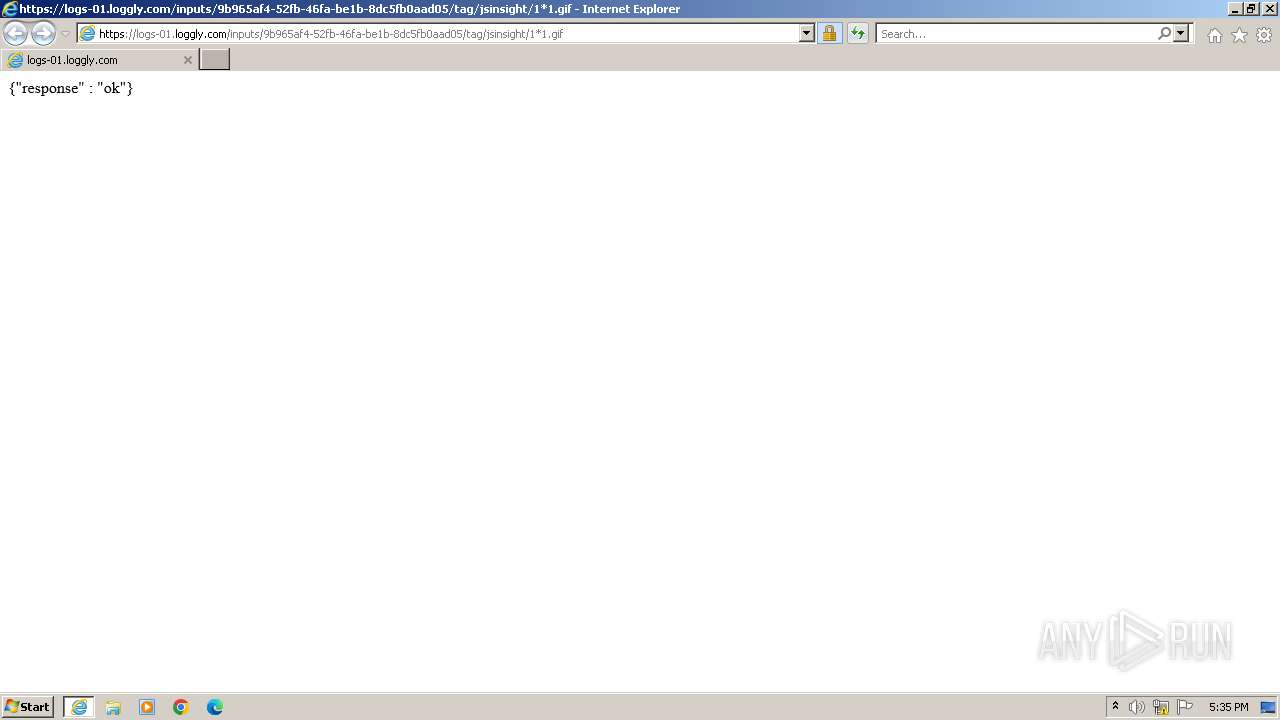
| URL: | https://logs-01.loggly.com/inputs/9b965af4-52fb-46fa-be1b-8dc5fb0aad05/tag/jsinsight/1*1.gif |
| Full analysis: | https://app.any.run/tasks/728fc04d-2de5-4085-ac22-3974d7185eef |
| Verdict: | Malicious activity |
| Analysis date: | November 20, 2023, 17:35:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | 44A1408FF66ECB2B298606998DC2F93648BEB521 |
| SHA256: | 908EEB47FEF59F6DF4424FDC60ED366FFBA803BC19665117631619AF34F4FFDD |
| SSDEEP: | 3:N8KVmBJcLVwH8ftXbIJRBEHbJKW6b:2KVmB4VZLQRi7r6b |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Manual execution by a user
- wmpnscfg.exe (PID: 3864)
Reads the computer name
- wmpnscfg.exe (PID: 3864)
Checks supported languages
- wmpnscfg.exe (PID: 3864)
Application launched itself
- iexplore.exe (PID: 3448)
Reads the machine GUID from the registry
- wmpnscfg.exe (PID: 3864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3448 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://logs-01.loggly.com/inputs/9b965af4-52fb-46fa-be1b-8dc5fb0aad05/tag/jsinsight/1*1.gif" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3484 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
25 055
Read events
24 890
Write events
158
Delete events
7
Modification events
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
108
Text files
154
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:8753C35D49141D6DE18A042504096FC8 | SHA256:D622E0DCC6167A98F5BE66263ABEC395D69A6B87A3E20A614D3E507173A24B80 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:CB9070B1297D06B71950CB2F92DF924B | SHA256:6FF0EAB72ECB65DA50408AC276C4A0D4E0F11327E1AF52C04167168DCADC8E57 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BC2602F5489CFE3E69F81C6328A4C17C_849A9AE095E451B9FFDF6A58F3A98E26 | binary | |
MD5:D1C8C99BFB8A5E1D095CBEA158117B1E | SHA256:431228686BE87E303E504AA2754921496C157A8B03F634B9C0611A6492CA8CEE | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\1_1[1].htm | binary | |
MD5:B5EFA112CE475F8BF73086A68521EA2E | SHA256:CDC7A3D8F9CE204E8853C2F7088B9C3FE488432314D1EA6C17CF8FD4AE179261 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\08E1E1CFC1E88036B6947B1C5F8B9B0E_F2F531FBF13F7E9723085D96238FF195 | binary | |
MD5:FB762651A150C61BD912E571F91AFB63 | SHA256:484AD12FD3438F29FCB6C149115DB474368DE812C3E4B9B754A8ABE0DD770F35 | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3484 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\84AFE219AEC53B0C9251F5E19EF019BD_2C9D5E6D83DF507CBE6C15521D5D3562 | binary | |
MD5:33FE6EAEF357B52E0126CBE50E8F8A7A | SHA256:5191B41939551FD7E7621E8ACB7F7D0C2682AEB2F7F9CEFF4815505AB847FDD7 | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:F75CB6E0AE1E50FDDA7354221C7A2BFD | SHA256:8A84A3DDAED6E9E093163F49A018F5F297AD80700E173DB4E17BE160434EA9F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
160
DNS requests
70
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | iexplore.exe | GET | 301 | 13.107.238.45:80 | http://loggly.com/ | unknown | — | — | unknown |
3484 | iexplore.exe | GET | 200 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2747dc4fd30729d5 | unknown | compressed | 4.66 Kb | unknown |
3484 | iexplore.exe | GET | 200 | 184.24.77.187:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d6bb2ad0af14907d | unknown | compressed | 4.66 Kb | unknown |
3484 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com//MEQwQjBAMD4wPDAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCAzkUhA%3D%3D | unknown | binary | 2.01 Kb | unknown |
3484 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQUwPiEZQ6%2FsVZNPaFToNfxx8ZwqAQUfAwyH6fZMH%2FEfWijYqihzqsHWycCAQc%3D | unknown | binary | 2.05 Kb | unknown |
3484 | iexplore.exe | GET | 200 | 192.124.249.36:80 | http://ocsp.starfieldtech.com//MEkwRzBFMEMwQTAJBgUrDgMCGgUABBT1ZqtwV0O1KcYi0gdzcFkHM%2BuArAQUJUWBaFAmOD07LSy%2BzWrZtj2zZmMCCG%2FZI0EsyQey | unknown | binary | 2.10 Kb | unknown |
3448 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3484 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnxLiz3Fu1WB6n1%2FE6xWn1b0jXiQQUdIWAwGbH3zfez70pN6oDHb7tzRcCEAeMiOauFmgffpRqrXLB9lo%3D | unknown | binary | 471 b | unknown |
3484 | iexplore.exe | GET | 200 | 142.250.185.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCVN9Jf3G%2B1pAqd7QzTt1vx | unknown | binary | 472 b | unknown |
3484 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
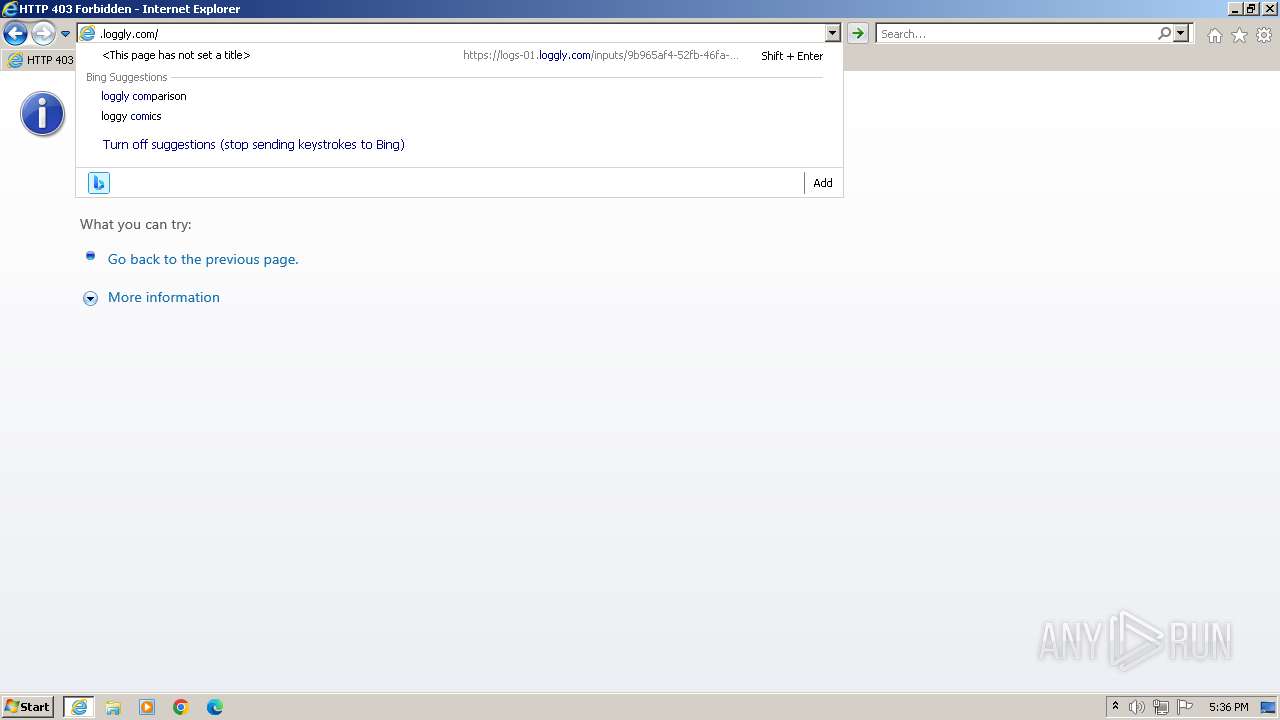
3484 | iexplore.exe | 54.164.8.26:443 | logs-01.loggly.com | AMAZON-AES | US | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3484 | iexplore.exe | 184.24.77.187:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
3484 | iexplore.exe | 192.124.249.36:80 | ocsp.starfieldtech.com | SUCURI-SEC | US | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3448 | iexplore.exe | 54.164.8.26:443 | logs-01.loggly.com | AMAZON-AES | US | unknown |
3448 | iexplore.exe | 92.123.104.26:443 | www.bing.com | Akamai International B.V. | DE | unknown |
3448 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
logs-01.loggly.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.starfieldtech.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
loggly.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |