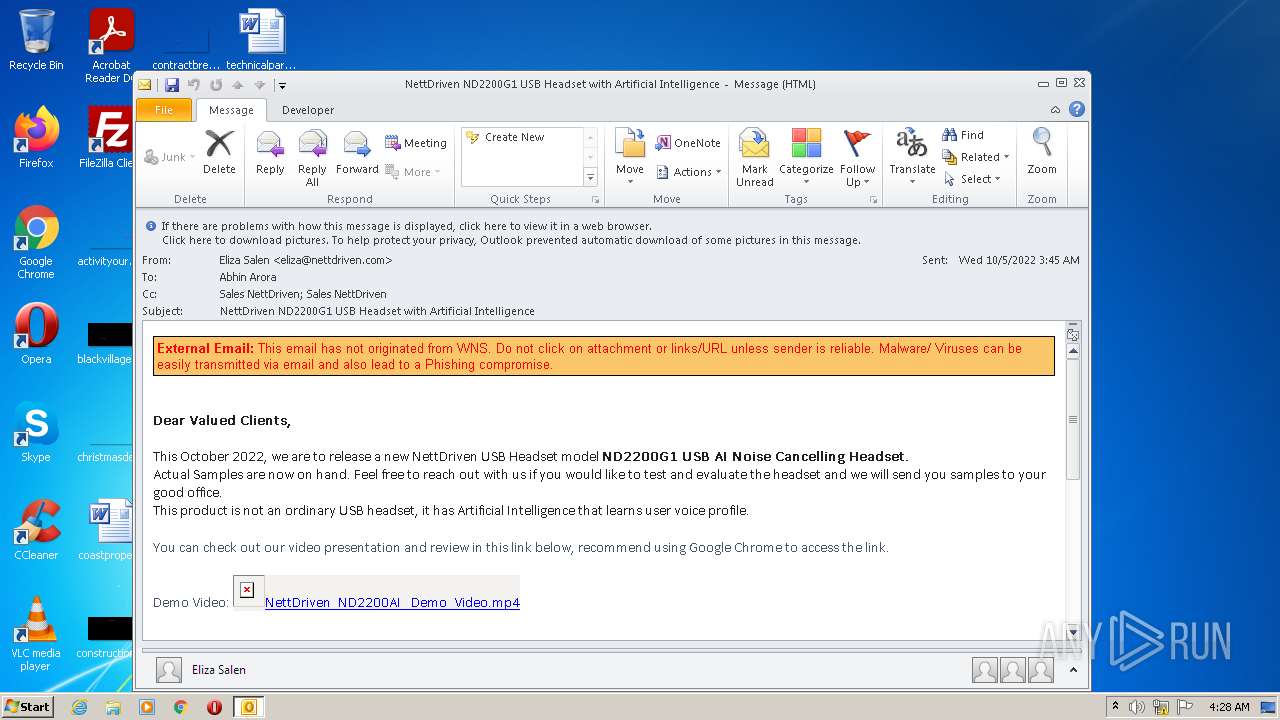
| File name: | phish_alert_sp2_2.0.0.0.eml |
| Full analysis: | https://app.any.run/tasks/b397fe1a-545c-4447-a0a5-4ce454d16c63 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 03:27:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 465CD398064604946BD93C7AADDA84CD |
| SHA1: | FD3EDF9D61D26555D22ADEBE5BD3329E94756D41 |
| SHA256: | 906A9A6419DECB4271A3751D21C13923223E7EC3582732391838AAB2B2C0B594 |
| SSDEEP: | 384:7PArZ2GRMR2GRMZIkfxjgneYwO5tumNupE0jY9chwYCDnmTIGMdyJxrw71Mpj292:OIyvYV3P9ciJuIPd8uQ9H |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the computer name
- OUTLOOK.EXE (PID: 1420)
Searches for installed software
- OUTLOOK.EXE (PID: 1420)
Checks supported languages
- OUTLOOK.EXE (PID: 1420)
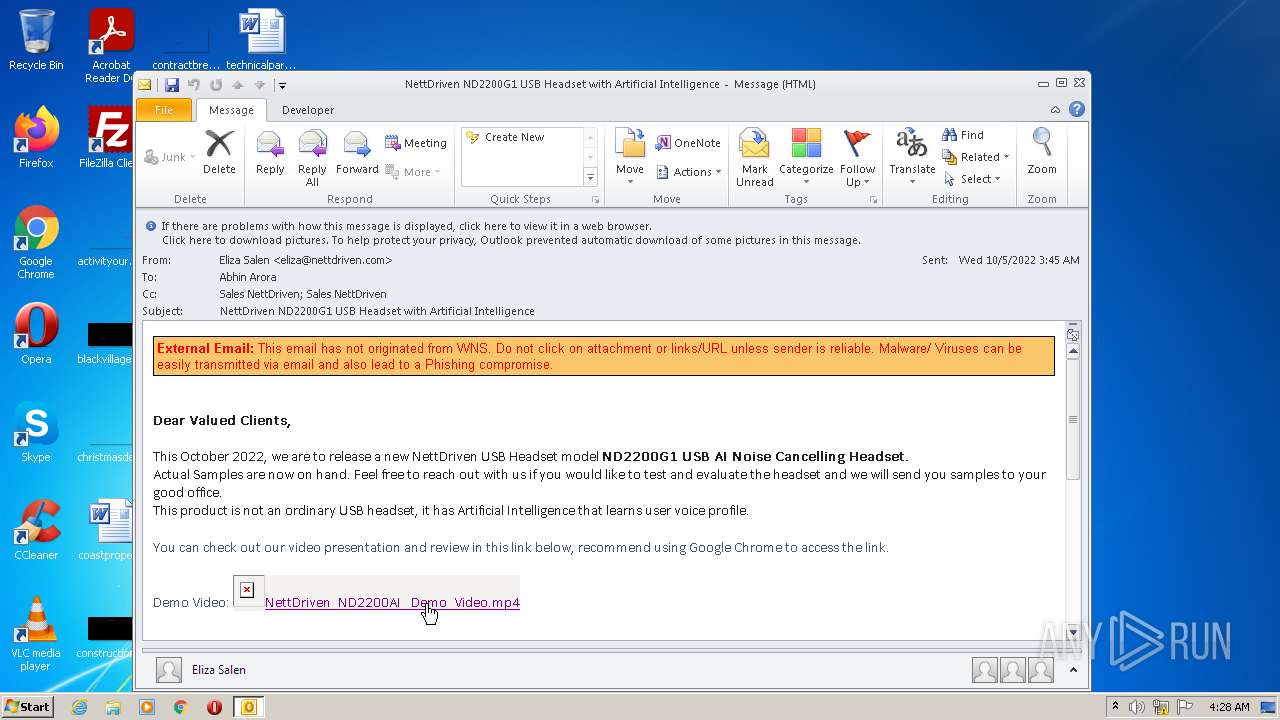
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1420)
Creates files in the user directory
- OUTLOOK.EXE (PID: 1420)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1040)
INFO
Reads the computer name
- iexplore.exe (PID: 676)
- iexplore.exe (PID: 1040)
Checks supported languages
- iexplore.exe (PID: 676)
- iexplore.exe (PID: 1040)
Application launched itself
- iexplore.exe (PID: 676)
Changes internet zones settings
- iexplore.exe (PID: 676)
Reads settings of System Certificates
- iexplore.exe (PID: 1040)
- iexplore.exe (PID: 676)
Creates files in the user directory
- iexplore.exe (PID: 1040)
- iexplore.exe (PID: 676)
Checks Windows Trust Settings
- iexplore.exe (PID: 1040)
- iexplore.exe (PID: 676)
Reads internet explorer settings
- iexplore.exe (PID: 1040)
Modifies the phishing filter of IE
- iexplore.exe (PID: 676)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1420)
Changes settings of System certificates
- iexplore.exe (PID: 676)
Adds / modifies Windows certificates
- iexplore.exe (PID: 676)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
39
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
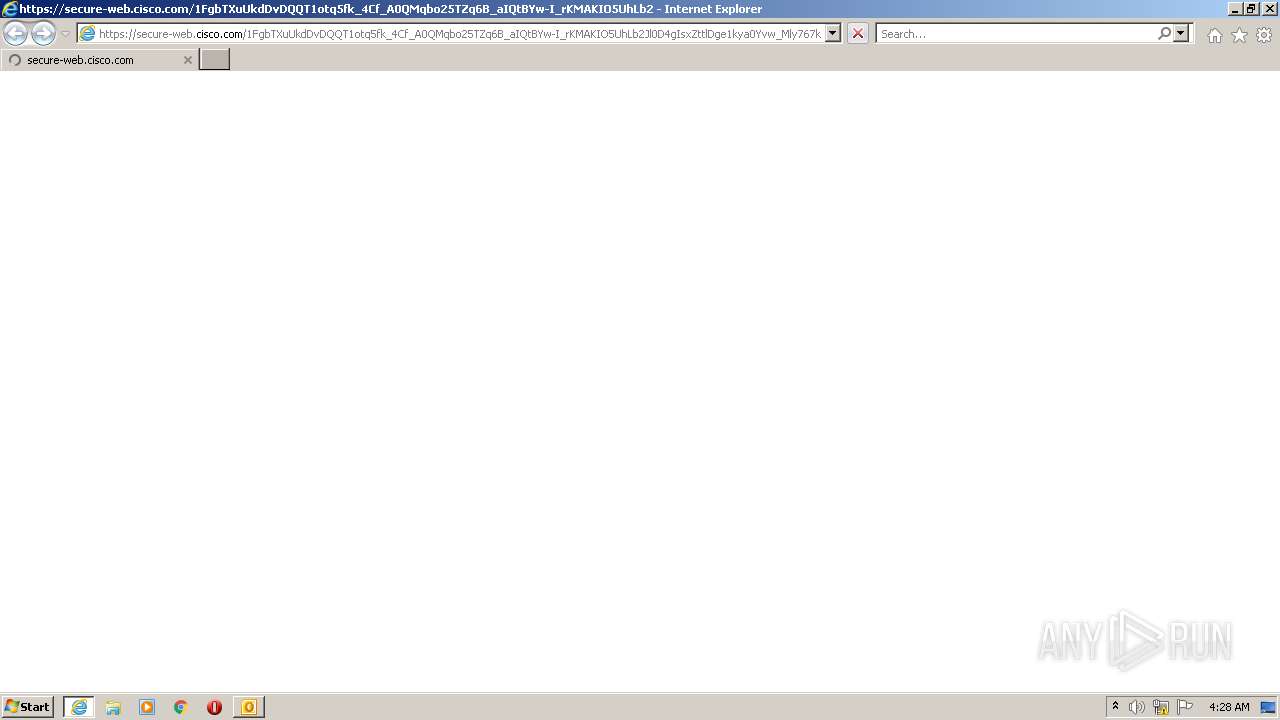
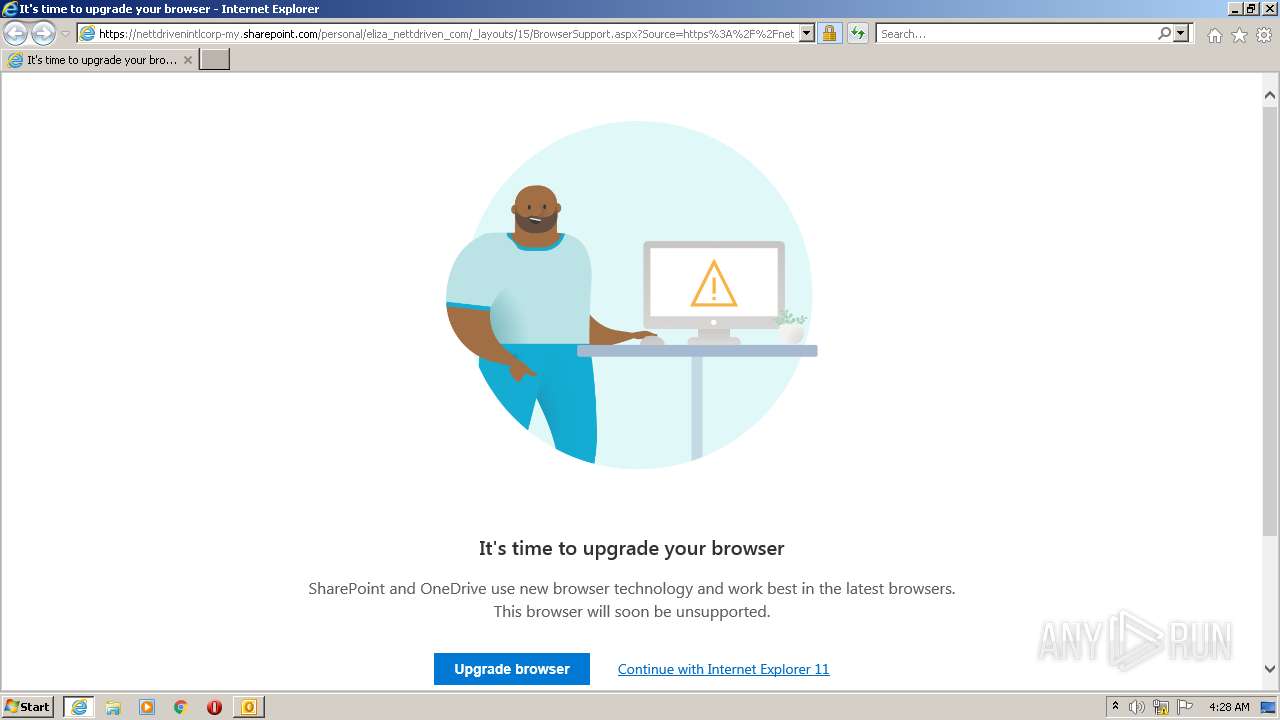
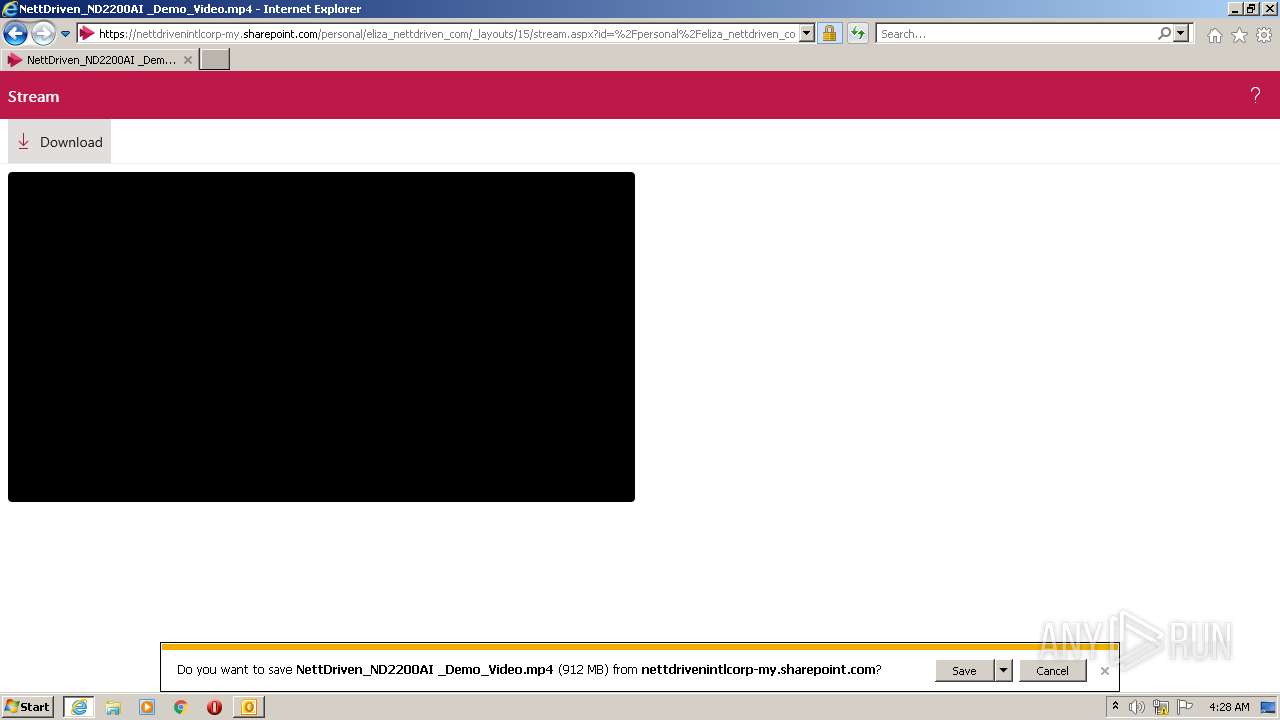
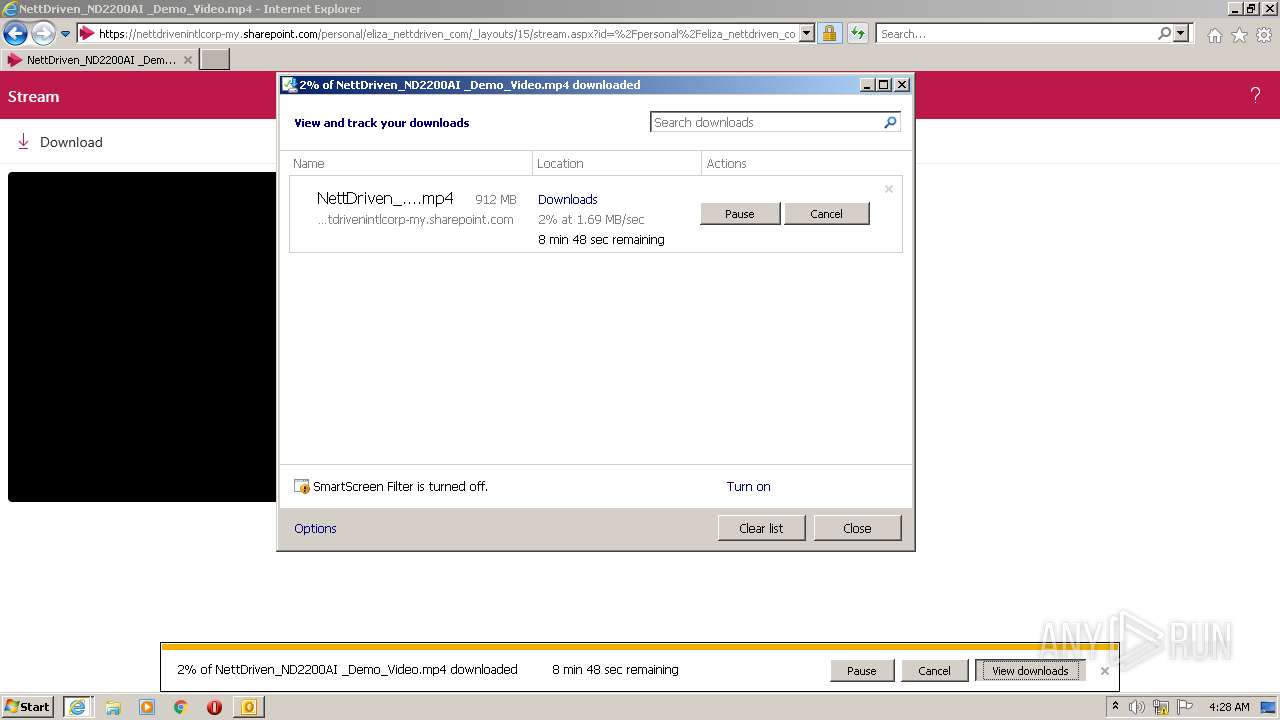
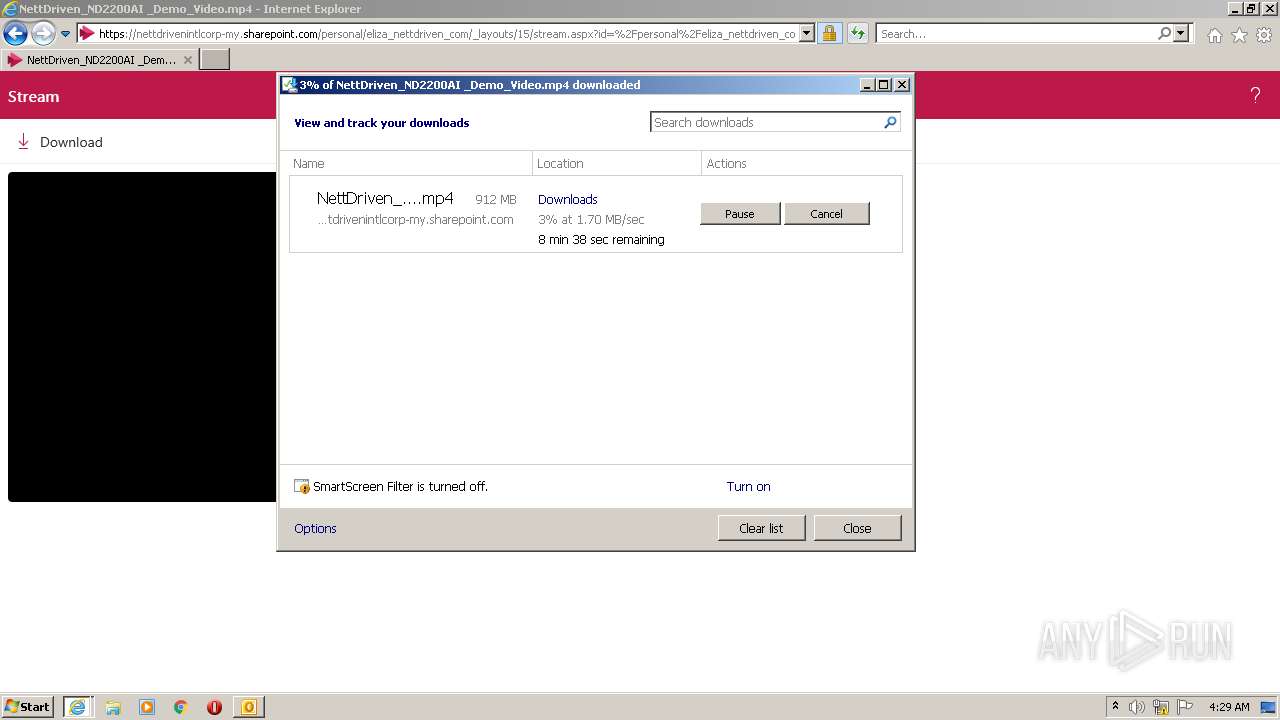
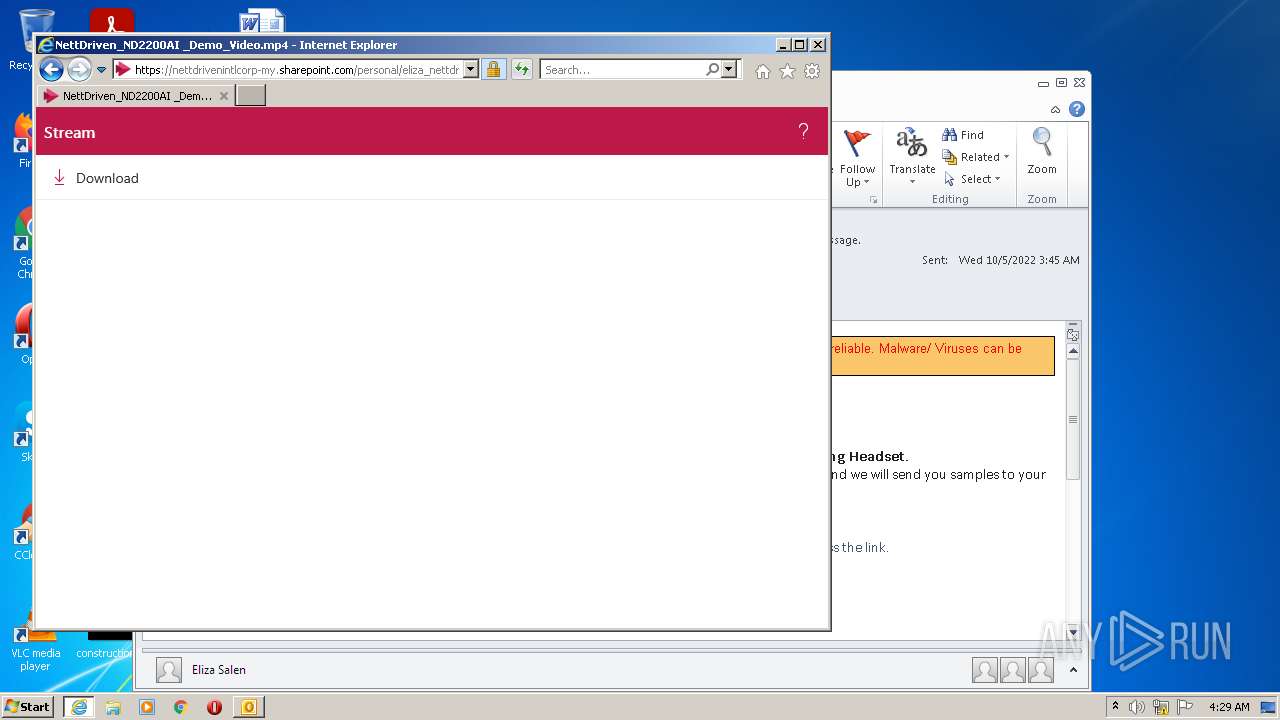
| 676 | "C:\Program Files\Internet Explorer\iexplore.exe" https://secure-web.cisco.com/1FgbTXuUkdDvDQQT1otq5fk_4Cf_A0QMqbo25TZq6B_aIQtBYw-I_rKMAKIO5UhLb2Jl0D4gIsxZttlDge1kya0Yvw_Mly767k90JuKBIYYDHyhbK2ubtHSMfAcnb4kLTalLma6W_mwpmMSOp0Lucair-kB8Ao9Ong3Rw4iiOf_-Xb9QY9-7uLKWDMitlAgjjA441Y_EUT8xUVZZk3DOQDhVT0G8UFEWAyg7qrMMvvEp1dHssuE3PqgxLsXhYN1EpWWGbI1XT8Ri0unhgY7MUKSe0XKJfyh1okWsM4scwmJ8ARMHYLrGbOvRo3bptg3-m/https%3A%2F%2Fnettdrivenintlcorp-my.sharepoint.com%2F%3Av%3A%2Fg%2Fpersonal%2Feliza_nettdriven_com%2FERq4Kse7UD1IkftYWQGMP80BNP5EEfYRWFQTbY3IDaO-mg%3Fe%3DehMDZU | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:676 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1420 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\phish_alert_sp2_2.0.0.0.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
18 160
Read events
17 423
Write events
715
Delete events
22
Modification events
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1420) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
15
Text files
65
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1420 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR99EF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1420 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 1420 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1420 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1420 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_A5CE06CBB17D2A4D8D9D92D1C0606C06.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 1040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\263821BCA2CBC5EA0B25012F05788322_41310C887E59D4EB5B8FD9D3DCA2C98D | der | |
MD5:— | SHA256:— | |||
| 676 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:— | SHA256:— | |||
| 1040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | der | |
MD5:— | SHA256:— | |||
| 1040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\263821BCA2CBC5EA0B25012F05788322_41310C887E59D4EB5B8FD9D3DCA2C98D | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
60
DNS requests
24
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1420 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1040 | iexplore.exe | GET | 200 | 104.18.25.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRSHuNsR4EZqcsD%2BrdOV%2BEZevGBiwQUtXYMMBHOx5JCTUzHXCzIqQzoC2QCExIAID0mTAYs5VcQIg4AAAAgPSY%3D | US | der | 1.70 Kb | whitelisted |
1040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/DigiCertGlobalRootCA.crl | US | der | 631 b | whitelisted |
1040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1040 | iexplore.exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTULRG8NAnkG2vMiFulhUophWOf2gQUibibtp7t%2B7DGvQ3sZ048o5KdLfkCEEABfOt6GkOKldoRYnQ%2BdUA%3D | US | der | 1.46 Kb | whitelisted |
676 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
1040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
1040 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6fdabcad10f44235 | US | compressed | 4.70 Kb | whitelisted |
1040 | iexplore.exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTQfEOioPd4%2FtCA3%2FhgDklRXB0FwgQU7UQZwNPwBovupHu%2BQucmVMiONnYCEEABbvsKIFz66%2BGPcdc6u3g%3D | US | der | 1.63 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1420 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1040 | iexplore.exe | 146.112.255.69:443 | secure-web.cisco.com | OPENDNS | US | suspicious |
1040 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
1040 | iexplore.exe | 13.107.136.9:443 | nettdrivenintlcorp-my.sharepoint.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1040 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
676 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
676 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
— | — | 13.107.136.9:443 | nettdrivenintlcorp-my.sharepoint.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1040 | iexplore.exe | 13.107.6.163:443 | config.fp.measure.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1040 | iexplore.exe | 40.79.141.152:443 | browser.pipe.aria.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
secure-web.cisco.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
commercial.ocsp.identrust.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
nettdrivenintlcorp-my.sharepoint.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
shell.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1040 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
1040 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |