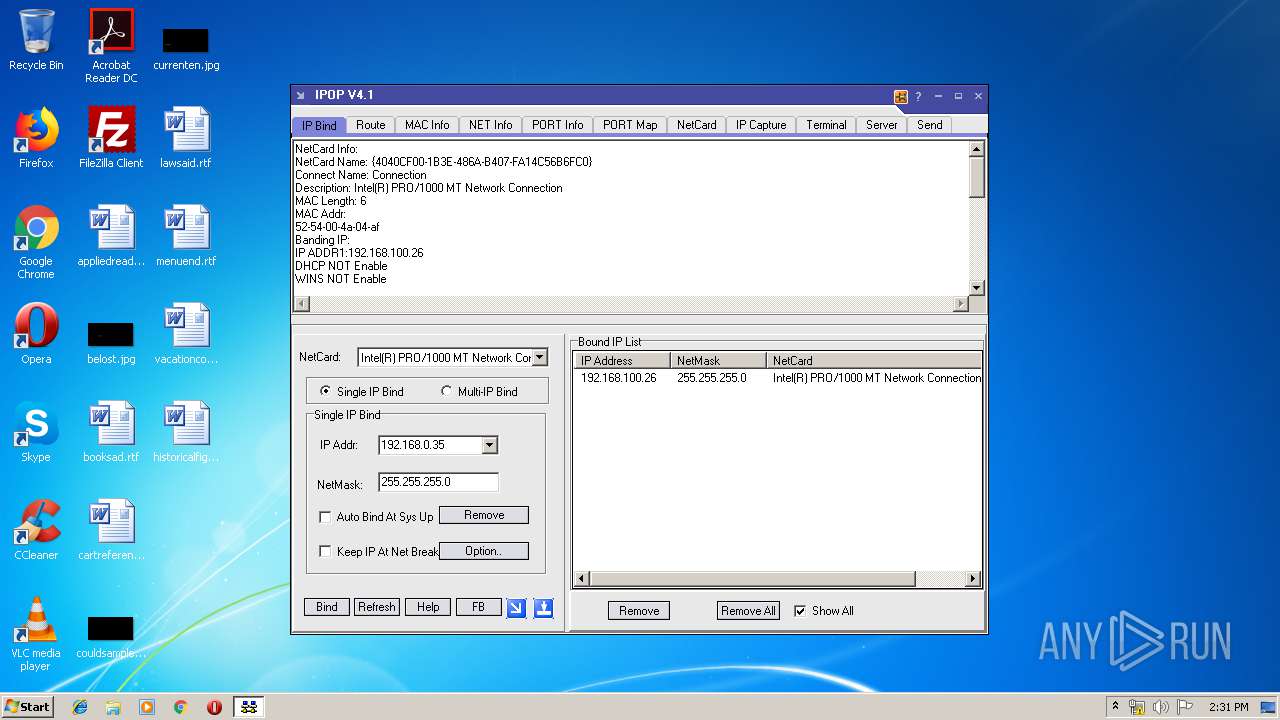
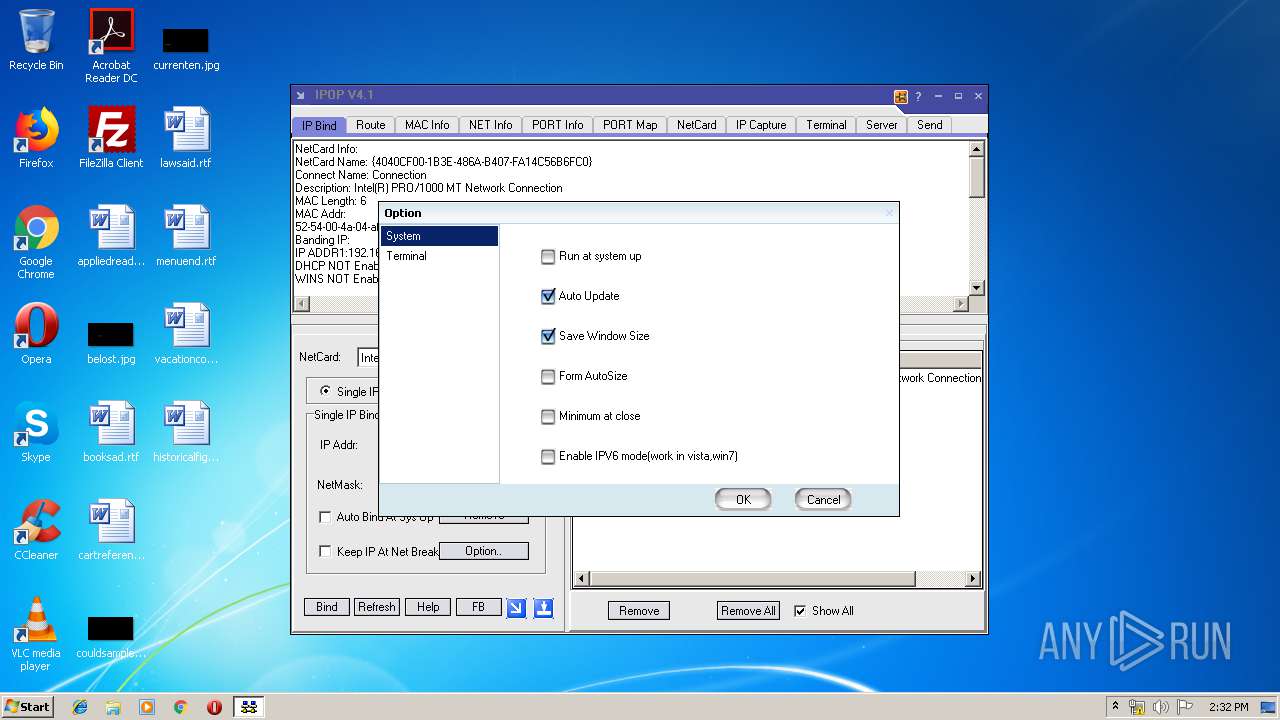
| File name: | IPOP 4.1.EXE |
| Full analysis: | https://app.any.run/tasks/b07ec01b-0807-4651-bcb0-5e632e24640e |
| Verdict: | No threats detected |
| Analysis date: | July 24, 2019, 13:31:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | A4133204F5CAC1555AC39B4B85C703A4 |
| SHA1: | 7AF8898BD146E77D38EA16D1A5DD1CC426E6F636 |
| SHA256: | 9021C54902A0BC8EE49A25E57DE9BA299FC463A09EA550293786D89F0660B6B8 |
| SSDEEP: | 49152:HB/E2LMYjLwcFfHdUyoUqidKHPXoEc1MwvbFfyJIP24N9XZ:h/LLMYj0c/i0KvXoeURfyMx3J |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (75.6) |
|---|---|---|
| .exe | | | InstallShield setup (6.2) |
| .exe | | | Win32 EXE PECompact compressed (generic) (6) |
| .exe | | | UPX compressed Win32 Executable (3.9) |
| .exe | | | Win32 EXE Yoda's Crypter (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:07:24 08:14:58+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 2002944 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | 5644288 |
| EntryPoint: | 0x7f0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.1.0.0 |
| ProductVersionNumber: | 4.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | Bowlder Studio |
| FileDescription: | IPOP V4.0 |
| FileVersion: | 4.1.0.0 |
| InternalName: | - |
| LegalCopyright: | ThinkSoft系列软件之一 |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| ProductName: | IPOP |
| ProductVersion: | 4.1.0.0 |
| Comments: | 维护:袁文波,Notes:118932,E-Mail:ywb94@sohu.com |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jul-2012 06:14:58 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 24-Jul-2012 06:14:58 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00562000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00563000 | 0x001E9000 | 0x001E8C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.92852 |
.rsrc | 0x007E9000 | 0x00000338 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.876563 |
.pe | 0x00759000 | 0x00001000 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.804324 |
.text | 0x0075A000 | 0x00071BDE | 0x00072000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.50571 |
.rdata | 0x007CC000 | 0x0000884F | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.61689 |
.data | 0x007D5000 | 0x00013FF0 | 0x00013000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.73663 |
.reloc | 0x007EA000 | 0x0000523C | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.08529 |
pebundle | 0x007F0000 | 0x00002000 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.82754 |
Imports
KERNEL32.DLL |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1600 | "C:\Users\admin\AppData\Local\Temp\IPOP 4.1.EXE" | C:\Users\admin\AppData\Local\Temp\IPOP 4.1.EXE | explorer.exe | ||||||||||||
User: admin Company: Bowlder Studio Integrity Level: HIGH Description: IPOP V4.0 Exit code: 0 Version: 4.1.0.0 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\Temp\IPOP 4.1.EXE" | C:\Users\admin\AppData\Local\Temp\IPOP 4.1.EXE | — | explorer.exe | |||||||||||
User: admin Company: Bowlder Studio Integrity Level: MEDIUM Description: IPOP V4.0 Exit code: 3221226540 Version: 4.1.0.0 Modules
| |||||||||||||||
Total events
30
Read events
10
Write events
20
Delete events
0
Modification events
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA} |
| Operation: | write | Name: | |
Value: app Object | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA}\LocalServer32 |
| Operation: | write | Name: | |
Value: C:\Users\admin\AppData\Local\Temp\IPOP41~1.EXE /Automation | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA}\LocalServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IPOP.app |
| Operation: | write | Name: | |
Value: app Object | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\IPOP.app\CLSID |
| Operation: | write | Name: | |
Value: {B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA} | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA}\ProgID |
| Operation: | write | Name: | |
Value: IPOP.app | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA}\Version |
| Operation: | write | Name: | |
Value: 1.0 | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{B7C389C1-1D29-44C2-9DCB-1CF8BD8D71EA}\Typelib |
| Operation: | write | Name: | |
Value: {9FEC2353-5242-41C1-B22C-3B4DF740B456} | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{9FEC2353-5242-41C1-B22C-3B4DF740B456}\1.0 |
| Operation: | write | Name: | |
Value: IPOP Library | |||
| (PID) Process: | (1600) IPOP 4.1.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\TypeLib\{9FEC2353-5242-41C1-B22C-3B4DF740B456}\1.0\FLAGS |
| Operation: | write | Name: | |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
IPOP 4.1.EXE | wsocket.pas initialization section |