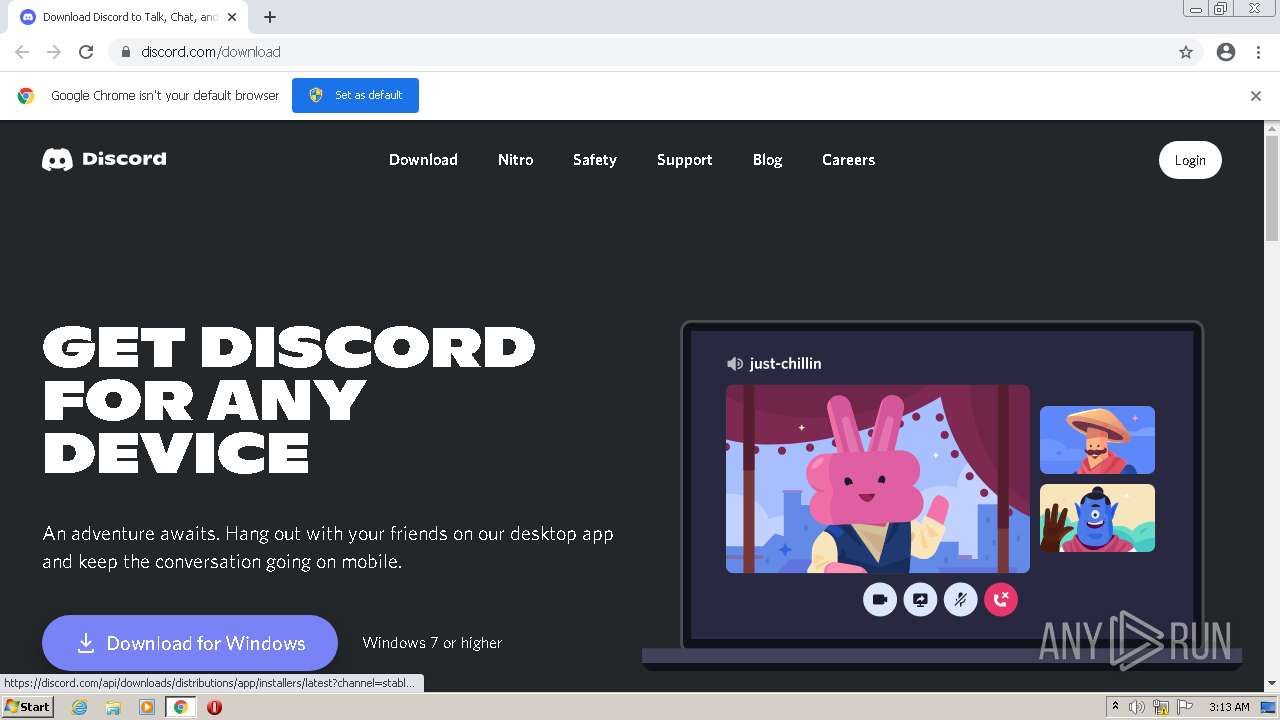
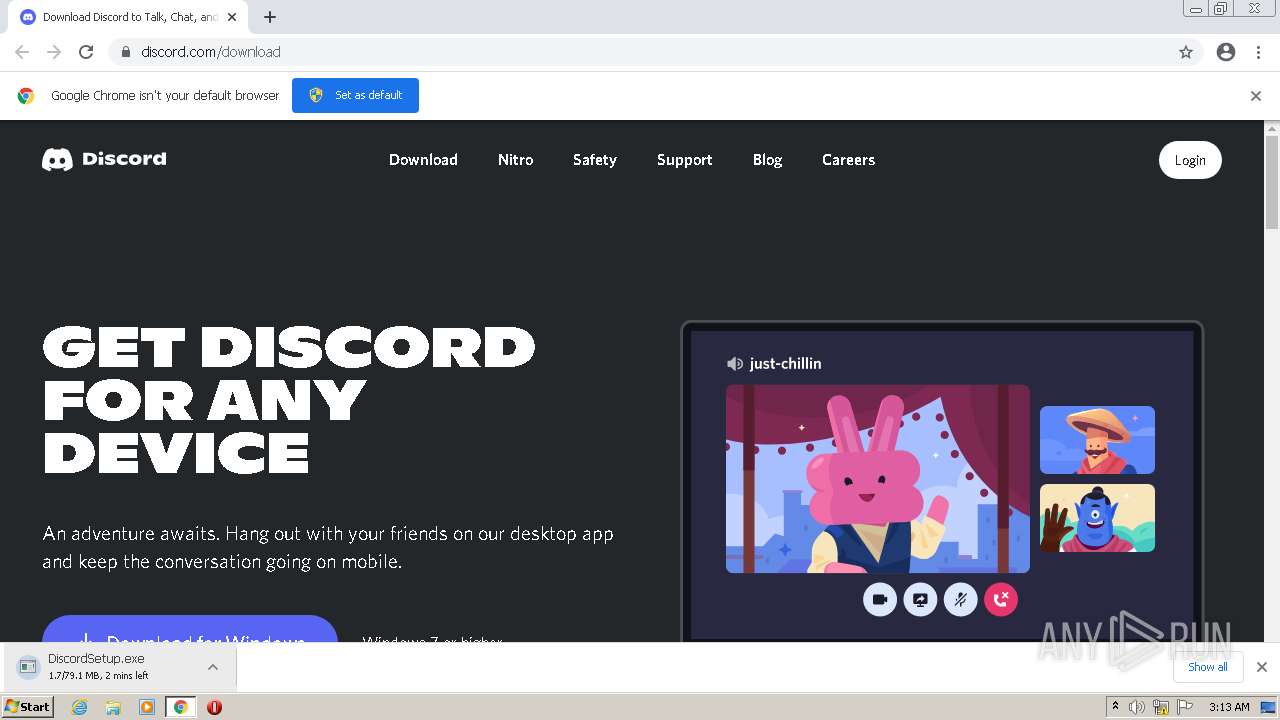
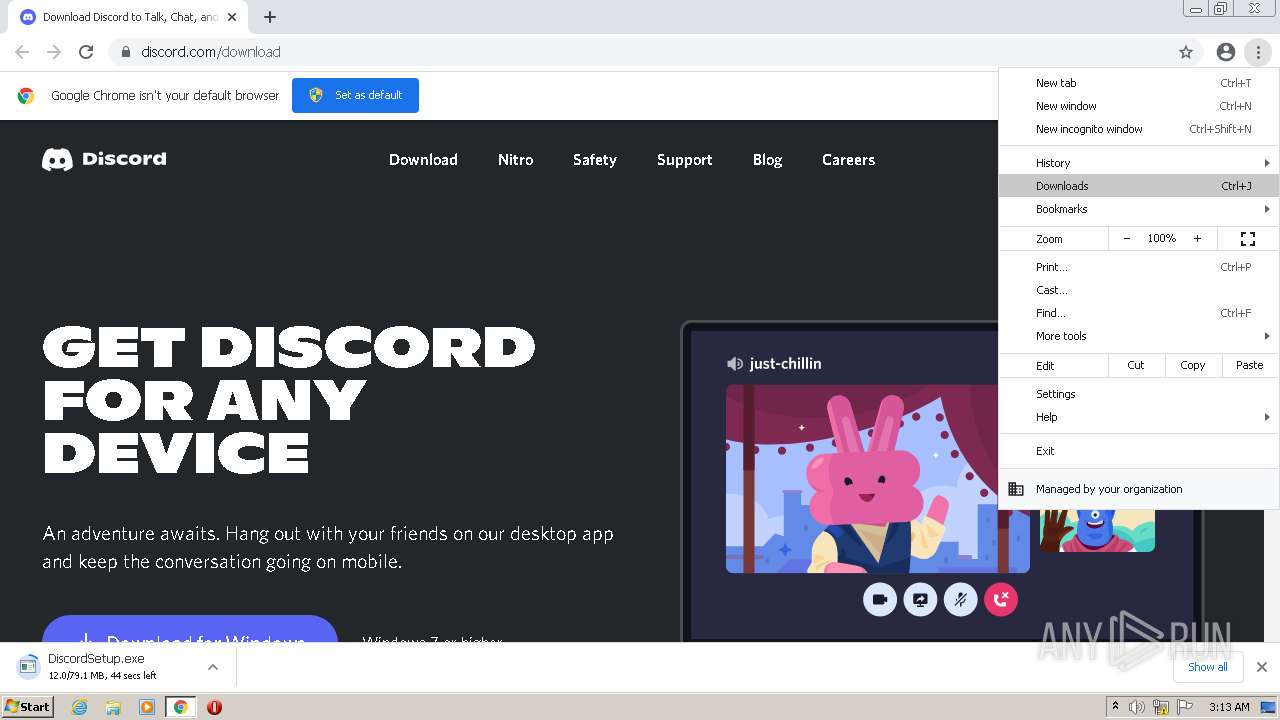
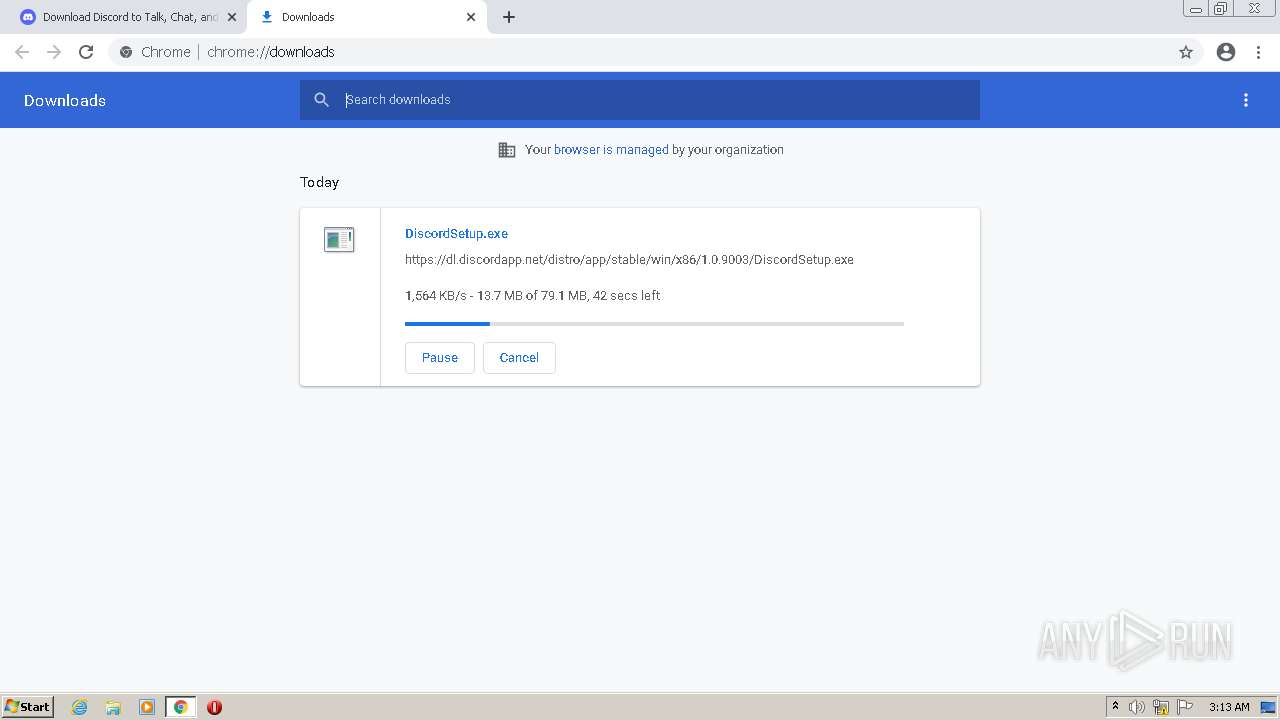
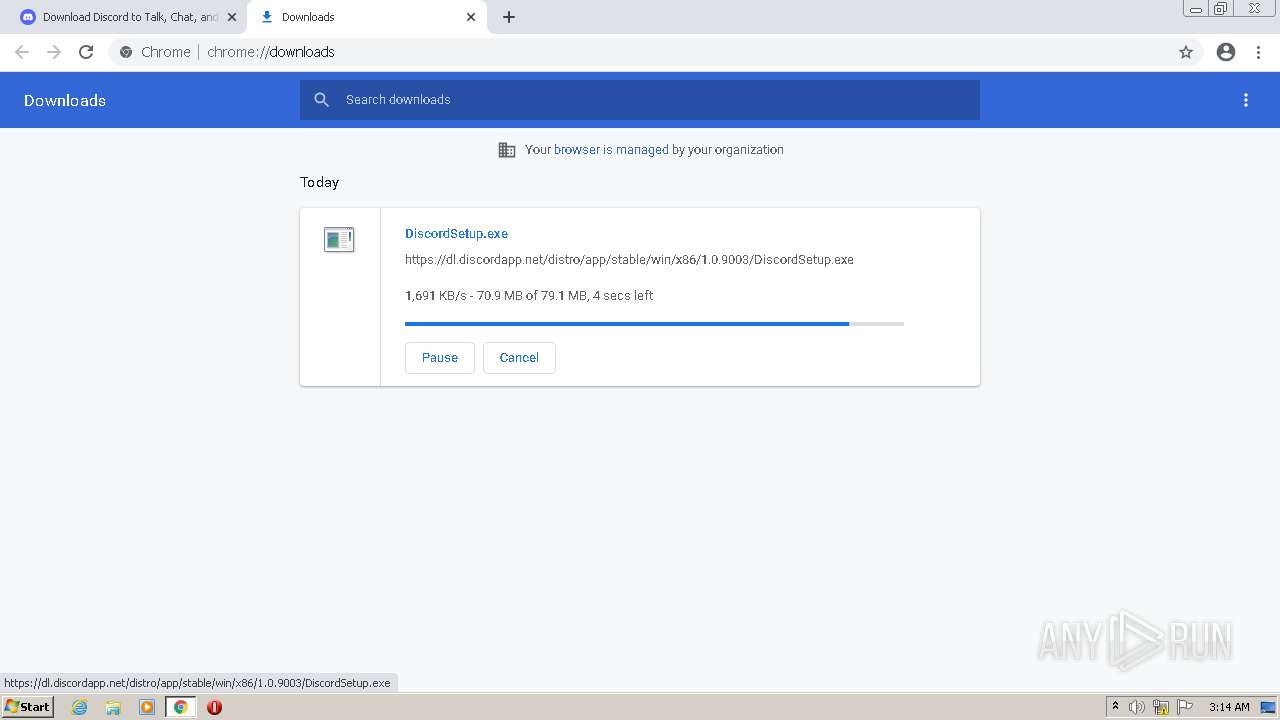
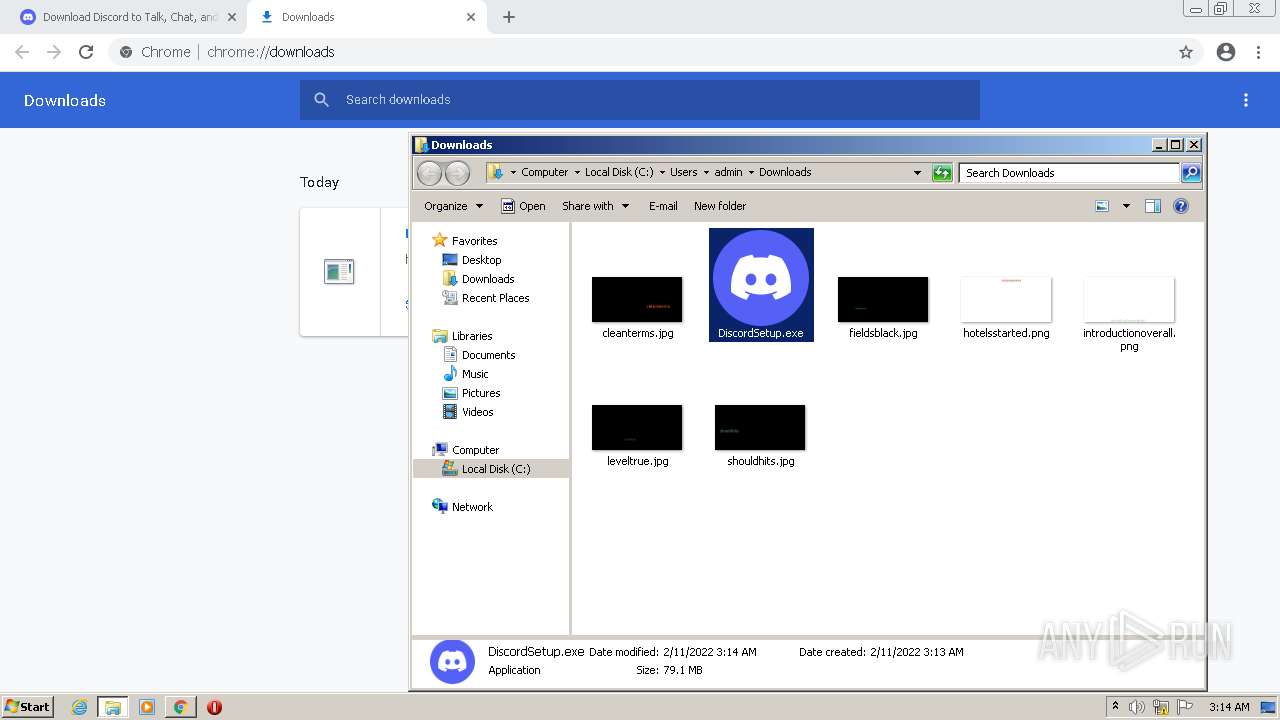
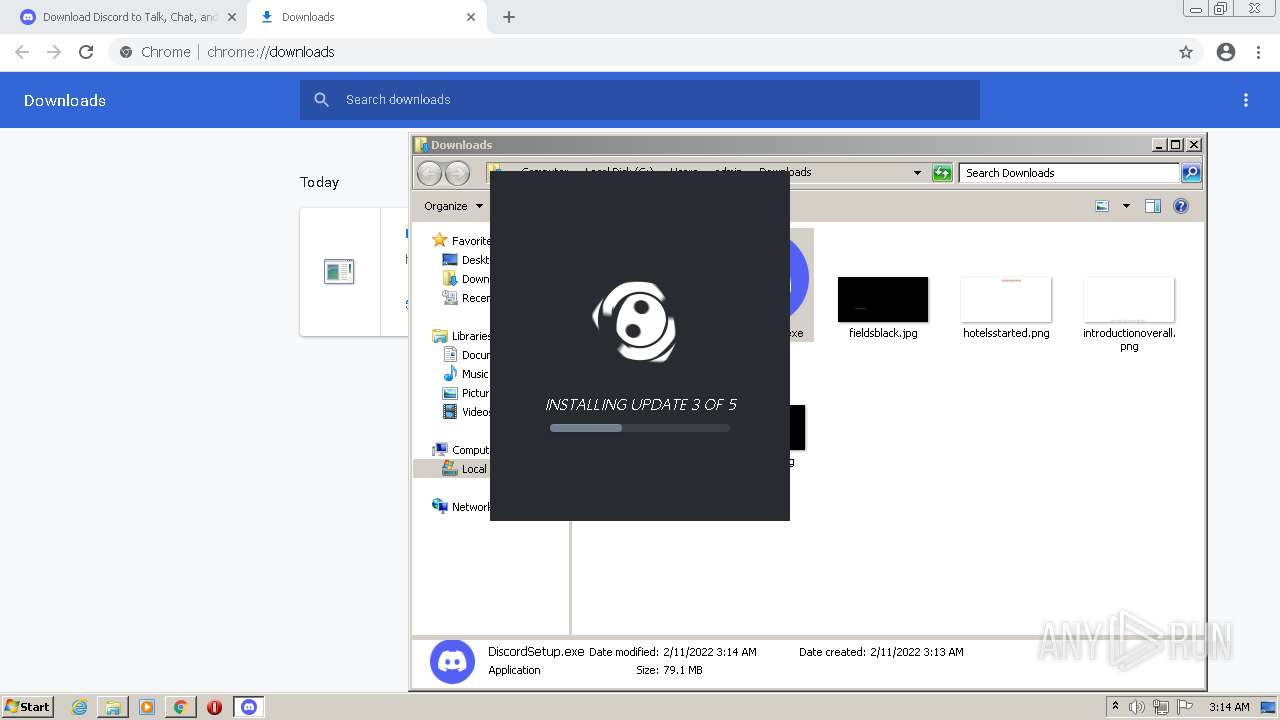
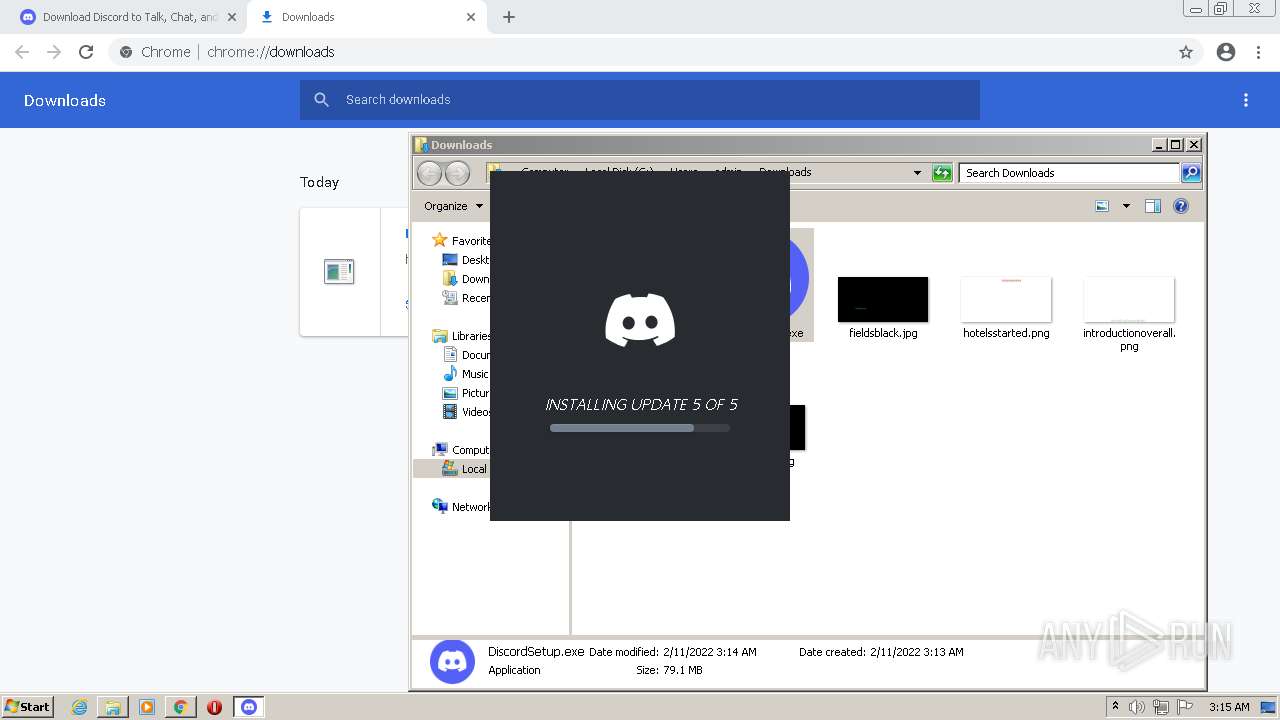
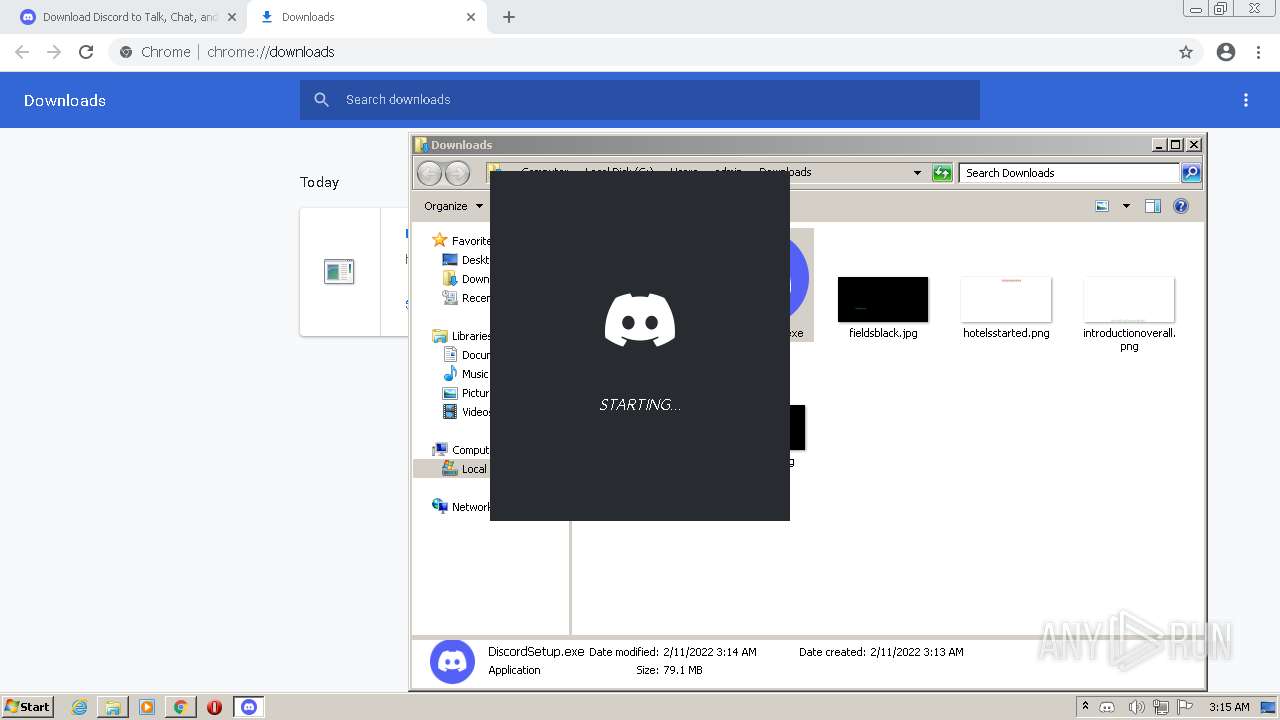
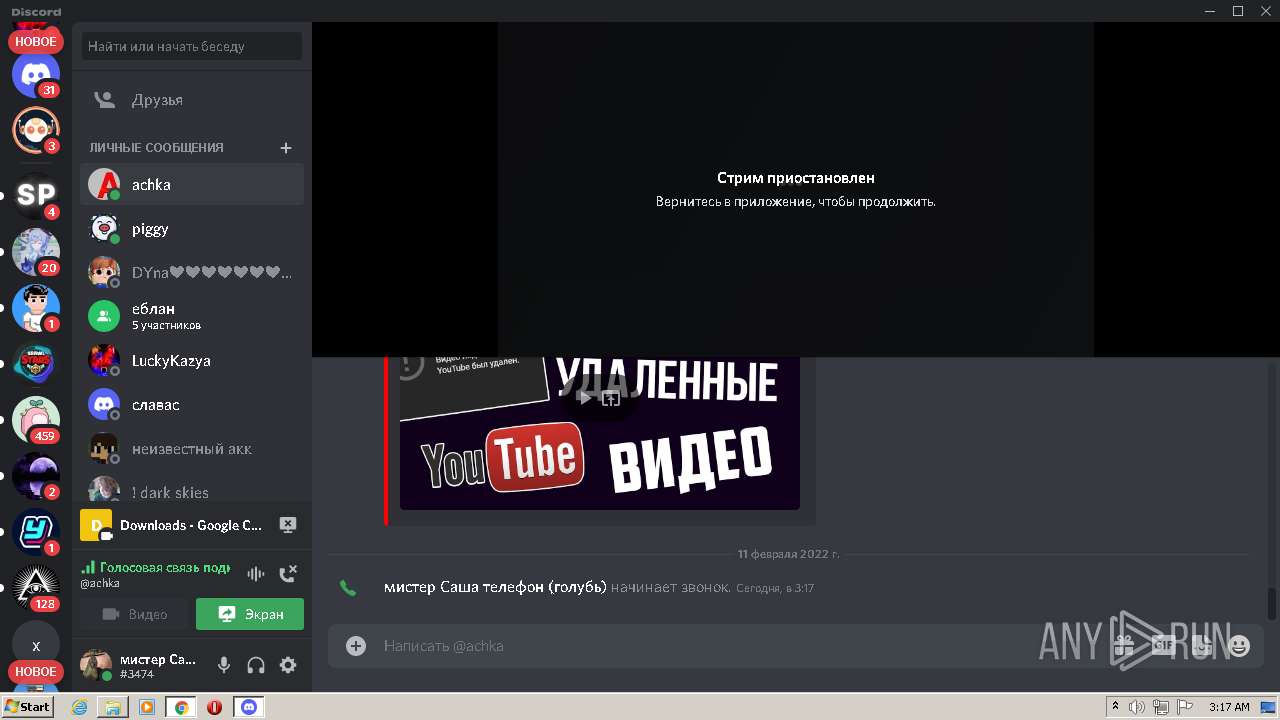
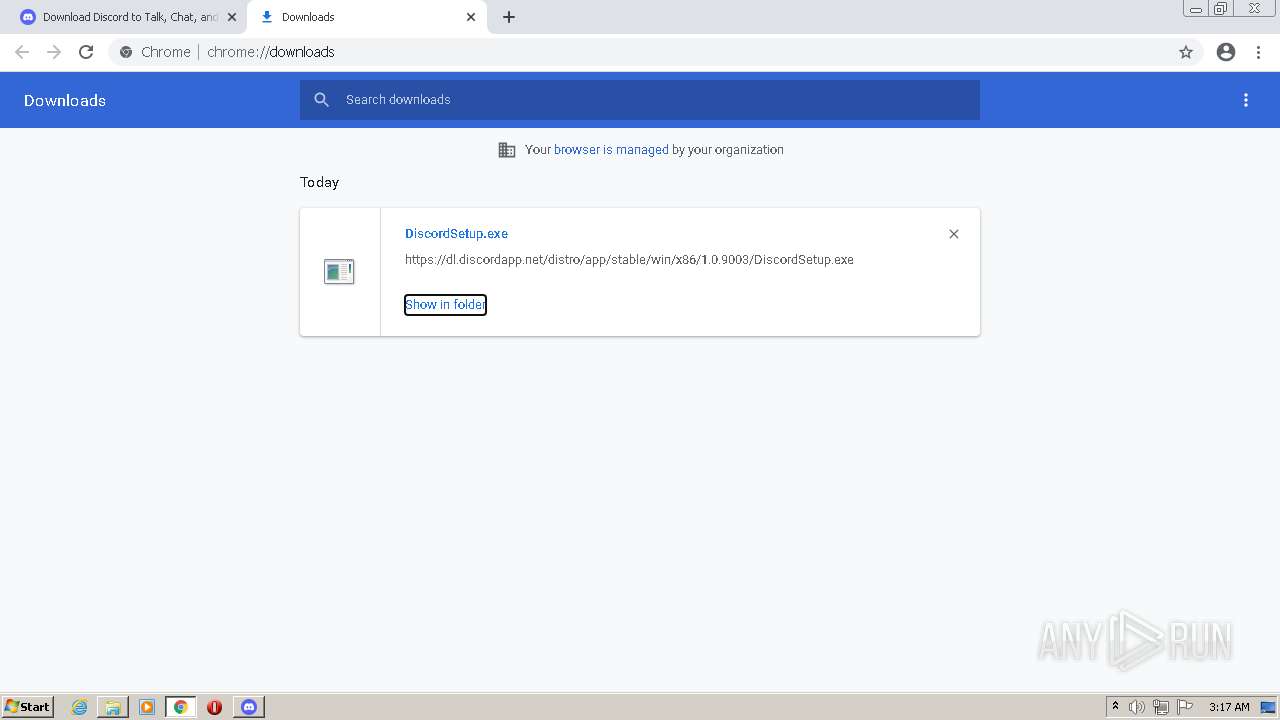
| URL: | https://discord.com/download |
| Full analysis: | https://app.any.run/tasks/cde3232d-d99c-482c-8702-5fb1a3a99fa4 |
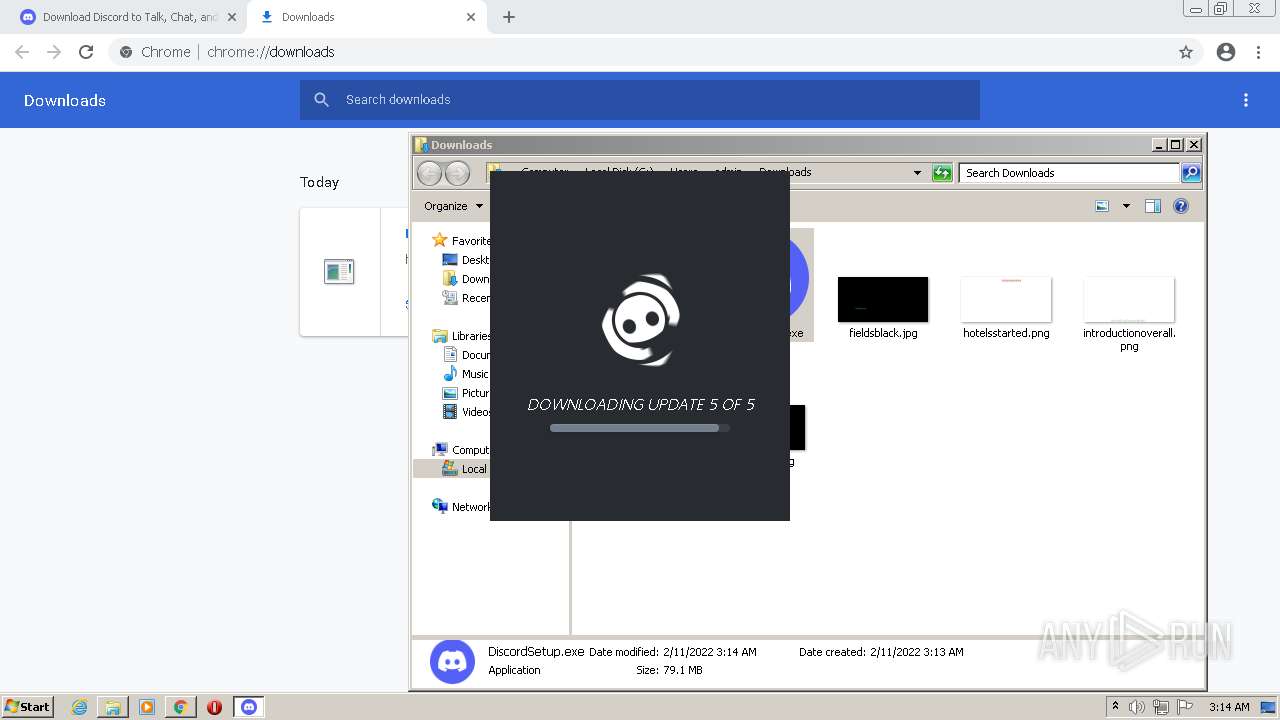
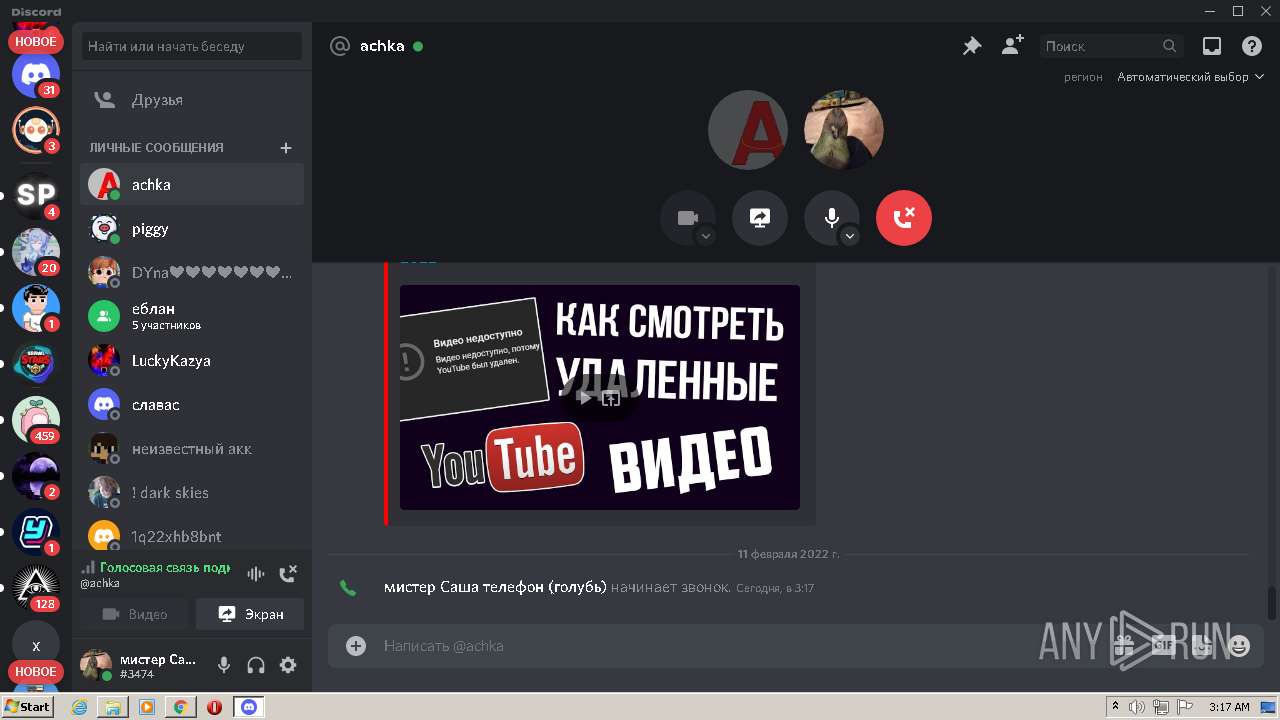
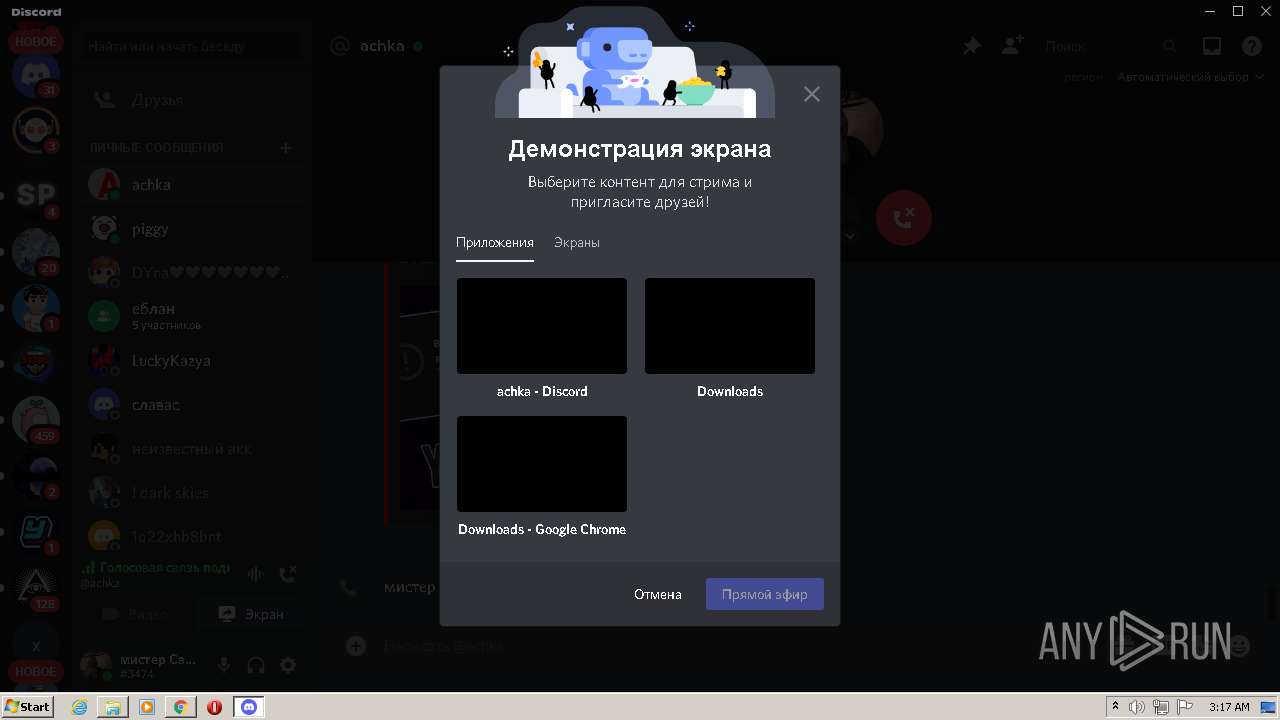
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2022, 03:13:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D6DE219245C31C782275DD186846A4CE |
| SHA1: | 0243022D6B47DD49CCD65FBCCE333807A123D103 |
| SHA256: | 903F001BC99F5017AF8C8FD2826D9E84A0B19D9B1AA420BC5DDB6257C27BB000 |
| SSDEEP: | 3:N8U8XkTBM:2UtM |
MALICIOUS
Application was dropped or rewritten from another process
- DiscordSetup.exe (PID: 300)
- Update.exe (PID: 3228)
- DiscordSetup.exe (PID: 3032)
- Update.exe (PID: 3608)
Changes the autorun value in the registry
- DiscordSetup.exe (PID: 300)
- reg.exe (PID: 2104)
- reg.exe (PID: 1536)
Drops executable file immediately after starts
- Update.exe (PID: 3228)
- chrome.exe (PID: 2772)
Loads dropped or rewritten executable
- Discord.exe (PID: 460)
- Discord.exe (PID: 576)
- Discord.exe (PID: 3092)
- Discord.exe (PID: 2804)
- Discord.exe (PID: 2480)
- Discord.exe (PID: 3200)
- Discord.exe (PID: 3488)
- Discord.exe (PID: 448)
- Discord.exe (PID: 368)
- Discord.exe (PID: 2596)
- Discord.exe (PID: 2288)
- Discord.exe (PID: 3160)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 3660)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2880)
- Update.exe (PID: 3228)
- DiscordSetup.exe (PID: 3032)
- Discord.exe (PID: 2804)
- chrome.exe (PID: 2772)
Reads the computer name
- DiscordSetup.exe (PID: 300)
- Update.exe (PID: 3228)
- Discord.exe (PID: 460)
- Update.exe (PID: 3608)
- Discord.exe (PID: 3092)
- Discord.exe (PID: 2804)
- Discord.exe (PID: 3200)
- Discord.exe (PID: 3488)
- Discord.exe (PID: 368)
- Discord.exe (PID: 2596)
- Discord.exe (PID: 2288)
- DiscordHookHelper.exe (PID: 3052)
- DiscordHookHelper.exe (PID: 4032)
Checks supported languages
- DiscordSetup.exe (PID: 3032)
- Update.exe (PID: 3228)
- DiscordSetup.exe (PID: 300)
- Discord.exe (PID: 460)
- Discord.exe (PID: 576)
- Discord.exe (PID: 3092)
- Update.exe (PID: 3608)
- Discord.exe (PID: 2804)
- Discord.exe (PID: 2480)
- Discord.exe (PID: 3200)
- Discord.exe (PID: 448)
- Discord.exe (PID: 3488)
- Discord.exe (PID: 368)
- Discord.exe (PID: 2596)
- Discord.exe (PID: 2288)
- cmd.exe (PID: 4080)
- Discord.exe (PID: 3160)
- DiscordHookHelper.exe (PID: 3052)
- DiscordHookHelper.exe (PID: 4032)
Creates files in the program directory
- DiscordSetup.exe (PID: 300)
Drops a file that was compiled in debug mode
- Update.exe (PID: 3228)
- Discord.exe (PID: 2804)
- chrome.exe (PID: 2772)
Drops a file with a compile date too recent
- Update.exe (PID: 3228)
- Discord.exe (PID: 2804)
Reads Environment values
- Discord.exe (PID: 460)
- Discord.exe (PID: 2804)
- Discord.exe (PID: 2596)
Application launched itself
- Discord.exe (PID: 460)
- Discord.exe (PID: 2804)
Creates files in the user directory
- Discord.exe (PID: 460)
- Discord.exe (PID: 576)
- Discord.exe (PID: 2804)
- Update.exe (PID: 3608)
- Discord.exe (PID: 2596)
- Discord.exe (PID: 3488)
Changes default file association
- reg.exe (PID: 3884)
- reg.exe (PID: 2820)
Creates a software uninstall entry
- Update.exe (PID: 3228)
Uses REG.EXE to modify Windows registry
- Discord.exe (PID: 2804)
- Discord.exe (PID: 460)
Reads CPU info
- Discord.exe (PID: 2596)
Starts CMD.EXE for commands execution
- Discord.exe (PID: 2596)
INFO
Reads the computer name
- chrome.exe (PID: 2880)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 940)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 1132)
- chrome.exe (PID: 872)
- WISPTIS.EXE (PID: 876)
- chrome.exe (PID: 3660)
Checks supported languages
- chrome.exe (PID: 872)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 1988)
- chrome.exe (PID: 4040)
- chrome.exe (PID: 1132)
- chrome.exe (PID: 2104)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 940)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 4064)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 3872)
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 3864)
- WISPTIS.EXE (PID: 876)
- reg.exe (PID: 2104)
- reg.exe (PID: 2760)
- reg.exe (PID: 2532)
- reg.exe (PID: 2620)
- reg.exe (PID: 3884)
- reg.exe (PID: 1068)
- reg.exe (PID: 476)
- reg.exe (PID: 488)
- reg.exe (PID: 2820)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 2772)
- chrome.exe (PID: 3684)
- chrome.exe (PID: 1080)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 2588)
- chrome.exe (PID: 4008)
- chrome.exe (PID: 2984)
- chrome.exe (PID: 2444)
- reg.exe (PID: 2416)
- reg.exe (PID: 1536)
- chrome.exe (PID: 3660)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 3660)
Reads the hosts file
- chrome.exe (PID: 2880)
- chrome.exe (PID: 872)
- Discord.exe (PID: 460)
- Discord.exe (PID: 2804)
- Discord.exe (PID: 3488)
Reads settings of System Certificates
- chrome.exe (PID: 872)
- chrome.exe (PID: 2880)
- Discord.exe (PID: 2804)
- DiscordHookHelper.exe (PID: 4032)
- DiscordHookHelper.exe (PID: 3052)
- Discord.exe (PID: 2596)
Application launched itself
- chrome.exe (PID: 2880)
Reads the date of Windows installation
- chrome.exe (PID: 2792)
Checks Windows Trust Settings
- chrome.exe (PID: 2880)
- Discord.exe (PID: 2596)
- DiscordHookHelper.exe (PID: 3052)
- DiscordHookHelper.exe (PID: 4032)
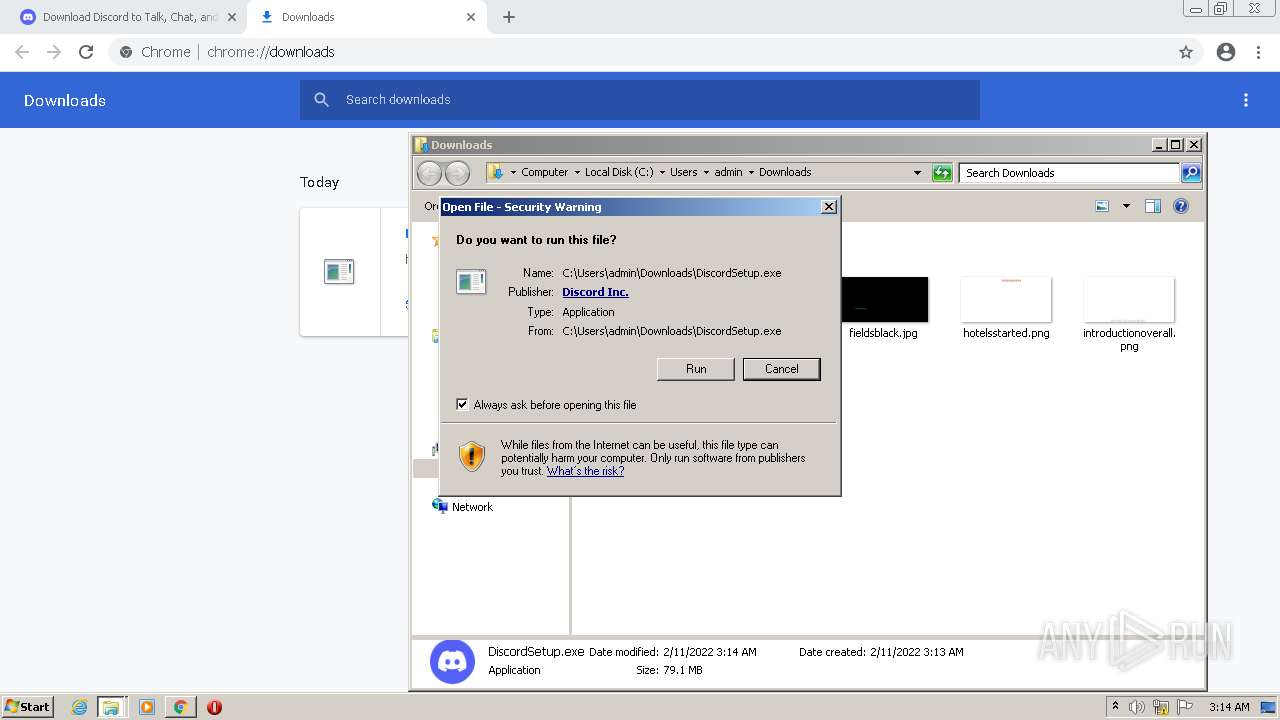
Manual execution by user
- DiscordSetup.exe (PID: 300)
- DiscordSetup.exe (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
62
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
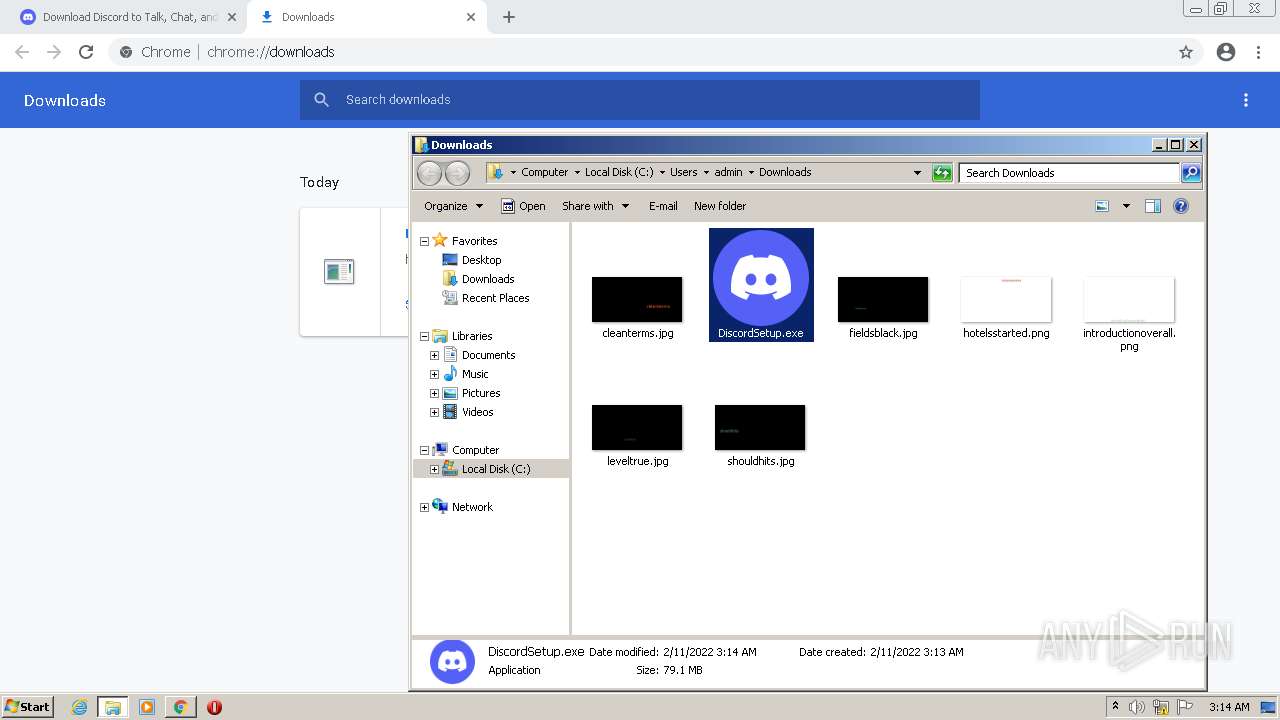
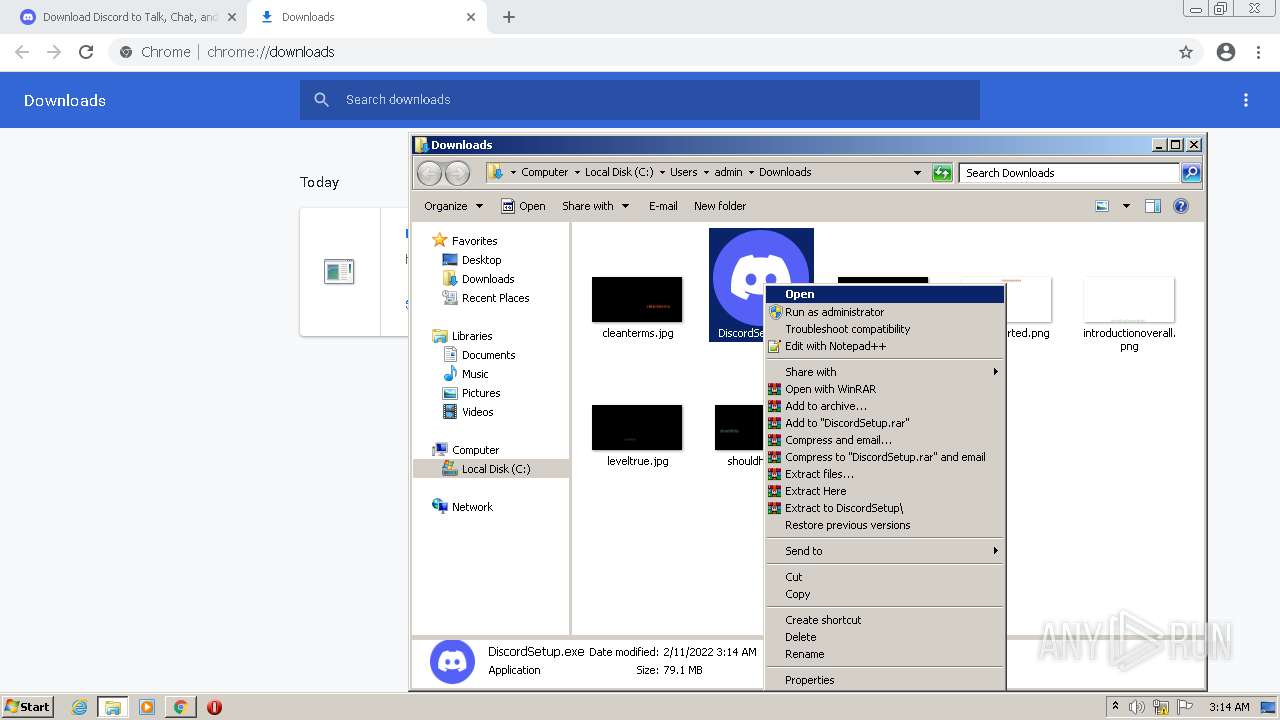
| 300 | "C:\Users\admin\Downloads\DiscordSetup.exe" | C:\Users\admin\Downloads\DiscordSetup.exe | Explorer.EXE | ||||||||||||
User: admin Company: Discord Inc. Integrity Level: HIGH Description: Discord - https://discord.com/ Exit code: 0 Version: 1.0.9003 Modules
| |||||||||||||||
| 368 | "C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe" --type=gpu-process --field-trial-handle=1032,12174891301984265469,15263379958152935905,131072 --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand --gpu-preferences=SAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAoAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAB4AAAAAAAAAHgAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAAIAAAAAAAAAAgAAAAAAAAA --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: LOW Description: Discord Exit code: 0 Version: 1.0.9003 Modules
| |||||||||||||||
| 448 | "C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe" --type=renderer --autoplay-policy=no-user-gesture-required --field-trial-handle=1032,12174891301984265469,15263379958152935905,131072 --disable-features=CookiesWithoutSameSiteMustBeSecure,SameSiteByDefaultCookies,SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand --lang=en-US --app-user-model-id=com.squirrel.Discord.Discord --app-path="C:\Users\admin\AppData\Local\Discord\app-1.0.9003\resources\app.asar" --no-sandbox --no-zygote --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1692 /prefetch:1 | C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 1.0.9003 Modules
| |||||||||||||||
| 460 | "C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe" --squirrel-install 1.0.9003 | C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe | — | Update.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 1.0.9003 Modules
| |||||||||||||||
| 476 | C:\Windows\System32\reg.exe add HKCU\Software\Classes\Discord /v "URL Protocol" /f | C:\Windows\System32\reg.exe | — | Discord.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 488 | C:\Windows\System32\reg.exe add HKCU\Software\Classes\Discord\DefaultIcon /ve /d "\"C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe\",-1" /f | C:\Windows\System32\reg.exe | — | Discord.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 576 | C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\discord /prefetch:7 --no-rate-limit --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\discord\Crashpad --url=https://sentry.io/api/146342/minidump/?sentry_key=384ce4413de74fe0be270abe03b2b35a "--annotation=_companyName=Discord Inc." --annotation=_productName=Discord --annotation=_version=1.0.9003 --annotation=prod=Electron --annotation=ver=13.4.0 --initial-client-data=0x2e8,0x2ec,0x2f0,0x2e4,0x2f4,0x6f08820,0x6f08830,0x6f0883c | C:\Users\admin\AppData\Local\Discord\app-1.0.9003\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: MEDIUM Description: Discord Exit code: 0 Version: 1.0.9003 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1036,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 876 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | Update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1616 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
35 133
Read events
34 841
Write events
287
Delete events
5
Modification events
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2880) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
46
Suspicious files
359
Text files
1 416
Unknown types
100
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6205D44E-B40.pma | — | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\75f690a5-6bd4-46fc-981a-7a2e699fe531.tmp | text | |
MD5:— | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF193677.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\93cc6b67-f8dc-4a55-97c4-16315a675e10.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2880 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
43
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | — | — | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 21.1 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 720 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 43.6 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 5.78 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 88.6 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 9.90 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/APhHMzuprJvS7ixvnAk_gdI_1/anGnv31dmOJhheXBnYQ3gw | US | binary | 19.9 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 1.10 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
872 | chrome.exe | 142.250.179.141:443 | accounts.google.com | Google Inc. | US | suspicious |
872 | chrome.exe | 162.159.128.233:443 | discord.com | Cloudflare Inc | — | malicious |
872 | chrome.exe | 142.250.179.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 216.58.208.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 142.251.39.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 142.251.36.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
872 | chrome.exe | 35.190.80.1:443 | a.nel.cloudflare.com | Google Inc. | US | suspicious |
872 | chrome.exe | 8.253.208.113:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
3488 | Discord.exe | 142.250.179.206:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3488 | Discord.exe | 74.125.162.199:443 | r2---sn-4g5ednds.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
discord.com |
| whitelisted |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
dl.discordapp.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
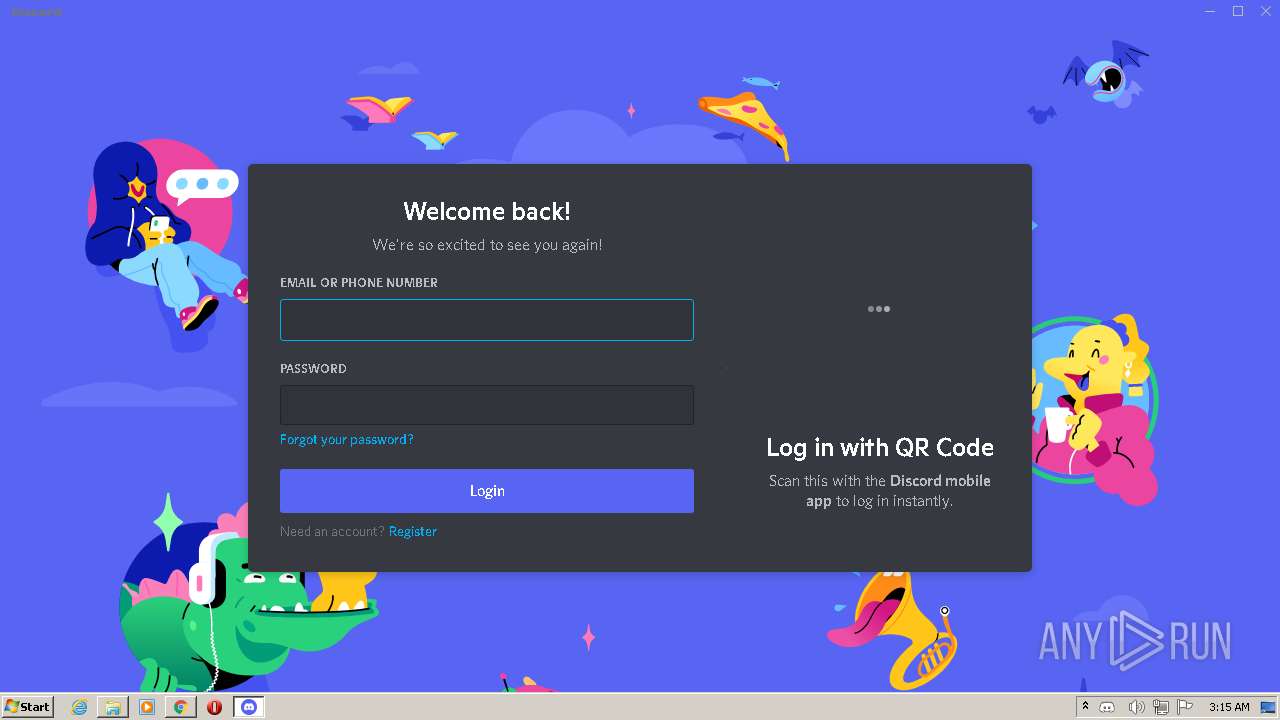
DiscordSetup.exe | Start up installer: |
DiscordSetup.exe | Elevated process: ?s?
|
DiscordSetup.exe | Want machine install |
DiscordSetup.exe | we are UAC elevated, so restart C:\Users\admin\Downloads\DiscordSetup.exe,
|
DiscordSetup.exe | Start up installer: |
DiscordSetup.exe | Elevated process: ?
|
DiscordSetup.exe | Want standard install |
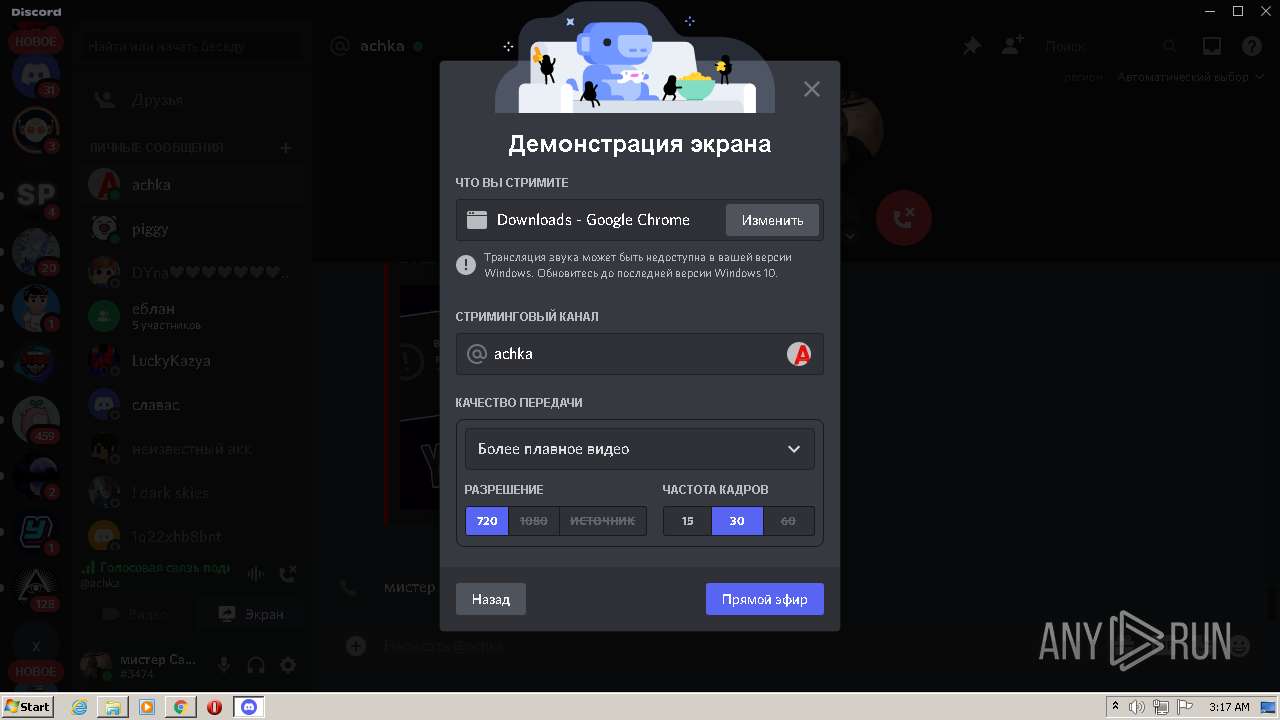
Discord.exe | [2022-02-11 03:17:10.723] [364] (audio_send_stream.cc:344): Failed to set up send codec state.
|
Discord.exe | [2022-02-11 03:17:10.765] [364] (audio_send_stream.cc:344): Failed to set up send codec state.
|
Discord.exe | [2022-02-11 03:17:10.784] [364] (audio_device_core_win.cc:3475): Attempt to set Windows AEC with recording already initialized
|