| File name: | aa6d2272617597069417744260e17ff7 |
| Full analysis: | https://app.any.run/tasks/65f2f51f-9b2e-4c12-a06a-5ad4a8ae3884 |
| Verdict: | Malicious activity |
| Analysis date: | August 30, 2019, 07:09:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AA6D2272617597069417744260E17FF7 |
| SHA1: | DB8163AB027D9D0AAB9CAF13B1D24CB647E755B3 |
| SHA256: | 9060F8F19D46A256FD2D67D8222956A3D6DF427CE77732E0136810DF0106A7A5 |
| SSDEEP: | 49152:v81BMu+VwGSrICIhST8tRb14k8pQd0xbZRFscvezu:DbGECWGWRj50xFLezu |
MALICIOUS
Changes internet zones settings
- aa6d2272617597069417744260e17ff7.exe (PID: 3004)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- aa6d2272617597069417744260e17ff7.exe (PID: 3004)
- iexplore.exe (PID: 3816)
Reads Internet Cache Settings
- rundll32.exe (PID: 2764)
- rundll32.exe (PID: 3568)
- rundll32.exe (PID: 4076)
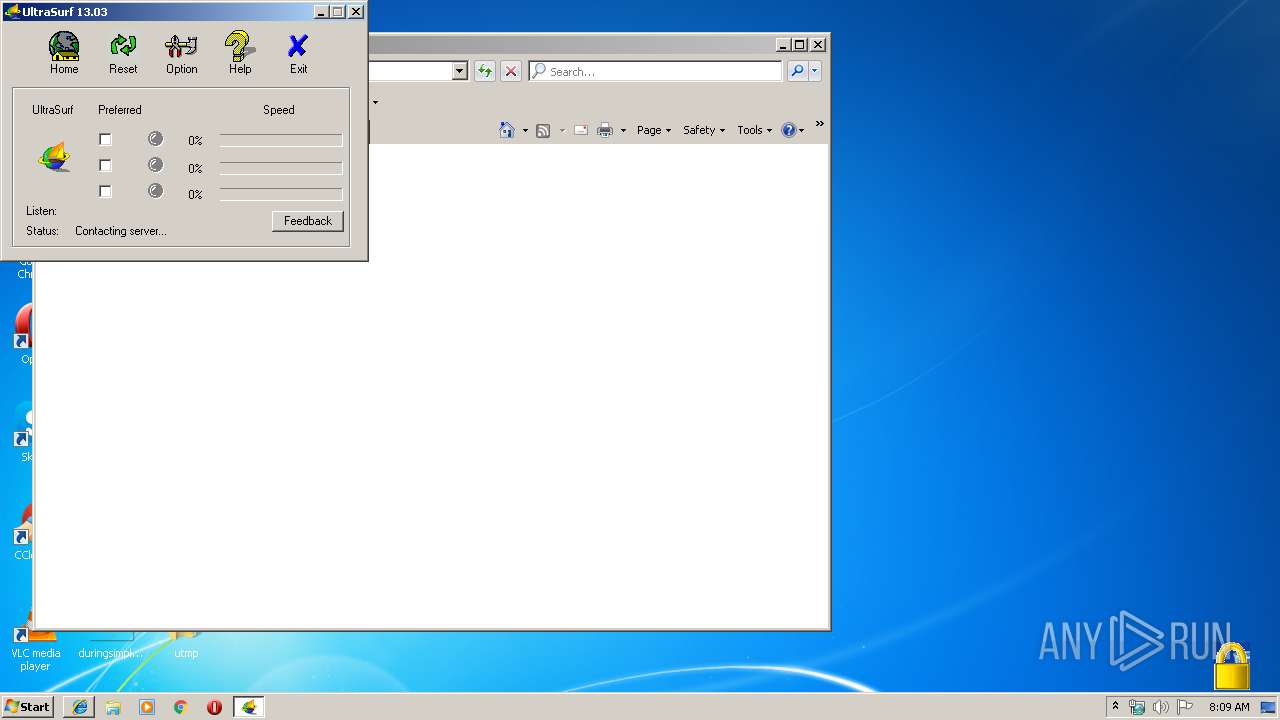
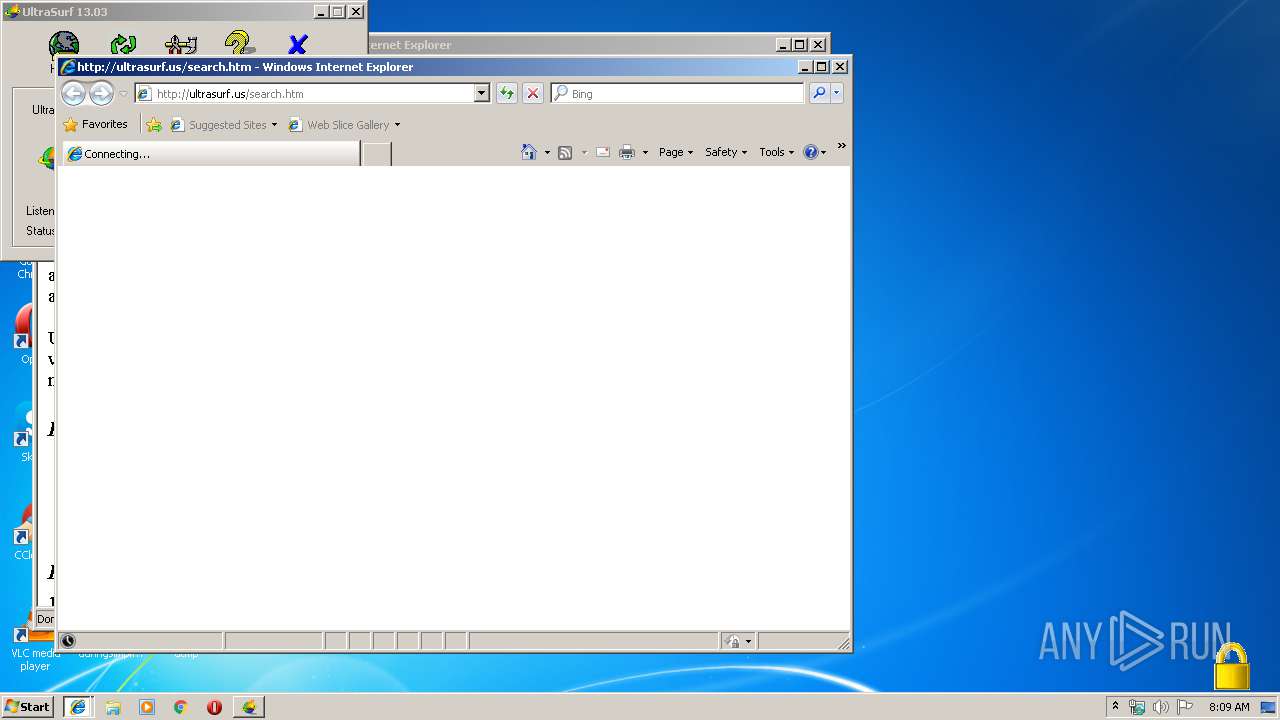
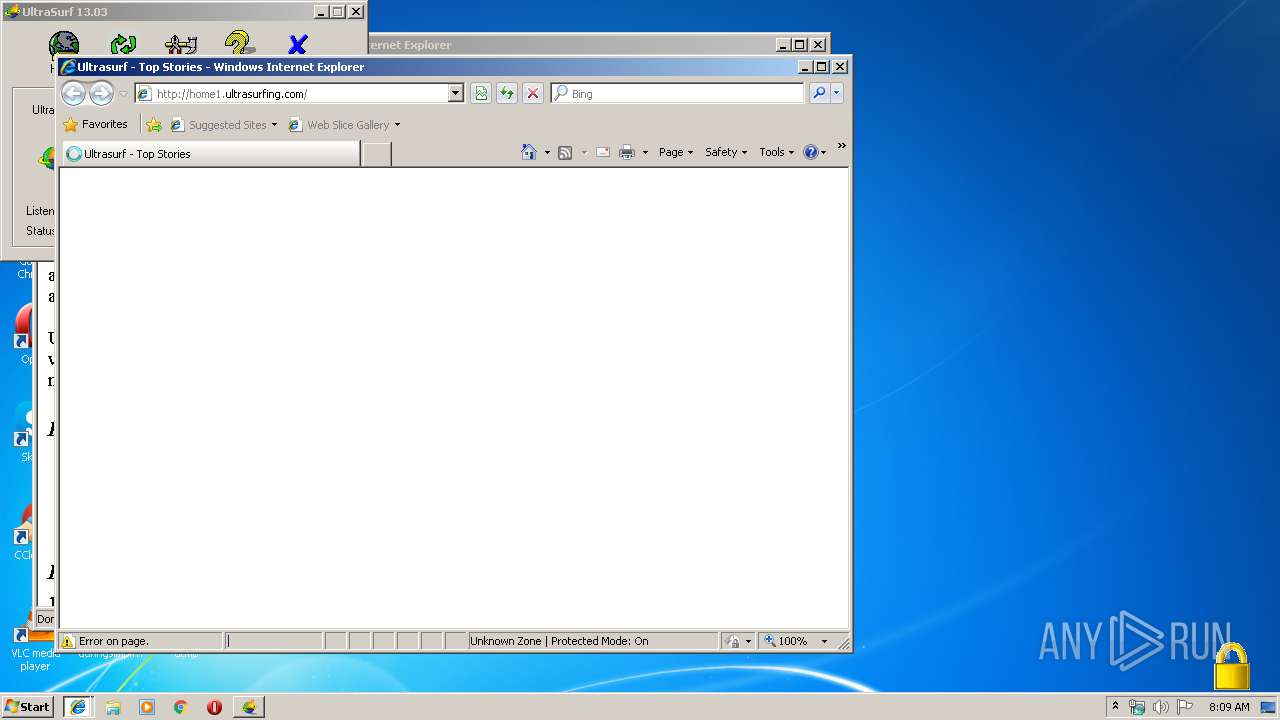
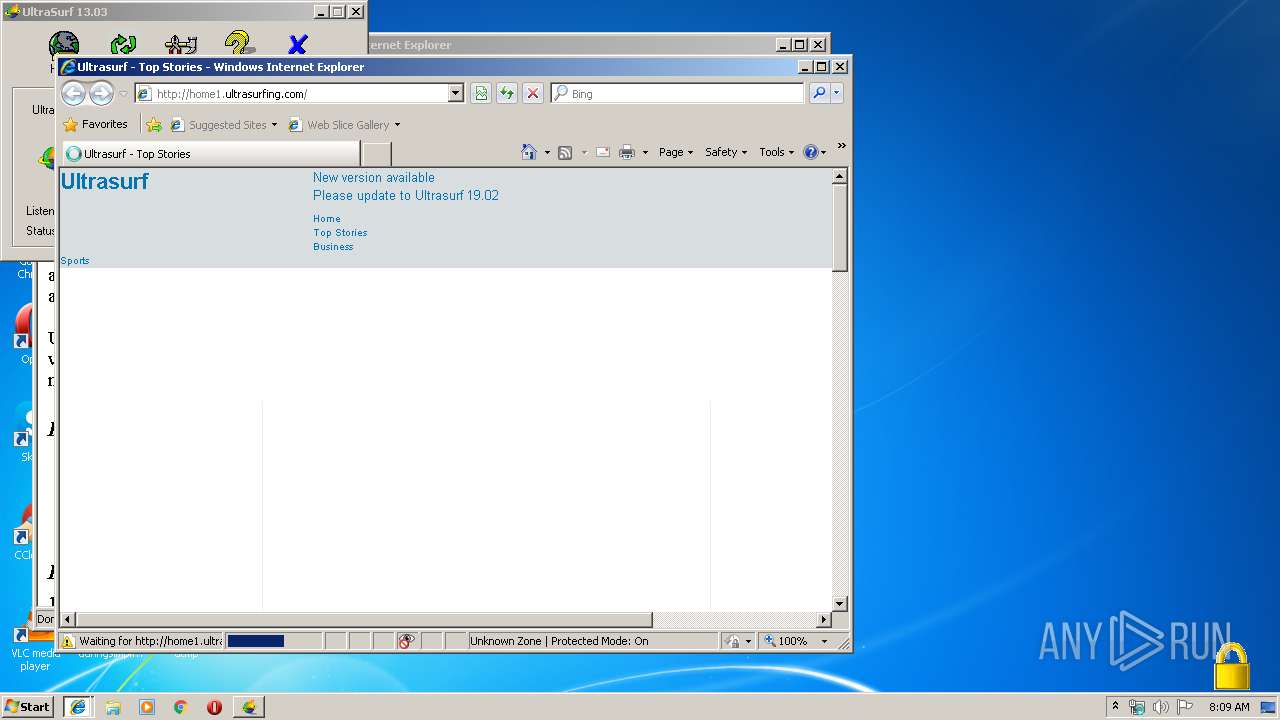
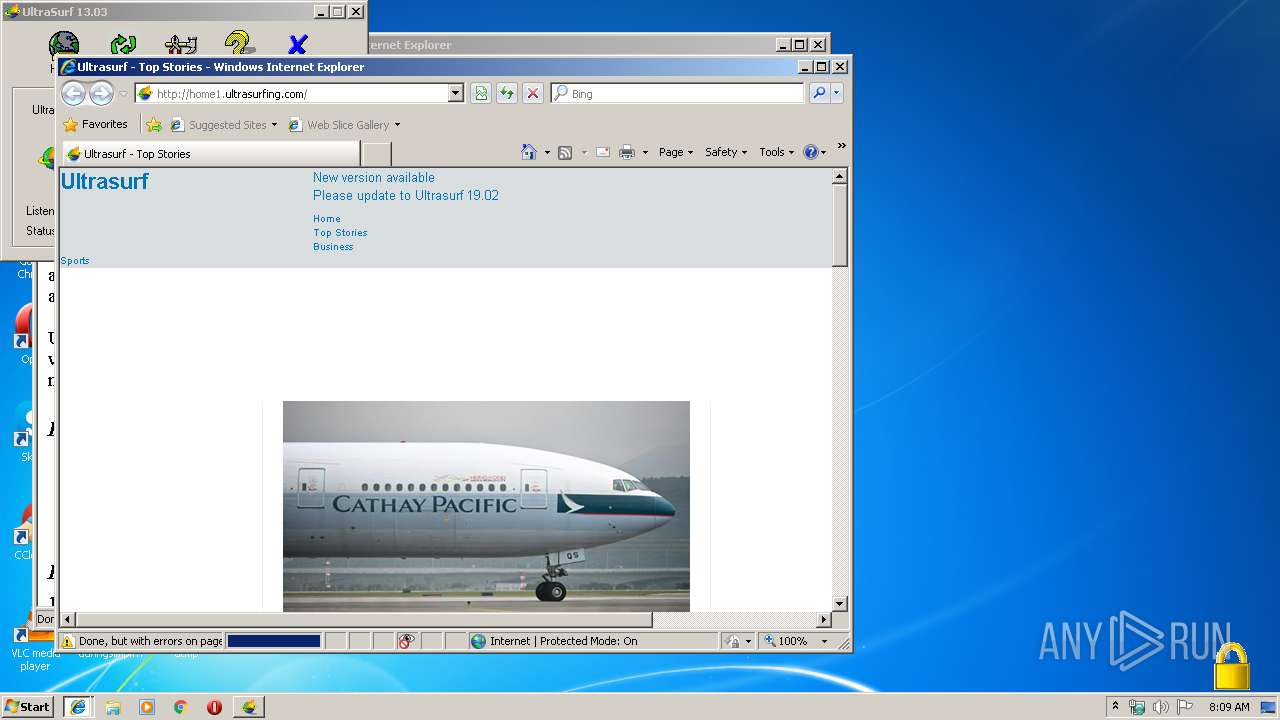
Starts Internet Explorer
- aa6d2272617597069417744260e17ff7.exe (PID: 3004)
INFO
Creates files in the user directory
- iexplore.exe (PID: 3816)
- iexplore.exe (PID: 1628)
Reads internet explorer settings
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 1628)
Changes internet zones settings
- iexplore.exe (PID: 3816)
Application launched itself
- iexplore.exe (PID: 3816)
Reads Internet Cache Settings
- iexplore.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:11:17 04:11:55+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 958464 |
| InitializedDataSize: | 5292032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x81a000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Nov-2013 03:11:55 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 17-Nov-2013 03:11:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
0x00001000 | 0x005E6000 | 0x00108000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.97406 | |
.rsrc | 0x005E7000 | 0x0000F880 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.27931 |
.idata | 0x005F7000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.219778 |
0x005F8000 | 0x0014B000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0421692 | |
lynhwtzr | 0x00743000 | 0x000D7000 | 0x000D7000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89697 |
xwchxswi | 0x0081A000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.623453 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.85369 | 192 | UNKNOWN | Chinese - PRC | RT_STRING |
2 | 7.43755 | 538 | UNKNOWN | Chinese - PRC | RT_STRING |
3 | 2.64201 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.00118 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 2.03845 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 1.9542 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.10419 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.46564 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.66074 | 3240 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 3.43329 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
comctl32.dll |
kernel32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_EXECryptor_GetHardwareID@0 | 1 | 0x0000E5C0 |
_EXECryptor_IsAppProtected@0 | 2 | 0x0000E5A0 |
Total processes
42
Monitored processes
8
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1628 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3816 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3816 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2764 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | aa6d2272617597069417744260e17ff7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3004 | "C:\Users\admin\Desktop\aa6d2272617597069417744260e17ff7.exe" | C:\Users\admin\Desktop\aa6d2272617597069417744260e17ff7.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3568 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | aa6d2272617597069417744260e17ff7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3596 | "C:\Program Files\Internet Explorer\iexplore.exe" http://ultrasurf.us/search.htm | C:\Program Files\Internet Explorer\iexplore.exe | — | aa6d2272617597069417744260e17ff7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
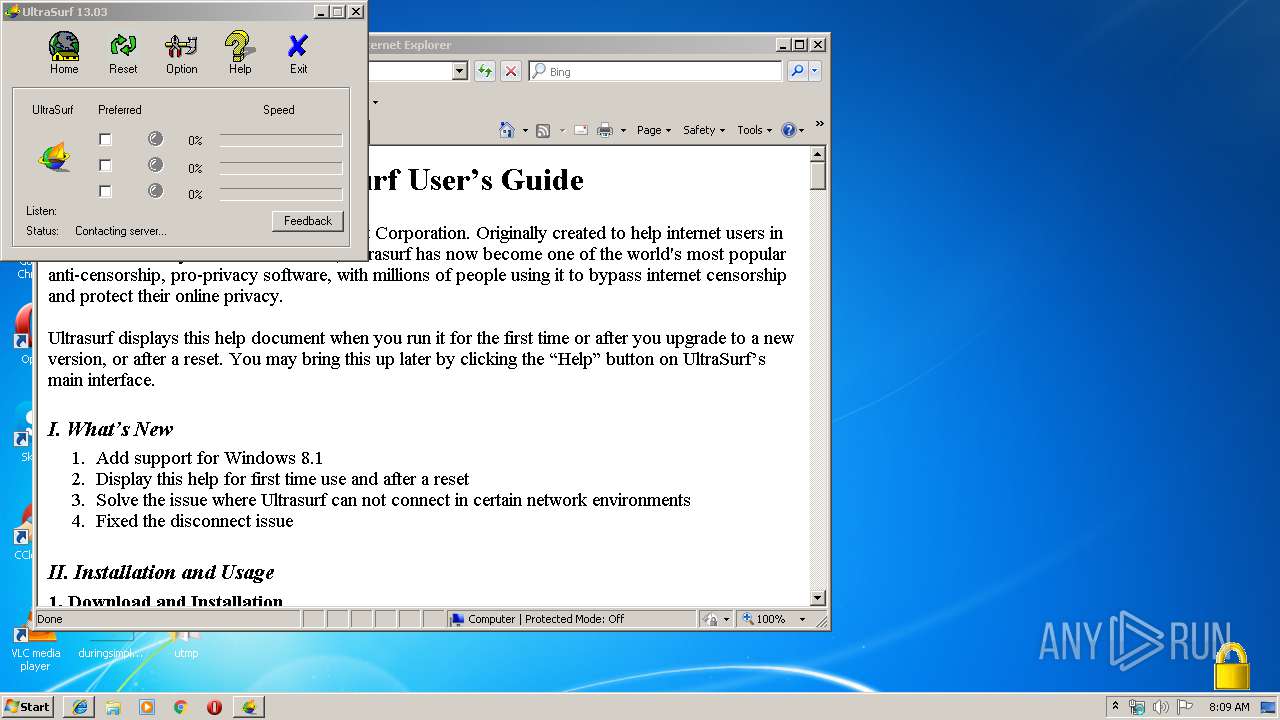
| 3816 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\utmp\help.htm | C:\Program Files\Internet Explorer\iexplore.exe | aa6d2272617597069417744260e17ff7.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4076 | "C:\Windows\system32\rundll32.exe" "C:\Windows\system32\WININET.dll",DispatchAPICall 1 | C:\Windows\system32\rundll32.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
665
Read events
512
Write events
151
Delete events
2
Modification events
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3004) aa6d2272617597069417744260e17ff7.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\aa6d2272617597069417744260e17ff7_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
13
Text files
31
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3816 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3816 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\8F0GNN98\home1_ultrasurfing_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 3004 | aa6d2272617597069417744260e17ff7.exe | C:\Users\admin\Desktop\utmp\~jxgwifinn5g1t6o | binary | |
MD5:— | SHA256:— | |||
| 3004 | aa6d2272617597069417744260e17ff7.exe | C:\Users\admin\Desktop\utmp\~hsmcoljtt9z9u2f | binary | |
MD5:— | SHA256:— | |||
| 3568 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3004 | aa6d2272617597069417744260e17ff7.exe | C:\Users\admin\Desktop\utmp\~dtfxezwwb2e5p4p | binary | |
MD5:— | SHA256:— | |||
| 3568 | rundll32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OZ1I0CS3\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 1628 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 1628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\6YUOZ5CD\style3[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
8
DNS requests
5
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3004 | aa6d2272617597069417744260e17ff7.exe | 216.58.205.238:443 | appspot.com | Google Inc. | US | whitelisted |
3004 | aa6d2272617597069417744260e17ff7.exe | 172.217.22.110:443 | google.com | Google Inc. | US | whitelisted |
3004 | aa6d2272617597069417744260e17ff7.exe | 65.49.14.70:443 | — | Hurricane Electric, Inc. | US | suspicious |
3004 | aa6d2272617597069417744260e17ff7.exe | 65.49.14.159:443 | — | Hurricane Electric, Inc. | US | suspicious |
3004 | aa6d2272617597069417744260e17ff7.exe | 52.219.36.117:443 | s3-ap-southeast-1.amazonaws.com | Amazon.com, Inc. | SG | unknown |
3004 | aa6d2272617597069417744260e17ff7.exe | 52.216.110.173:443 | s3.amazonaws.com | Amazon.com, Inc. | US | shared |
3004 | aa6d2272617597069417744260e17ff7.exe | 216.58.207.68:80 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
appspot.com |
| whitelisted |
google.com |
| malicious |
s3-ap-southeast-1.amazonaws.com |
| shared |
s3.amazonaws.com |
| shared |
Threats
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
aa6d2272617597069417744260e17ff7.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|