| File name: | dobrota clean.exe |
| Full analysis: | https://app.any.run/tasks/b9b623e3-c391-4a49-af74-f6daaec3b094 |
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2025, 18:03:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | C8B999419A3C103270290E99189F794C |
| SHA1: | 90148745B61D2C77C1694E43F11FAAA9A3D05A0A |
| SHA256: | 9093FF3BC7E78CFE84CADC3A993EEB1C15CE497E94EFDCF51C1ADCAFD0AEDF18 |
| SSDEEP: | 98304:sAY5AuJzlAnj/6rrQ97TKf2Ssk9530HEPungyEVxfEHCDoGrYRQWwIRcahreRWhk:LaqG/vRePgOu |
MALICIOUS
GENERIC has been found (auto)
- dobrota clean.exe (PID: 6944)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 7332)
SUSPICIOUS
Executable content was dropped or overwritten
- dobrota clean.exe (PID: 6944)
Reads security settings of Internet Explorer
- dobrota clean.exe (PID: 6944)
Executing commands from a ".bat" file
- dobrota clean.exe (PID: 6944)
Starts CMD.EXE for commands execution
- dobrota clean.exe (PID: 6944)
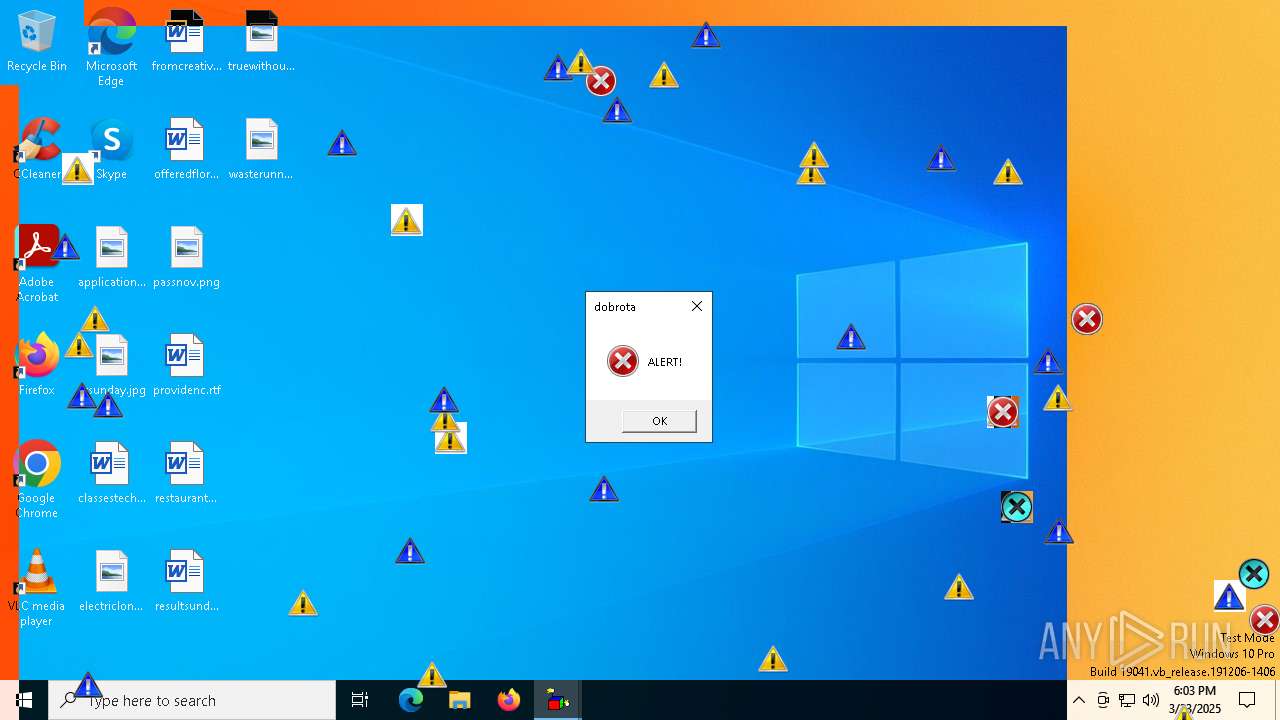
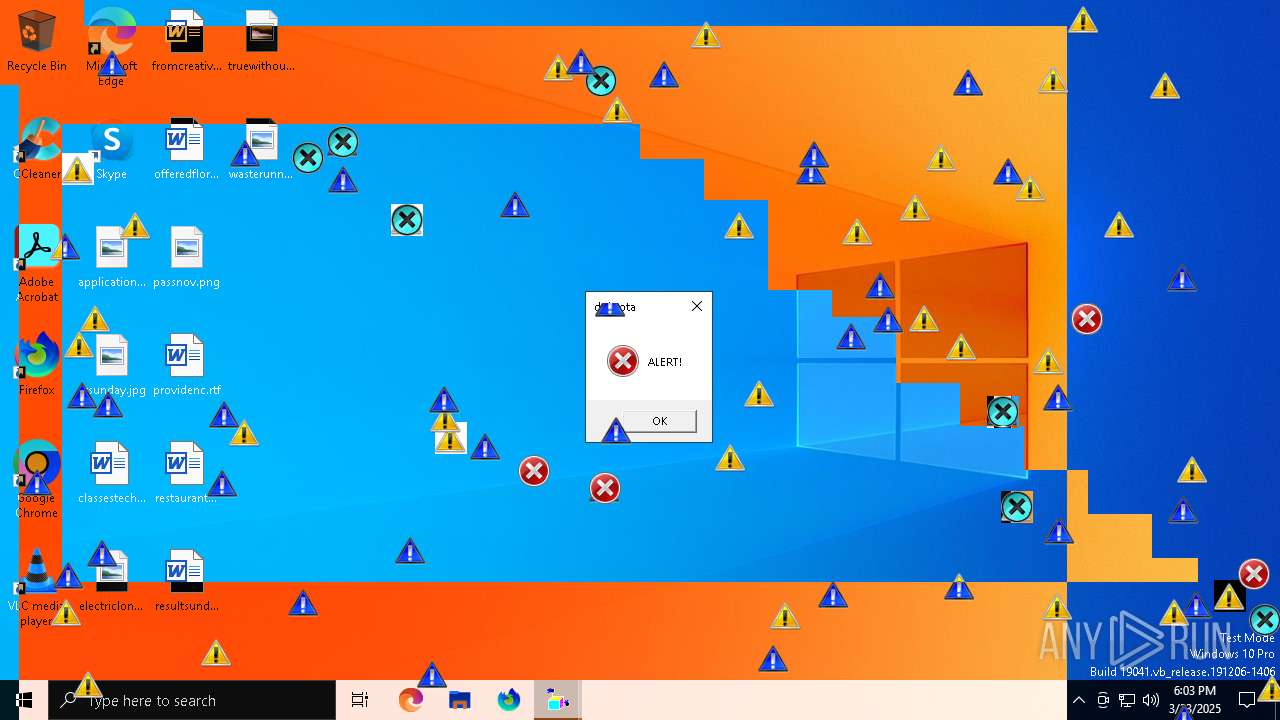
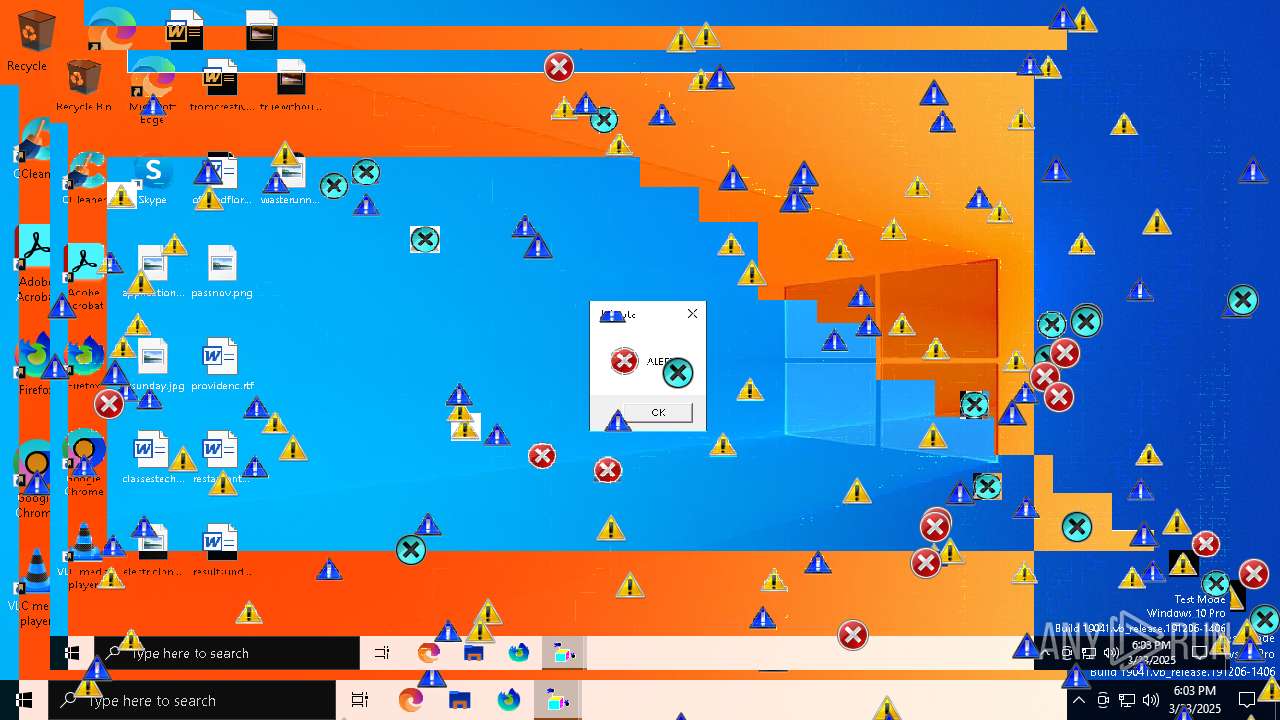
The executable file from the user directory is run by the CMD process
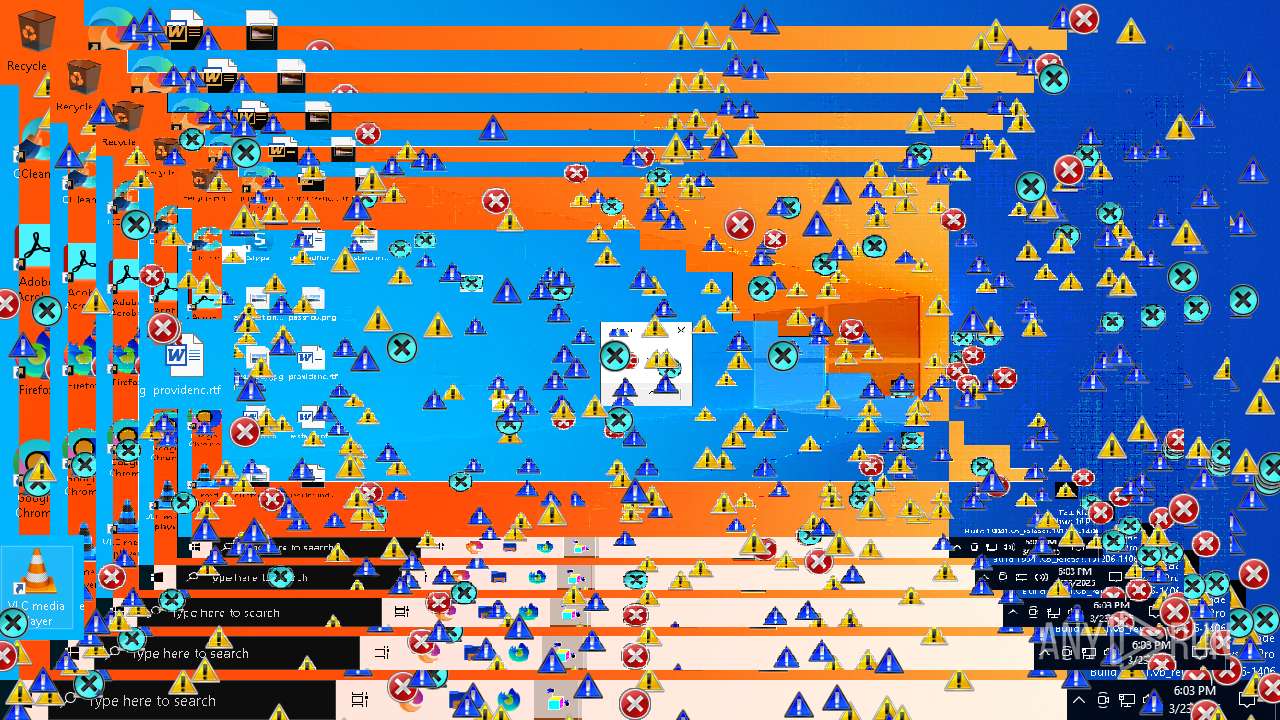
- erroricons.exe (PID: 7340)
- INVERS.exe (PID: 7360)
- crazywarningicons.exe (PID: 7372)
- crazyinvers.exe (PID: 7396)
- erroriconscursor.exe (PID: 7416)
- toonel.exe (PID: 7424)
Working with threads in the GNU C Compiler (GCC) libraries related mutex has been found
- INVERS.exe (PID: 7360)
- crazyinvers.exe (PID: 7396)
SQL CE related mutex has been found
- wscript.exe (PID: 7332)
The process executes VB scripts
- cmd.exe (PID: 2140)
INFO
Checks supported languages
- dobrota clean.exe (PID: 6944)
- erroricons.exe (PID: 7340)
- INVERS.exe (PID: 7360)
- crazywarningicons.exe (PID: 7372)
- crazyinvers.exe (PID: 7396)
- erroriconscursor.exe (PID: 7416)
- toonel.exe (PID: 7424)
Reads the computer name
- dobrota clean.exe (PID: 6944)
Create files in a temporary directory
- dobrota clean.exe (PID: 6944)
Process checks computer location settings
- dobrota clean.exe (PID: 6944)
Checks proxy server information
- wscript.exe (PID: 7332)
Creates files in the program directory
- wscript.exe (PID: 7332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:11 09:16:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 114688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1eef0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
144
Monitored processes
15
Malicious processes
2
Suspicious processes
3
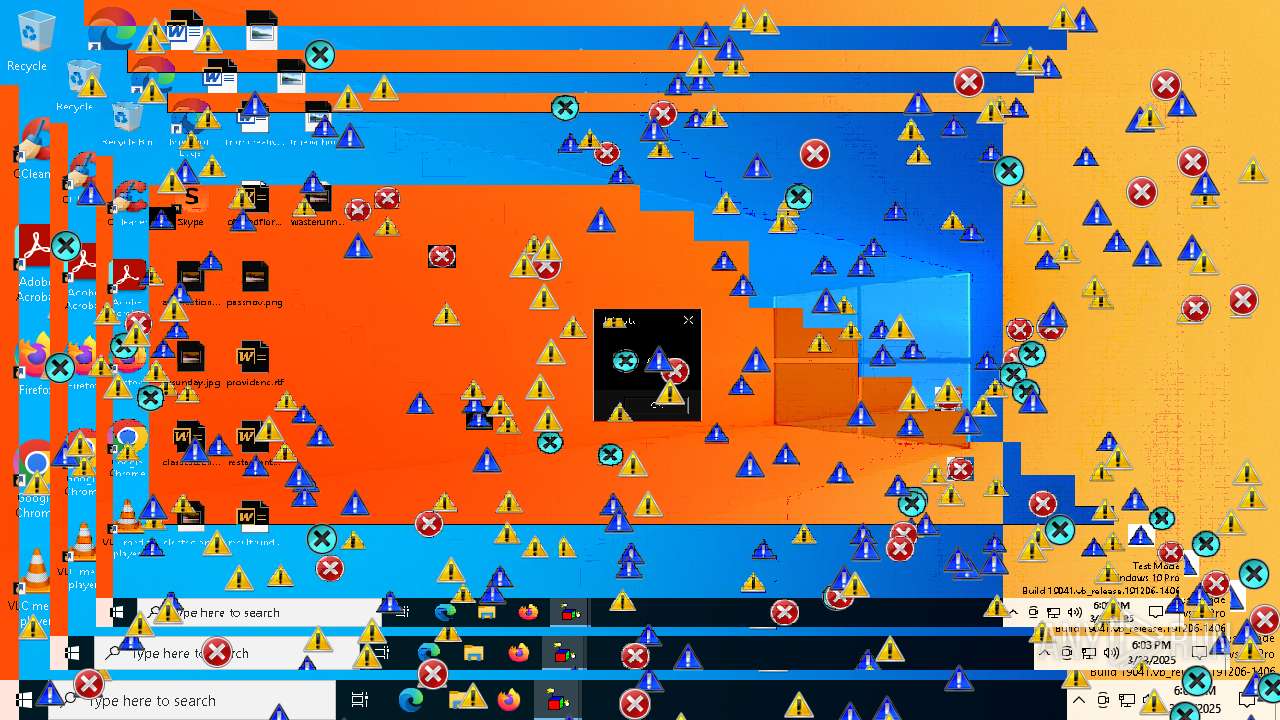
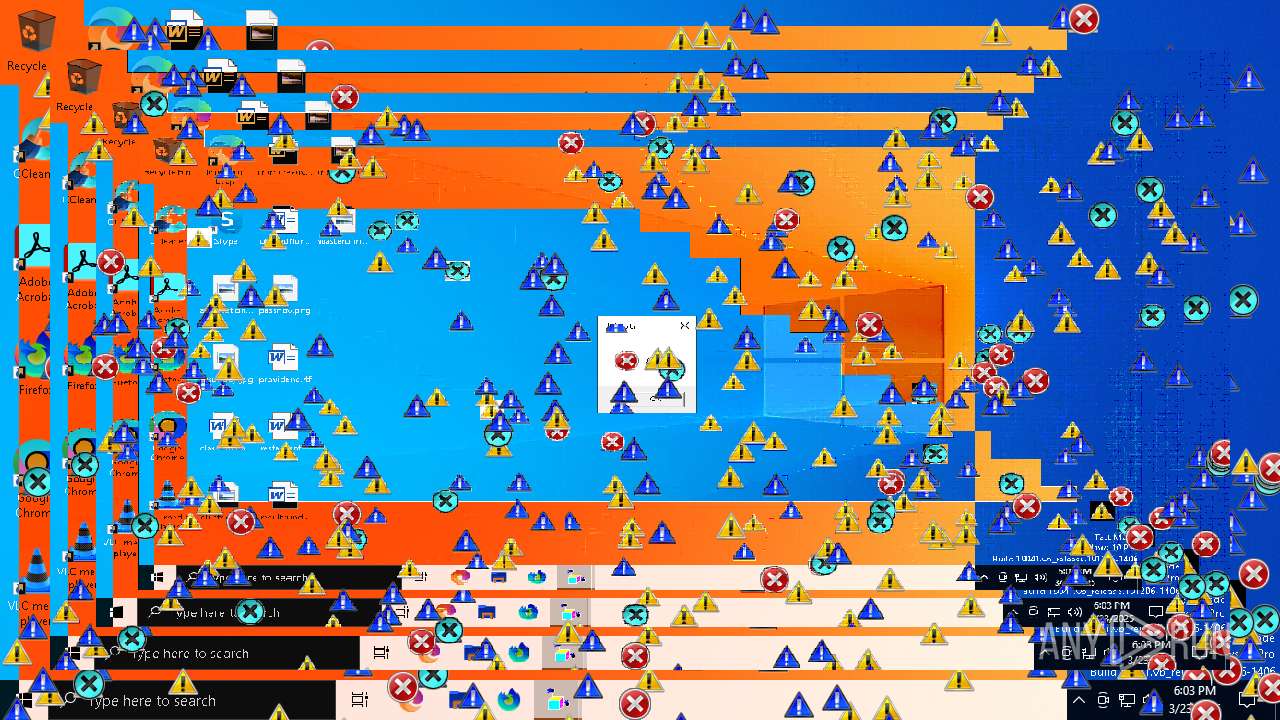
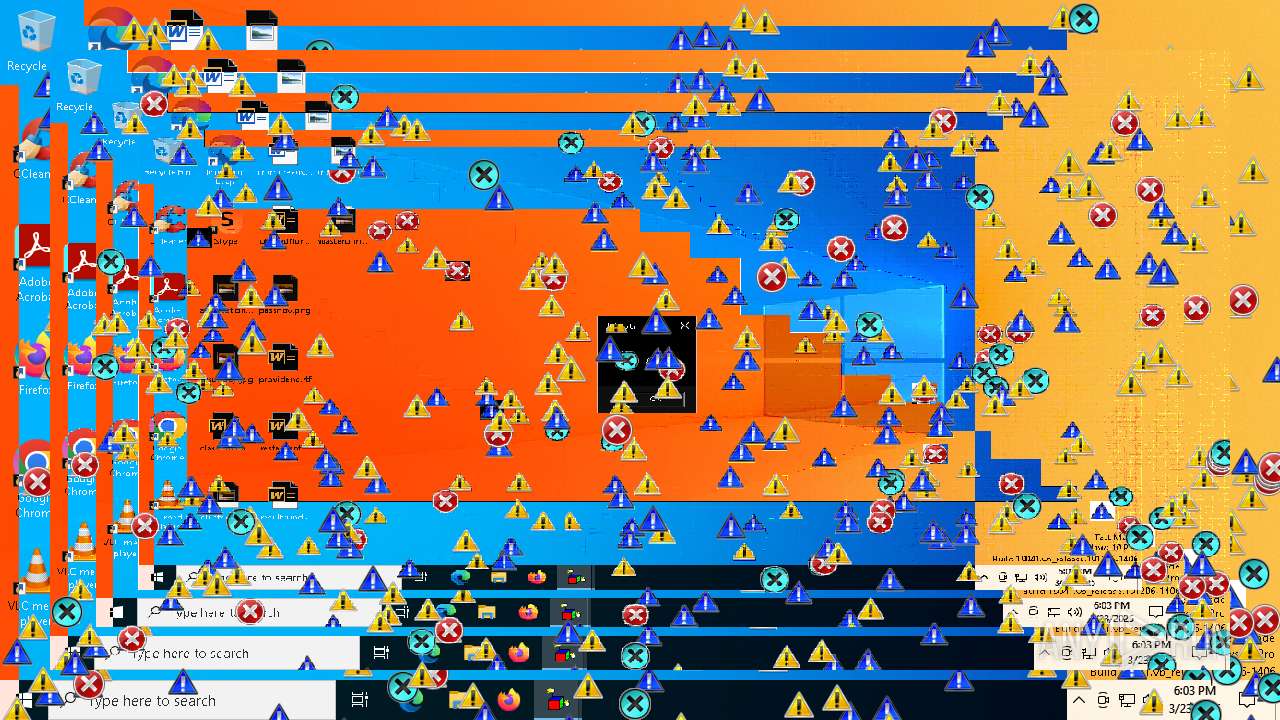
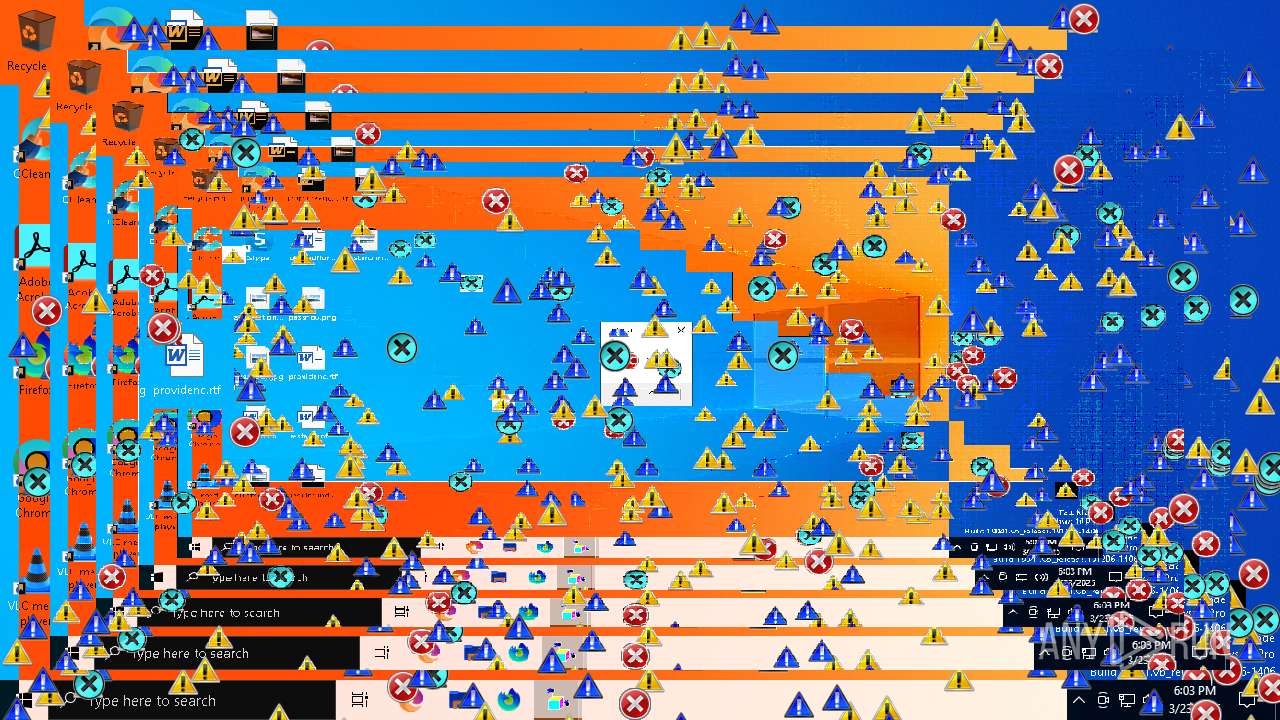
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2140 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\start_dobrota.bat" " | C:\Windows\SysWOW64\cmd.exe | — | dobrota clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5936 | "C:\Users\admin\Downloads\dobrota clean.exe" | C:\Users\admin\Downloads\dobrota clean.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 6944 | "C:\Users\admin\Downloads\dobrota clean.exe" | C:\Users\admin\Downloads\dobrota clean.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7332 | "C:\WINDOWS\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs" | C:\Windows\SysWOW64\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7340 | erroricons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroricons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7360 | INVERS.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7372 | crazywarningicons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazywarningicons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7396 | crazyinvers.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazyinvers.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7416 | erroriconscursor.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
2 982
Read events
2 913
Write events
68
Delete events
1
Modification events
| (PID) Process: | (2140) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | UniqueID |
Value: {30CE7E7C-9E9F-448B-ADB6-29F7AB4FF38E} | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | ComputerName |
Value: DESKTOP-JGLLJLD | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\General |
| Operation: | write | Name: | VolumeSerialNumber |
Value: 649566714 | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Player\Settings |
| Operation: | delete value | Name: | Client ID |
Value: {CECDFD5C-8F08-4FEF-8713-FAA895A422EB} | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | LocalBase |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | DTDFile |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.DTD | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | LocalDelta |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSD.XML | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Media\WMSDK\Namespace |
| Operation: | write | Name: | RemoteDelta |
Value: C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNSR.XML | |||
| (PID) Process: | (7332) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\MediaPlayer\Preferences\ProxySettings\HTTP |
| Operation: | write | Name: | ProxyStyle |
Value: 1 | |||
Executable files
8
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dobrota.mp3 | — | |
MD5:— | SHA256:— | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\libgcc_s_dw2-1.dll | executable | |
MD5:E2AC23418781F632311513944EDD0A4C | SHA256:B4CC93CF4D7C2906C1929C079CD98EF00C7A33832E132AC57ADDE71857082E36 | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\messages2.vbs | text | |
MD5:63954D8930E517637C254F9DA0749E7A | SHA256:BFFA14678B8C39C2FBFA54B76FBAC5F750AEBC8DC2954DA10A55B7F1F90F351C | |||
| 7332 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows Media\12.0\WMSDKNS.XML | text | |
MD5:5433EAB10C6B5C6D55B7CBD302426A39 | SHA256:23DBF7014E99E93AF5F2760F18EE1370274F06A453145C8D539B66D798DAD131 | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | executable | |
MD5:5134F289DBF4ABAE370E3F36B637B73E | SHA256:E69C9383B5D9FE4E069DDEE15797C52E9116F883AD3B1717D2519621AB2751B2 | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\libstdc++-6.dll | executable | |
MD5:0C4A3DE21D6551D43D1F8A11D4F09390 | SHA256:D0DE05720C15F6B7105B90EAF005952BEB73161DF5D1B24EECD5BB892E1C6C8E | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazyinvers.exe | executable | |
MD5:A44458813E819777013EB3E644D74362 | SHA256:47F0E9A90D45B193E81D3E60B7A43E5A4550A07A3DD1F7C98110FDE12265D999 | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | executable | |
MD5:135EEB256E92D261066CFD3FFD31FB3E | SHA256:F0FE346146C30129ED6F507906C973F1A54C7D8DD8821C97E9B6EDC42545699D | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\messages.vbs | text | |
MD5:35FBF9BF29760B9E120B37900B3C1343 | SHA256:E1CDAB59DF6508013E8B91C71043C8ECFE81B94A037706147ED19ADF992539E6 | |||
| 6944 | dobrota clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\start_dobrota.bat | text | |
MD5:47FEF7E366F39175F9467A5A33675B40 | SHA256:7670D34D64F41AE60BFFDD902E4D566B7FDD0C7782738782D5A8DBE59CCE2001 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
18
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.24.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7272 | backgroundTaskHost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.24.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.63.118.230:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7272 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |