| File name: | 13072020-047.IMG |
| Full analysis: | https://app.any.run/tasks/872ed51f-c17e-4802-9ce0-c00375677029 |
| Verdict: | Malicious activity |
| Analysis date: | July 13, 2020, 06:35:01 |
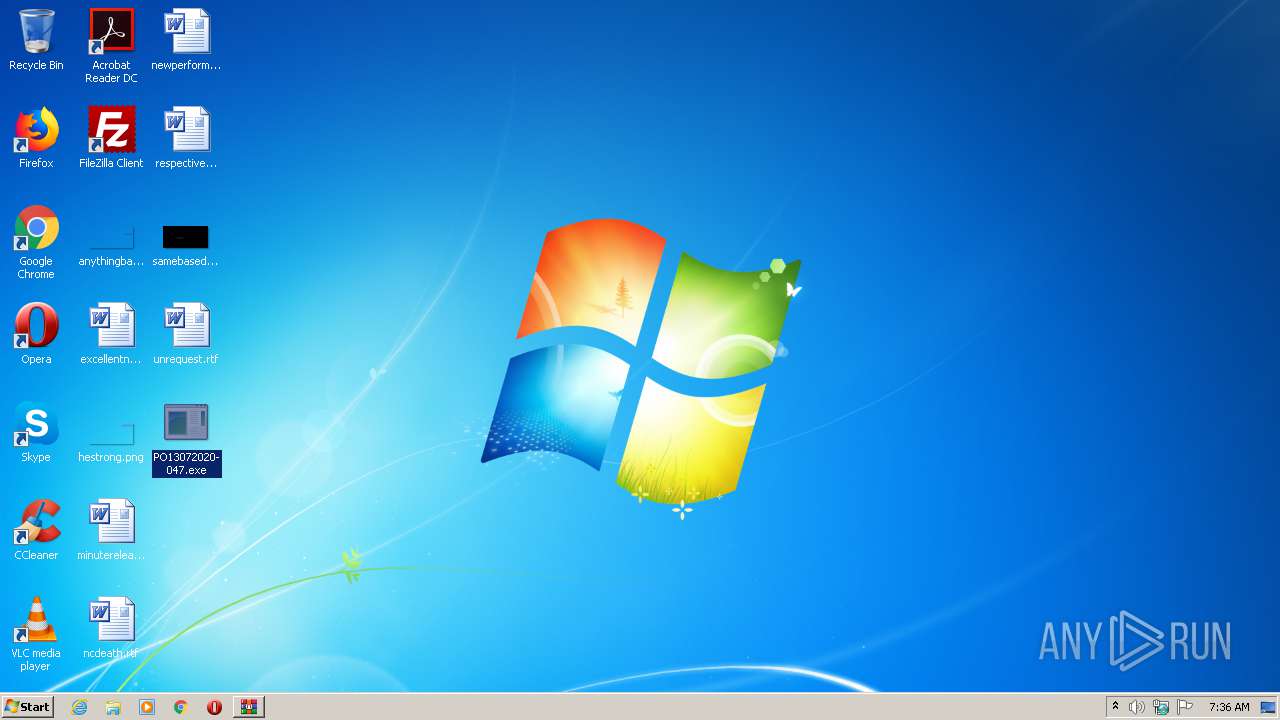
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | UDF filesystem data (version 1.5) '' |
| MD5: | 8EBD61DE8BE3F9EABB951BAC7D13098D |
| SHA1: | A689D9605B3330FA5F4B87FDC9F6909BA55BA307 |
| SHA256: | 9072D32CF9019EC2BF82E0D9506501504305700B7314DC6A1B0DECD50937793D |
| SSDEEP: | 6144:unqVYIWDfr5ILvI+7RO0j4Sgl2HMiy6WCCzRz+GFVLjfezM3rcaOL9fdv4:qGWDtILzdE2HMiy6WhF+GFVnmo3rPO9 |
MALICIOUS
Application was dropped or rewritten from another process
- PO13072020-047.exe (PID: 3404)
- PO13072020-047.exe (PID: 1880)
Actions looks like stealing of personal data
- PO13072020-047.exe (PID: 3404)
SUSPICIOUS
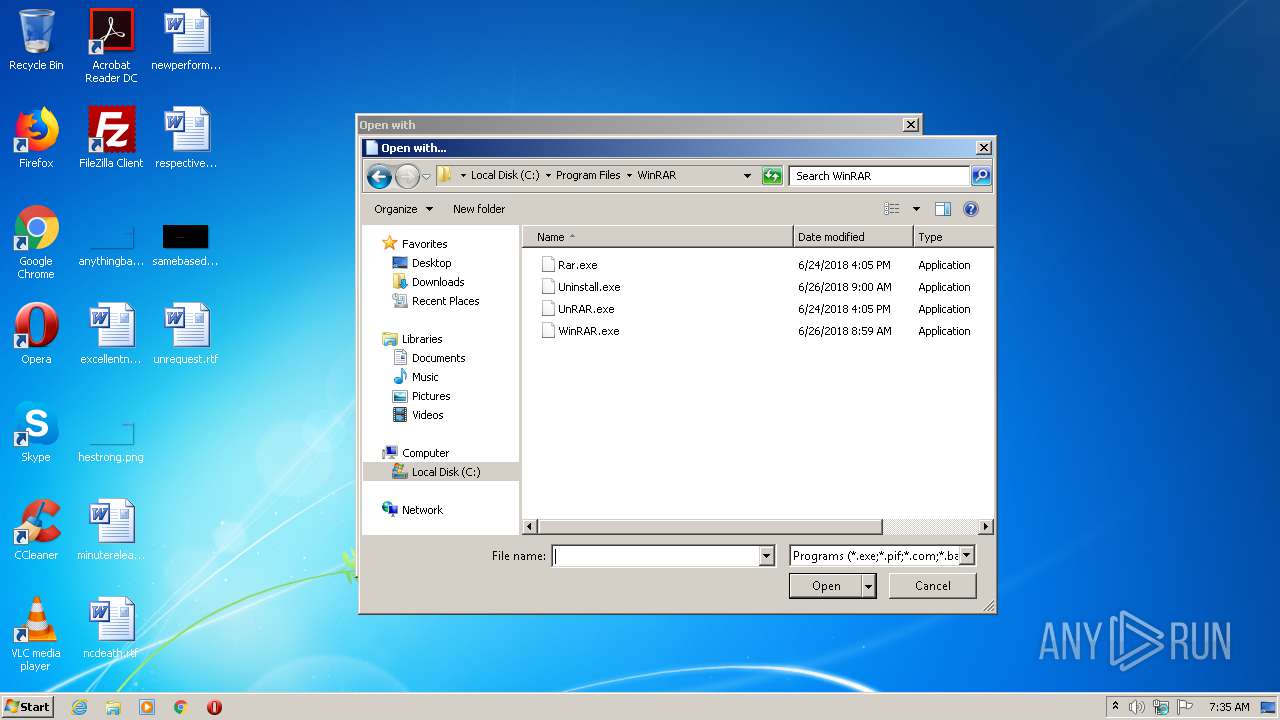
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1328)
- PO13072020-047.exe (PID: 3404)
Reads Environment values
- PO13072020-047.exe (PID: 3404)
INFO
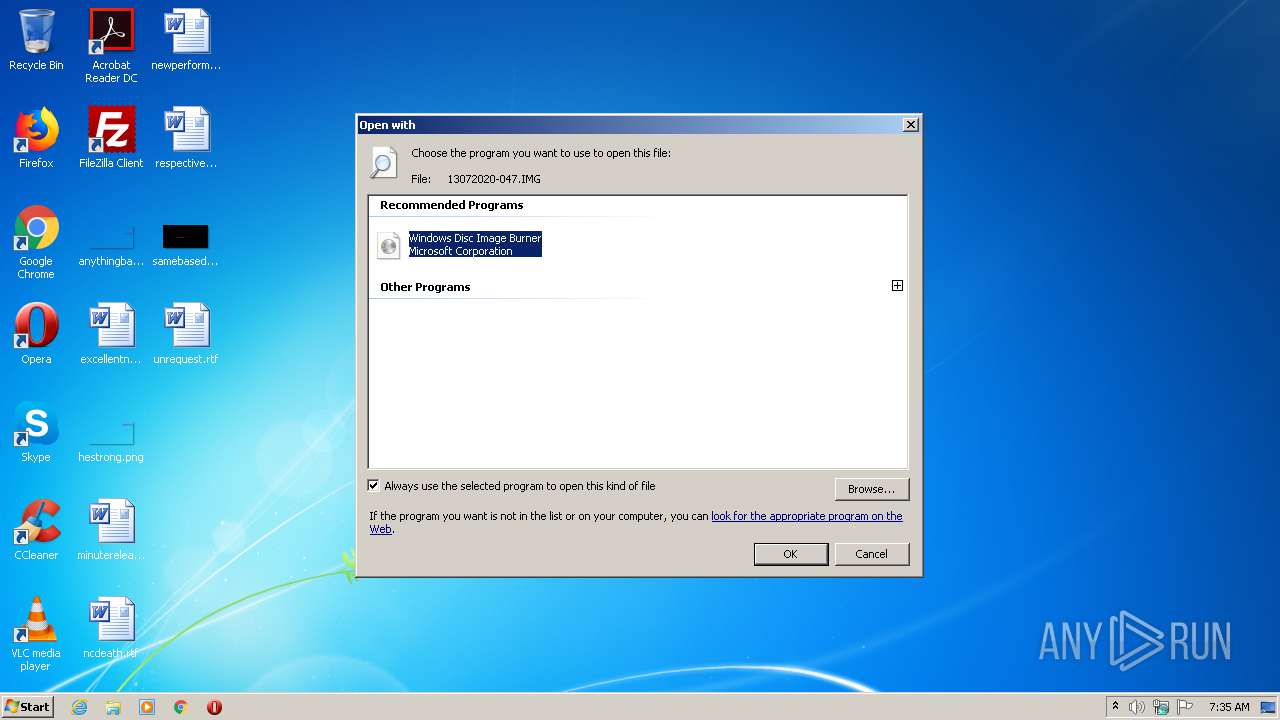
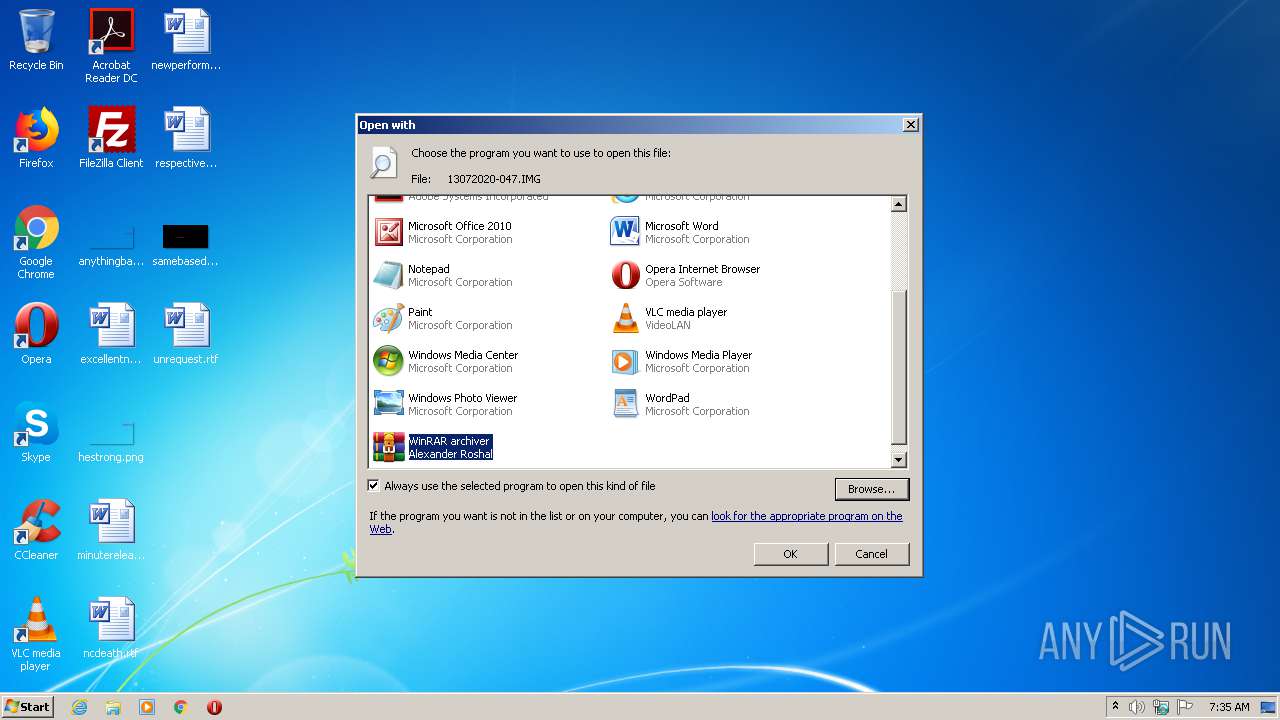
Modifies the open verb of a shell class
- rundll32.exe (PID: 3208)
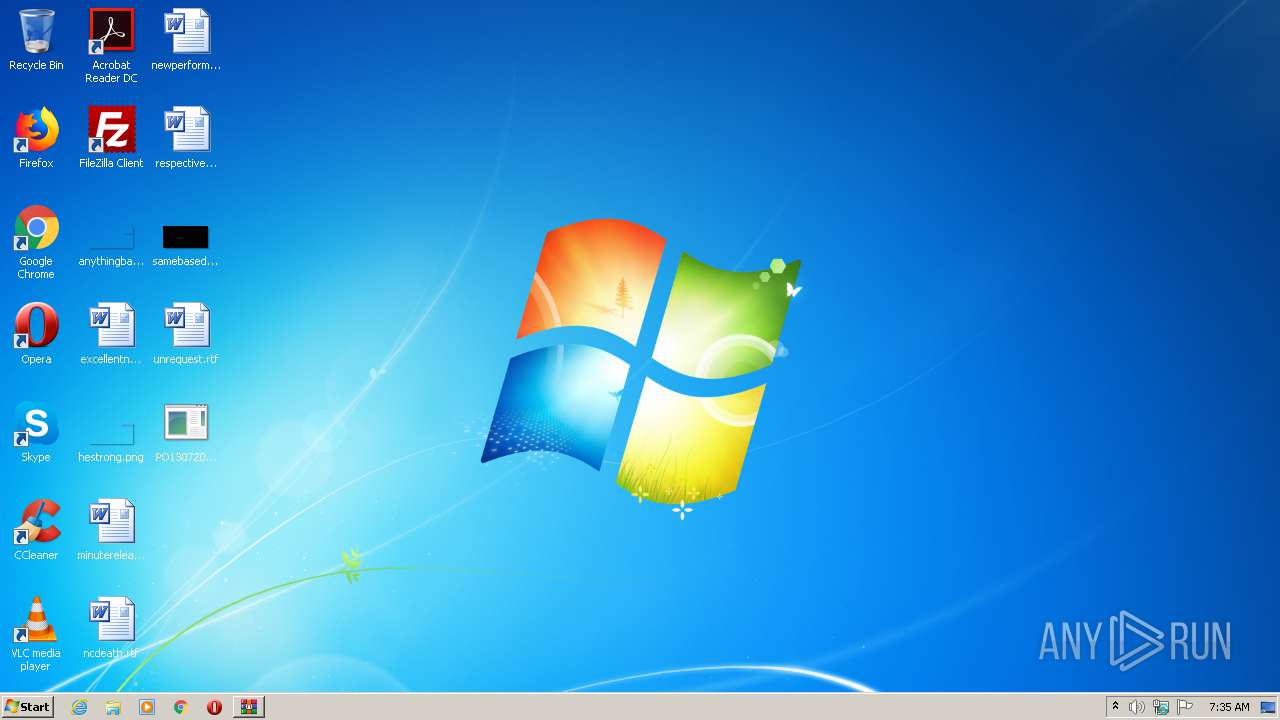
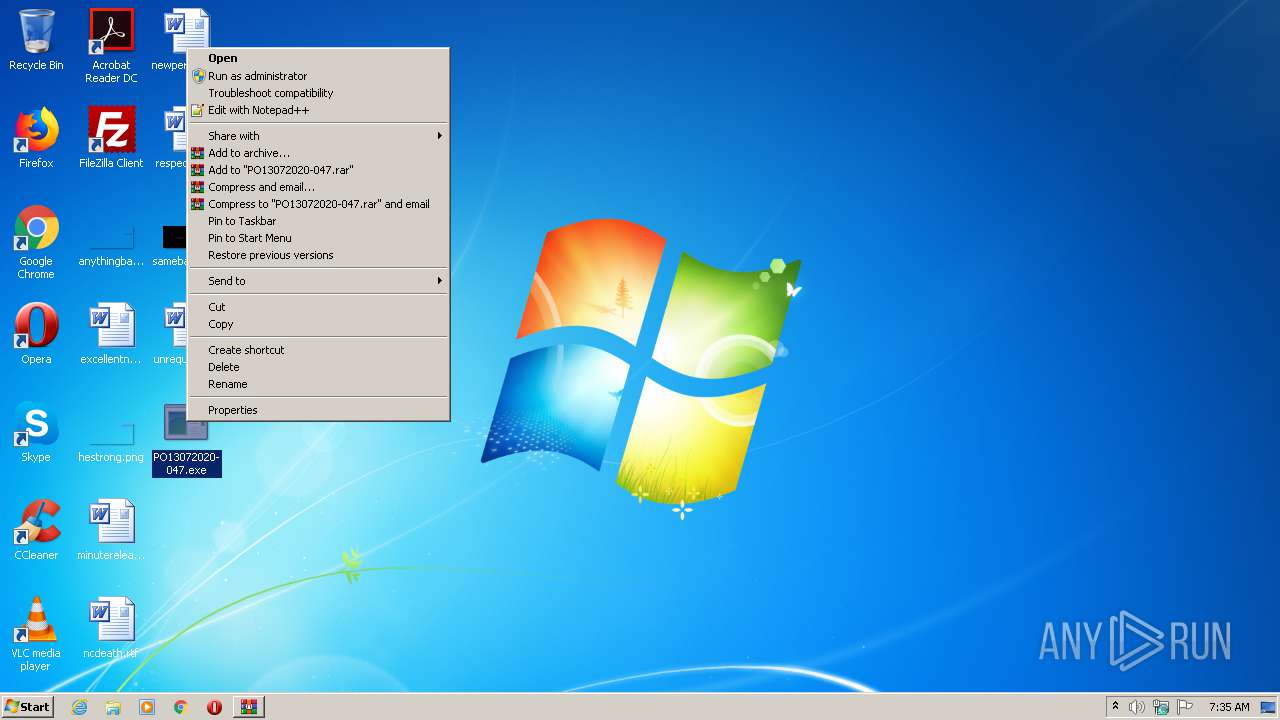
Manual execution by user
- PO13072020-047.exe (PID: 1880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| VolumeBlockCount: | 599 |
|---|---|
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 2020:07:13 01:13:49-07:00 |
| VolumeSetName: | UNDEFINED |
| Software: | IMGBURN V2.5.8.0 - THE ULTIMATE IMAGE BURNER! |
| VolumeCreateDate: | 2020:07:13 01:13:49.00-07:00 |
| VolumeModifyDate: | 2020:07:13 01:13:49.00-07:00 |
Composite
| VolumeSize: | 1198 kB |
|---|
Total processes
42
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
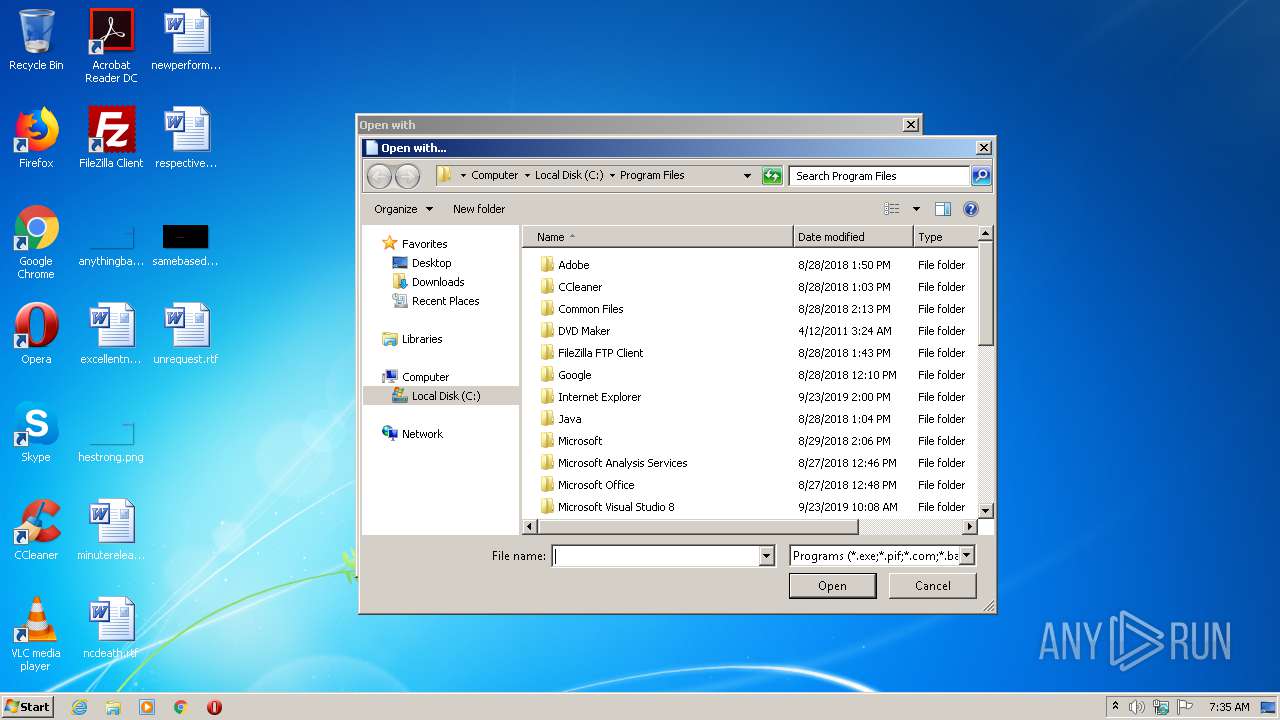
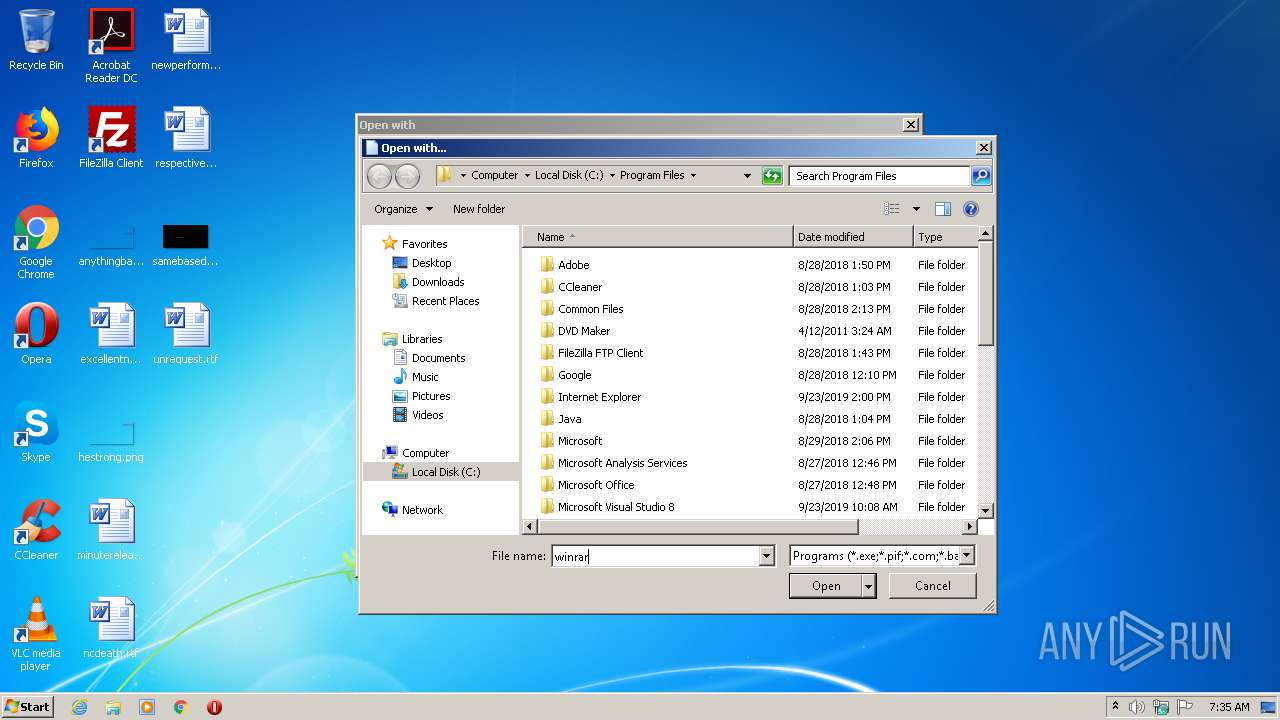
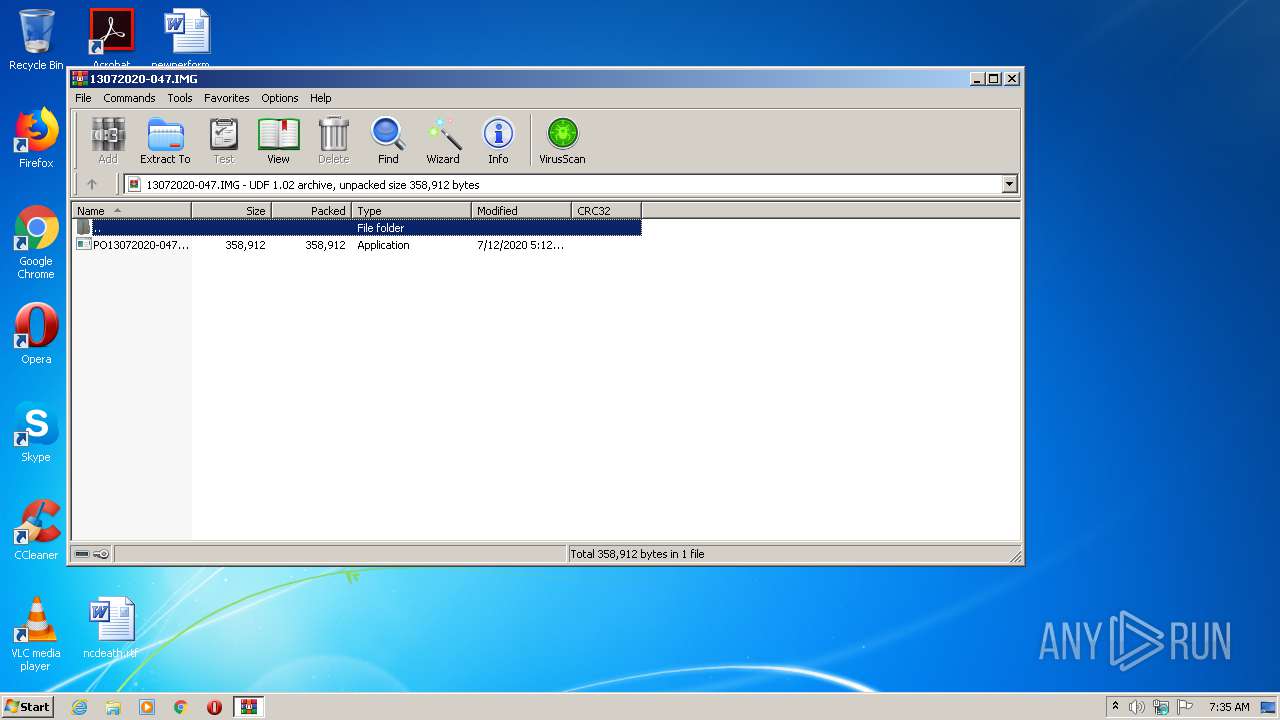
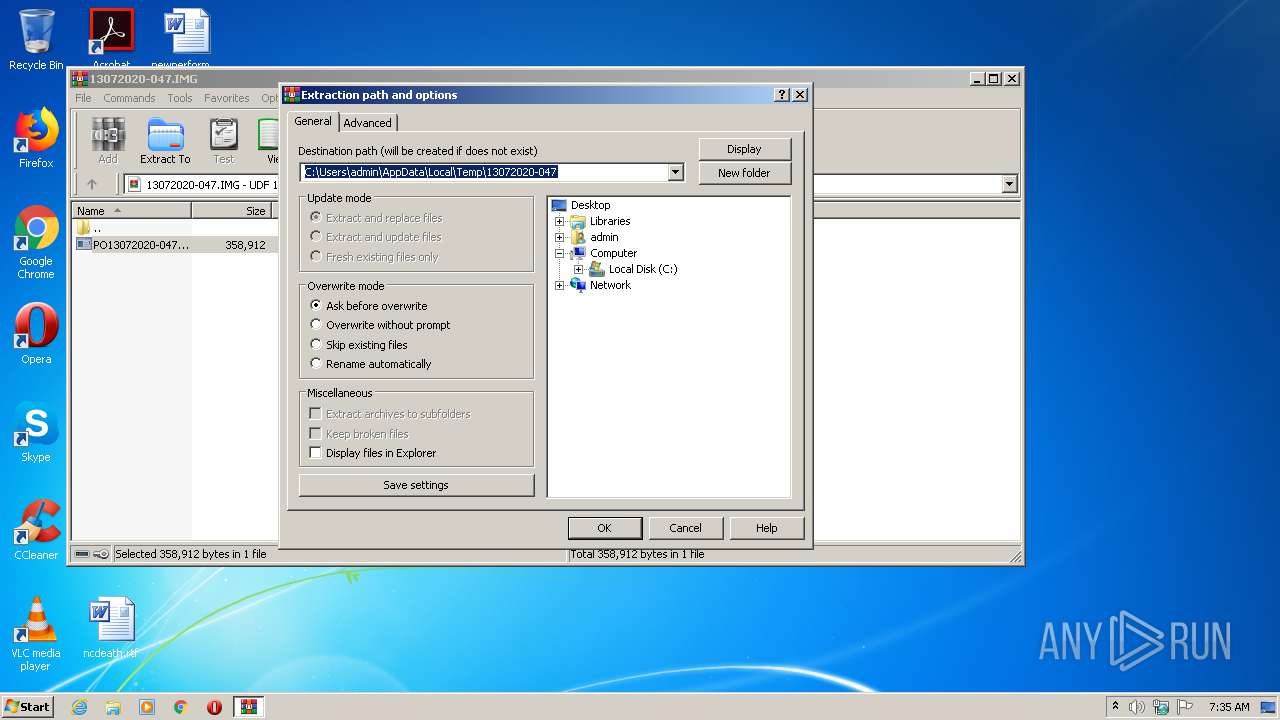
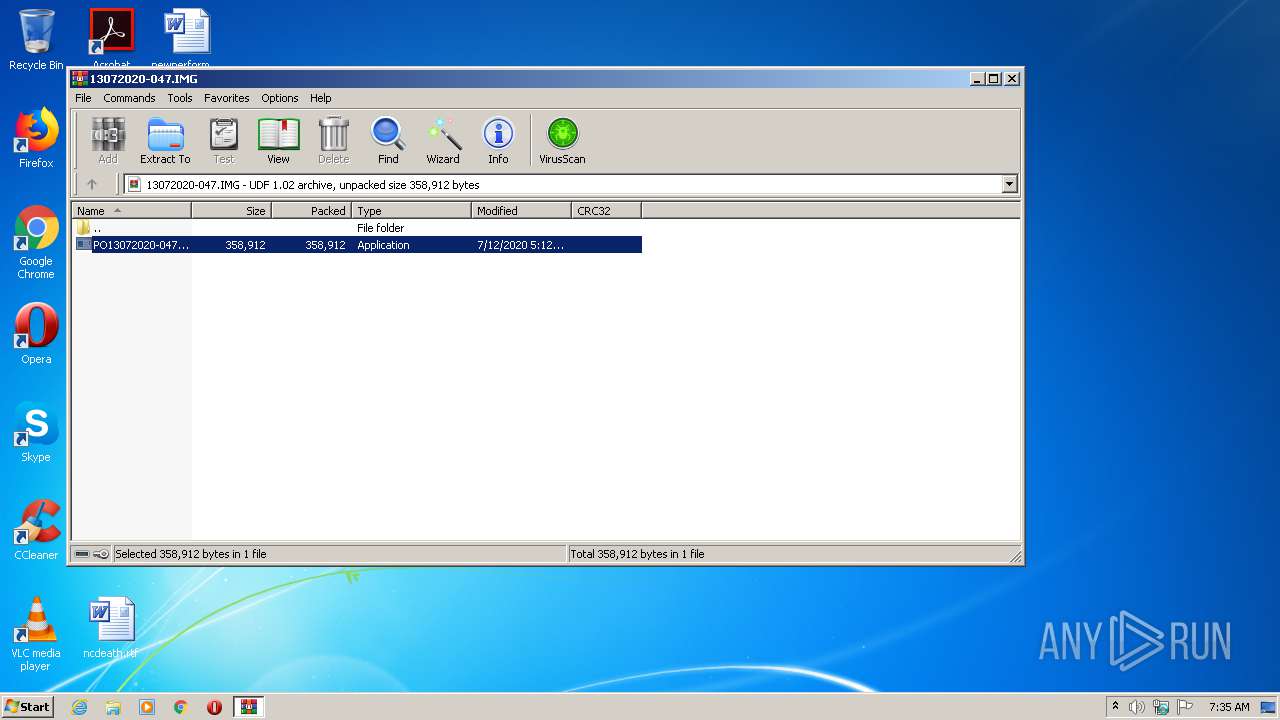
| 1328 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\13072020-047.IMG" | C:\Program Files\WinRAR\WinRAR.exe | rundll32.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1880 | "C:\Users\admin\Desktop\PO13072020-047.exe" | C:\Users\admin\Desktop\PO13072020-047.exe | explorer.exe | ||||||||||||
User: admin Company: Harman International Integrity Level: HIGH Description: AutoSave Paint Exit code: 4294967295 Version: 26.0.0.0 Modules
| |||||||||||||||
| 3208 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\13072020-047.IMG | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3404 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1328.47889\PO13072020-047.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa1328.47889\PO13072020-047.exe | WinRAR.exe | ||||||||||||
User: admin Company: Harman International Integrity Level: MEDIUM Description: AutoSave Paint Exit code: 0 Version: 26.0.0.0 Modules
| |||||||||||||||
Total events
1 355
Read events
1 171
Write events
183
Delete events
1
Modification events
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\isoburn.exe,-350 |
Value: Disc Image File | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.IMG\OpenWithProgids |
| Operation: | write | Name: | Windows.IsoFile |
Value: | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\isoburn.exe,-352 |
Value: Windows Disc Image Burner | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\System32\isoburn.exe |
Value: Windows Disc Image Burner | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (3208) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1328 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa1328.47889\PO13072020-047.exe | executable | |
MD5:— | SHA256:— | |||
| 3404 | PO13072020-047.exe | C:\Users\admin\AppData\Local\Temp\tmpG836.tmp | executable | |
MD5:— | SHA256:— | |||
| 1328 | WinRAR.exe | C:\Users\admin\Desktop\PO13072020-047.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3404 | PO13072020-047.exe | 85.17.123.84:587 | mail.baslog.rs | LeaseWeb Netherlands B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mail.baslog.rs |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3404 | PO13072020-047.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |