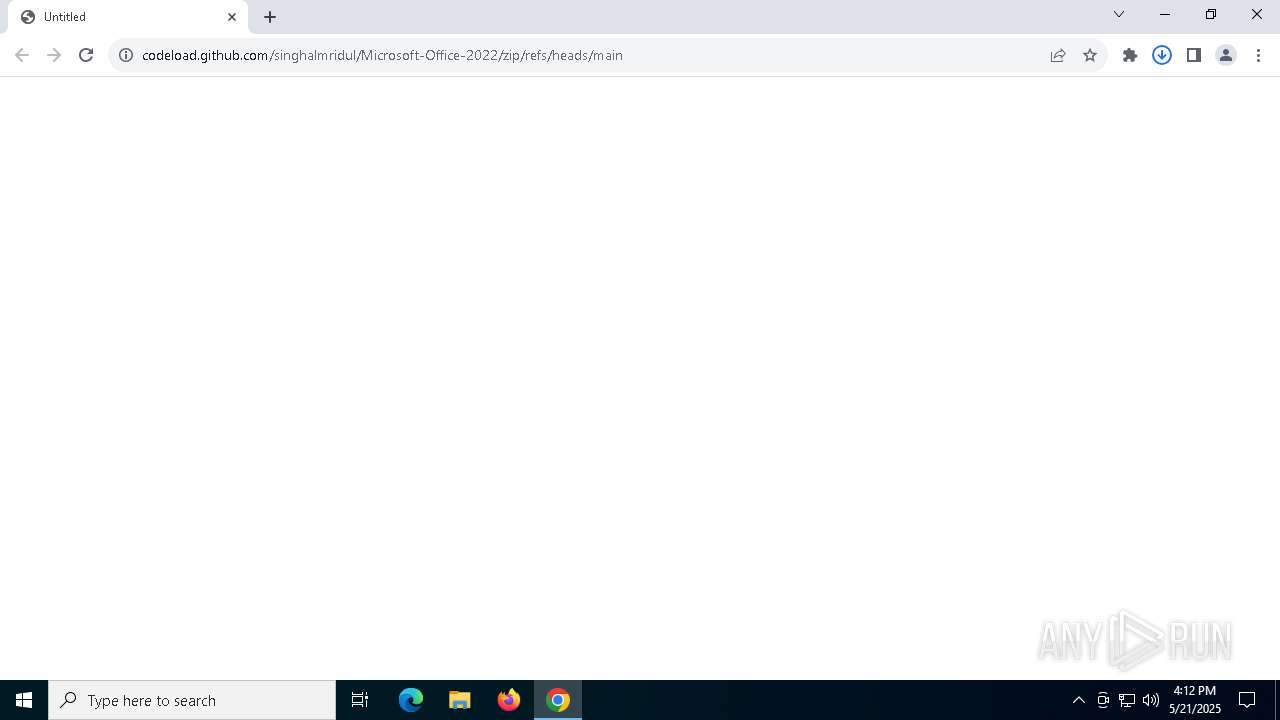
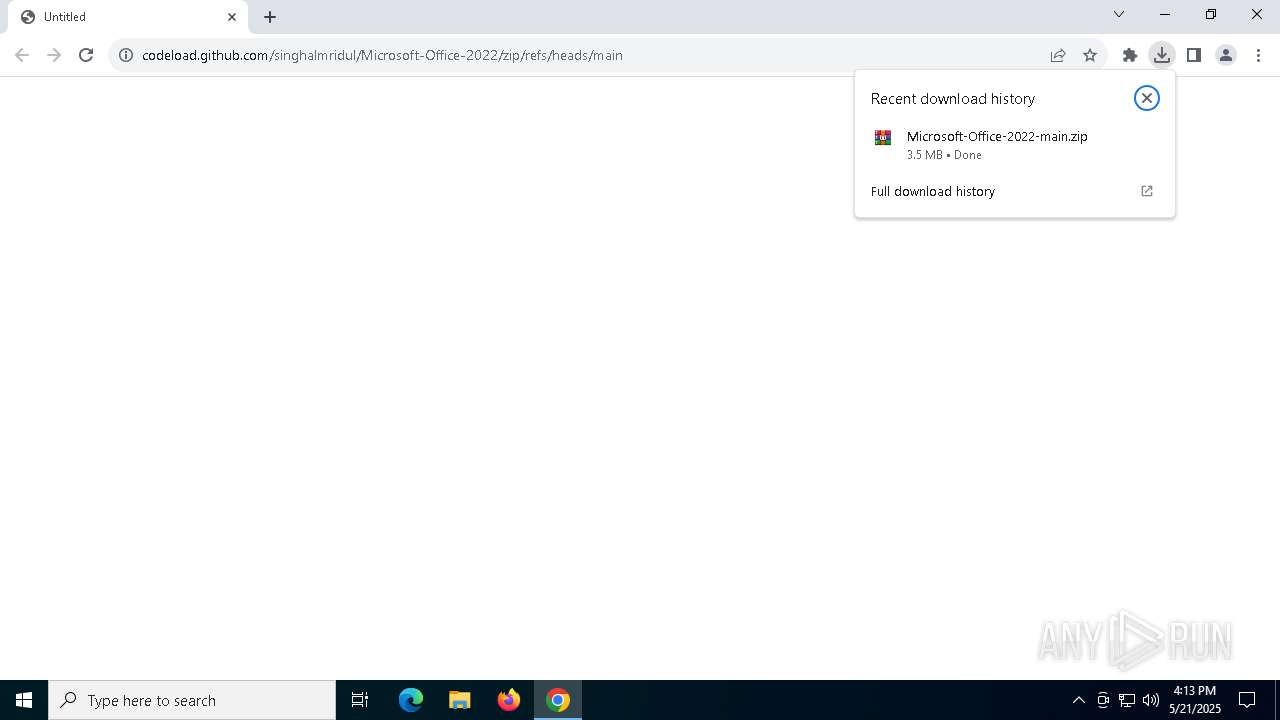
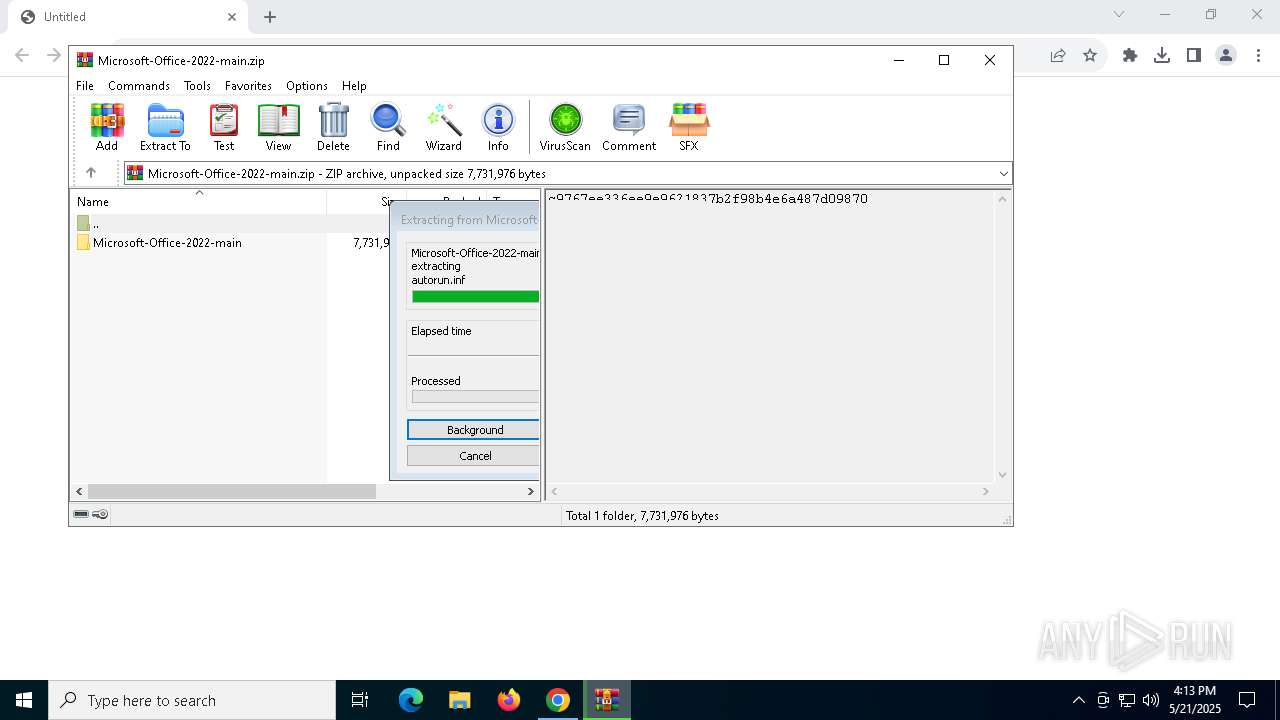
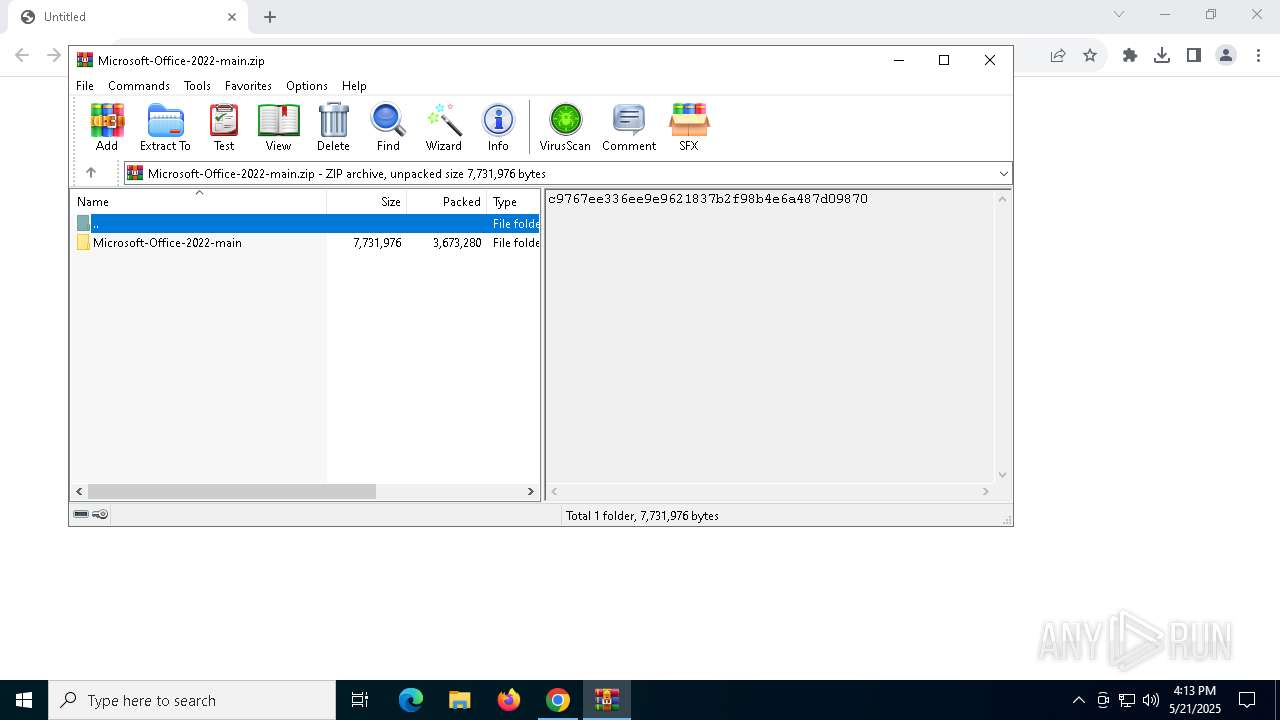
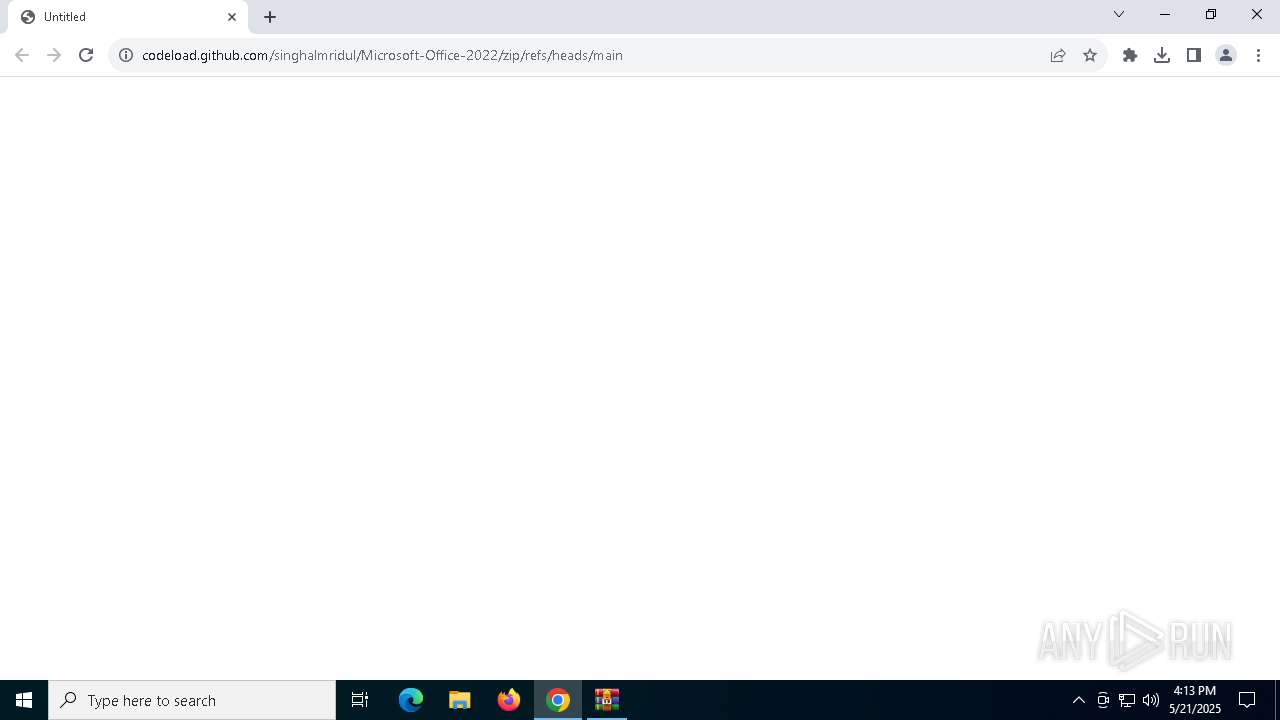
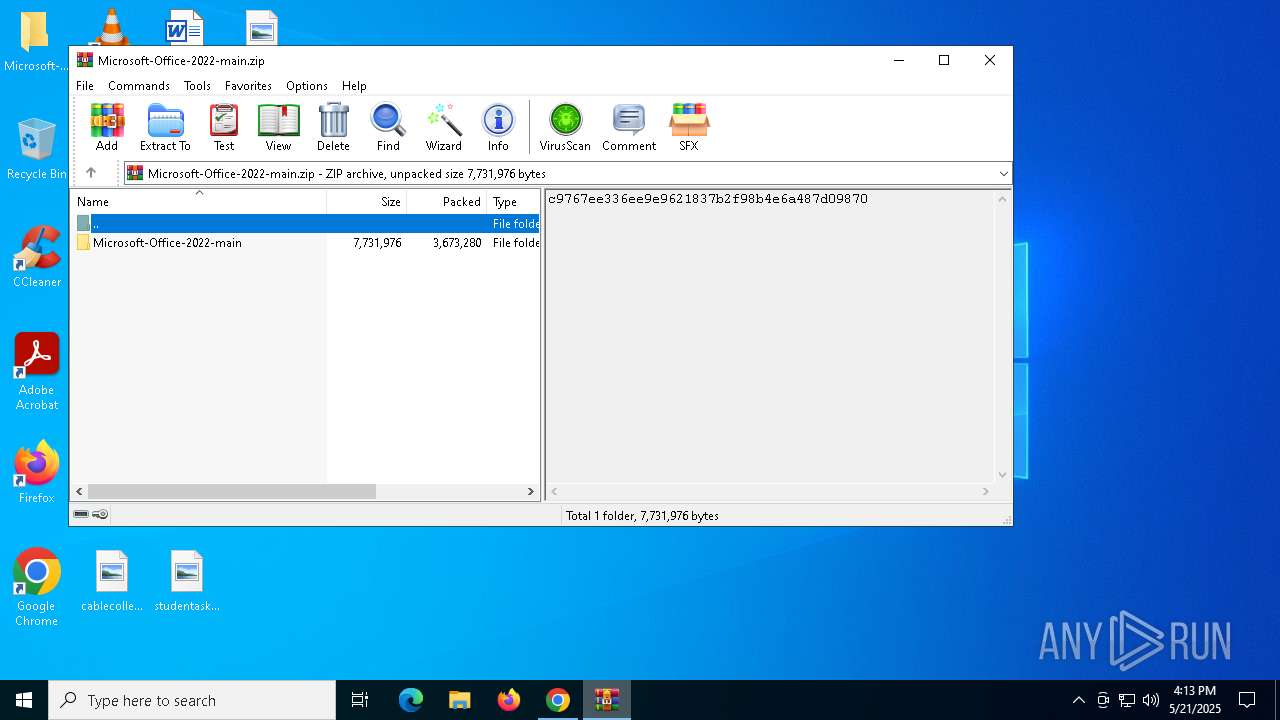
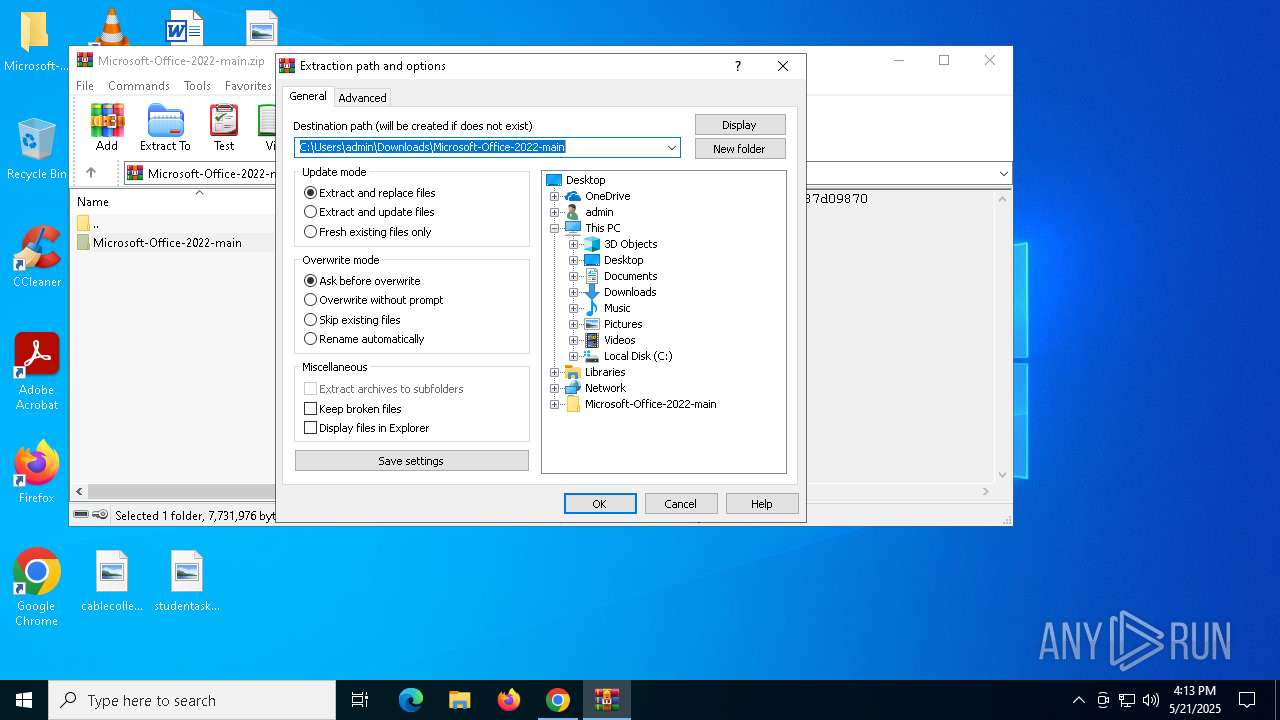
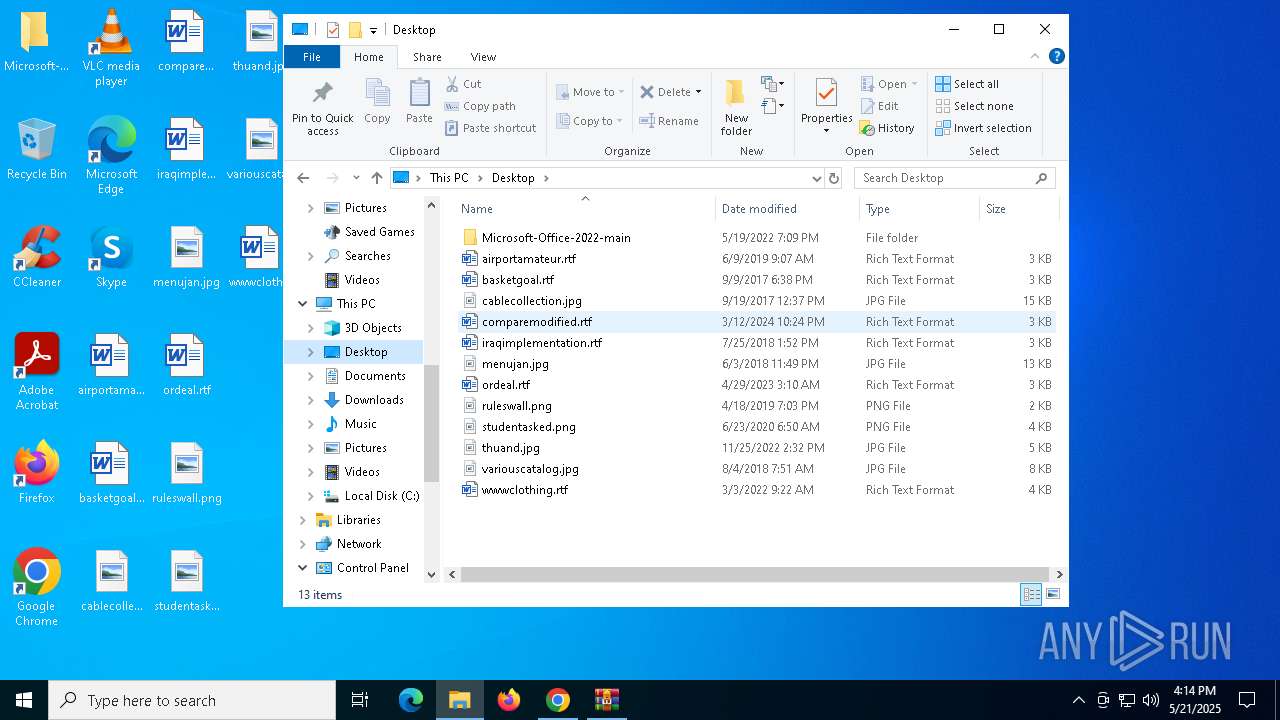
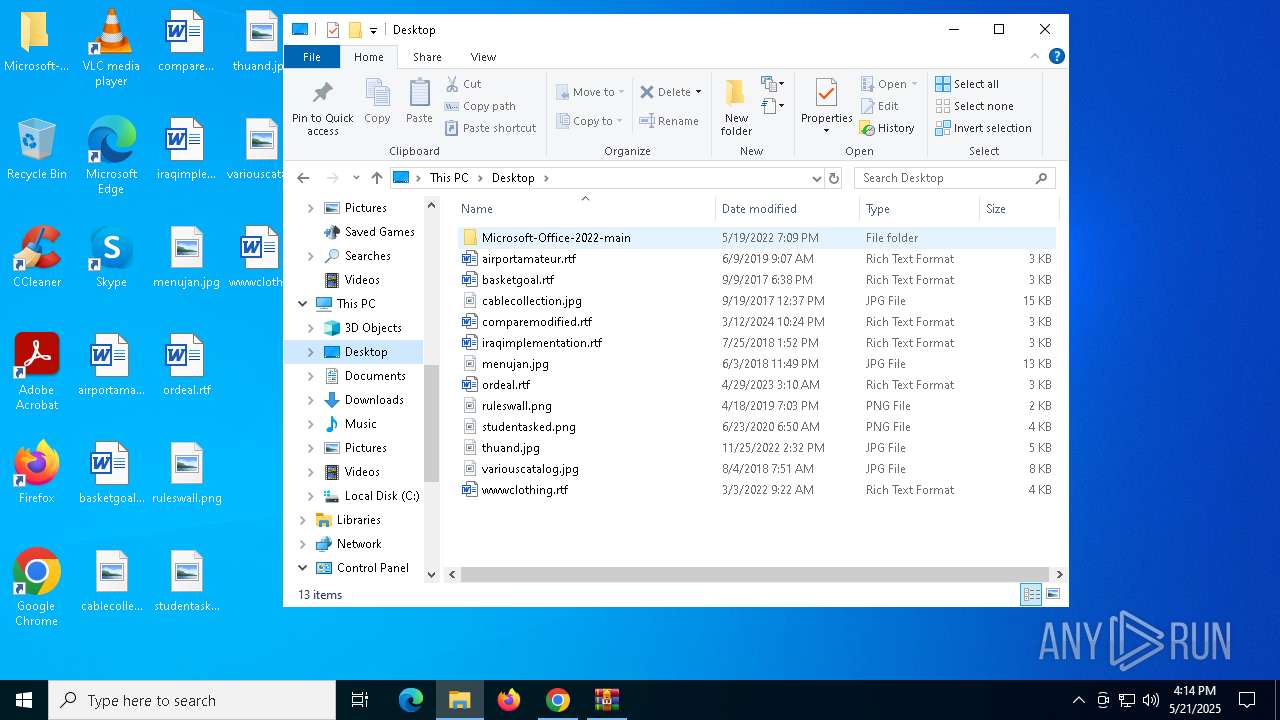
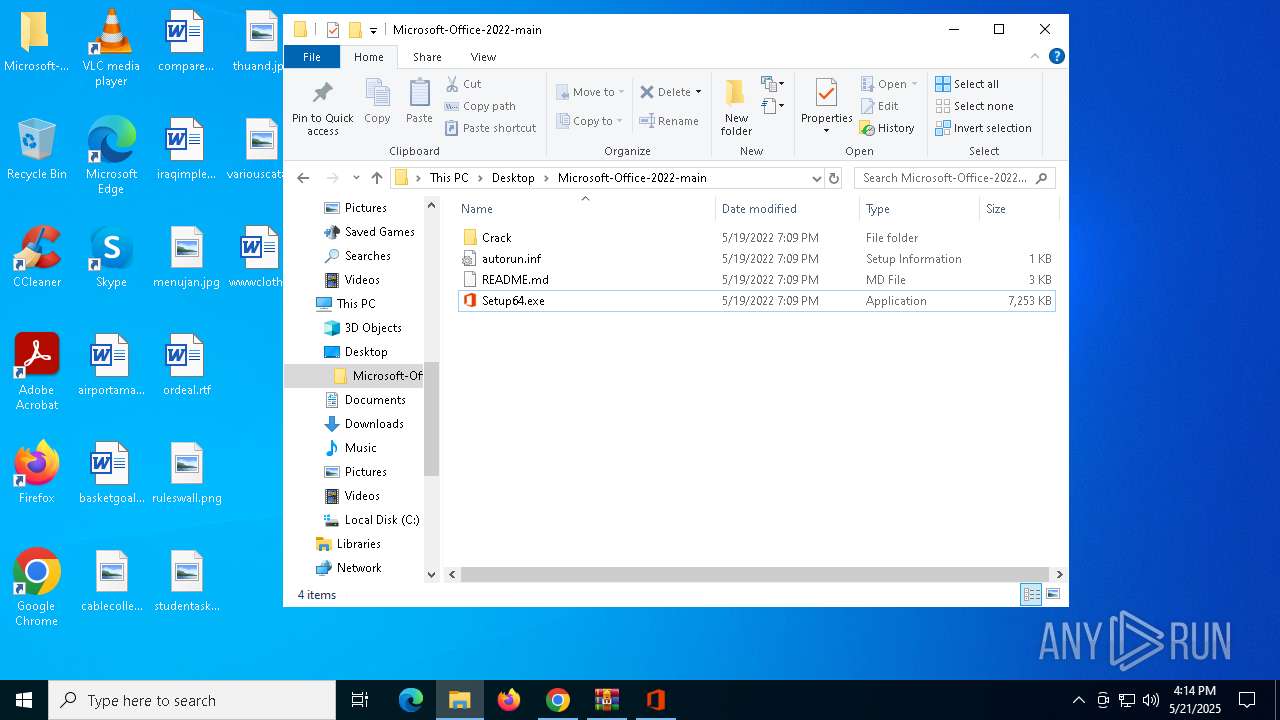
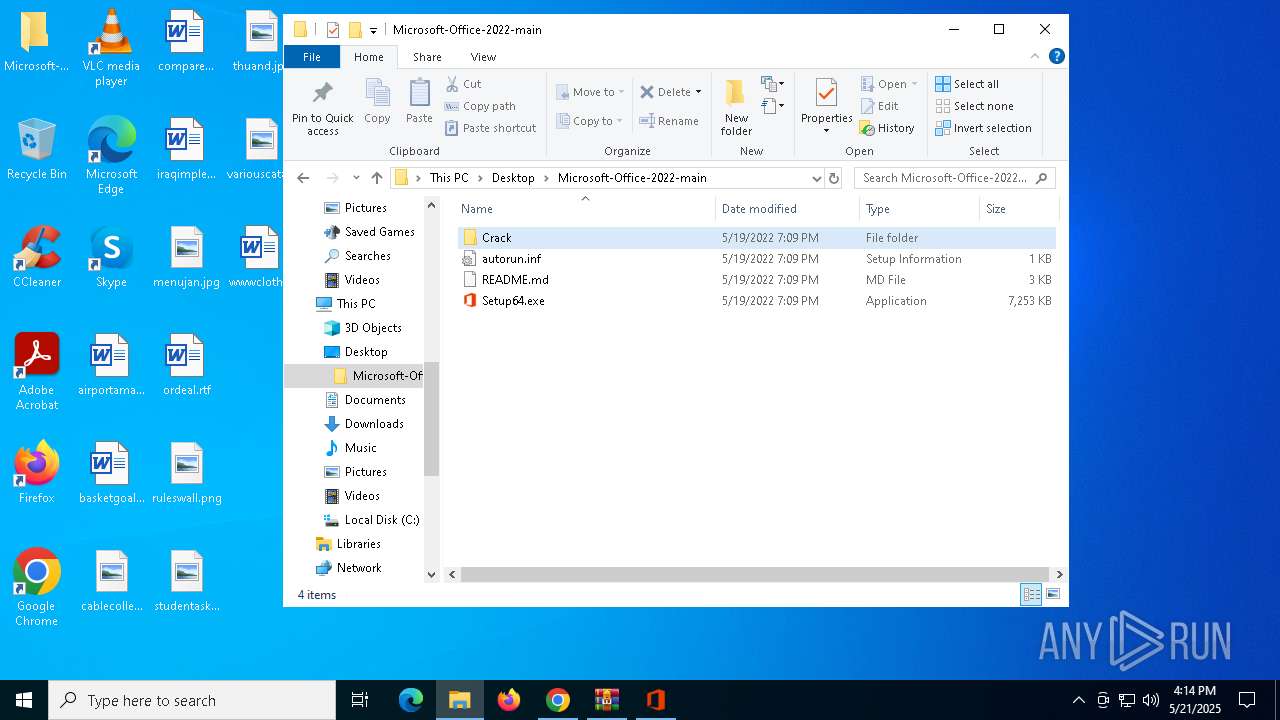
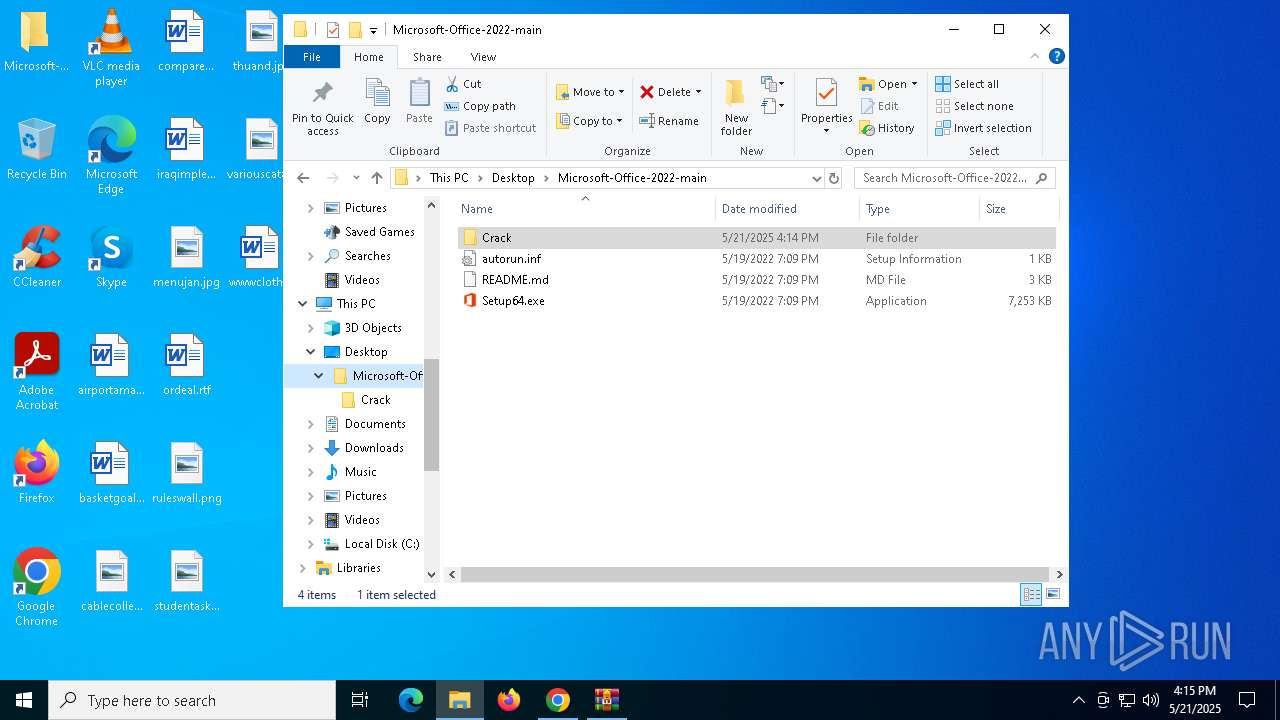
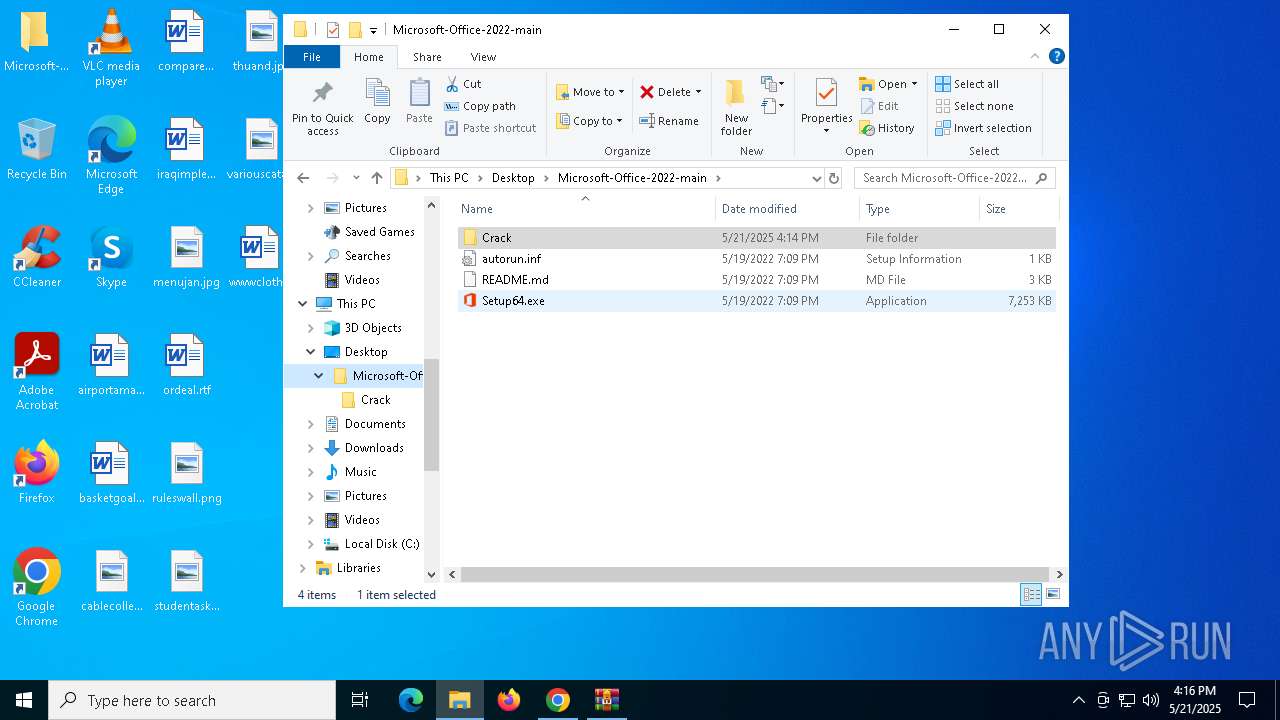
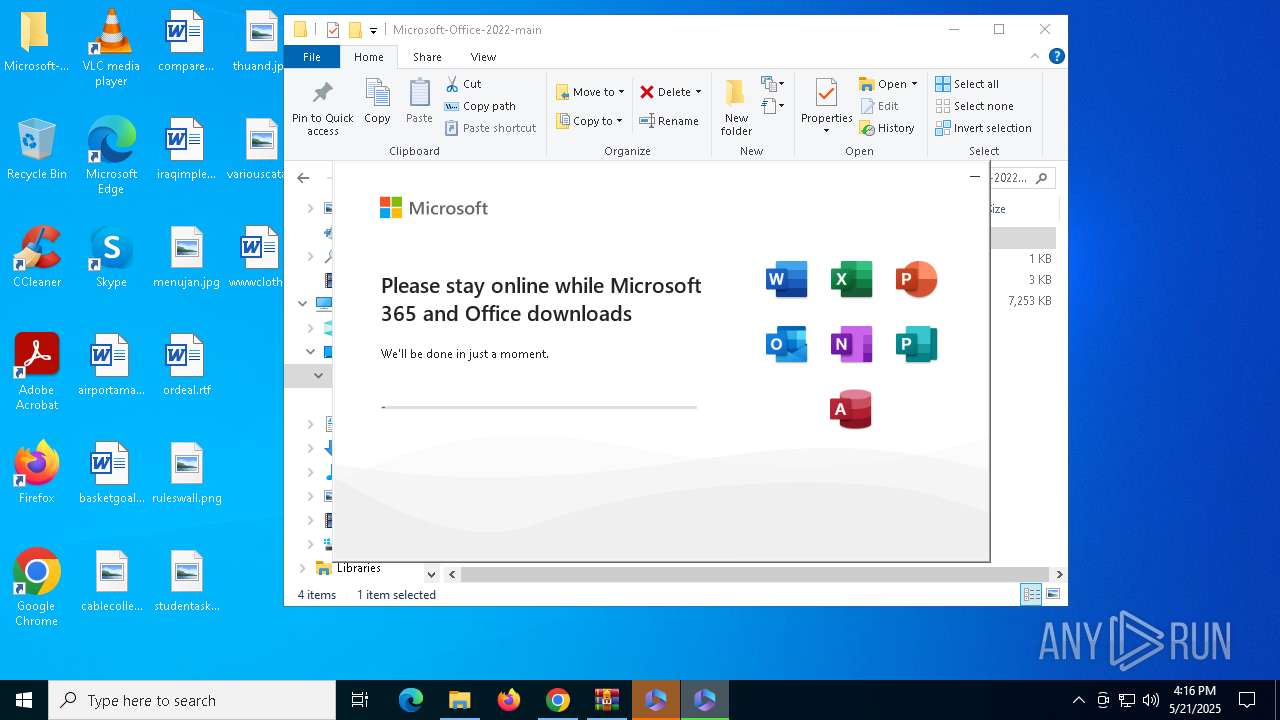
| URL: | https://codeload.github.com/singhalmridul/Microsoft-Office-2022/zip/refs/heads/main |
| Full analysis: | https://app.any.run/tasks/9e64c920-0a99-46f1-8520-1ffafe1fbe6a |
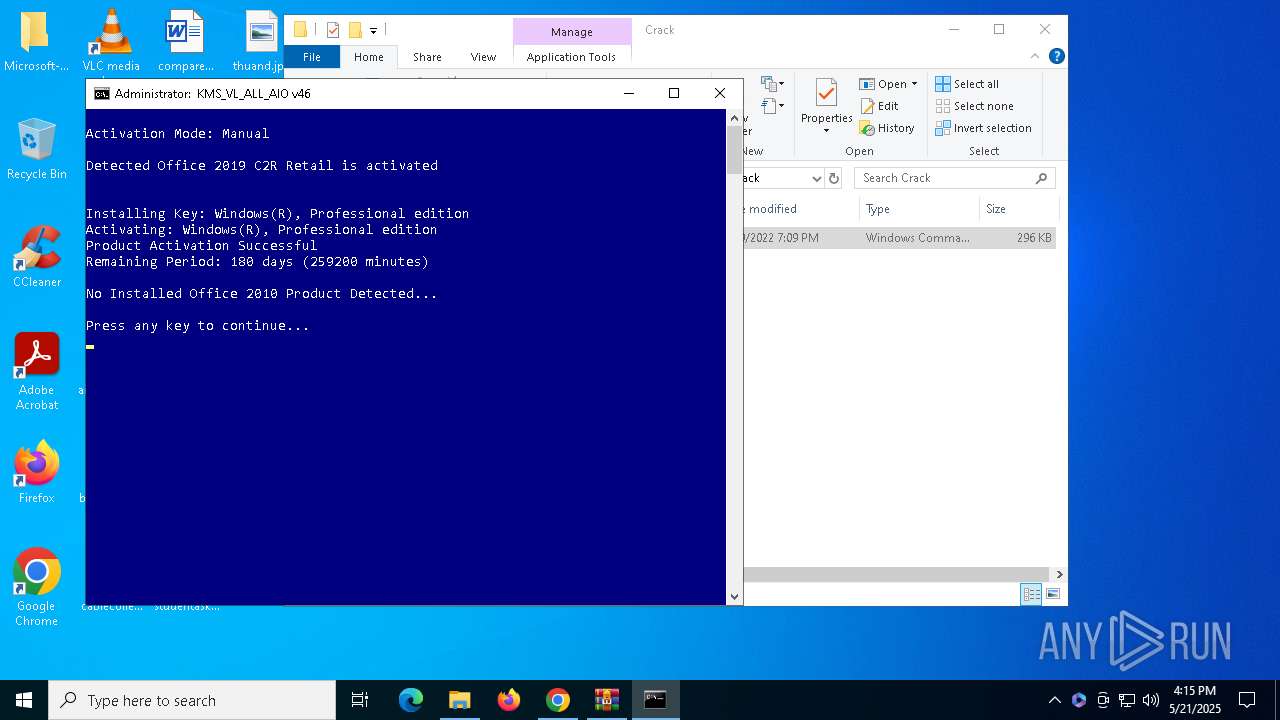
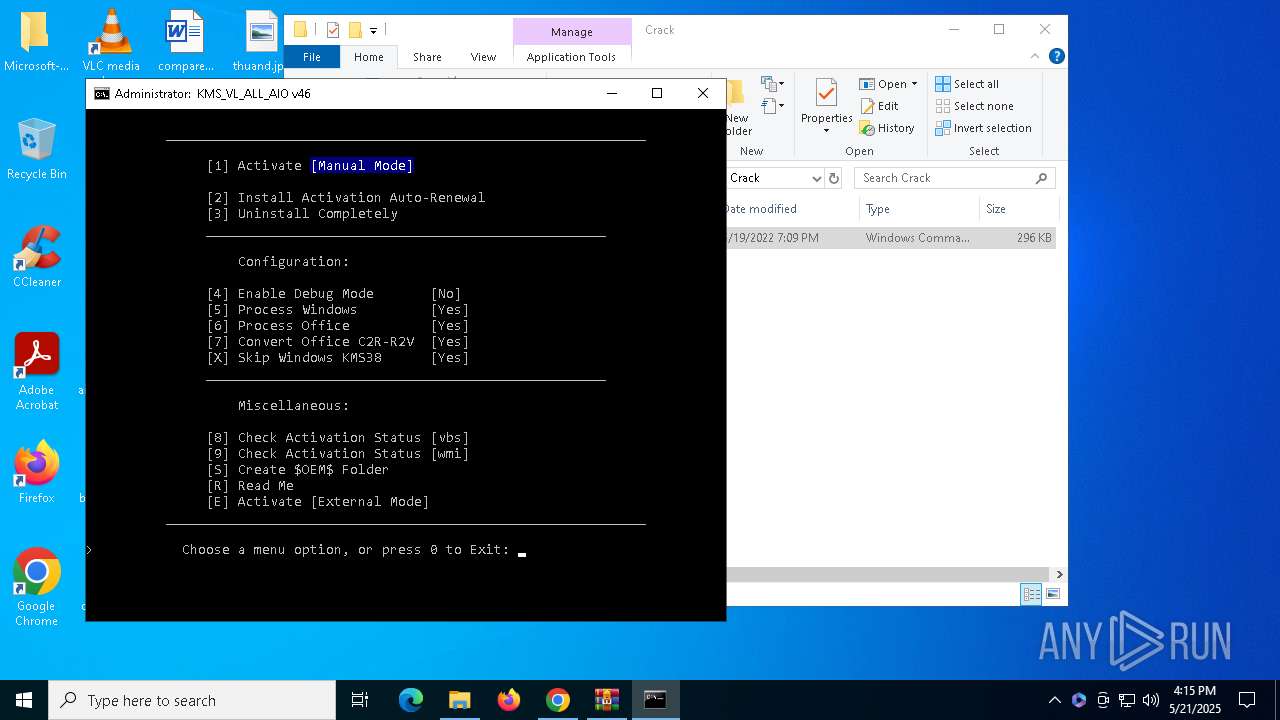
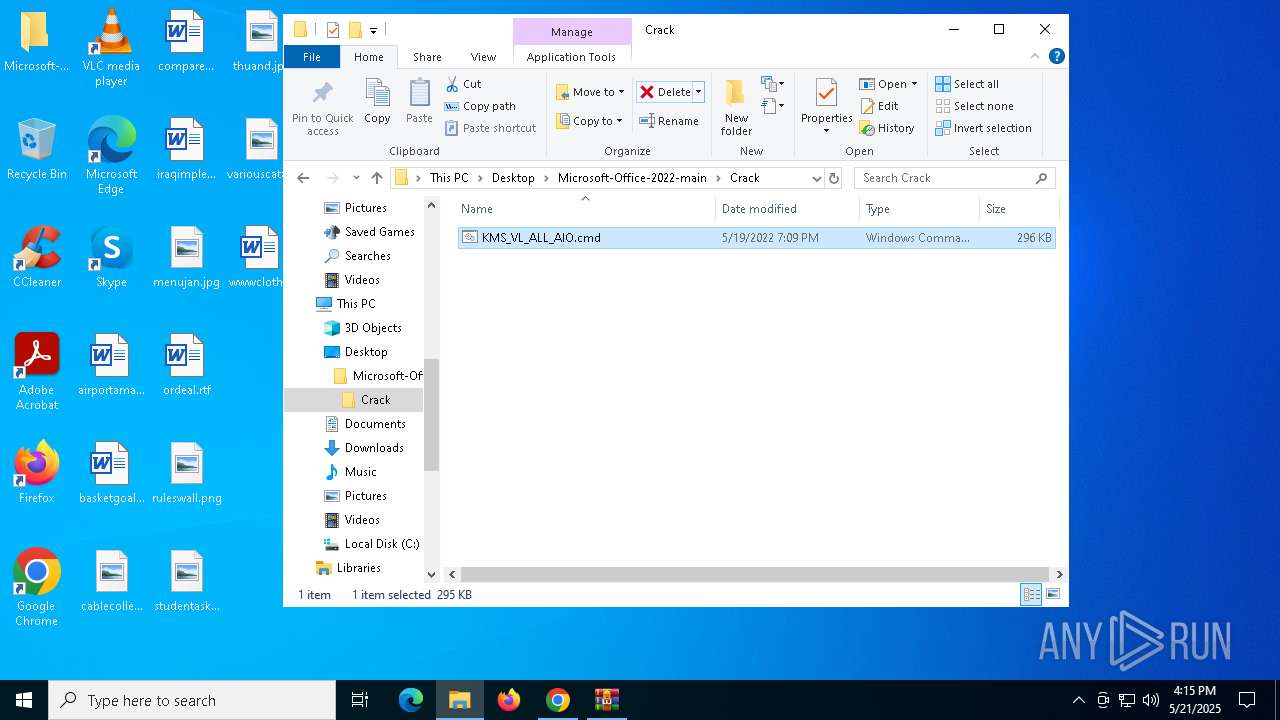
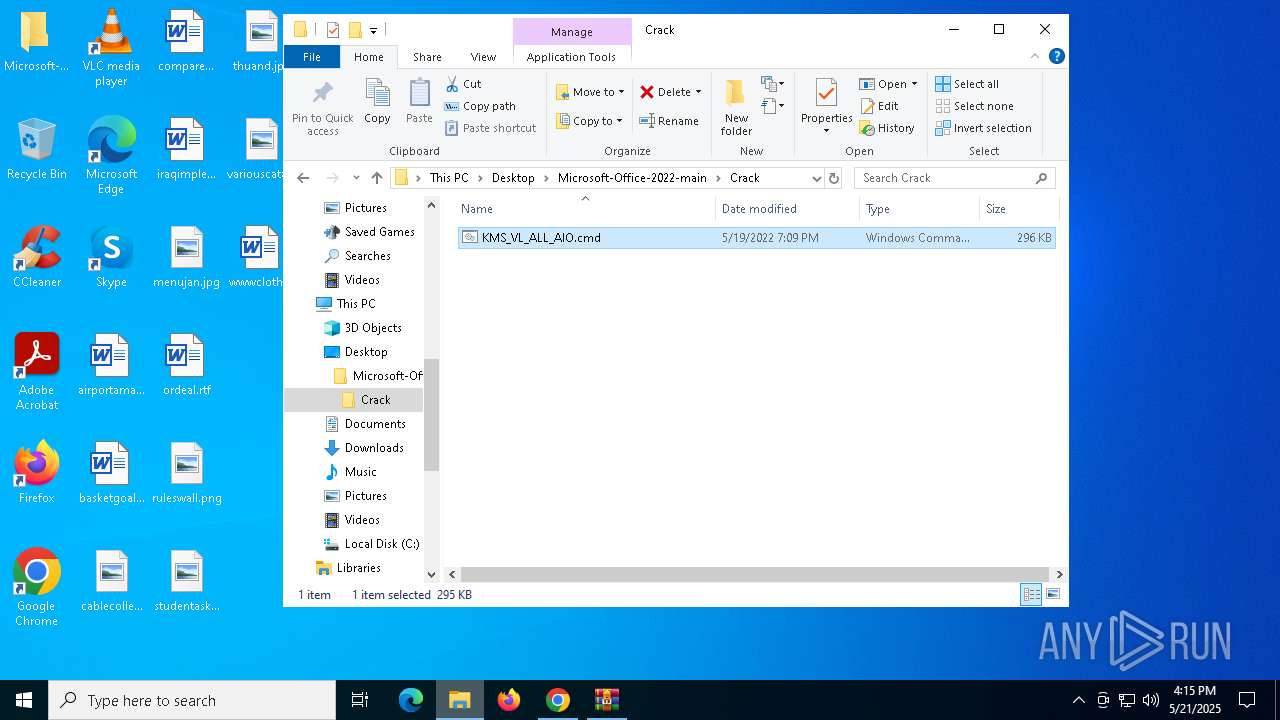
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2025, 16:12:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 17A307EAE10DC95CEF407B8E7C9DF636 |
| SHA1: | 995893FB498FE00D9291791E6F019BE3EDE70D4C |
| SHA256: | 90280C9F7F935706E223E583C62A05A93B328DA04B120534DEE6924E457E14F8 |
| SSDEEP: | 3:N8X2EFQCrdmMLCW0KoMZuqPlVXaMULNn:2m8wKCTKzuqPhULNn |
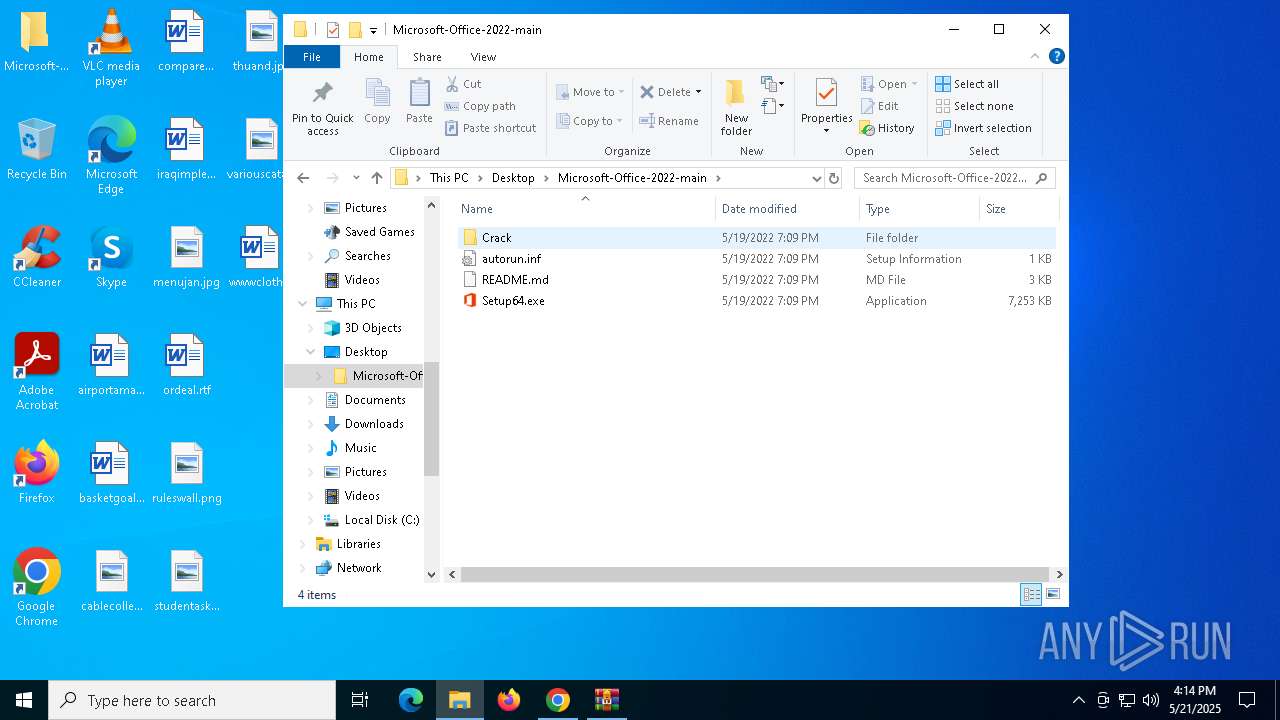
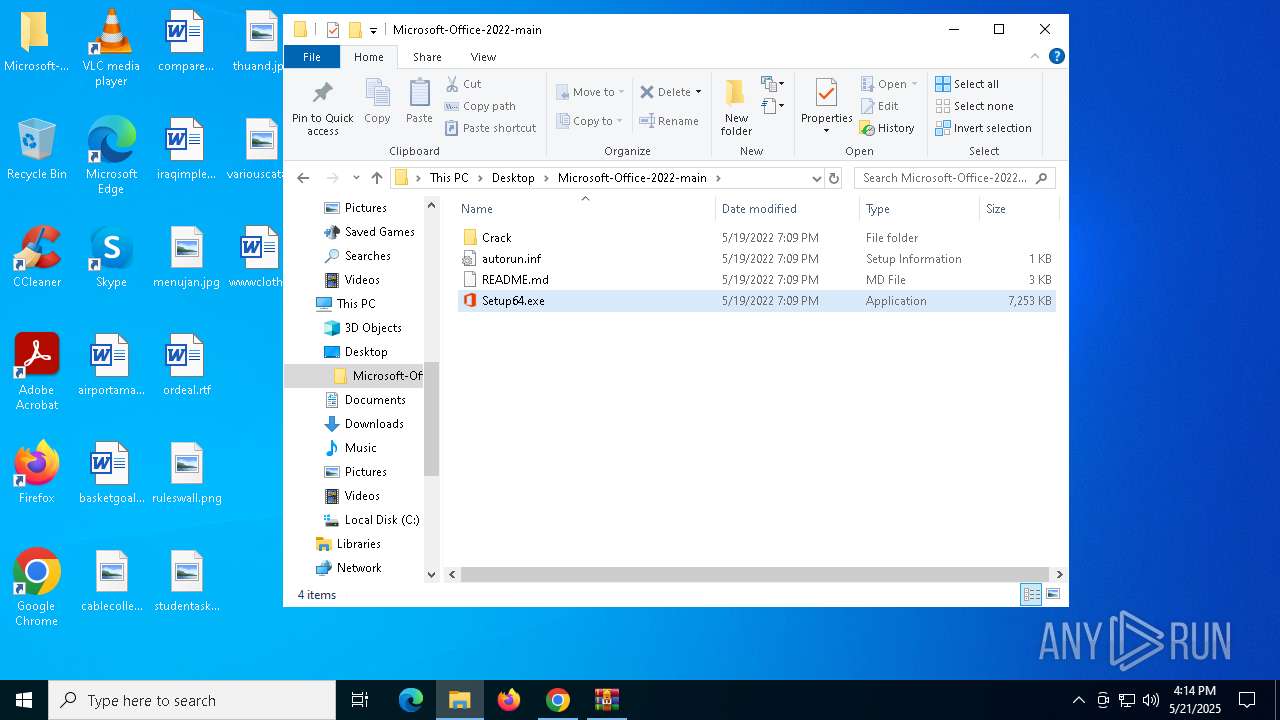
MALICIOUS
Scans artifacts that could help determine the target
- Setup64.exe (PID: 6744)
GENERIC has been found (auto)
- OfficeClickToRun.exe (PID: 8184)
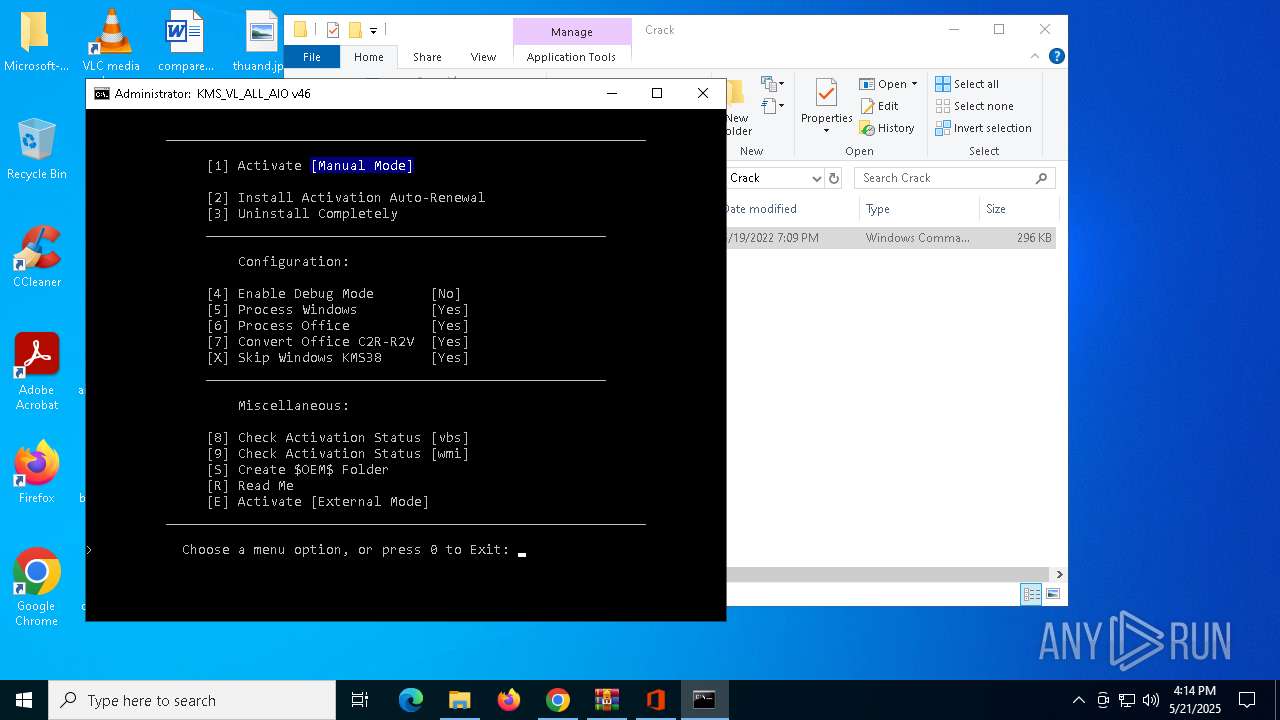
Starts NET.EXE for service management
- cmd.exe (PID: 3828)
- net.exe (PID: 5544)
- net.exe (PID: 4812)
- net.exe (PID: 7108)
Uses WMIC.EXE to add exclusions to the Windows Defender
- cmd.exe (PID: 3828)
SUSPICIOUS
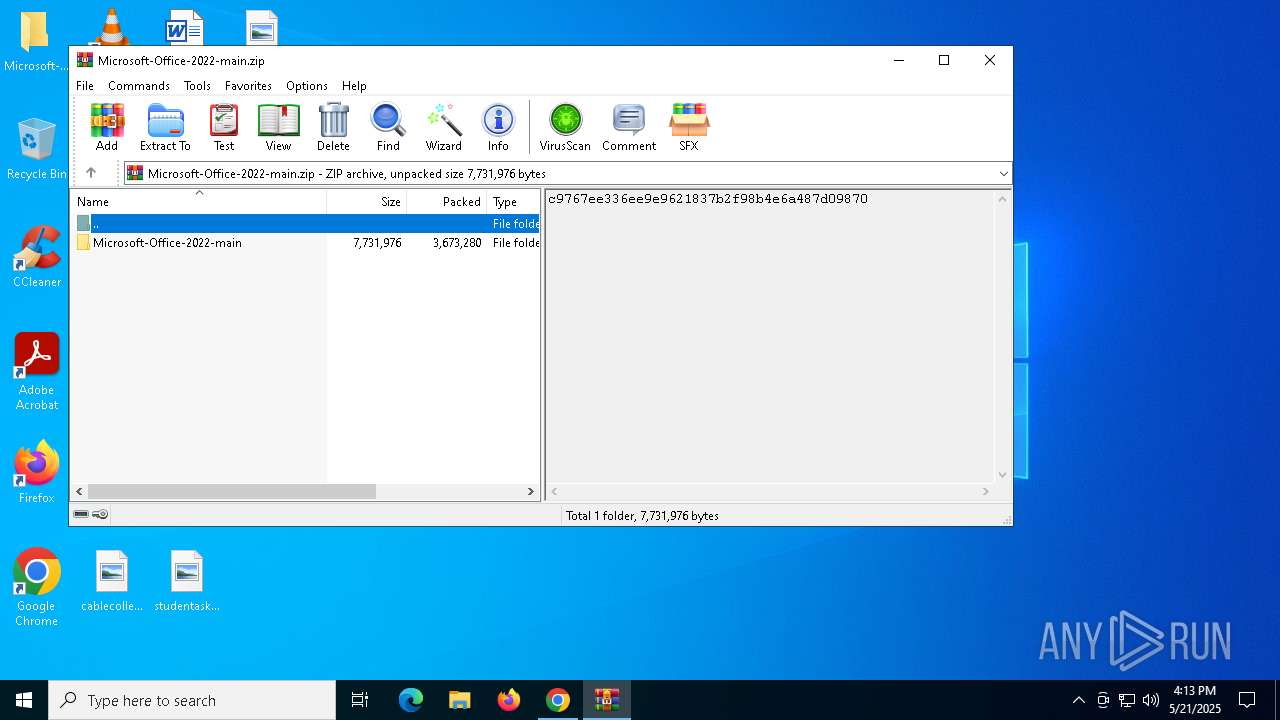
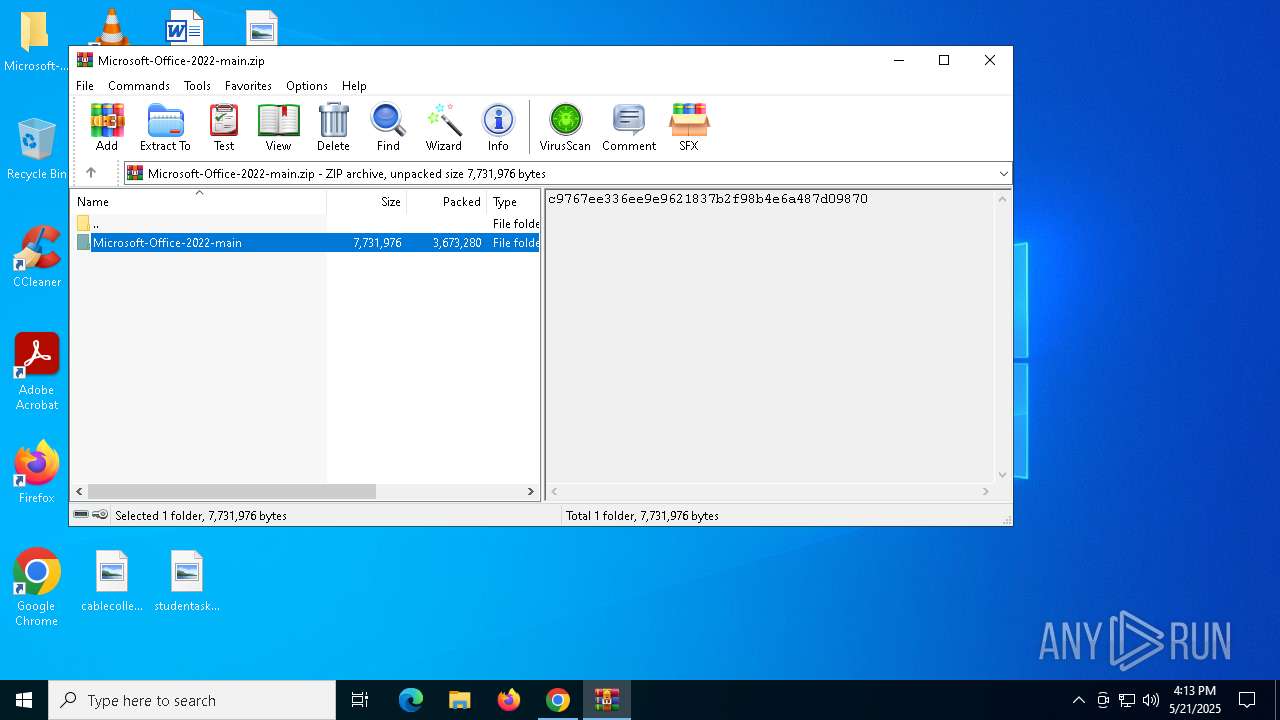
Process drops legitimate windows executable
- WinRAR.exe (PID: 672)
- chrome.exe (PID: 7460)
- OfficeClickToRun.exe (PID: 8184)
- OfficeClickToRun.exe (PID: 7976)
Starts a Microsoft application from unusual location
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
Reads security settings of Internet Explorer
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
Application launched itself
- Setup64.exe (PID: 5548)
- cmd.exe (PID: 3828)
Starts POWERSHELL.EXE for commands execution
- Setup64.exe (PID: 6744)
- cmd.exe (PID: 3828)
The process bypasses the loading of PowerShell profile settings
- Setup64.exe (PID: 6744)
- cmd.exe (PID: 3828)
Searches for installed software
- Setup64.exe (PID: 6744)
Executable content was dropped or overwritten
- OfficeClickToRun.exe (PID: 8184)
- OfficeClickToRun.exe (PID: 7976)
- csc.exe (PID: 2852)
- powershell.exe (PID: 4336)
The process drops C-runtime libraries
- OfficeClickToRun.exe (PID: 8184)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6668)
- cmd.exe (PID: 3828)
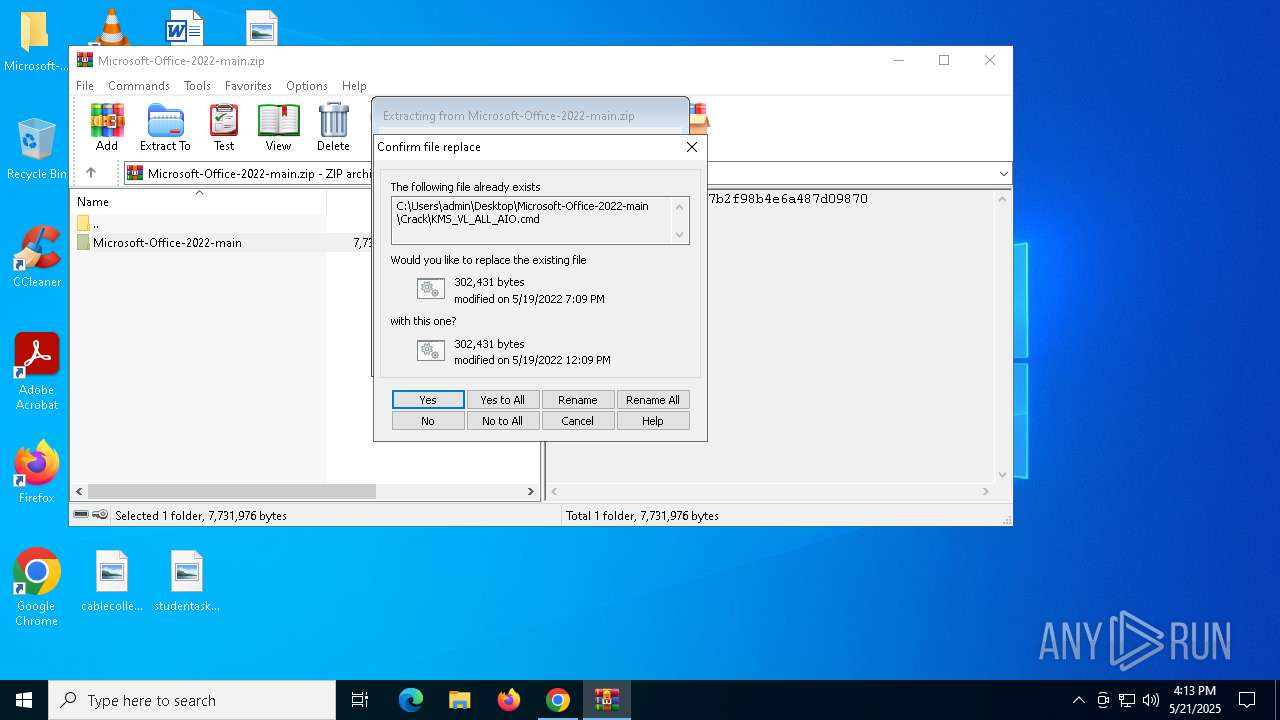
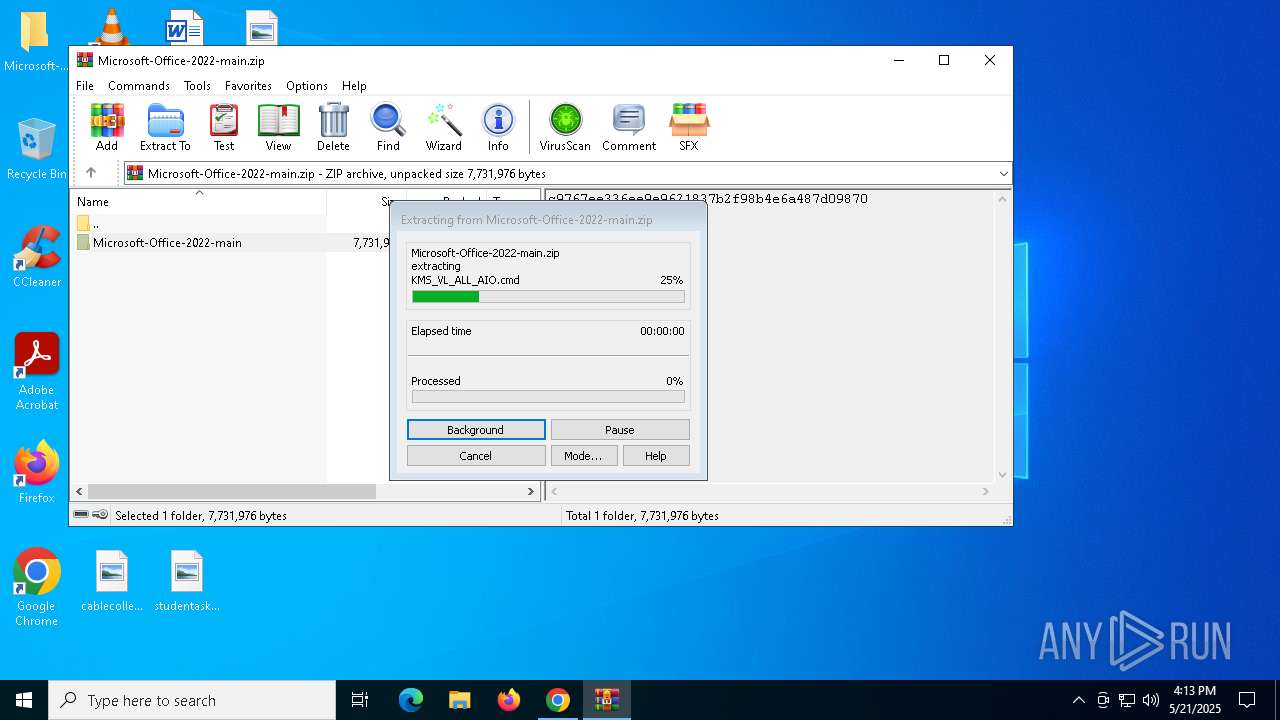
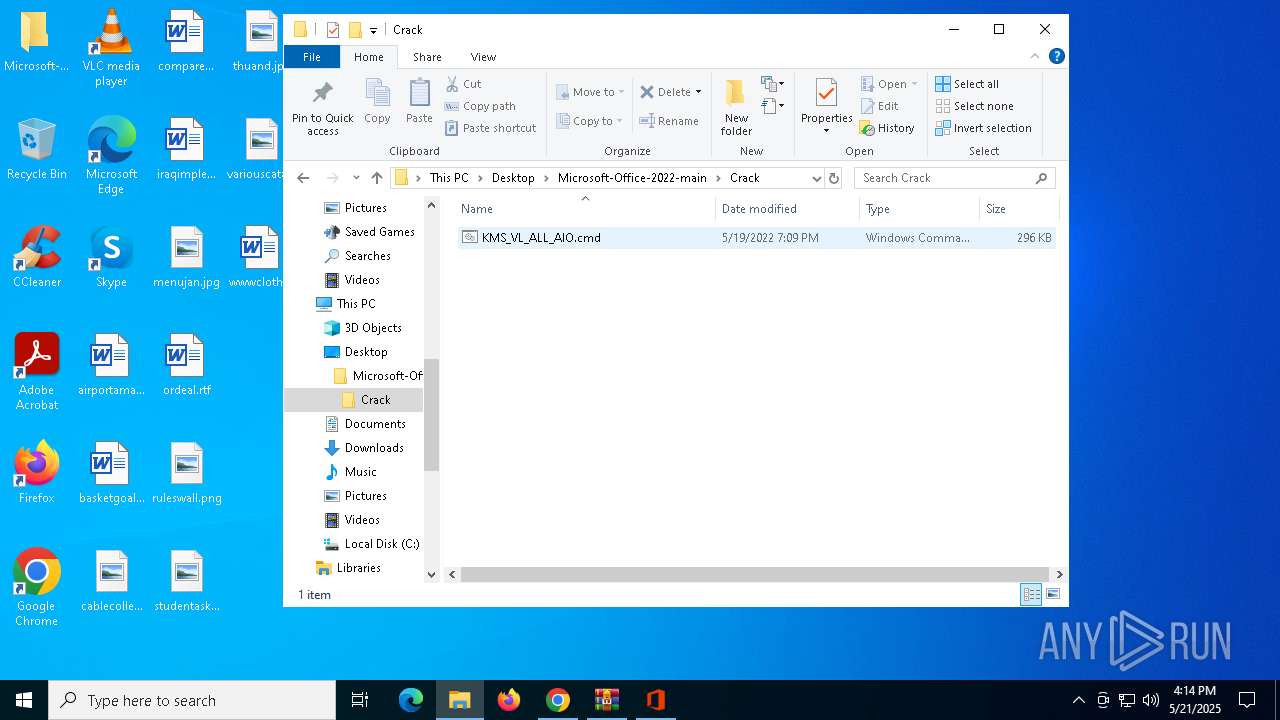
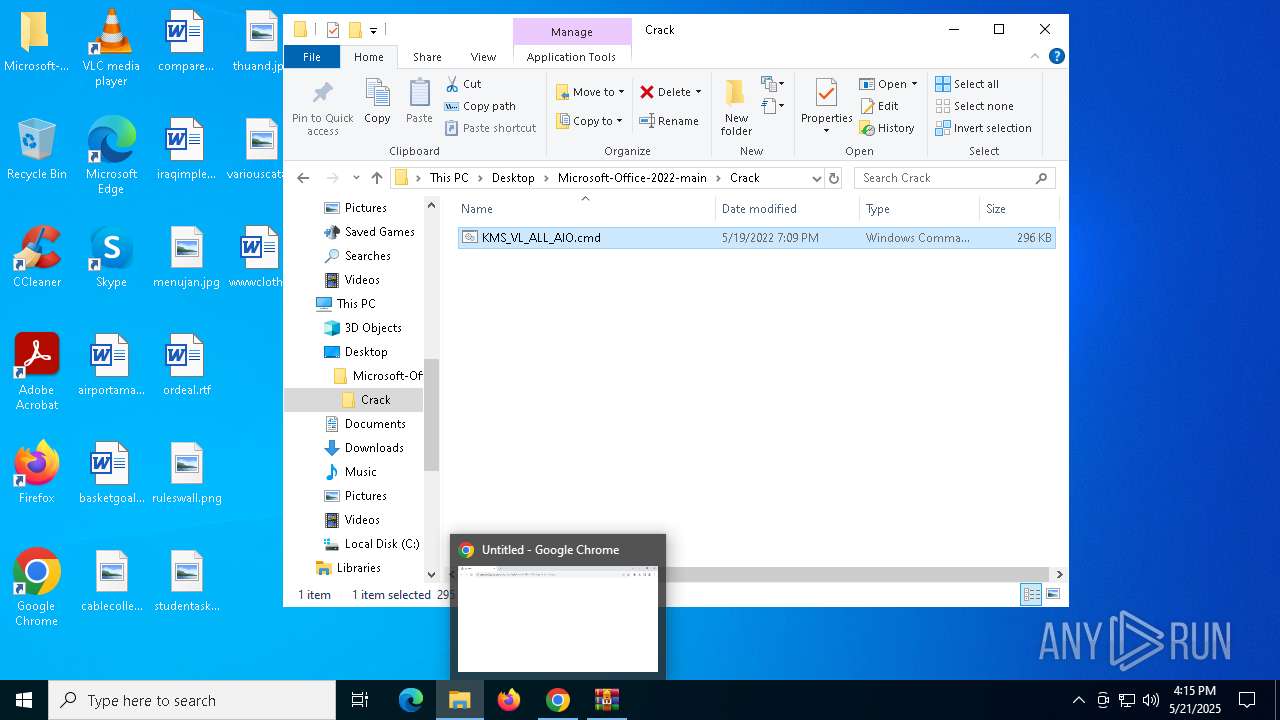
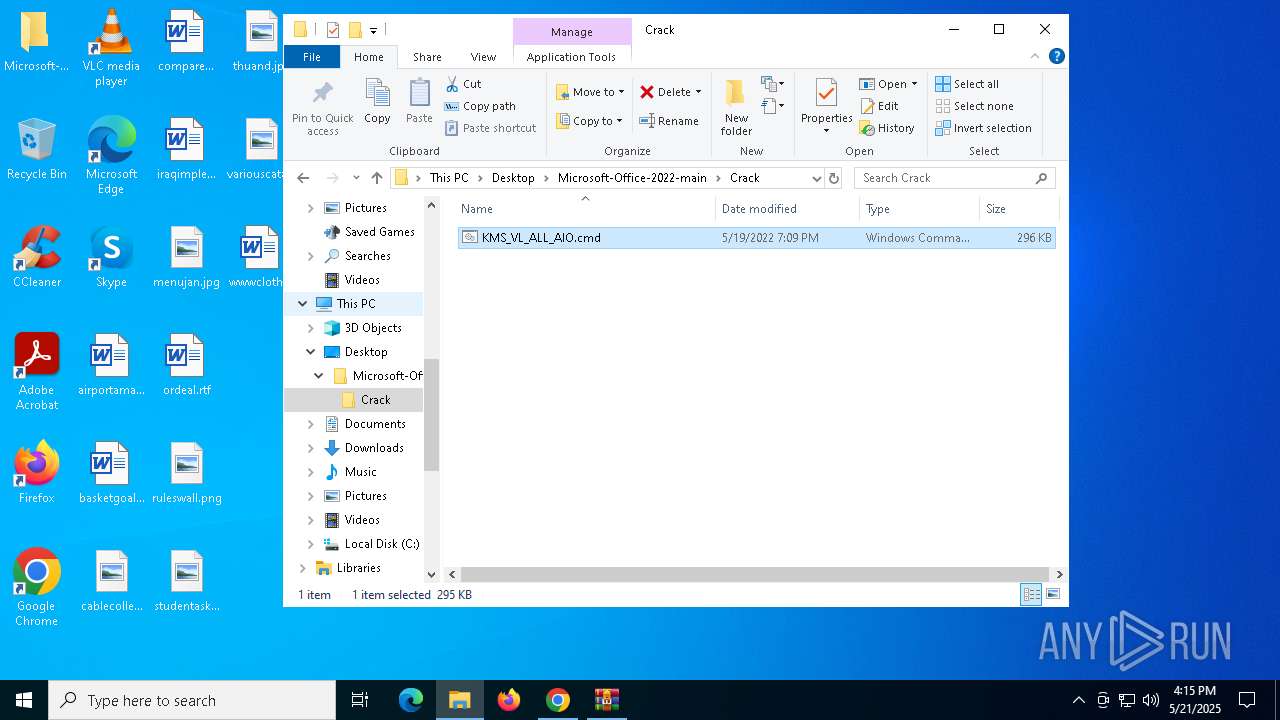
Executing commands from ".cmd" file
- cscript.exe (PID: 3992)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 3992)
- cmd.exe (PID: 3828)
Uses RUNDLL32.EXE to load library
- cscript.exe (PID: 3992)
Starts SC.EXE for service management
- cmd.exe (PID: 3828)
Windows service management via SC.EXE
- sc.exe (PID: 4436)
- sc.exe (PID: 5972)
- sc.exe (PID: 4012)
- sc.exe (PID: 7332)
- sc.exe (PID: 1748)
- sc.exe (PID: 8032)
- sc.exe (PID: 3716)
- sc.exe (PID: 4932)
There is functionality for taking screenshot (YARA)
- OfficeClickToRun.exe (PID: 8184)
Executes script without checking the security policy
- powershell.exe (PID: 5716)
- powershell.exe (PID: 4336)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3828)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3828)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 3828)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2852)
Hides command output
- cmd.exe (PID: 7568)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 7308)
- cmd.exe (PID: 5868)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7192)
- cmd.exe (PID: 5968)
- cmd.exe (PID: 5024)
- cmd.exe (PID: 2796)
- cmd.exe (PID: 7176)
- cmd.exe (PID: 3800)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 8180)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 1512)
- cmd.exe (PID: 6392)
- cmd.exe (PID: 4976)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 6964)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 6488)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 1164)
- cmd.exe (PID: 4920)
- cmd.exe (PID: 2088)
- cmd.exe (PID: 7296)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 3828)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 2320)
- cmd.exe (PID: 632)
- cmd.exe (PID: 3828)
Lists all scheduled tasks
- schtasks.exe (PID: 7244)
The process executes VB scripts
- cmd.exe (PID: 3828)
INFO
Application launched itself
- chrome.exe (PID: 7460)
Reads Microsoft Office registry keys
- chrome.exe (PID: 7460)
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 672)
- chrome.exe (PID: 5304)
- chrome.exe (PID: 5928)
The sample compiled with english language support
- chrome.exe (PID: 5304)
- OfficeClickToRun.exe (PID: 8184)
- chrome.exe (PID: 5928)
Reads the software policy settings
- slui.exe (PID: 7288)
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
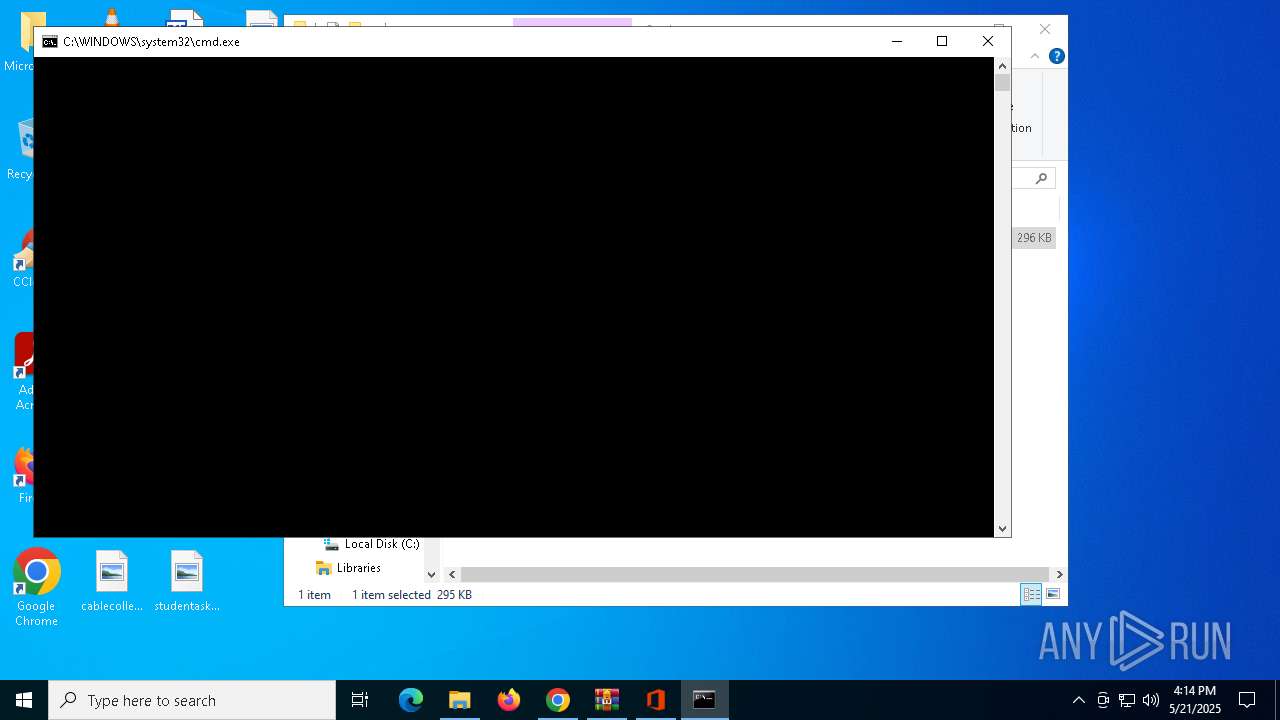
Manual execution by a user
- Setup64.exe (PID: 5548)
- cmd.exe (PID: 6668)
- OfficeC2RClient.exe (PID: 3332)
Reads the computer name
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
- InspectorOfficeGadget.exe (PID: 2852)
- OfficeClickToRun.exe (PID: 8184)
Checks supported languages
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
- InspectorOfficeGadget.exe (PID: 2852)
- OfficeClickToRun.exe (PID: 8184)
Process checks whether UAC notifications are on
- Setup64.exe (PID: 5548)
Reads the machine GUID from the registry
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
- InspectorOfficeGadget.exe (PID: 2852)
Checks proxy server information
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
Process checks computer location settings
- Setup64.exe (PID: 5548)
- Setup64.exe (PID: 6744)
Create files in a temporary directory
- Setup64.exe (PID: 5548)
- InspectorOfficeGadget.exe (PID: 2852)
- Setup64.exe (PID: 6744)
Reads Environment values
- Setup64.exe (PID: 6744)
Creates files or folders in the user directory
- Setup64.exe (PID: 6744)
The sample compiled with bulgarian language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with arabic language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with french language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with Italian language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with korean language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with japanese language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with russian language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with turkish language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with portuguese language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with slovak language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with swedish language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with Indonesian language support
- OfficeClickToRun.exe (PID: 8184)
Starts MODE.COM to configure console settings
- mode.com (PID: 7312)
- mode.com (PID: 6252)
Checks operating system version
- cmd.exe (PID: 3828)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 7976)
The sample compiled with polish language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with spanish language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with german language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with czech language support
- OfficeClickToRun.exe (PID: 8184)
The sample compiled with chinese language support
- OfficeClickToRun.exe (PID: 8184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
646
Monitored processes
505
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | findstr /I /C:"VisioProXVolume" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | findstr /I /C:"AccessRetail" "C:\WINDOWS\Temp\c2rchk.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | findstr /I /C:"HomeBusiness2019Retail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | wmic path SoftwareLicensingProduct where (ID='e4db50ea-bda1-4566-b047-0ca50abc6f07') get LicenseStatus /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | reg query "HKLM\SOFTWARE\Microsoft\Windows Script Host\Settings" /v Enabled | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | reg query HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\15.0\Common\InstallRoot /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | wmic path SoftwareLicensingProduct where (ID='2de67392-b7a7-462a-b1ca-108dd189f588') get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4176 --field-trial-handle=1364,i,15375451580503185959,3354464455972066249,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 540 | findstr /I /C:"SkypeforBusinessRetail" "C:\WINDOWS\Temp\crvProductIds.txt" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
95 233
Read events
94 698
Write events
300
Delete events
235
Modification events
| (PID) Process: | (7460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7460) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7460) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1164) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000004CE4BB3B6BCADB01 | |||
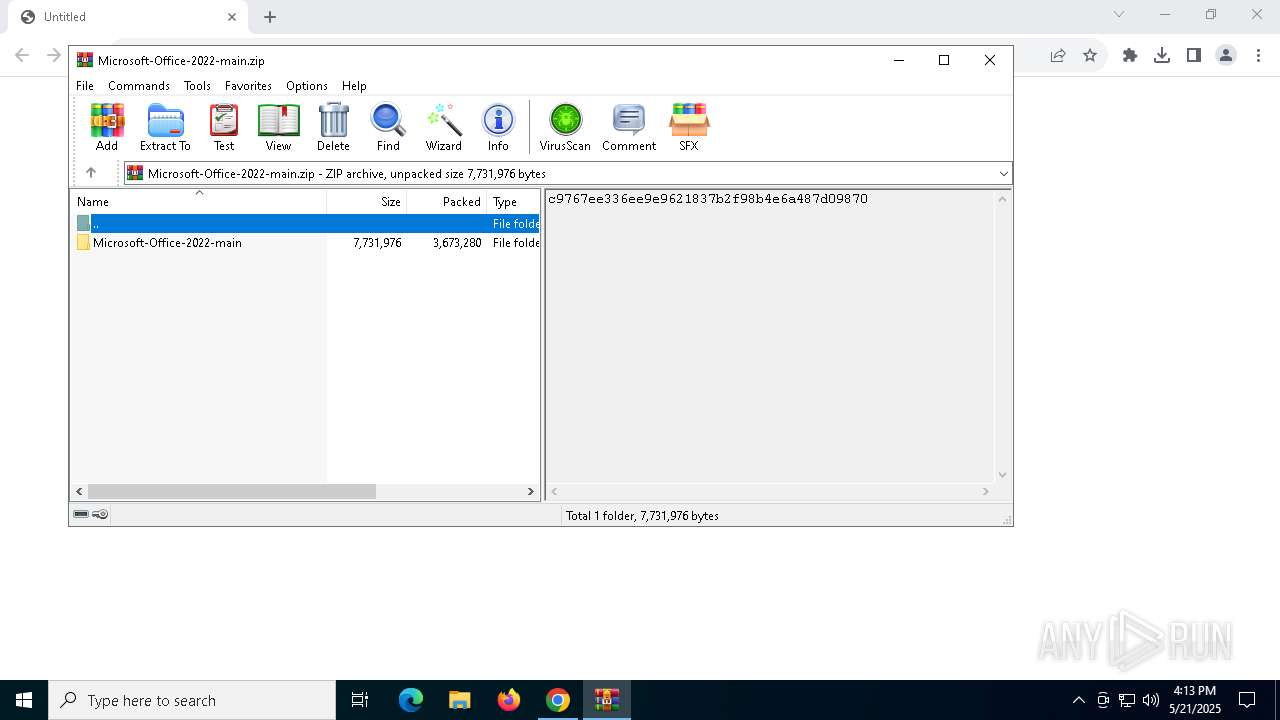
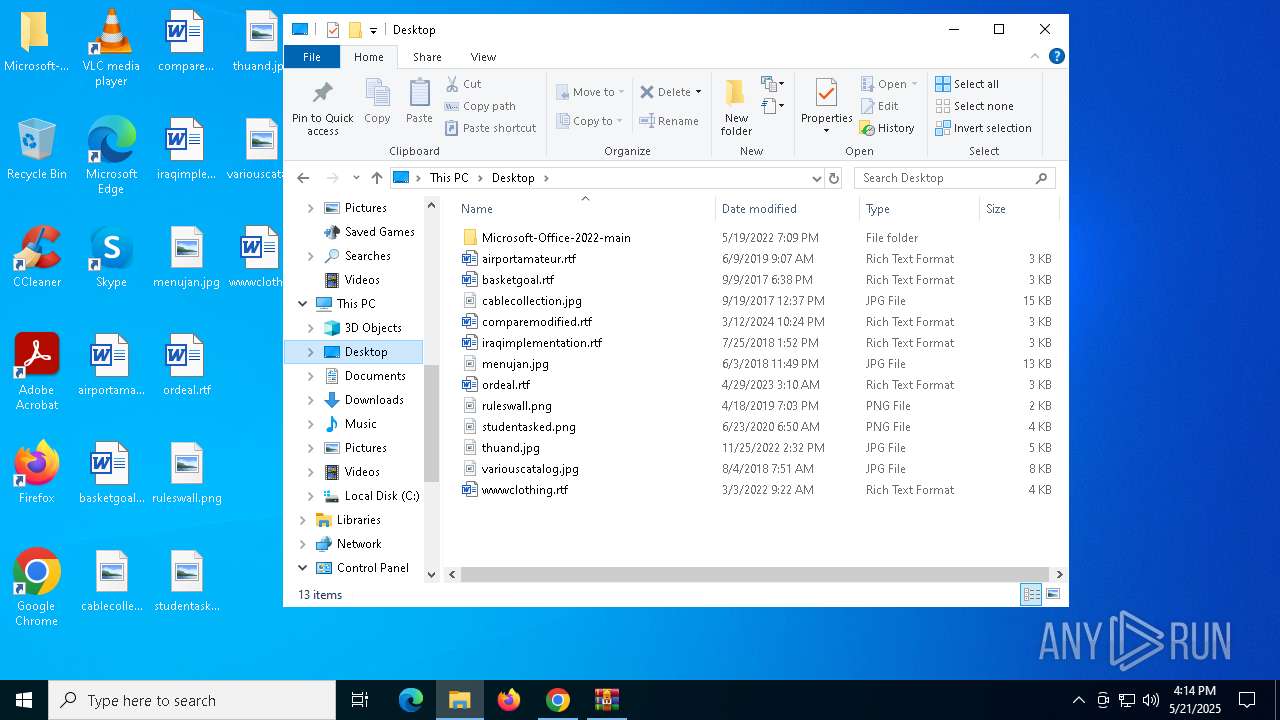
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (672) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
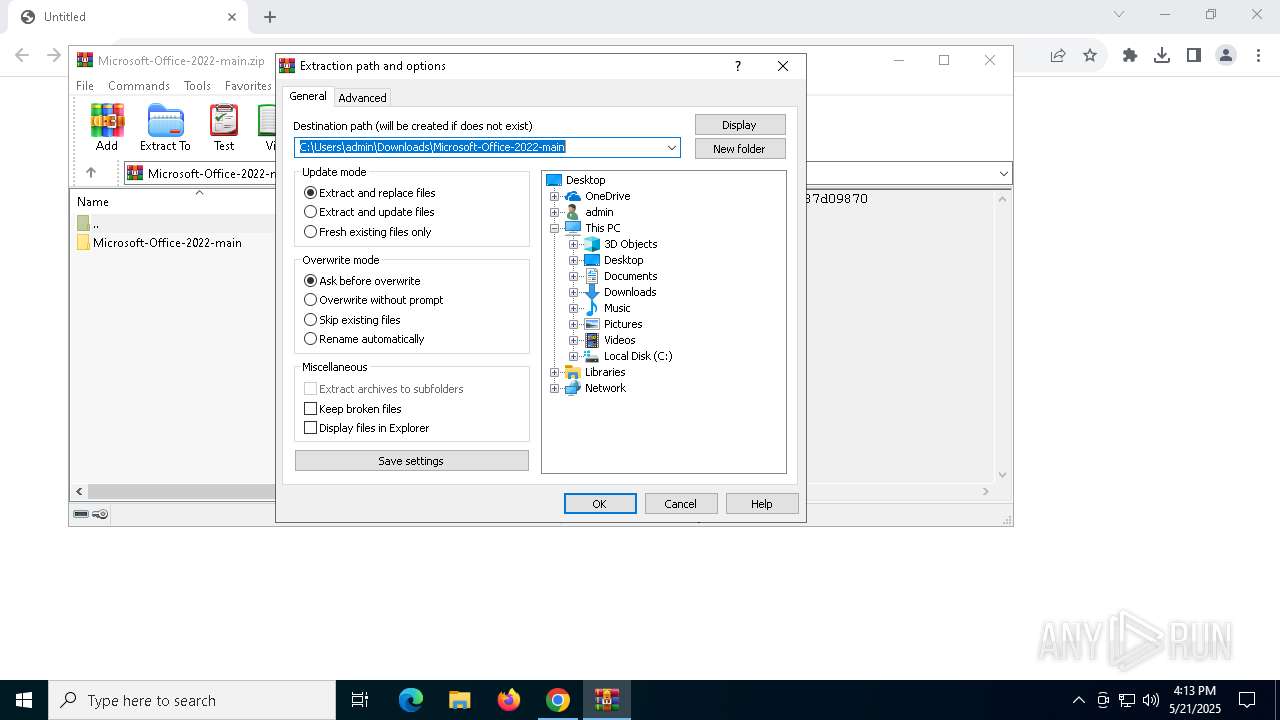
Value: C:\Users\admin\Downloads\Microsoft-Office-2022-main.zip | |||
Executable files
415
Suspicious files
468
Text files
212
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10cc3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10cc3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10cc3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10cc3b.TMP | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10cc4b.TMP | — | |
MD5:— | SHA256:— | |||
| 7460 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10cc4b.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
220
TCP/UDP connections
184
DNS requests
130
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6808 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6808 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1128 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1128 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1128 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1128 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1128 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7680 | chrome.exe | 140.82.121.10:443 | codeload.github.com | GITHUB | US | whitelisted |
7460 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7680 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6544 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
codeload.github.com |
| whitelisted |
accounts.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.google.com |
| whitelisted |