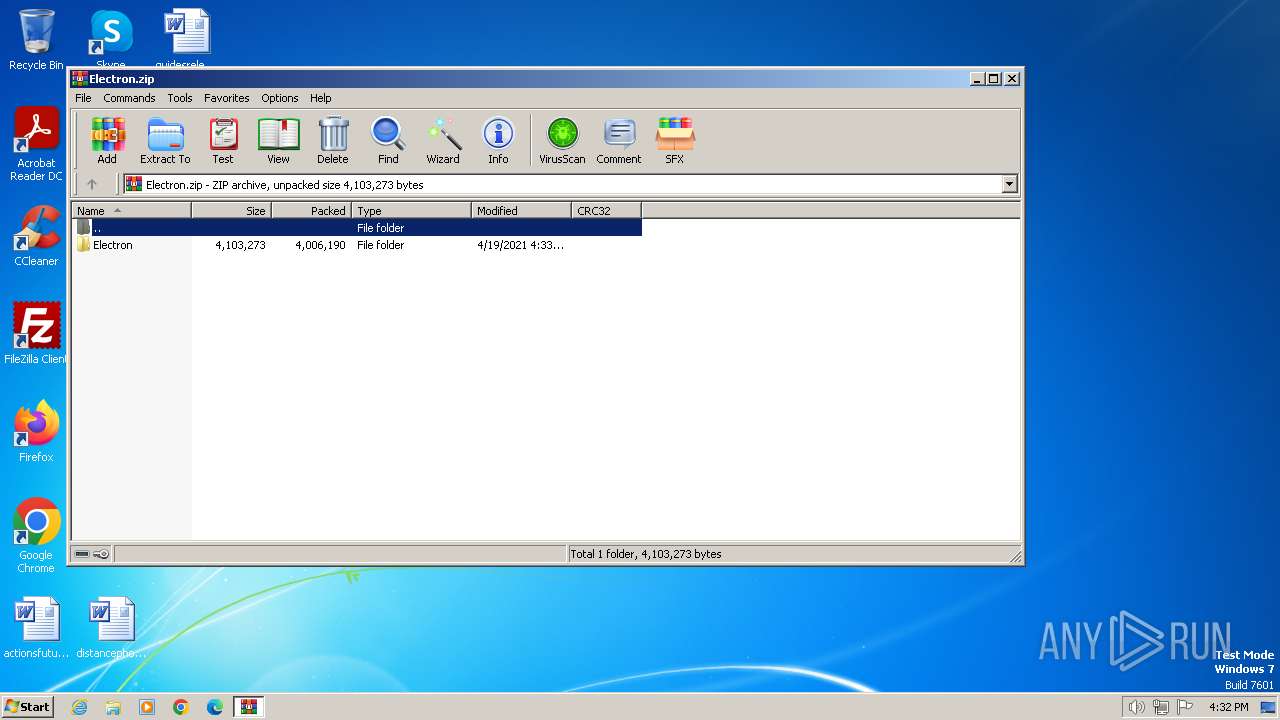
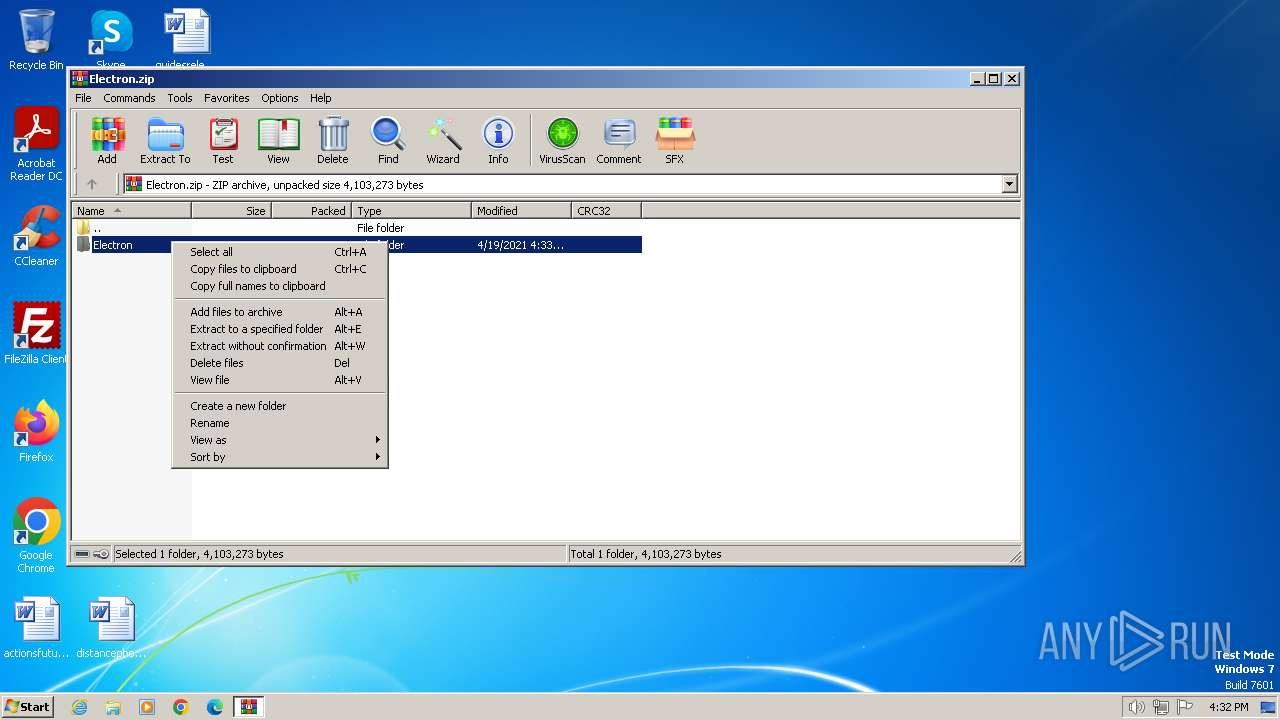
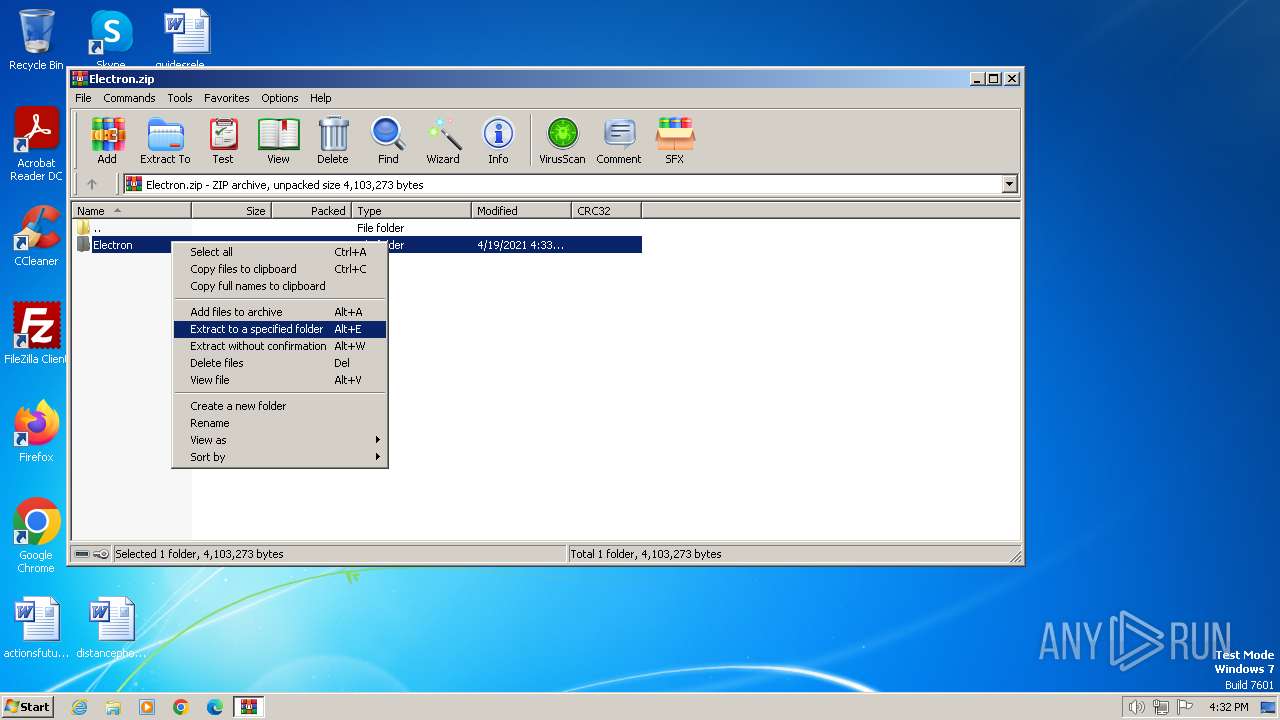
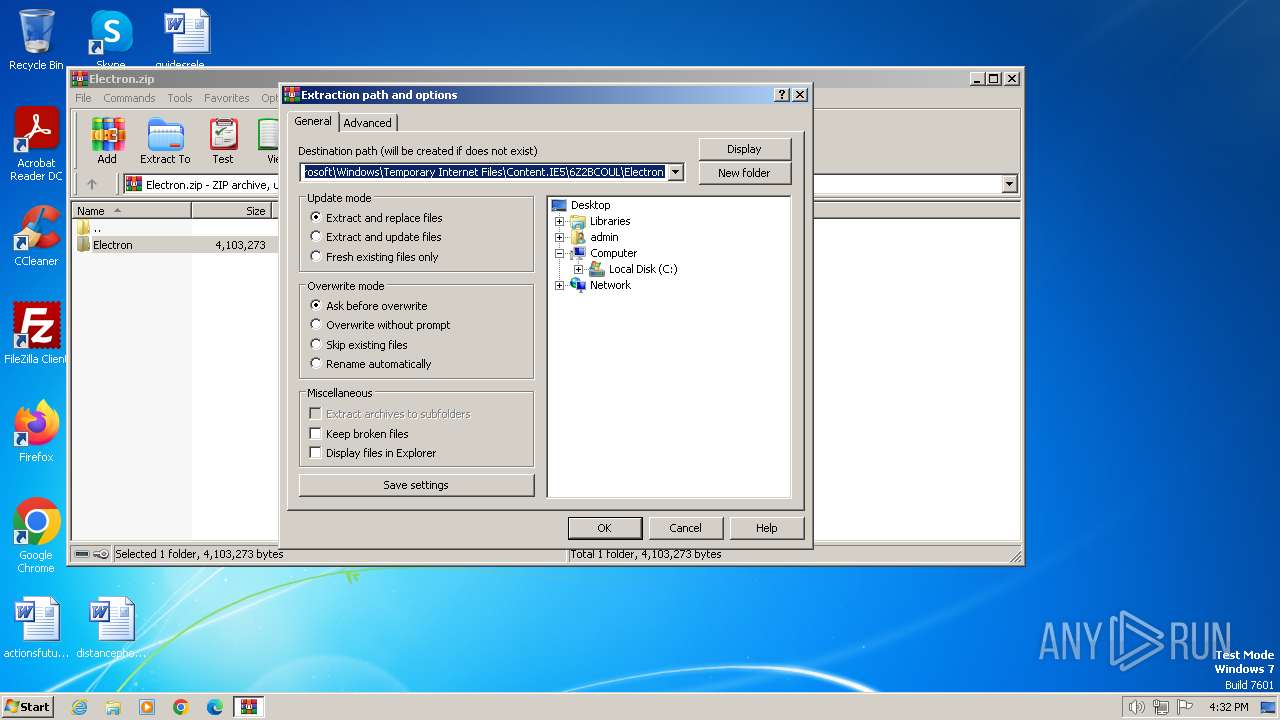
| 1336 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Electron.zip" | C:\Program Files\WinRAR\WinRAR.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
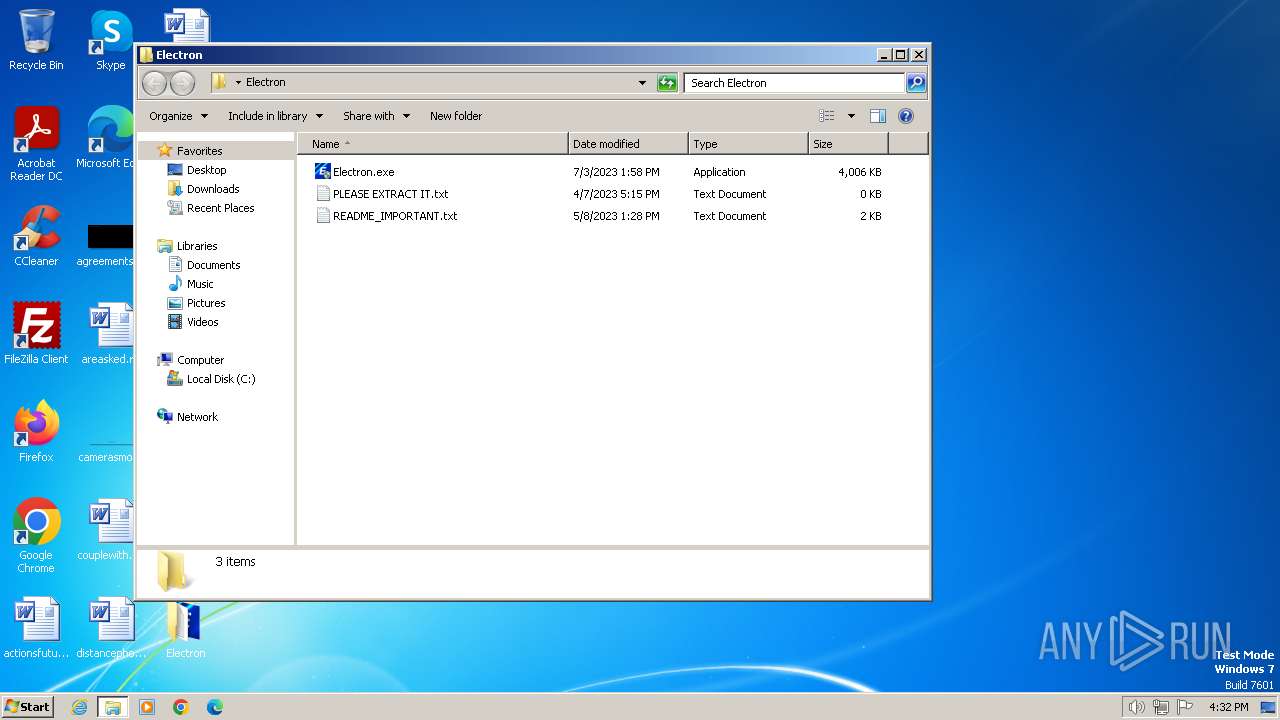
| 1544 | "C:\Users\admin\Desktop\Electron\Electron.exe" | C:\Users\admin\Desktop\Electron\Electron.exe | explorer.exe | ||||||||||||
User: admin Company: ryos.lol Integrity Level: HIGH Description: Electron Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3656 CREDAT:1381644 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
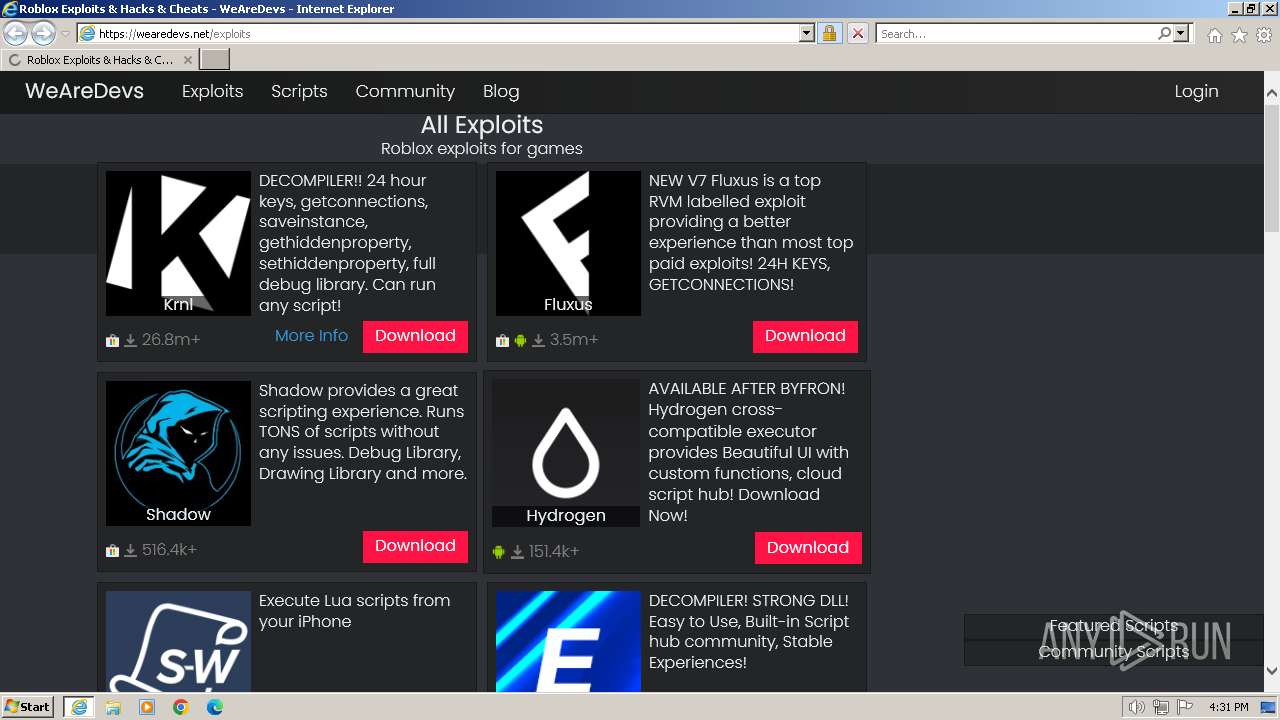
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" "www.wearedevs.net" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3664 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3656 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3980 | "C:\Users\admin\Desktop\Electron\Electron.exe" | C:\Users\admin\Desktop\Electron\Electron.exe | — | explorer.exe | |||||||||||
User: admin Company: ryos.lol Integrity Level: MEDIUM Description: Electron Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
44 832
Read events
44 600
Write events
178
Delete events
54
Modification events
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31092707 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31092707 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3656) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
4
Suspicious files
68
Text files
180
Unknown types
29
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarCCD.tmp | cat | |
MD5:DD73CEAD4B93366CF3465C8CD32E2796 | SHA256:A6752B7851B591550E4625B832A393AABCC428DE18D83E8593CD540F7D7CAE22 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\exploits[1].htm | html | |
MD5:9DD4C6CB21BE1B871409222CA2ACF90C | SHA256:156D67E8BB91760ADA91E647E3D7C7A69A299D988718256D1300B24CEDA9E4EC | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\timestamp[1].js | text | |
MD5:F56E6252B1A797488376F3C46D8AE6EF | SHA256:3619C1468E207E66EC8D47FC1A4776C27A20F383CF28F5650F594A026F12DA79 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\navheader[1].css | text | |
MD5:7395C3382BA806D2EF0C9F2AEB2B4AC5 | SHA256:75560503D03353E0880B93C71003172DF0E184C0ED8F6C28EF0C1B1D91119AA2 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\exploits[1].css | text | |
MD5:909FC52951BB8B15B38136D3B26CFF08 | SHA256:1C1B6E4B27D808F7066CBB717DB875098E2E05A94FF82D7FBB05105FCBCA3292 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarCEE.tmp | cat | |
MD5:DD73CEAD4B93366CF3465C8CD32E2796 | SHA256:A6752B7851B591550E4625B832A393AABCC428DE18D83E8593CD540F7D7CAE22 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\dM3ipLu7q0SolgbDApkhduCYXKU[1].js | text | |
MD5:E25AA44CE193238EB43038178EEE15F0 | SHA256:E041697F6DCA33396CA095C8CDFC6BE764176CF4950EE907A299C5E60463425C | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:235E88577B81833601F0F56FDE2B77C7 | SHA256:D02E4CA41AF2462B167B9EC2588B5DF3A6FD4EE323E64BAA2A47E16AEF1D2409 | |||
| 3664 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabCED.tmp | compressed | |
MD5:753DF6889FD7410A2E9FE333DA83A429 | SHA256:B42DC237E44CBC9A43400E7D3F9CBD406DBDEFD62BFE87328F8663897D69DF78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
107
DNS requests
43
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3664 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | binary | 724 b | unknown |
3664 | iexplore.exe | GET | 301 | 104.26.6.147:80 | http://www.wearedevs.net/ | US | — | — | unknown |
3664 | iexplore.exe | GET | 304 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | DE | — | — | unknown |
3664 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCimReIRyQtphKmdTNhBzaE | US | binary | 472 b | unknown |
3664 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEmjnEcAcBIRCdkf7NhadAI%3D | US | binary | 471 b | unknown |
3664 | iexplore.exe | GET | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGHsycmQas7CCZXEOfu%2B%2Bqs%3D | US | binary | 471 b | unknown |
3656 | iexplore.exe | GET | 304 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?aeb32cb922858c96 | DE | — | — | unknown |
3656 | iexplore.exe | GET | 304 | 184.24.77.194:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f5b4526b422520f4 | DE | — | — | unknown |
3664 | iexplore.exe | GET | 200 | 72.246.169.163:80 | http://x2.c.lencr.org/ | DE | binary | 299 b | unknown |
3664 | iexplore.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | DE | binary | 717 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | unknown |
3664 | iexplore.exe | 104.26.6.147:80 | www.wearedevs.net | CLOUDFLARENET | US | unknown |
3664 | iexplore.exe | 104.26.7.147:443 | www.wearedevs.net | CLOUDFLARENET | US | unknown |
3664 | iexplore.exe | 184.24.77.194:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3664 | iexplore.exe | 184.24.77.202:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3664 | iexplore.exe | 72.246.169.163:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
3664 | iexplore.exe | 142.250.185.226:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
3664 | iexplore.exe | 172.67.71.2:443 | www.wearedevs.net | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.wearedevs.net |
| unknown |
wearedevs.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
x2.c.lencr.org |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdn.wearedevs.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |