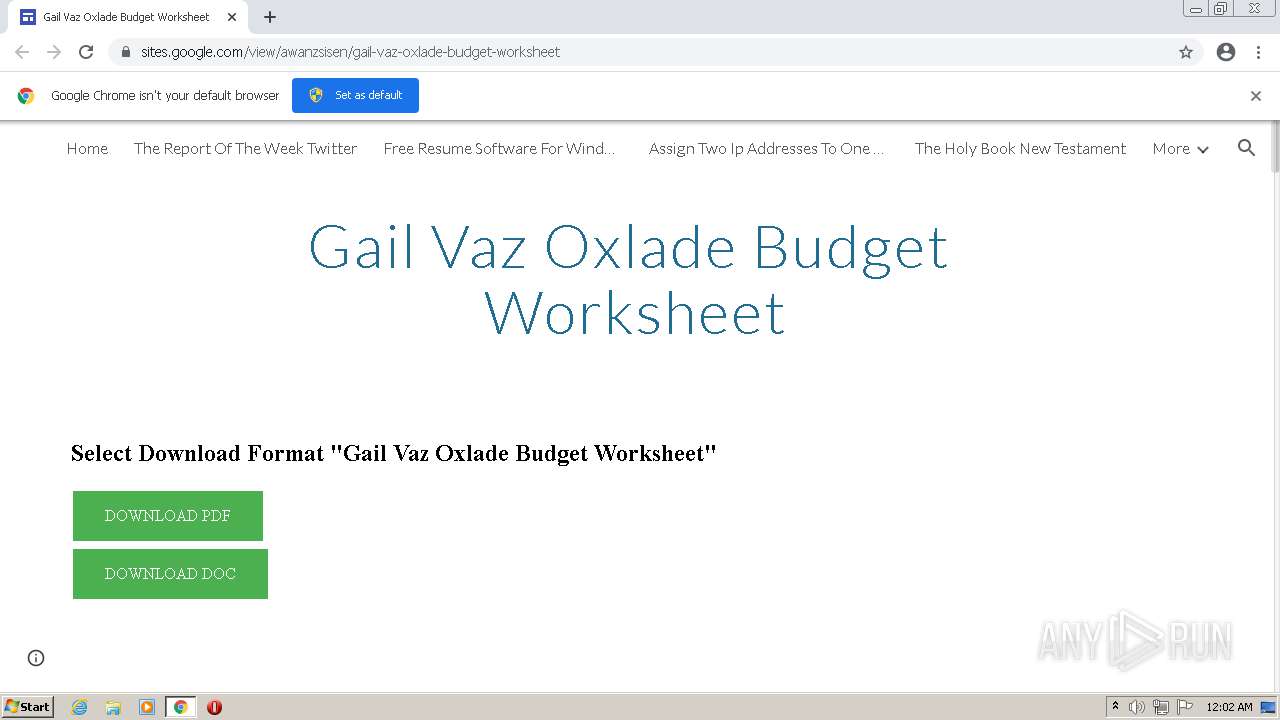
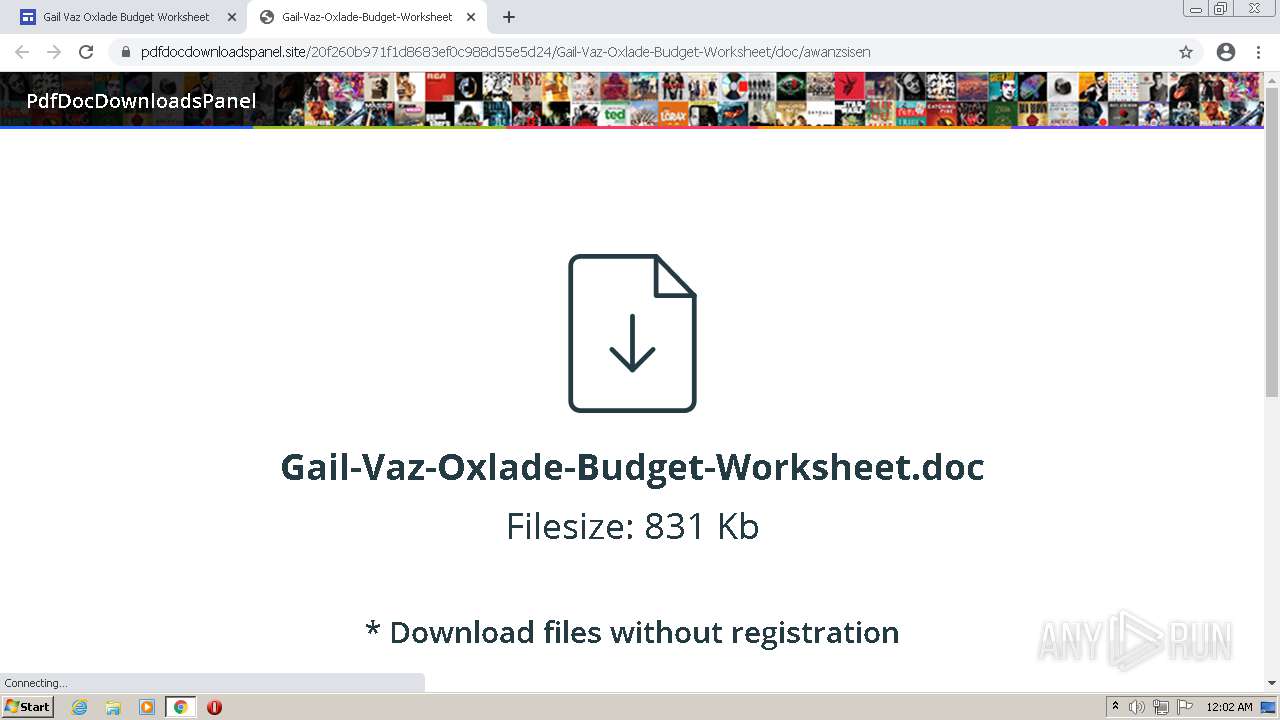
| URL: | https://sites.google.com/view/awanzsisen/gail-vaz-oxlade-budget-worksheet |
| Full analysis: | https://app.any.run/tasks/dae6d705-ef63-4e2d-9177-27fa52841d27 |
| Verdict: | Malicious activity |
| Analysis date: | June 11, 2021, 23:01:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7FAEB48DE4E3E21B4DA6360F31006A02 |
| SHA1: | 40584DB19BB945A44E50B9C653ACE7B53439B833 |
| SHA256: | 909018E49D501F266BB2F8D568ACE194D0E176075C53BC02220F2DCF34DEF16F |
| SSDEEP: | 3:N8BhLJ3u1MLfWXALnLJdPYn:2J+Q+XAHXg |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 3912)
Checks supported languages
- chrome.exe (PID: 2404)
- chrome.exe (PID: 3912)
Reads the computer name
- chrome.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e3fd988,0x6e3fd998,0x6e3fd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 3064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1056,9401926046747144701,1910316252846258891,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1348 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | |||||||||||||||
| 3912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://sites.google.com/view/awanzsisen/gail-vaz-oxlade-budget-worksheet" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
42
Read events
37
Write events
5
Delete events
0
Modification events
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60C3EB68-F48.pma | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
35
DNS requests
23
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | — | — | whitelisted |
— | — | HEAD | 200 | 74.125.100.103:80 | http://r2---sn-5hnekn7z.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=45.92.228.15&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1623452420&mv=m&mvi=2&pl=25&rmhost=r1---sn-5hnekn7z.gvt1.com&shardbypass=yes&smhost=r1---sn-5hnekn76.gvt1.com | US | — | — | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 548 b | whitelisted |
— | — | GET | 206 | 74.125.100.103:80 | http://r2---sn-5hnekn7z.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=45.92.228.15&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1623452181&mv=m&mvi=2&pl=25&rmhost=r1---sn-5hnekn7z.gvt1.com&shardbypass=yes&smhost=r1---sn-5hnekn76.gvt1.com | US | binary | 43.5 Kb | whitelisted |
— | — | GET | 206 | 74.125.100.103:80 | http://r2---sn-5hnekn7z.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=45.92.228.15&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1623452420&mv=m&mvi=2&pl=25&rmhost=r1---sn-5hnekn7z.gvt1.com&shardbypass=yes&smhost=r1---sn-5hnekn76.gvt1.com | US | binary | 5.76 Kb | whitelisted |
— | — | GET | 206 | 74.125.100.103:80 | http://r2---sn-5hnekn7z.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=45.92.228.15&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1623452420&mv=m&mvi=2&pl=25&rmhost=r1---sn-5hnekn7z.gvt1.com&shardbypass=yes&smhost=r1---sn-5hnekn76.gvt1.com | US | binary | 88.6 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 548 b | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 548 b | whitelisted |
— | — | GET | 206 | 74.125.100.103:80 | http://r2---sn-5hnekn7z.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ?cms_redirect=yes&mh=Pe&mip=45.92.228.15&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1623452181&mv=m&mvi=2&pl=25&rmhost=r1---sn-5hnekn7z.gvt1.com&shardbypass=yes&smhost=r1---sn-5hnekn76.gvt1.com | US | bs | 20.9 Kb | whitelisted |
— | — | GET | 302 | 142.250.185.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/AIDSJGrIAR_6GKekQJvhOSI_1.3.36.81/FlU1w6tFdzzsxVNvvqMiCQ | US | html | 548 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.20.13:443 | accounts.google.com | Google Inc. | US | unknown |
— | — | 142.250.184.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 142.250.180.238:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.185.234:443 | content-autofill.googleapis.com | Google Inc. | US | whitelisted |
— | — | 142.250.181.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
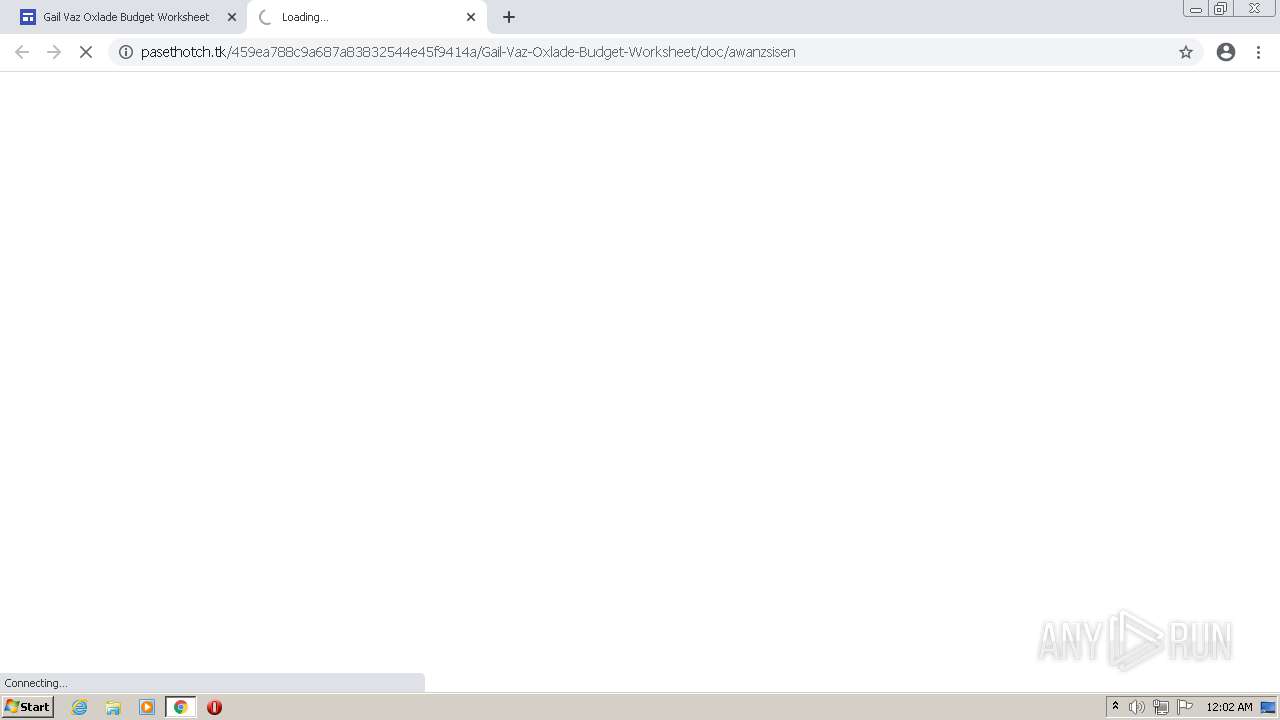
— | — | 172.67.143.237:443 | esfurfestremo.tk | — | US | unknown |
— | — | 54.221.196.120:443 | compact.coolvillehub.com | Amazon.com, Inc. | US | unknown |
— | — | 172.217.18.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
— | — | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
sites.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
esfurfestremo.tk |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
— | — | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |