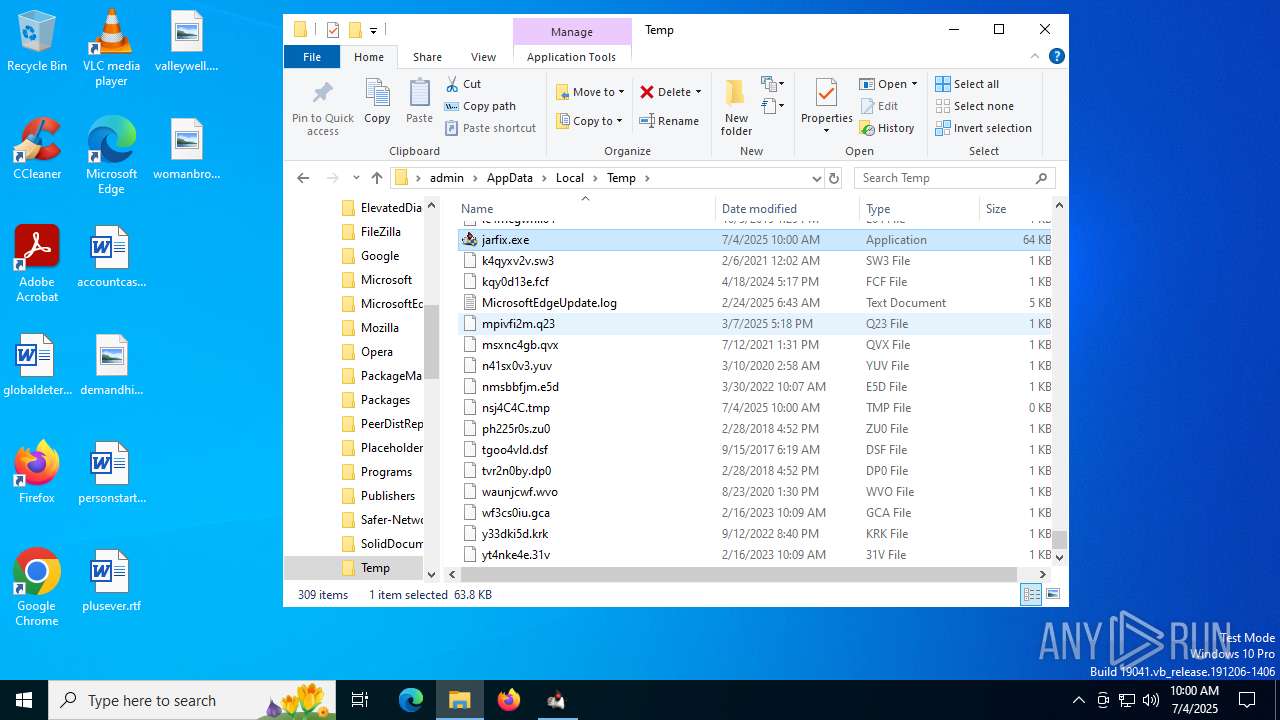
| File name: | jarfix.exe |
| Full analysis: | https://app.any.run/tasks/3cab0ea0-375c-447d-9d7c-8b910246131c |
| Verdict: | Malicious activity |
| Analysis date: | July 04, 2025, 10:00:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 562FFC6D21FB467401754301A8D826EE |
| SHA1: | 2173672223BAA5B34C14A6CF080A7D18EEE5921E |
| SHA256: | 9044DAC3C977C6AC561C24CDEB2073A8967E563916943EEA10367A56EC5E7ECE |
| SSDEEP: | 768:dwdk1aQk/MxBzLM3PrZS/Sd2bX7P+LPOFyVtMnJoieSqZhhSEflDG2regRwuF:W69IMxWflSQ2T7P+MnJ1uhhSEfliiwE |
MALICIOUS
No malicious indicators.SUSPICIOUS
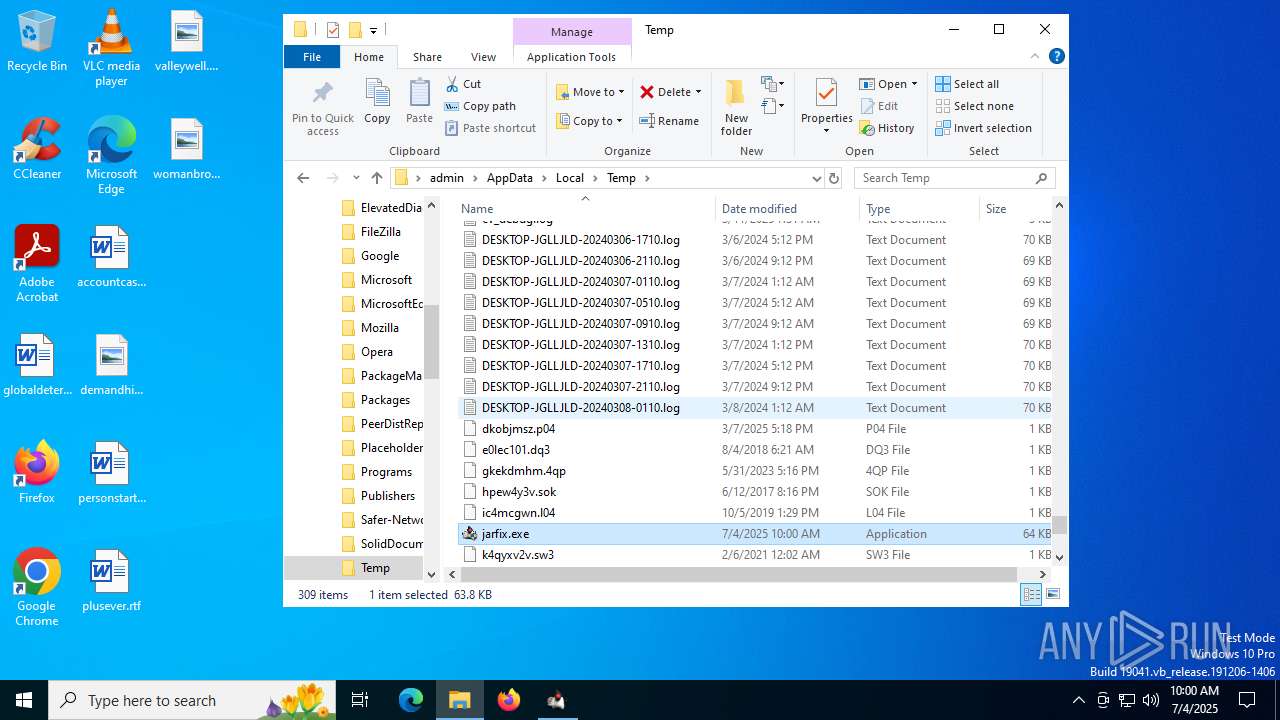
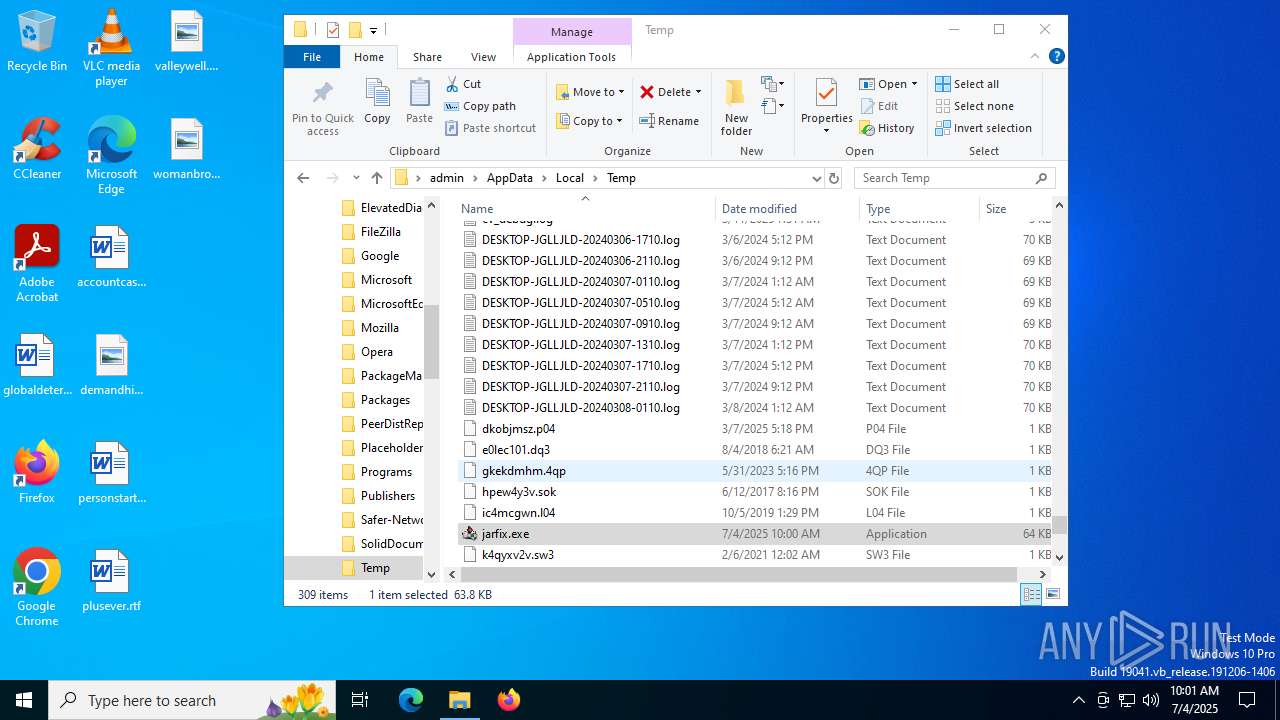
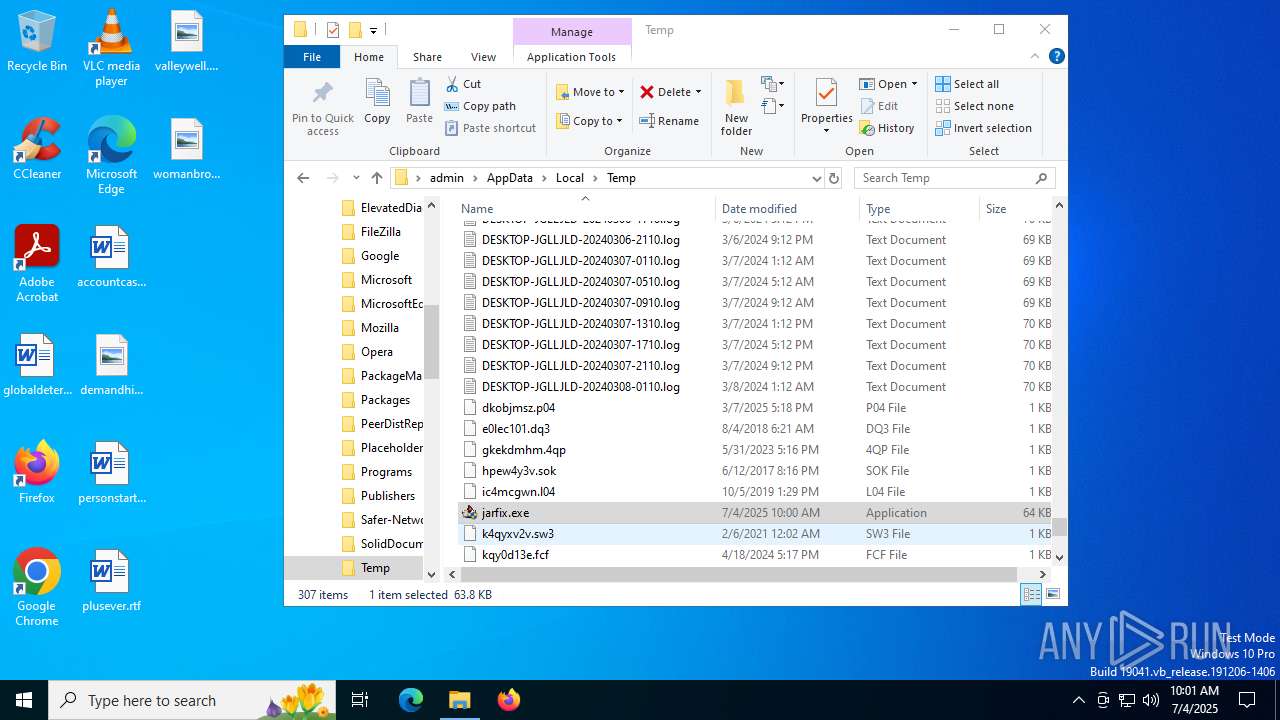
The process creates files with name similar to system file names
- jarfix.exe (PID: 5712)
- jarfix.exe (PID: 4916)
- jarfix.exe (PID: 2148)
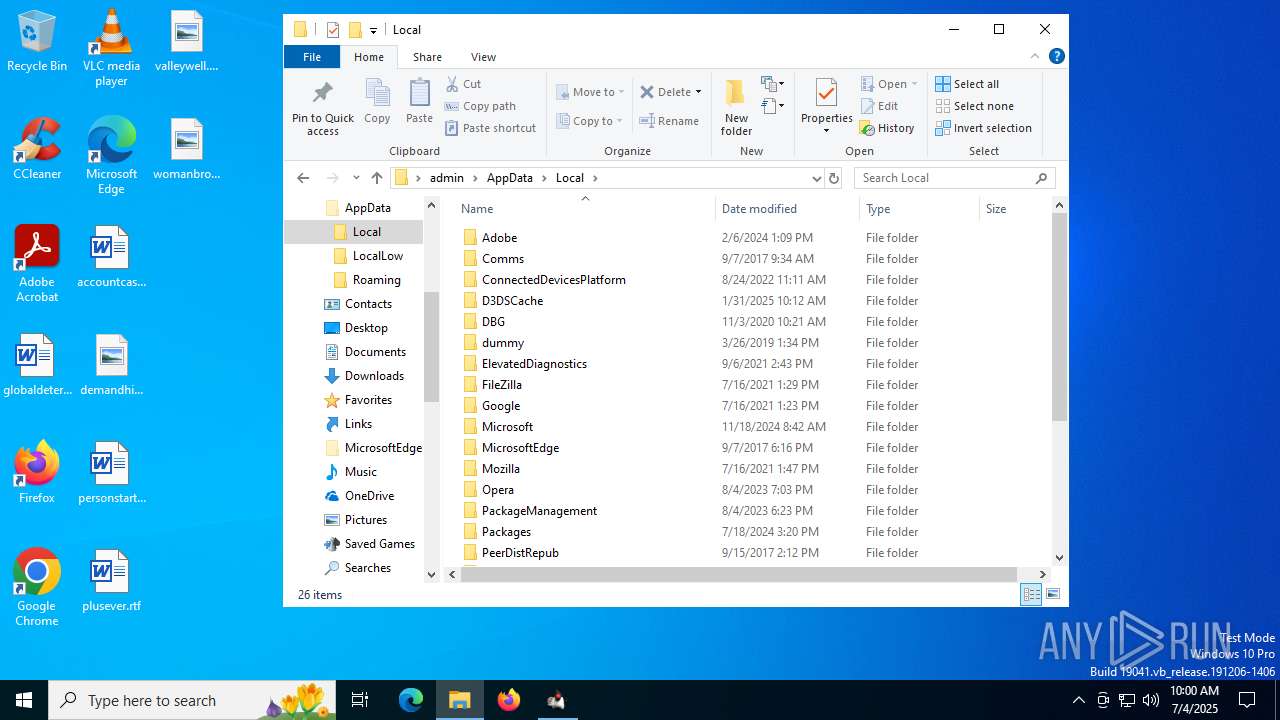
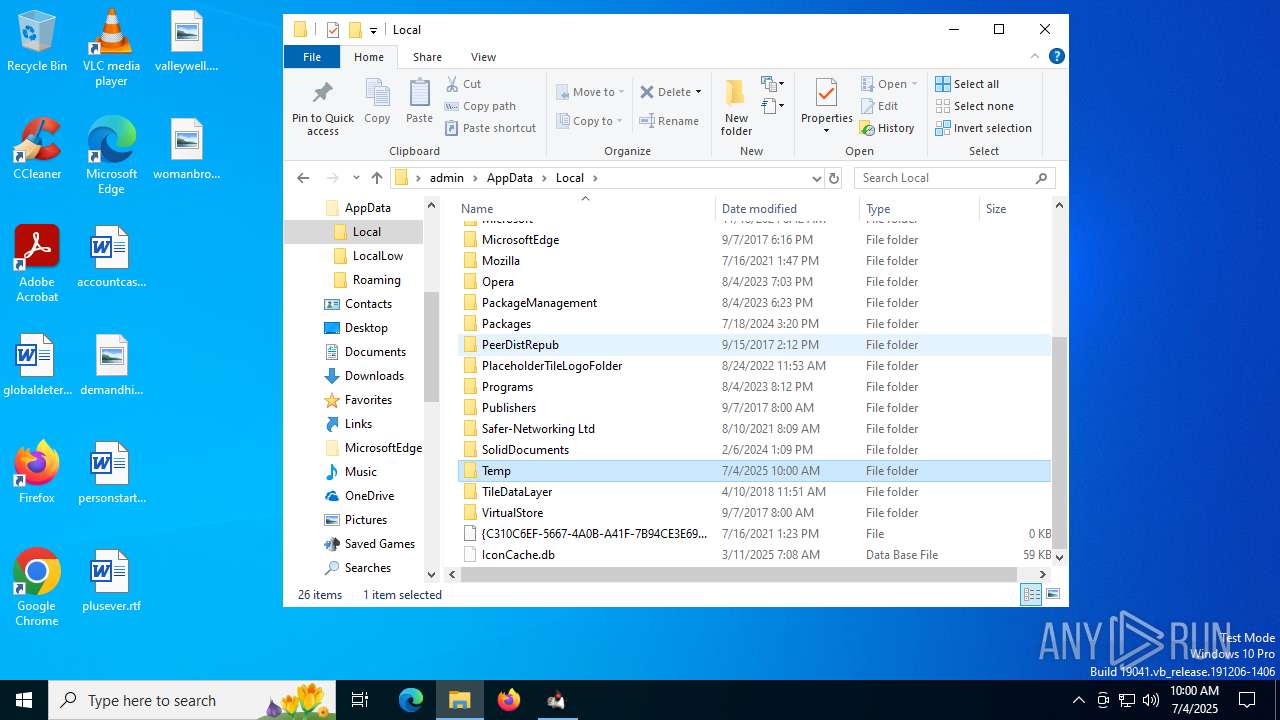
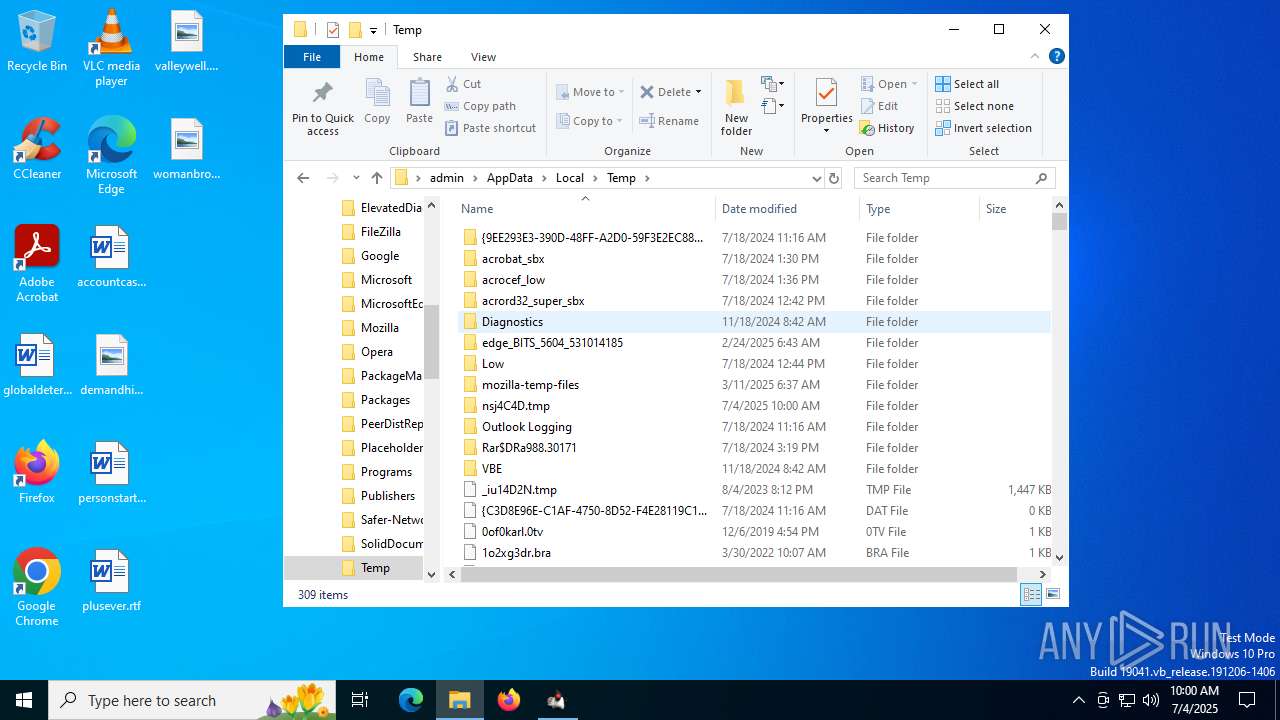
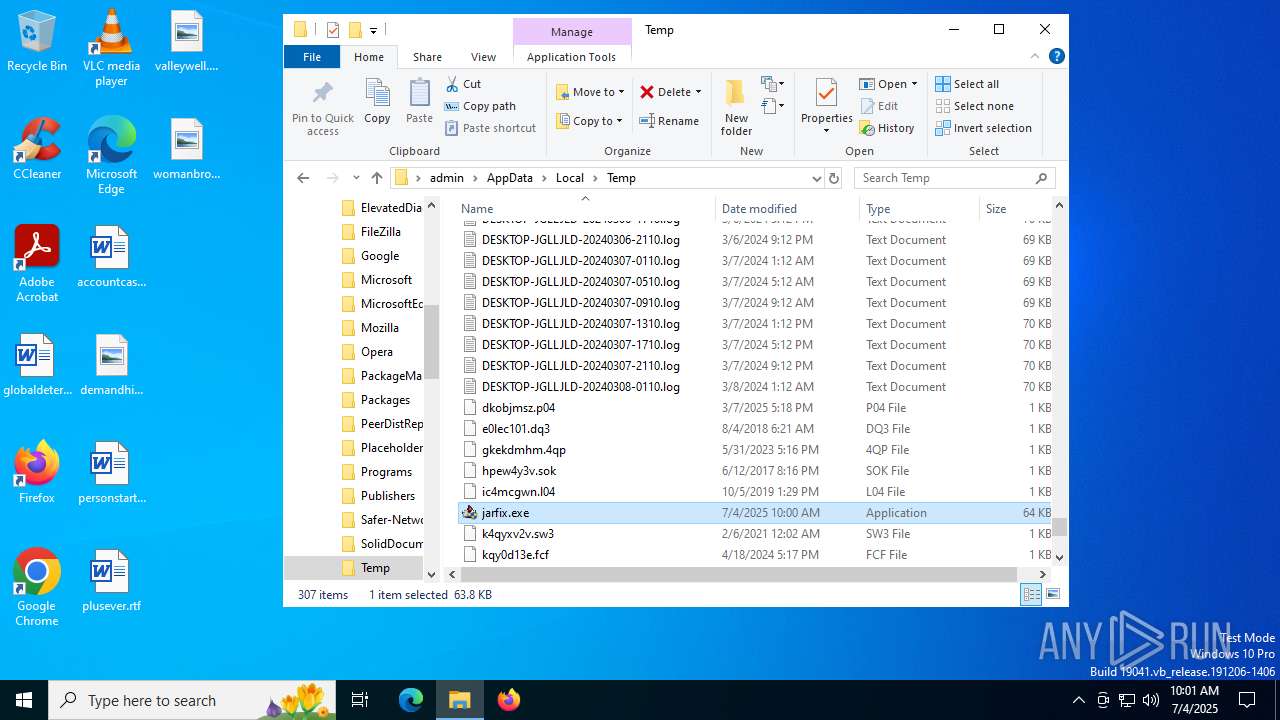
Malware-specific behavior (creating "System.dll" in Temp)
- jarfix.exe (PID: 5712)
- jarfix.exe (PID: 2148)
- jarfix.exe (PID: 4916)
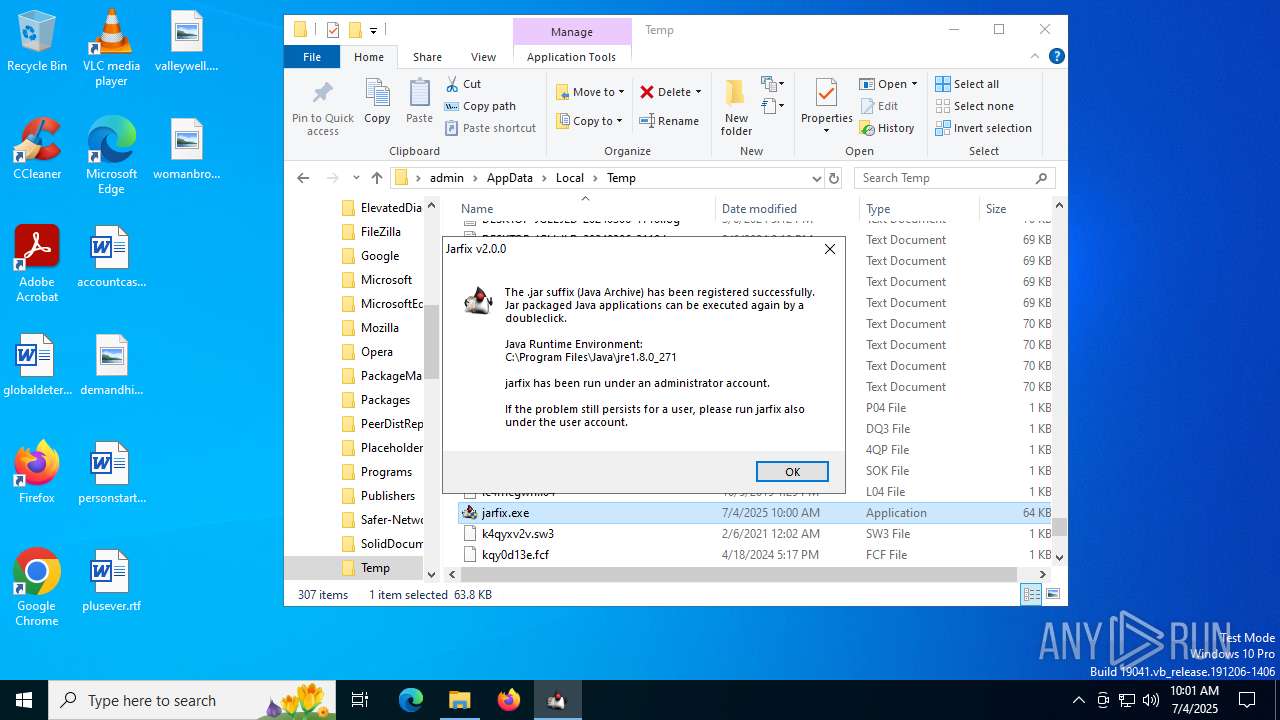
Checks for Java to be installed
- jarfix.exe (PID: 5712)
- jarfix.exe (PID: 4916)
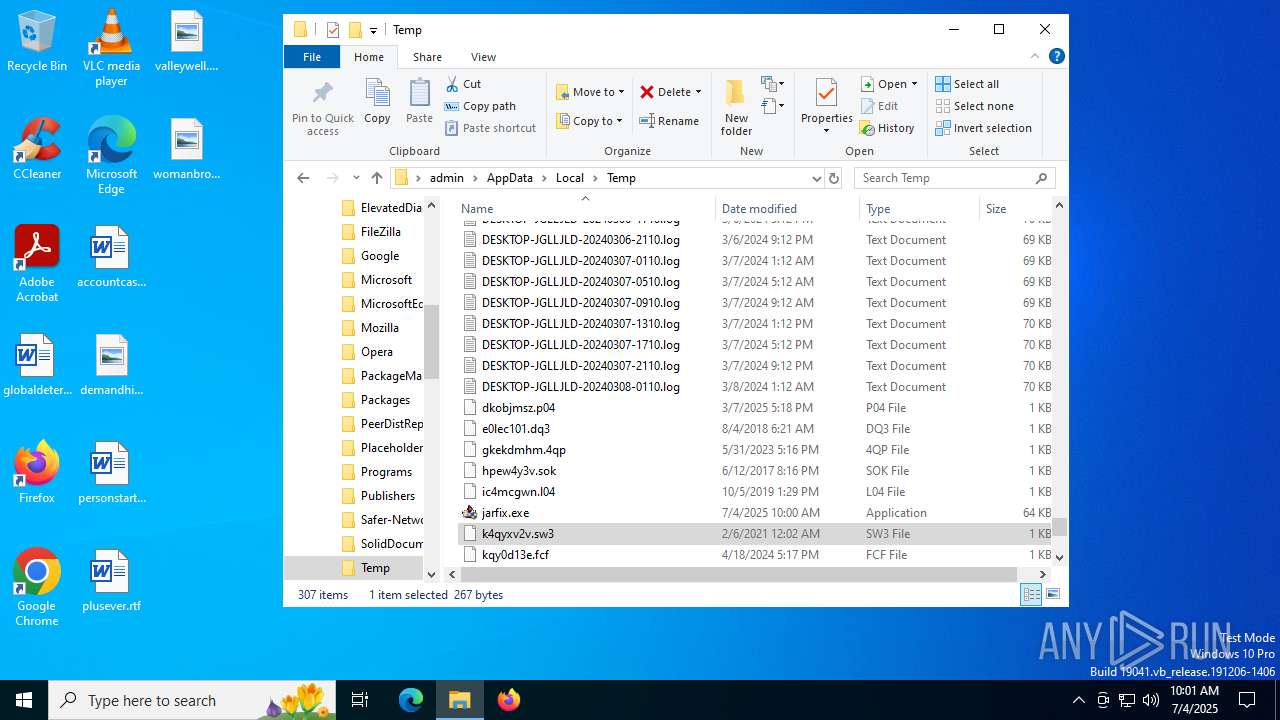
Executable content was dropped or overwritten
- jarfix.exe (PID: 5712)
- jarfix.exe (PID: 2148)
- jarfix.exe (PID: 4916)
INFO
Checks supported languages
- jarfix.exe (PID: 5712)
- jarfix.exe (PID: 2148)
- jarfix.exe (PID: 4916)
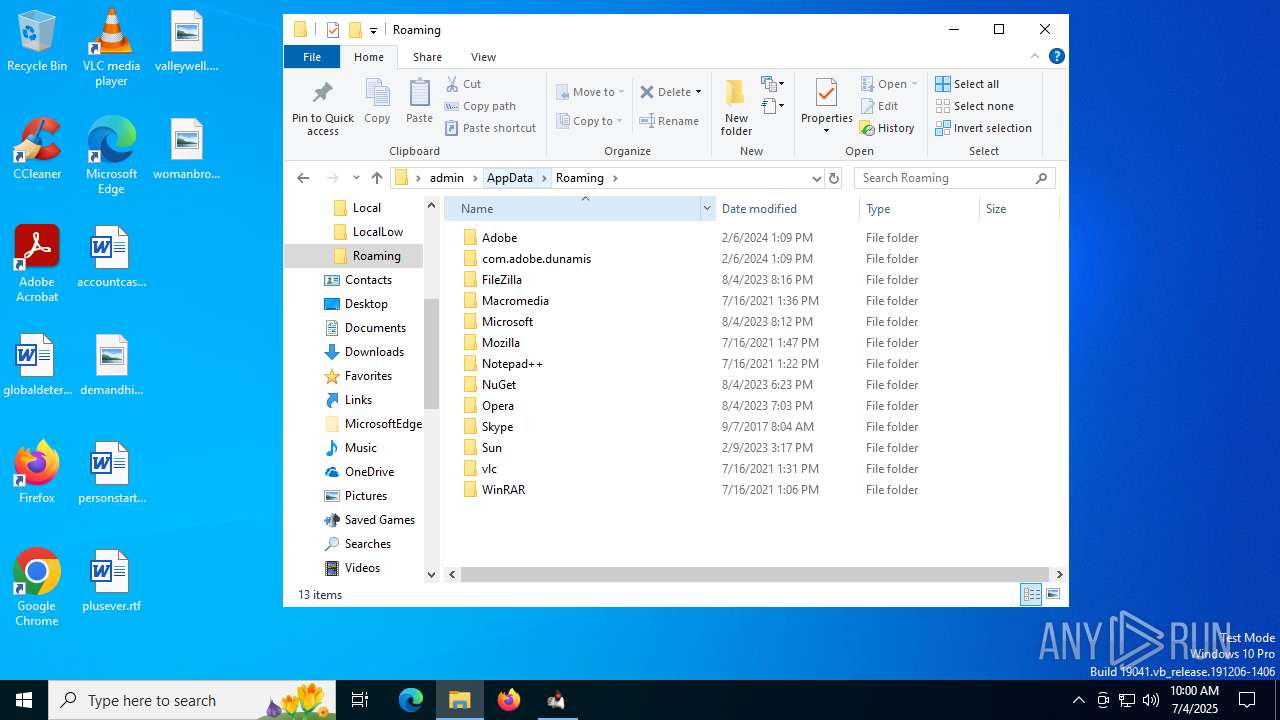
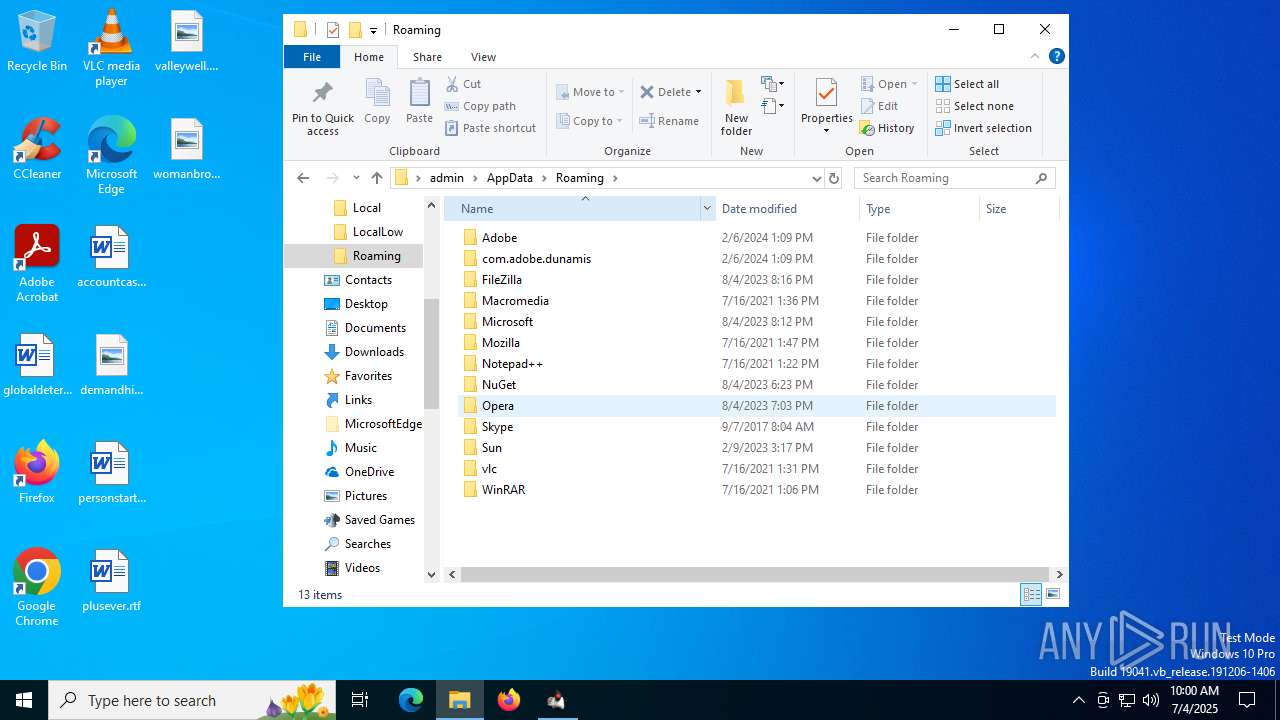
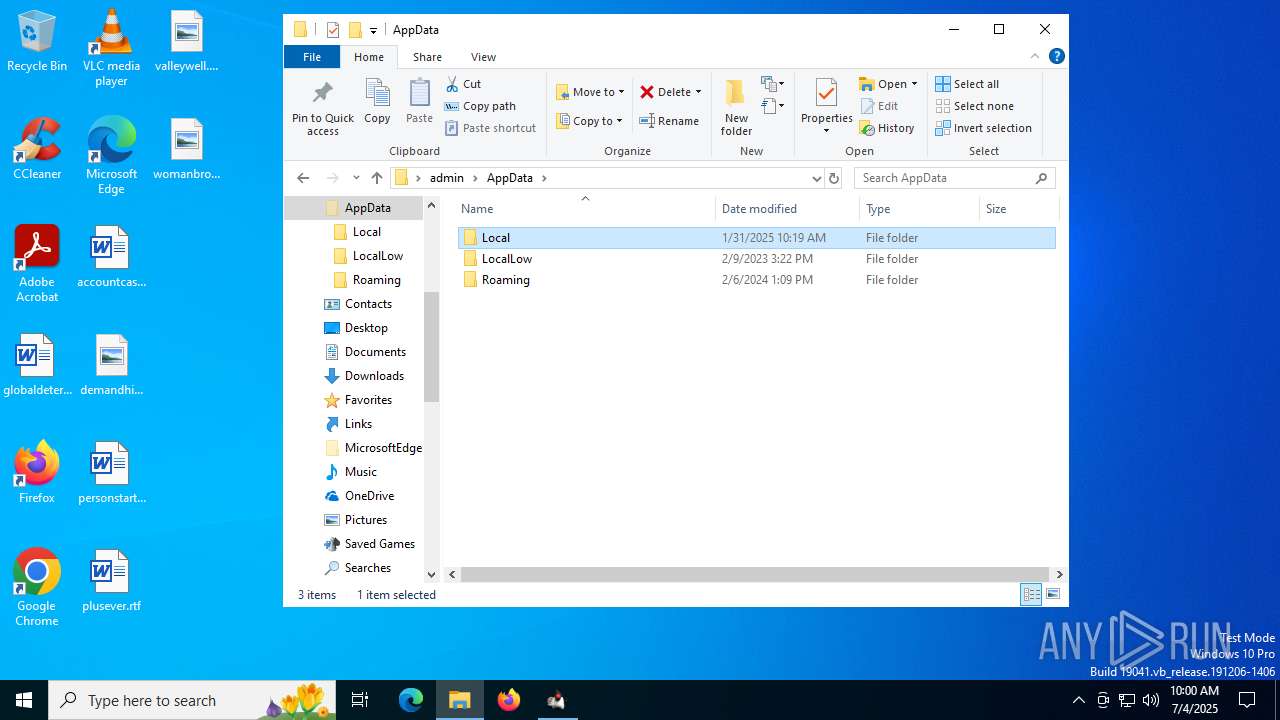
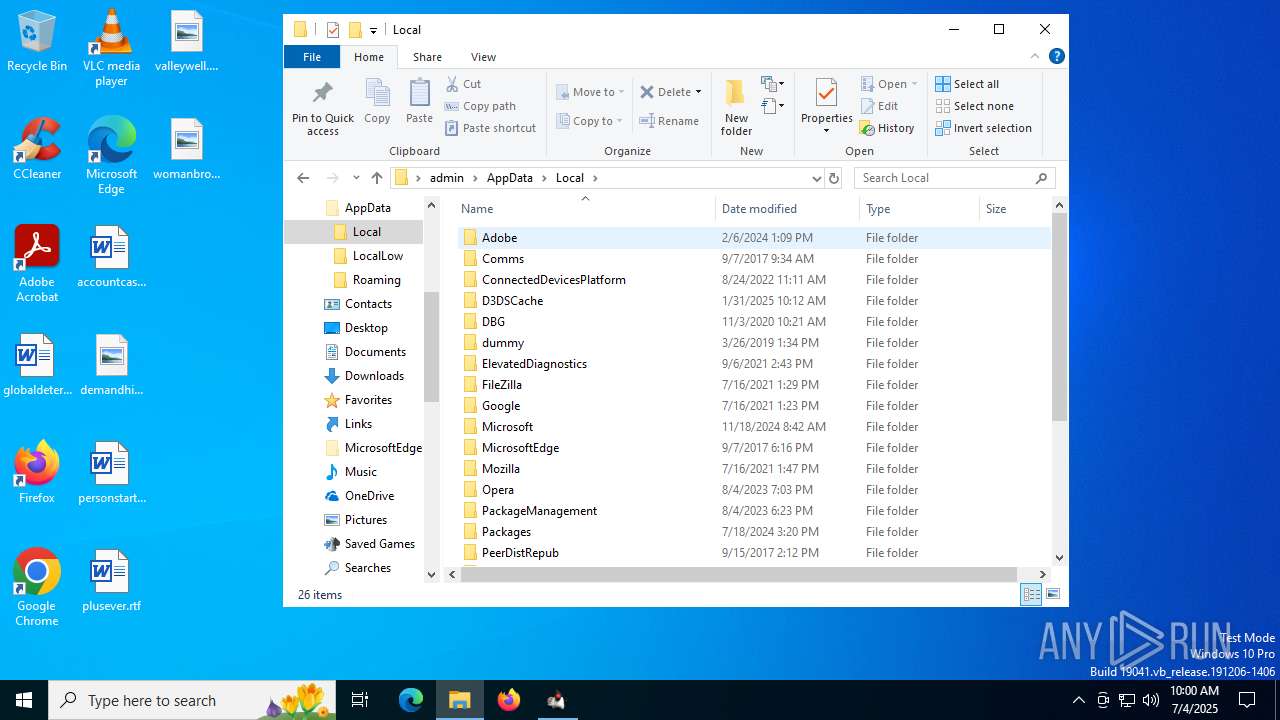
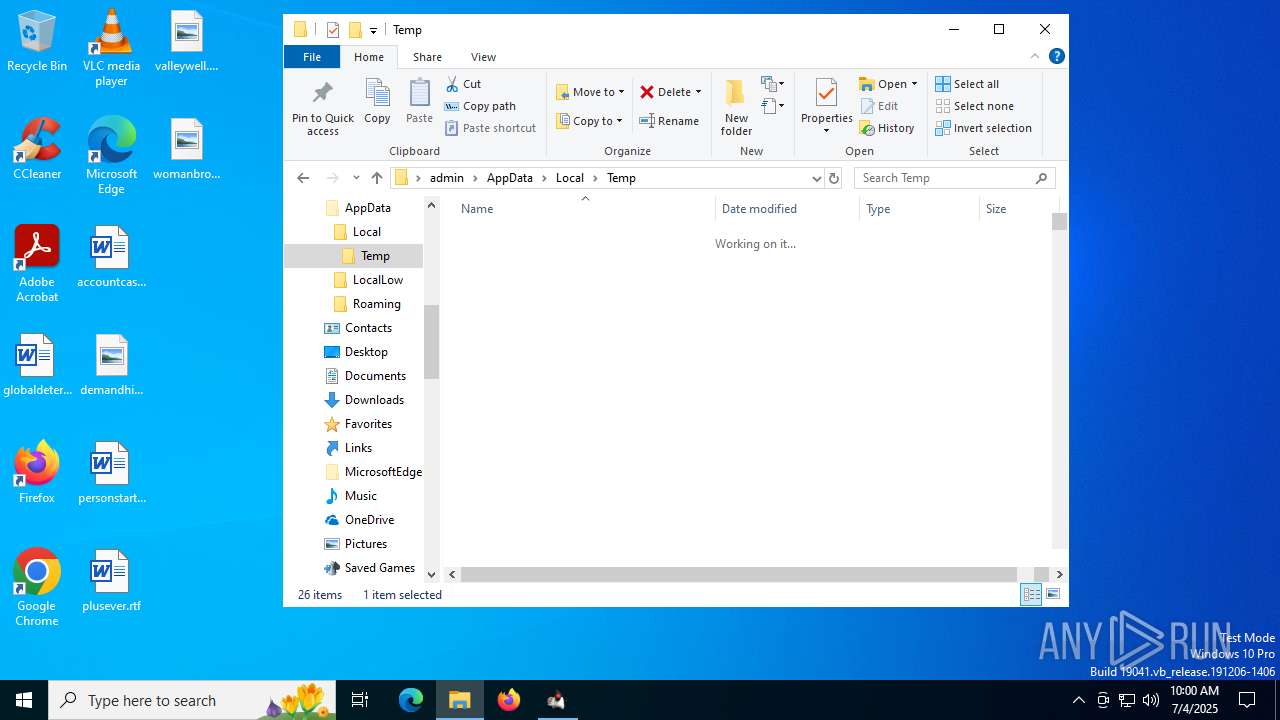
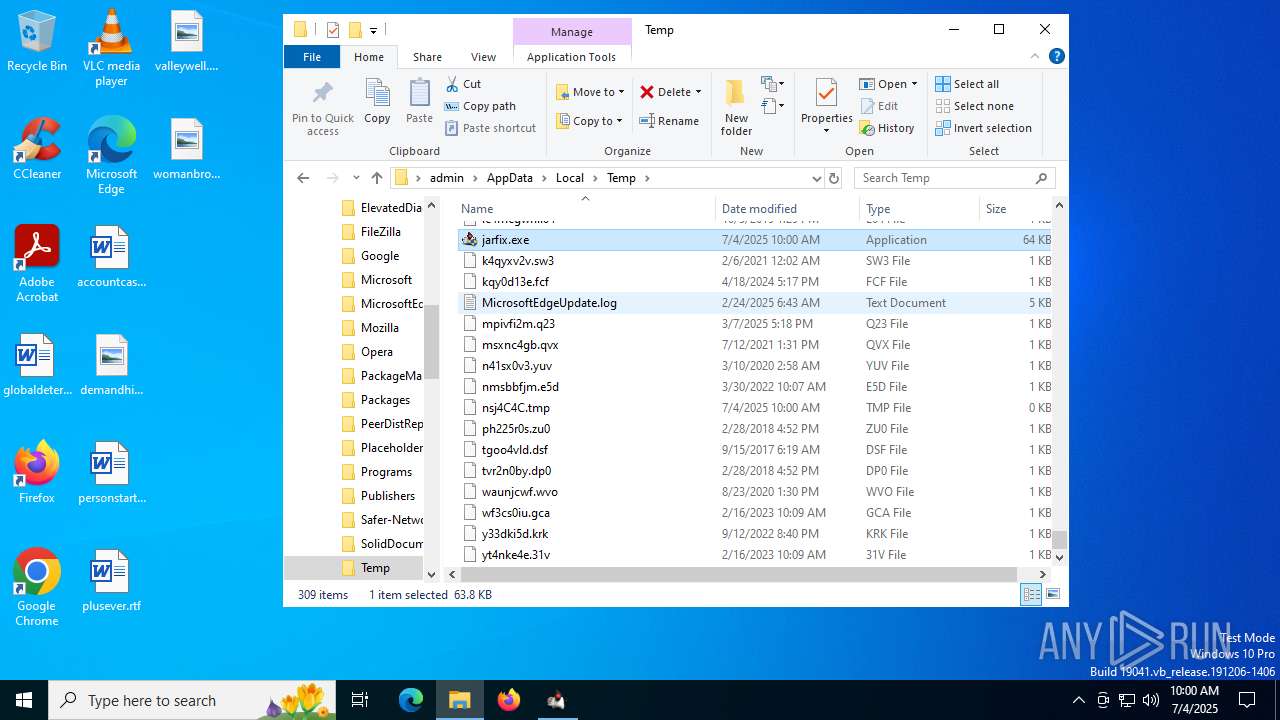
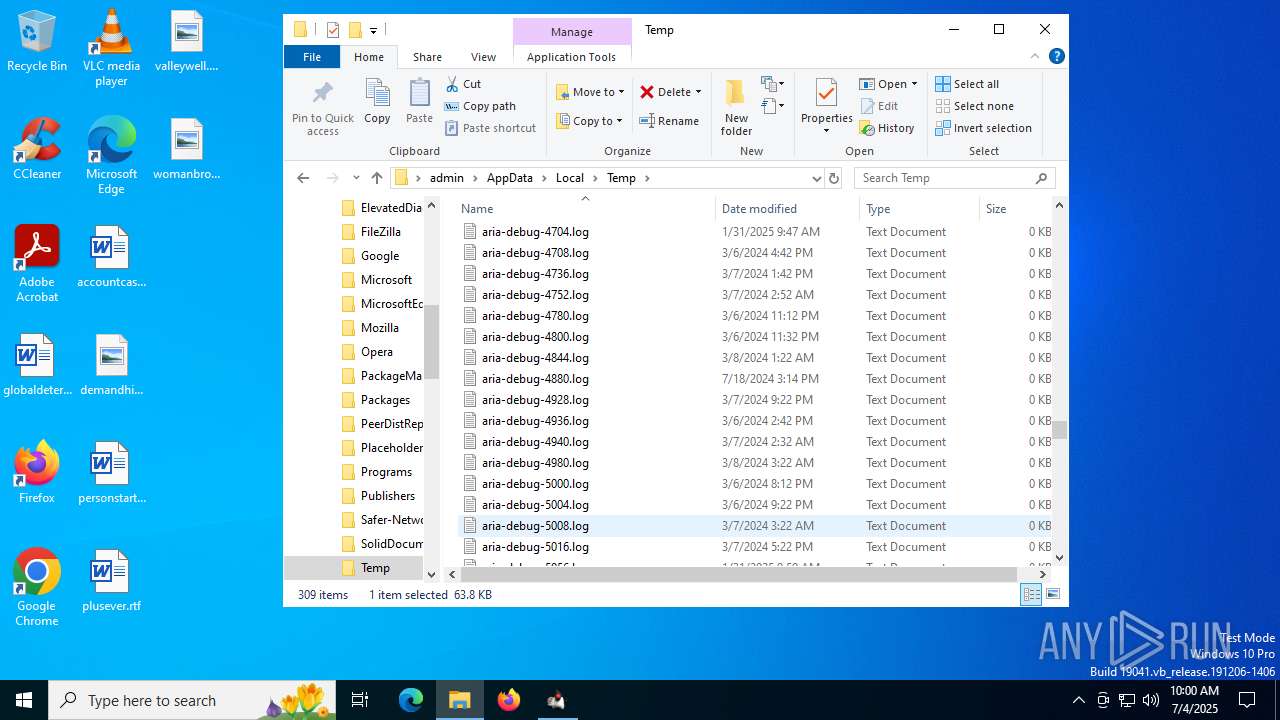
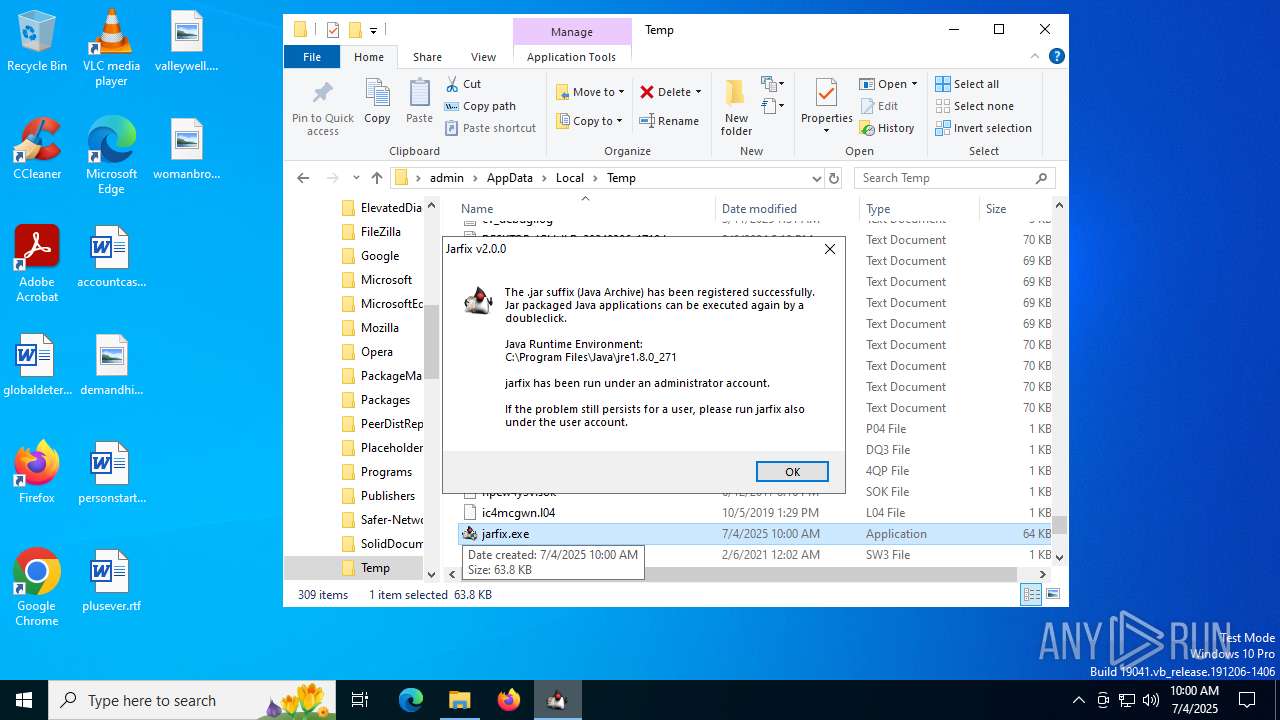
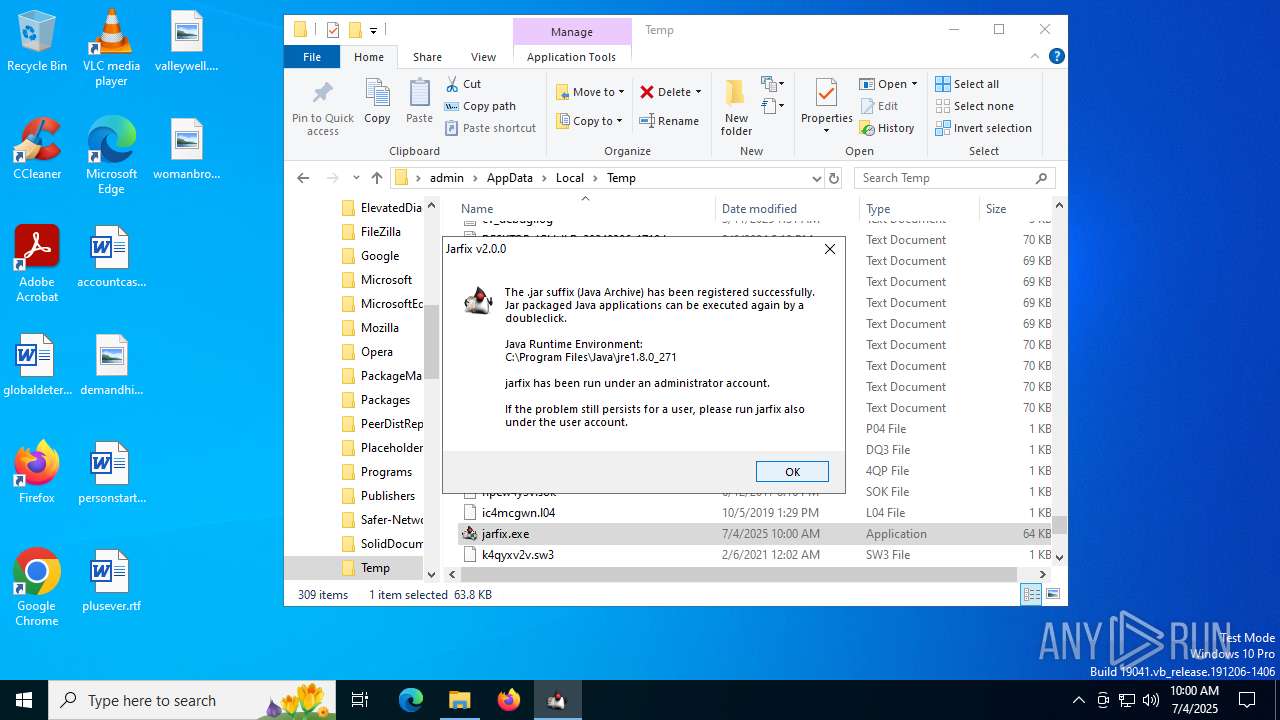
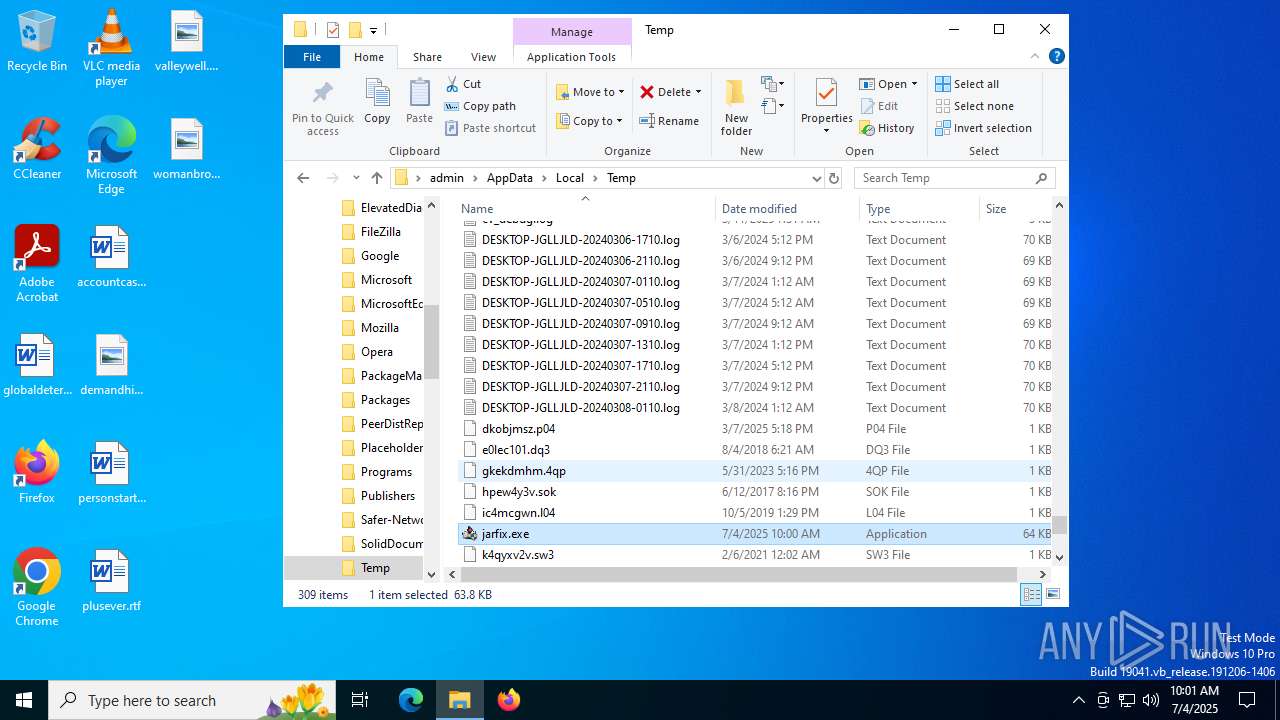
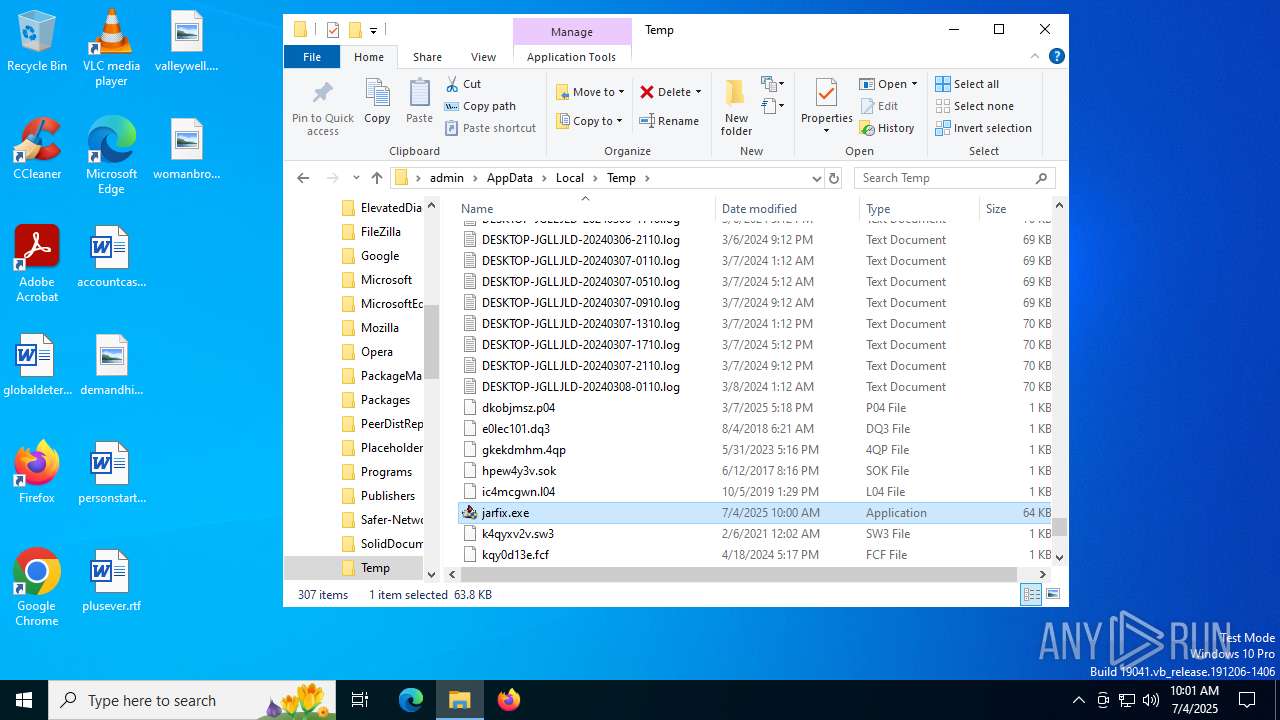
Create files in a temporary directory
- jarfix.exe (PID: 2148)
- jarfix.exe (PID: 4916)
- jarfix.exe (PID: 5712)
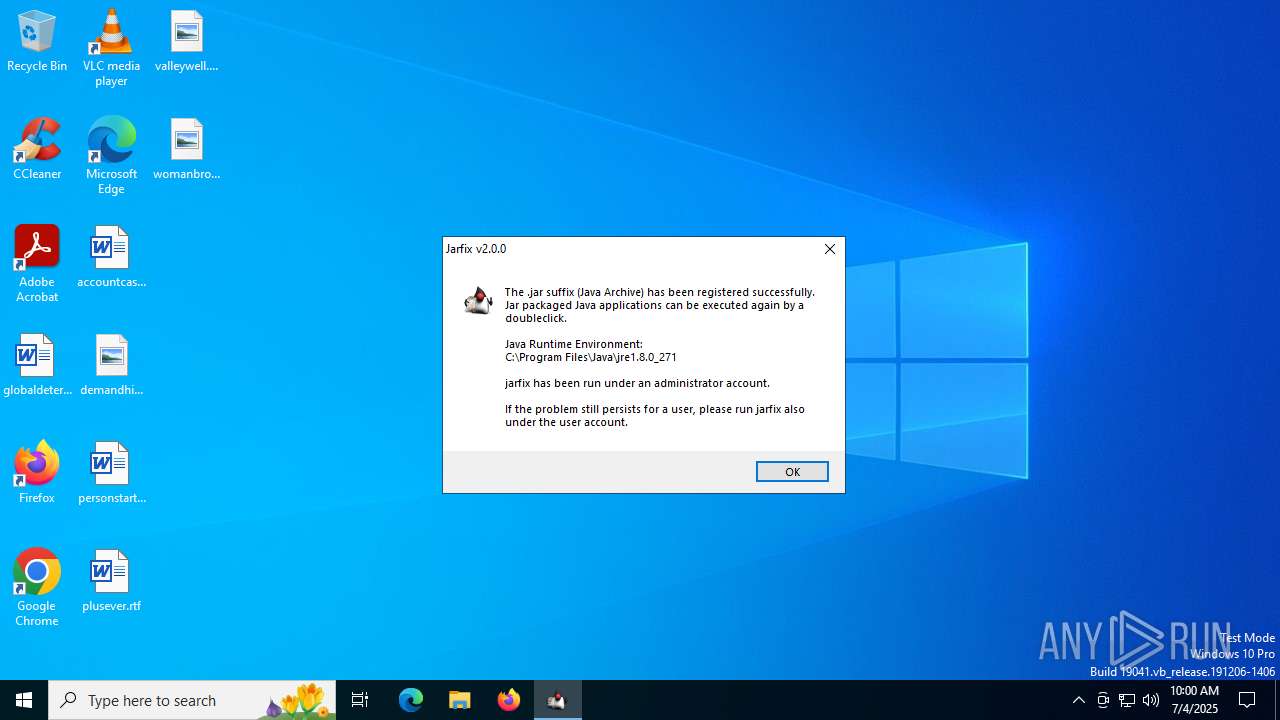
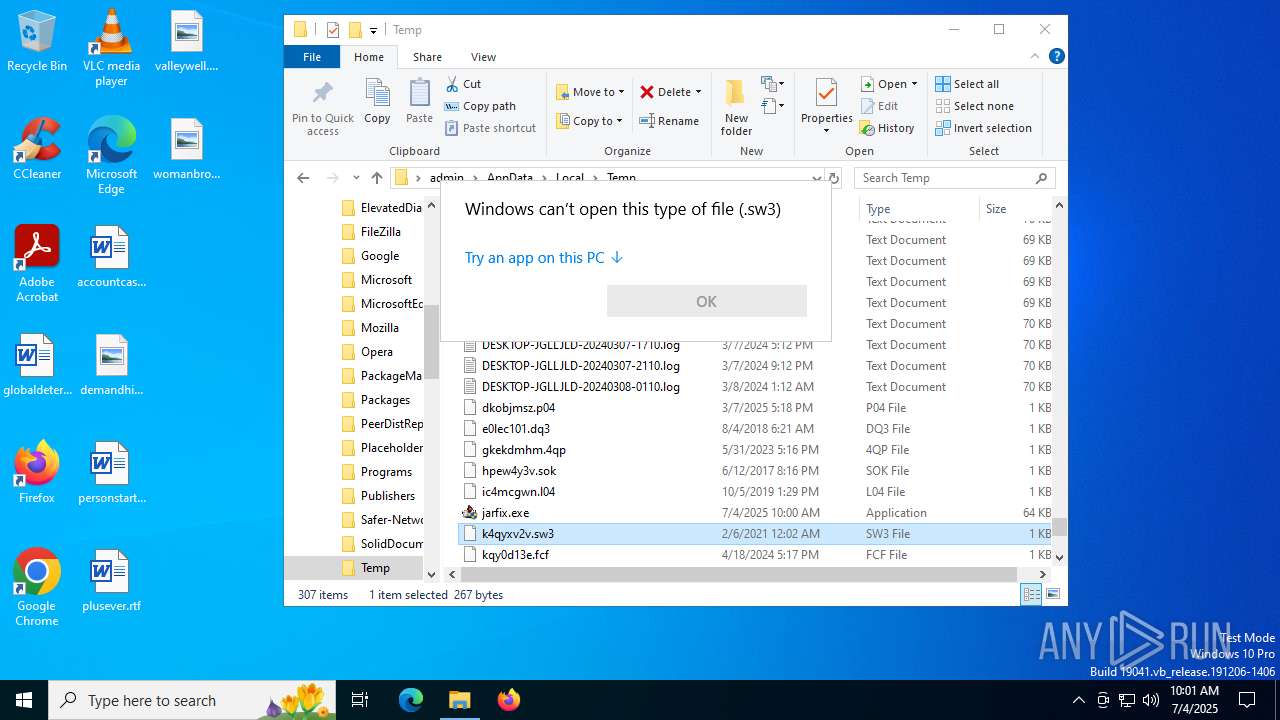
Manual execution by a user
- jarfix.exe (PID: 2180)
- jarfix.exe (PID: 1944)
- jarfix.exe (PID: 4916)
- jarfix.exe (PID: 2148)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 4860)
Checks proxy server information
- slui.exe (PID: 4808)
Reads the computer name
- jarfix.exe (PID: 4916)
- jarfix.exe (PID: 5712)
Reads the software policy settings
- slui.exe (PID: 4808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:46+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
152
Monitored processes
9
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1944 | "C:\Users\admin\AppData\Local\Temp\jarfix.exe" | C:\Users\admin\AppData\Local\Temp\jarfix.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2148 | "C:\Users\admin\AppData\Local\Temp\jarfix.exe" | C:\Users\admin\AppData\Local\Temp\jarfix.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\AppData\Local\Temp\jarfix.exe" | C:\Users\admin\AppData\Local\Temp\jarfix.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4808 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4860 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4916 | "C:\Users\admin\AppData\Local\Temp\jarfix.exe" | C:\Users\admin\AppData\Local\Temp\jarfix.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 5712 | "C:\Users\admin\AppData\Local\Temp\jarfix.exe" | C:\Users\admin\AppData\Local\Temp\jarfix.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 5808 | "C:\Users\admin\AppData\Local\Temp\jarfix.exe" | C:\Users\admin\AppData\Local\Temp\jarfix.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7104 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 757
Read events
1 743
Write events
2
Delete events
12
Modification events
| (PID) Process: | (5712) jarfix.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
| (PID) Process: | (5712) jarfix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.jar |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5712) jarfix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\jarfile\shell\open\command |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5712) jarfix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\jarfile\shell\open |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5712) jarfix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\jarfile\shell |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5712) jarfix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\jarfile |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) jarfix.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) jarfix.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4916) jarfix.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.jar\OpenWithProgids |
| Operation: | write | Name: | jarfile |
Value: | |||
| (PID) Process: | (4916) jarfix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.jar |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
5
Suspicious files
0
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5712 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nsj4C4D.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 4916 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nsd1615.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 4916 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nsd1614.tmp | pcx | |
MD5:BCA3F36C4800B3A6E48EA8B30FC15D70 | SHA256:00D52147D27553CB79EB420687D1F359C94F2DE97569FC31B693966E39E9D9C6 | |||
| 2148 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nscC63F.tmp | pcx | |
MD5:BCA3F36C4800B3A6E48EA8B30FC15D70 | SHA256:00D52147D27553CB79EB420687D1F359C94F2DE97569FC31B693966E39E9D9C6 | |||
| 2148 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nscC640.tmp\System.dll | executable | |
MD5:C17103AE9072A06DA581DEC998343FC1 | SHA256:DC58D8AD81CACB0C1ED72E33BFF8F23EA40B5252B5BB55D393A0903E6819AE2F | |||
| 5712 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nsj4C4C.tmp | pcx | |
MD5:BCA3F36C4800B3A6E48EA8B30FC15D70 | SHA256:00D52147D27553CB79EB420687D1F359C94F2DE97569FC31B693966E39E9D9C6 | |||
| 5712 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nsj4C4D.tmp\UserInfo.dll | executable | |
MD5:7579ADE7AE1747A31960A228CE02E666 | SHA256:564C80DEC62D76C53497C40094DB360FF8A36E0DC1BDA8383D0F9583138997F5 | |||
| 4916 | jarfix.exe | C:\Users\admin\AppData\Local\Temp\nsd1615.tmp\UserInfo.dll | executable | |
MD5:7579ADE7AE1747A31960A228CE02E666 | SHA256:564C80DEC62D76C53497C40094DB360FF8A36E0DC1BDA8383D0F9583138997F5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
26
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.35:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4320 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
2388 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2072 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.35:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4320 | svchost.exe | 20.190.160.132:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4320 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |