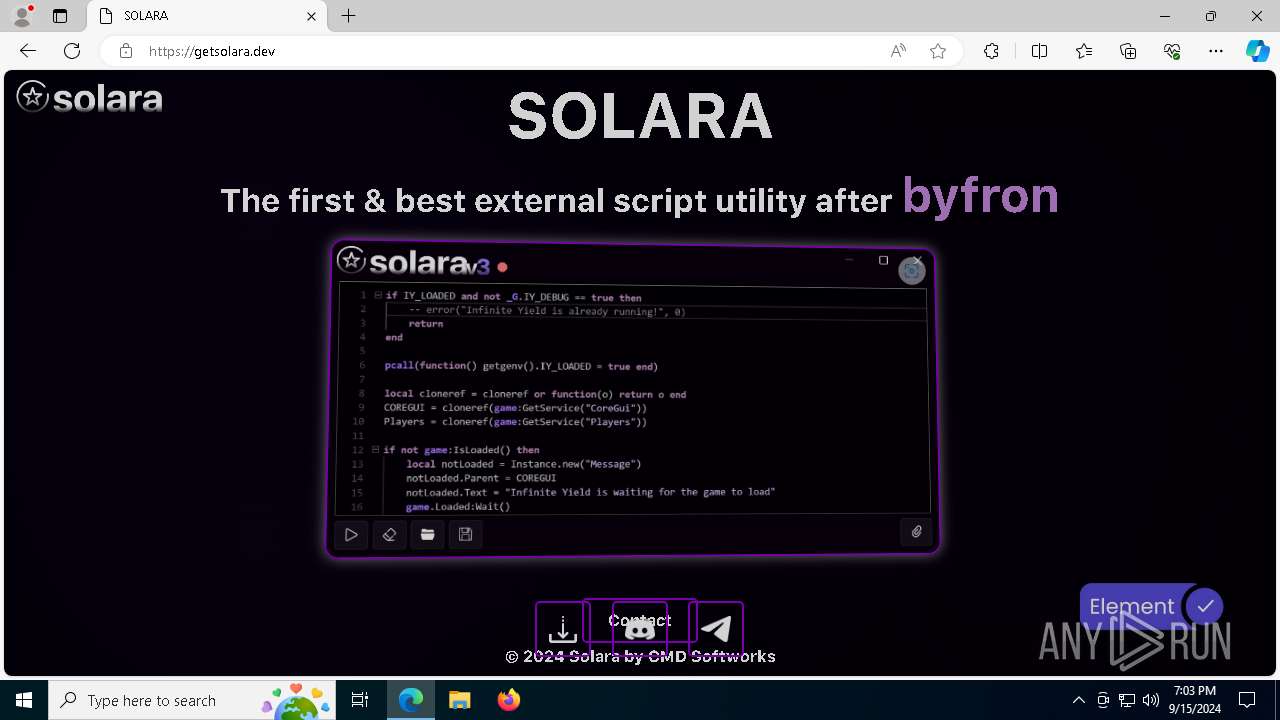
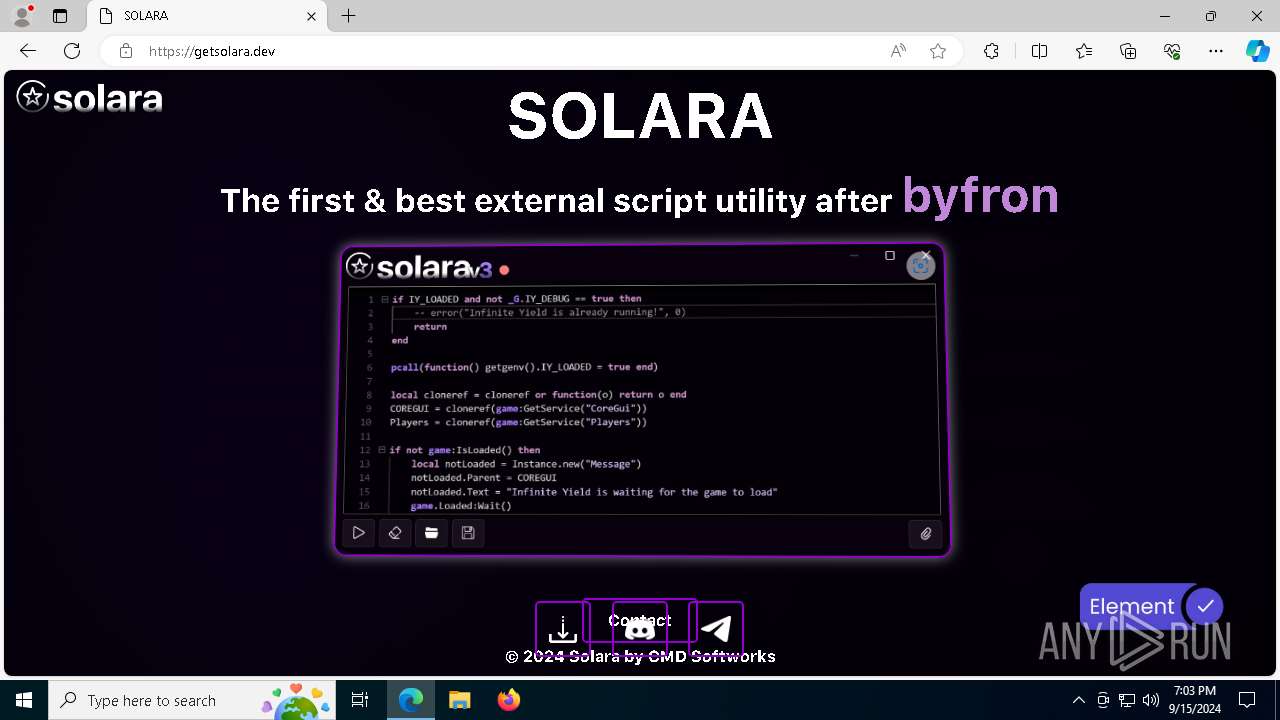
| URL: | https://getsolara.dev/ |
| Full analysis: | https://app.any.run/tasks/55a8cf1a-85aa-4481-ad46-3d4ea012f3c8 |
| Verdict: | Malicious activity |
| Analysis date: | September 15, 2024, 19:03:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 895212477ADC792C77F61B22FCD086DE |
| SHA1: | B500AD173FD9998E2A15ED1D95F5C167DA59DC19 |
| SHA256: | 9069E714CFAB64E4EDCBAC1C48B99301F895D279137C62A0D72D43B5C354AA68 |
| SSDEEP: | 3:N8h/J+S:2n |
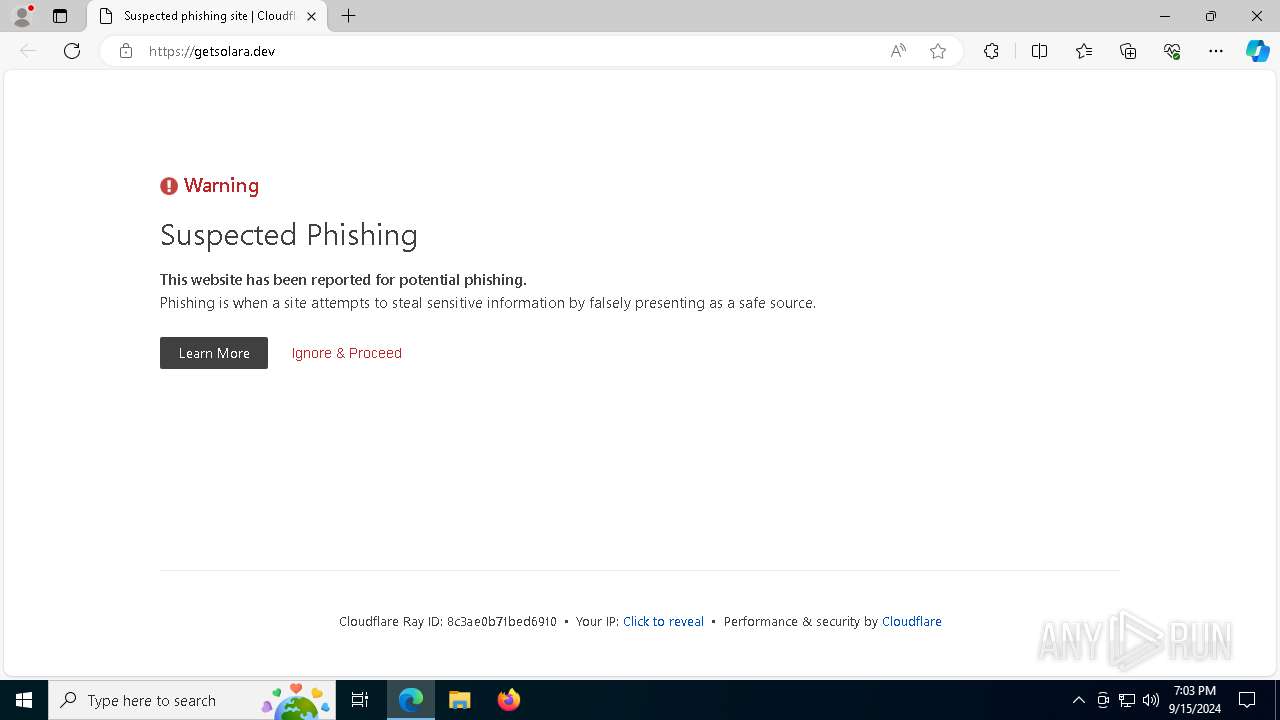
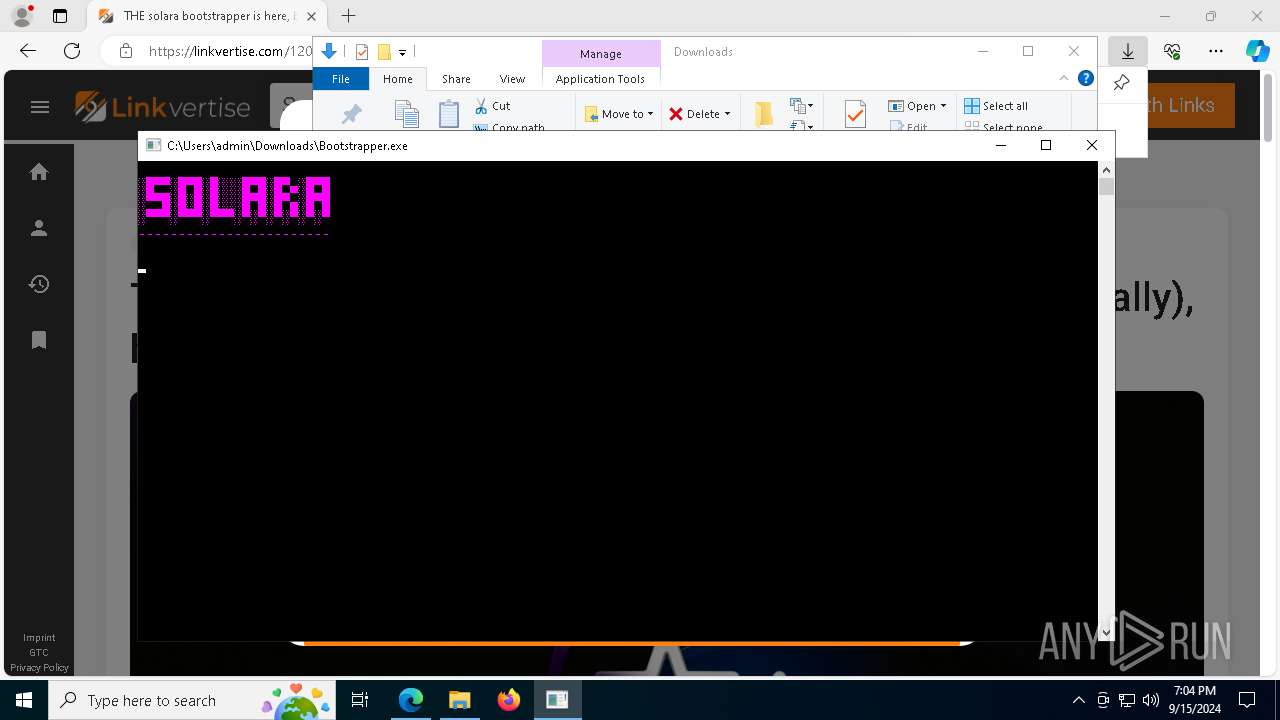
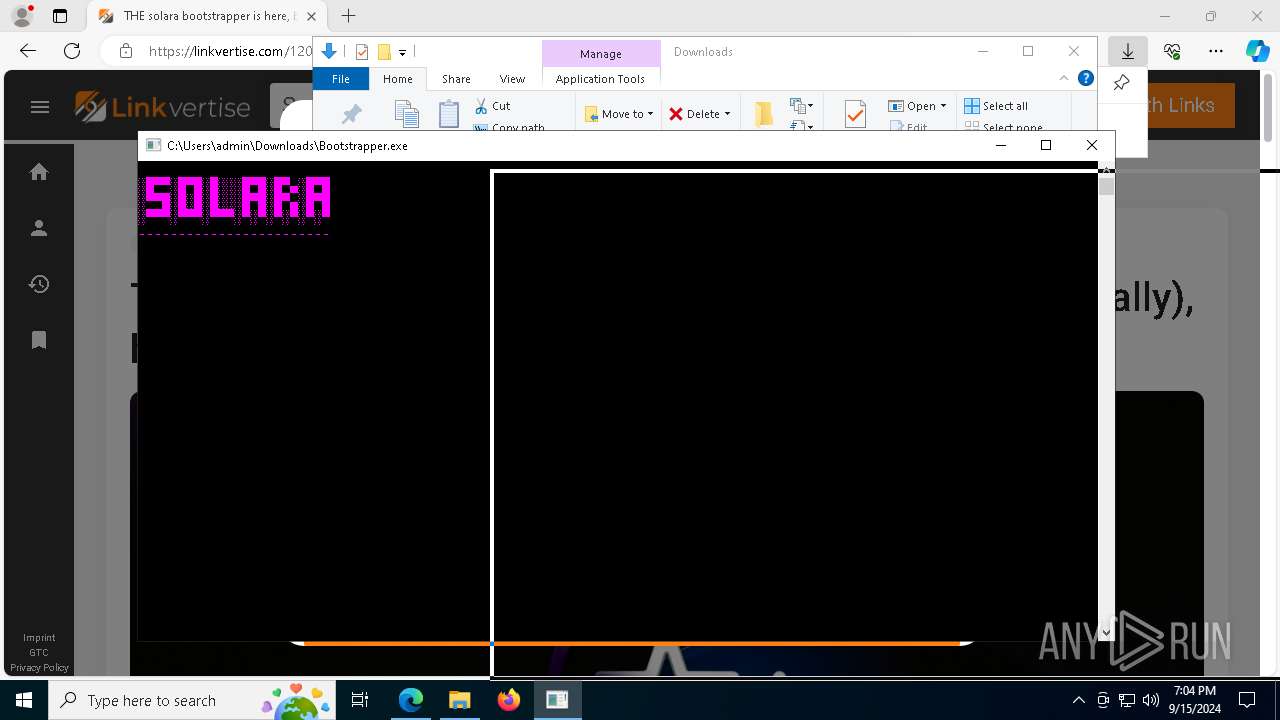
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 5164)
- svchost.exe (PID: 2256)
SUSPICIOUS
Connecting to InterPlanetary File System domains
- msedge.exe (PID: 5164)
Reads the date of Windows installation
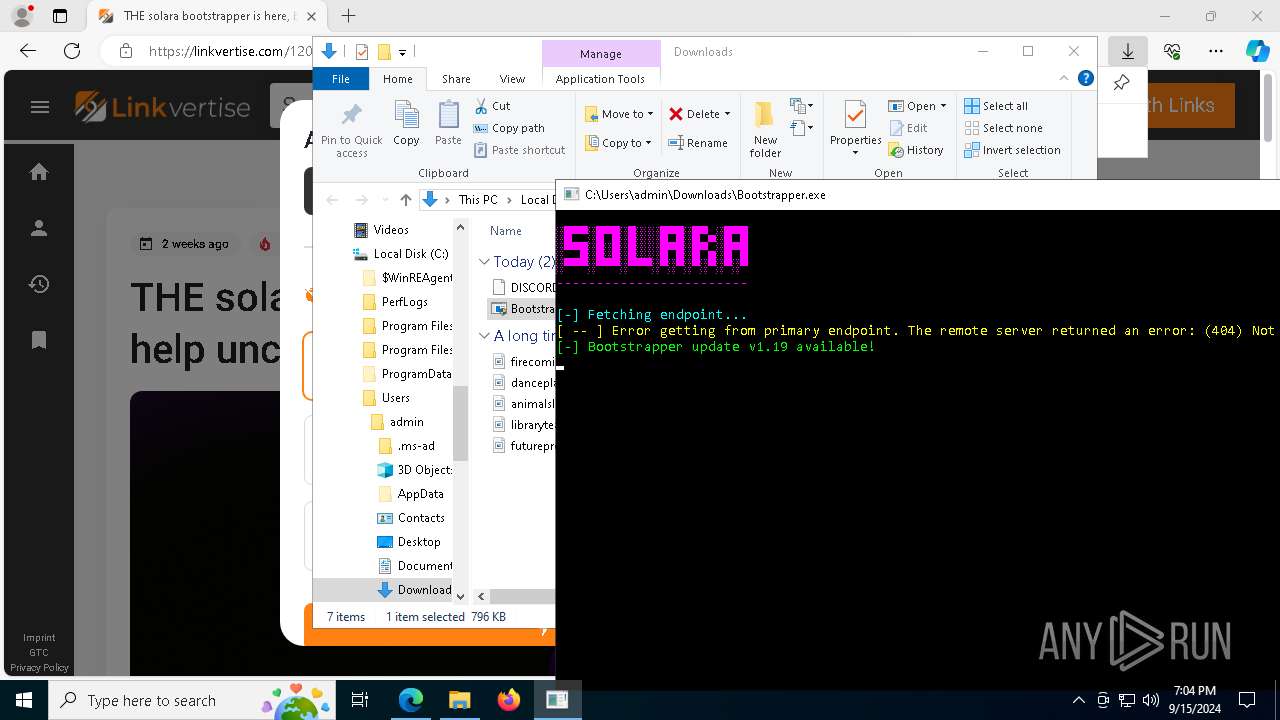
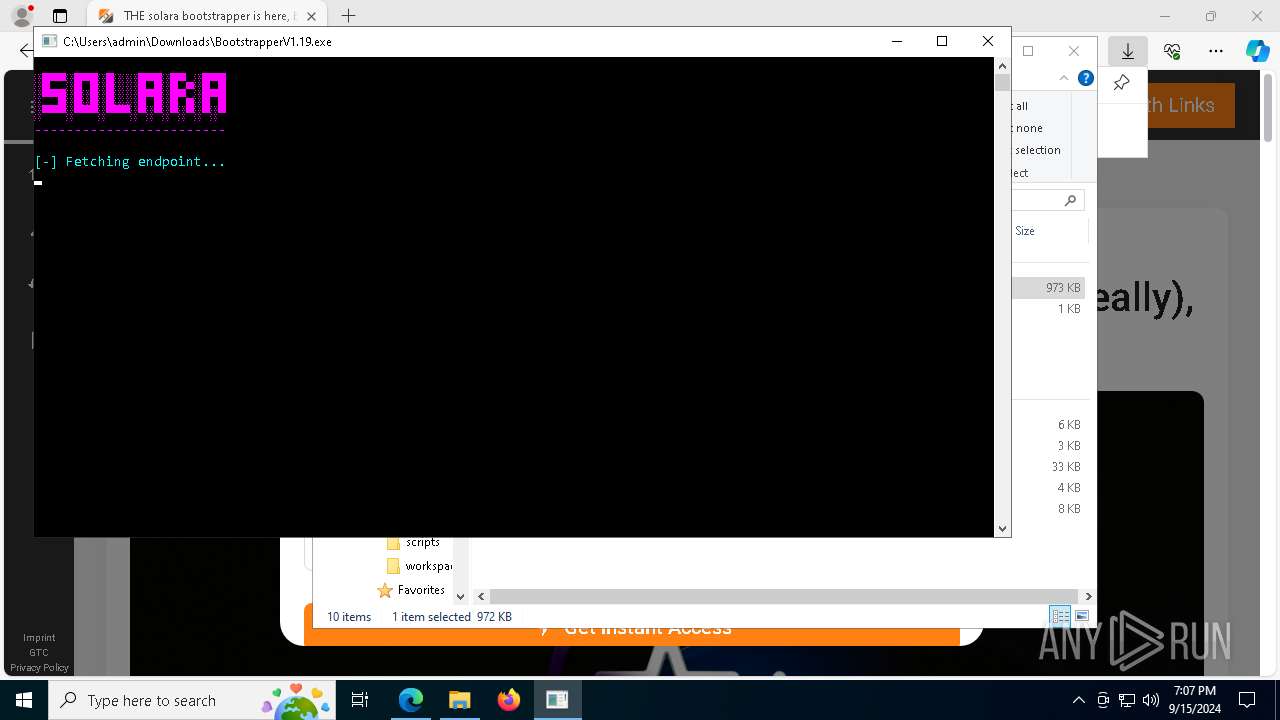
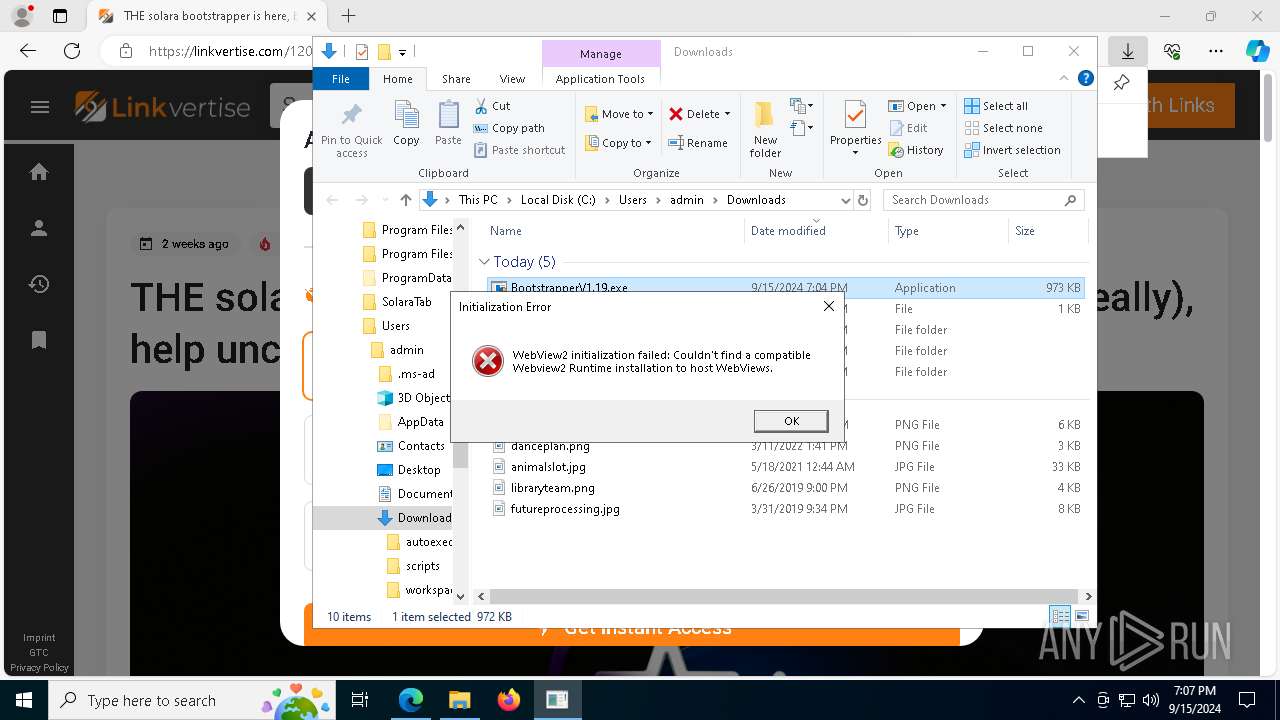
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- BootstrapperV1.19.exe (PID: 7596)
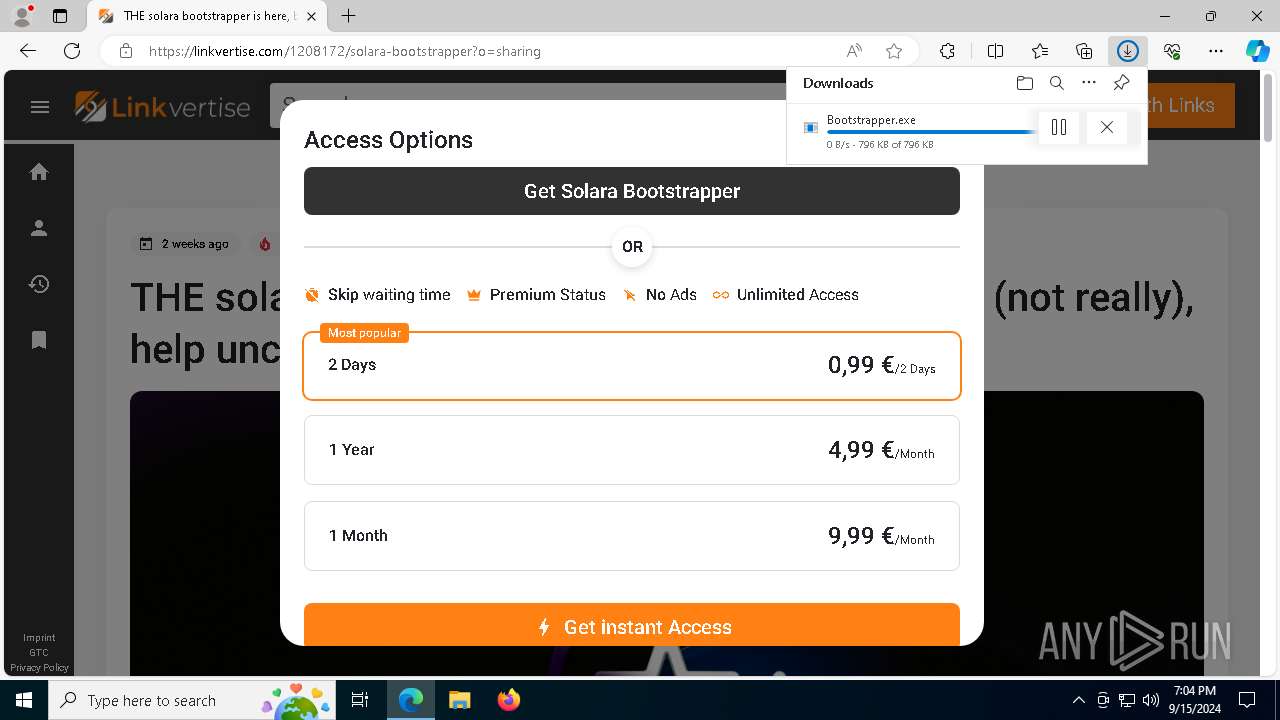
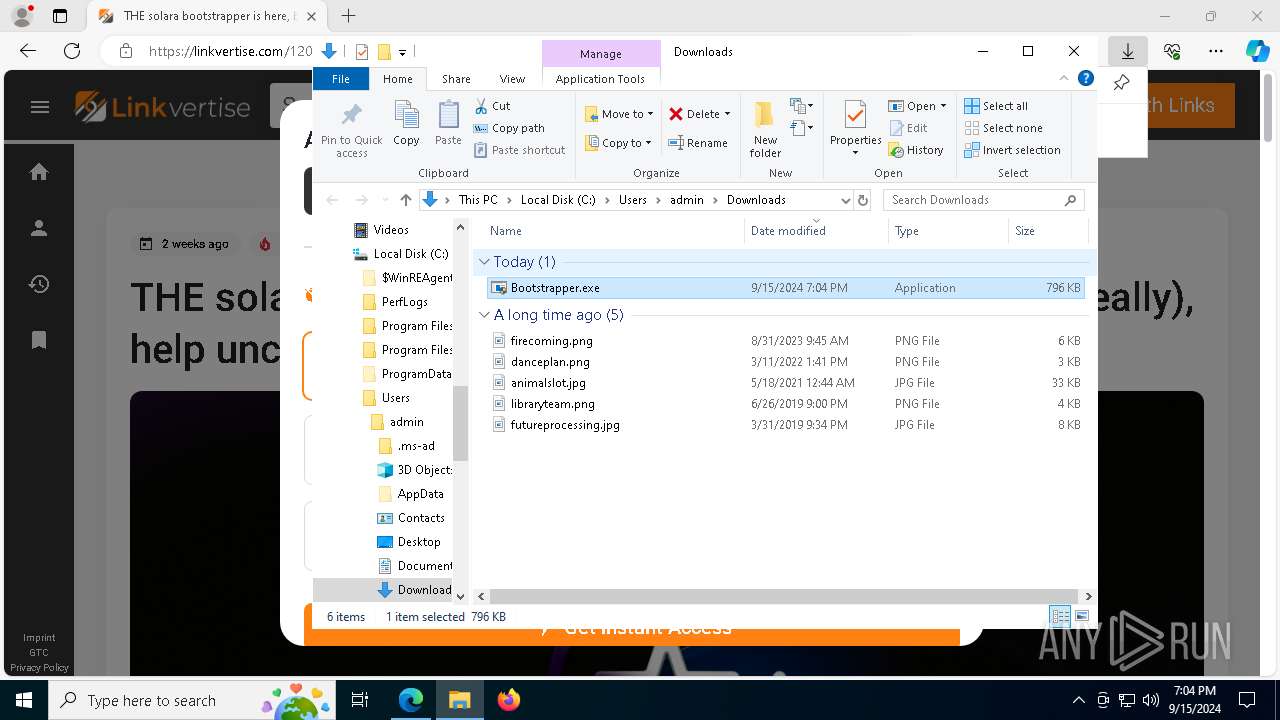
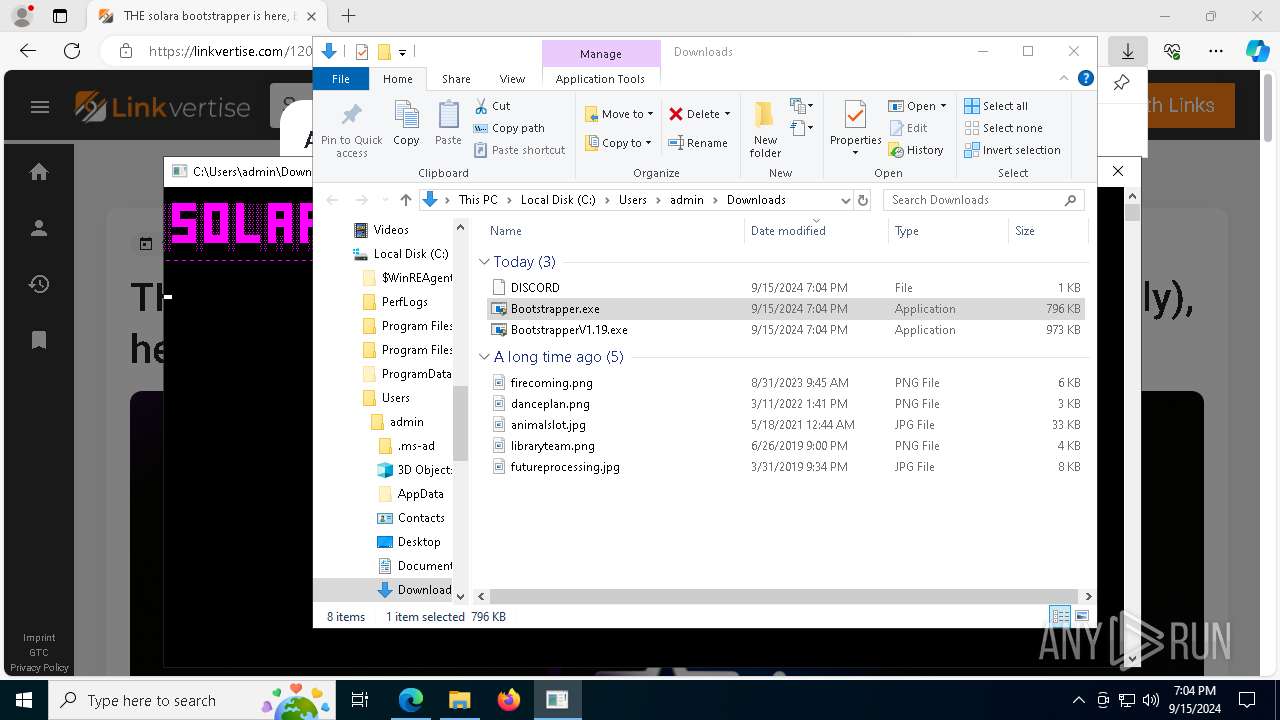
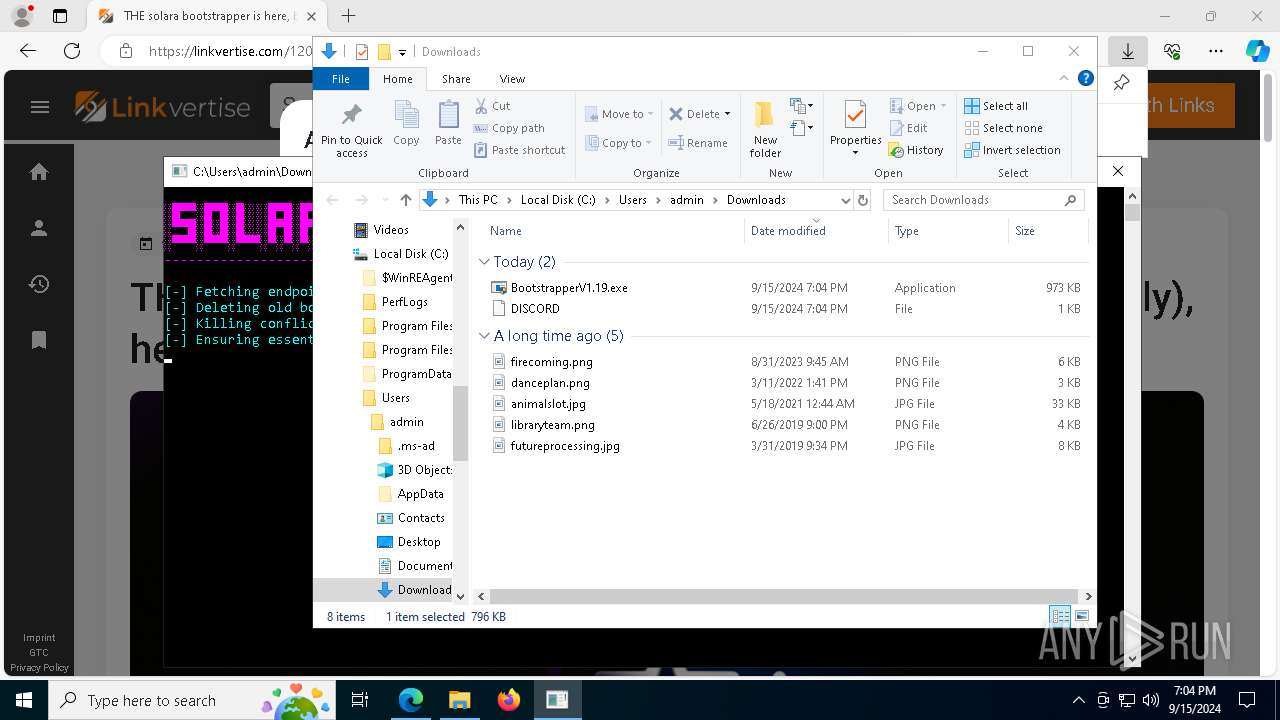
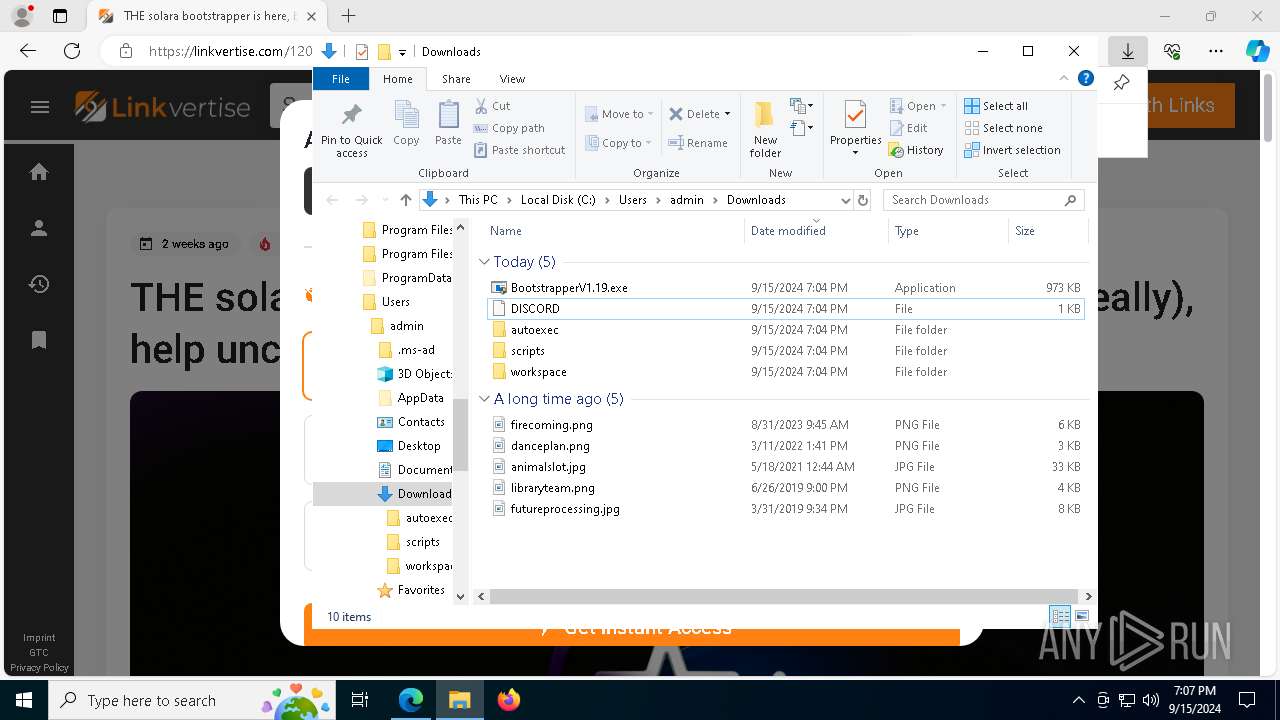
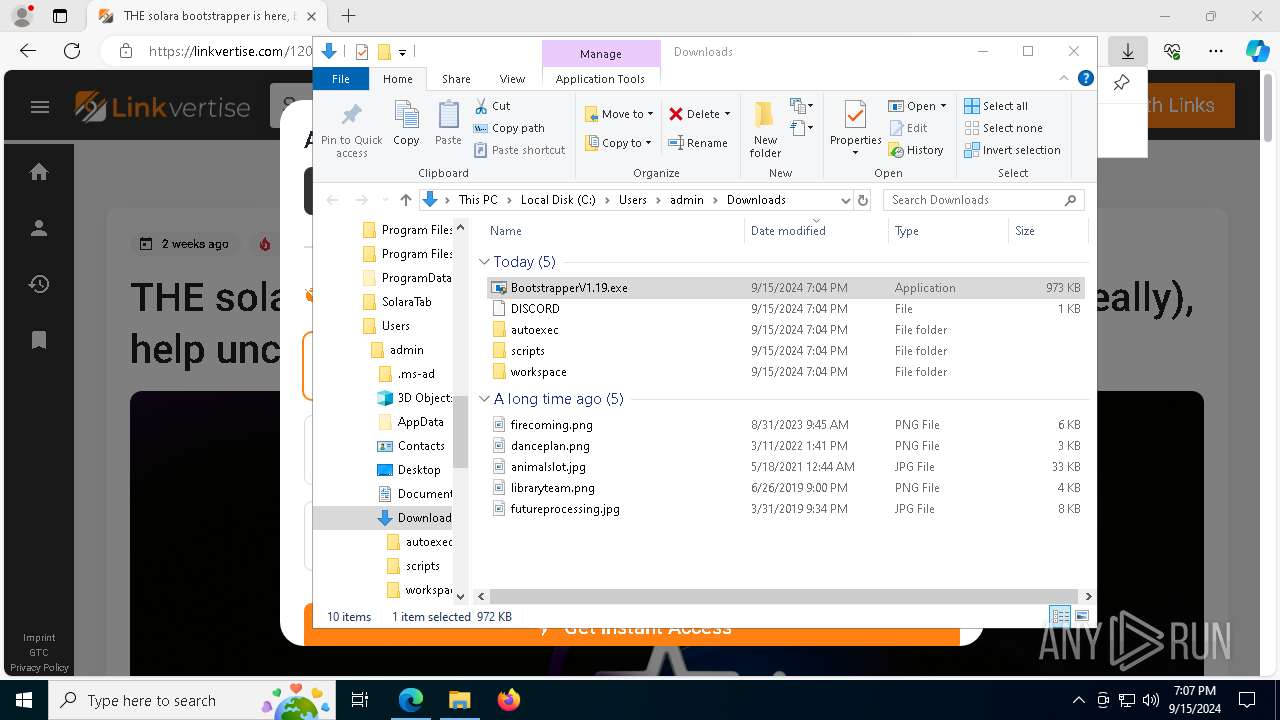
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
Reads security settings of Internet Explorer
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 7820)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Checks Windows Trust Settings
- msiexec.exe (PID: 6156)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 6156)
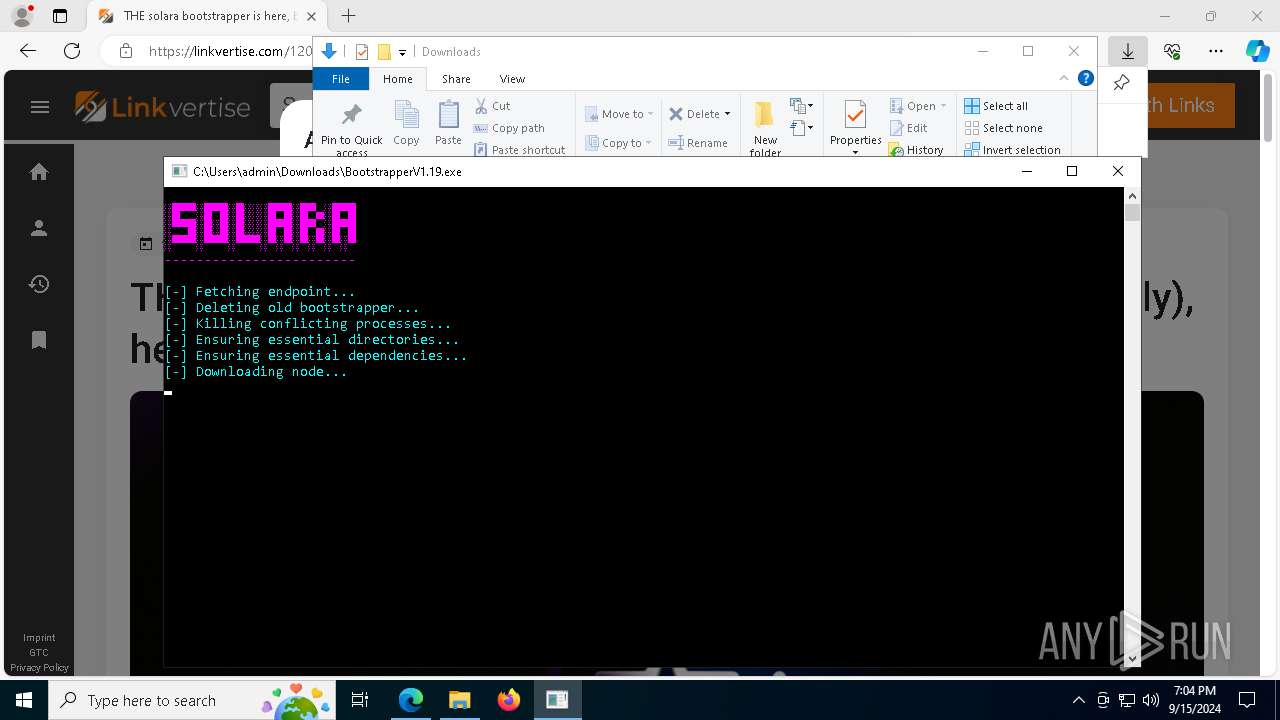
Uses WEVTUTIL.EXE to install publishers and event logs from the manifest
- msiexec.exe (PID: 7820)
- wevtutil.exe (PID: 4024)
Executes script using NodeJS
- node.exe (PID: 3116)
Reads the BIOS version
- Solara.exe (PID: 5796)
INFO
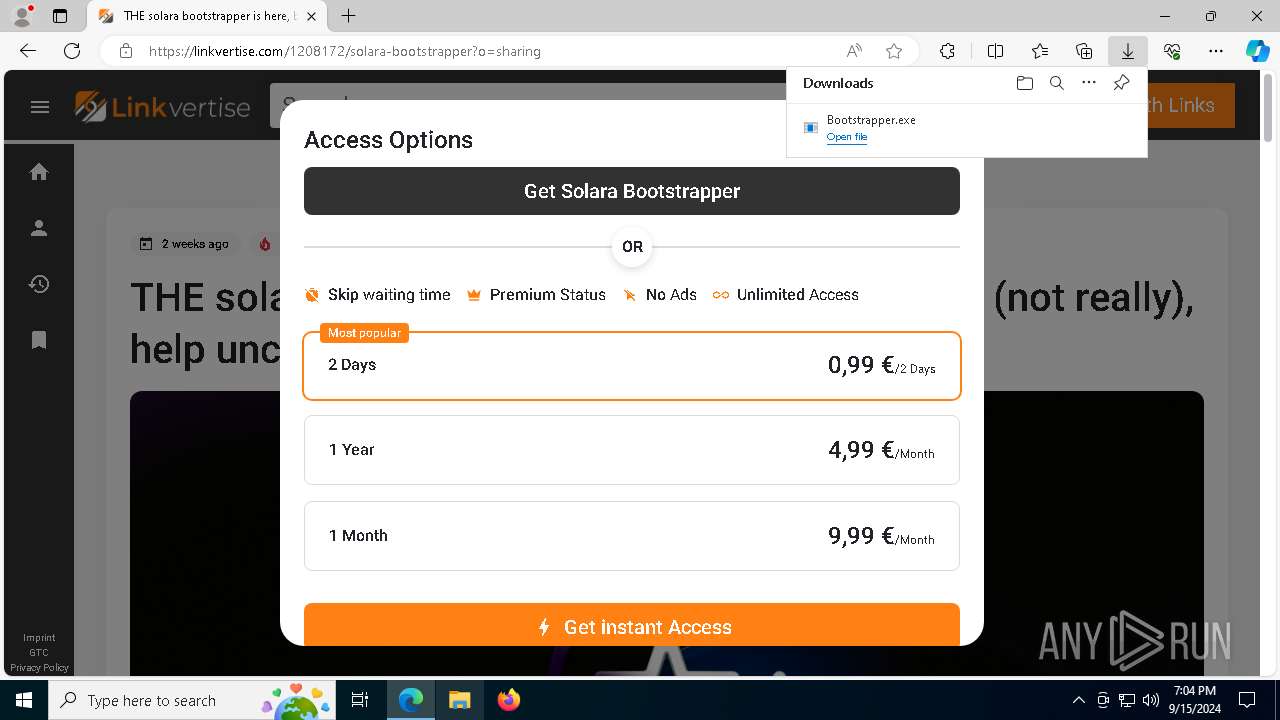
The process uses the downloaded file
- msedge.exe (PID: 7940)
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- BootstrapperV1.19.exe (PID: 7596)
Executable content was dropped or overwritten
- msedge.exe (PID: 6188)
- msedge.exe (PID: 5164)
- msiexec.exe (PID: 6156)
- msedge.exe (PID: 6264)
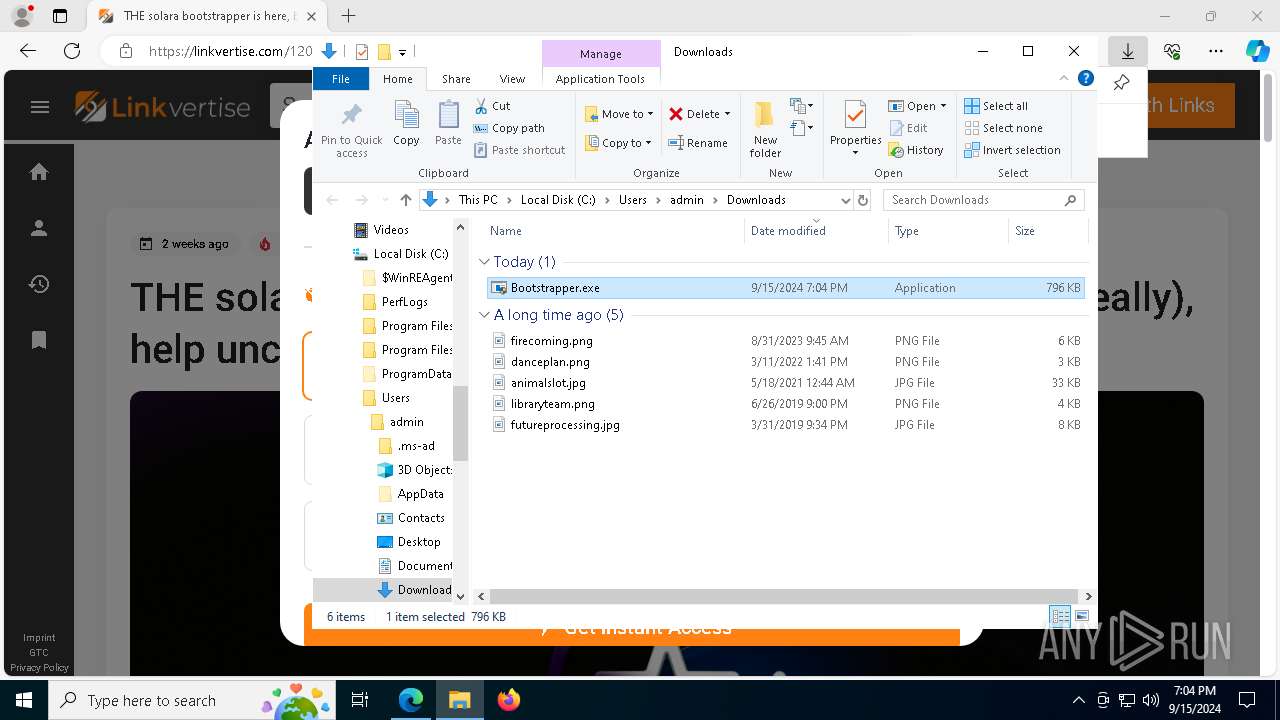
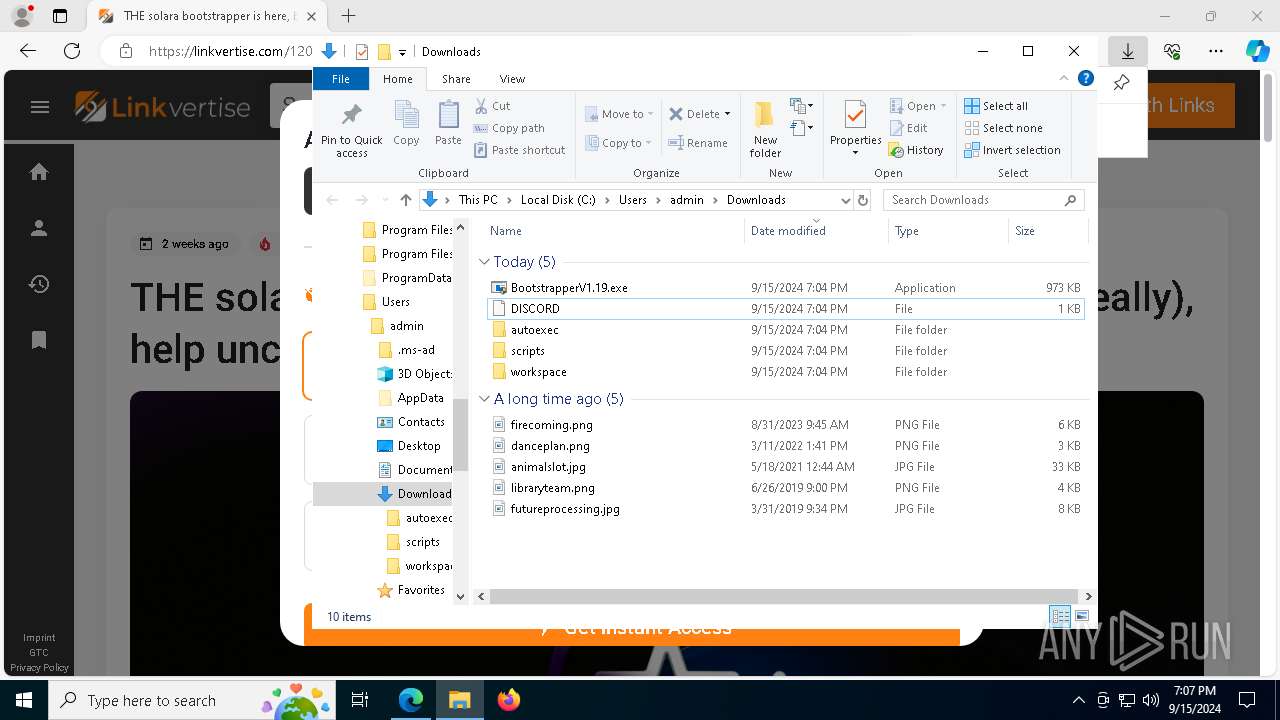
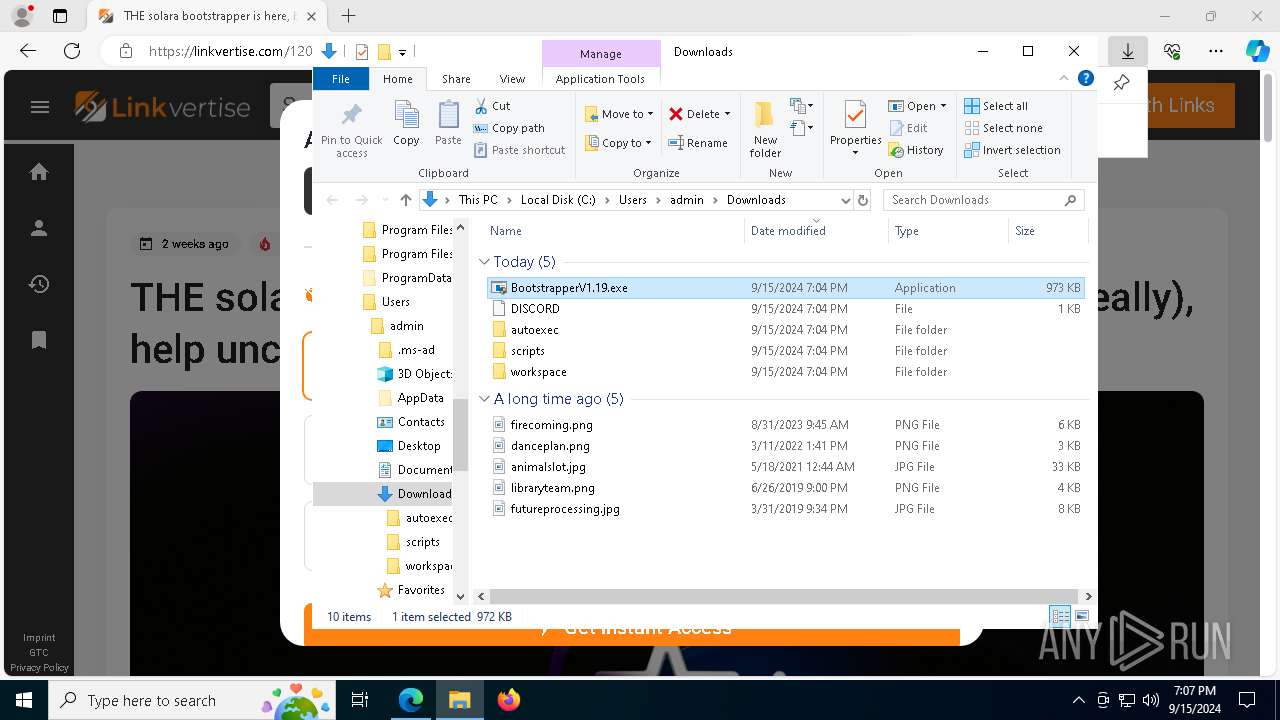
Manual execution by a user
- Bootstrapper.exe (PID: 6988)
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 7596)
- BootstrapperV1.19.exe (PID: 6784)
Checks supported languages
- Bootstrapper.exe (PID: 4316)
- msiexec.exe (PID: 6156)
- BootstrapperV1.19.exe (PID: 4440)
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 7820)
- BootstrapperV1.19.exe (PID: 7596)
- node.exe (PID: 6412)
- Solara.exe (PID: 5796)
- node.exe (PID: 3116)
Reads the computer name
- Bootstrapper.exe (PID: 4316)
- msiexec.exe (PID: 6156)
- BootstrapperV1.19.exe (PID: 4440)
- msiexec.exe (PID: 6576)
- msiexec.exe (PID: 7064)
- msiexec.exe (PID: 7820)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Reads the machine GUID from the registry
- Bootstrapper.exe (PID: 4316)
- msiexec.exe (PID: 6156)
- BootstrapperV1.19.exe (PID: 4440)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Disables trace logs
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Reads Environment values
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Checks proxy server information
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- slui.exe (PID: 8128)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Application launched itself
- msedge.exe (PID: 6188)
- msiexec.exe (PID: 6156)
Reads the software policy settings
- Bootstrapper.exe (PID: 4316)
- msiexec.exe (PID: 6156)
- BootstrapperV1.19.exe (PID: 4440)
- slui.exe (PID: 4672)
- slui.exe (PID: 8128)
- BootstrapperV1.19.exe (PID: 7596)
- Solara.exe (PID: 5796)
Process checks computer location settings
- Bootstrapper.exe (PID: 4316)
- BootstrapperV1.19.exe (PID: 4440)
- BootstrapperV1.19.exe (PID: 7596)
Creates files or folders in the user directory
- msiexec.exe (PID: 6156)
Create files in a temporary directory
- BootstrapperV1.19.exe (PID: 4440)
Creates files in the program directory
- BootstrapperV1.19.exe (PID: 4440)
Creates a software uninstall entry
- msiexec.exe (PID: 6156)
Process checks whether UAC notifications are on
- Solara.exe (PID: 5796)
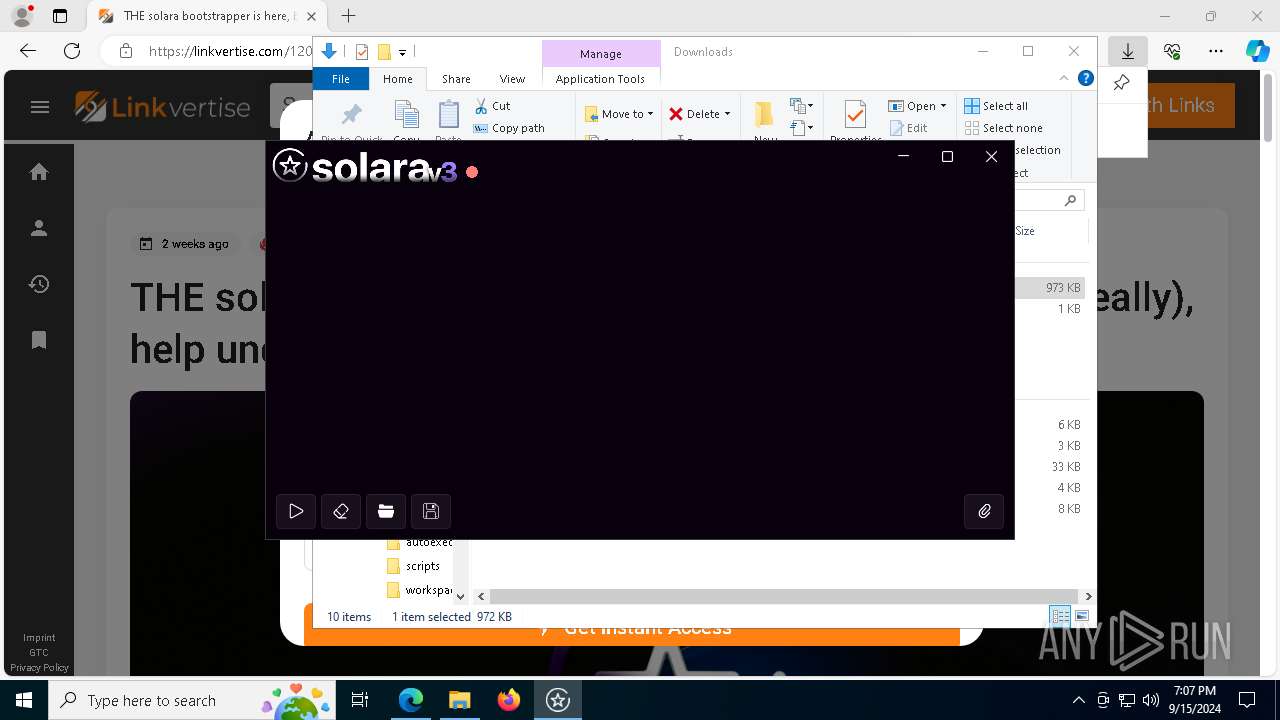
Themida protector has been detected
- Solara.exe (PID: 5796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
209
Monitored processes
73
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3356 --field-trial-handle=2520,i,11235857009141435499,17758533126844351449,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 752 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x300,0x2f8,0x7fffd2885fd8,0x7fffd2885fe4,0x7fffd2885ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1064 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=price_comparison_service.mojom.DataProcessor --lang=en-US --service-sandbox-type=entity_extraction --no-appcompat-clear --mojo-platform-channel-handle=4616 --field-trial-handle=2520,i,11235857009141435499,17758533126844351449,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1084 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --no-appcompat-clear --mojo-platform-channel-handle=6860 --field-trial-handle=2520,i,11235857009141435499,17758533126844351449,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1812 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\node-v18.16.0-x64.msi" /qn | C:\Windows\System32\msiexec.exe | — | BootstrapperV1.19.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2256 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | node.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2584 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=3652 --field-trial-handle=2520,i,11235857009141435499,17758533126844351449,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2816 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=6352 --field-trial-handle=2520,i,11235857009141435499,17758533126844351449,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
22 167
Read events
19 187
Write events
2 972
Delete events
8
Modification events
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 55218D65C3802F00 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F80B9465C3802F00 | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525104 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E59EA53D-CF8C-4E1C-A2BA-D4E98EB140FD} | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525104 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2334D0FC-2B29-4C11-83EB-30618191F18E} | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525104 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D7A65901-6248-4A9B-BC77-06EA0C71C750} | |||
| (PID) Process: | (6188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\525104 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3823C165-7867-4838-9871-9C253B7CA91C} | |||
Executable files
44
Suspicious files
1 375
Text files
1 730
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF12a05f.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF12a05f.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF12a06e.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF12a0ad.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF12a0ad.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF12a06e.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
205
DNS requests
230
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6616 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d027e63e-31f9-4887-9ef0-9bc042390907?P1=1726923946&P2=404&P3=2&P4=Y06xeqsT1G%2ffyCMkwbaOFeOQlx4QbVs6v%2fUhE66tbA3igSjK1U%2flkopg0eQtrNyxXvkqPMh%2fjlecMQpTjf0cnw%3d%3d | DE | binary | 4.31 Kb | whitelisted |
6616 | svchost.exe | GET | 200 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a1310cb6-94be-46c6-b8dc-986450234260?P1=1726551334&P2=404&P3=2&P4=BRpRZVyJMXWh7f82BhmK%2bv%2bCKTa9ukLx4VWNdMkpNPogsgQ8OM9igtWHP8P7FoE9qhpqqpcEQ0yHMFgeGHuELA%3d%3d | DE | binary | 14.8 Kb | whitelisted |
6616 | svchost.exe | HEAD | 200 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726991226&P2=404&P3=2&P4=RN6OsDOc6XvBccEB7t6h2ubGyi1JPDIIsZBmoMHeRoC2Ek2QAcp4Y505BABmDZrIz5fSJCmGAQTTiLQTtm7W2Q%3d%3d | DE | binary | 14.8 Kb | whitelisted |
6616 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726991226&P2=404&P3=2&P4=RN6OsDOc6XvBccEB7t6h2ubGyi1JPDIIsZBmoMHeRoC2Ek2QAcp4Y505BABmDZrIz5fSJCmGAQTTiLQTtm7W2Q%3d%3d | DE | binary | 41.3 Kb | whitelisted |
6616 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726991226&P2=404&P3=2&P4=RN6OsDOc6XvBccEB7t6h2ubGyi1JPDIIsZBmoMHeRoC2Ek2QAcp4Y505BABmDZrIz5fSJCmGAQTTiLQTtm7W2Q%3d%3d | DE | binary | 25.6 Kb | whitelisted |
6616 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726991226&P2=404&P3=2&P4=RN6OsDOc6XvBccEB7t6h2ubGyi1JPDIIsZBmoMHeRoC2Ek2QAcp4Y505BABmDZrIz5fSJCmGAQTTiLQTtm7W2Q%3d%3d | DE | binary | 35.1 Kb | whitelisted |
6616 | svchost.exe | GET | 206 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d2188a02-1d02-462f-bc1f-f8291a96a5c1?P1=1726991226&P2=404&P3=2&P4=RN6OsDOc6XvBccEB7t6h2ubGyi1JPDIIsZBmoMHeRoC2Ek2QAcp4Y505BABmDZrIz5fSJCmGAQTTiLQTtm7W2Q%3d%3d | DE | binary | 70.1 Kb | whitelisted |
6616 | svchost.exe | HEAD | 200 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/15d253df-7d48-4338-8759-fb2e882eb7ec?P1=1726772083&P2=404&P3=2&P4=gPS%2fRBtyRmFtXf2%2f9POjCiXNWlVyS2zFPFqSM8JNvMbttJK7ECSXXuwQHxiG%2bkWl%2fgn0Cw0%2b04QxbWHXwlMJow%3d%3d | DE | binary | 35.1 Kb | whitelisted |
1752 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6616 | svchost.exe | HEAD | 200 | 2.19.126.157:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/d027e63e-31f9-4887-9ef0-9bc042390907?P1=1726923946&P2=404&P3=2&P4=Y06xeqsT1G%2ffyCMkwbaOFeOQlx4QbVs6v%2fUhE66tbA3igSjK1U%2flkopg0eQtrNyxXvkqPMh%2fjlecMQpTjf0cnw%3d%3d | DE | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
608 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
892 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5164 | msedge.exe | 104.21.93.27:443 | getsolara.dev | — | — | malicious |
6188 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5164 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5164 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5164 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5164 | msedge.exe | 94.245.104.56:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
getsolara.dev |
| malicious |
edge.microsoft.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5164 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5164 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5164 | msedge.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
5164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5164 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5164 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5164 | msedge.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
5164 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (checkcdnjs) |