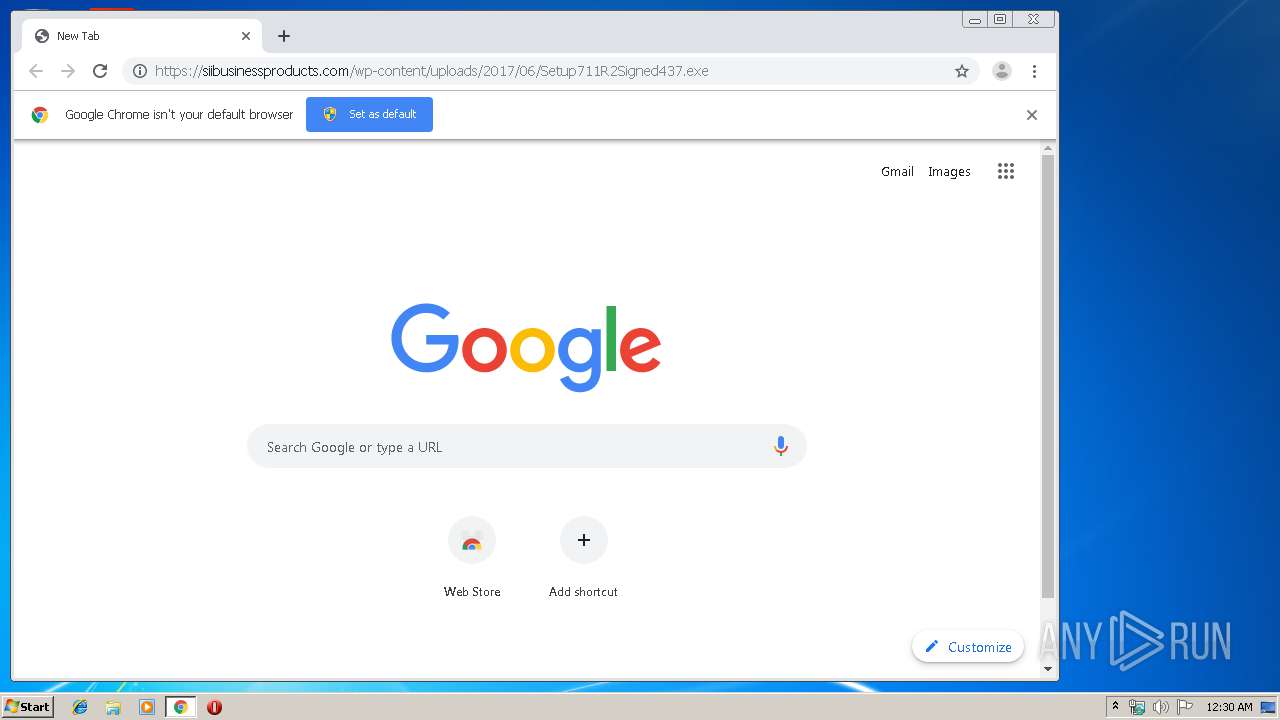
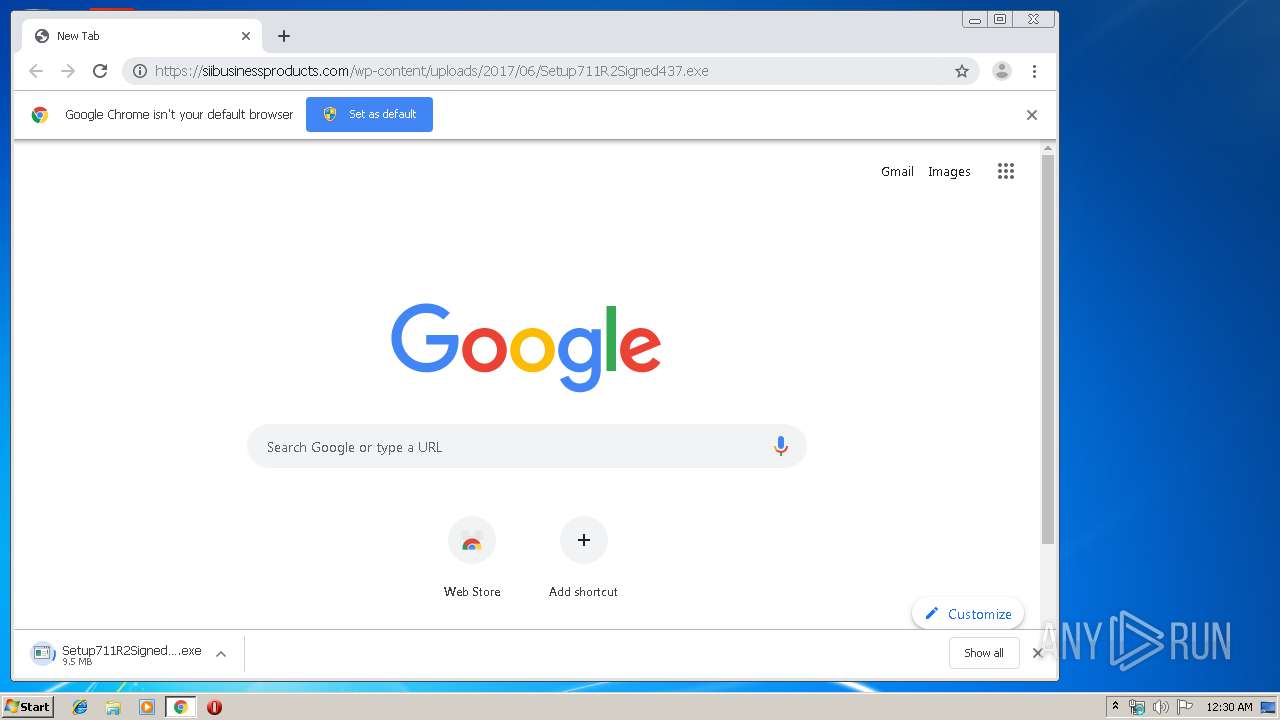
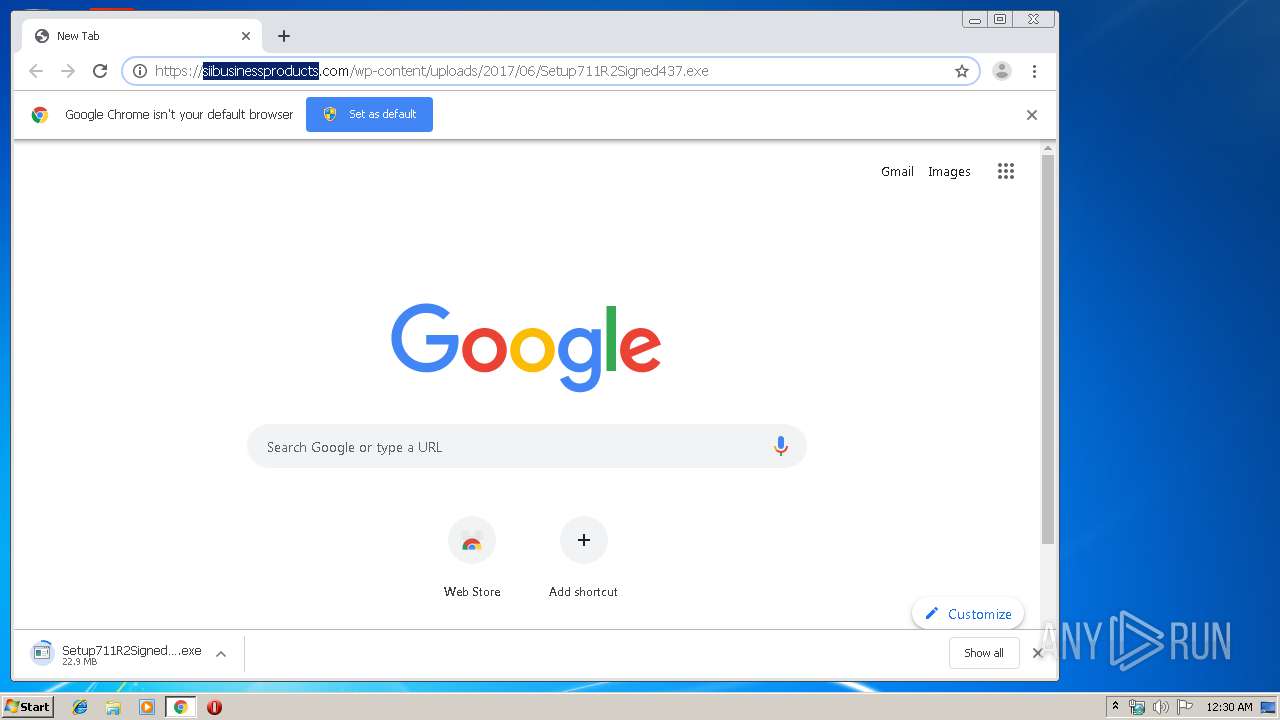
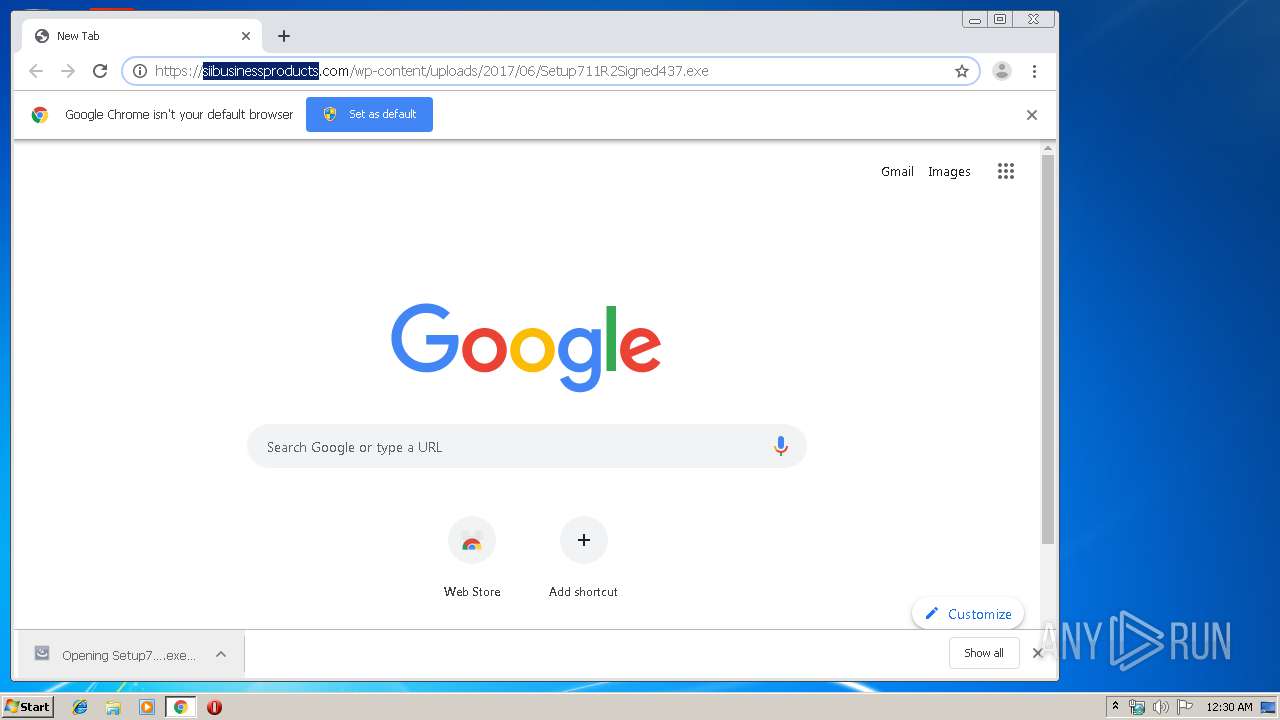
| download: | index.html |
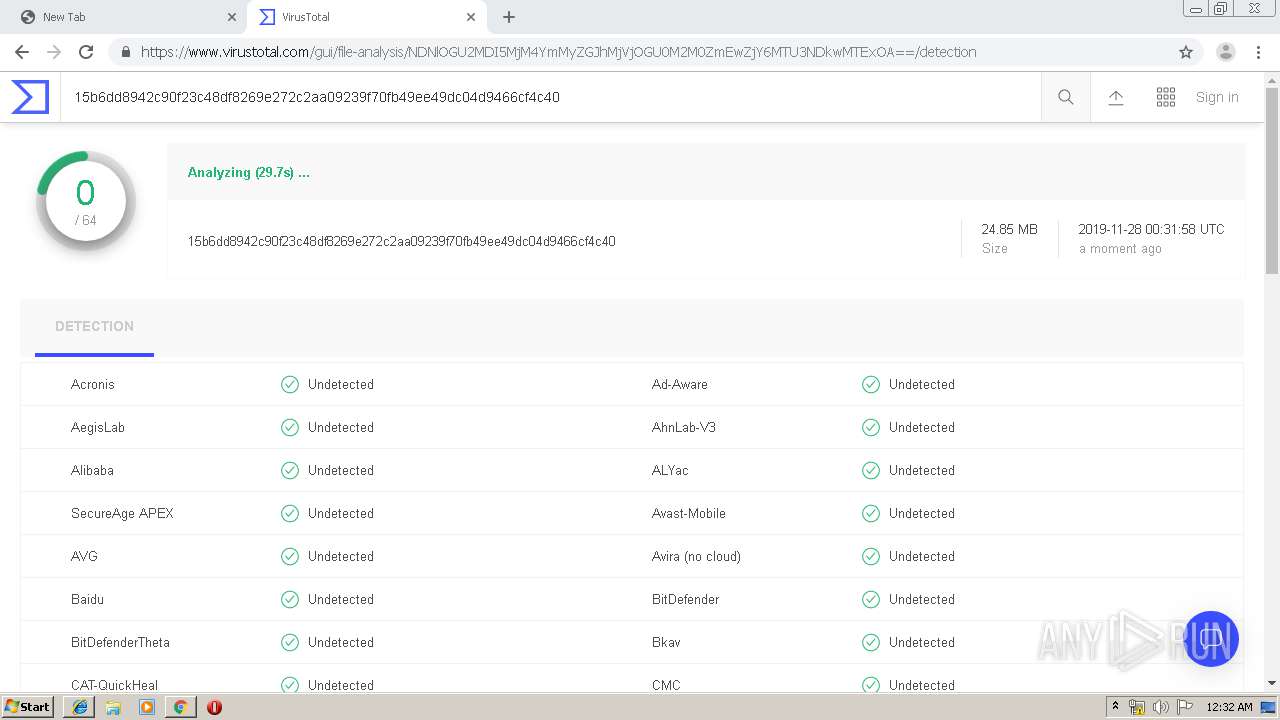
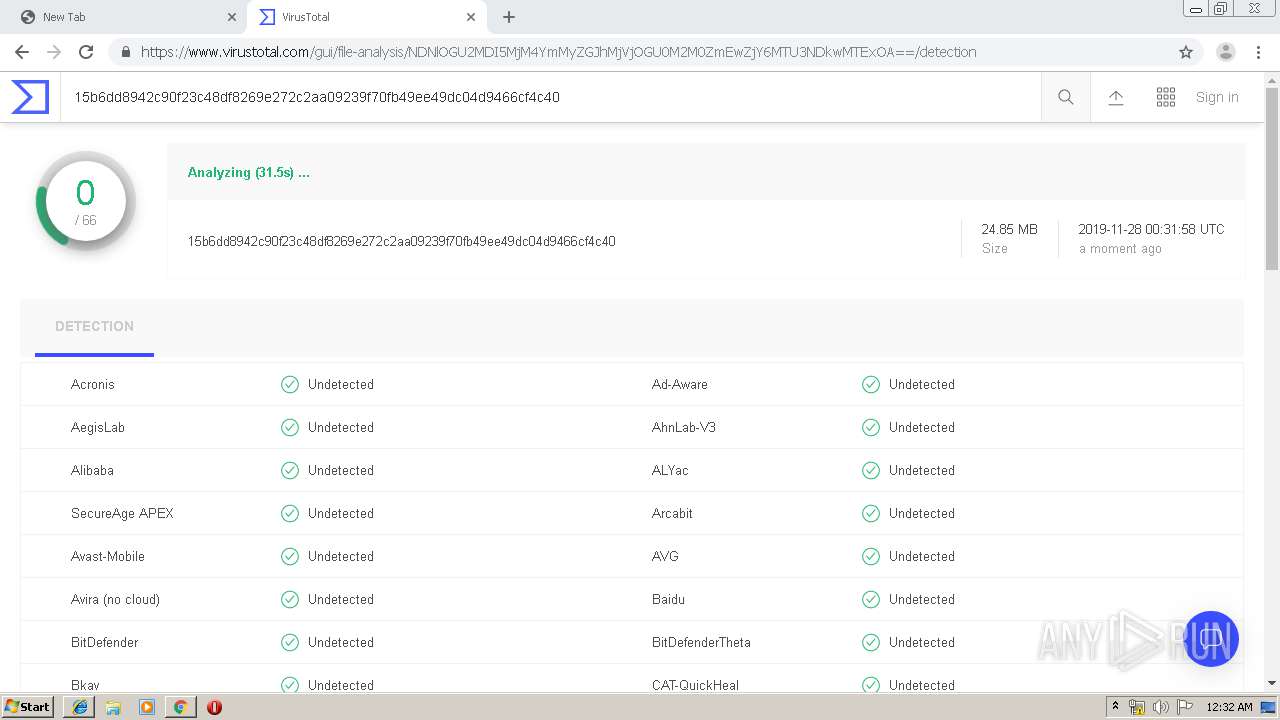
| Full analysis: | https://app.any.run/tasks/b52652ae-4c77-4140-984f-71964936148b |
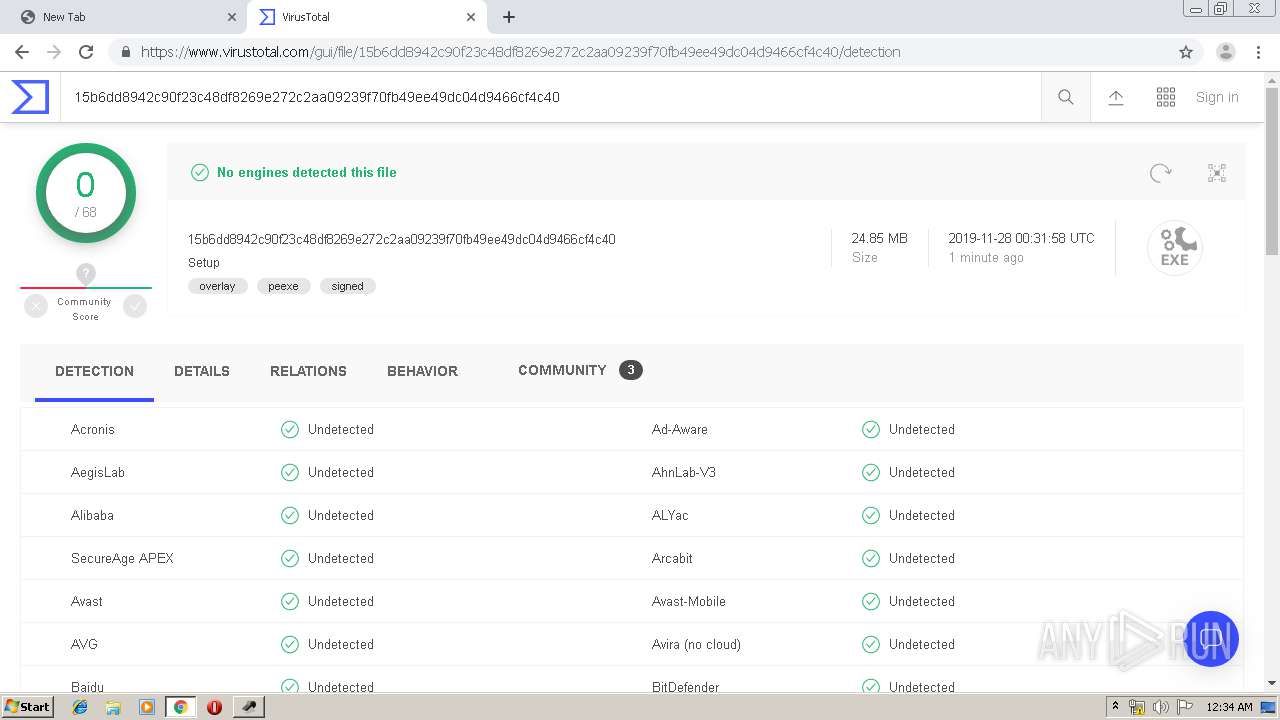
| Verdict: | Malicious activity |
| Analysis date: | November 28, 2019, 00:29:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 260C1411E282A6D932818B776CC8172B |
| SHA1: | B8298507E6F5B27B5F609F9411BB2664459099B2 |
| SHA256: | 9078DECD88745554BCF4619B39CBCE5B497AC7F6EE018F8ABD2CDF81C3AA341B |
| SSDEEP: | 1536:mpUQtZPHavYJ6YN9IVPP7vZUuDheJ4qm0Bz4wyv3ySK8twOm:mmQtoveN9I0u9+GDVwx |
MALICIOUS
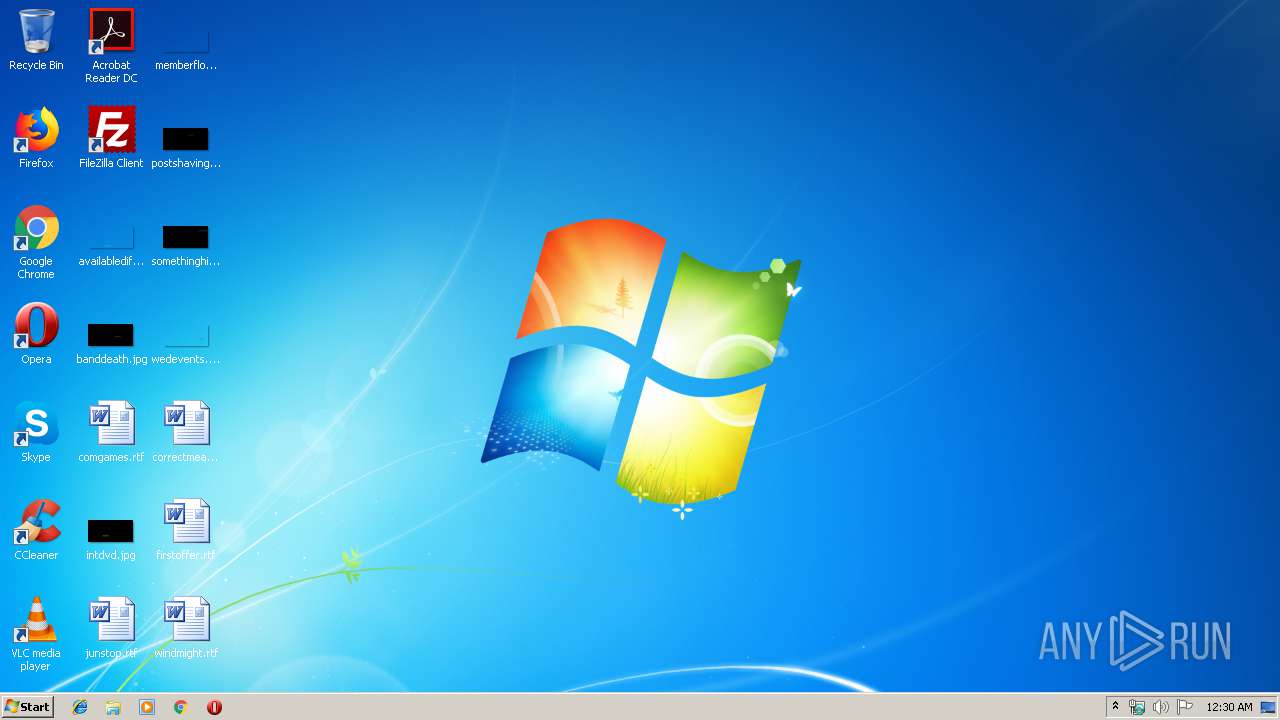
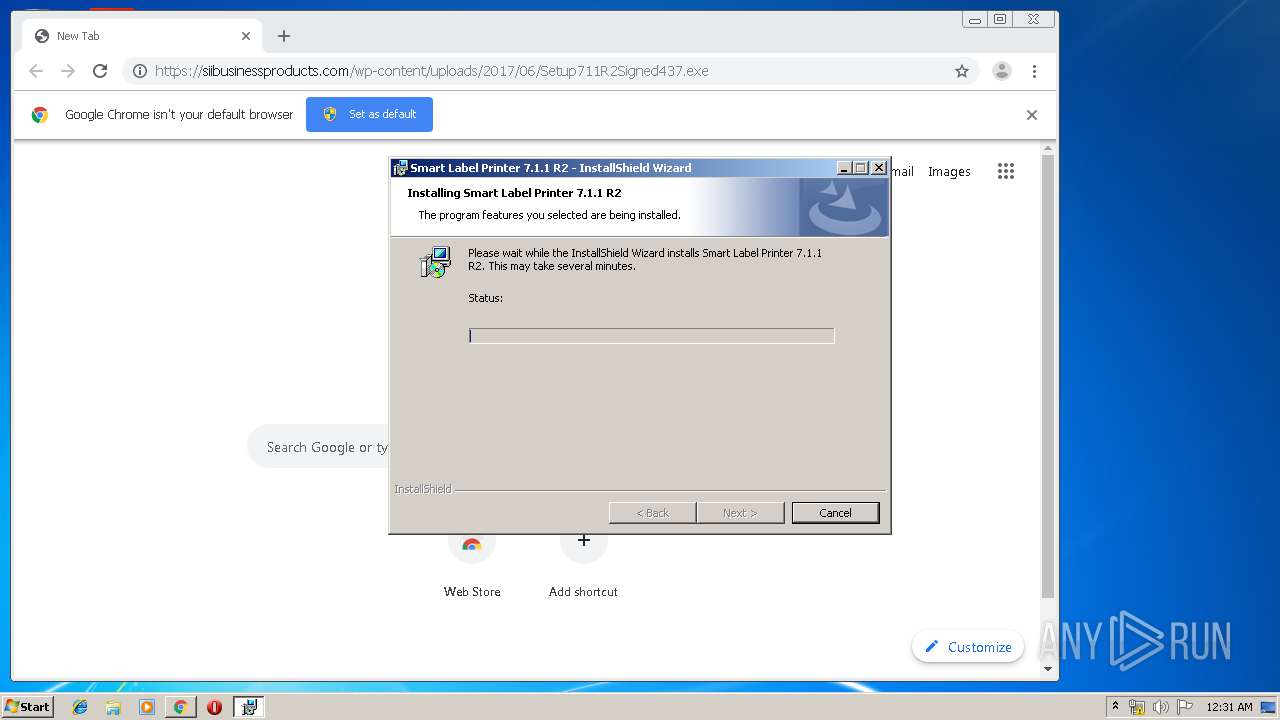
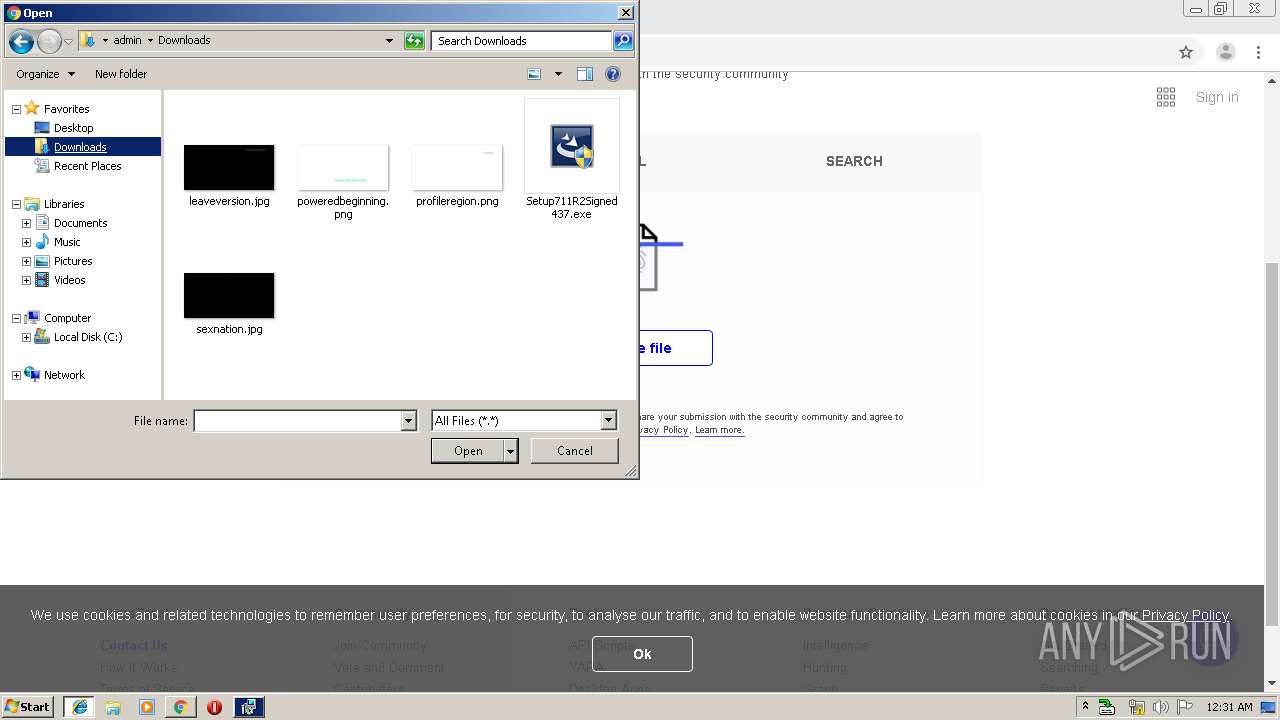
Application was dropped or rewritten from another process
- Setup711R2Signed437.exe (PID: 1792)
- Setup711R2Signed437.exe (PID: 2708)
- SlpCfgCvt.exe (PID: 2724)
- slpcap.exe (PID: 1948)
- SmartLabel.exe (PID: 284)
Changes settings of System certificates
- MSIEXEC.EXE (PID: 2720)
Writes to a start menu file
- msiexec.exe (PID: 3960)
Loads dropped or rewritten executable
- slpcap.exe (PID: 1948)
- SlpCfgCvt.exe (PID: 2724)
- SmartLabel.exe (PID: 284)
SUSPICIOUS
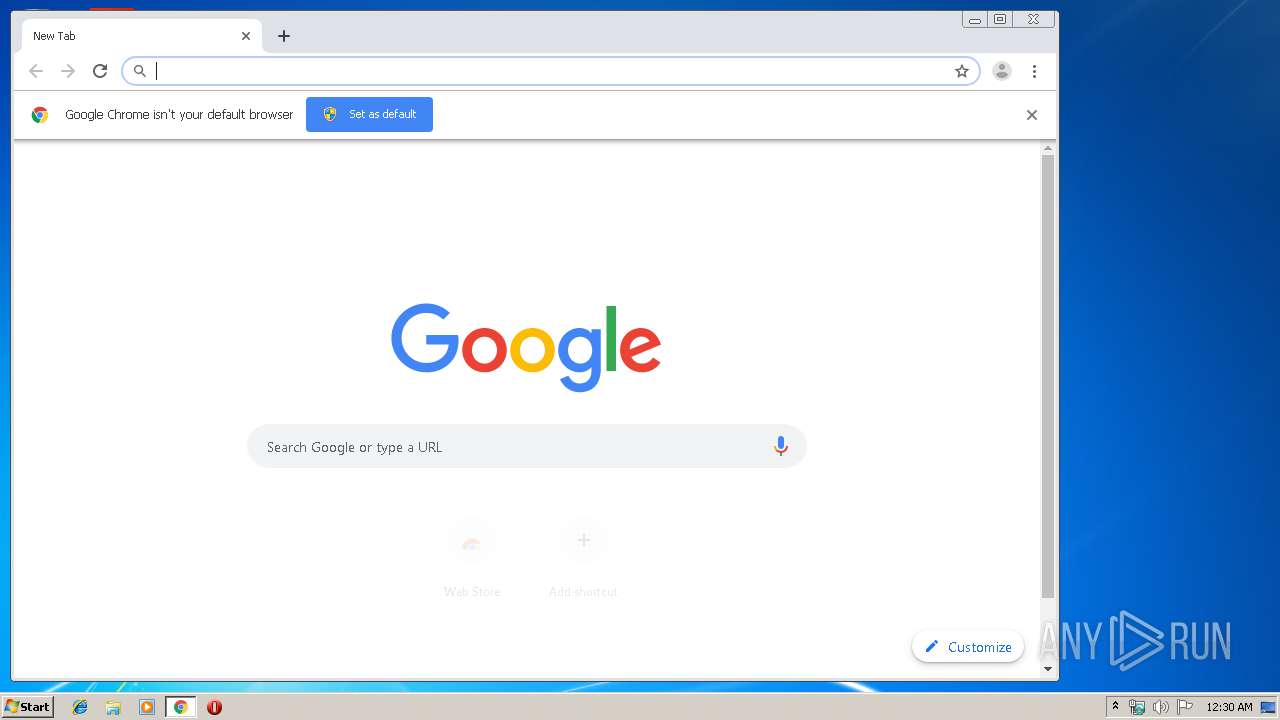
Modifies files in Chrome extension folder
- chrome.exe (PID: 2200)
Executable content was dropped or overwritten
- chrome.exe (PID: 2200)
- msiexec.exe (PID: 3960)
- MsiExec.exe (PID: 3776)
- DrvInst.exe (PID: 3584)
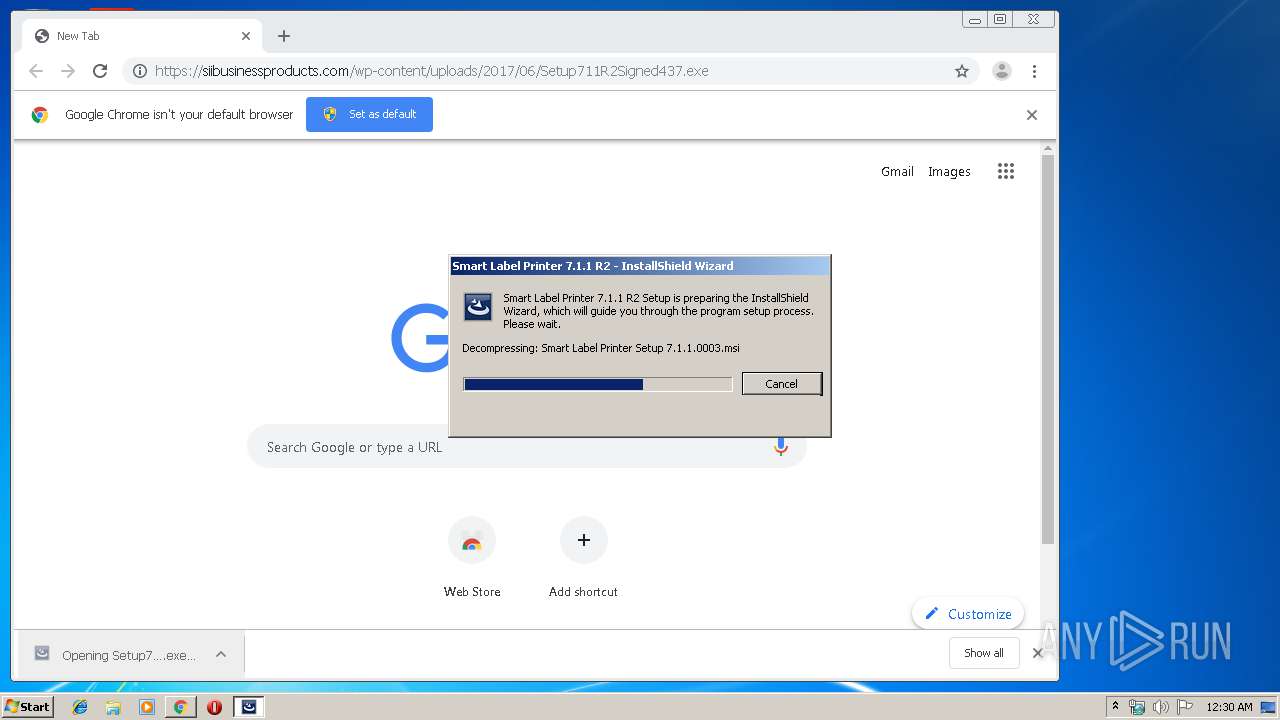
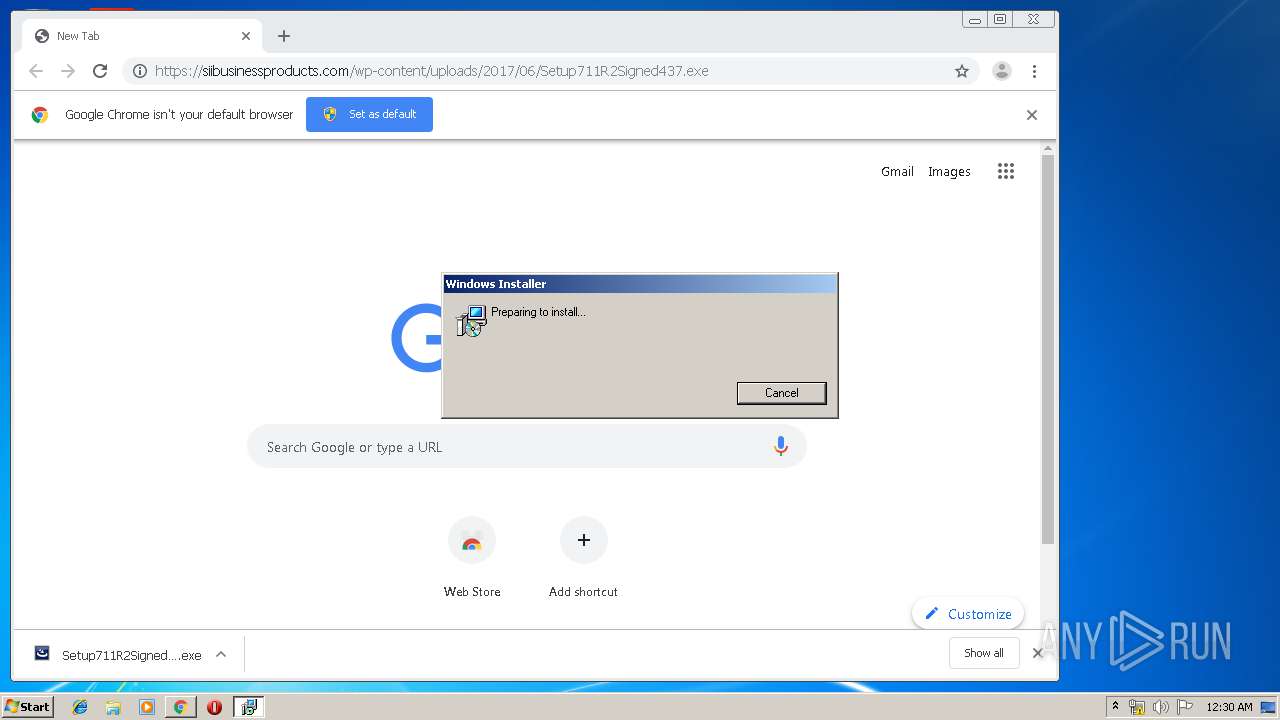
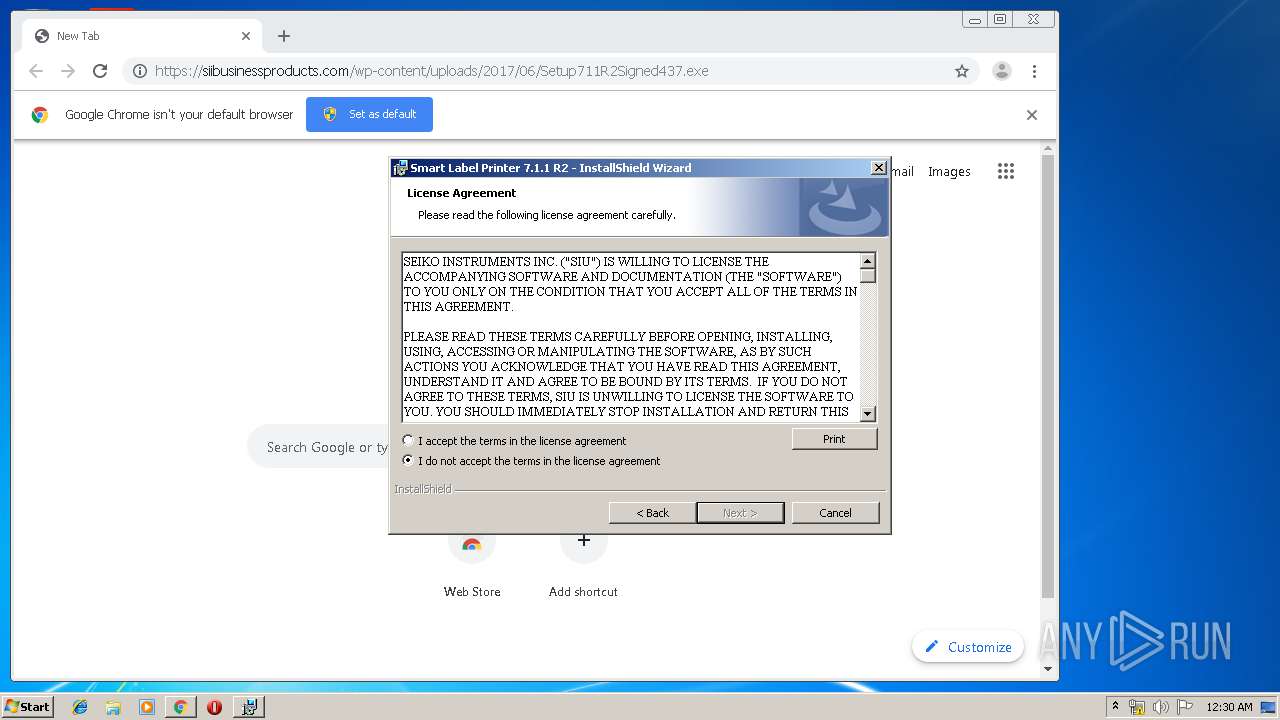
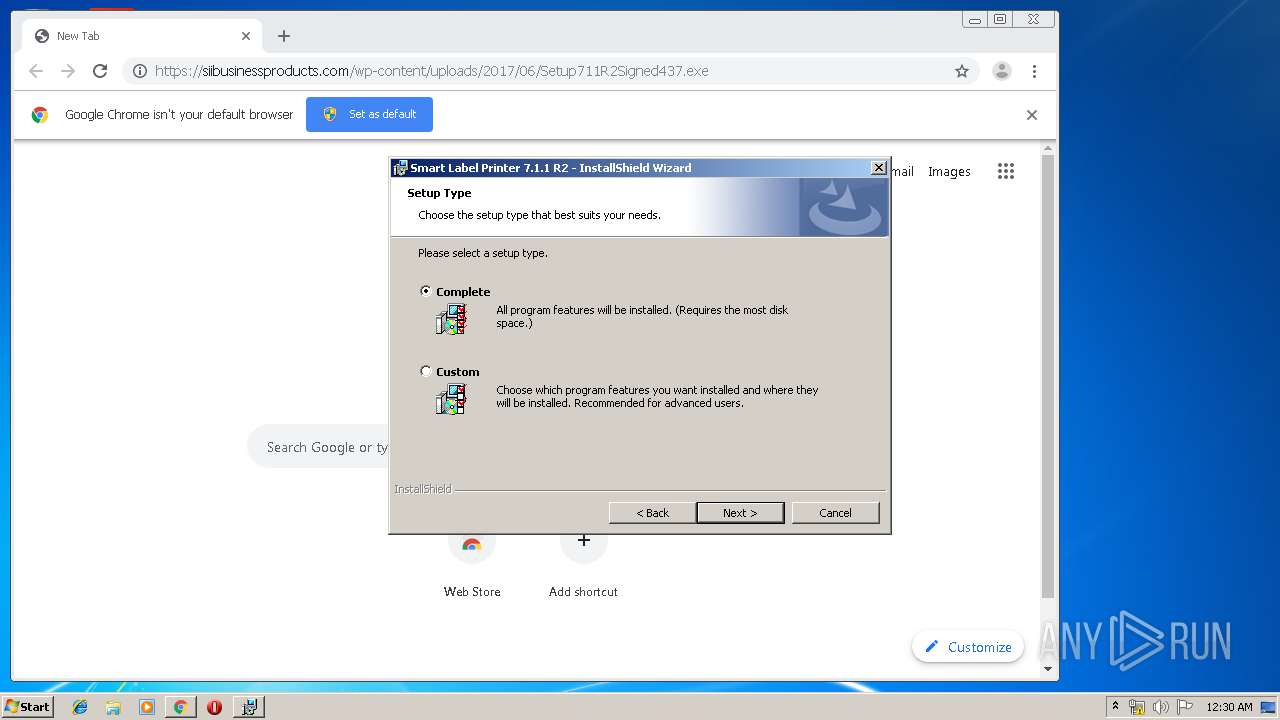
Starts Microsoft Installer
- Setup711R2Signed437.exe (PID: 2708)
Adds / modifies Windows certificates
- MSIEXEC.EXE (PID: 2720)
Creates COM task schedule object
- MsiExec.exe (PID: 3776)
- msiexec.exe (PID: 3960)
Creates files in the user directory
- msiexec.exe (PID: 3960)
- SmartLabel.exe (PID: 284)
Executed as Windows Service
- vssvc.exe (PID: 2836)
Creates files in the Windows directory
- msiexec.exe (PID: 3960)
- DrvInst.exe (PID: 3584)
Executed via COM
- DrvInst.exe (PID: 3584)
Creates files in the driver directory
- DrvInst.exe (PID: 3584)
Removes files from Windows directory
- DrvInst.exe (PID: 3584)
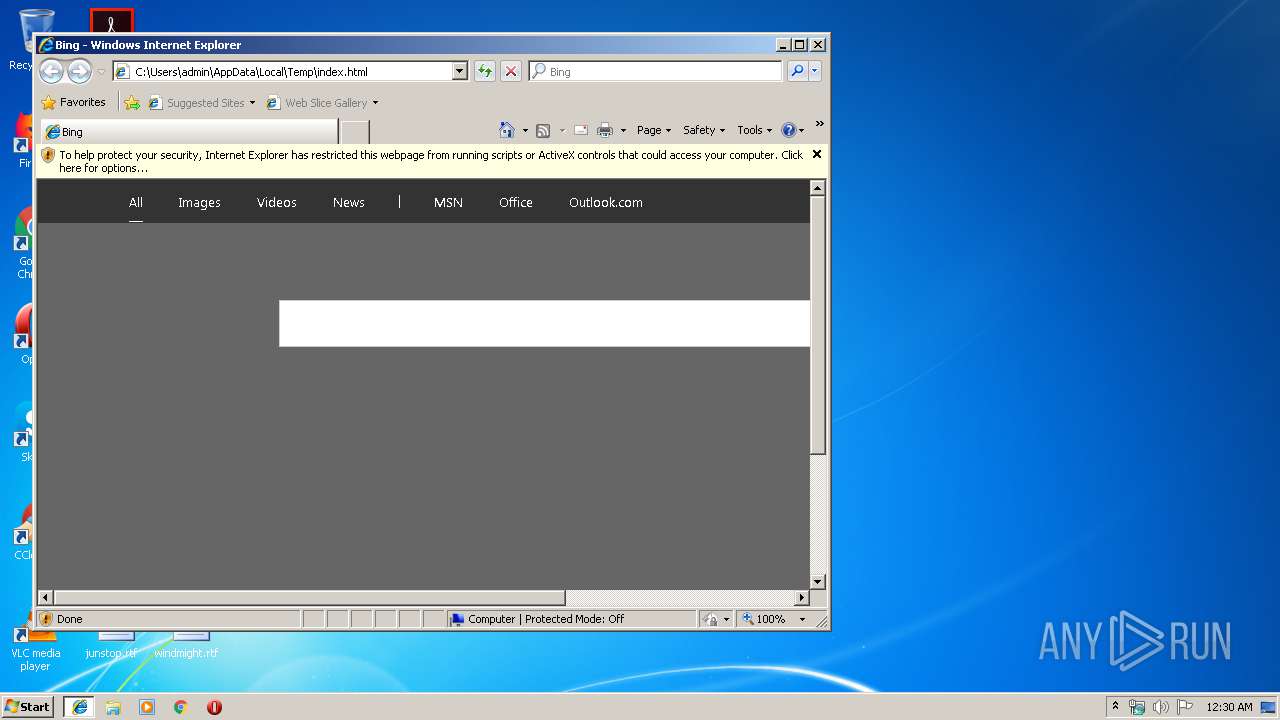
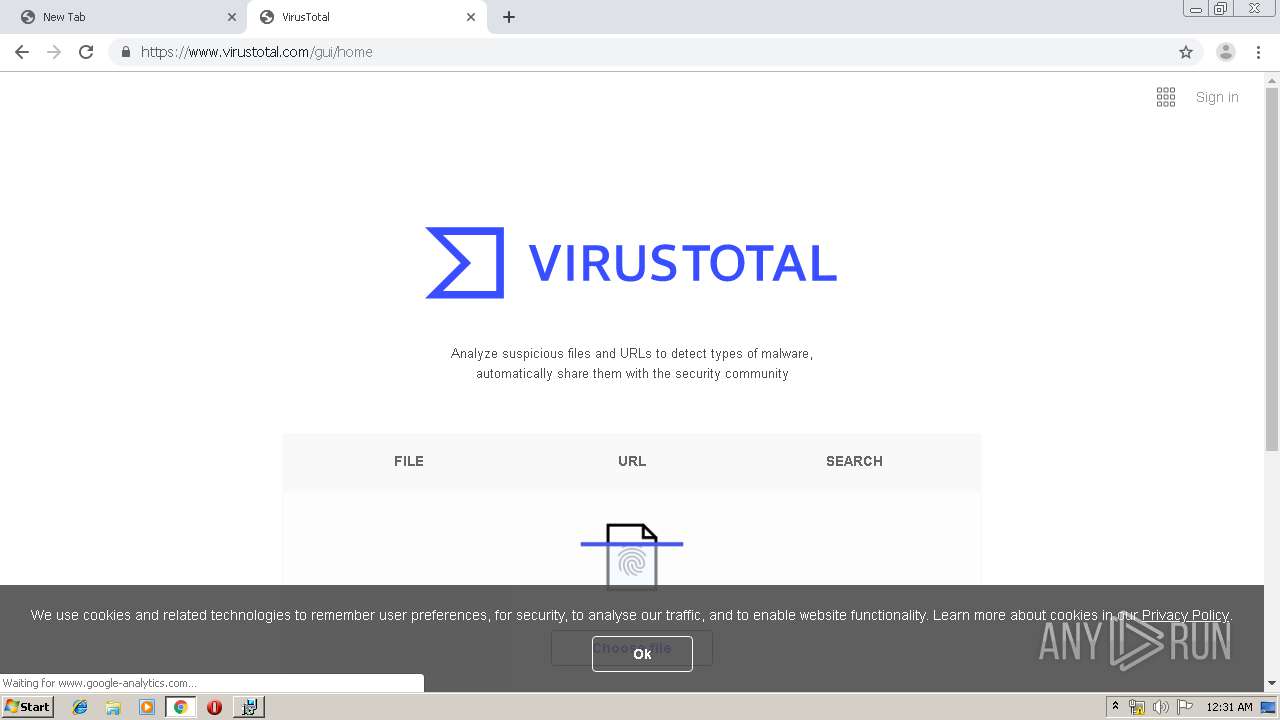
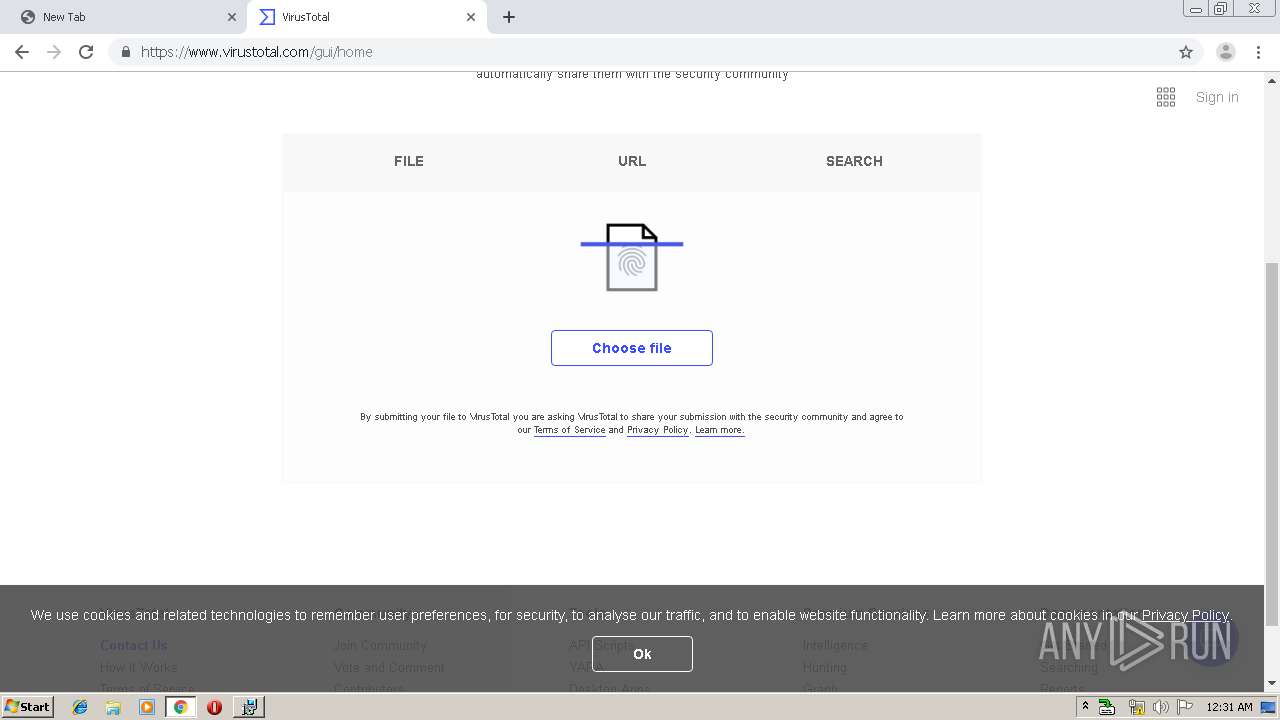
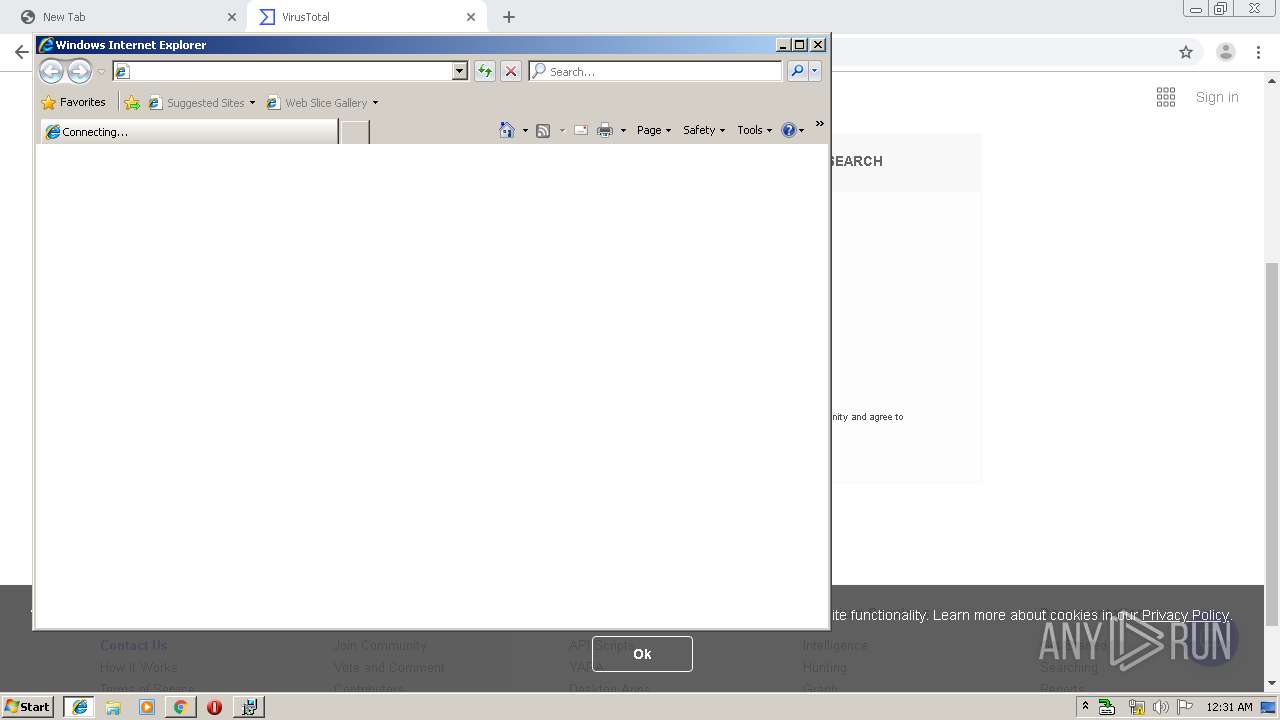
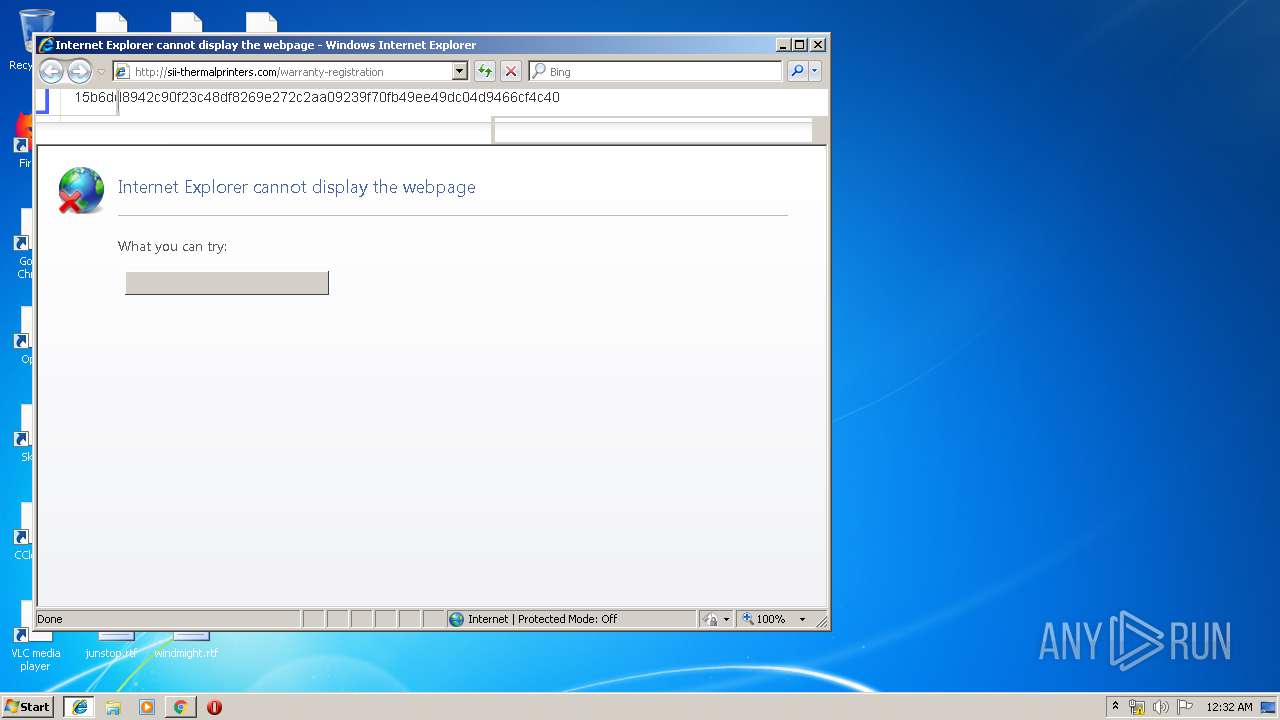
Starts Internet Explorer
- MsiExec.exe (PID: 2824)
Creates files in the program directory
- slpcap.exe (PID: 1948)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2200)
- chrome.exe (PID: 1880)
Reads the hosts file
- chrome.exe (PID: 2200)
- chrome.exe (PID: 1880)
Application launched itself
- chrome.exe (PID: 2200)
- iexplore.exe (PID: 1608)
- msiexec.exe (PID: 3960)
- iexplore.exe (PID: 3728)
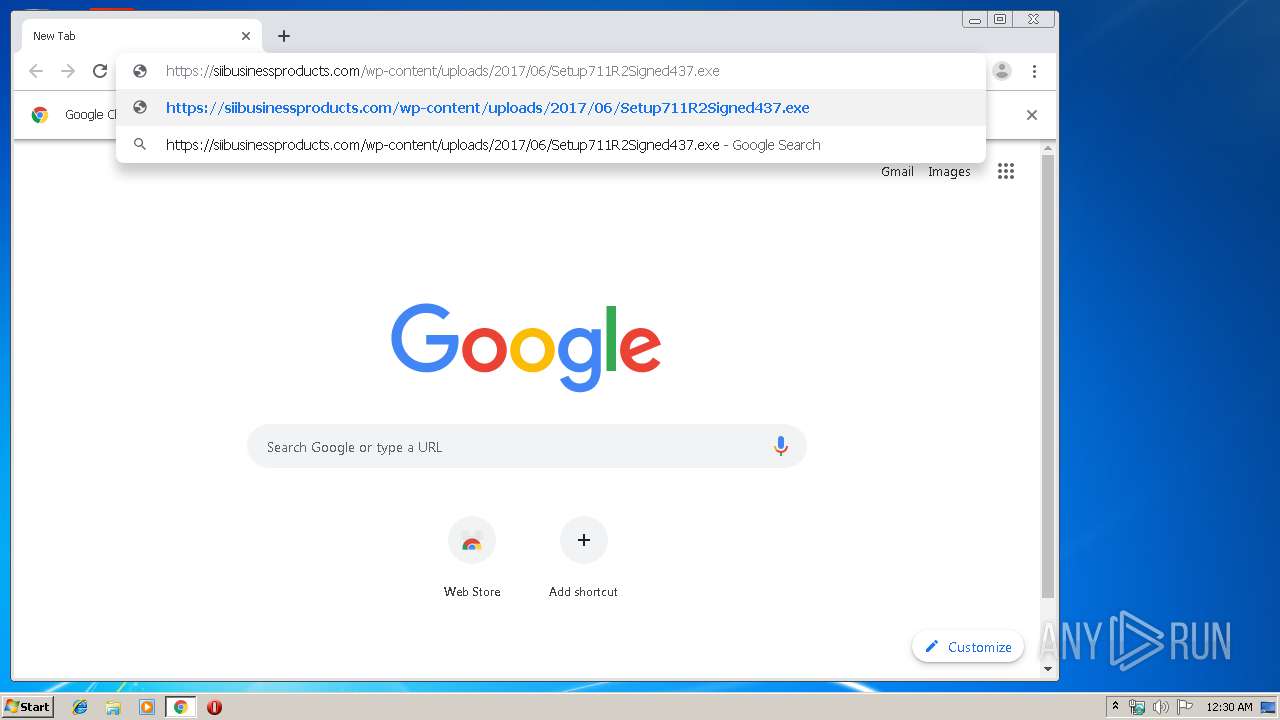
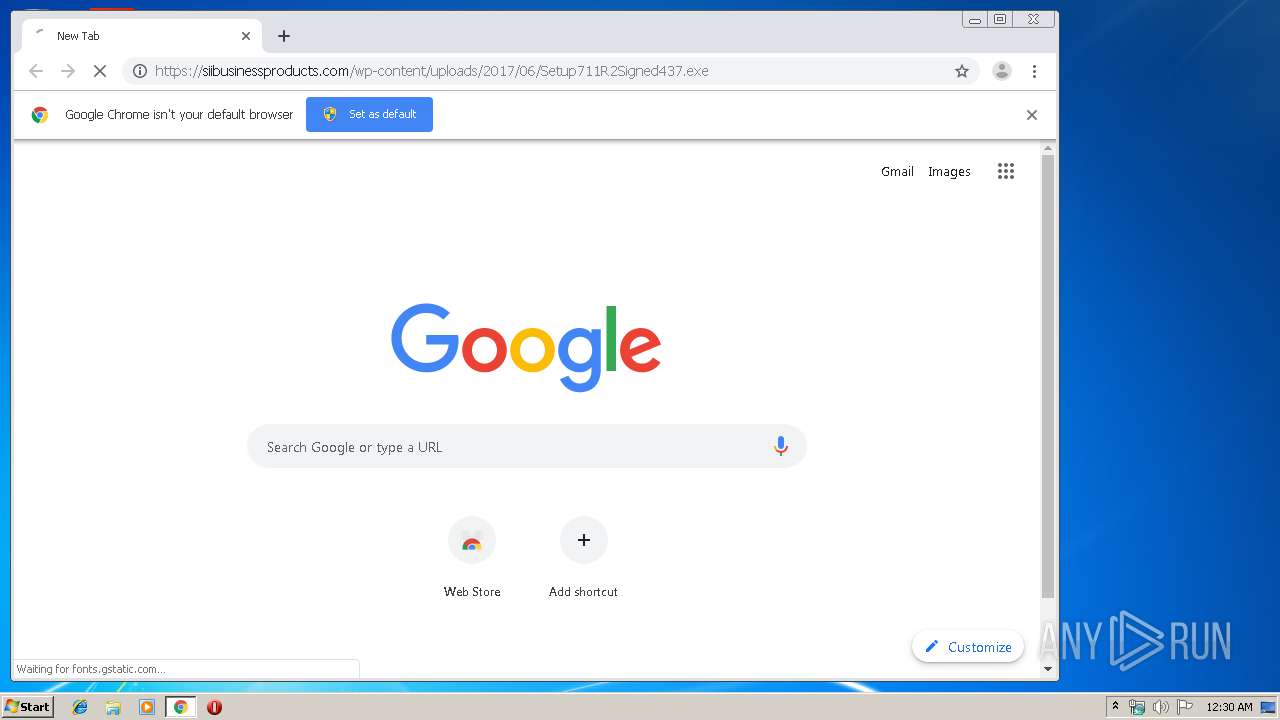
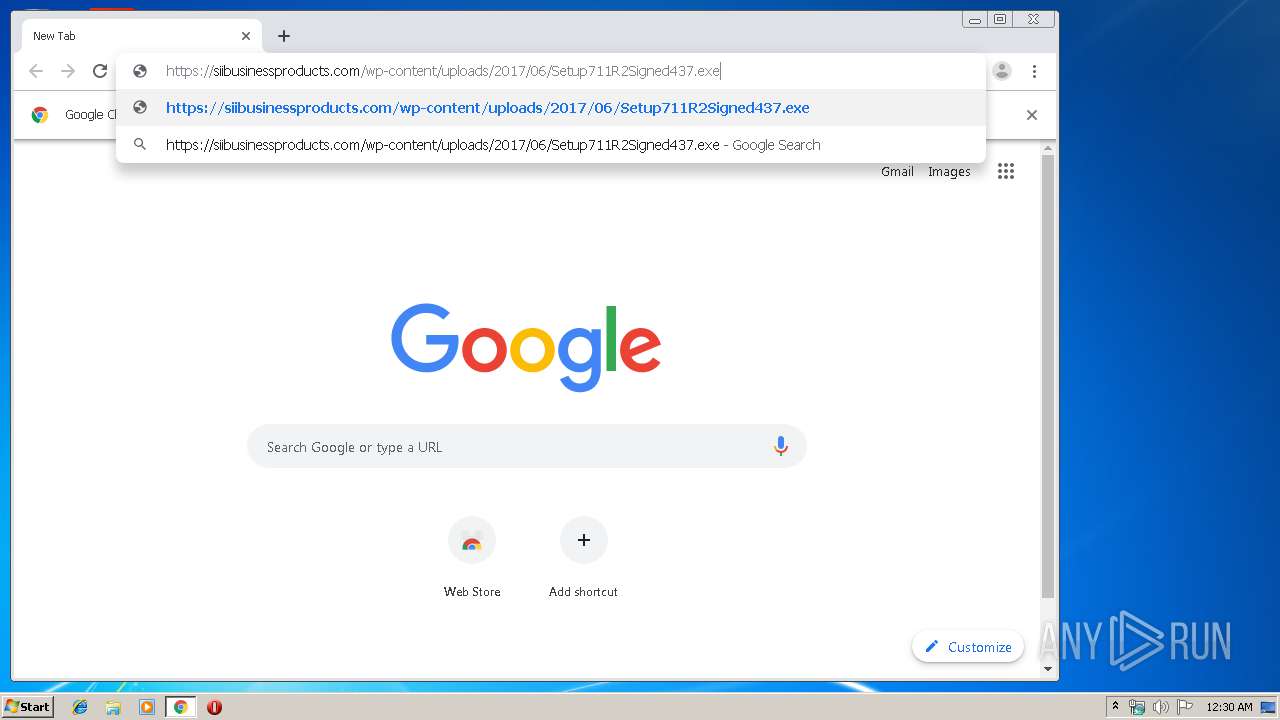
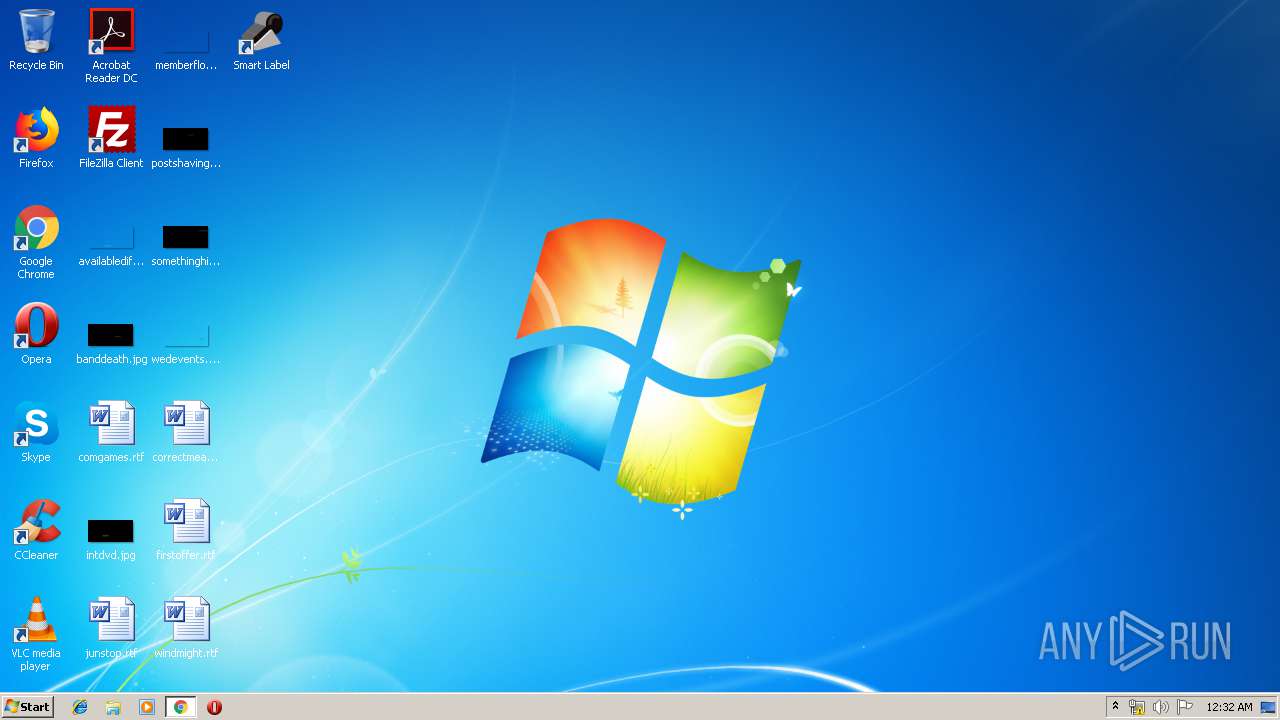
Manual execution by user
- chrome.exe (PID: 2200)
- SmartLabel.exe (PID: 284)
Reads Internet Cache Settings
- iexplore.exe (PID: 1608)
- chrome.exe (PID: 2200)
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 1764)
Reads internet explorer settings
- iexplore.exe (PID: 2428)
- iexplore.exe (PID: 1764)
Changes internet zones settings
- iexplore.exe (PID: 1608)
- iexplore.exe (PID: 3728)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2824)
- MsiExec.exe (PID: 2156)
- MsiExec.exe (PID: 3776)
Searches for installed software
- msiexec.exe (PID: 3960)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3960)
- SmartLabel.exe (PID: 284)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2836)
Creates files in the program directory
- msiexec.exe (PID: 3960)
Creates a software uninstall entry
- msiexec.exe (PID: 3960)
Creates files in the user directory
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| ContentType: | text/html; charset=utf-8 |
|---|---|
| Title: | Bing |
| Description: | Bing helps you turn information into action, making it faster and easier to go from searching to doing. |
| Robots: | NOODP |
Total processes
102
Monitored processes
56
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
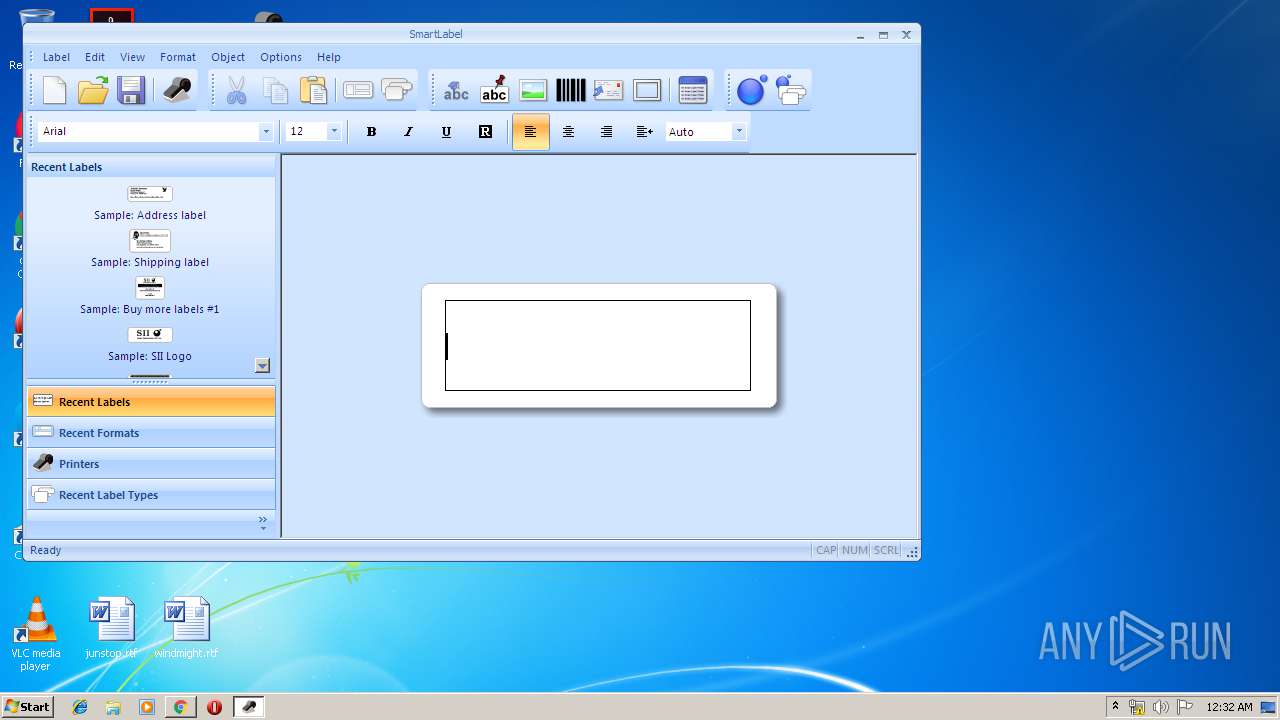
| 284 | "C:\Program Files\Seiko Instruments Inc\Smart Label Printer 7.1.1\SmartLabel.exe" | C:\Program Files\Seiko Instruments Inc\Smart Label Printer 7.1.1\SmartLabel.exe | explorer.exe | ||||||||||||
User: admin Company: Seiko Instruments Inc. Integrity Level: MEDIUM Description: Smart Label Exit code: 0 Version: 7.1.1.437 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17410371039702432414 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5843389568880023040 --mojo-platform-channel-handle=2548 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4188765587438620200 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11521381814727002652 --mojo-platform-channel-handle=3644 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7195682628699837590 --mojo-platform-channel-handle=4768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=14906715517673205437 --mojo-platform-channel-handle=4836 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,16710910886997994937,11609505605646415181,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11890202985386179383 --mojo-platform-channel-handle=4788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3728 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 585
Read events
2 696
Write events
850
Delete events
39
Modification events
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1608) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (2428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070B0004001C0000001D003700E602 | |||
| (PID) Process: | (2428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{761497BB-D6F0-462C-B6EB-D4DAF1D92D43}\iexplore |
| Operation: | write | Name: | LoadTime |
Value: 8 | |||
| (PID) Process: | (2428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{B4F3A835-0E21-4959-BA22-42B3008E02FF}\iexplore |
| Operation: | write | Name: | Type |
Value: 3 | |||
| (PID) Process: | (2428) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{B4F3A835-0E21-4959-BA22-42B3008E02FF}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
Executable files
74
Suspicious files
123
Text files
507
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF640F341CD4678B2B.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD4EDA9098326B702.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9CDE56BDB118BE48.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{32B23C7E-1176-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFE9EB2348183C6B51.TMP | — | |
MD5:— | SHA256:— | |||
| 1608 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{32B23C7D-1176-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\37f4b50a-fe9b-47e7-8caa-d2efb45e13fb.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
39
DNS requests
30
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
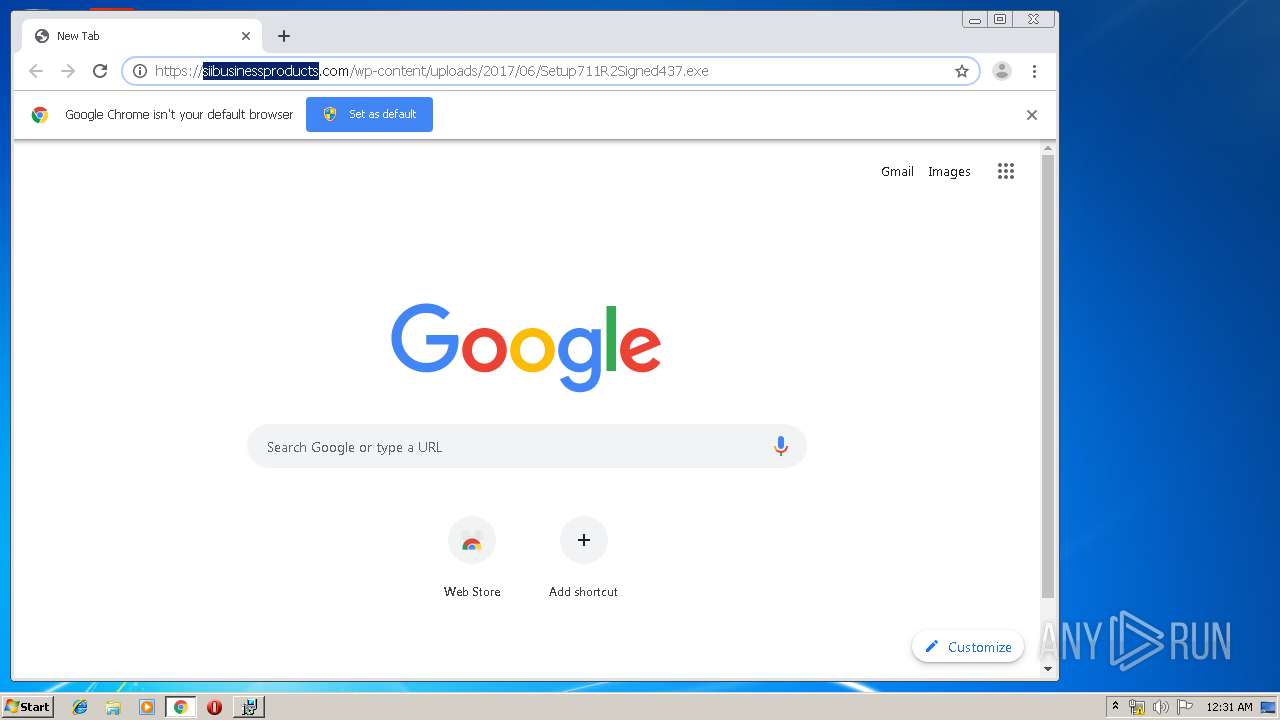
1764 | iexplore.exe | GET | 301 | 148.72.10.61:80 | http://sii-thermalprinters.com/warranty-registration | US | — | — | malicious |
1880 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
1880 | chrome.exe | GET | 200 | 74.125.97.138:80 | http://r5---sn-h5q7kne6.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.253.99.196&mm=28&mn=sn-h5q7kne6&ms=nvh&mt=1574900901&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
1880 | chrome.exe | GET | 200 | 8.253.95.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 57.4 Kb | whitelisted |
1880 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
1880 | chrome.exe | GET | 200 | 74.125.168.39:80 | http://r2---sn-h5q7knee.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.253.99.196&mm=28&mn=sn-h5q7knee&ms=nvh&mt=1574900901&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
1880 | chrome.exe | GET | 200 | 8.253.95.120:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
1608 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1608 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1880 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.21.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 216.58.206.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 216.58.208.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 74.125.168.39:80 | r2---sn-h5q7knee.gvt1.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.23.174:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
clients2.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
r2---sn-h5q7knee.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
slpcap.exe | SLPCAP [DEBUG] Loading SLPUTIL.DLL... (SlpLib.cpp:LogMessages:569)
|
slpcap.exe | SLPCAP [DEBUG] PrivateDocuments path == 'C:\Users\admin\Documents' (SlpLib.cpp:LogMessages:569)
|
slpcap.exe | SLPCAP [DEBUG] PublicDocuments path == 'C:\Users\Public\Documents' (SlpLib.cpp:LogMessages:569)
|
slpcap.exe | SLPCAP [DEBUG] PublicData path == 'C:\ProgramData' (SlpLib.cpp:LogMessages:569)
|
slpcap.exe | SLPCAP [DEBUG] PrivateData path == 'C:\Users\admin\AppData\Roaming' (SlpLib.cpp:LogMessages:569)
|
slpcap.exe | SLPCAP [ INFO] Loading C:\Program Files\Seiko Instruments Inc\Smart Label Printer 7.1.1\SlpUtil.dll (7.1.1.437)... (MESSAGES.CPP:DiagShowModuleLoadPathEx:695)
|
slpcap.exe | SLPCAP [ INFO] Loading C:\Program Files\Seiko Instruments Inc\Smart Label Printer 7.1.1\slpcap.exe (7.1.1.437)... (MESSAGES.CPP:DiagShowModuleLoadPathEx:695)
|
slpcap.exe | SLPCAP [DEBUG] GetLocalFileName('C:\Program Files\Seiko Instruments Inc\Smart Label Printer 7.1.1\SmartLabelENU.DLL') == 1 (SlpLib.cpp:GetLocalFileName:335)
|
slpcap.exe | SLPCAP [ INFO] Local language is: ENU (SlpLib.cpp:GetLocalFileName:367)
|
slpcap.exe | SLPCAP [DEBUG] Loading DLL 'C:\Program Files\Seiko Instruments Inc\Smart Label Printer 7.1.1\SmartLabelENU.DLL'... (SlpLib.cpp:LoadDLL:420)
|