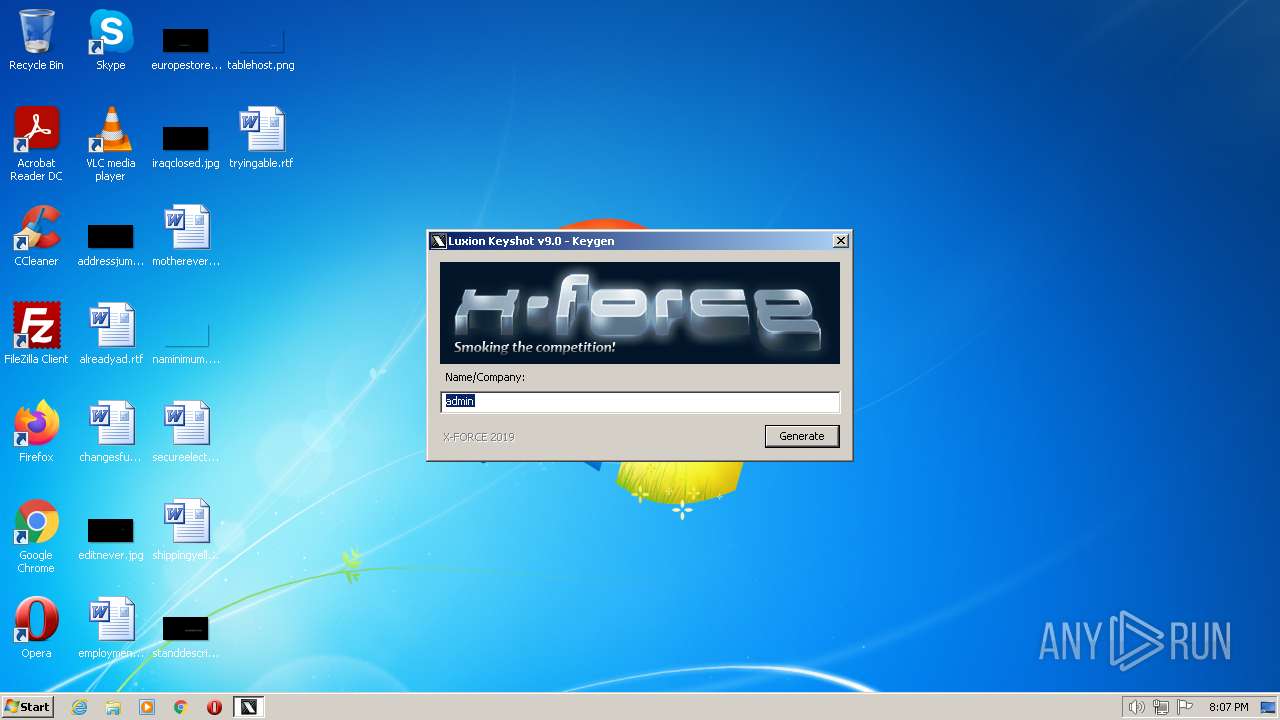
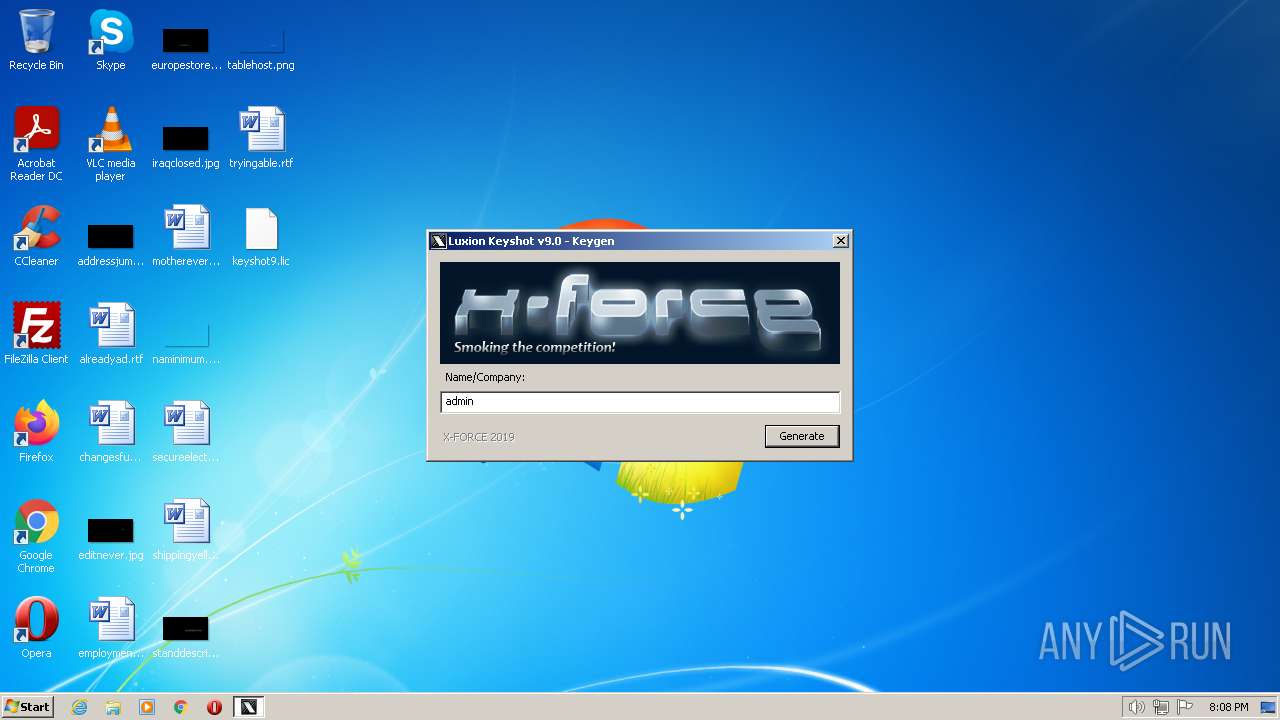
| File name: | keygen KeyShot v9.0 - MOD by YOLAWS.exe |
| Full analysis: | https://app.any.run/tasks/4c83a8ce-b54a-42d2-8af0-eea8946fc18a |
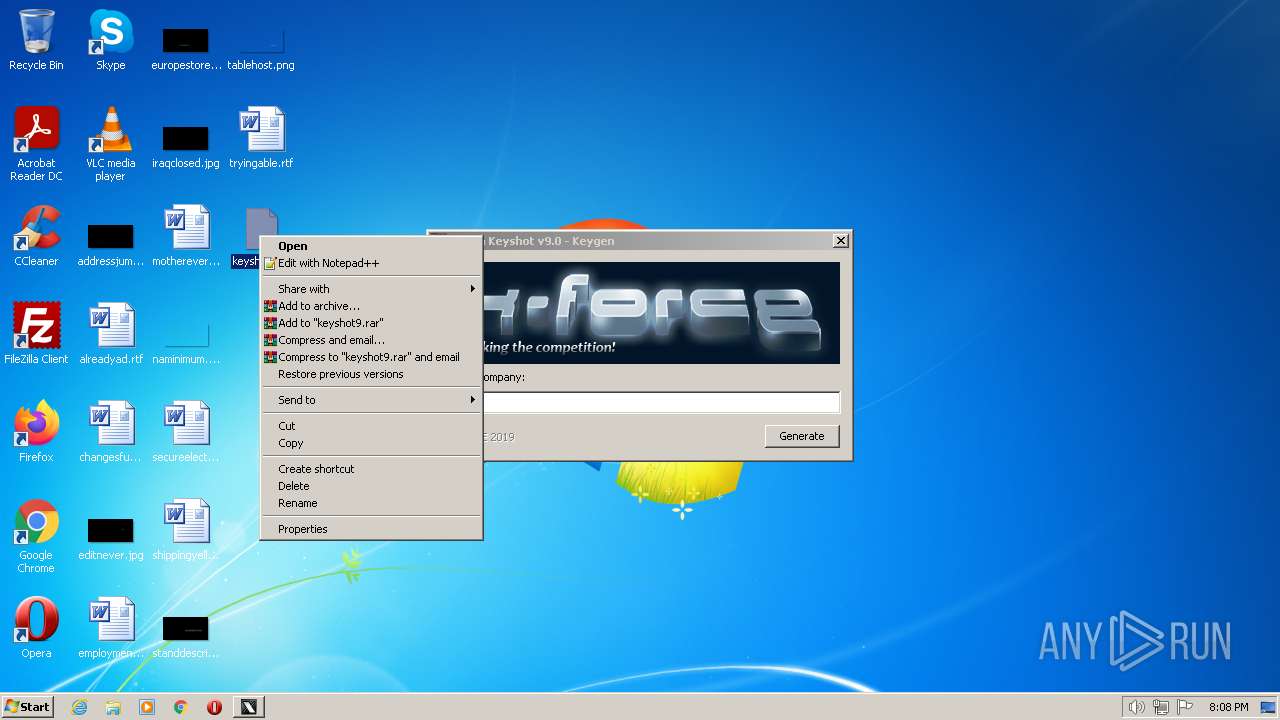
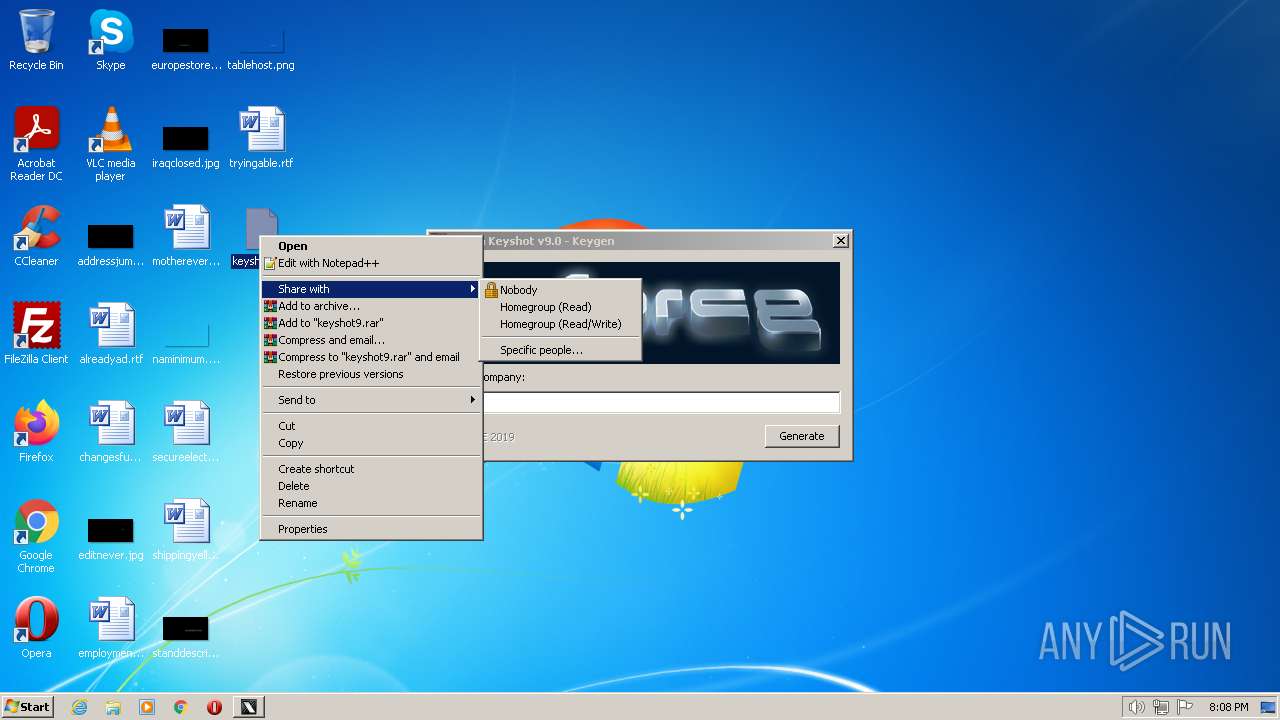
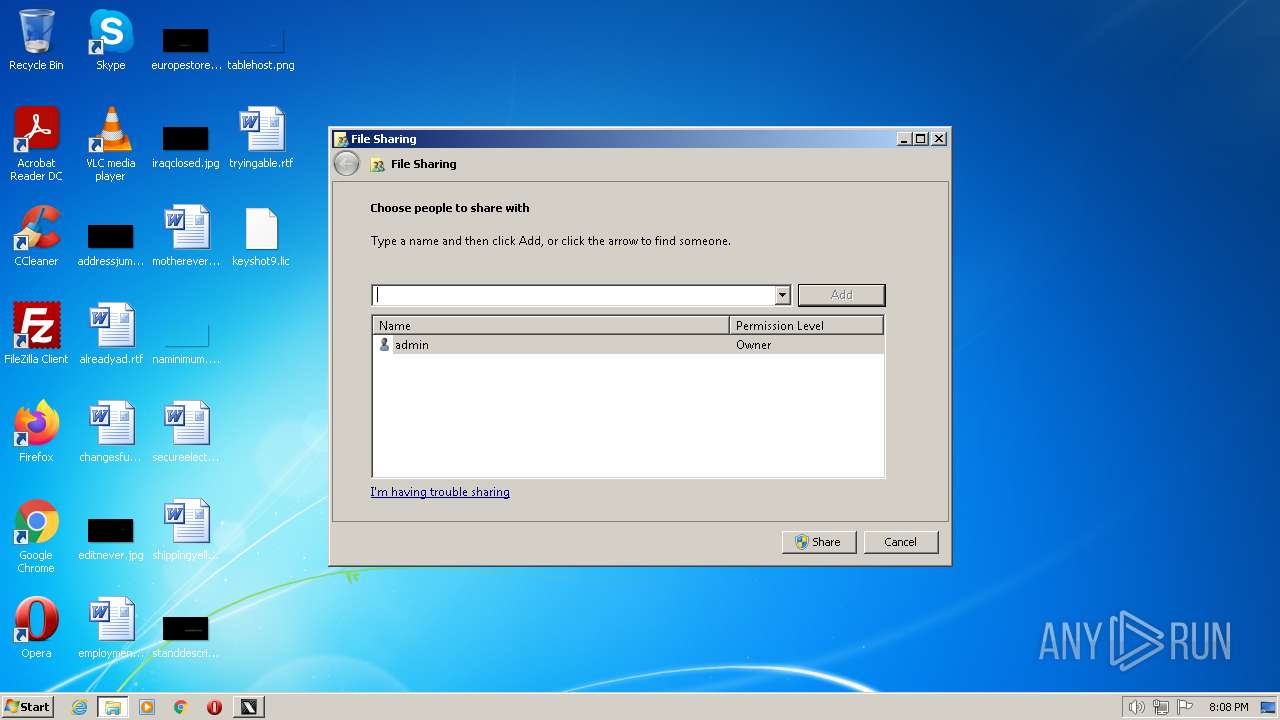
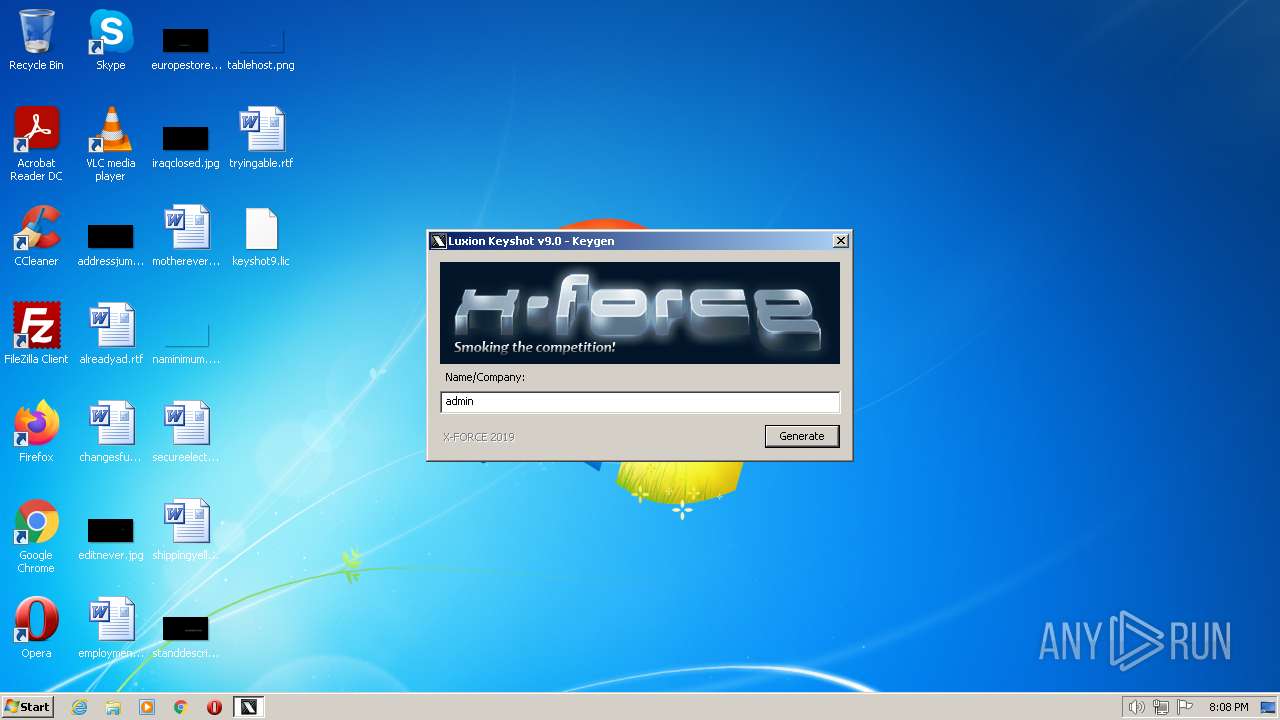
| Verdict: | Malicious activity |
| Analysis date: | February 28, 2023, 20:07:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6A928467B3AB5EF5174A733E2495DDEC |
| SHA1: | 73B59860A71ED7342A780E516F1B90EAD49FADA6 |
| SHA256: | 9072EB37FED42A7F9BF5886DBD425BB7D485813A77225B6AF1CFA4C2D75522FF |
| SSDEEP: | 12288:zxmtef37XjxOStxd/XpNe2opRzeOY+VnBnjlw+PVXKQQ:zxmm37lFropRz1ZdBnRw+PY |
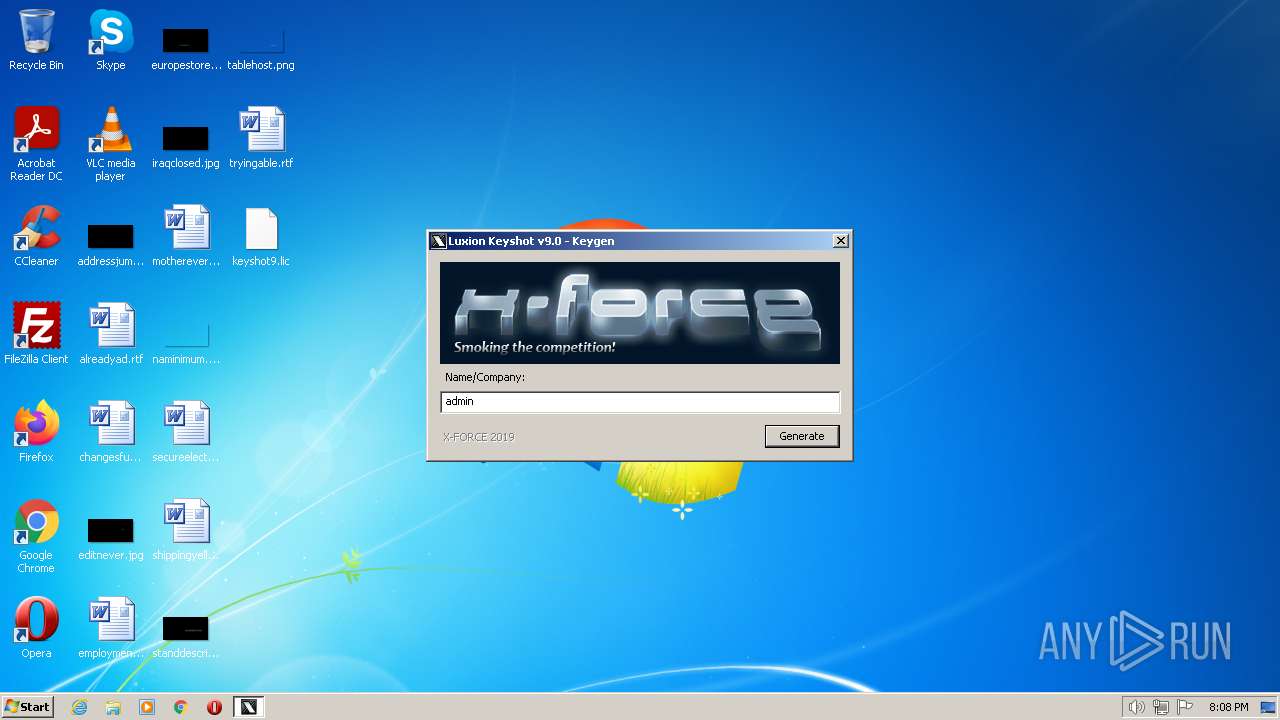
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- keygen KeyShot v9.0 - MOD by YOLAWS.exe (PID: 3452)
INFO
Reads the computer name
- keygen KeyShot v9.0 - MOD by YOLAWS.exe (PID: 3452)
Checks supported languages
- keygen KeyShot v9.0 - MOD by YOLAWS.exe (PID: 3452)
Reads the machine GUID from the registry
- keygen KeyShot v9.0 - MOD by YOLAWS.exe (PID: 3452)
The process checks LSA protection
- keygen KeyShot v9.0 - MOD by YOLAWS.exe (PID: 3452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x48649 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 278016 |
| CodeSize: | 396800 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2013:03:11 21:35:19+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 11-Mar-2013 21:35:19 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 11-Mar-2013 21:35:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00060D68 | 0x00060E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64787 |
.rdata | 0x00062000 | 0x00023A90 | 0x00023C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39591 |
.data | 0x00086000 | 0x00005F24 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.71532 |
.rsrc | 0x0008C000 | 0x0000BD28 | 0x0000BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.25867 |
.reloc | 0x00098000 | 0x0000E2CA | 0x0000E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.31556 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.85183 | 4264 | UNKNOWN | French - France | RT_ICON |
101 | 3.24269 | 308 | UNKNOWN | French - France | RT_DIALOG |
102 | 6.01782 | 41862 | UNKNOWN | French - France | RT_BITMAP |
104 | 2.21059 | 34 | UNKNOWN | French - France | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMDLG32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
USER32.dll |
Total processes
39
Monitored processes
2
Malicious processes
1
Suspicious processes
0
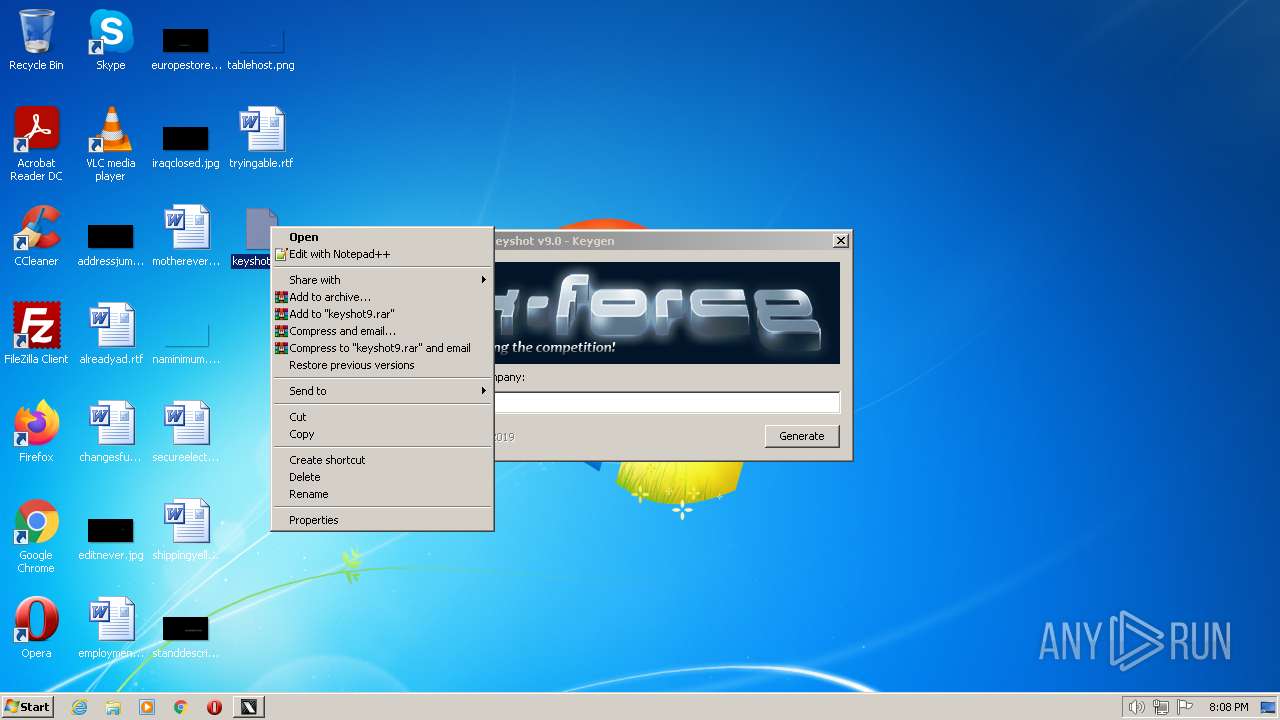
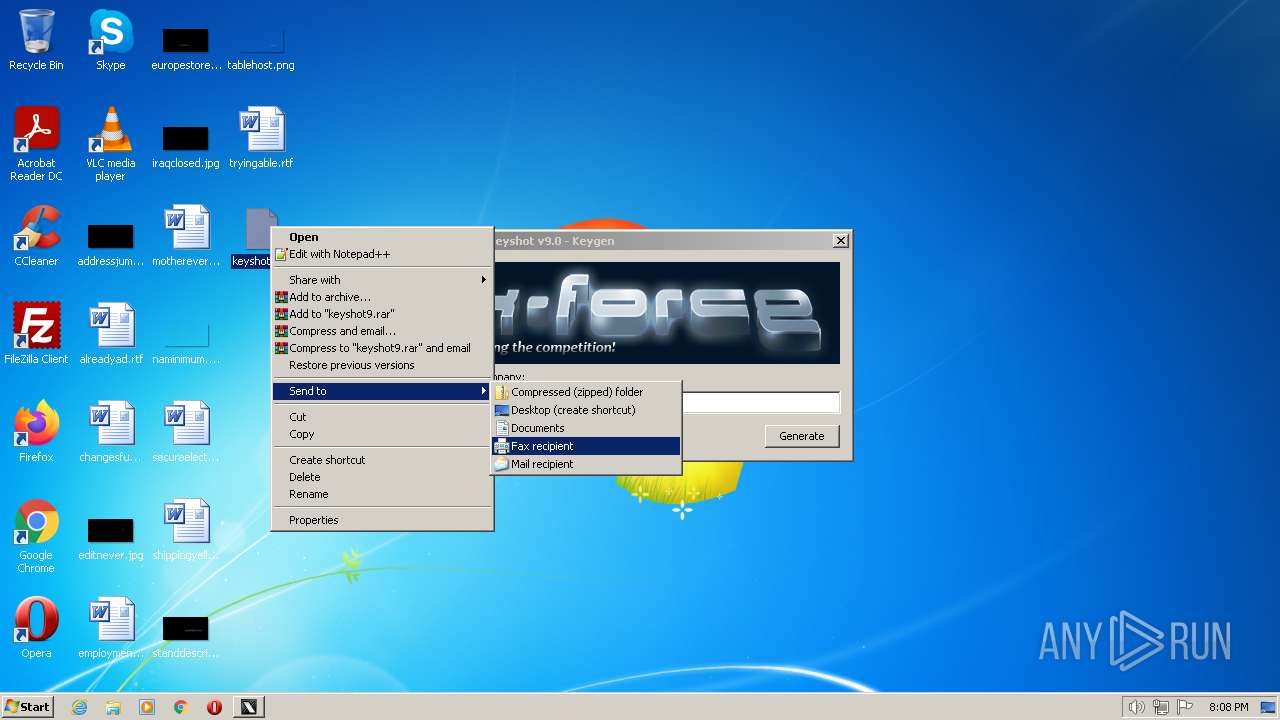
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
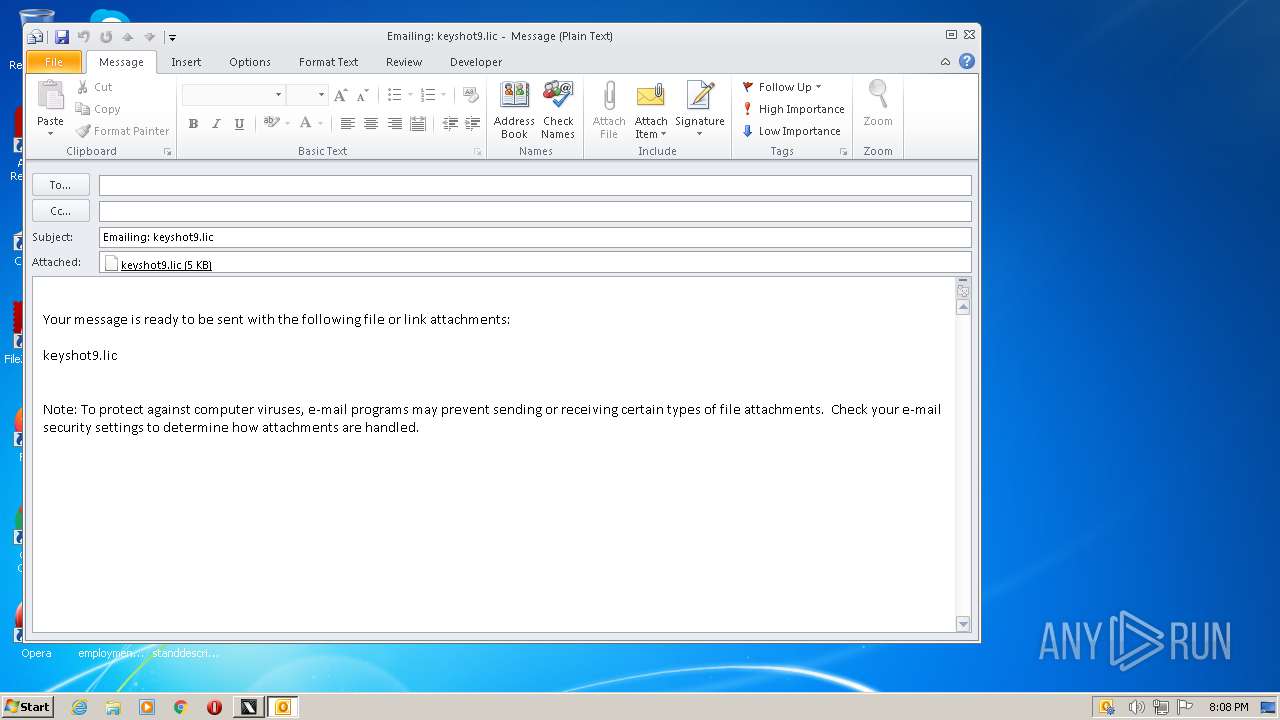
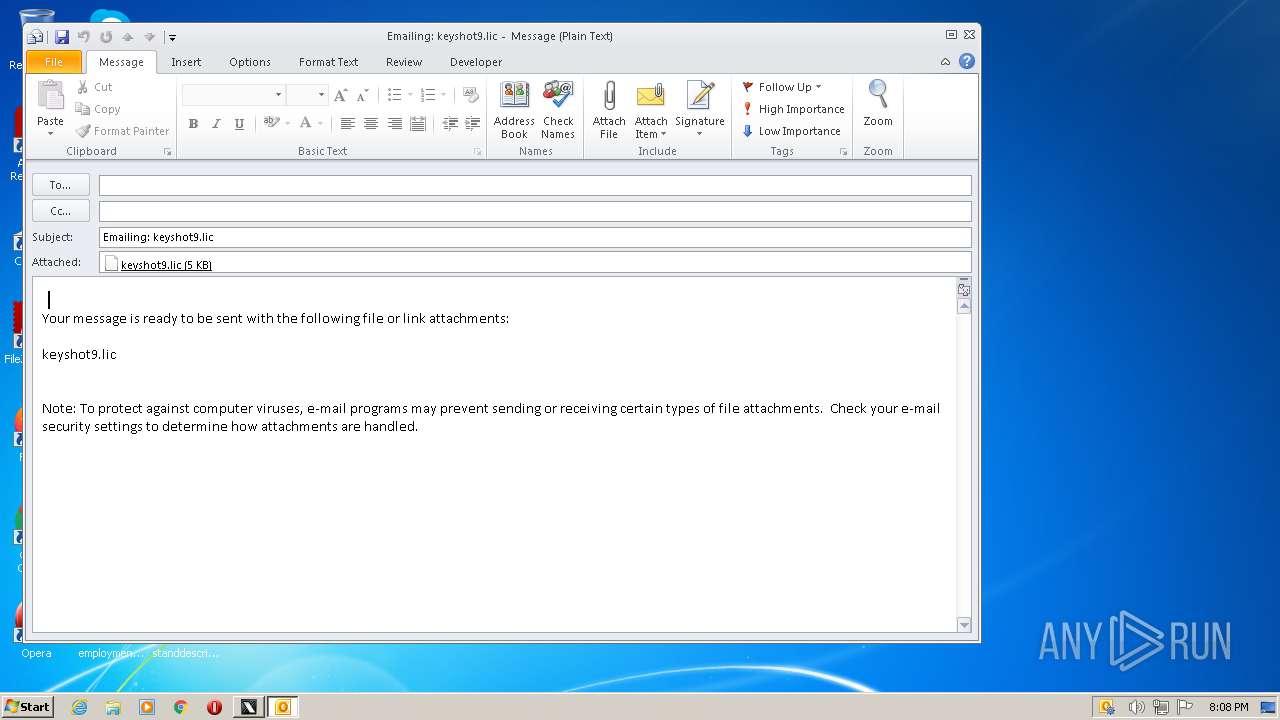
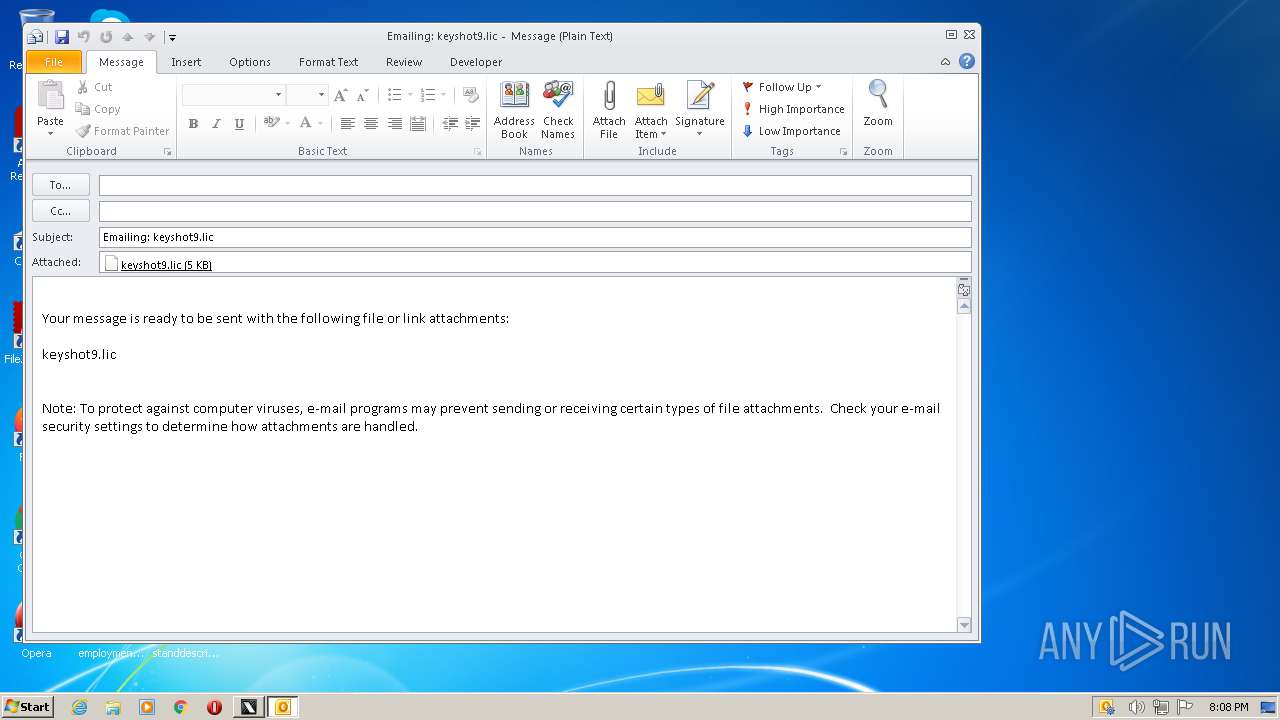
| 3316 | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE -Embedding | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3452 | "C:\Users\admin\AppData\Local\Temp\keygen KeyShot v9.0 - MOD by YOLAWS.exe" | C:\Users\admin\AppData\Local\Temp\keygen KeyShot v9.0 - MOD by YOLAWS.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
10 732
Read events
9 566
Write events
1 112
Delete events
54
Modification events
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 020000000C000000000000000B000000010000000D00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (3452) keygen KeyShot v9.0 - MOD by YOLAWS.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
0
Suspicious files
10
Text files
4
Unknown types
4
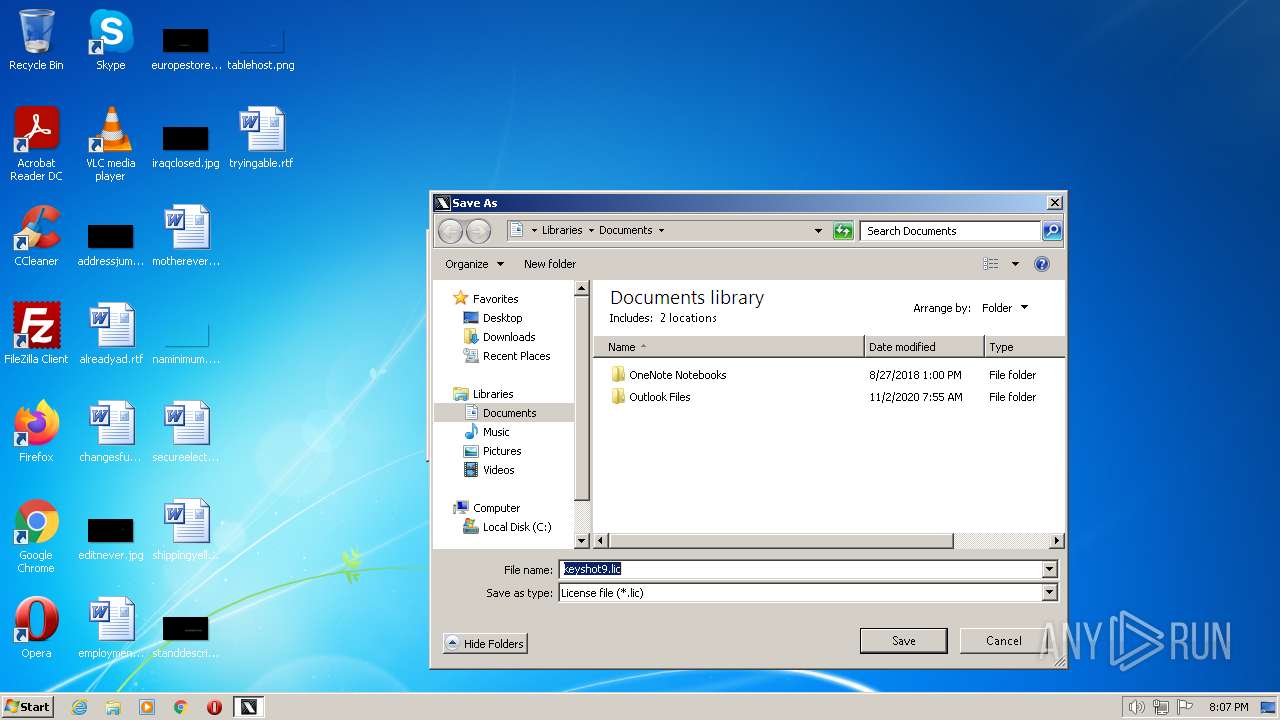
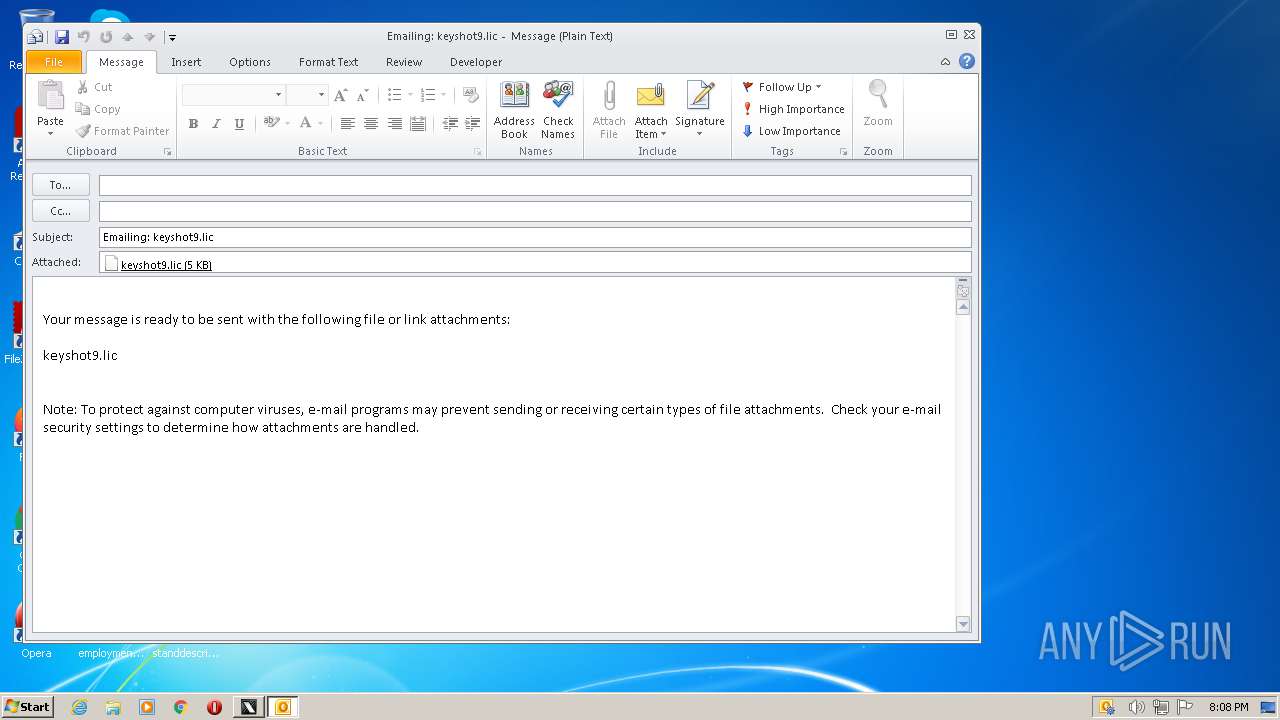
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR72C7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
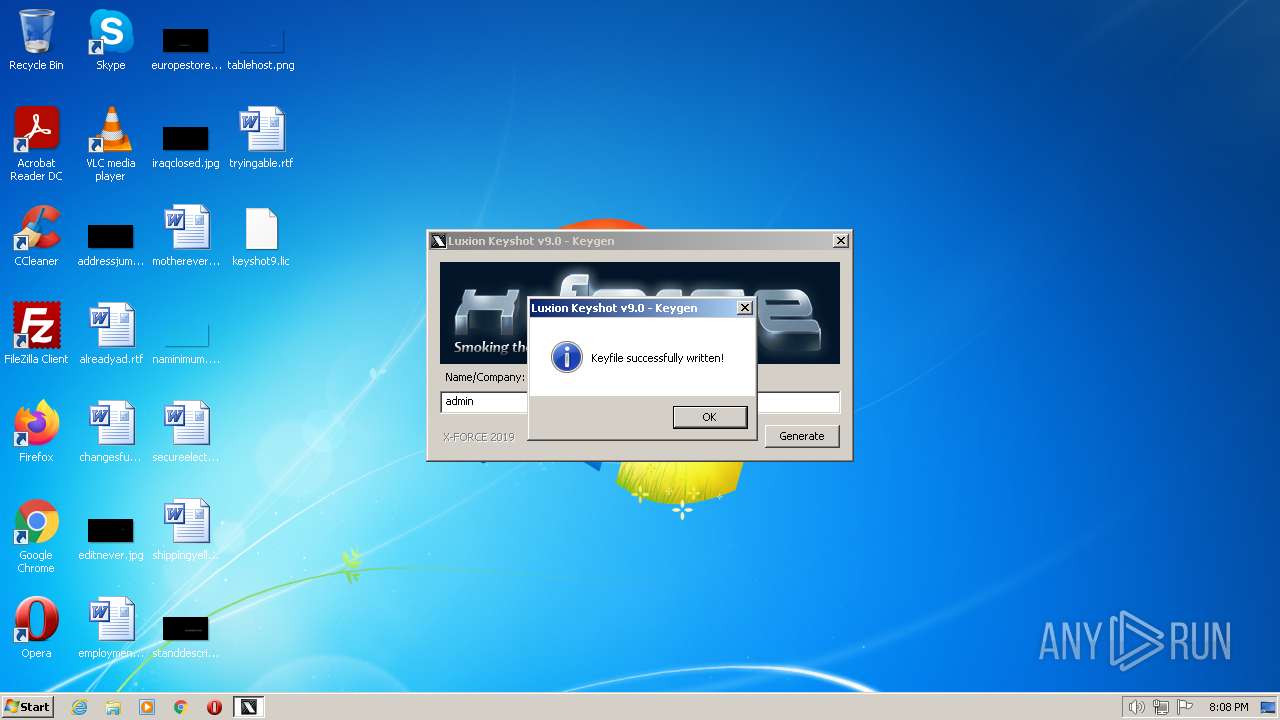
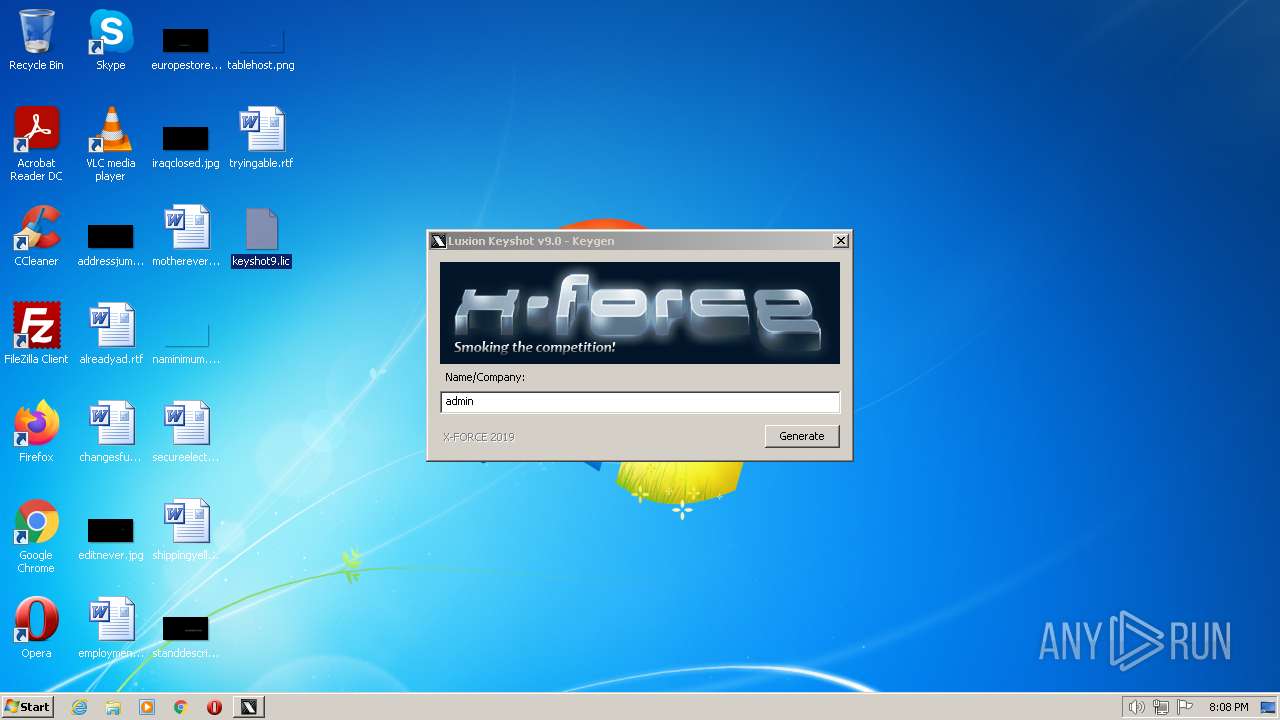
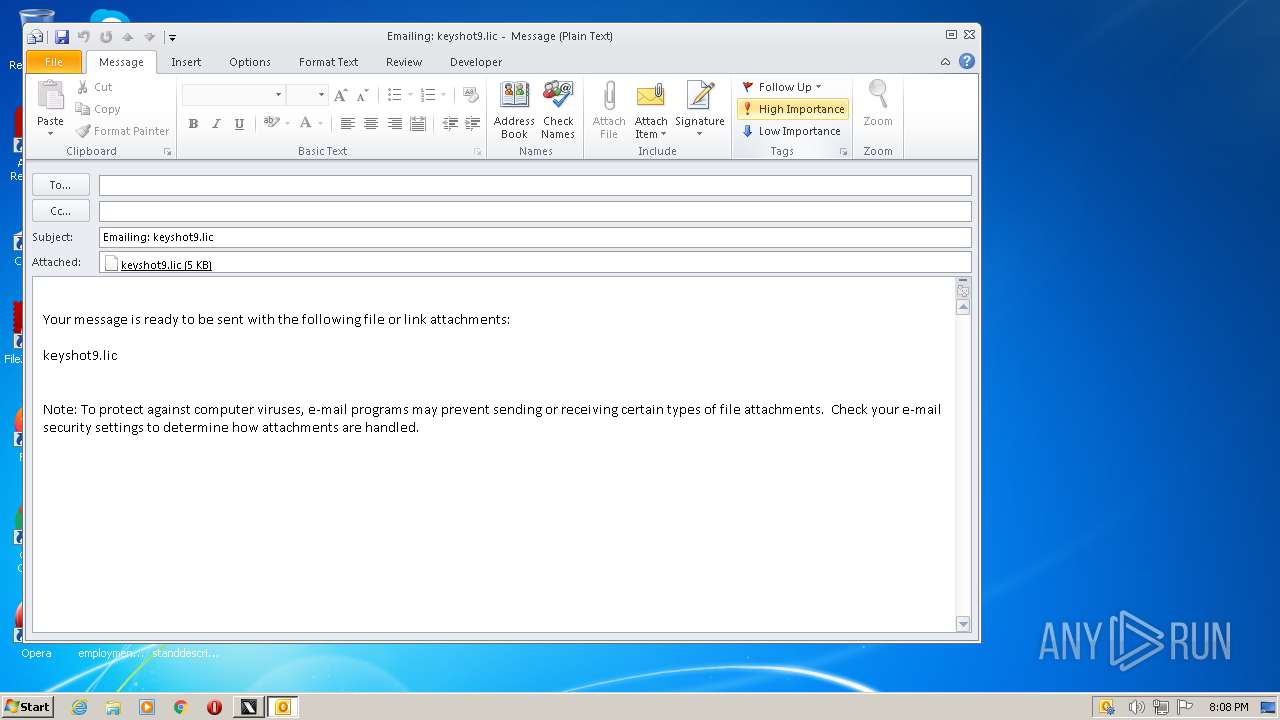
| 3452 | keygen KeyShot v9.0 - MOD by YOLAWS.exe | C:\Users\admin\Desktop\keyshot9.lic | binary | |
MD5:AB7527A7056BD803F0F835A3590403B6 | SHA256:E1C8EBA66909744BBAE9F7AE0448266DBFF04797C0BB08DC73BD99D0A4C15E81 | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | binary | |
MD5:962C6E2C5543789F7B262CBD5F159A85 | SHA256:F74F2A1A6D2B00640C0A1E9732A0DB3048E0B7E168C6C3E686A12C8F6F1ADEDB | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:6B7636A68C7197939ED0127021C790B5 | SHA256:0D449353BA8B7B5F0BF23440E9E24C8D8E9D8E1B14F87D7A04667E19587BA519 | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:2B9B2BA1F7B07815A627D812AB27EDF9 | SHA256:C3CA35E871475CFA541A1012C455FD7E5A6659DB1332C71158546F1B5AFE5C00 | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~WRD0000.tmp | document | |
MD5:3BC0BFE45D15EEFF6E83E2F4F518A4FA | SHA256:62613FF37EB90861D749B823C16396A2440DFE2ABDE25F673E48CE2C6EEC687C | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\NormalEmail.dotm | document | |
MD5:3BC0BFE45D15EEFF6E83E2F4F518A4FA | SHA256:62613FF37EB90861D749B823C16396A2440DFE2ABDE25F673E48CE2C6EEC687C | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3316 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~WRL0001.tmp | document | |
MD5:5A154DF961EE464DEAD4DA3A0E713FE3 | SHA256:C8F044761493937003C21164C6687D4F30A45A2E68568FA921A346BDA28F40DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report