| URL: | https://statics.teams.cdn.office.net/production-windows-x64/1.7.00.1864/Teams_windows_x64.exe |
| Full analysis: | https://app.any.run/tasks/de9d7d66-ee59-49be-9b6a-d03ab58465d5 |
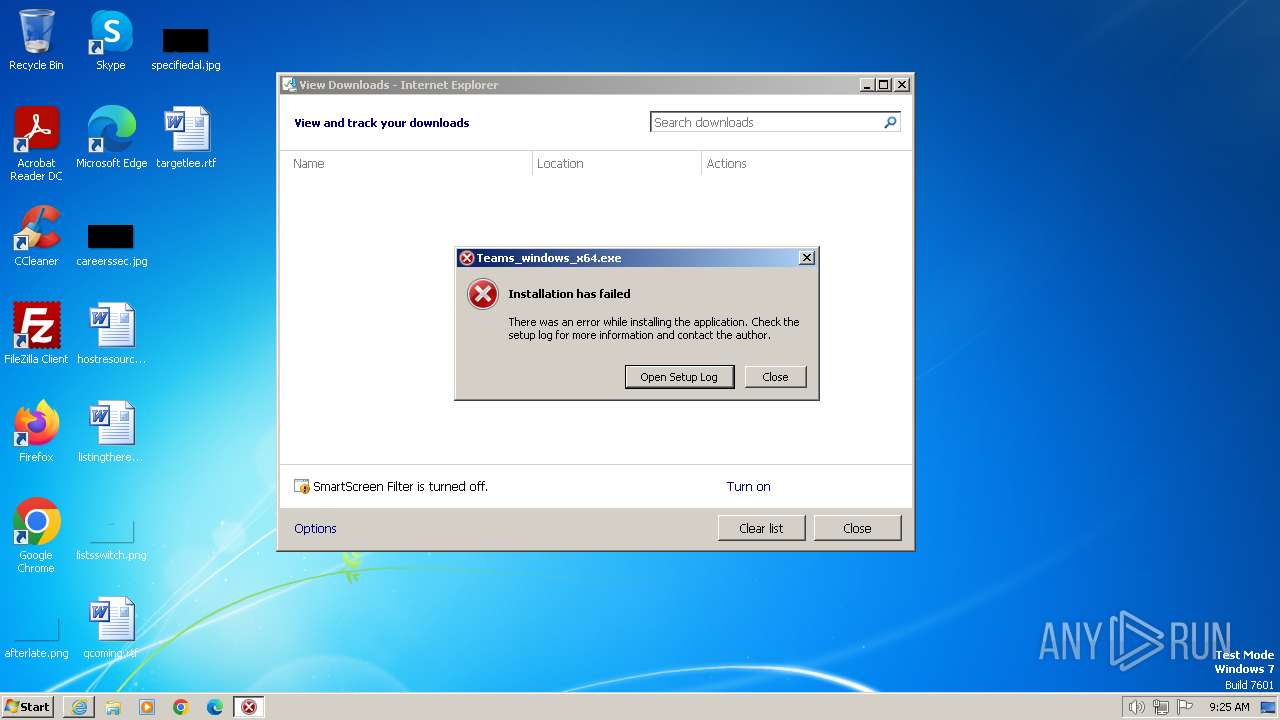
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2024, 09:23:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A7824F9CA81D1BA12E75DADF77E16AD6 |
| SHA1: | 500BA64006536DF0E852459DCABE1B6125B131C7 |
| SHA256: | 9025744F0368AD0E3A4339DDC254DD6A5EC75603D7560F8A38AF1128EFAA5569 |
| SSDEEP: | 3:N8cwu9puaQGRMdv3LSheMhu/xN:2cDH7TRMdv3LYeyu5N |
MALICIOUS
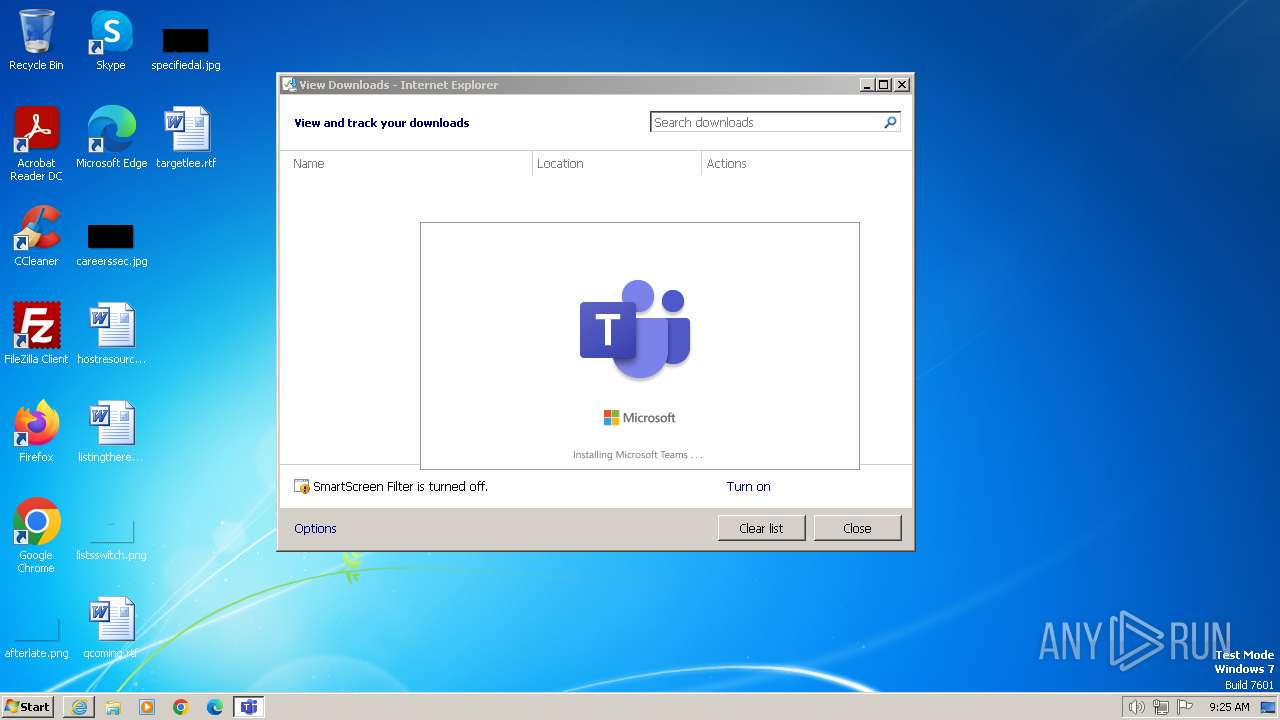
Drops the executable file immediately after the start
- Teams_windows_x64.exe (PID: 2408)
- Update.exe (PID: 2672)
SUSPICIOUS
Process drops legitimate windows executable
- Update.exe (PID: 2672)
- Teams_windows_x64.exe (PID: 2408)
Executable content was dropped or overwritten
- Teams_windows_x64.exe (PID: 2408)
- Update.exe (PID: 2672)
The process drops C-runtime libraries
- Update.exe (PID: 2672)
Reads security settings of Internet Explorer
- Update.exe (PID: 2672)
Reads the Internet Settings
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Reads settings of System Certificates
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Start notepad (likely ransomware note)
- Teams_windows_x64.exe (PID: 2408)
INFO
Creates files or folders in the user directory
- Teams_windows_x64.exe (PID: 2408)
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Checks supported languages
- Update.exe (PID: 2672)
- Teams_windows_x64.exe (PID: 2408)
- Squirrel.exe (PID: 3068)
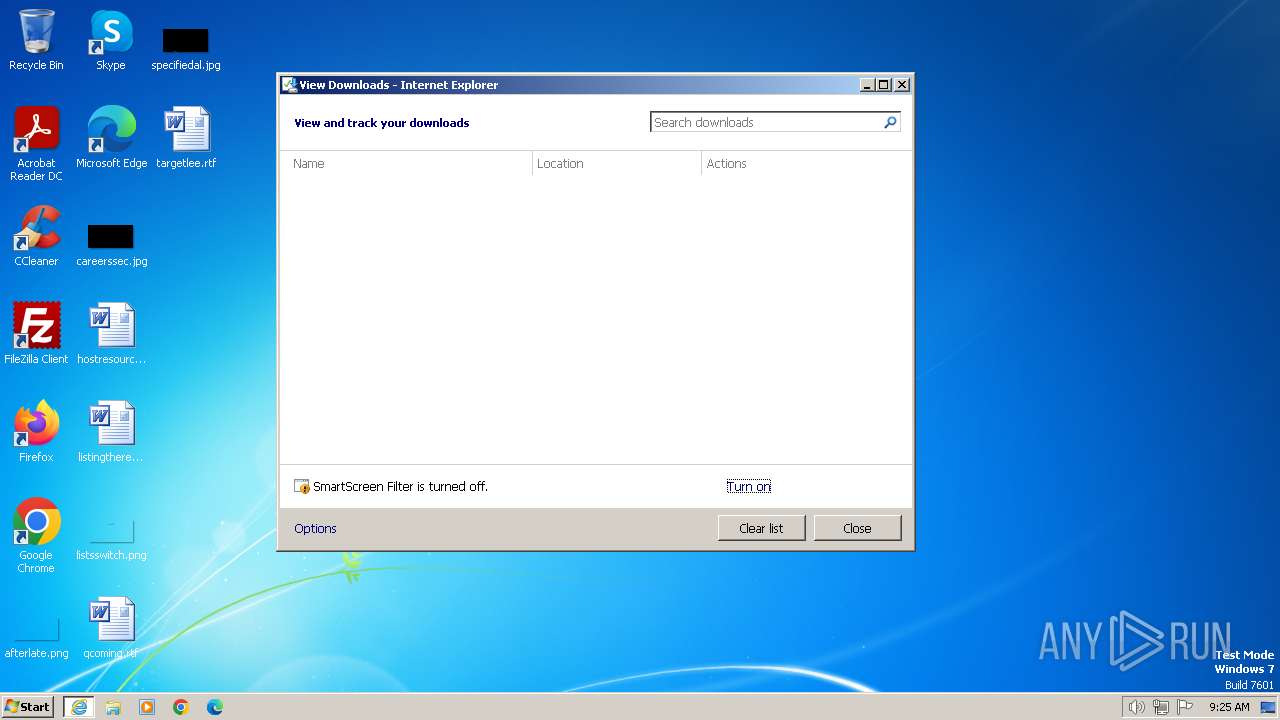
Modifies the phishing filter of IE
- iexplore.exe (PID: 3668)
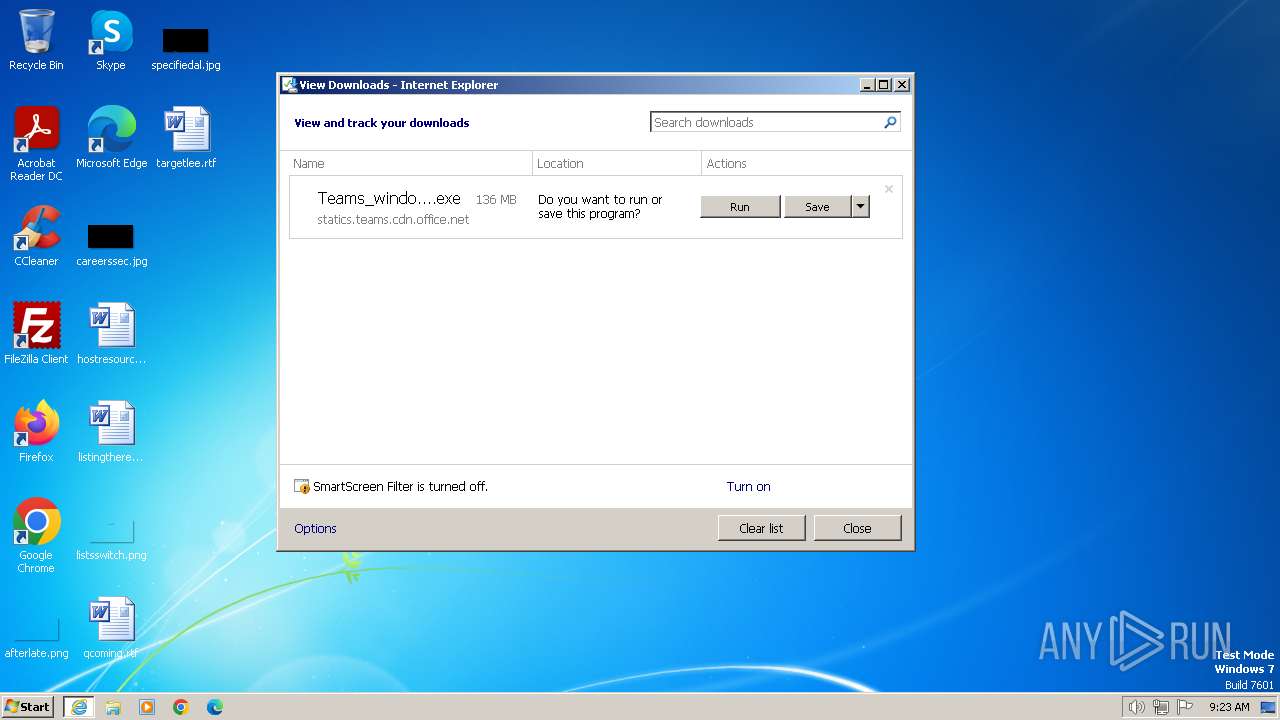
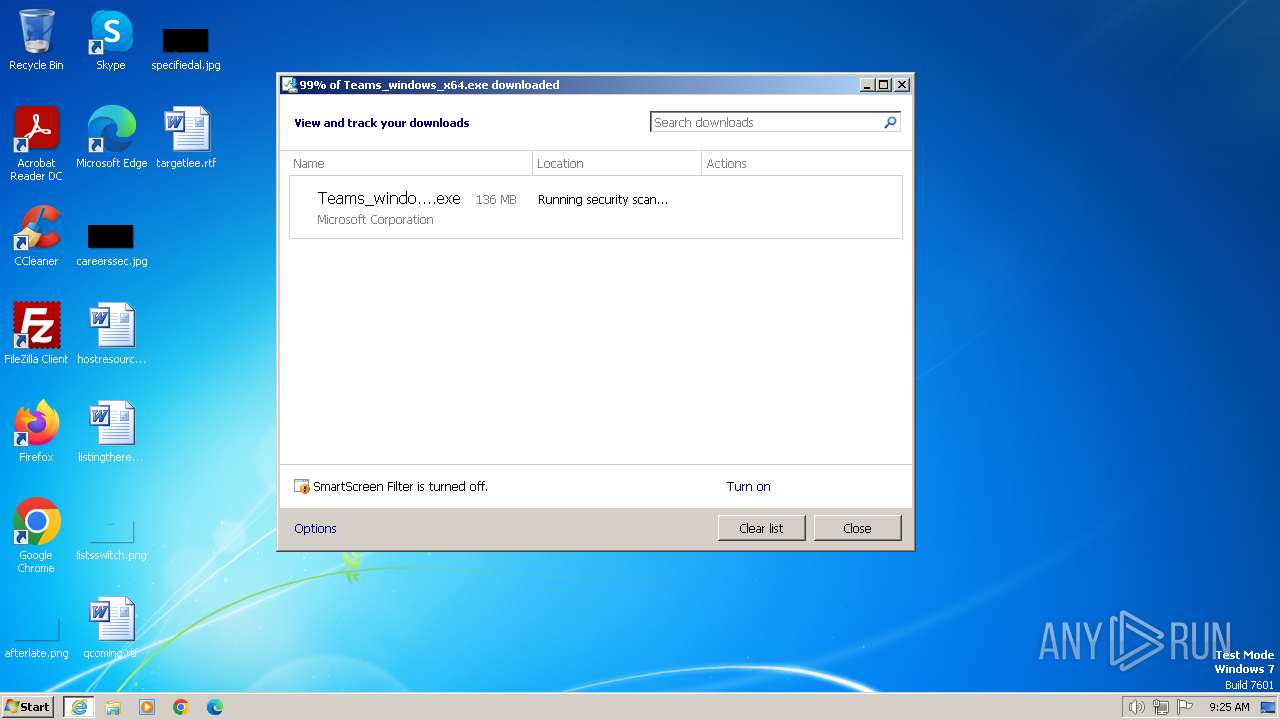
The process uses the downloaded file
- iexplore.exe (PID: 3668)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3972)
Drops the executable file immediately after the start
- iexplore.exe (PID: 3972)
Application launched itself
- iexplore.exe (PID: 3668)
Reads the computer name
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
- Teams_windows_x64.exe (PID: 2408)
Reads Environment values
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Reads the machine GUID from the registry
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Reads Microsoft Office registry keys
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Create files in a temporary directory
- Update.exe (PID: 2672)
Reads the software policy settings
- Update.exe (PID: 2672)
- Squirrel.exe (PID: 3068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2408 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Teams_windows_x64.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Teams_windows_x64.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 4294967295 Version: 1.7.00.1864 Modules
| |||||||||||||||
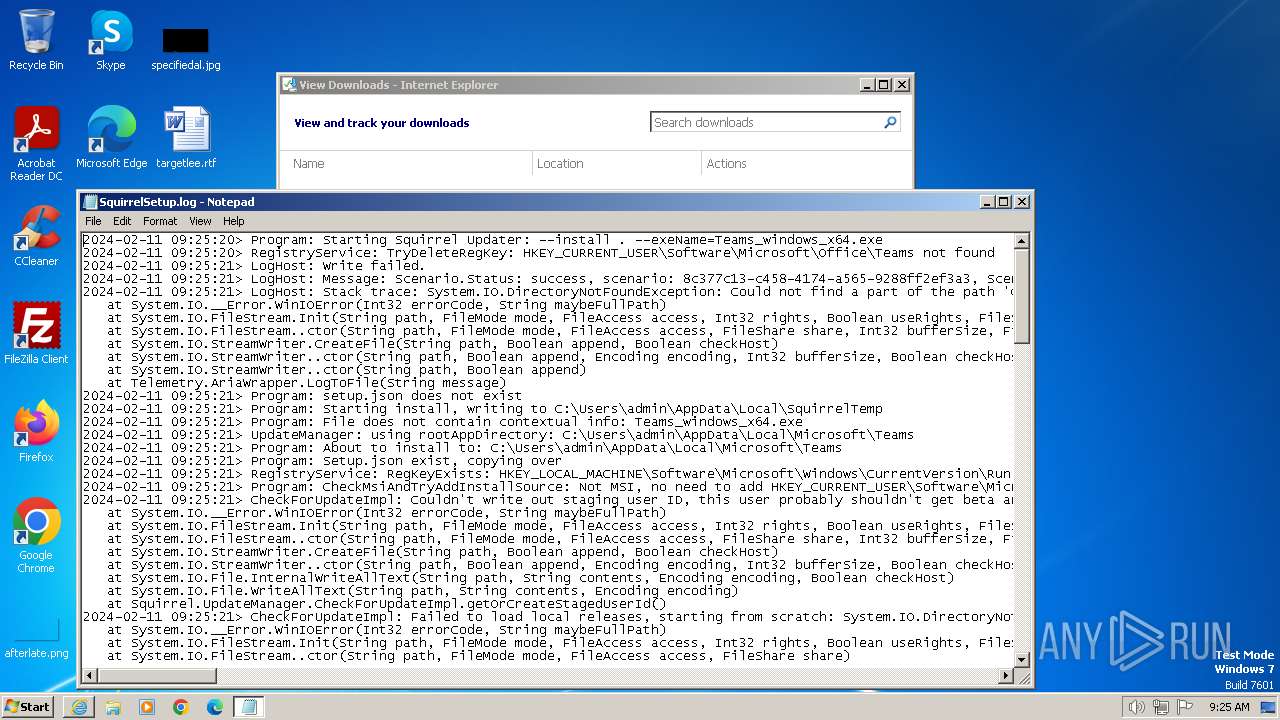
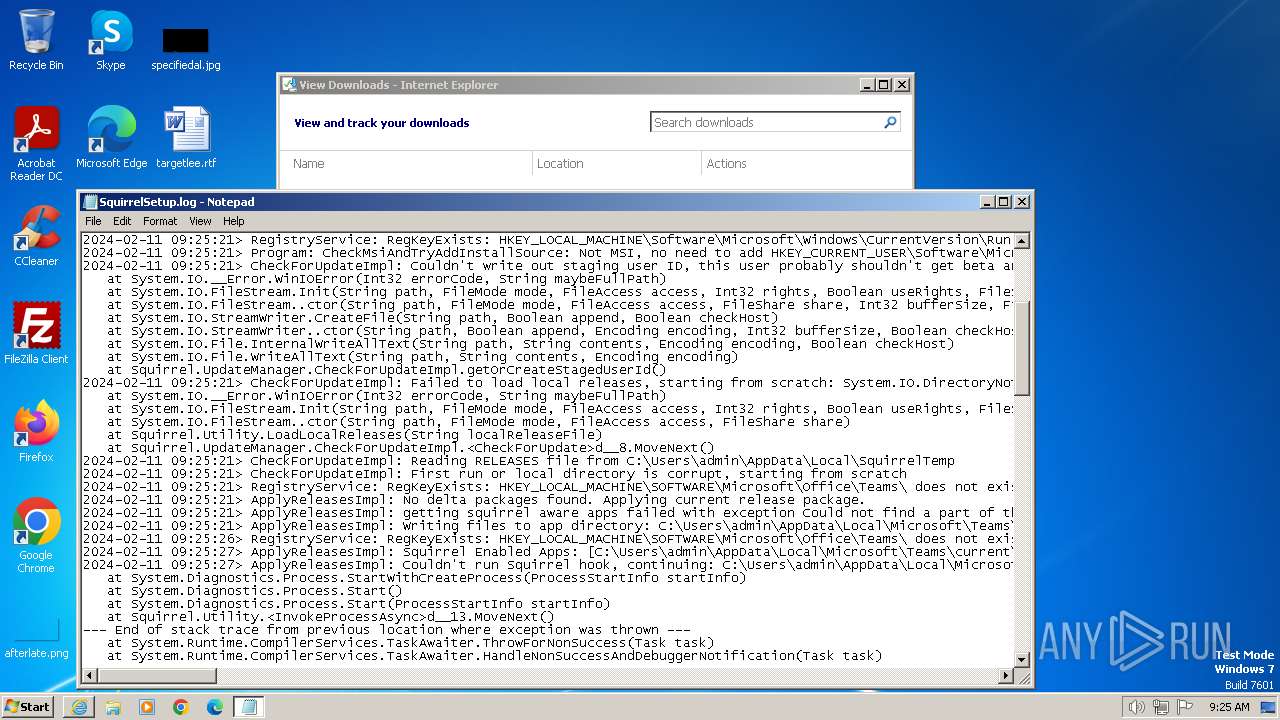
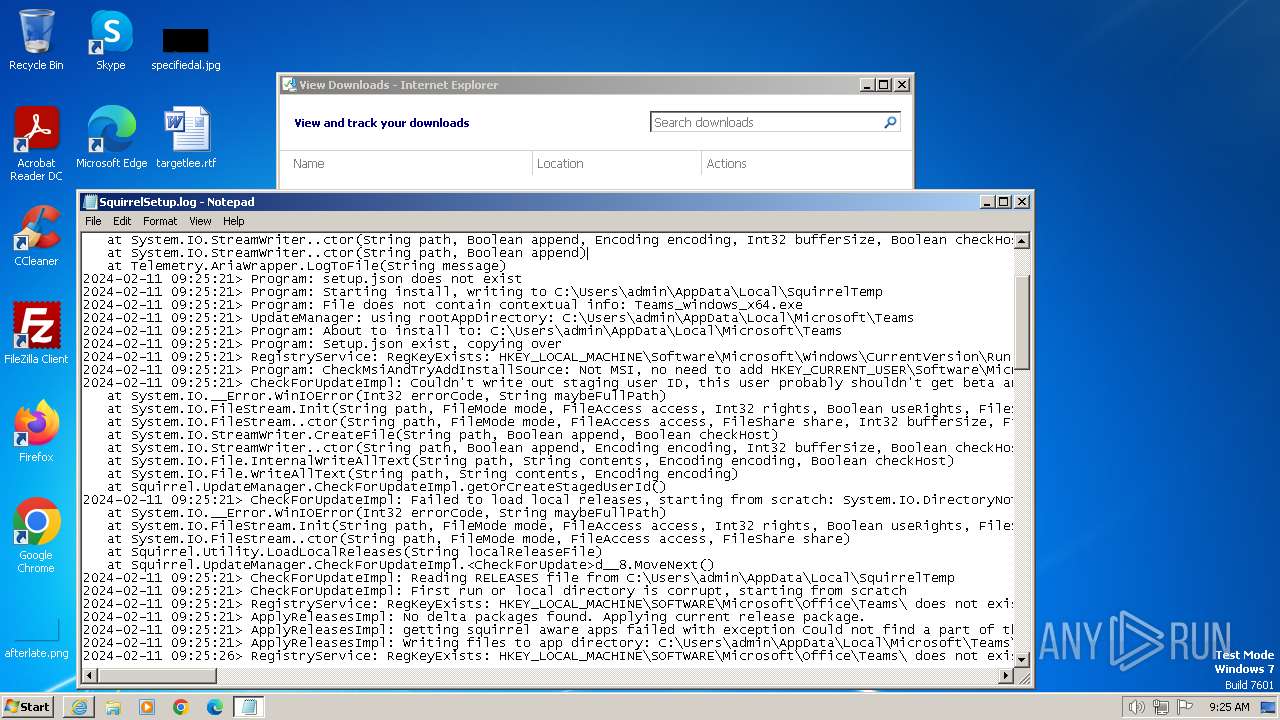
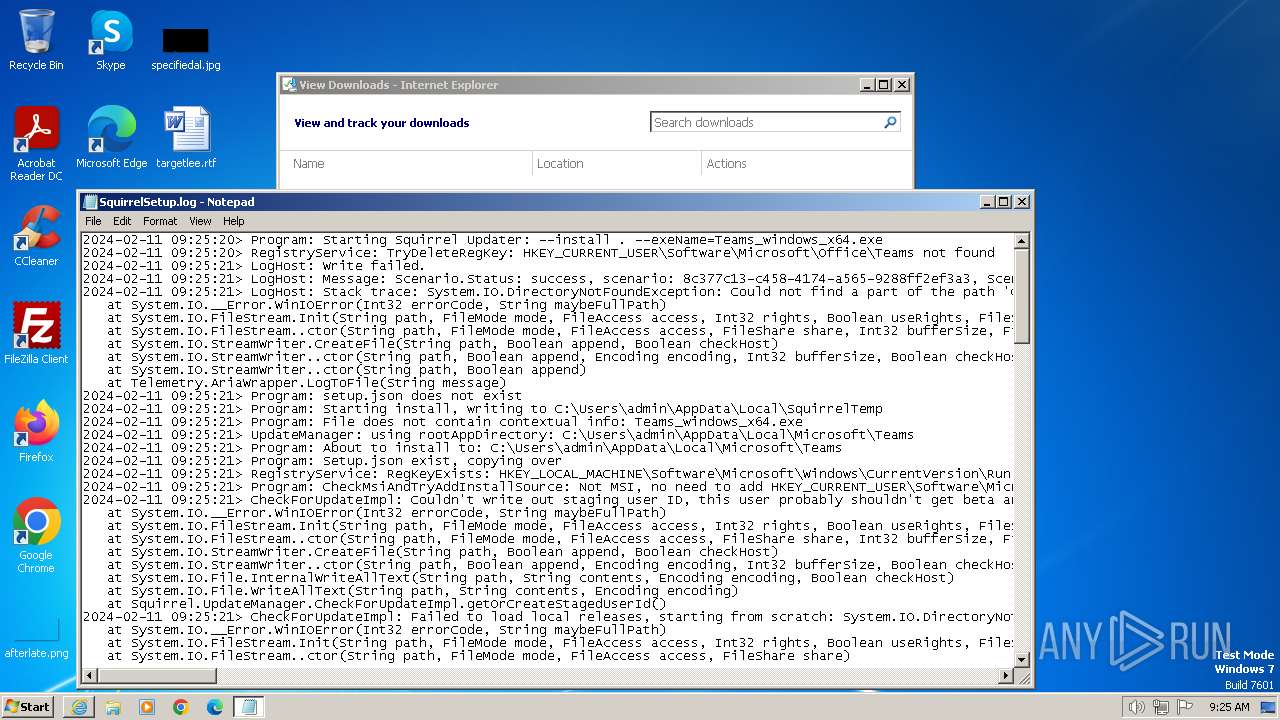
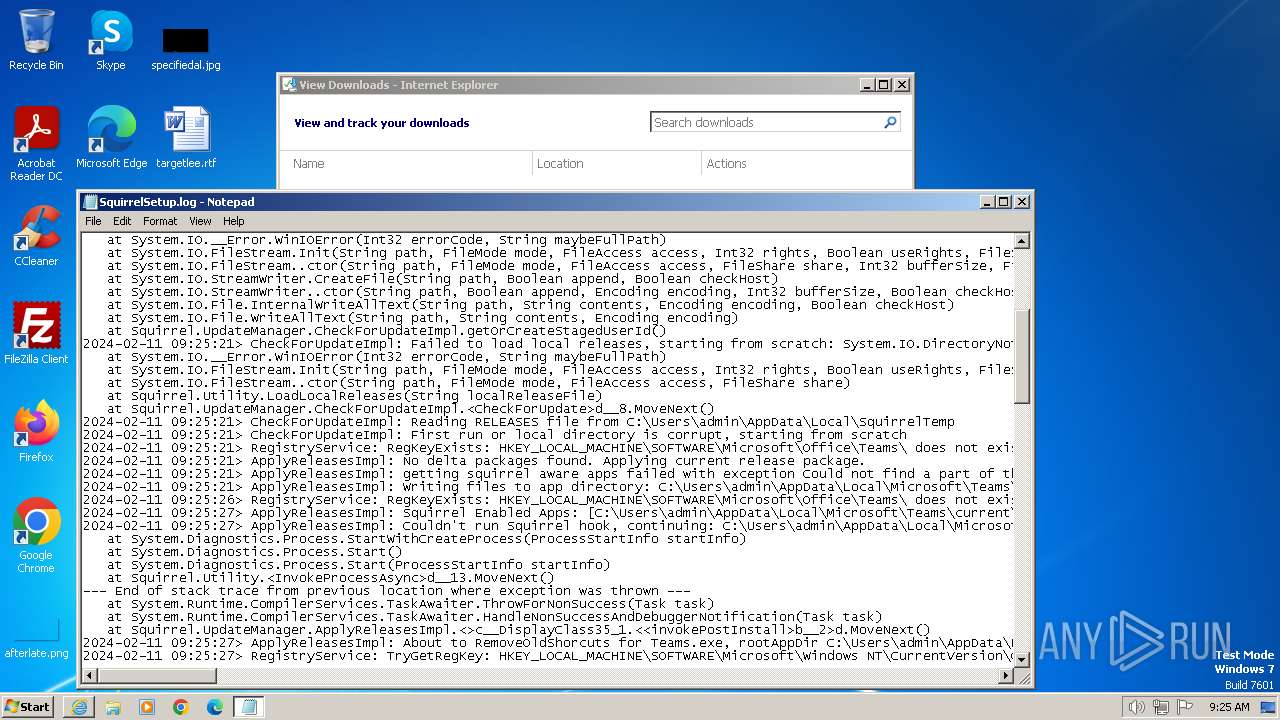
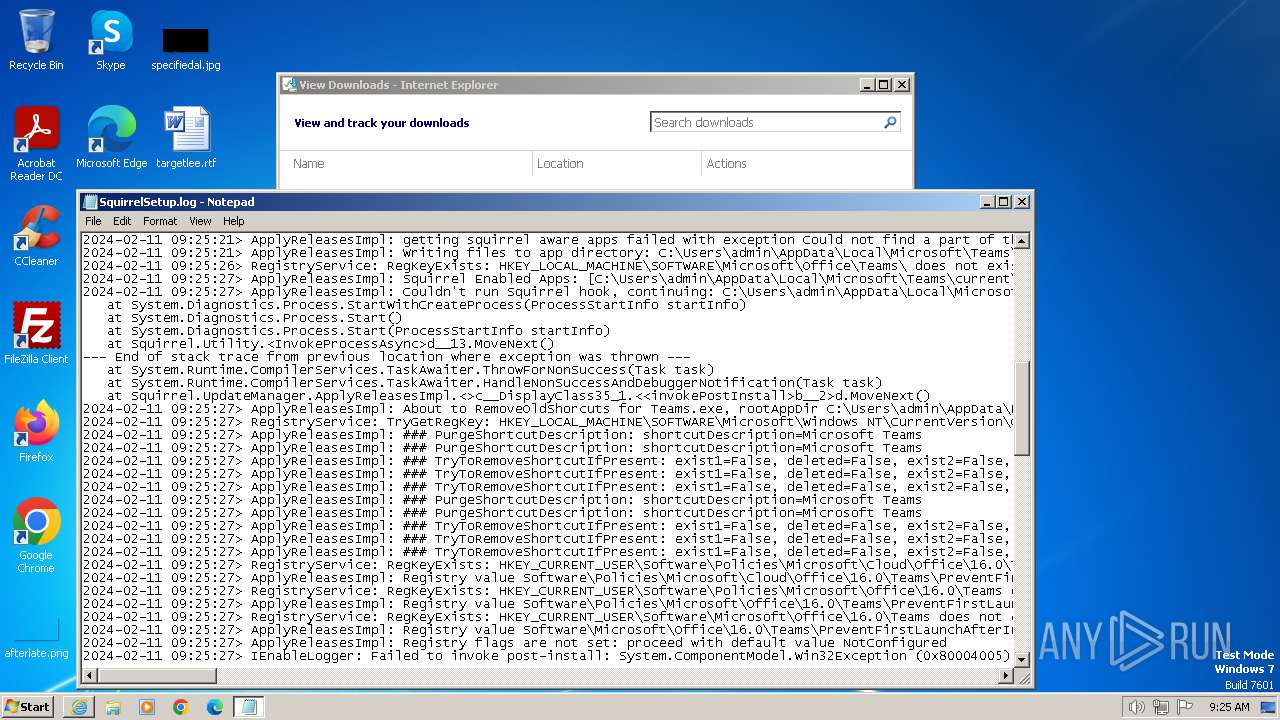
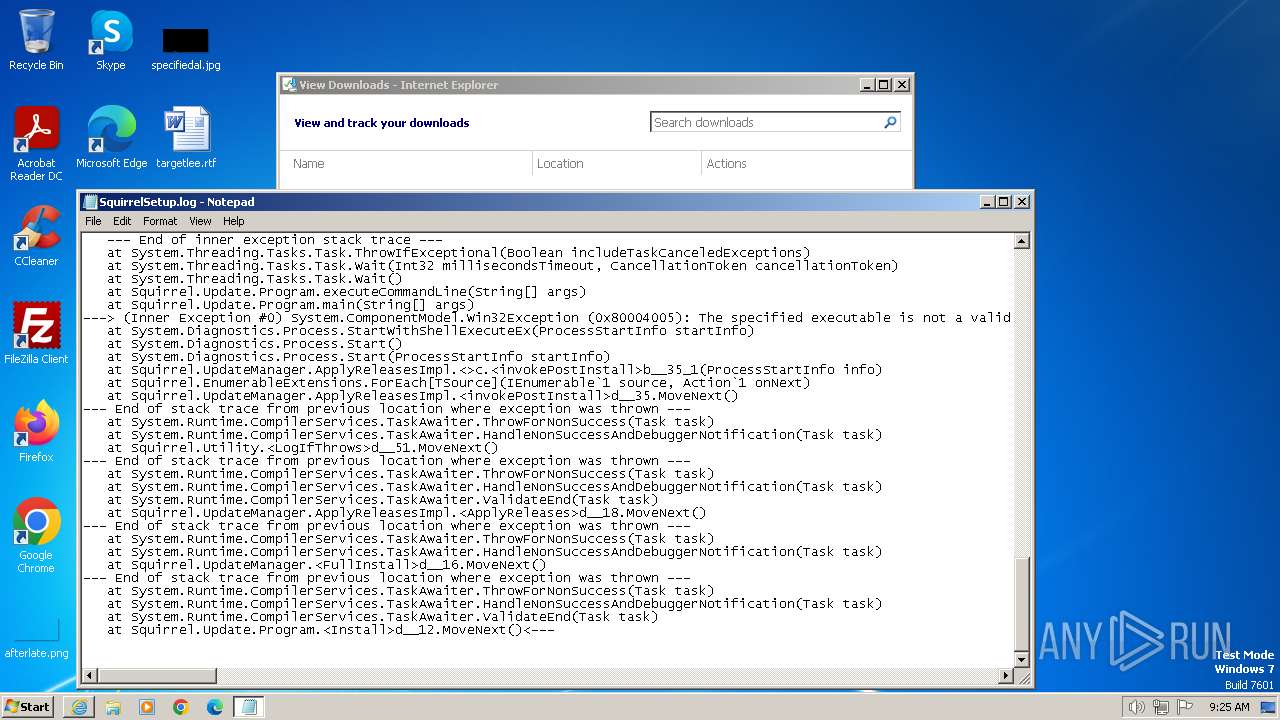
| 2592 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\SquirrelTemp\SquirrelSetup.log | C:\Windows\System32\notepad.exe | — | Teams_windows_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe" --install . --exeName=Teams_windows_x64.exe | C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | Teams_windows_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams classic Exit code: 4294967295 Version: 3.3.11.0 Modules
| |||||||||||||||
| 3068 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Squirrel.exe" --updateSelf=C:\Users\admin\AppData\Local\SquirrelTemp\Update.exe | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Squirrel.exe | Update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams classic Exit code: 0 Version: 3.3.11.0 Modules
| |||||||||||||||
| 3668 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://statics.teams.cdn.office.net/production-windows-x64/1.7.00.1864/Teams_windows_x64.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3972 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3668 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
36 646
Read events
36 459
Write events
152
Delete events
35
Modification events
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31087819 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 256429030 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31087820 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3668) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
222
Suspicious files
131
Text files
123
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EFF7024A782CA19967D35387999EB4E0 | SHA256:823835824B91188C79C55892DBE5C6B3D7E9D2708F9EFAA4B94CE2DF065E679C | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | binary | |
MD5:F0B5C2A24A06C274FA5D30FD3B5C4F32 | SHA256:36B234FFC641448376D58D4893DEF34D9594B301600B905B744405221033A67A | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\Teams_windows_x64[1].exe | executable | |
MD5:D52C5BF74F2E6A353317CDC4A788D442 | SHA256:0679BDBCE48188E84F667FBD61A703F667C3A01CA4E90D7442587ED9708B3643 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_E503B048B745DFA14B81FCFC68D6DECE | der | |
MD5:06A785D09D5A855F53D5DDB13D8E6B04 | SHA256:0F29AED4A95C0D01CB3D184DDEBD58517E8F79BD415D89BB84D97BEACDDECAAF | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:AE042CBB1AC8C1449D76ACCECF94DD81 | SHA256:B186D44EF30080B9D84D7DD60AEE0B63265D192602AE4C5AE33D5048F787D653 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:E941407CC2A8F2CF7A905A6693918BCE | SHA256:DB2766E4E87B1BA4D8D025D73C9F505F7CB25D561F784E0AE7CEEAAE37D3D39B | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver677F.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 3972 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\Teams_windows_x64.exe.v3k9p51.partial | — | |
MD5:— | SHA256:— | |||
| 3668 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\BM55N9RC.txt | text | |
MD5:CE83C1BB4825A749A0B77AE54ABA67F2 | SHA256:E373C11B37562FE3BA18121365C8727E1FE657B46424CA333973173144514461 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
25
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3972 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?f78d505714a595e3 | GB | — | — | unknown |
3668 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b0be6f4ad90be2e5 | GB | — | — | unknown |
3972 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | binary | 471 b | unknown |
3668 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?719f0b64dcb4a601 | GB | — | — | unknown |
3668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | unknown |
3668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | unknown |
3668 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | binary | 471 b | unknown |
3668 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e55f0cb727843010 | GB | — | — | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?89bca2e7018c82c0 | GB | compressed | 65.2 Kb | unknown |
3972 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?545e1839169dd0e6 | GB | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3972 | iexplore.exe | 2.16.164.130:443 | statics.teams.cdn.office.net | Akamai International B.V. | NL | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3972 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3972 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3668 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3668 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3668 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
statics.teams.cdn.office.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
mobile.pipe.aria.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Update.exe | Update.exe Information: 0 : |
Update.exe | Starting TelemetryManager constructor
|
Update.exe | Update.exe Information: 0 : |
Update.exe | TelemetryManagerImpl creation started
|
Update.exe | Update.exe Information: 0 : |
Update.exe | Performance counters are disabled. Skipping creation of counters category.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | RecordBatcherTask with ID 4 started.
|
Update.exe | Update.exe Information: 0 : |
Update.exe | DataPackageSender with UserAgent name: AST-exe-C#, version: 3.3.11.0, [Ast_Default_Source]
|