| File name: | dobrota_clean.exe |
| Full analysis: | https://app.any.run/tasks/5b5e719a-c117-41b0-8445-ae8025782aa1 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2022, 13:33:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C8B999419A3C103270290E99189F794C |
| SHA1: | 90148745B61D2C77C1694E43F11FAAA9A3D05A0A |
| SHA256: | 9093FF3BC7E78CFE84CADC3A993EEB1C15CE497E94EFDCF51C1ADCAFD0AEDF18 |
| SSDEEP: | 98304:JJx19RrCwXU7tTao36KJt6Oe2NhqCZao4+Axhy4V7FLEMUH82Z3dFRsFVsKtOepA:9thk7IInbrIh17FFWZnR0VsAHndDNE |
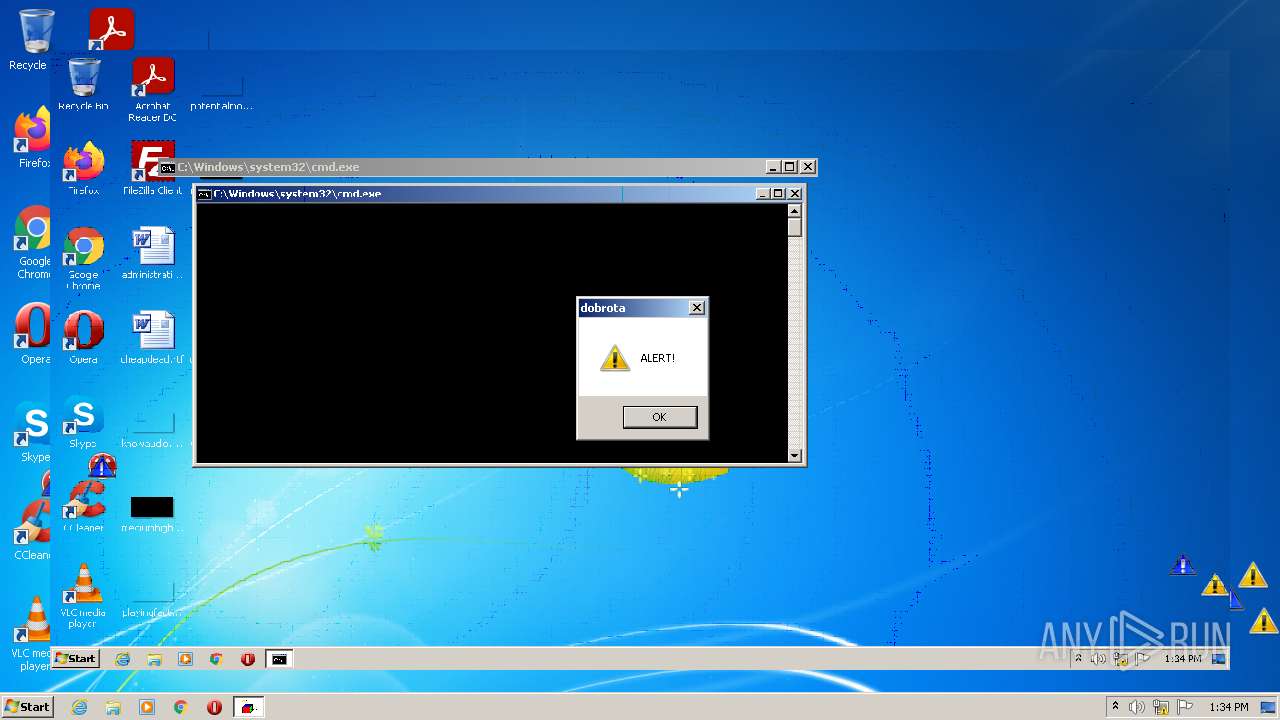
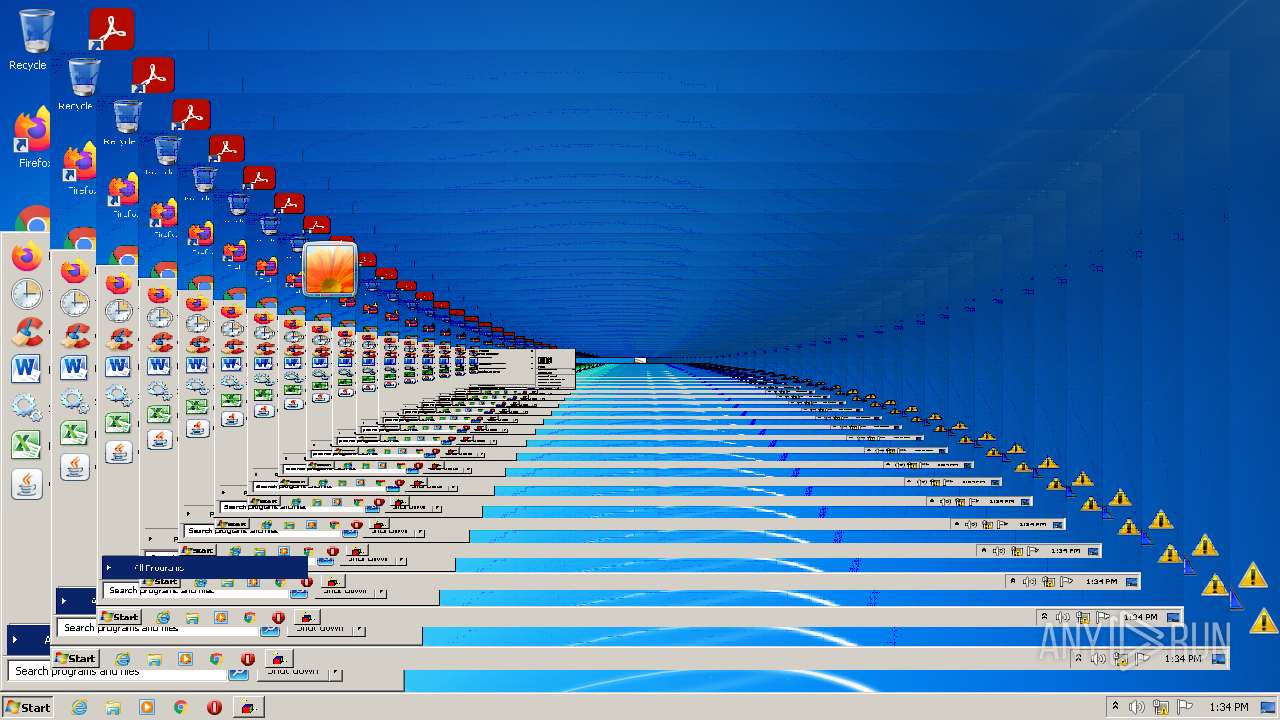
MALICIOUS
Drops executable file immediately after starts
- dobrota_clean.exe (PID: 2128)
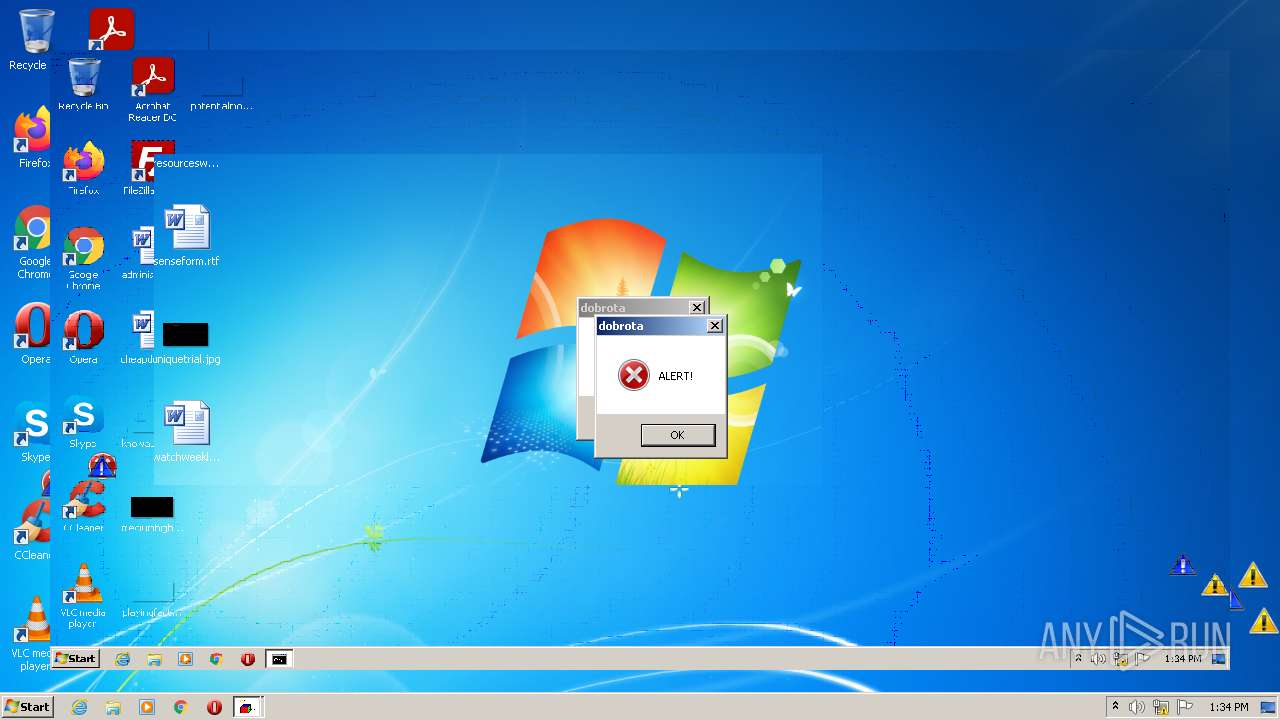
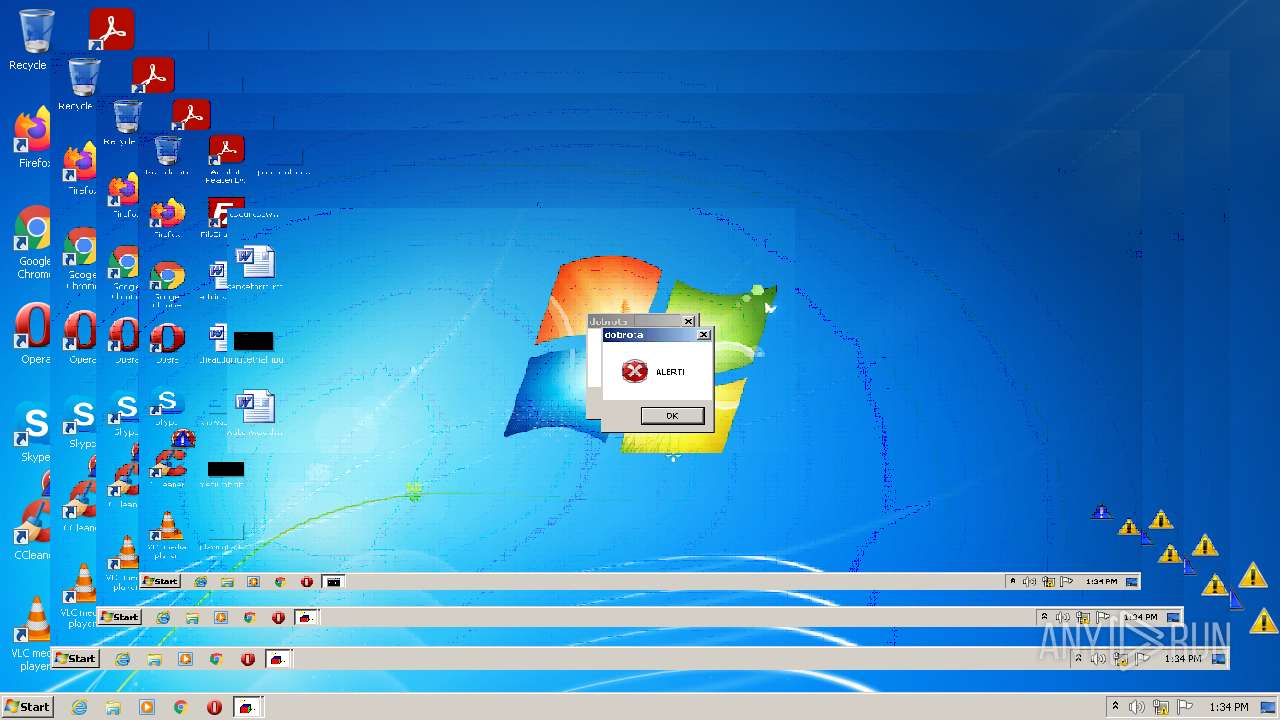
Application was dropped or rewritten from another process
- crazyinvers.exe (PID: 3936)
- crazywarningicons.exe (PID: 1004)
- toonel.exe (PID: 2808)
- INVERS.exe (PID: 2588)
- erroricons.exe (PID: 2196)
- erroriconscursor.exe (PID: 2736)
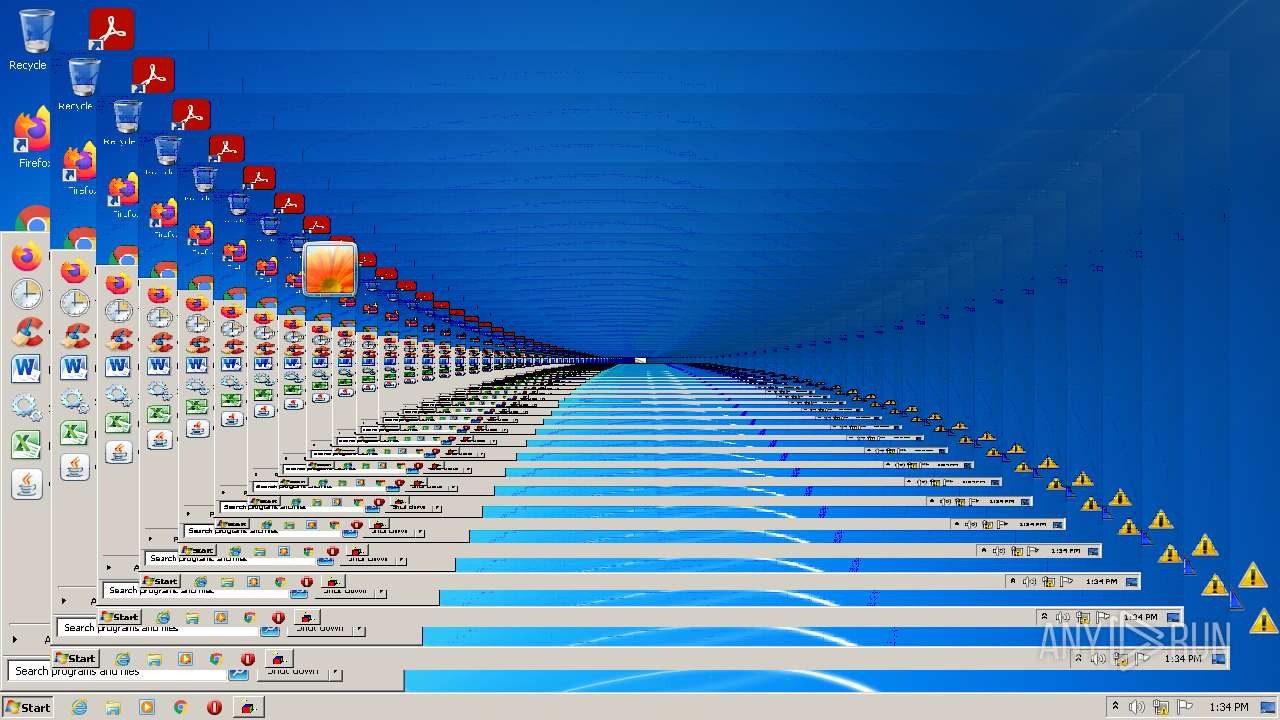
SUSPICIOUS
Checks supported languages
- dobrota_clean.exe (PID: 2128)
- cmd.exe (PID: 4060)
- WScript.exe (PID: 2516)
- erroricons.exe (PID: 2196)
- INVERS.exe (PID: 2588)
- crazywarningicons.exe (PID: 1004)
- crazyinvers.exe (PID: 3936)
- toonel.exe (PID: 2808)
- erroriconscursor.exe (PID: 2736)
- WScript.exe (PID: 3472)
- WScript.exe (PID: 3912)
Reads the computer name
- dobrota_clean.exe (PID: 2128)
- cmd.exe (PID: 4060)
- WScript.exe (PID: 2516)
- WScript.exe (PID: 3912)
- WScript.exe (PID: 3472)
Executable content was dropped or overwritten
- dobrota_clean.exe (PID: 2128)
Starts CMD.EXE for commands execution
- dobrota_clean.exe (PID: 2128)
Executes scripts
- cmd.exe (PID: 4060)
Drops a file that was compiled in debug mode
- dobrota_clean.exe (PID: 2128)
INFO
Checks Windows Trust Settings
- WScript.exe (PID: 2516)
- WScript.exe (PID: 3912)
- WScript.exe (PID: 3472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1eef0 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 114688 |
| CodeSize: | 201728 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2021:06:11 11:16:47+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Jun-2021 09:16:47 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 11-Jun-2021 09:16:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000313BA | 0x00031400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70981 |
.rdata | 0x00033000 | 0x0000A622 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22268 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x0000018C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.35543 |
.rsrc | 0x00063000 | 0x0000E038 | 0x0000E200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.80294 |
.reloc | 0x00072000 | 0x0000227C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56418 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.26192 | 1875 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 5.10026 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.25868 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.02609 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.18109 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.04307 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.66634 | 508 | Latin 1 / Western European | UNKNOWN | RT_STRING |
8 | 3.71728 | 582 | Latin 1 / Western European | UNKNOWN | RT_STRING |
9 | 3.73856 | 422 | Latin 1 / Western European | UNKNOWN | RT_STRING |
10 | 3.55807 | 220 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
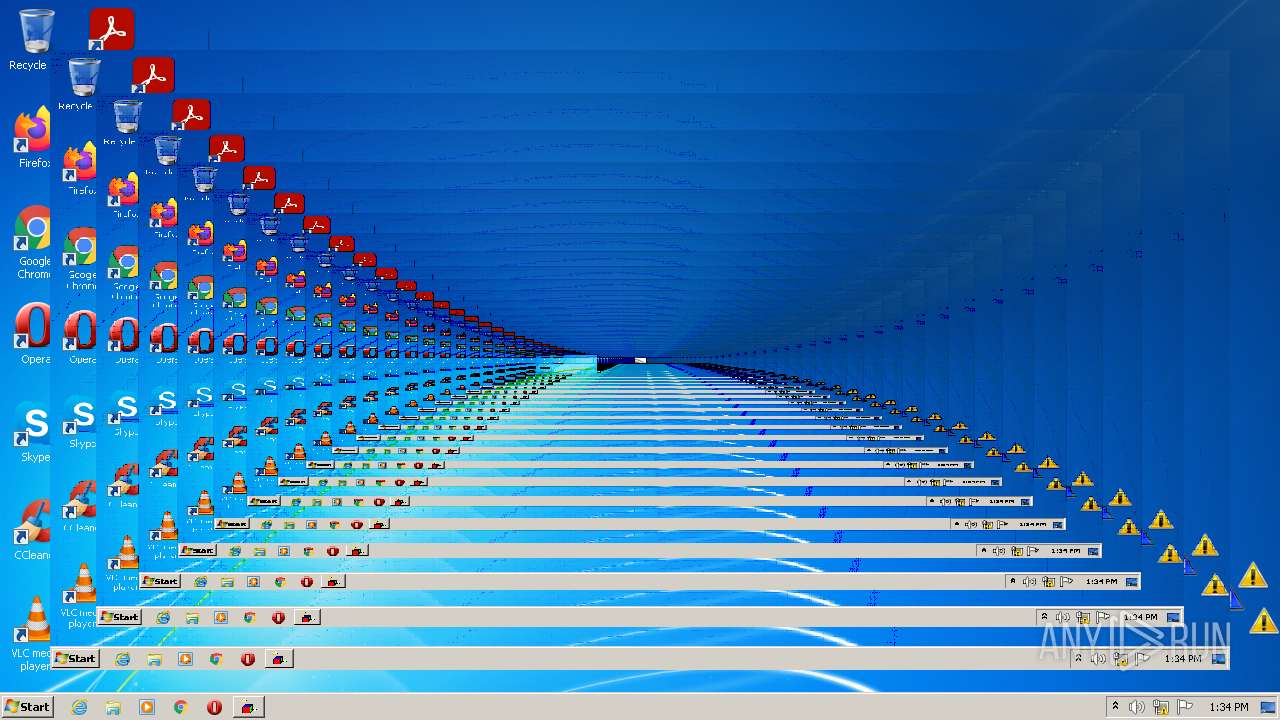
Total processes
49
Monitored processes
12
Malicious processes
1
Suspicious processes
1
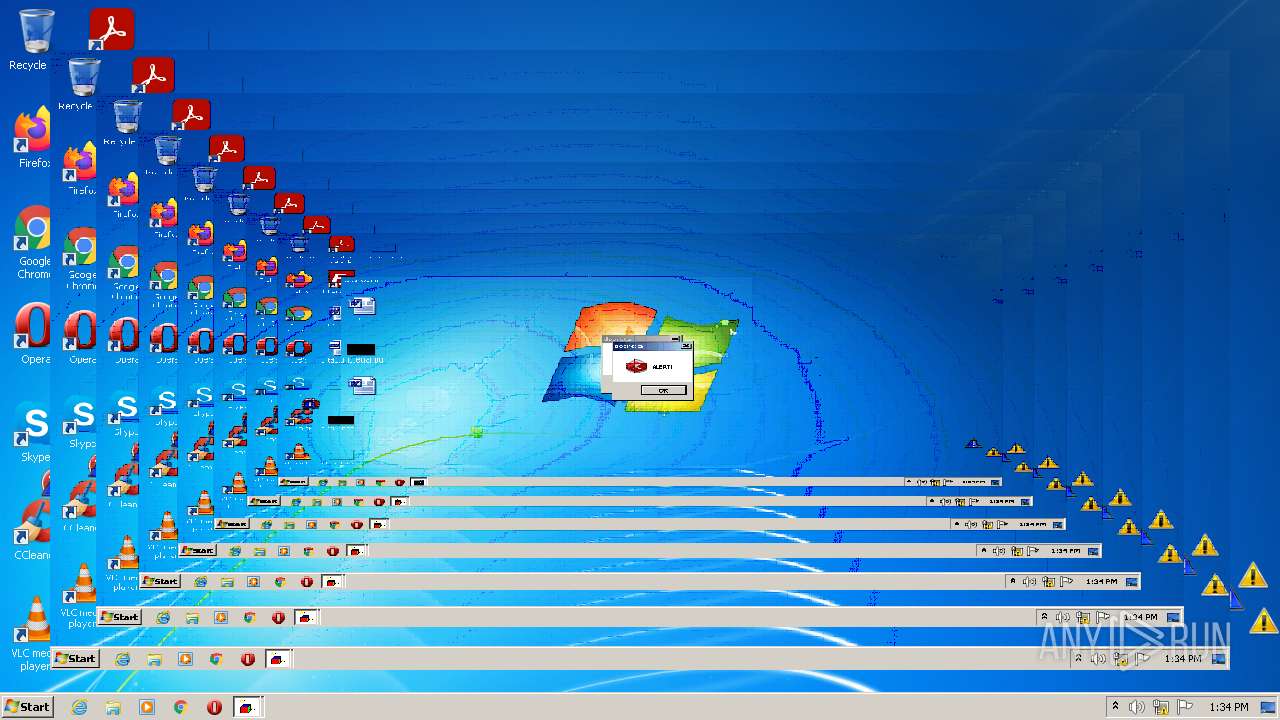
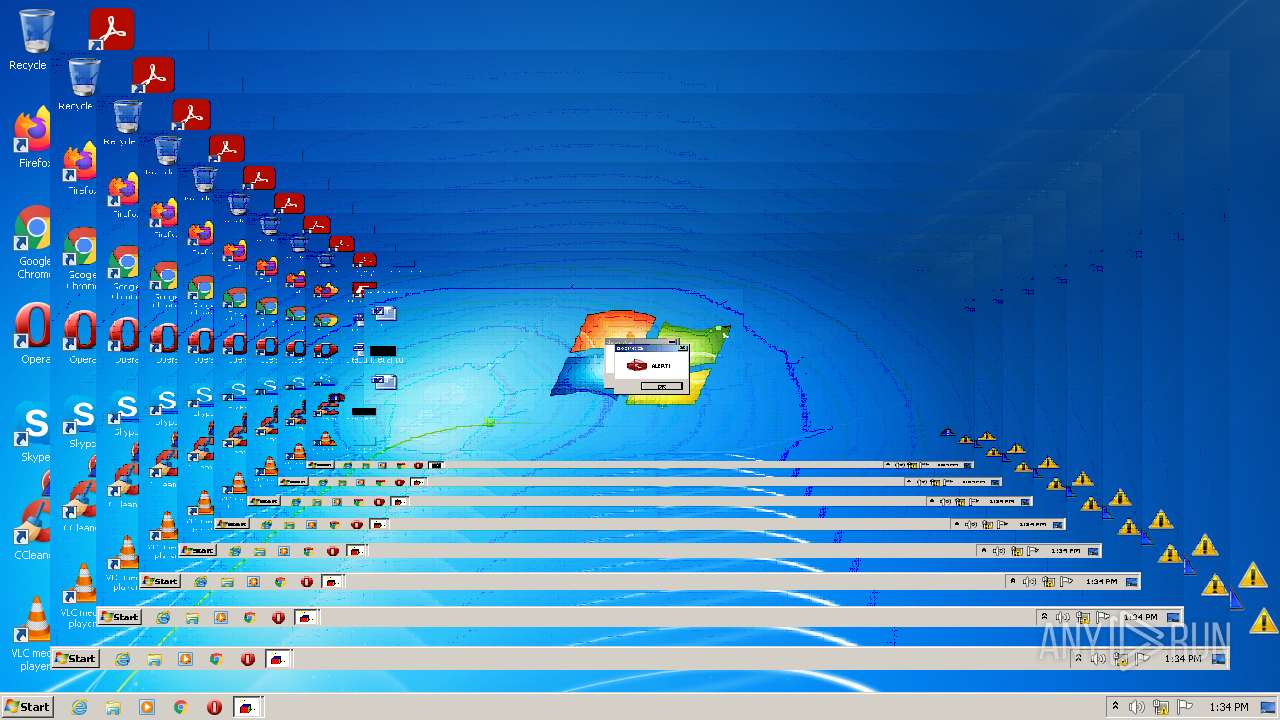
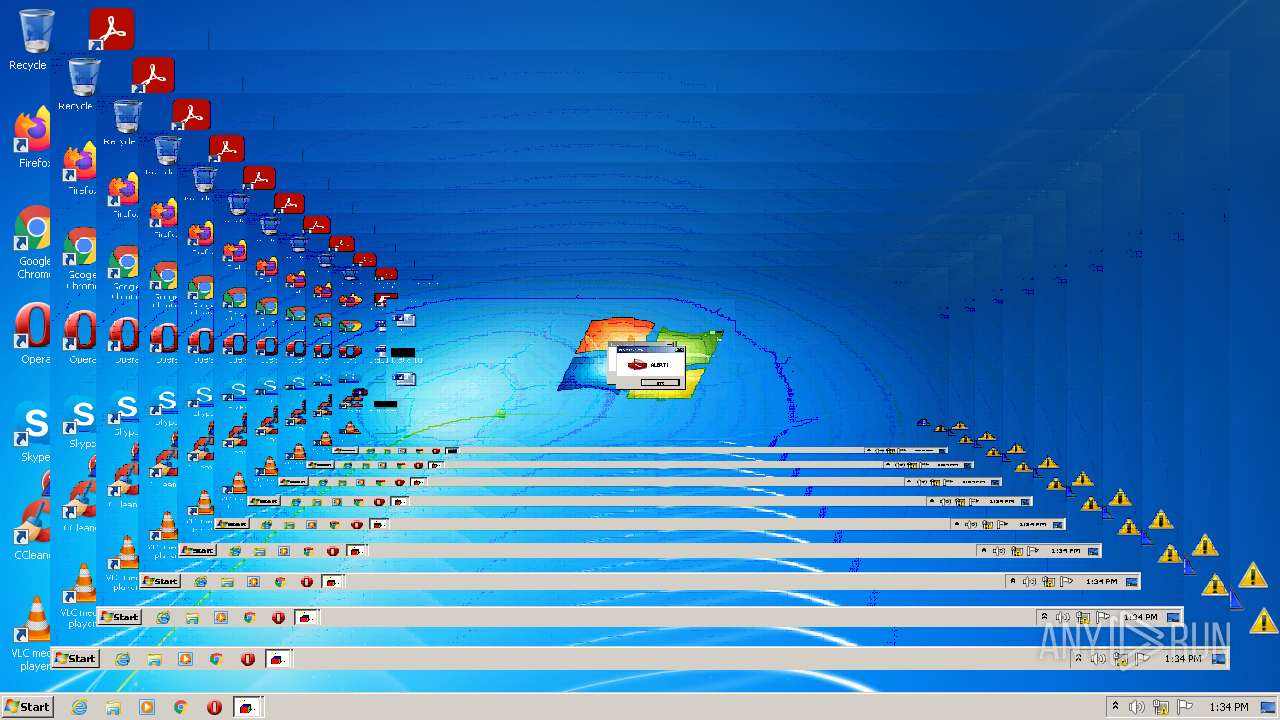
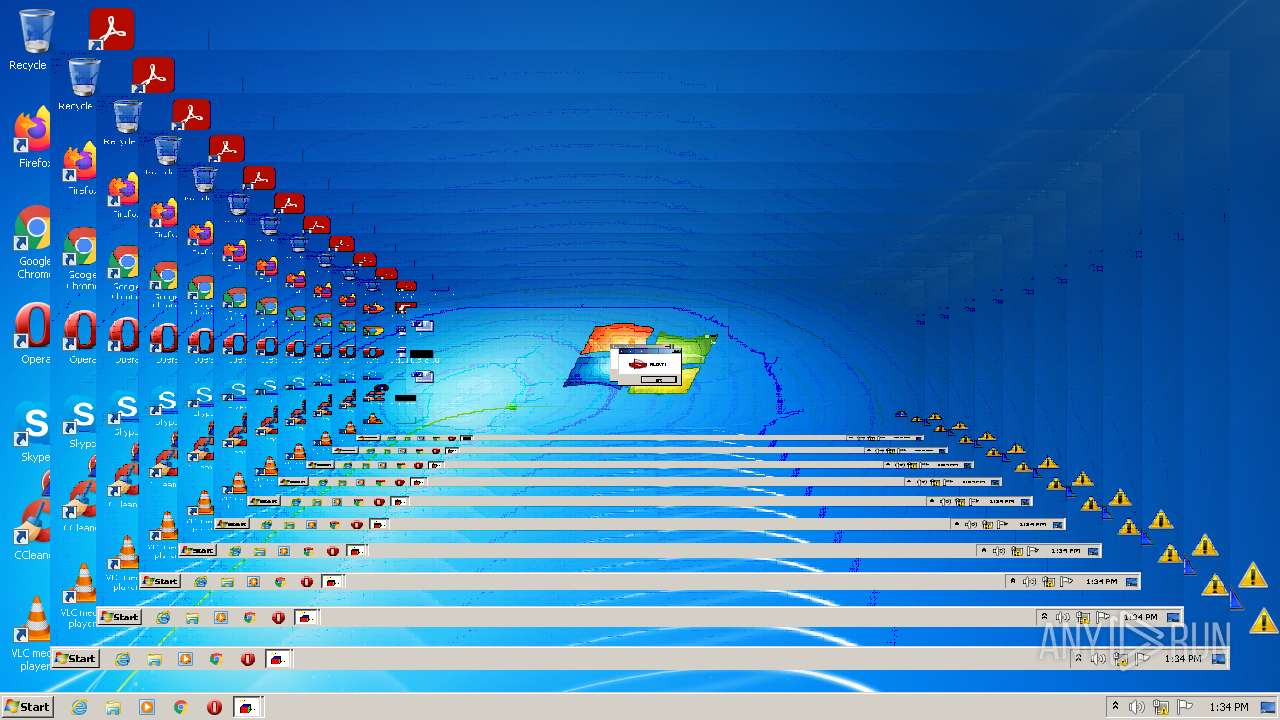
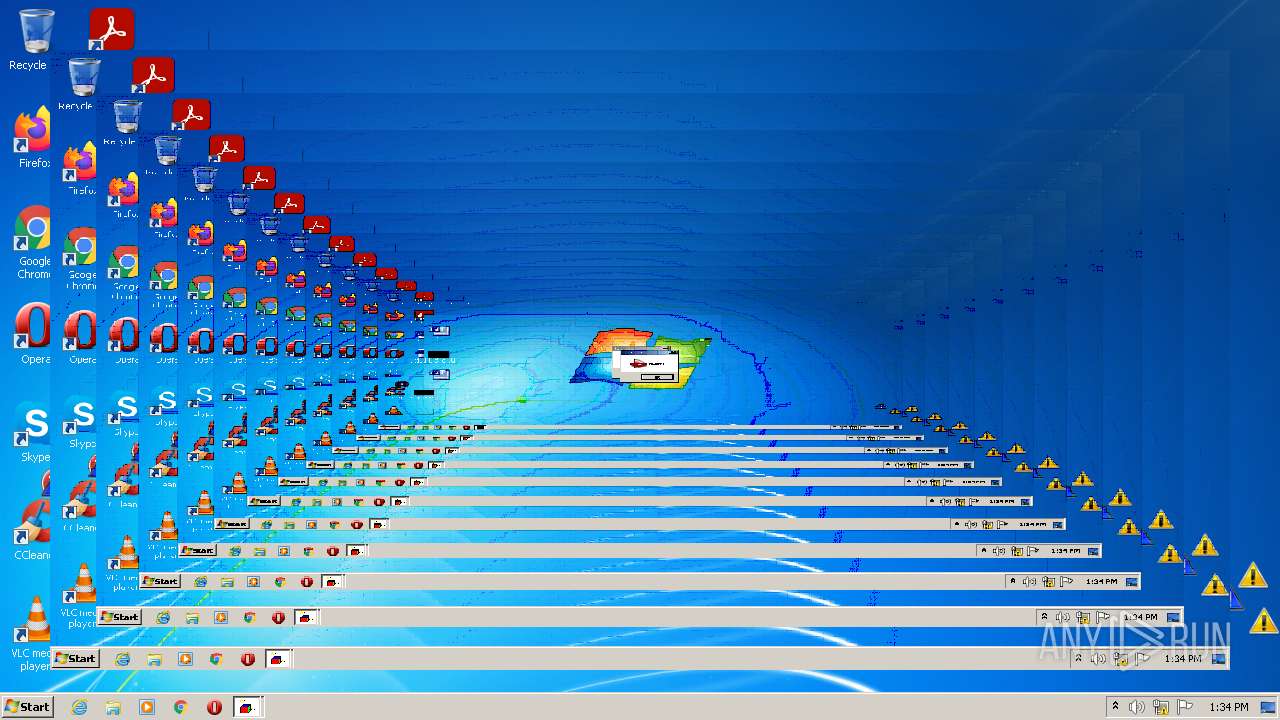
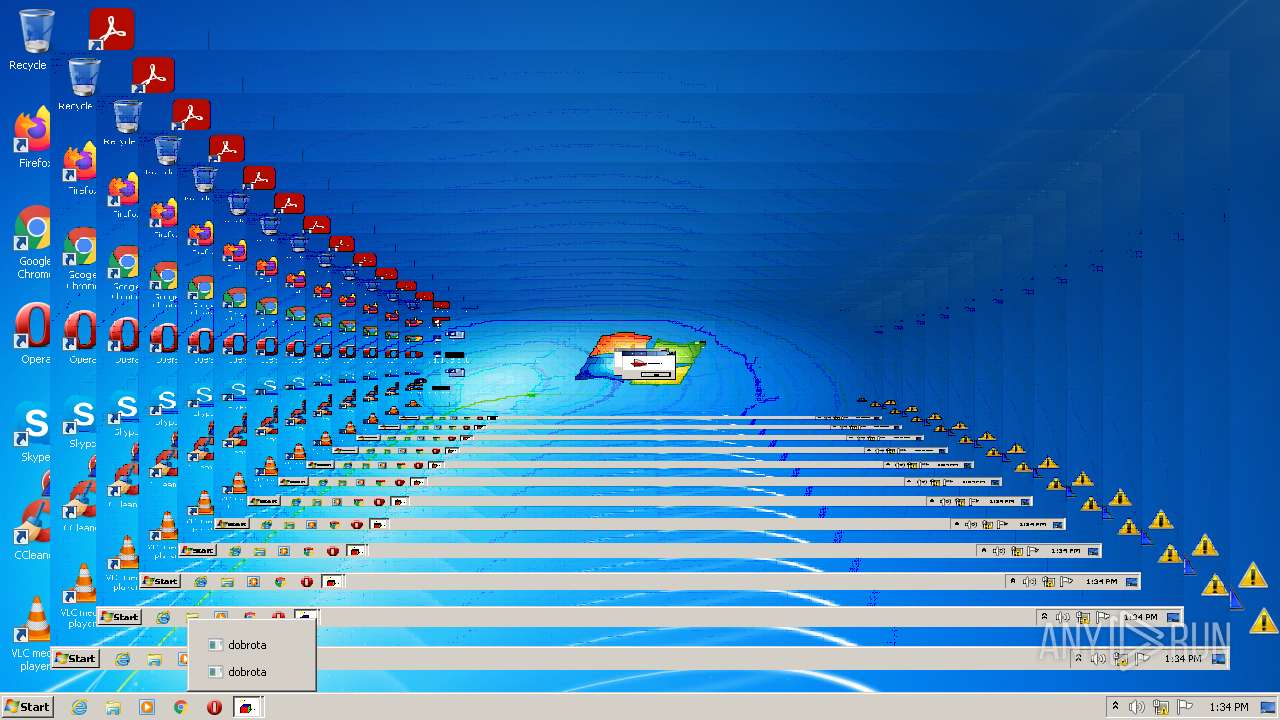
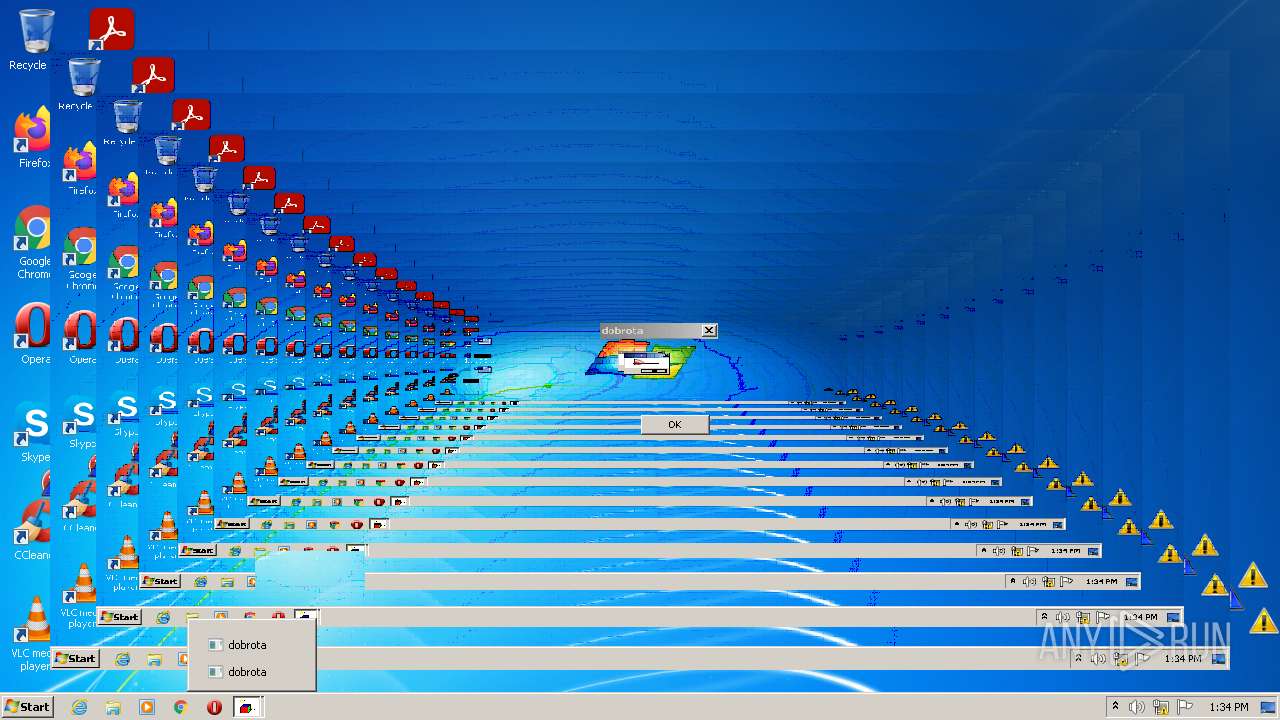
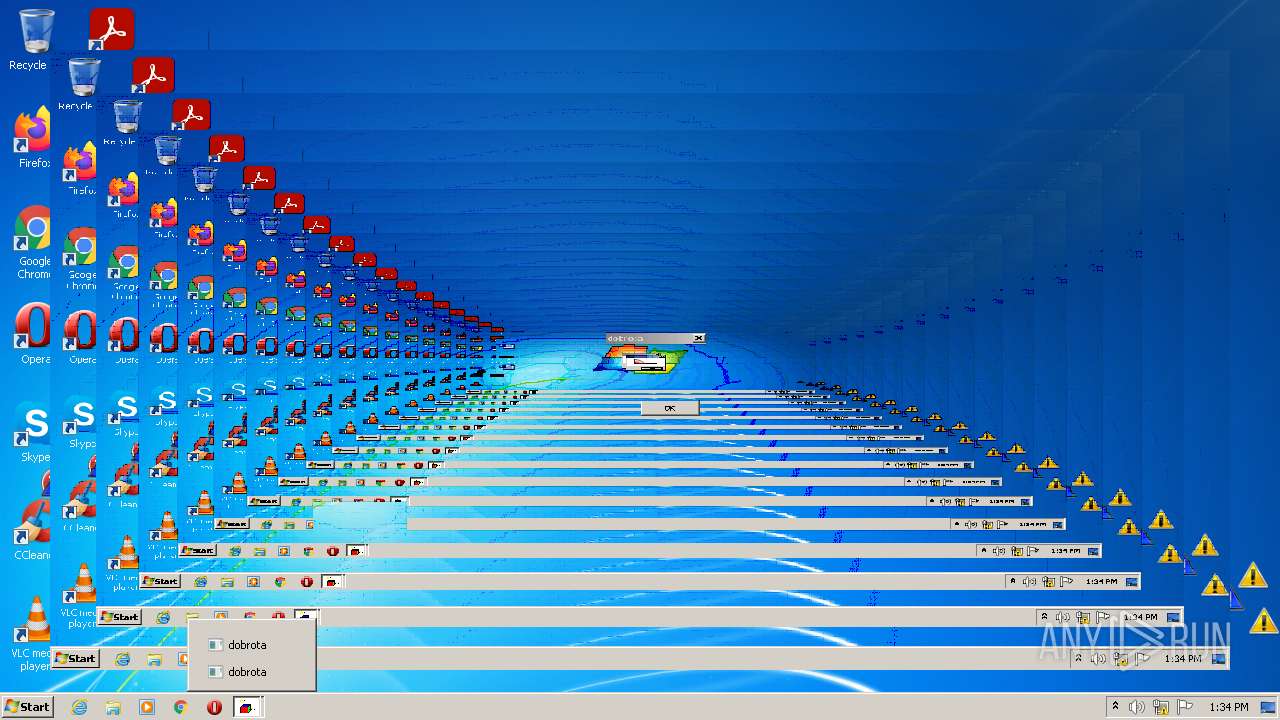
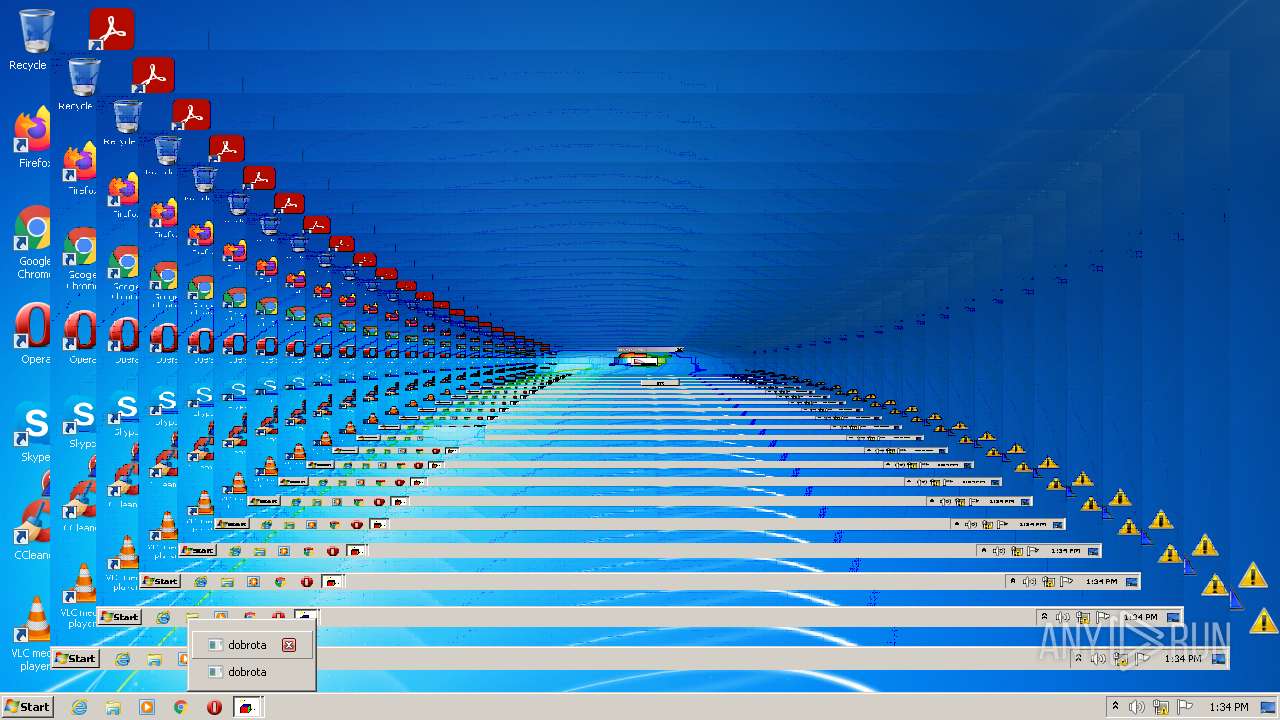
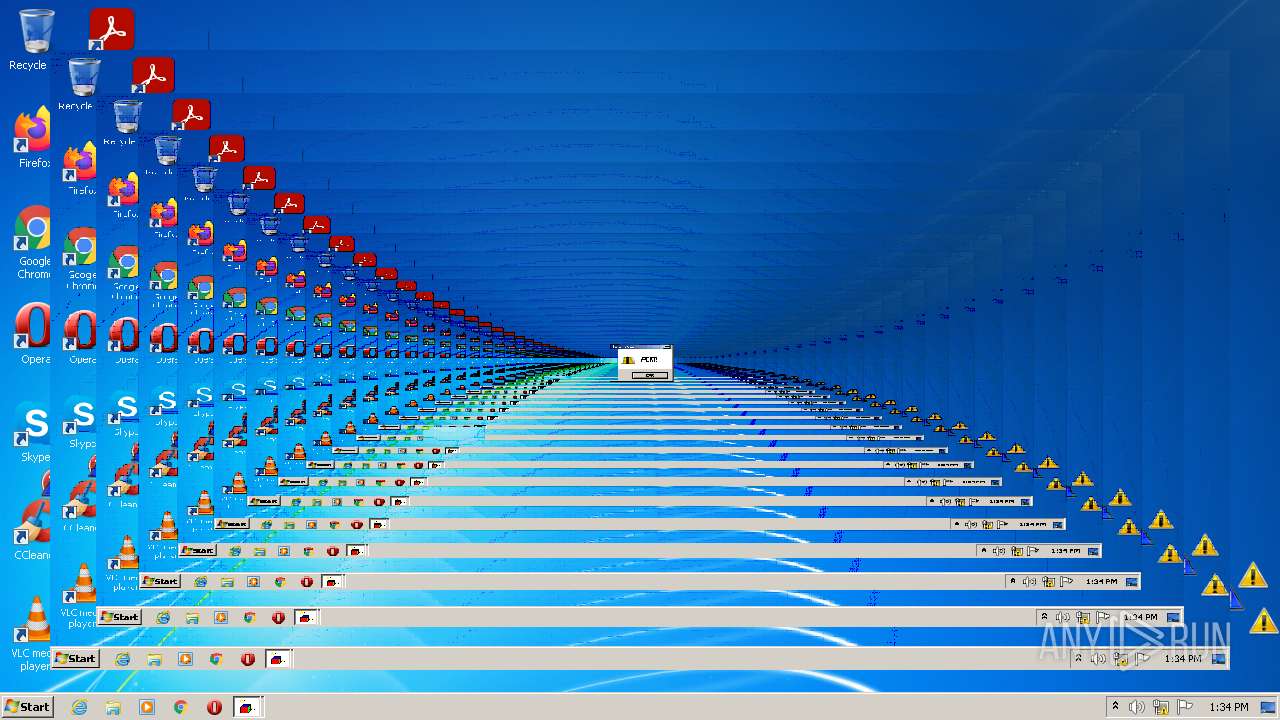
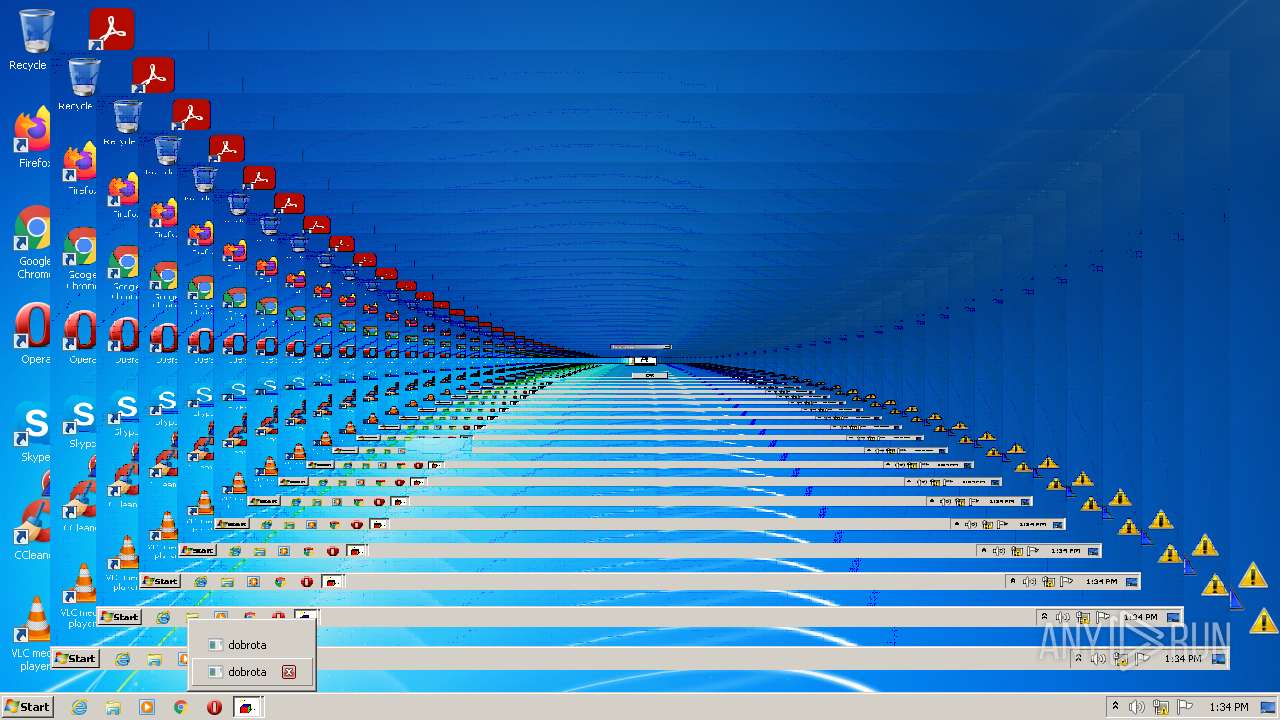
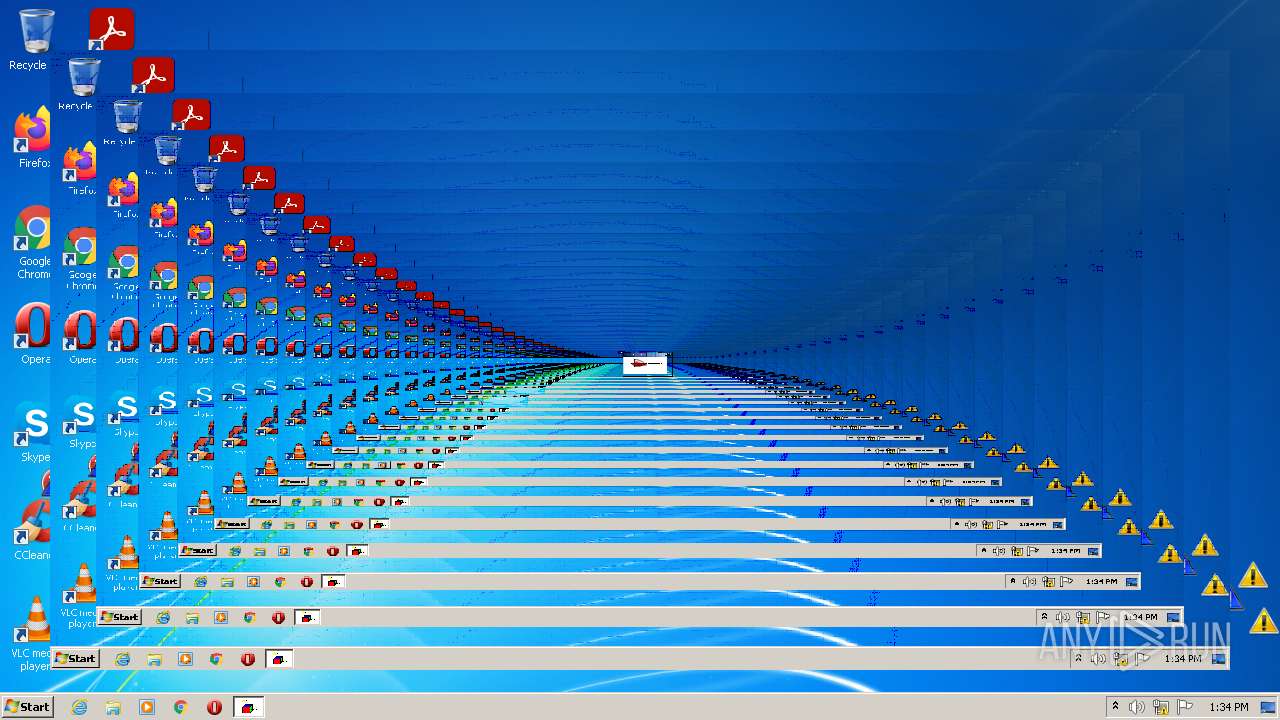
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1004 | crazywarningicons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazywarningicons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 2128 | "C:\Users\admin\AppData\Local\Temp\dobrota_clean.exe" | C:\Users\admin\AppData\Local\Temp\dobrota_clean.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2196 | erroricons.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroricons.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 2516 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2588 | INVERS.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Local\Temp\dobrota_clean.exe" | C:\Users\admin\AppData\Local\Temp\dobrota_clean.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2736 | erroriconscursor.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 2808 | toonel.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\toonel.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1073807364 Modules
| |||||||||||||||
| 3472 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\messages.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 1073807364 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3912 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\RarSFX0\messages2.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
2 115
Read events
2 068
Write events
47
Delete events
0
Modification events
| (PID) Process: | (2128) dobrota_clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2128) dobrota_clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2128) dobrota_clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2128) dobrota_clean.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (4060) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (4060) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (4060) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (4060) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2516) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2516) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
8
Suspicious files
1
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\dobrota.mp3 | — | |
MD5:— | SHA256:— | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazyinvers.exe | executable | |
MD5:A44458813E819777013EB3E644D74362 | SHA256:47F0E9A90D45B193E81D3E60B7A43E5A4550A07A3DD1F7C98110FDE12265D999 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroricons.exe | executable | |
MD5:7F31508D95BE3FE50E4E9AA646E86A12 | SHA256:994EFDB644CA1ACB029DFD8D8EEBA440E1CB74D93841B17F21165B9900730B15 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\start_dobrota.bat | text | |
MD5:47FEF7E366F39175F9467A5A33675B40 | SHA256:7670D34D64F41AE60BFFDD902E4D566B7FDD0C7782738782D5A8DBE59CCE2001 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\crazywarningicons.exe | executable | |
MD5:E21BB4749A8B1B6FC26A7BCF57781836 | SHA256:0ECBB8099ED1D9A1673165D3C4C9BBDE88DD9678540A98B99434FF23B9E6D82C | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\INVERS.exe | executable | |
MD5:5134F289DBF4ABAE370E3F36B637B73E | SHA256:E69C9383B5D9FE4E069DDEE15797C52E9116F883AD3B1717D2519621AB2751B2 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\sound.vbs | text | |
MD5:C36C15E1F99E1C0D093B9B089B1073C5 | SHA256:3D6123CAE8AC645D9C9D33B0DADA869A7FDD5117A2BF0F9080E4E30FE5BED736 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\messages.vbs | text | |
MD5:35FBF9BF29760B9E120B37900B3C1343 | SHA256:E1CDAB59DF6508013E8B91C71043C8ECFE81B94A037706147ED19ADF992539E6 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\toonel.exe | executable | |
MD5:A84257E64CFBD9F6C0A574AF416BC0D1 | SHA256:FE7FF85B95EC06CE0F3CB49FDFA4D36DE1F08669D36D381794AAF597510AFAD7 | |||
| 2128 | dobrota_clean.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\erroriconscursor.exe | executable | |
MD5:135EEB256E92D261066CFD3FFD31FB3E | SHA256:F0FE346146C30129ED6F507906C973F1A54C7D8DD8821C97E9B6EDC42545699D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report