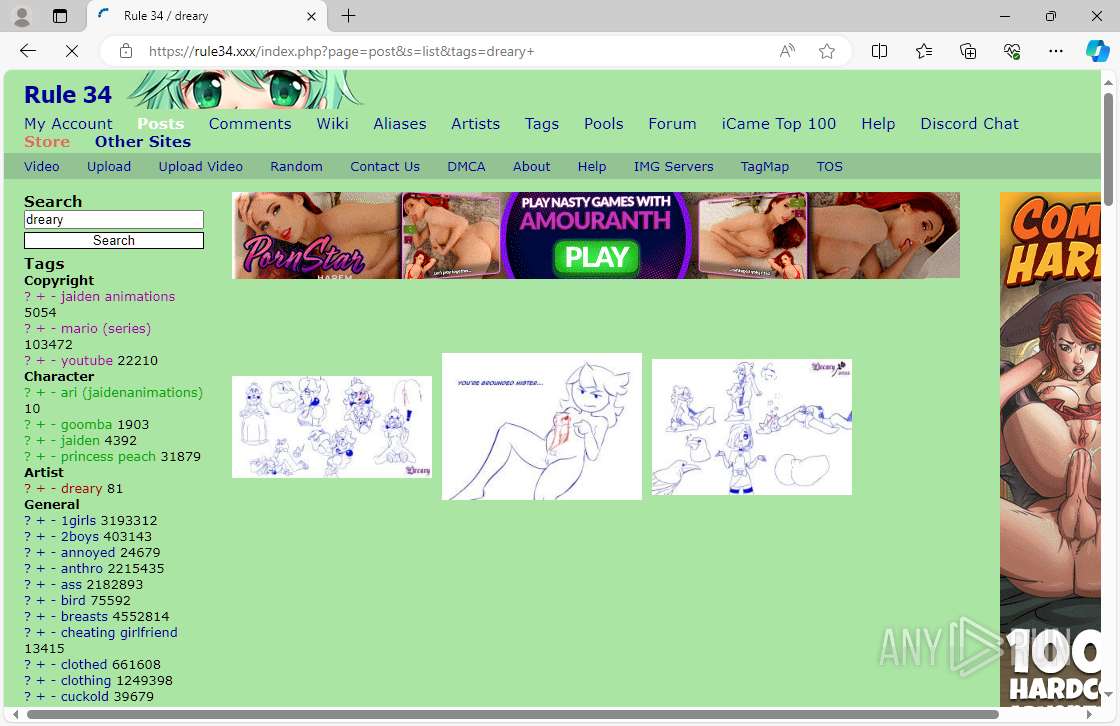
| URL: | Rule34.xxx |
| Full analysis: | https://app.any.run/tasks/3c2397de-81ae-4618-abd2-86ce6dfa4a34 |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 02:43:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| MD5: | 935DE03F1A89D987945646545D0620C0 |
| SHA1: | D037047C41D1E36E012000C804AF0904261B67C4 |
| SHA256: | 902309353F95A129B3CB00BA0D82986AFB939C1587109AF7E432D9819447016B |
| SSDEEP: | 3:Mzvdd:Mzvdd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 4792)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2604 --field-trial-handle=2320,i,16194277592197507296,15814343983252007256,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
108
Text files
26
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000be | binary | |
MD5:0820048F19F41B12EE58BFB903C54D9D | SHA256:5A80F50EF14211BF9F97CA138BF487A6D7D6C17BDF09E9AE4E8C39E38AA66076 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2ba23a.TMP | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\d81682a9-6b4d-4462-b137-8bf25bd0d188.tmp | binary | |
MD5:2A21453795942FD88CBB06714604B9FD | SHA256:5DFE0384325B556EE4B8668E502312B9BA6ADC298CD9213DDFA528CB959ADC06 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000bb | image | |
MD5:547BBB87EDA6F00DF223E1098ACCE4B4 | SHA256:E524CF27E82B10665B3F6F1838A4BA257D94DA793C24B3977C91771CD8662CF9 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\df9c6ed7-a2cf-4909-a82a-234318b9b040.tmp | binary | |
MD5:ED74D0CC3CAB53CA501F3CD6C50FAA1A | SHA256:331BB0DA5A3BE7843A14503DA9547E7309F3631916C6112882FF36D75025E7EE | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RF2b5e8a.TMP | binary | |
MD5:2A21453795942FD88CBB06714604B9FD | SHA256:5DFE0384325B556EE4B8668E502312B9BA6ADC298CD9213DDFA528CB959ADC06 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\ef46b436-ad7e-4260-8473-edae8e099ff4.tmp | binary | |
MD5:BF09D3445757C4FC231A4A1425687536 | SHA256:FB3BECF568EBC3E3B77AA588C548D459926BD51980B169BC6A9BA3F38E175B92 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\TransportSecurity~RF2b8fea.TMP | binary | |
MD5:474C68462189D0F0516CEF6994825A79 | SHA256:5FB793C95FBC237987A3F8B60EAF8592EBCAD78584F927C09438A838F69FB777 | |||
| 4792 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000c3 | compressed | |
MD5:DAF2F2045392C871AB910A13C21A2219 | SHA256:B65AA93D418B0D0234557CFF29FD70640D04D63D1FA5EB8B28706F028D92442C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
334
TCP/UDP connections
169
DNS requests
158
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 184.30.17.174:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | — |
— | — | GET | 200 | 104.16.79.73:443 | https://static.cloudflareinsights.com/beacon.min.js/vcd15cbe7772f49c399c6a5babf22c1241717689176015 | unknown | — | — | — |
6528 | RUXIMICS.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5968 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5968 | svchost.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6528 | RUXIMICS.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4304 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.211.229.248:443 | https://s.magsrv.com/cimp.php?t=api&data=H4sIAAAAAAAAA21OW04DMQy8Chdo5Nc6dv+Q4AKgHiC73eWHgtQVaJF8eJyKQj+IlWgmHnuGgGSHtEO+I9yL7KEGoRZCK44FmePwfB+Ccf54nVnKtm2BzoQUNphwIJoNkAoe6qBJIdhMXDmc0b1WCoFwC7hWAVBAC4d4PDylwUP+uTgGBgUqbAqQuDtHH0+MSLBV0j6vNs5HYncanWrz0ZZZ3LjNyjNmpBTdxL26CmvfVH+DyOAVMtsOf4iLRR6IS7utX29TxF/uGIhJMlCi4D6Tt7NbzX+Fl3ctp/aynj/L9H7KBSjSO9FYjotqawITzjjhaLrQ4tNirVahb4r/n3ajAQAA&scr_info=YXN5bmN8fDM%3D | unknown | — | — | — |
— | — | GET | 200 | 184.30.17.174:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | binary | 55 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5968 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
4792 | msedge.exe | 20.189.173.24:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
6528 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4304 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5988 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4792 | msedge.exe | 104.22.19.113:443 | rule34.xxx | — | — | whitelisted |
4792 | msedge.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5348 | svchost.exe | 184.30.17.174:443 | fs.microsoft.com | AKAMAI-AS | DE | whitelisted |
5968 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
rule34.xxx |
| whitelisted |
fs.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
www.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Potential Corporate Privacy Violation | ET POLICY DNS Query For XXX Adult Site Top Level Domain |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |