| download: | tweak-ssd-v2-setup.exe |
| Full analysis: | https://app.any.run/tasks/47554602-f8e2-4510-908f-4ea3541a2b43 |
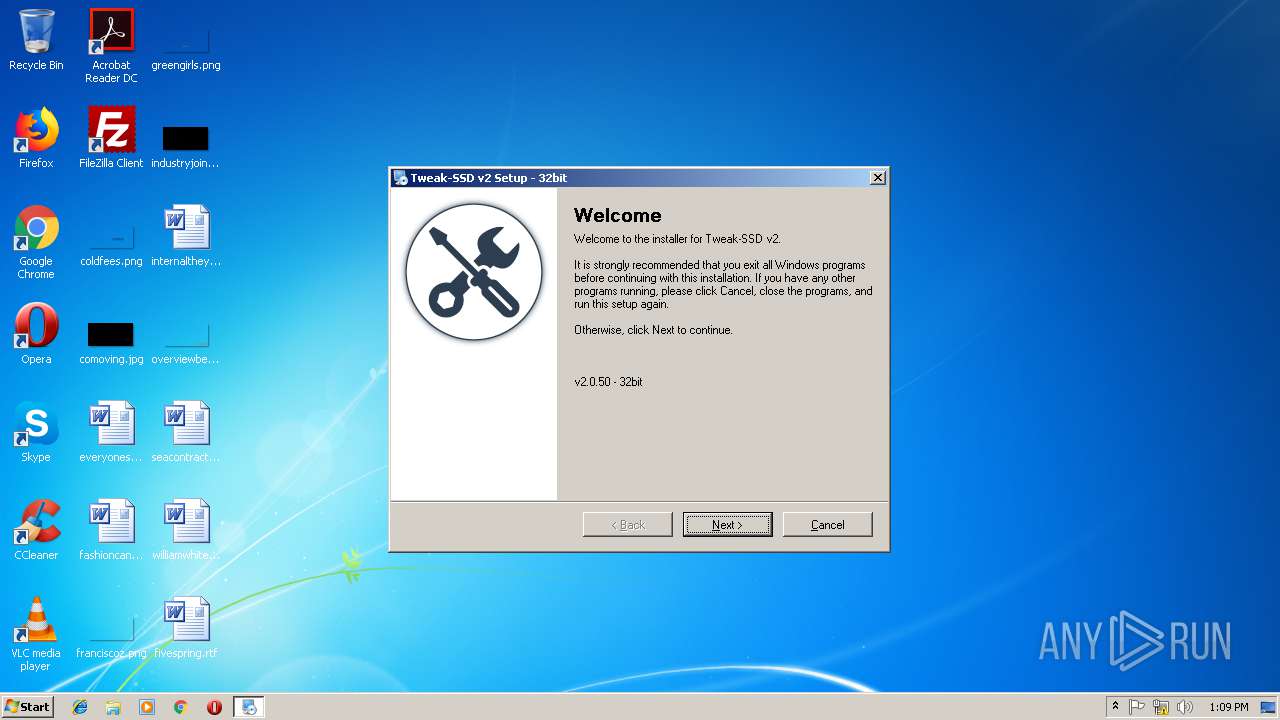
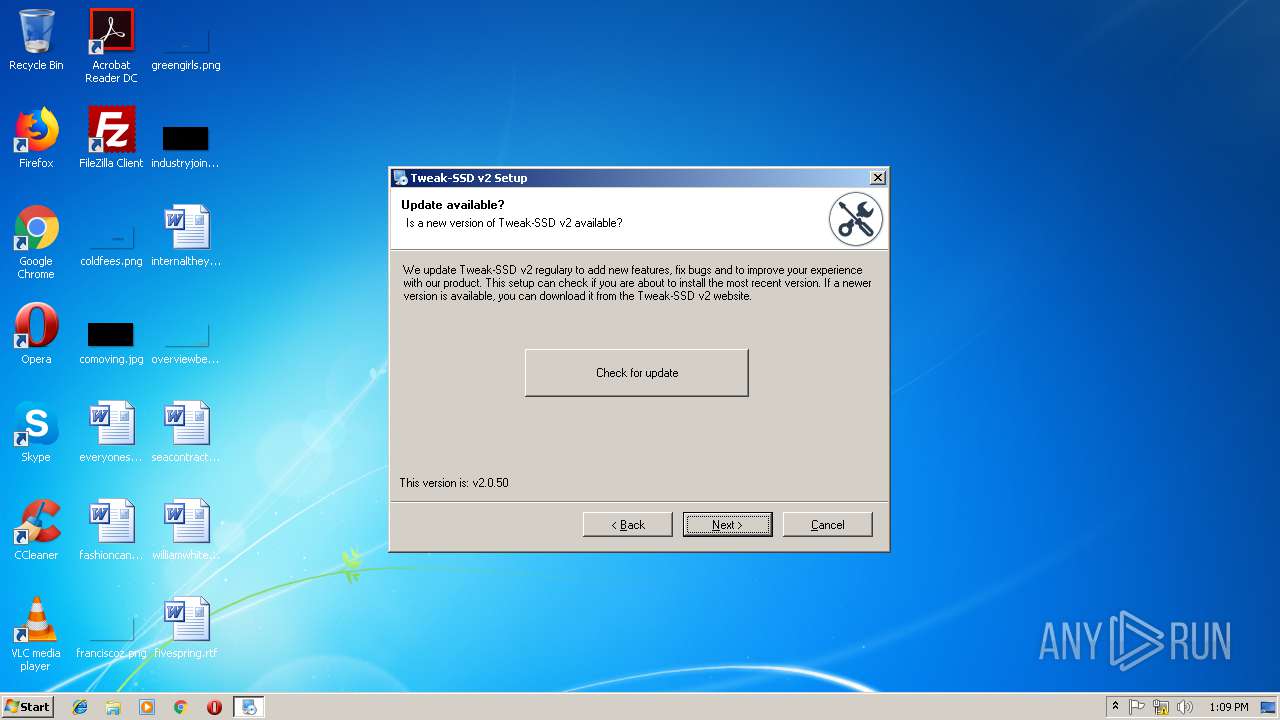
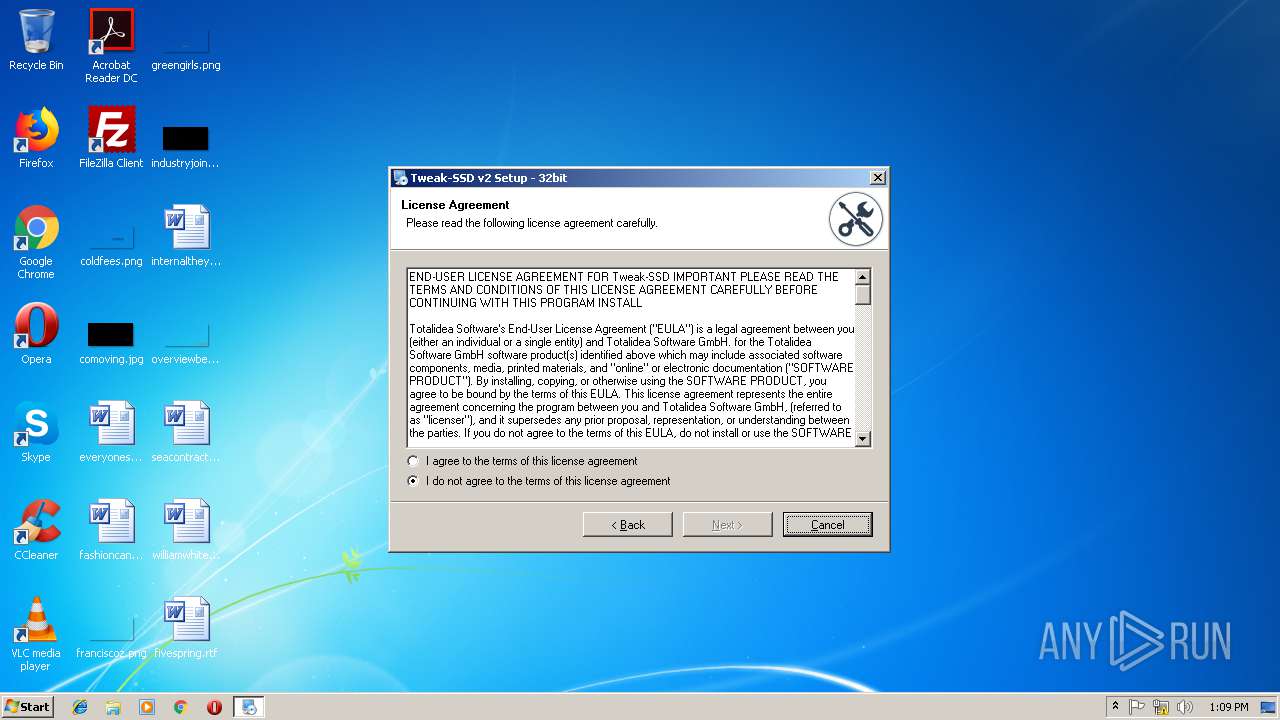
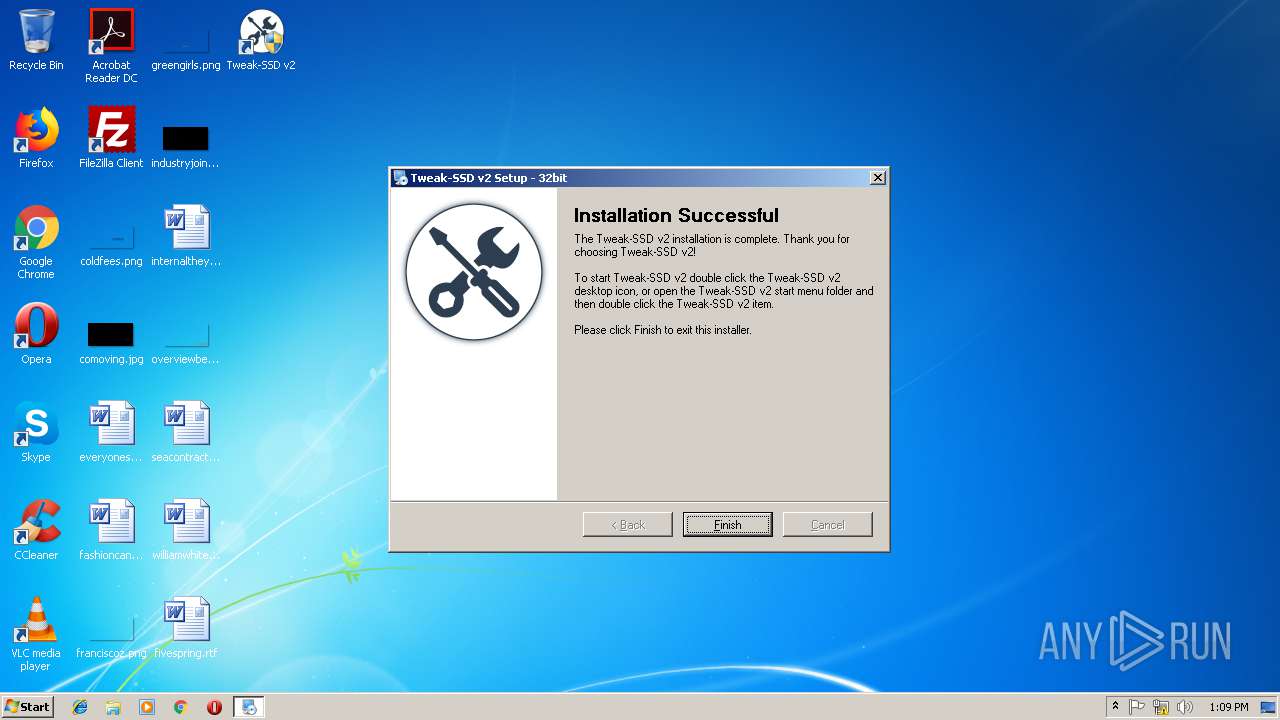
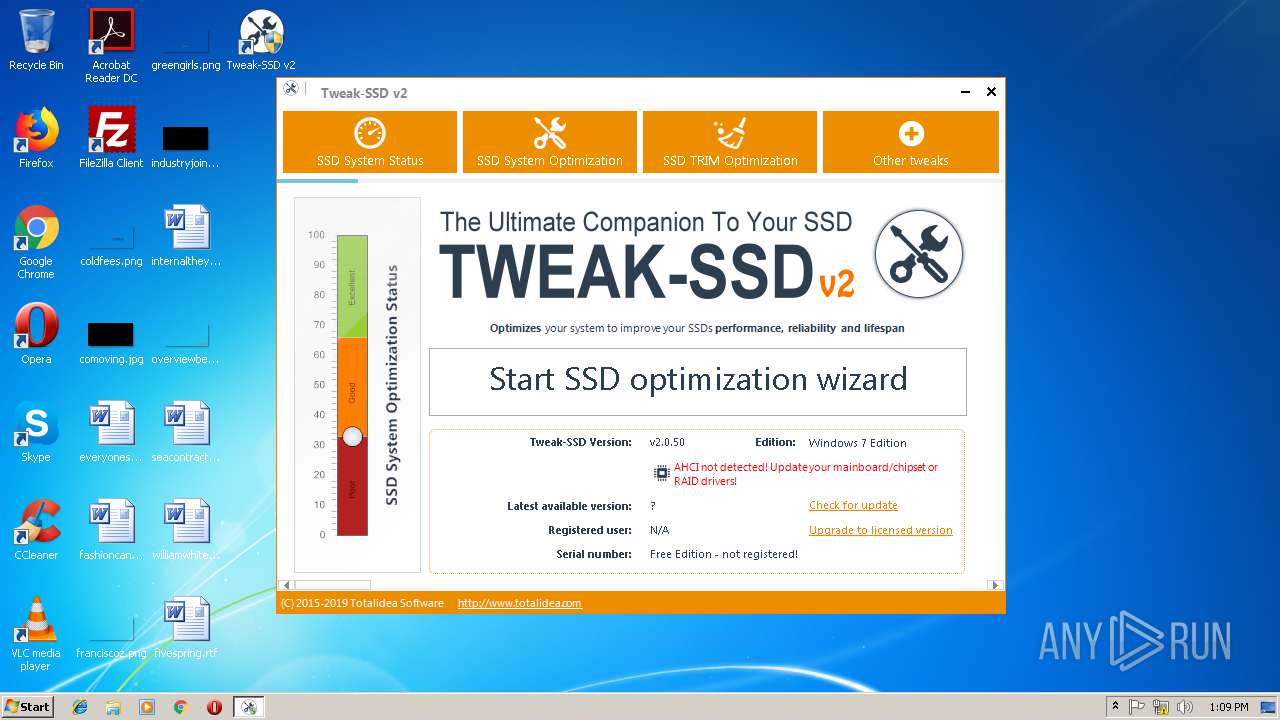
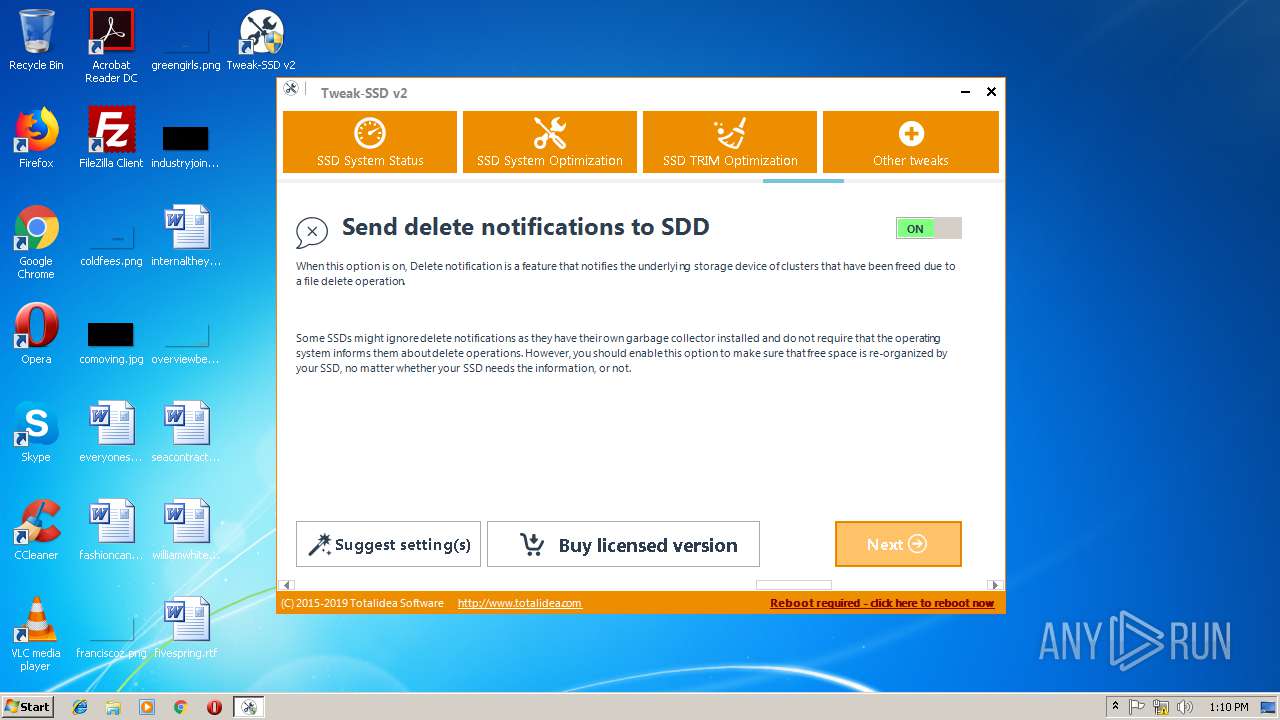
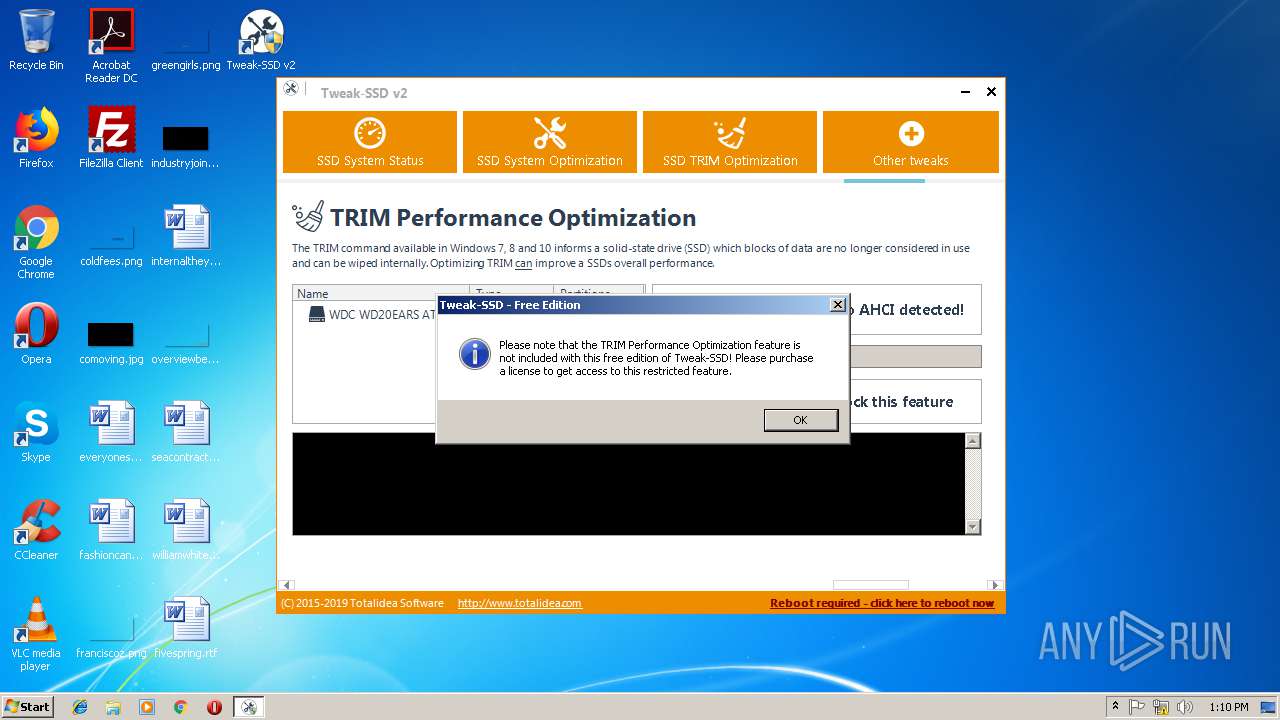
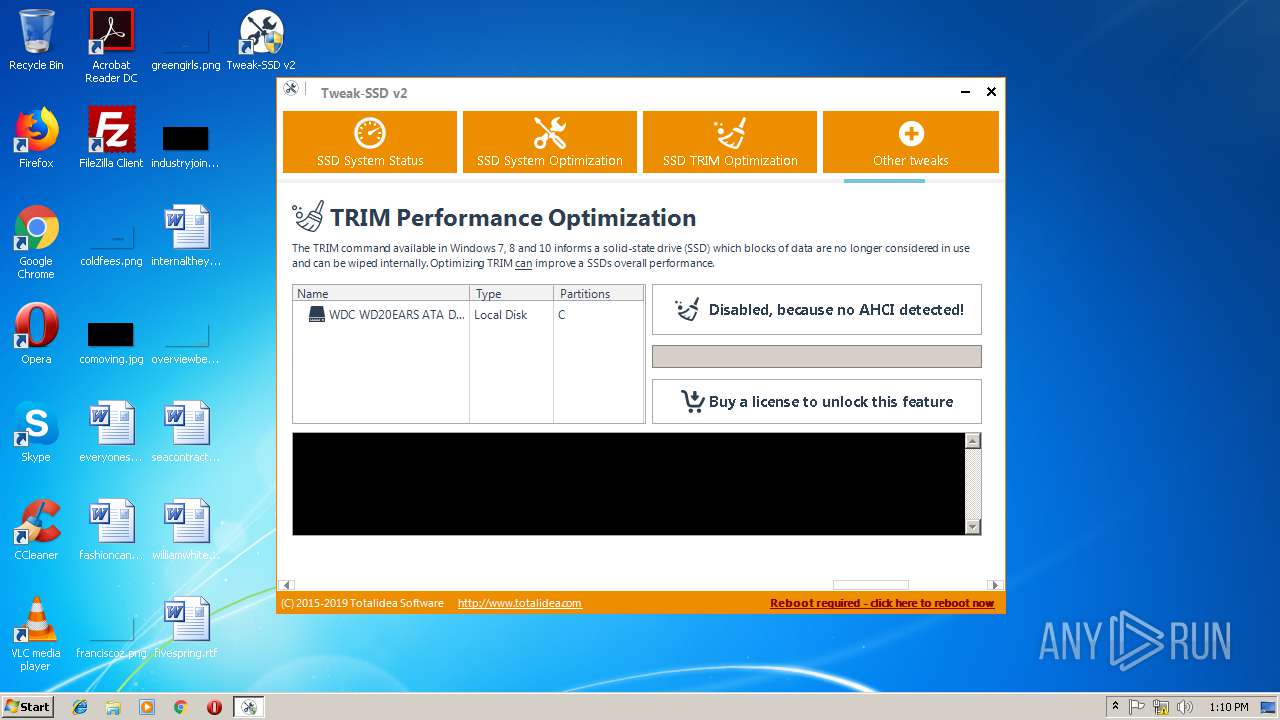
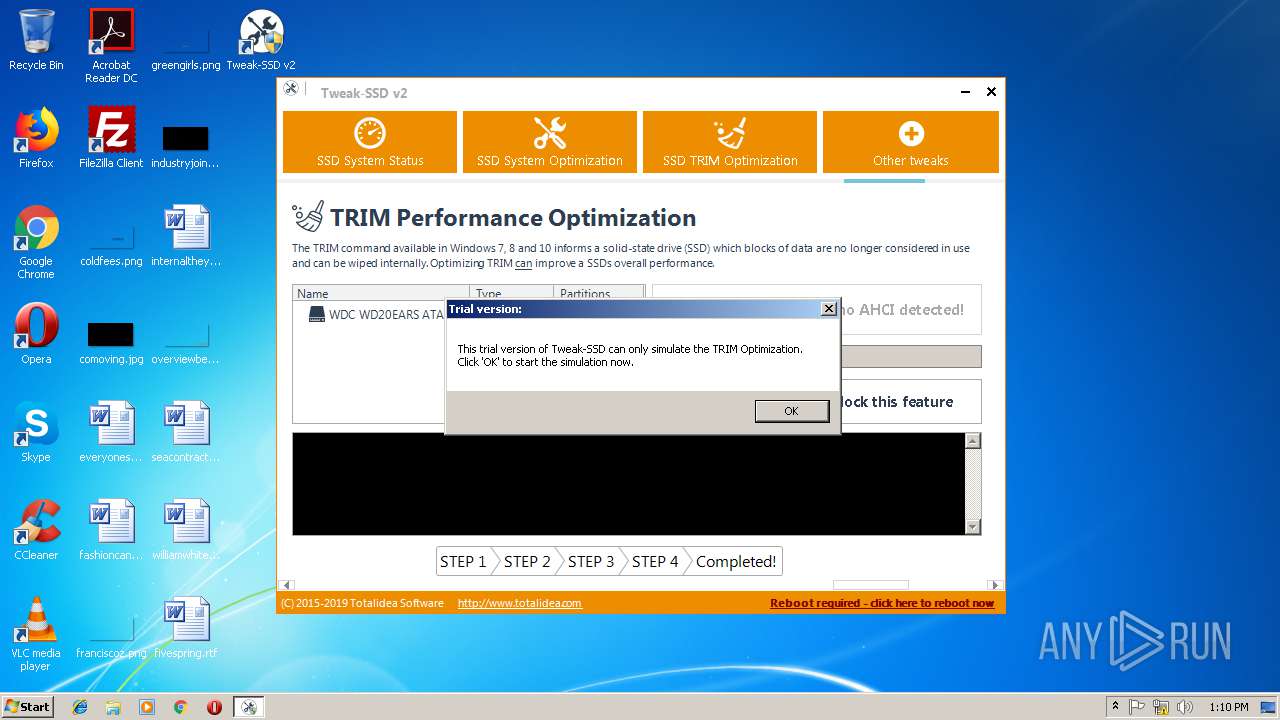
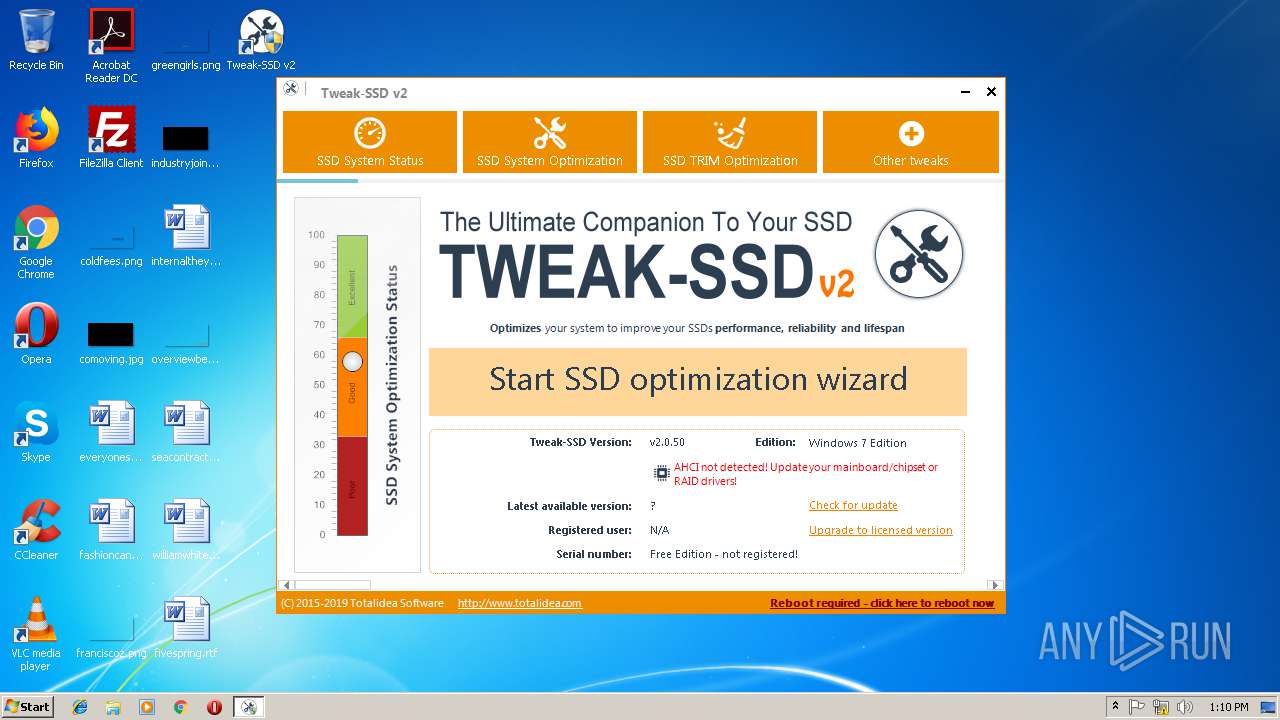
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2019, 13:08:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1FB76EAD3F3F34919DC4AED6943E7E05 |
| SHA1: | B580CCCD68DF278D9B8E4379433DBB39B8BD49D1 |
| SHA256: | 906018E7DE3E968230F1BB91DB59F1348631256B95DDCD5E5050AD34F92E22DB |
| SSDEEP: | 393216:tagyTDdOegqO0ySSvX5Zj7qmm8OdAfPbAgyeVBO+:taDVg3rfLjFgaPbzH7X |
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 3964)
- irsetup.exe (PID: 3076)
- Tweak-SSD.exe (PID: 3820)
- Tweak-SSD.exe (PID: 2436)
- tweak-ssd-x86.exe (PID: 2168)
Loads dropped or rewritten executable
- irsetup.exe (PID: 3076)
- irsetup.exe (PID: 3964)
SUSPICIOUS
Executable content was dropped or overwritten
- irsetup.exe (PID: 3964)
- tweak-ssd-v2-setup.exe (PID: 2052)
- tweak-ssd-x86.exe (PID: 2168)
- irsetup.exe (PID: 3076)
Creates files in the Windows directory
- irsetup.exe (PID: 3076)
Creates files in the program directory
- irsetup.exe (PID: 3076)
Creates a software uninstall entry
- irsetup.exe (PID: 3076)
Creates files in the user directory
- irsetup.exe (PID: 3076)
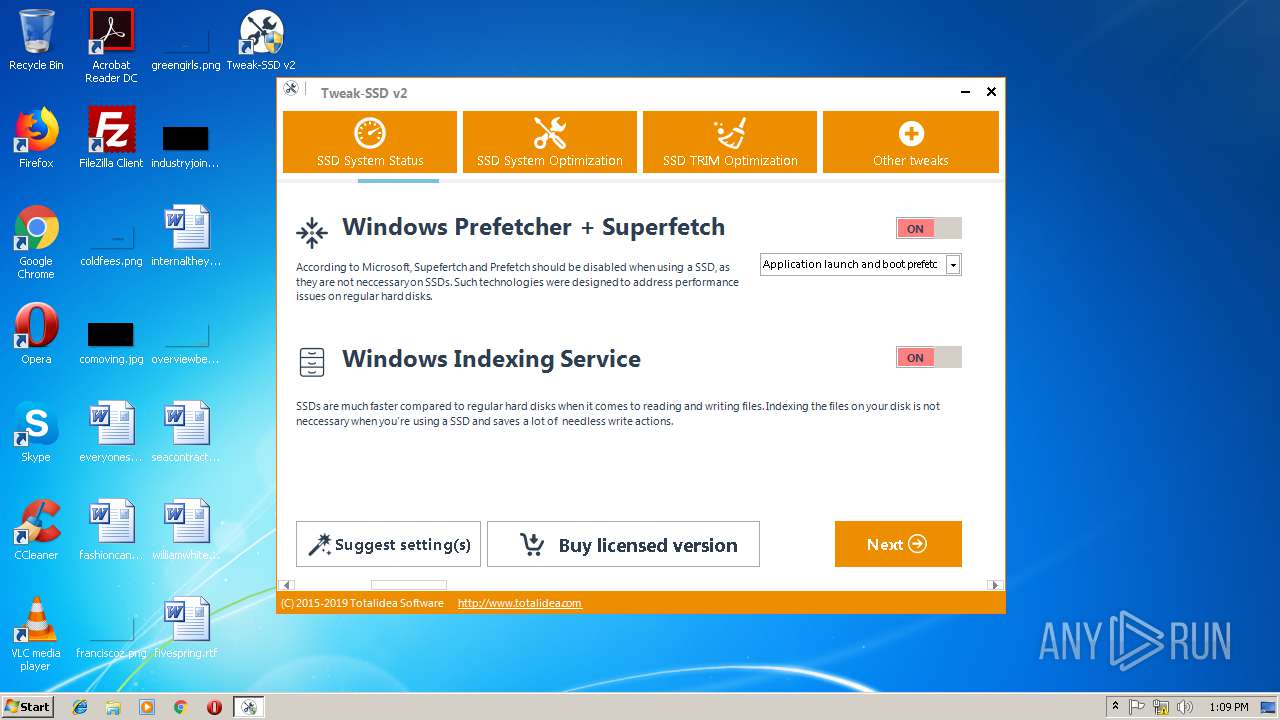
Creates or modifies windows services
- Tweak-SSD.exe (PID: 2436)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.8) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (36.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (9) |
| .exe | | | Win32 Executable (generic) (6.1) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:31 15:30:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 23552 |
| InitializedDataSize: | 48640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2ce1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.5.2.0 |
| ProductVersionNumber: | 9.5.2.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.5.2.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2018 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.5.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Jul-2018 13:30:07 |
| Detected languages: |
|
| Comments: | Created with Setup Factory |
| FileDescription: | Setup Application |
| FileVersion: | 9.5.2.0 |
| InternalName: | suf_launch |
| LegalCopyright: | Setup Engine Copyright © 2004-2018 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | suf_launch.exe |
| ProductName: | Setup Factory Runtime |
| ProductVersion: | 9.5.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Jul-2018 13:30:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A18 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.40733 |
.rdata | 0x00007000 | 0x00002F54 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.05968 |
.data | 0x0000A000 | 0x00001968 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.59807 |
.rsrc | 0x0000C000 | 0x00006E90 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.87362 |
.reloc | 0x00013000 | 0x000010D0 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.81847 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.3704 | 1425 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.31421 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.9477 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 3.78233 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.14953 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.83714 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 3.64397 | 1640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 5.84115 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.41049 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.89097 | 132 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
44
Monitored processes
7
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Users\admin\AppData\Local\Temp\tweak-ssd-v2-setup.exe" | C:\Users\admin\AppData\Local\Temp\tweak-ssd-v2-setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.2.0 Modules
| |||||||||||||||
| 2168 | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\tweak-ssd-x86.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\tweak-ssd-x86.exe | irsetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.2.0 Modules
| |||||||||||||||
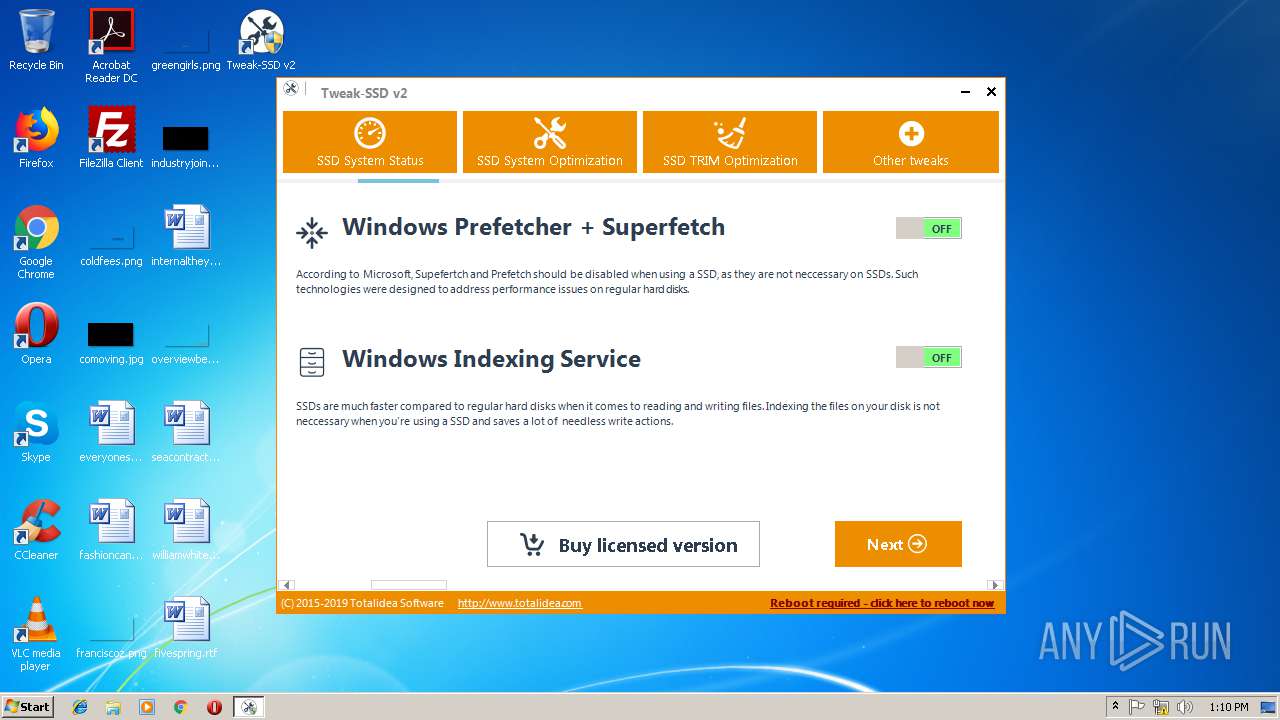
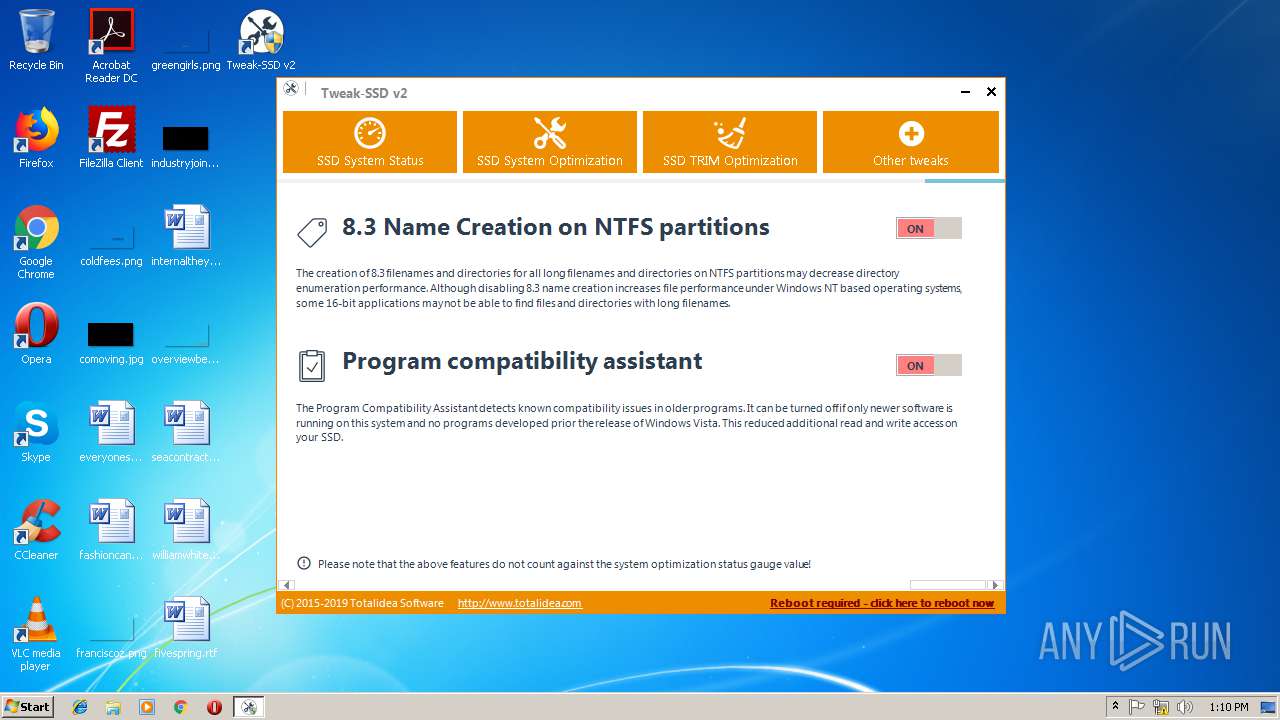
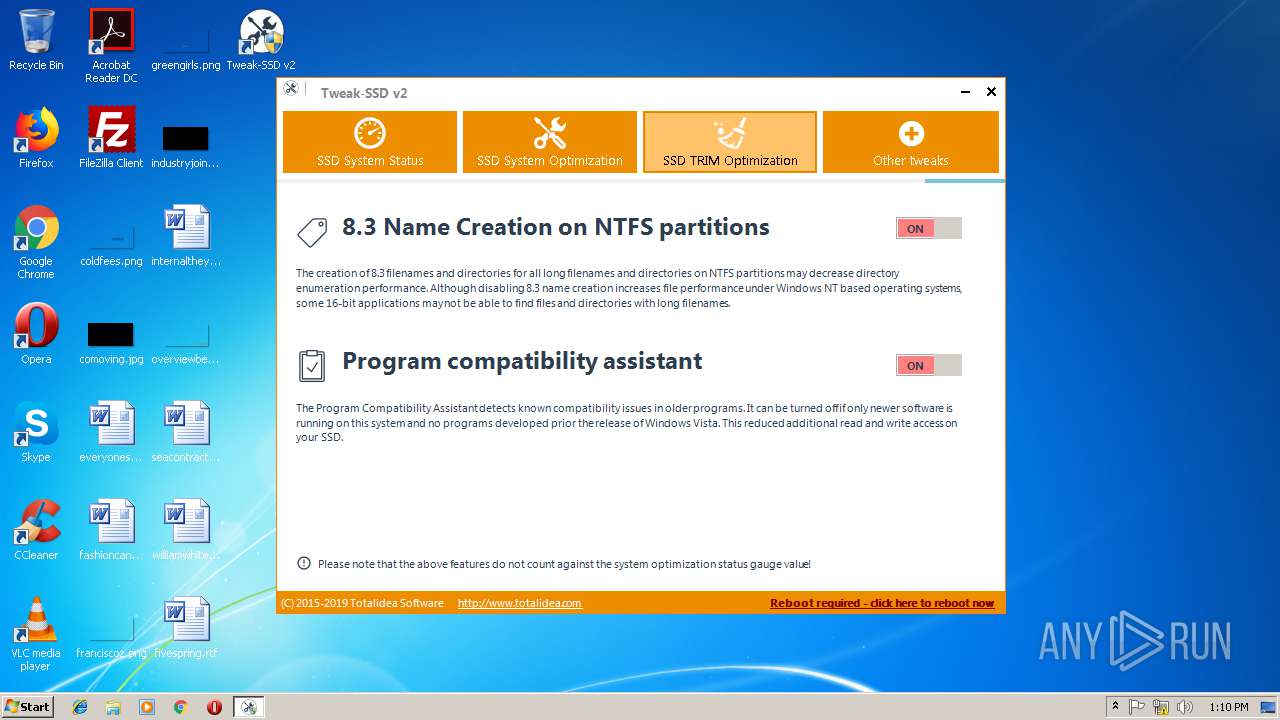
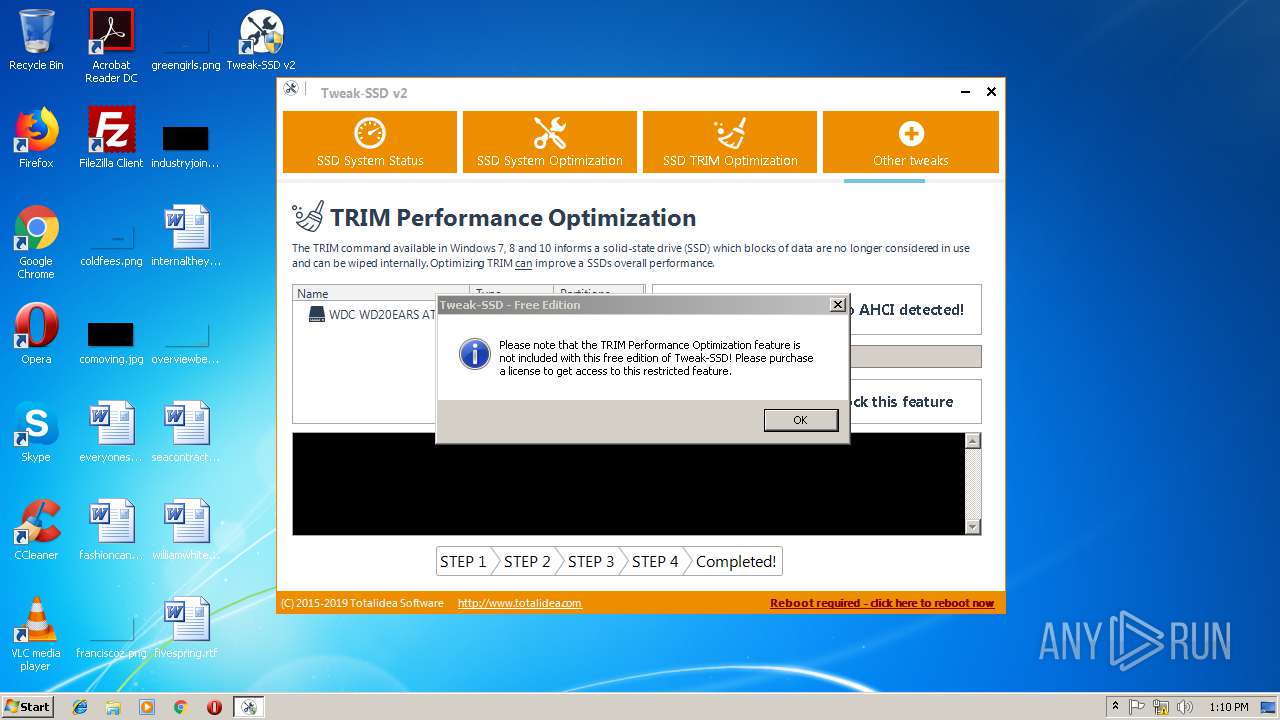
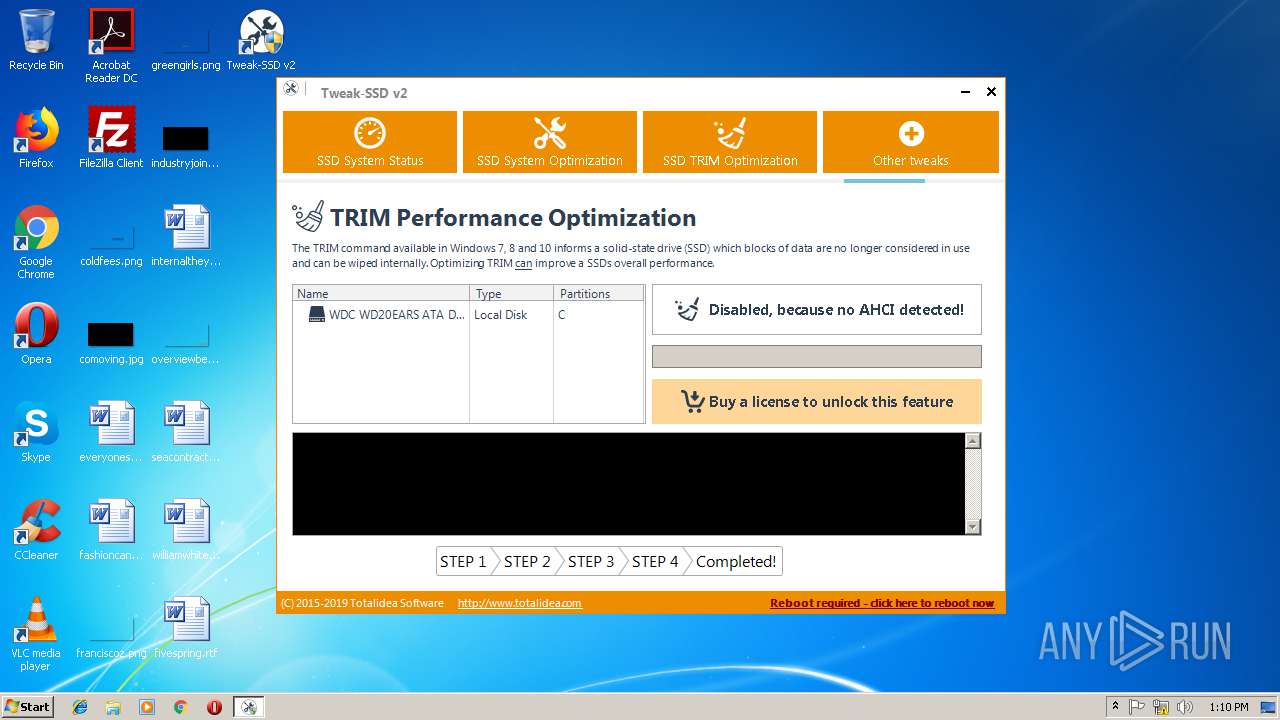
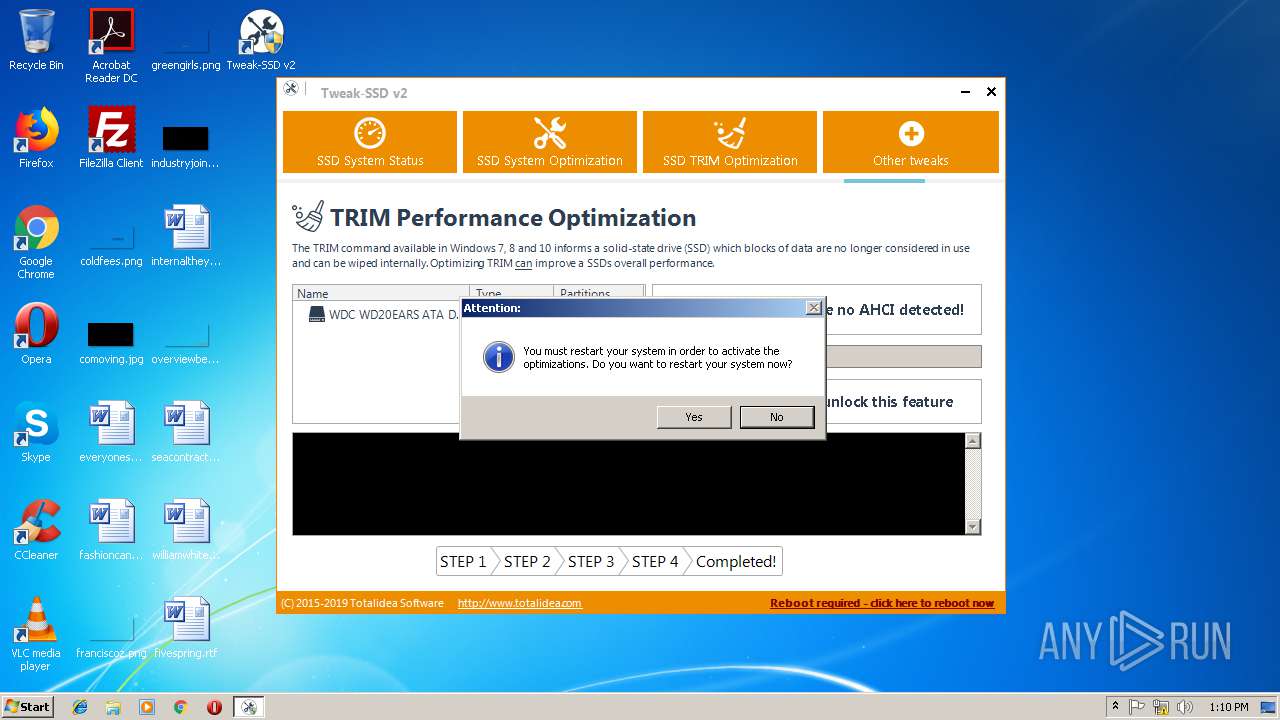
| 2436 | "C:\Program Files\Tweak-SSD v2\Tweak-SSD.exe" | C:\Program Files\Tweak-SSD v2\Tweak-SSD.exe | explorer.exe | ||||||||||||
User: admin Company: Totalidea Software GmbH Integrity Level: HIGH Description: Tweak-SSD v2 Exit code: 0 Version: 2.0.50.0 Modules
| |||||||||||||||
| 3076 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe" __IRAOFF:1804554 "__IRAFN:C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\tweak-ssd-x86.exe" "__IRCT:3" "__IRTSS:6316302" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe | tweak-ssd-x86.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.2.0 Modules
| |||||||||||||||
| 3536 | "C:\Users\admin\AppData\Local\Temp\tweak-ssd-v2-setup.exe" | C:\Users\admin\AppData\Local\Temp\tweak-ssd-v2-setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 9.5.2.0 Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Tweak-SSD v2\Tweak-SSD.exe" | C:\Program Files\Tweak-SSD v2\Tweak-SSD.exe | — | explorer.exe | |||||||||||
User: admin Company: Totalidea Software GmbH Integrity Level: MEDIUM Description: Tweak-SSD v2 Exit code: 3221226540 Version: 2.0.50.0 Modules
| |||||||||||||||
| 3964 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1804522 "__IRAFN:C:\Users\admin\AppData\Local\Temp\tweak-ssd-v2-setup.exe" "__IRCT:3" "__IRTSS:13998126" "__IRSID:S-1-5-21-1302019708-1500728564-335382590-1000" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | tweak-ssd-v2-setup.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.2.0 Modules
| |||||||||||||||
Total events
973
Read events
945
Write events
28
Delete events
0
Modification events
| (PID) Process: | (2052) tweak-ssd-v2-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2052) tweak-ssd-v2-setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2168) tweak-ssd-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2168) tweak-ssd-x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3076) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tweak-SSD v2 |
| Operation: | write | Name: | DisplayName |
Value: Tweak-SSD v2 | |||
| (PID) Process: | (3076) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tweak-SSD v2 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (3076) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tweak-SSD v2 |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (3076) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tweak-SSD v2 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Windows\Tweak-SSD v2\uninstall.exe" "/U:C:\Program Files\Tweak-SSD v2\Uninstall\uninstall.xml" | |||
| (PID) Process: | (3076) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tweak-SSD v2 |
| Operation: | write | Name: | Publisher |
Value: Totalidea Software | |||
| (PID) Process: | (3076) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Tweak-SSD v2 |
| Operation: | write | Name: | URLInfoAbout |
Value: http://www.totalidea.com | |||
Executable files
9
Suspicious files
3
Text files
17
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3076 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 3076 | irsetup.exe | C:\Program Files\Tweak-SSD v2\Uninstall\uni62D0.tmp | — | |
MD5:— | SHA256:— | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\tweak-ssd-x64.exe | executable | |
MD5:— | SHA256:— | |||
| 2052 | tweak-ssd-v2-setup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\tweak-ssd-x86.exe | executable | |
MD5:— | SHA256:— | |||
| 2168 | tweak-ssd-x86.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\irsetup.exe | executable | |
MD5:— | SHA256:— | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.dat | binary | |
MD5:— | SHA256:— | |||
| 2052 | tweak-ssd-v2-setup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\lua5.1.dll | executable | |
MD5:E7A789232EF503DCB4929791673009A3 | SHA256:89DAA79B558055F6F893ABF38A0F17D3E1E0193D59DAFBDF98D72D4E5961C2A1 | |||
| 3964 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG1.JPG | image | |
MD5:3220A6AEFB4FC719CC8849F060859169 | SHA256:988CF422CBF400D41C48FBE491B425A827A1B70691F483679C1DF02FB9352765 | |||
| 3076 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_1\IRIMG3.JPG | image | |
MD5:A4B429C7F32F0AB3DFDF35E20F963843 | SHA256:98941D6678060A367B770BB522CD1377B72EE4B5273ADCDAD4FBB0AE33852744 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report