| File name: | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4 |
| Full analysis: | https://app.any.run/tasks/2e3beae7-3fed-4ea0-b4f1-74c7f659e415 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 08:44:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 124A2DBD068FF5C324EBABA9F5E3B43C |
| SHA1: | A933DA52B3F7271E03BCC47E7FAFE6099209F620 |
| SHA256: | 902D2826CAD7AEF31B635D0B3909C09853592BFE0BF935137416B946849E46B4 |
| SSDEEP: | 12288:9rMIztyCK5x8CBmn+RrNbEyWYa0Ie1vUx9Vw:7ZyCA8CBmn+RrNj9ay5Iw |
MALICIOUS
Writes to a start menu file
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 3424)
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 2576)
SUSPICIOUS
Creates files in the user directory
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 3424)
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 2576)
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 3088)
Removes files from Windows directory
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 2576)
Creates files in the Windows directory
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 2576)
Executable content was dropped or overwritten
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 2576)
- 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe (PID: 3088)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (31.9) |
|---|---|---|
| .scr | | | Windows screen saver (29.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (14.8) |
| .exe | | | Win32 Executable (generic) (10.1) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:08:26 11:37:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 461824 |
| InitializedDataSize: | 71168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x72814 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 26-Aug-2011 09:37:40 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 26-Aug-2011 09:37:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0007002C | 0x00070200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57497 |
.itext | 0x00072000 | 0x00000874 | 0x00000A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.69331 |
.data | 0x00073000 | 0x000024CC | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.31691 |
.bss | 0x00076000 | 0x00004CE8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0007B000 | 0x00002A64 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.10468 |
.tls | 0x0007E000 | 0x00000034 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0007F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.reloc | 0x00080000 | 0x00006630 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65867 |
.rsrc | 0x00087000 | 0x0000583C | 0x00005A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.49442 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.91814 | 850 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.80231 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4083 | 1.74878 | 64 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4084 | 3.34199 | 1036 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4085 | 3.46183 | 168 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
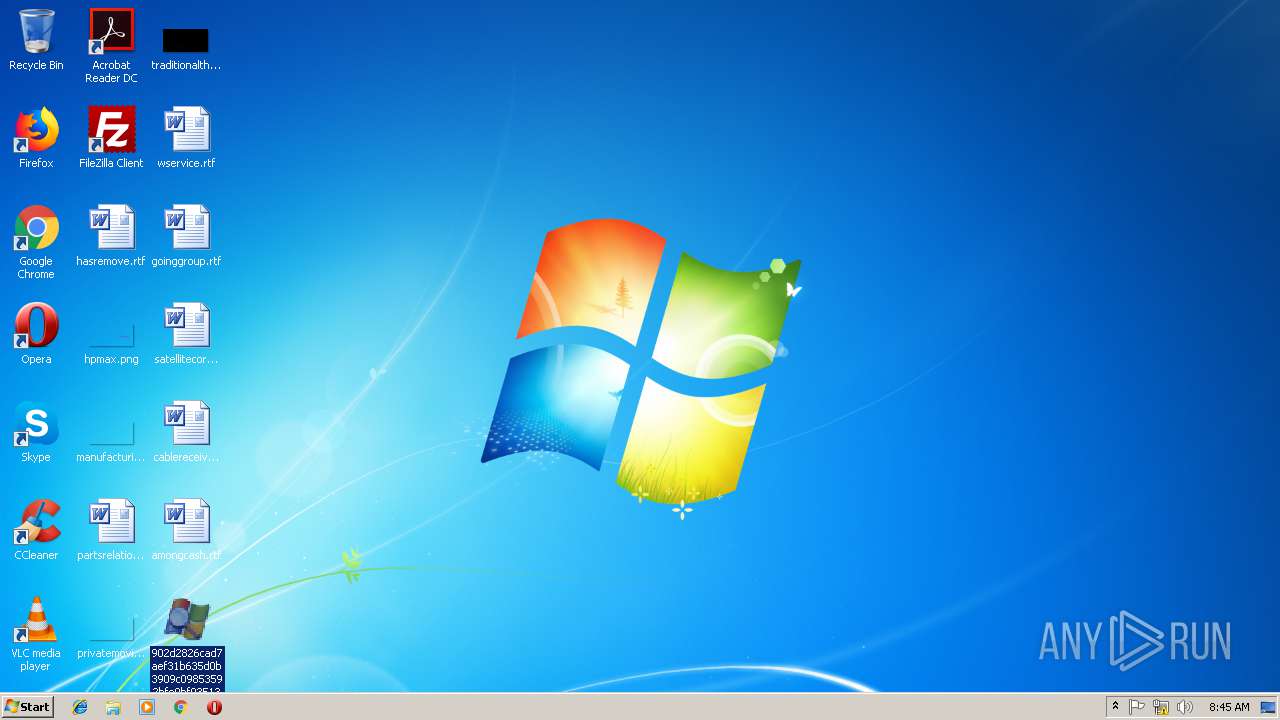
Total processes
36
Monitored processes
3
Malicious processes
1
Suspicious processes
0
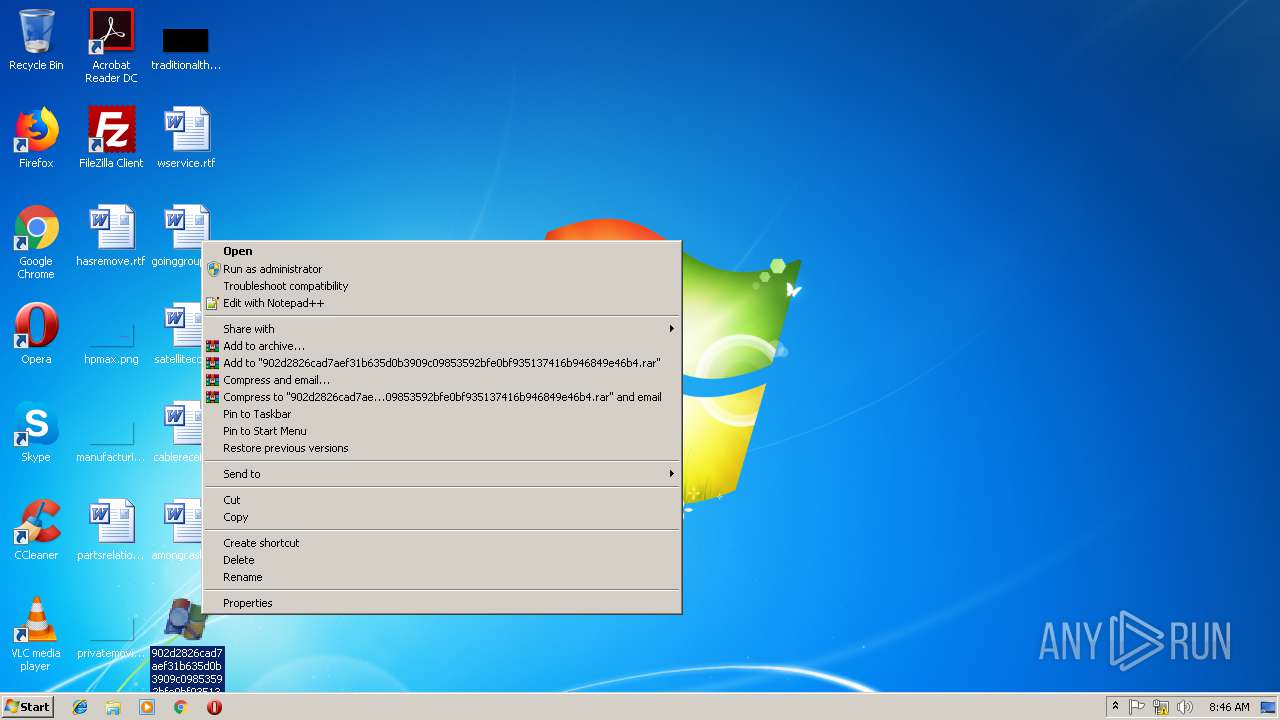
Behavior graph
Click at the process to see the details
Process information
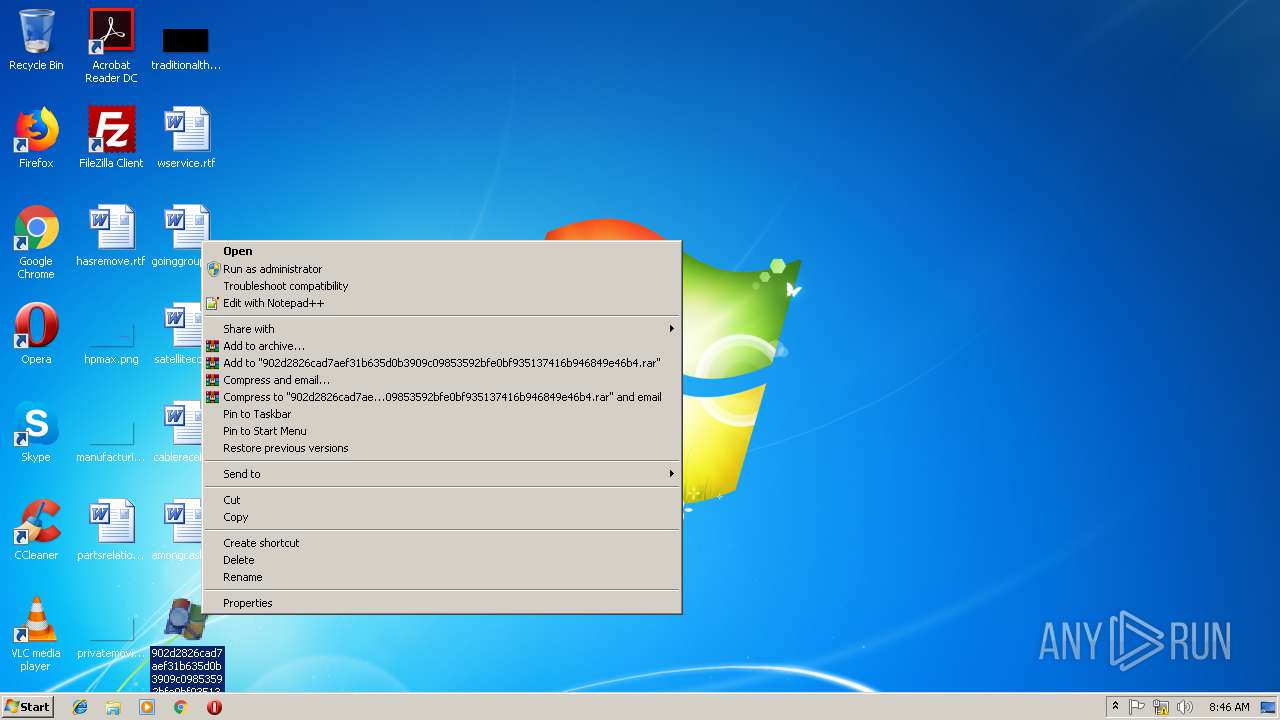
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2576 | "C:\Users\admin\Desktop\902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe" | C:\Users\admin\Desktop\902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3088 | "C:\Users\admin\Desktop\902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe" | C:\Users\admin\Desktop\902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3424 | "C:\Users\admin\Desktop\902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe" | C:\Users\admin\Desktop\902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
712
Read events
711
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2576) 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Ground |
| Operation: | write | Name: | Ground |
Value: 1 | |||
Executable files
20
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\gAlcrmv.ico | — | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\RCXE763.tmp | — | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\gSOUNDMAN.ico | — | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\RCXE774.tmp | — | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\Microsoft.NET\gNETFXRepair.ico | — | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\Microsoft.NET\RCXE7B4.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Ground.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Ground.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3088 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Users\admin\AppData\Roaming\Ground.exe | executable | |
MD5:— | SHA256:— | |||
| 2576 | 902d2826cad7aef31b635d0b3909c09853592bfe0bf935137416b946849e46b4.exe | C:\Windows\Microsoft.NET\assembly\GAC_MSIL\Microsoft.Workflow.Compiler\v4.0_4.0.0.0__31bf3856ad364e35\Microsoft.Workflow.Compiler.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report