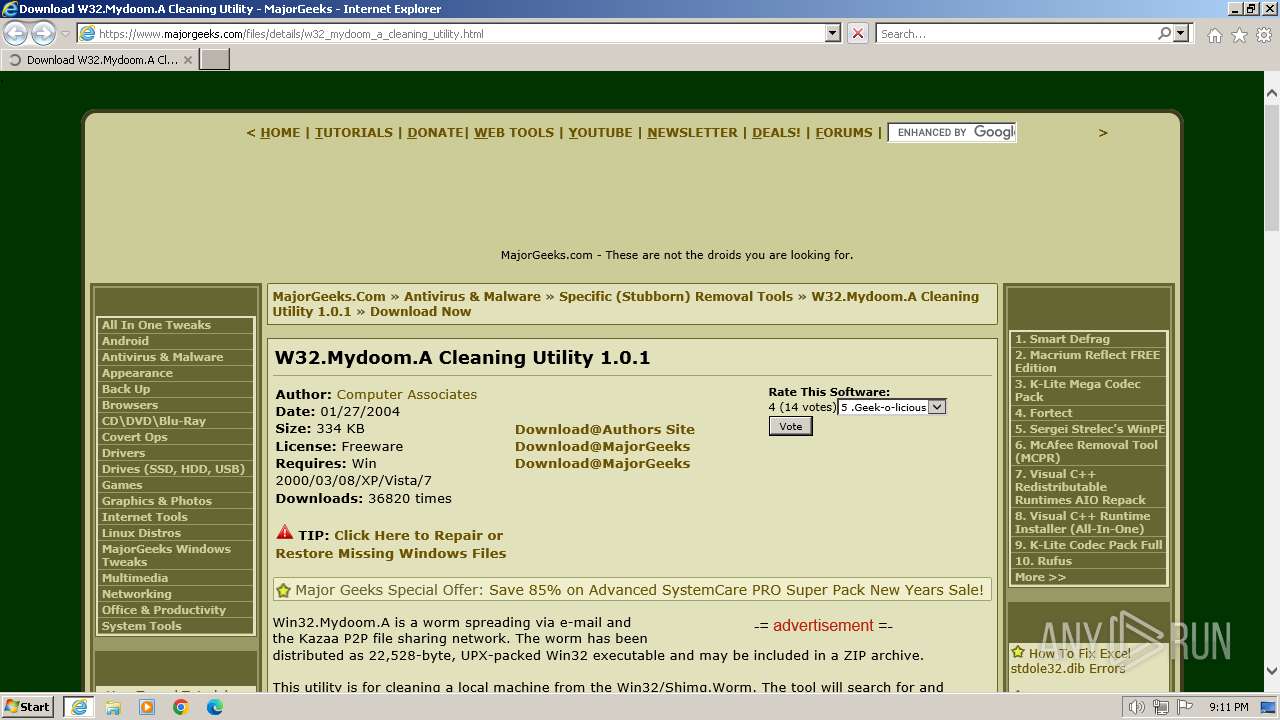
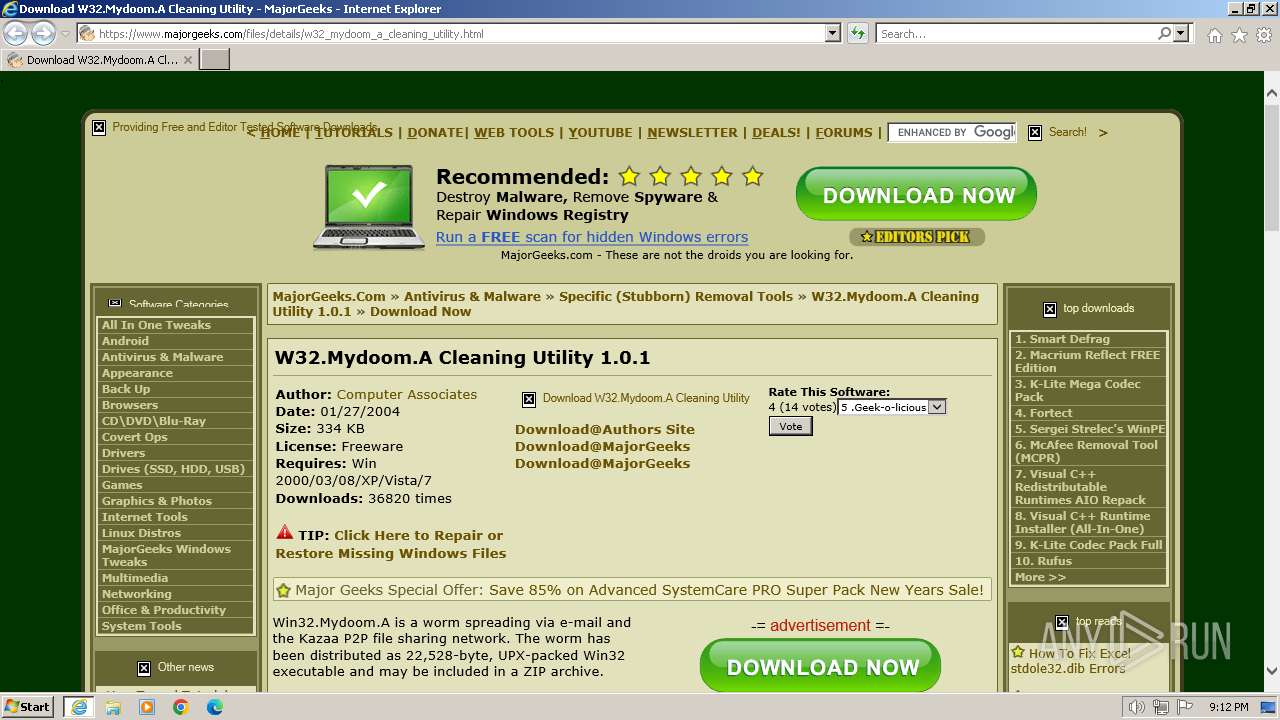
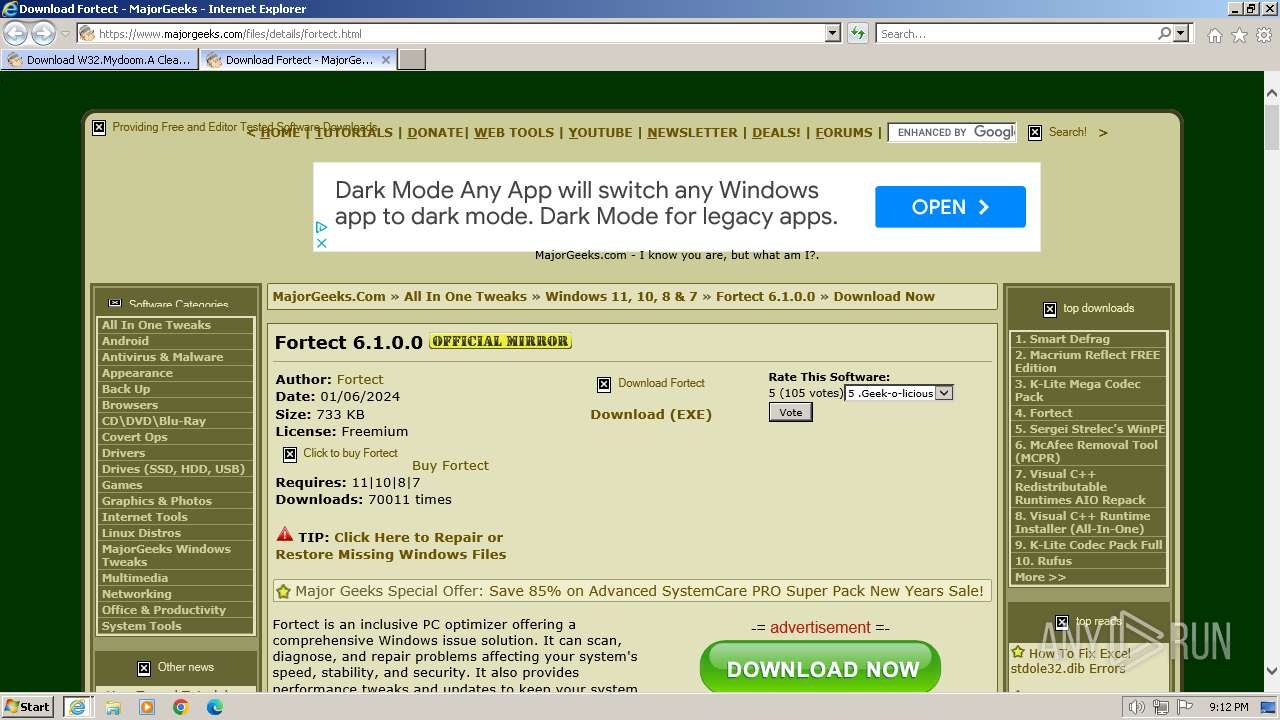
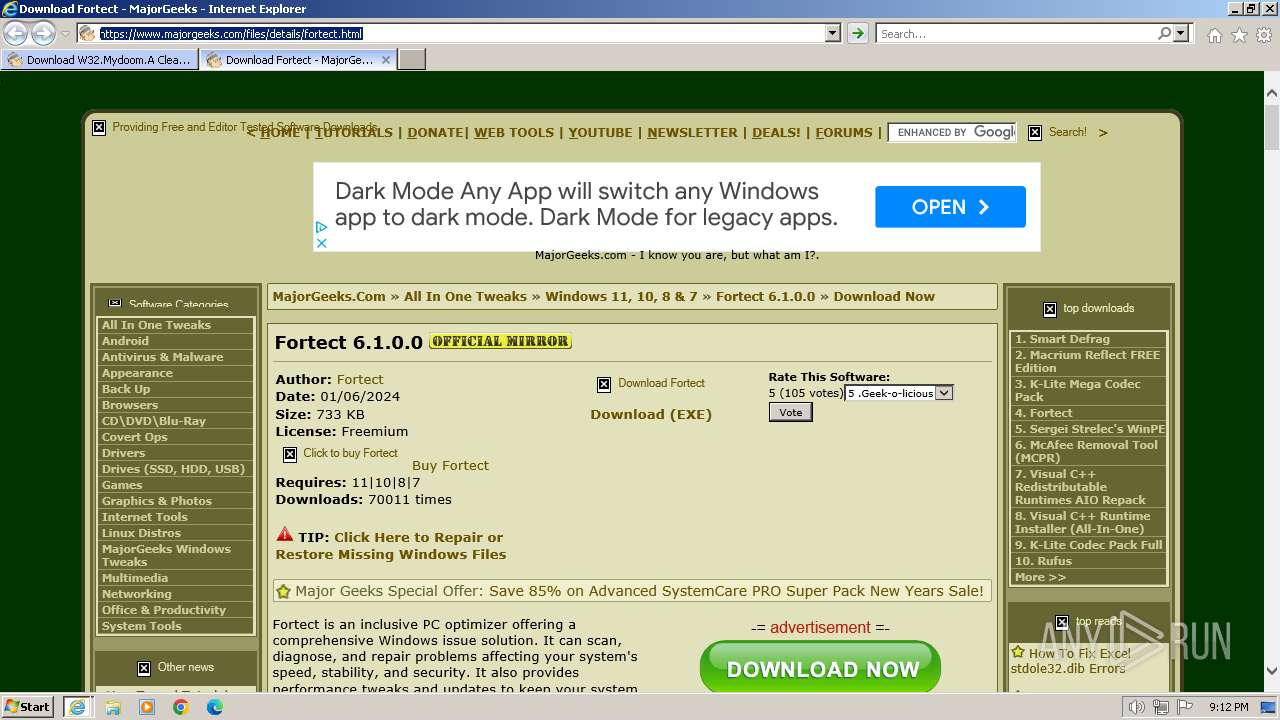
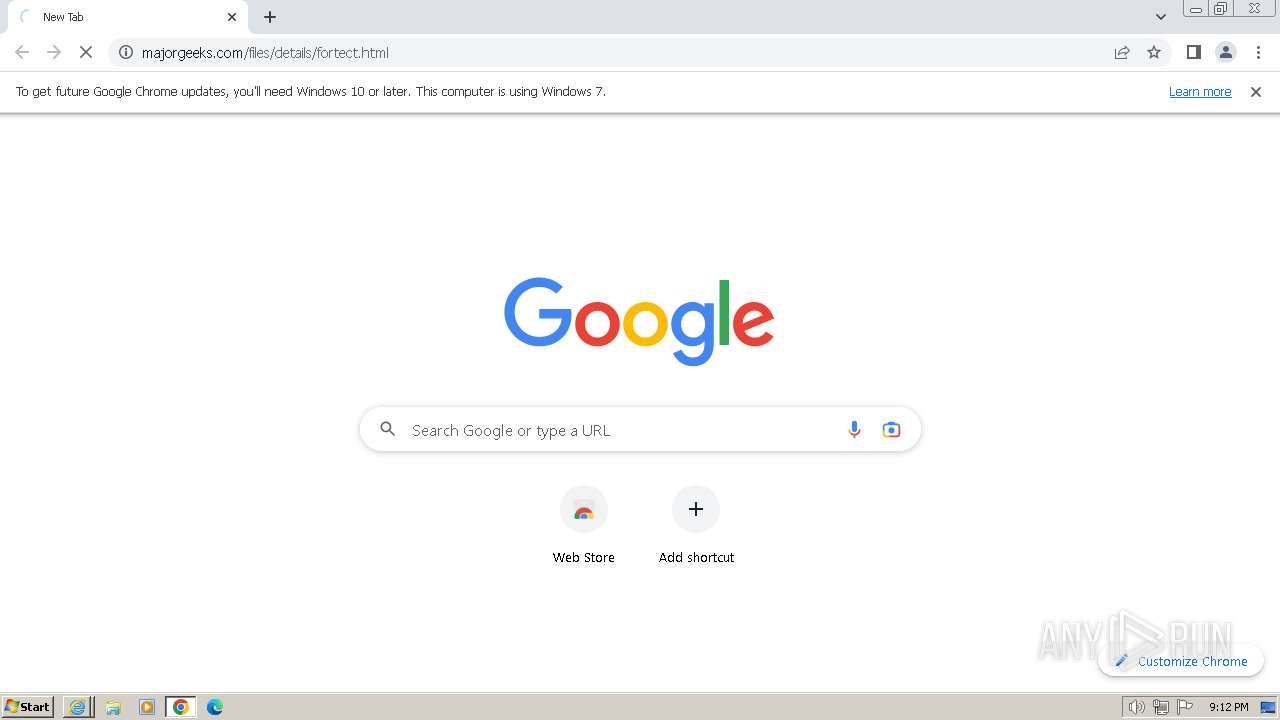
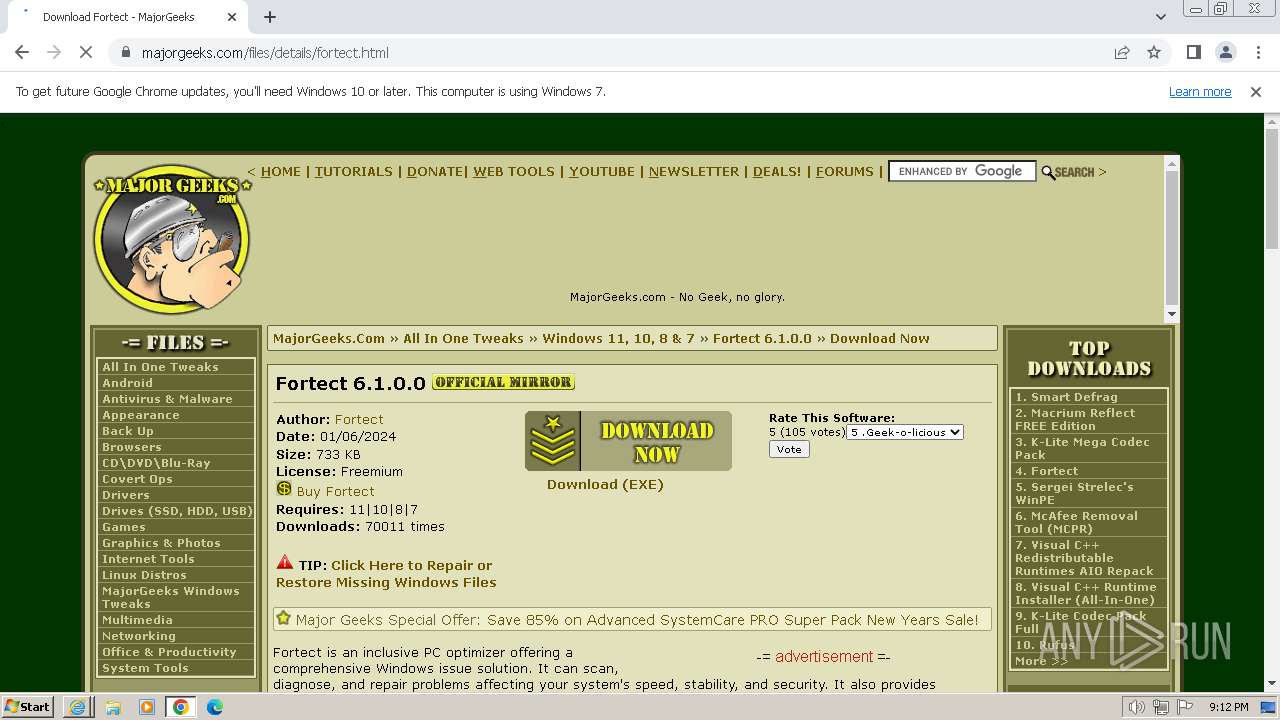
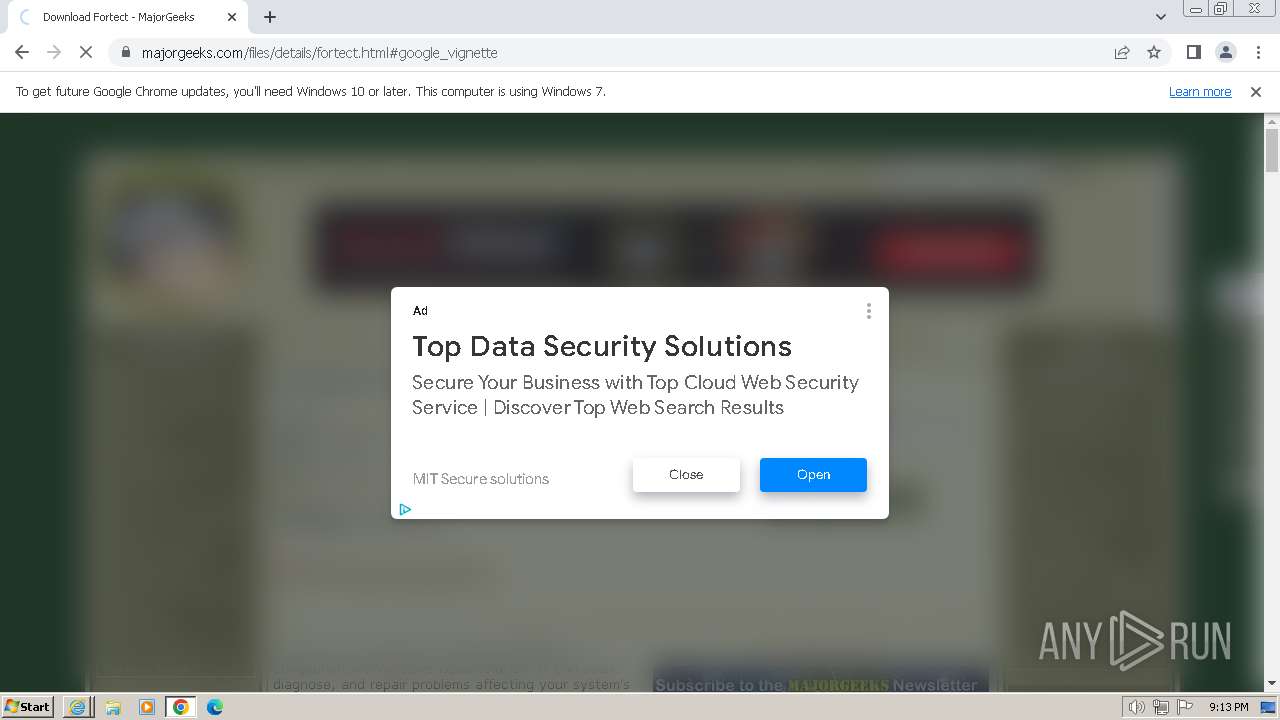
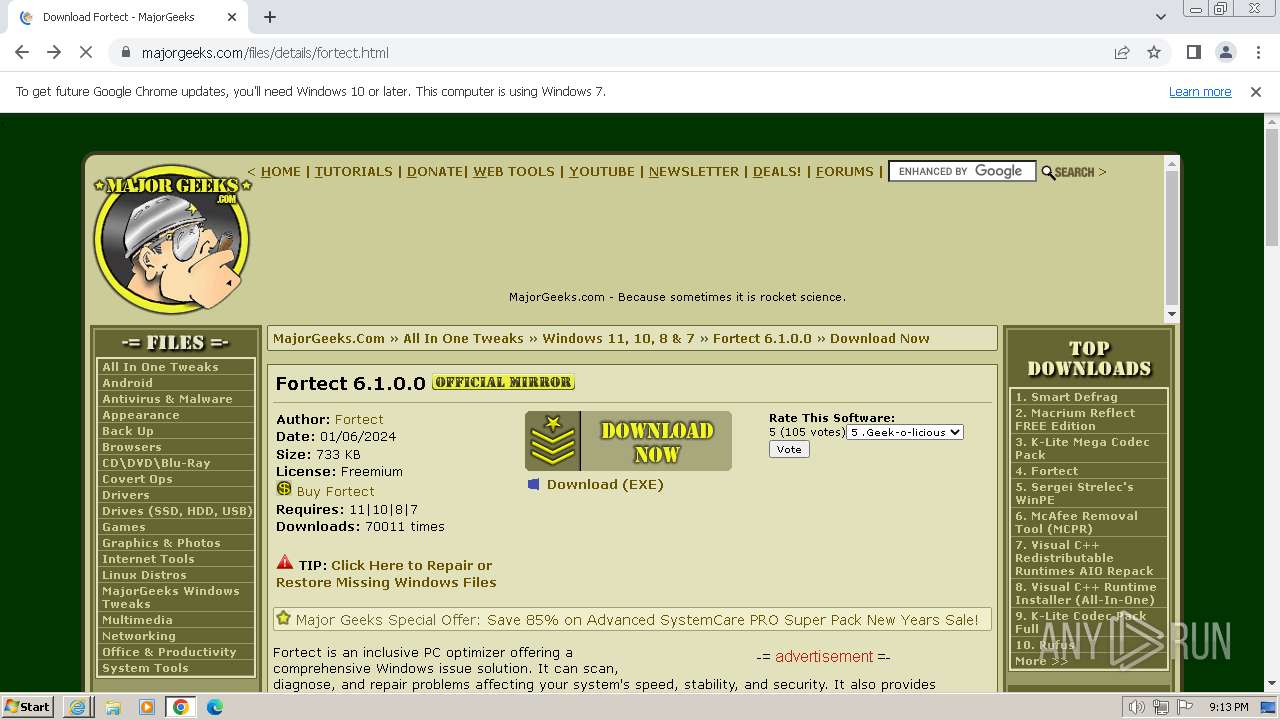
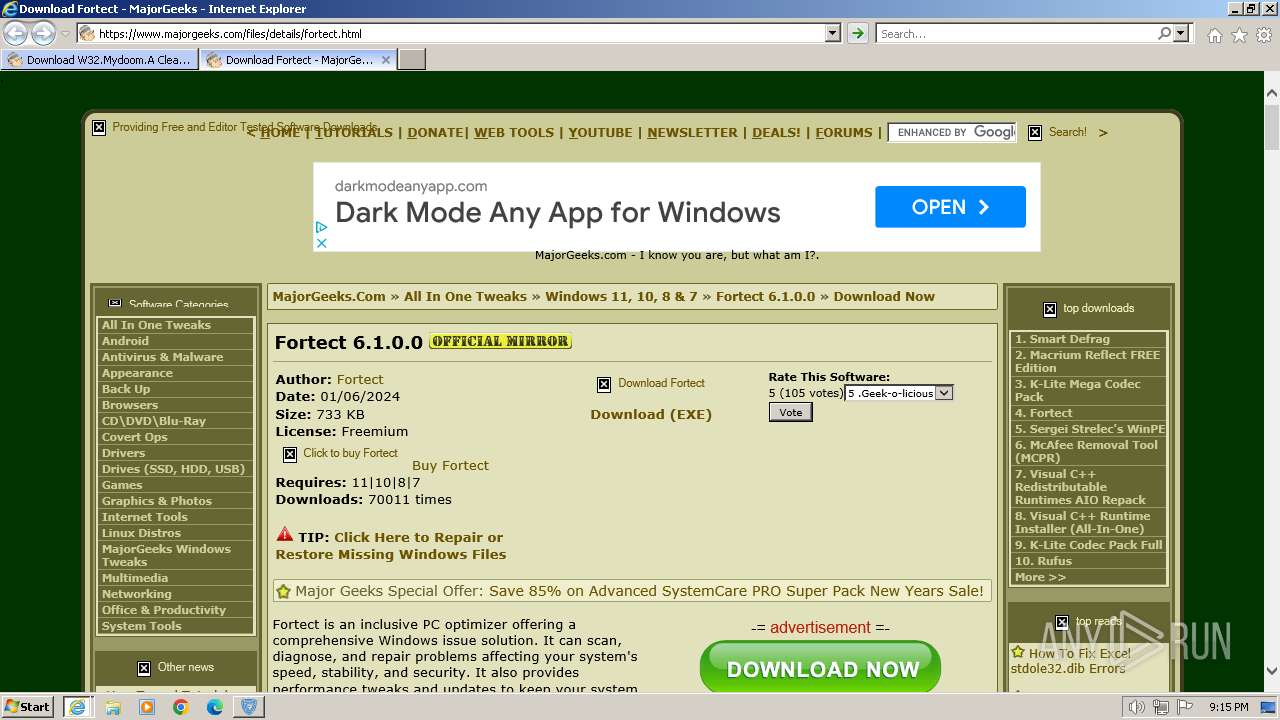
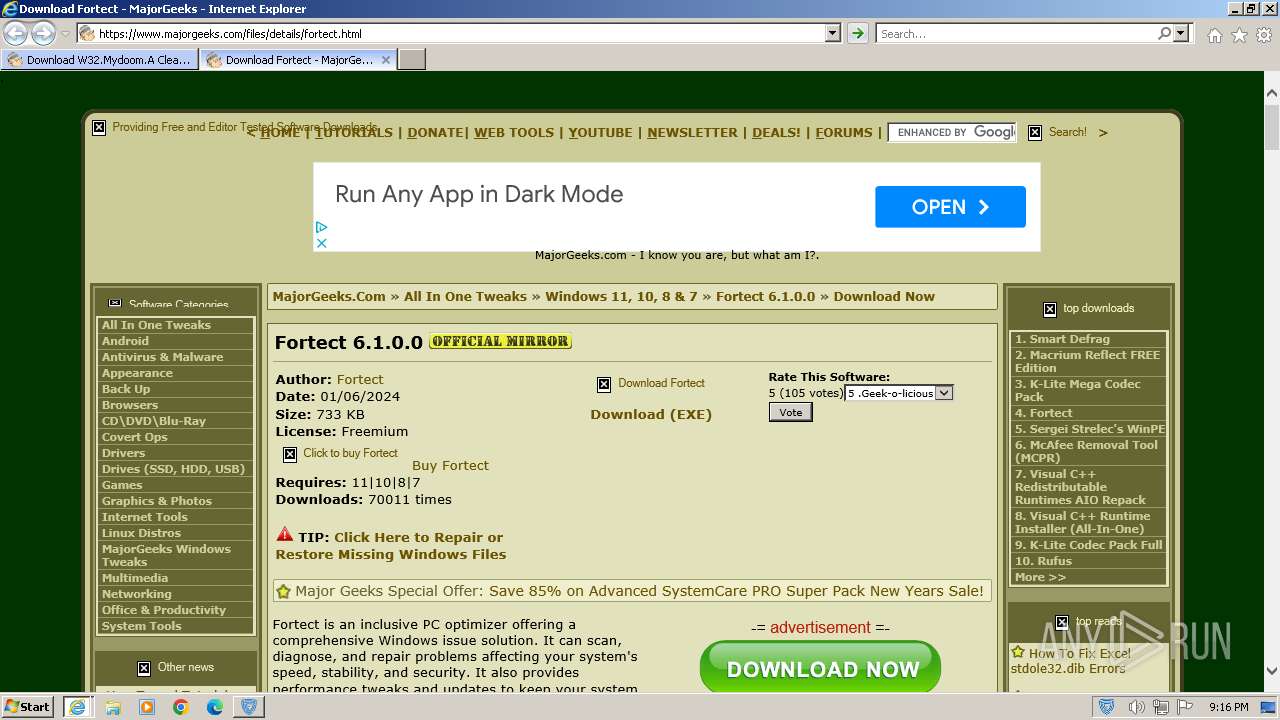
| URL: | https://www.majorgeeks.com/files/details/w32_mydoom_a_cleaning_utility.html |
| Full analysis: | https://app.any.run/tasks/2c0d377a-557a-4563-a419-5cbea8bdf9b4 |
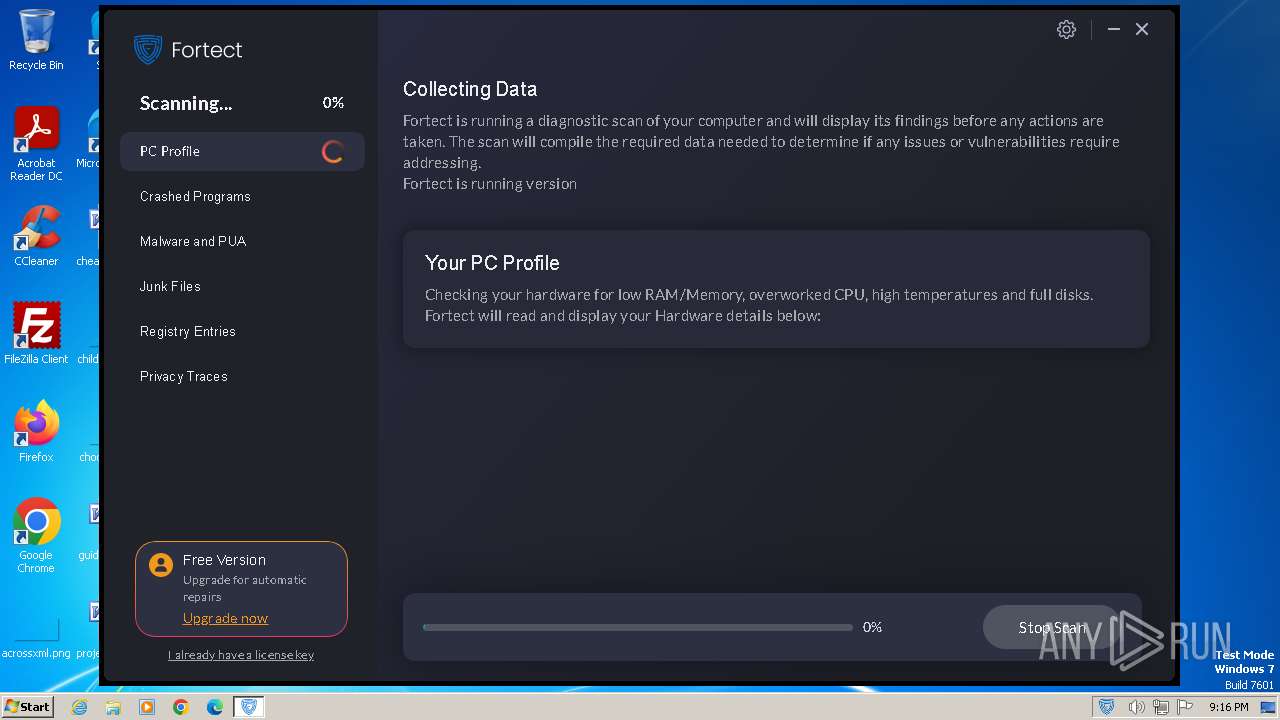
| Verdict: | Malicious activity |
| Analysis date: | January 19, 2024, 21:11:47 |
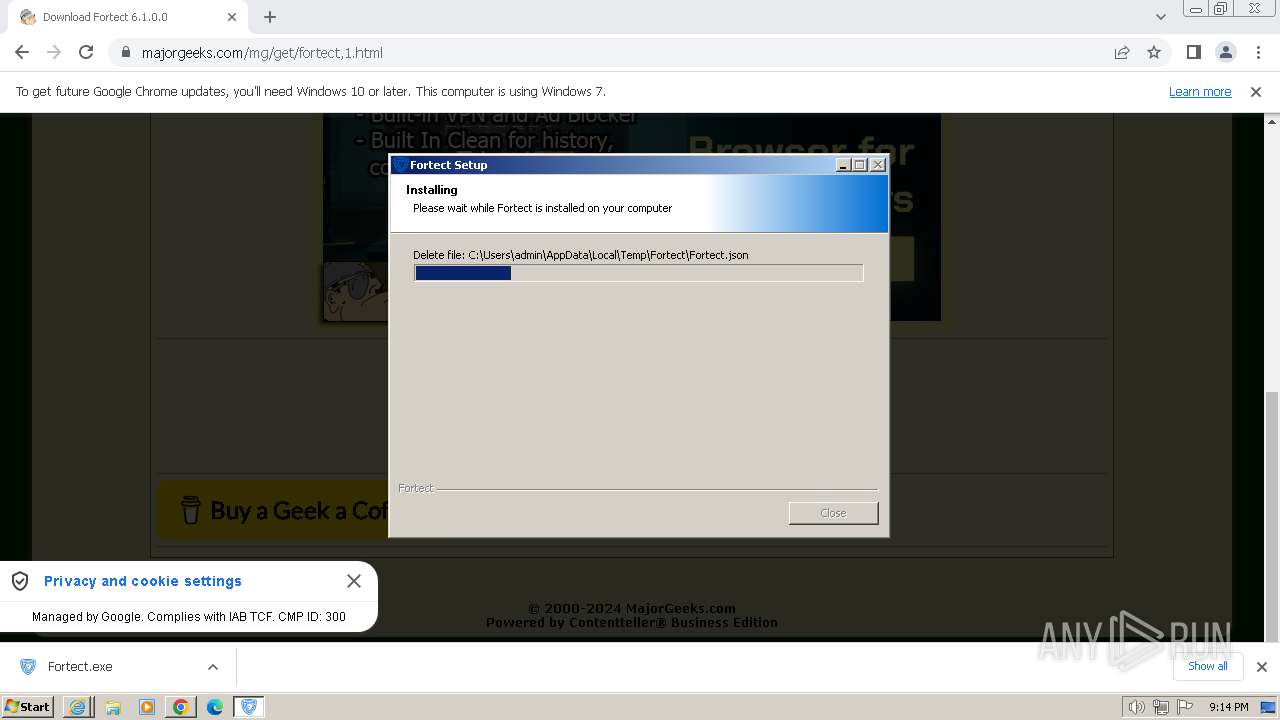
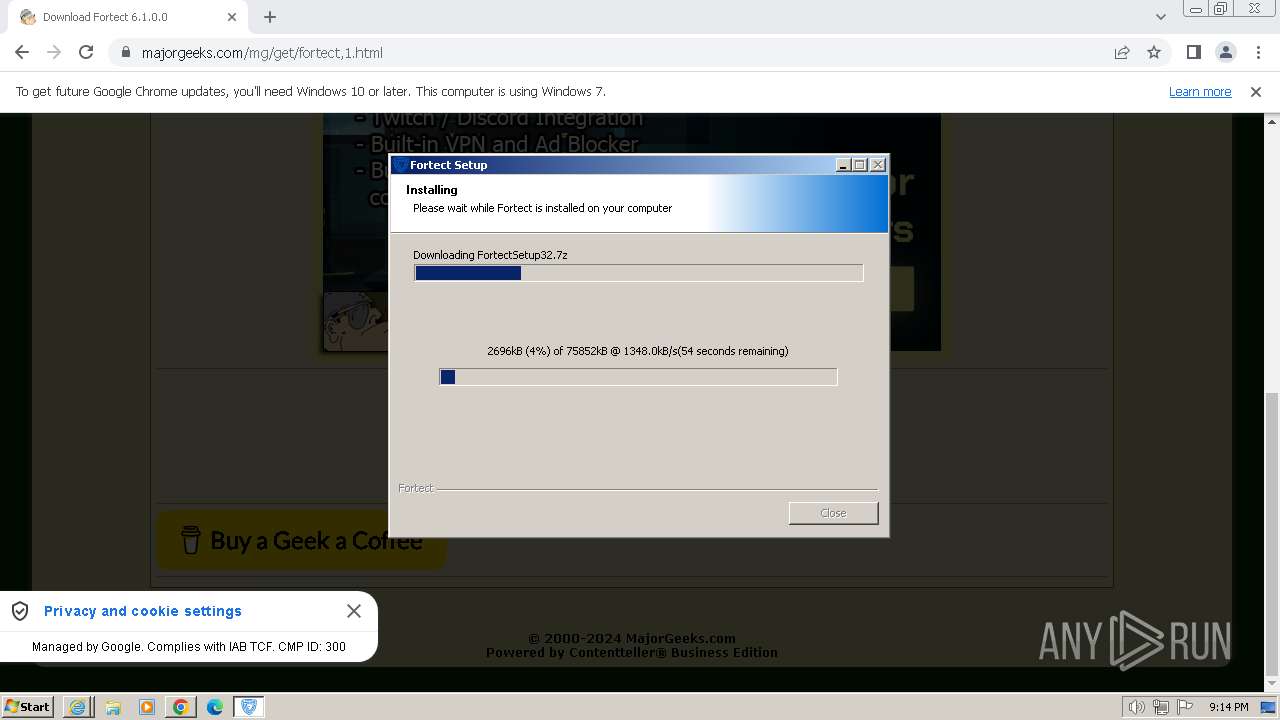
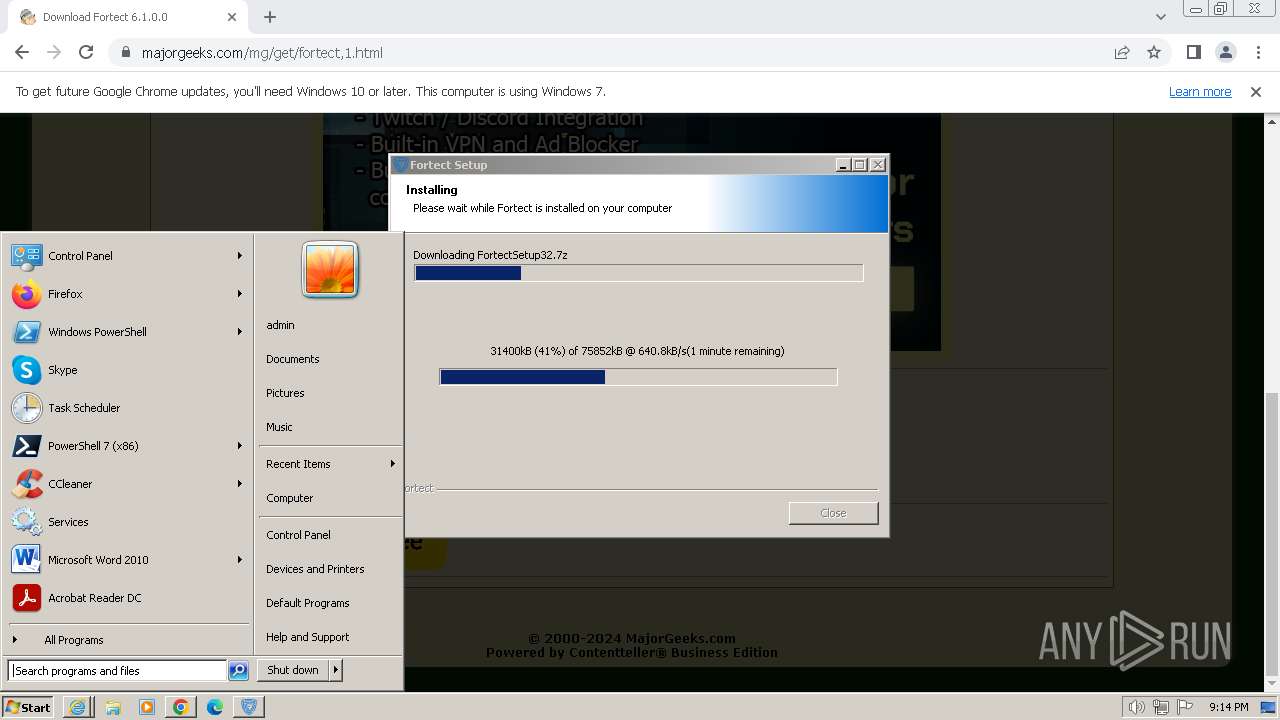
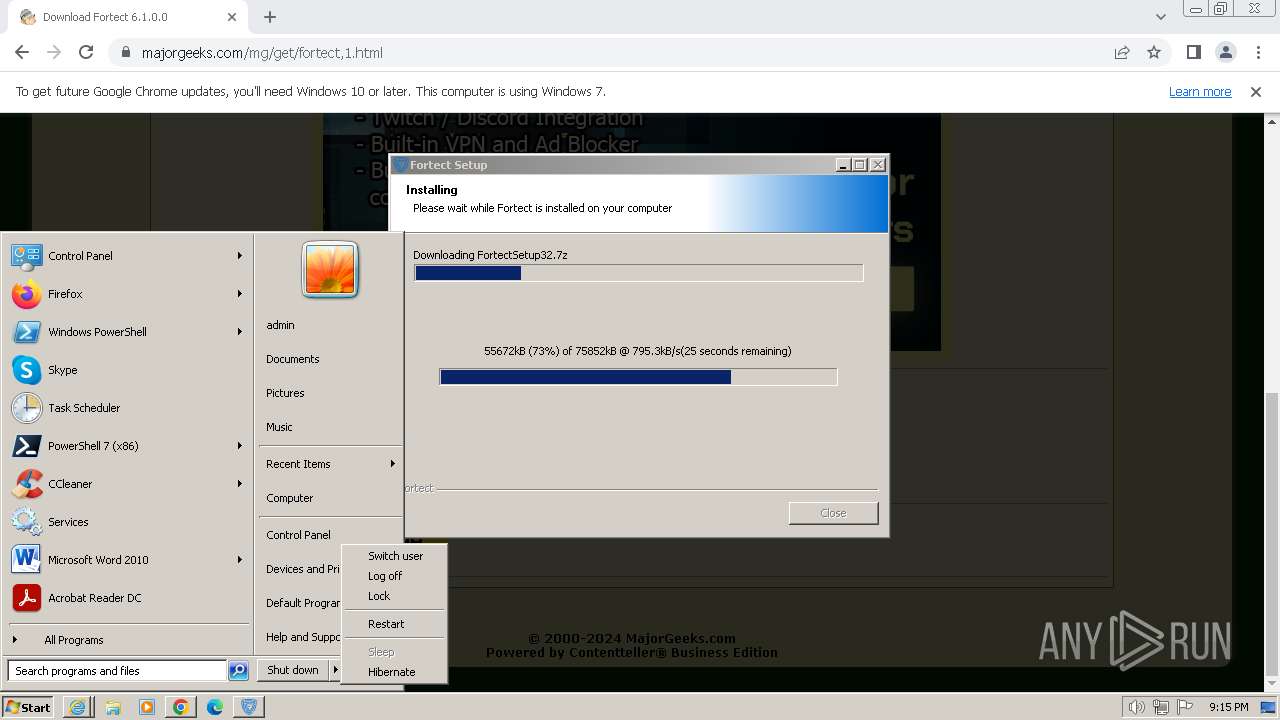
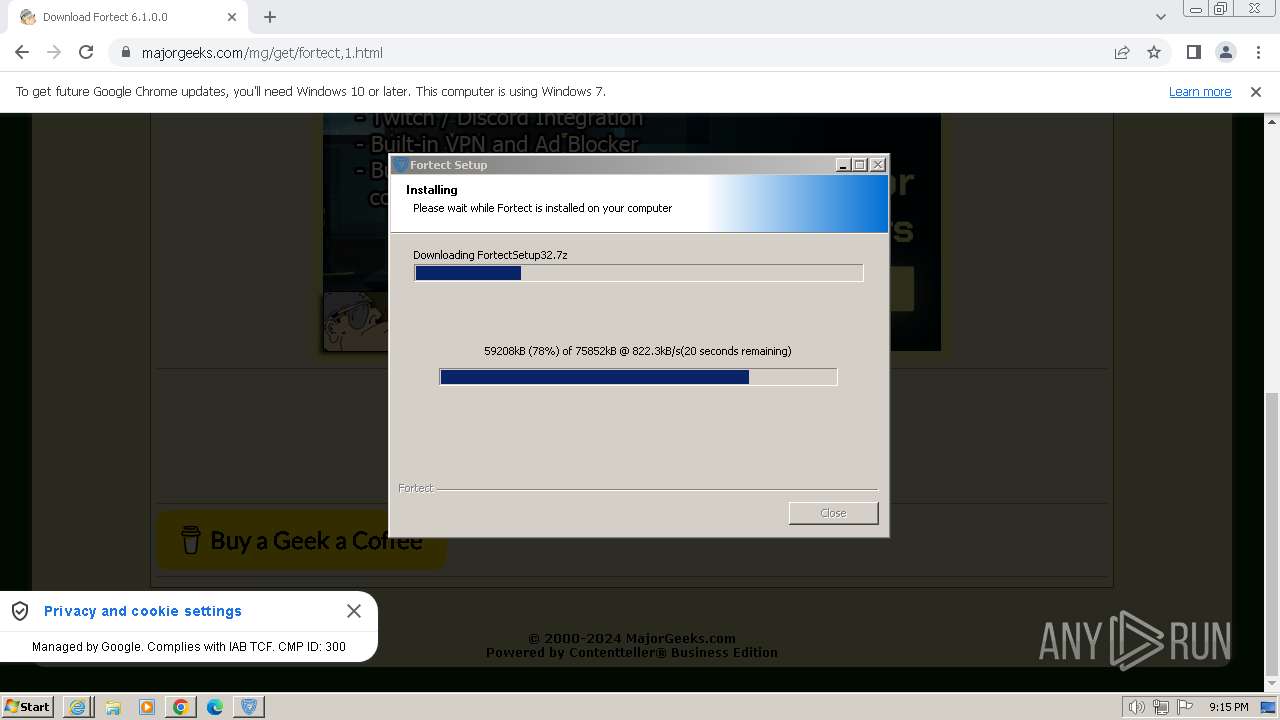
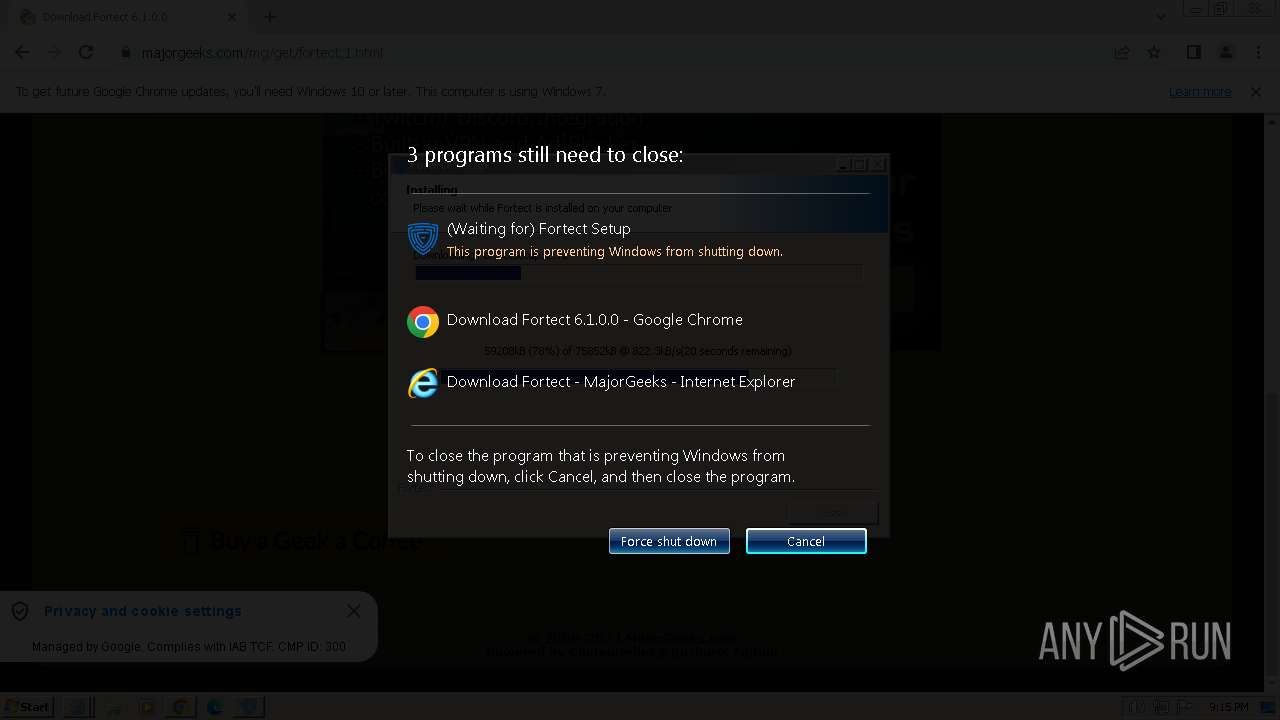
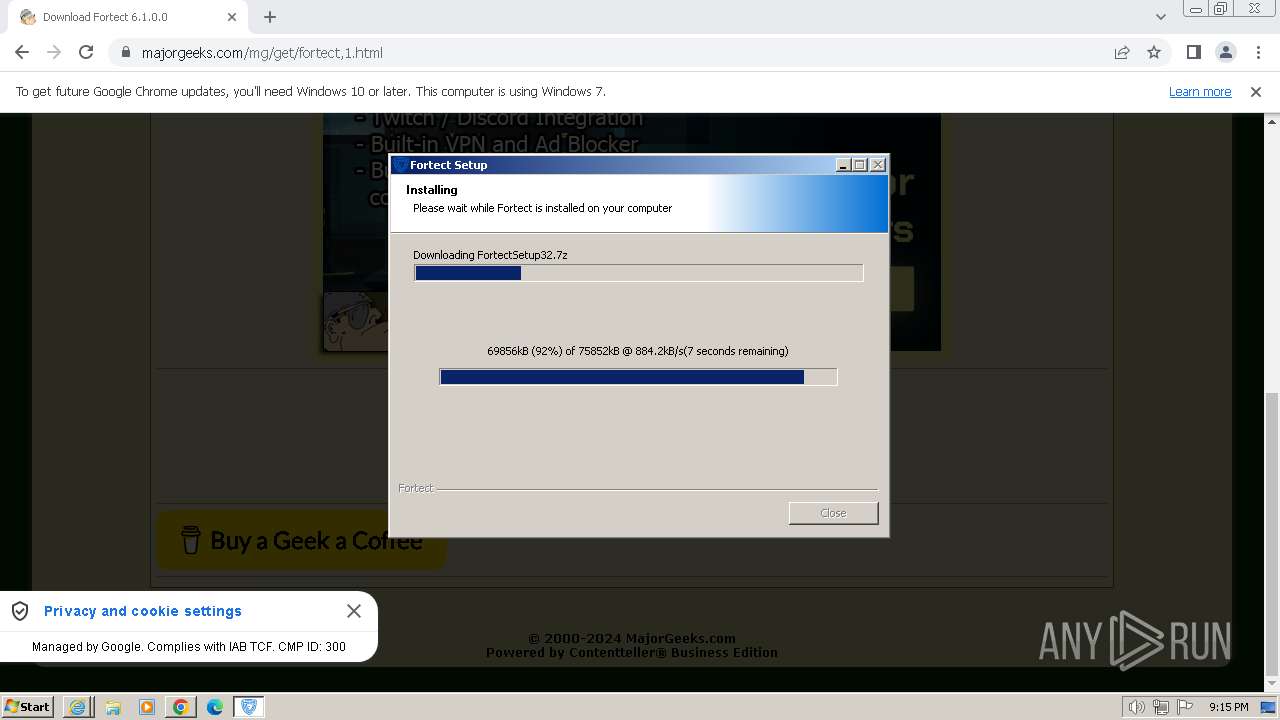
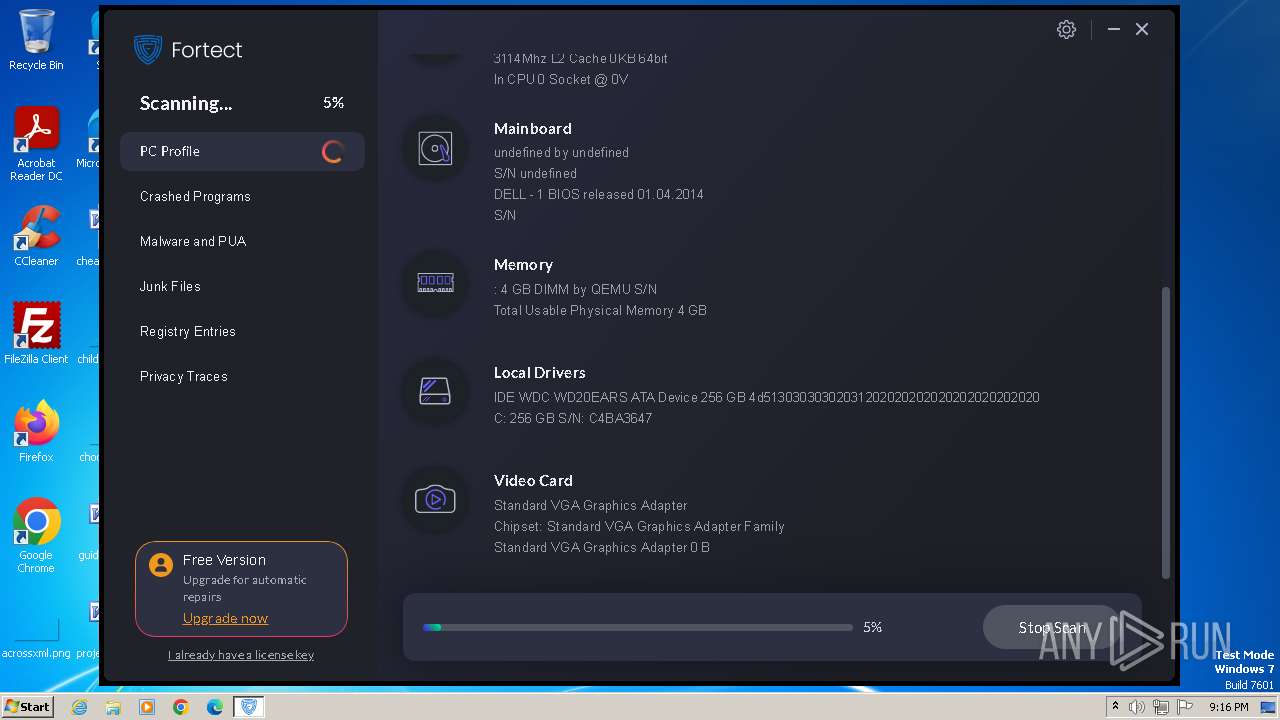
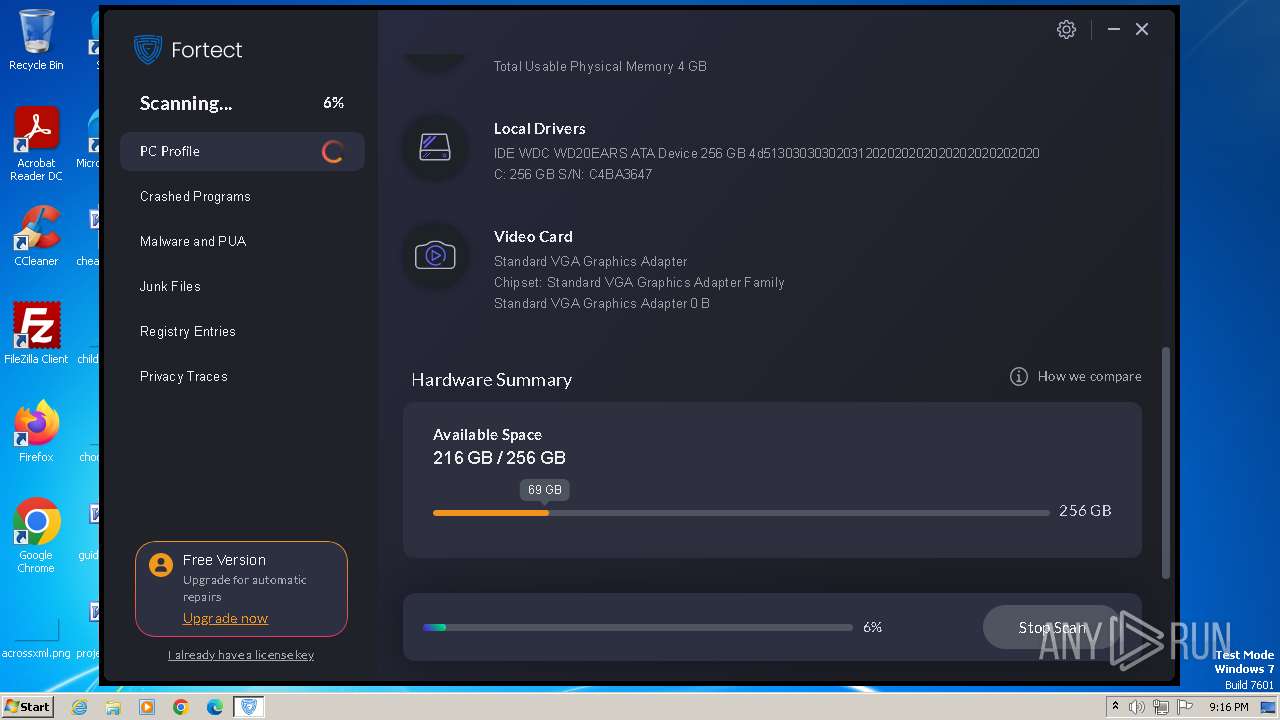
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EC84068933288C408A84F954BCEFBB8E |
| SHA1: | 351CBF1224722783BD6AA6B0B0E5BC47E9339984 |
| SHA256: | 906EE5ACFD27CCEE0B51DC169B842A46DACDD21D3A93094C5282E501F6F9DB1B |
| SSDEEP: | 3:N8DSLsXDAOmD0K2lJNSvFGOvLC6lSc5G:2OLstTNSvtvqc8 |
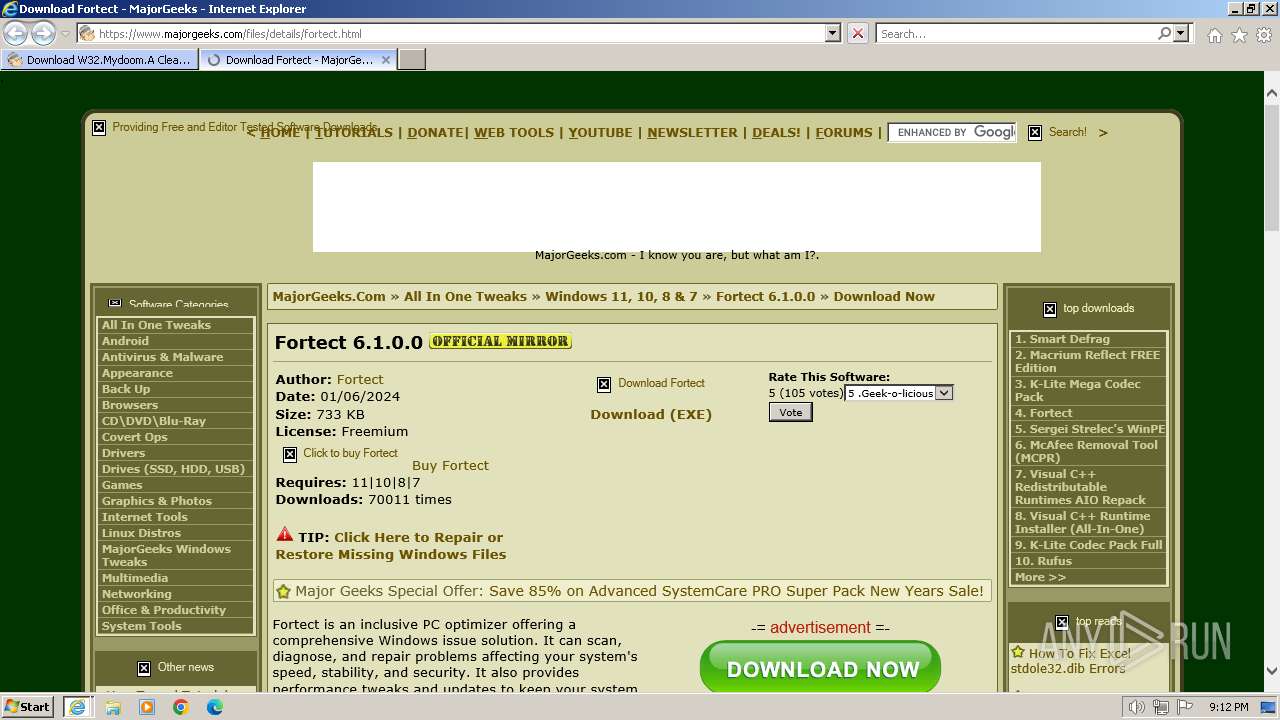
MALICIOUS
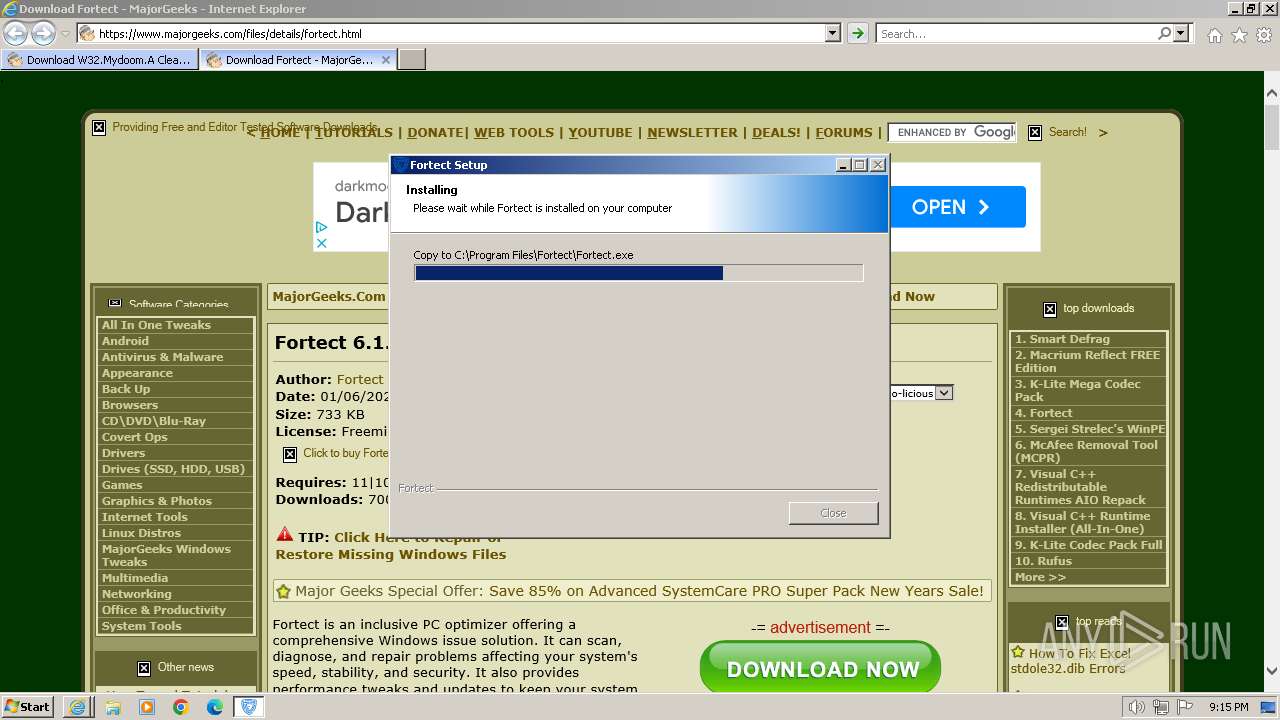
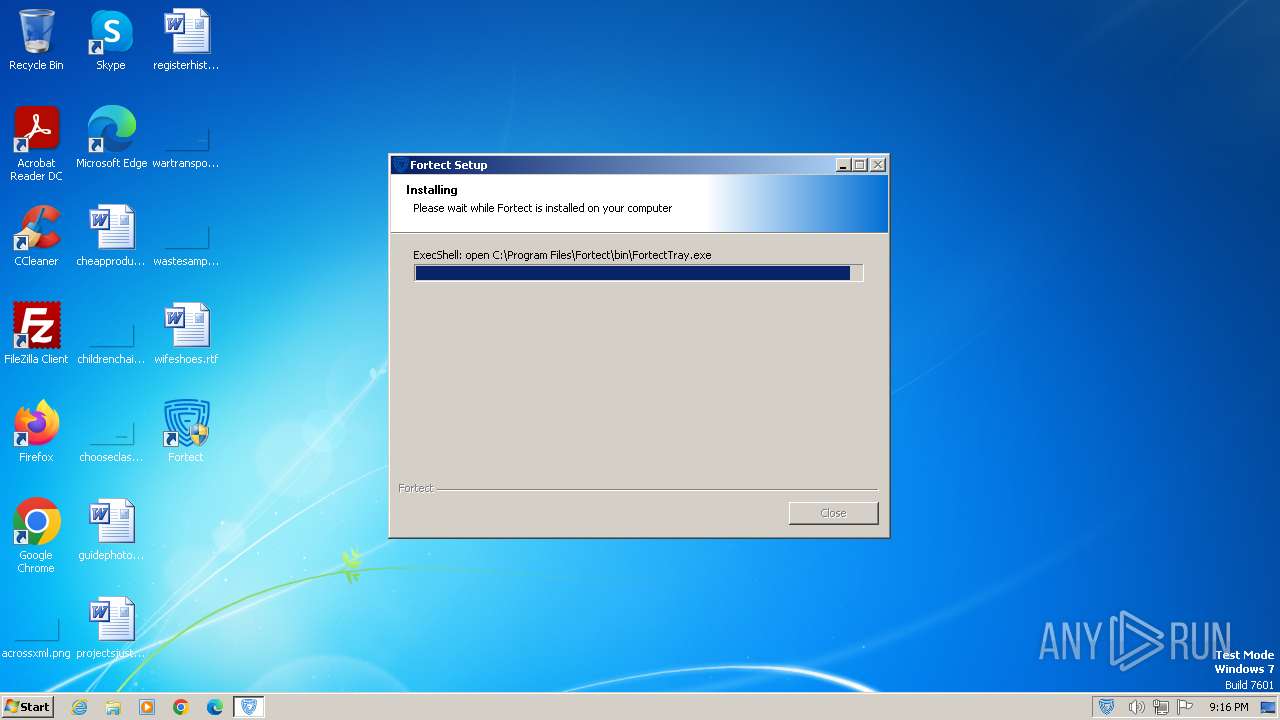
Drops the executable file immediately after the start
- Fortect.exe (PID: 2616)
- FortectMain.exe (PID: 2244)
Actions looks like stealing of personal data
- MainService.exe (PID: 2384)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Fortect.exe (PID: 2616)
Reads the Internet Settings
- WMIC.exe (PID: 4036)
- WMIC.exe (PID: 1192)
- WMIC.exe (PID: 2384)
- Fortect.exe (PID: 2616)
- WMIC.exe (PID: 2160)
- FortectMain.exe (PID: 2244)
The process creates files with name similar to system file names
- Fortect.exe (PID: 2616)
Executable content was dropped or overwritten
- Fortect.exe (PID: 2616)
- FortectMain.exe (PID: 2244)
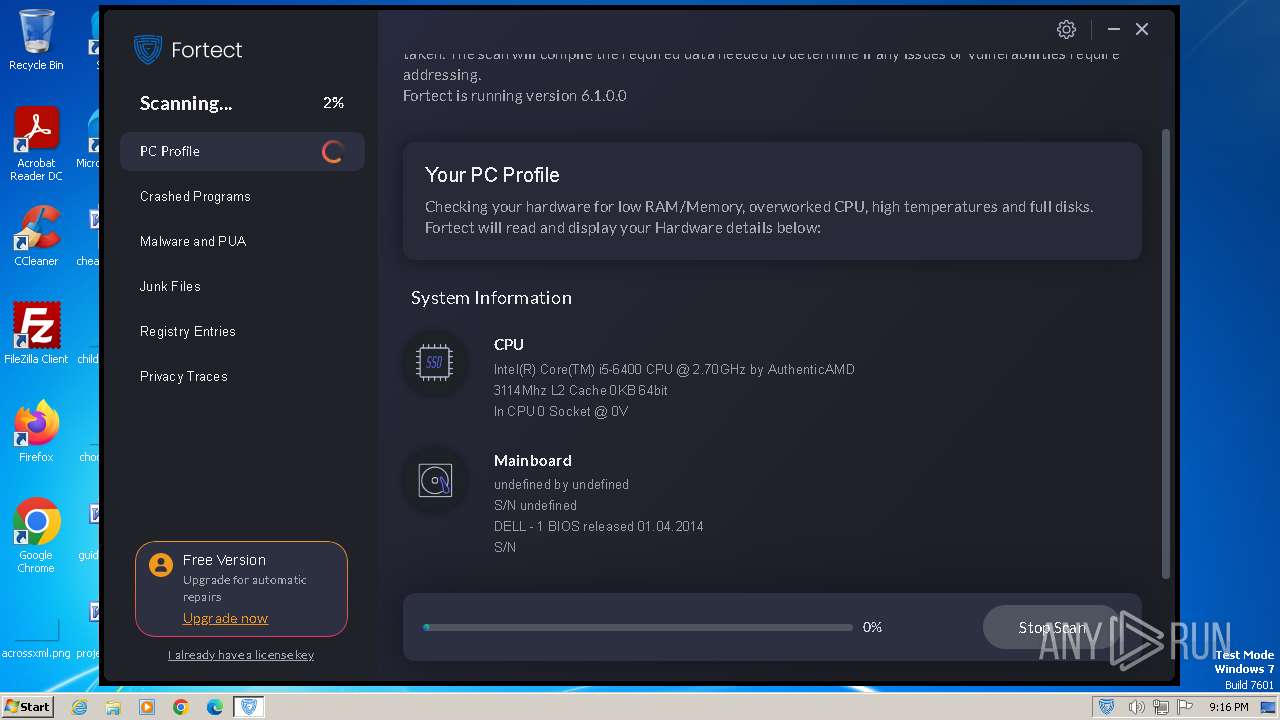
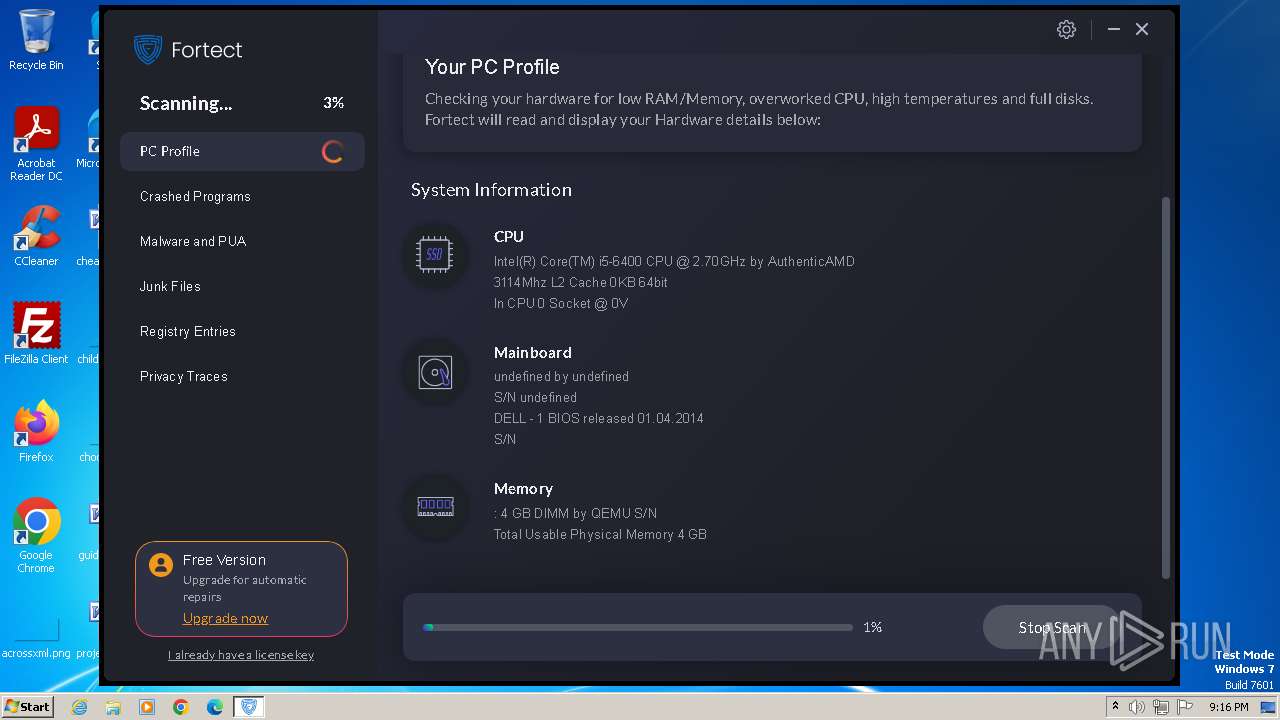
Uses WMIC.EXE to obtain BIOS management information
- cmd.exe (PID: 796)
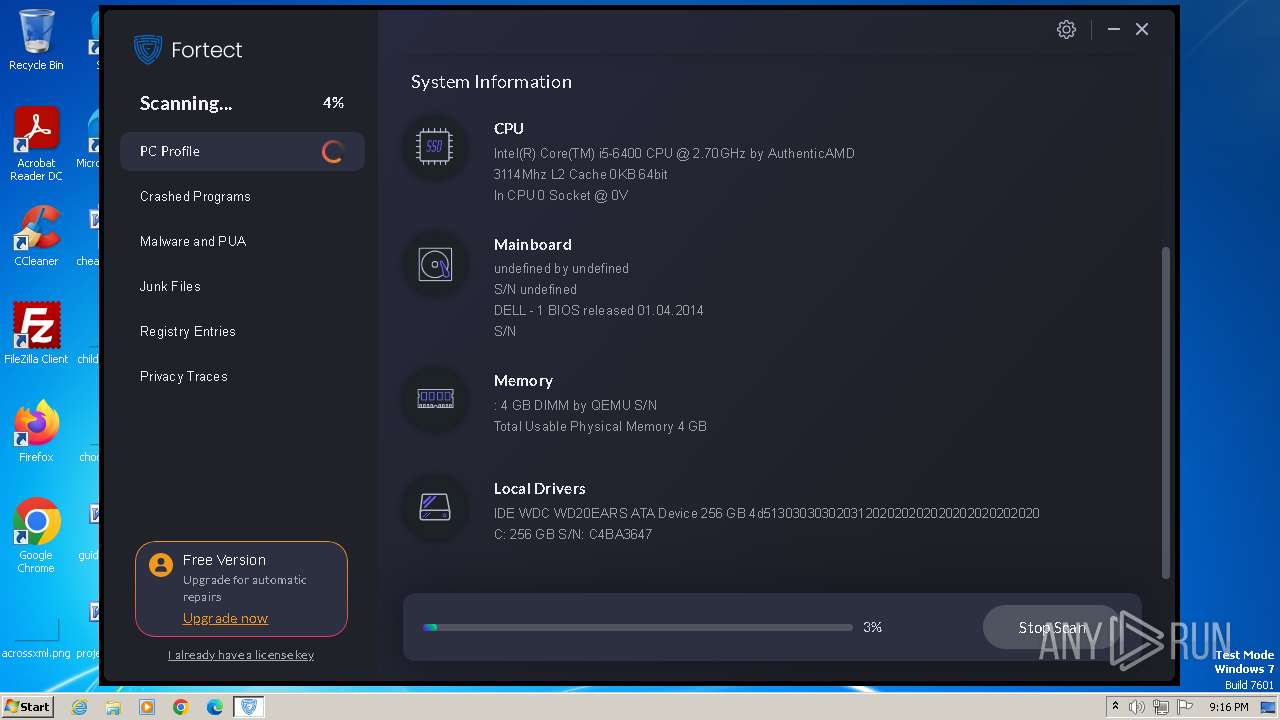
Uses WMIC.EXE to obtain data on the partitioned areas of a physical disk
- Fortect.exe (PID: 2616)
Accesses computer name via WMI (SCRIPT)
- WMIC.exe (PID: 1192)
Checks Windows Trust Settings
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- MainService.exe (PID: 2384)
Uses WMIC.EXE to obtain physical disk drive information
- Fortect.exe (PID: 2616)
Reads security settings of Internet Explorer
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
Reads settings of System Certificates
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- FortectMain.exe (PID: 2244)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1092)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 2160)
Drops 7-zip archiver for unpacking
- Fortect.exe (PID: 2616)
Process drops legitimate windows executable
- Fortect.exe (PID: 2616)
Executes as Windows Service
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2384)
Searches for installed software
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2384)
Application launched itself
- FortectMain.exe (PID: 2244)
Reads Internet Explorer settings
- MainService.exe (PID: 2384)
Reads Microsoft Outlook installation path
- MainService.exe (PID: 2384)
Adds/modifies Windows certificates
- MainService.exe (PID: 2384)
INFO
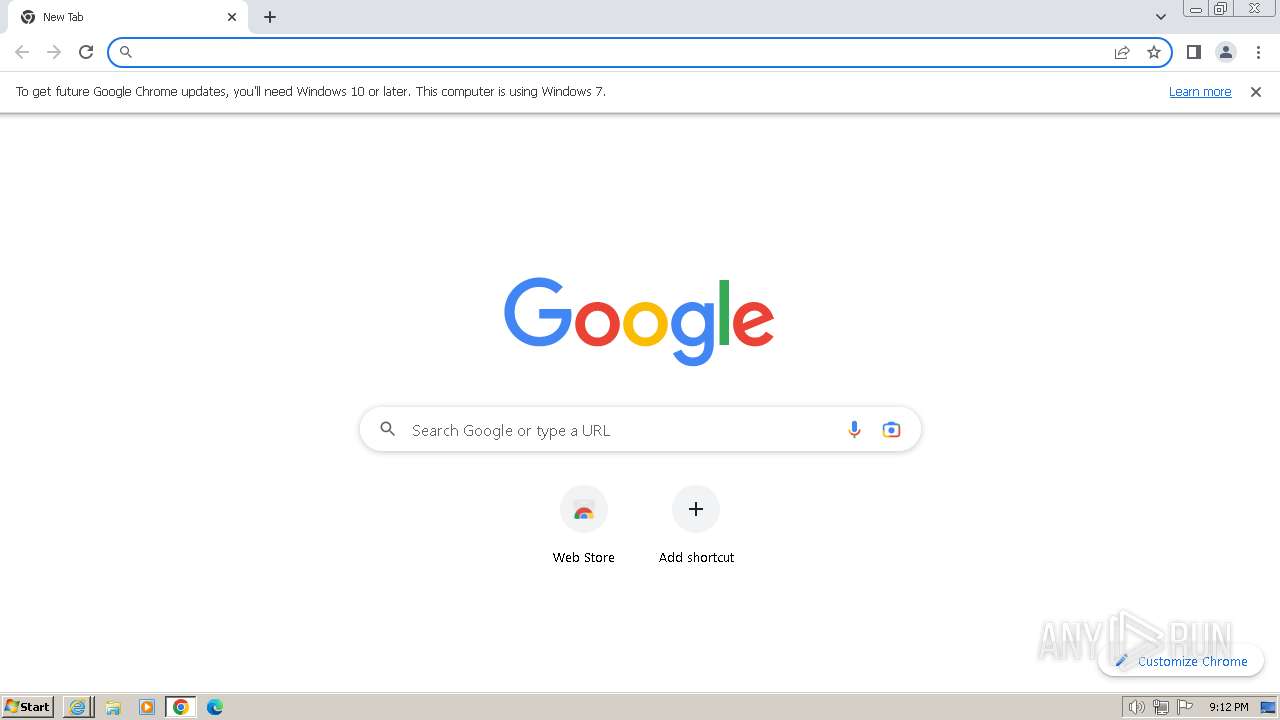
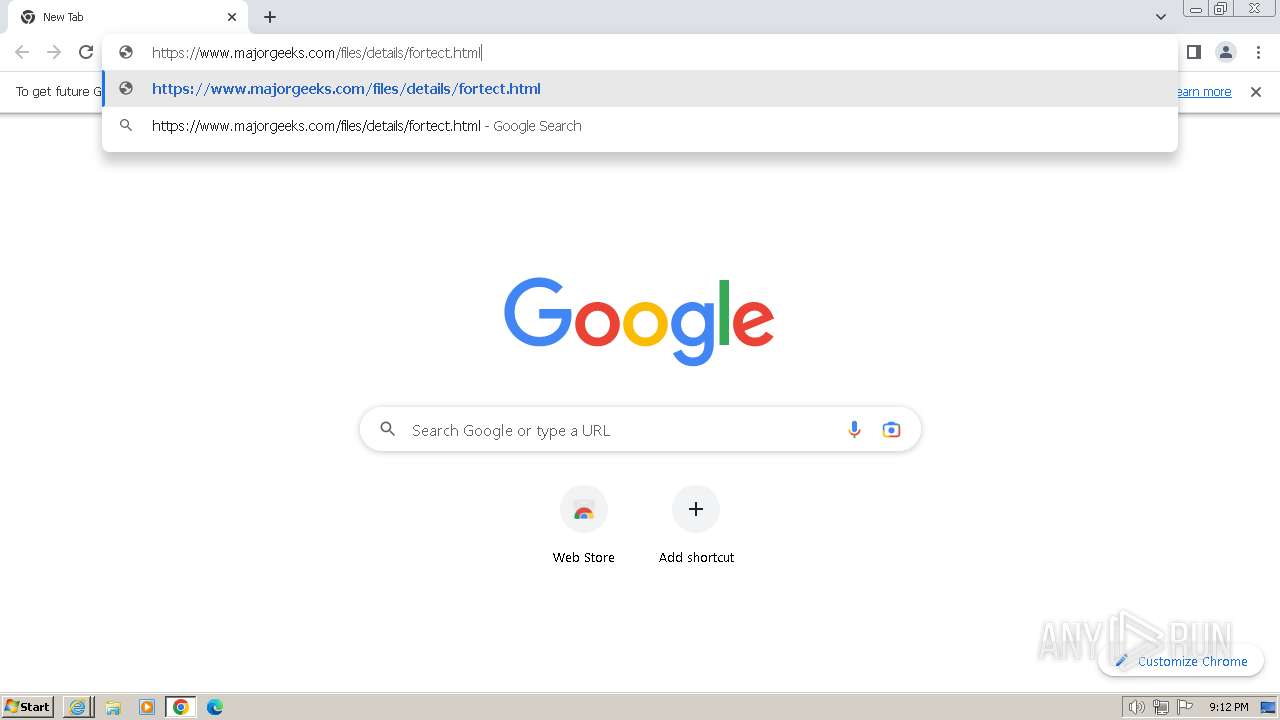
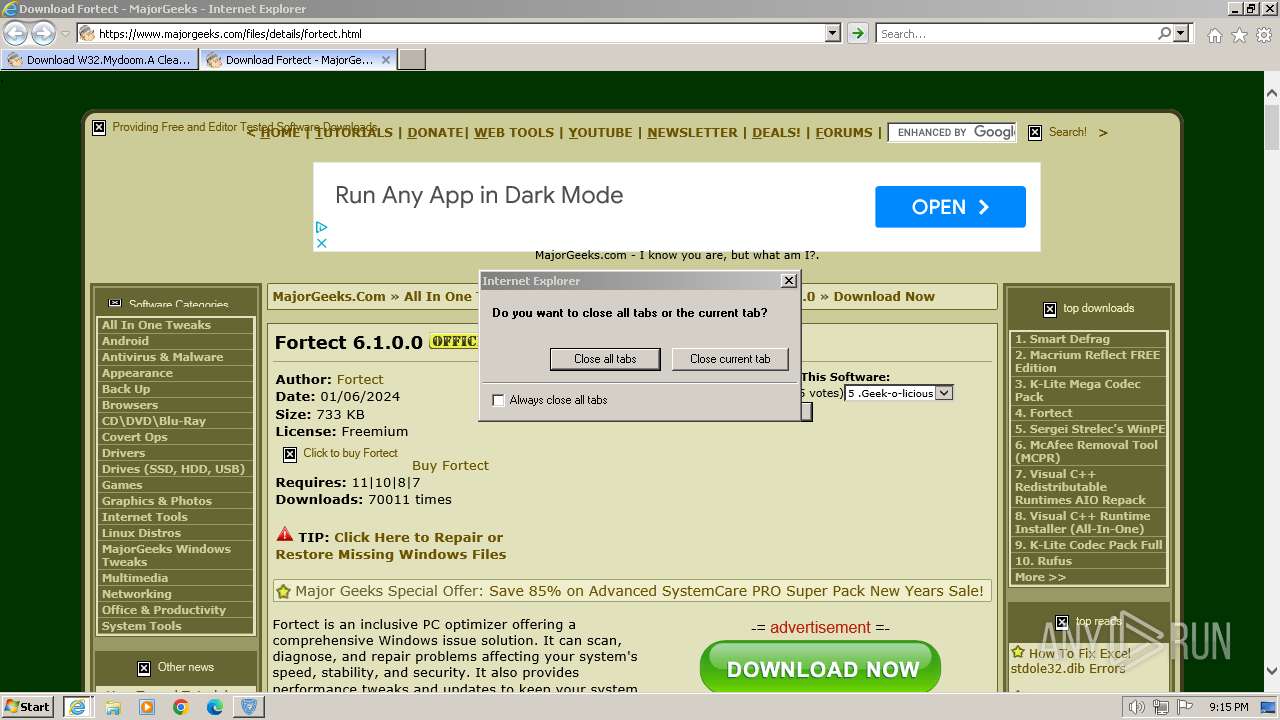
Application launched itself
- chrome.exe (PID: 2660)
- iexplore.exe (PID: 116)
Executable content was dropped or overwritten
- chrome.exe (PID: 2912)
- chrome.exe (PID: 2660)
The process uses the downloaded file
- chrome.exe (PID: 1604)
- chrome.exe (PID: 2660)
- Fortect.exe (PID: 2616)
Checks supported languages
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- MainService.exe (PID: 2788)
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2384)
- FortectTray.exe (PID: 3708)
- FortectMain.exe (PID: 2244)
- FortectMain.exe (PID: 3000)
- FortectMain.exe (PID: 2992)
- FortectMain.exe (PID: 3224)
- FortectMain.exe (PID: 572)
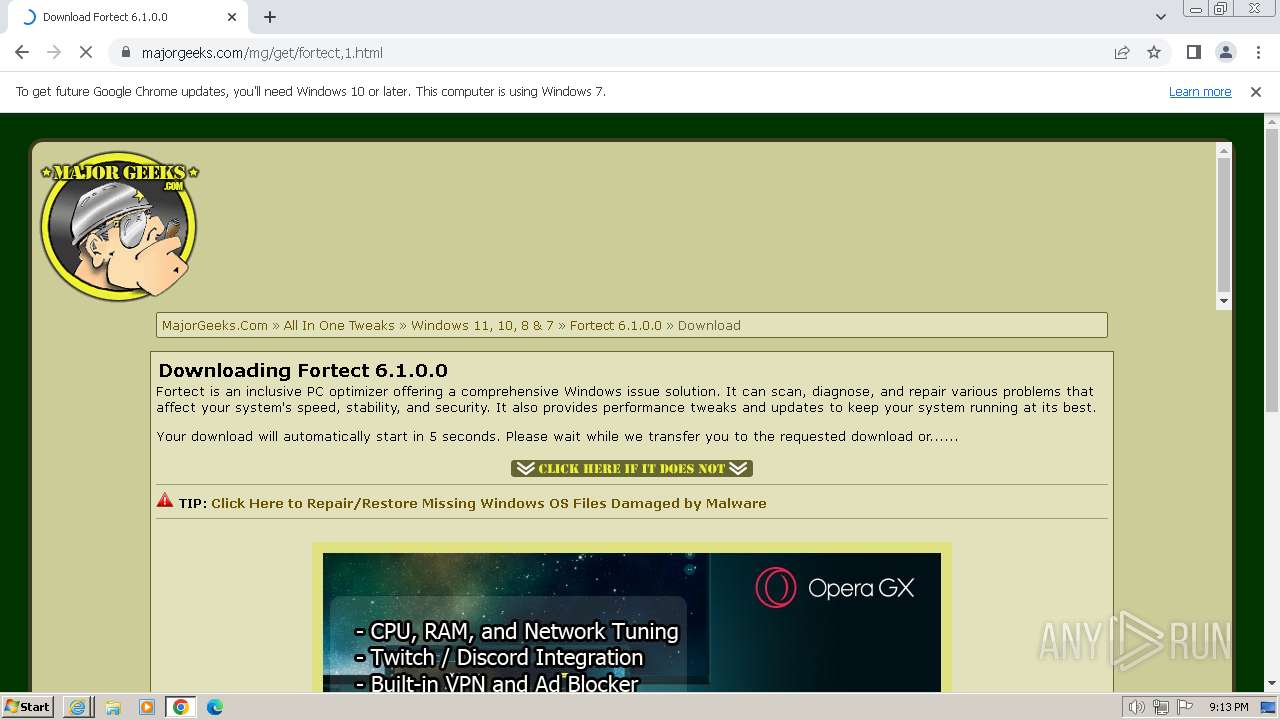
Manual execution by a user
- chrome.exe (PID: 2660)
- FortectMain.exe (PID: 2244)
Drops the executable file immediately after the start
- chrome.exe (PID: 2660)
- chrome.exe (PID: 2912)
Create files in a temporary directory
- Fortect.exe (PID: 2616)
- FortectMain.exe (PID: 2244)
Reads Environment values
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2788)
- MainService.exe (PID: 2384)
- FortectMain.exe (PID: 2244)
Reads the computer name
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2788)
- MainService.exe (PID: 2384)
- FortectMain.exe (PID: 2244)
- FortectMain.exe (PID: 3000)
- FortectMain.exe (PID: 2992)
- FortectMain.exe (PID: 572)
Reads the machine GUID from the registry
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2384)
- FortectMain.exe (PID: 2244)
Creates files in the program directory
- Fortect.exe (PID: 2616)
- MainDaemon.exe (PID: 3428)
- MainDaemon.exe (PID: 2884)
- MainService.exe (PID: 2788)
- MainService.exe (PID: 2384)
Checks proxy server information
- Fortect.exe (PID: 2616)
Creates files or folders in the user directory
- Fortect.exe (PID: 2616)
- FortectMain.exe (PID: 2244)
- FortectMain.exe (PID: 2992)
Dropped object may contain TOR URL's
- Fortect.exe (PID: 2616)
Reads product name
- FortectMain.exe (PID: 2244)
Process checks computer location settings
- FortectMain.exe (PID: 2244)
- FortectMain.exe (PID: 3224)
- MainService.exe (PID: 2384)
Process checks the number of cached credentials
- MainService.exe (PID: 2384)
Reads mouse settings
- MainService.exe (PID: 2384)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
53
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.majorgeeks.com/files/details/w32_mydoom_a_cleaning_utility.html" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 572 | "C:\Program Files\Fortect\FortectMain.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\Fortect" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1372 --field-trial-handle=1140,i,1140444327353785674,16567643288832391341,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Program Files\Fortect\FortectMain.exe | — | FortectMain.exe | |||||||||||
User: admin Company: Fortect LTD® Integrity Level: LOW Description: Fortect Main Exit code: 0 Version: 6.1.0.0 Modules
| |||||||||||||||
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3688 --field-trial-handle=1164,i,4703841617823365298,8947928370410879010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 796 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_BIOS get SerialNumber | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1092 | C:\Windows\system32\cmd.exe /Q /C "%SYSTEMROOT%\System32\wbem\wmic.exe" path Win32_ComputerSystemProduct get UUID | C:\Windows\System32\cmd.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1192 | "C:\Windows\system32\wbem\wmic.exe" logicaldisk where "DeviceID='C:'" ASSOC /assocclass:Win32_LogicalDiskToPartition | C:\Windows\System32\wbem\WMIC.exe | — | Fortect.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1636 --field-trial-handle=1164,i,4703841617823365298,8947928370410879010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4544 --field-trial-handle=1164,i,4703841617823365298,8947928370410879010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --mojo-platform-channel-handle=3652 --field-trial-handle=1164,i,4703841617823365298,8947928370410879010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1000 --field-trial-handle=1164,i,4703841617823365298,8947928370410879010,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
123 170
Read events
122 804
Write events
360
Delete events
6
Modification events
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
59
Suspicious files
547
Text files
364
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D8A8300C80EBE873D831EB864DEFFBE2 | binary | |
MD5:A9EA080A414ED6EDB1C31E1ADF92CC21 | SHA256:1147360FE370DC775960FFA0DA1E660FC3789456454DF978076F0797126DF12C | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:C158E700D10F297A066304BFED6B1C76 | SHA256:CB8CE096D7558544082C43C52E1CC2AE227B6CBE8DED1A17834A2BBB7A6E59CC | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFAFA.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarFAFB.tmp | binary | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:0E5393E57D811AA2188DF0414C9880BA | SHA256:1DA4C99C5AEEB86021934BF9D5519967E1DA57BEBF18029F55FEA26450349515 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\index[1].css | text | |
MD5:25ECF48402A2F38013EE4C9A51E4C61B | SHA256:F223B501BC77CB00C1213BEE7352DBDBB808A8FD6FAB3542E4401054683032D2 | |||
| 2032 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabFB0C.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
98
TCP/UDP connections
389
DNS requests
245
Threats
37
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2032 | iexplore.exe | GET | 200 | 23.48.23.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?947fb26d7412b1b7 | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 23.48.23.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?b67c9d757472bd69 | DE | compressed | 65.2 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 23.192.153.142:80 | http://x1.c.lencr.org/ | GB | binary | 717 b | unknown |
2032 | iexplore.exe | GET | 200 | 142.250.186.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | binary | 1.41 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 23.48.23.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | DE | compressed | 4.66 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 23.48.23.33:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | DE | compressed | 4.66 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 23.32.238.49:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNR%2F1o%2BMmGWq5mzYYevzju5mw%3D%3D | DE | binary | 503 b | unknown |
2032 | iexplore.exe | GET | 200 | 108.138.2.107:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | binary | 2.02 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 18.245.39.64:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | binary | 1.49 Kb | unknown |
2032 | iexplore.exe | GET | 200 | 23.32.238.49:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgT9S54BSJAluSIrohSmwlA2hQ%3D%3D | DE | binary | 503 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2032 | iexplore.exe | 51.81.2.245:443 | www.majorgeeks.com | OVH SAS | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2032 | iexplore.exe | 23.48.23.33:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2032 | iexplore.exe | 23.192.153.142:80 | x1.c.lencr.org | AKAMAI-AS | GB | unknown |
2032 | iexplore.exe | 23.32.238.49:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2032 | iexplore.exe | 51.81.2.248:443 | ra.majorgeeks.com | OVH SAS | US | unknown |
2032 | iexplore.exe | 142.250.186.104:443 | www.googletagmanager.com | GOOGLE | US | unknown |
2032 | iexplore.exe | 142.250.185.194:443 | pagead2.googlesyndication.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.majorgeeks.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.googletagmanager.com |
| whitelisted |
ra.majorgeeks.com |
| unknown |
pagead2.googlesyndication.com |
| whitelisted |
platform-api.sharethis.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
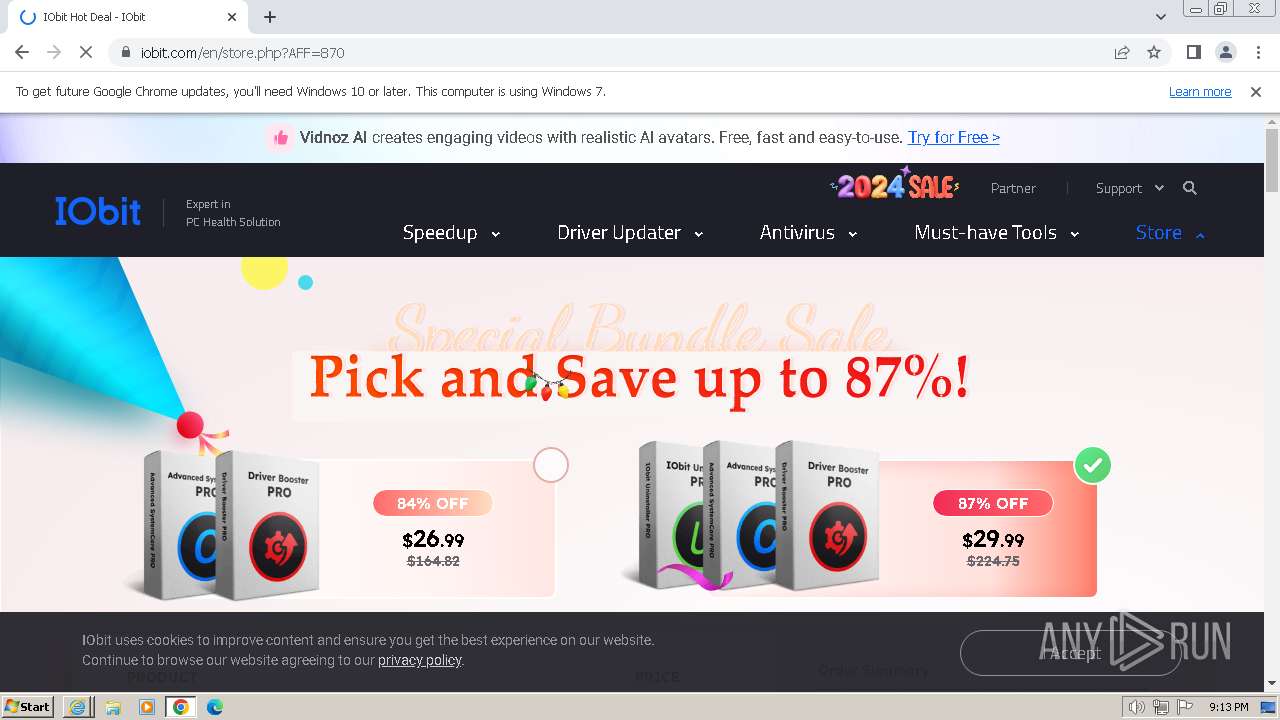
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2912 | chrome.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
2616 | Fortect.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed PC Optimizer Software Domain (fortect .com in TLS SNI) |
1080 | svchost.exe | Possibly Unwanted Program Detected | ET ADWARE_PUP Observed DNS Query to PC Optimizer Software Domain (fortect .com) |
Process | Message |
|---|---|
Fortect.exe | ExecShellAsUser: elevated process detected |
Fortect.exe | ExecShellAsUser: got desktop |
Fortect.exe | ExecShellAsUser: thread finished |
Fortect.exe | ExecShellAsUser: DLL_PROCESS_DETACH |