| File name: | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe |
| Full analysis: | https://app.any.run/tasks/37350f33-3cfb-4ab8-9b77-31022398ad3d |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2021, 10:47:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 432000C703C29E2B71838484D858CBD1 |
| SHA1: | B6B5CFD7FA8556810BBB5D758A38CCAF072F865F |
| SHA256: | 90084E0803417ADA8BDC29A7920D7E159C77C2A76C32139652126D8ECD9D4CAE |
| SSDEEP: | 196608:xDz+w58+AWU89s3N5wKBC2IIt1KFbYCa1WwDz+w58+AWd:QWU8W3rw2IQUb1OaWd |
MALICIOUS
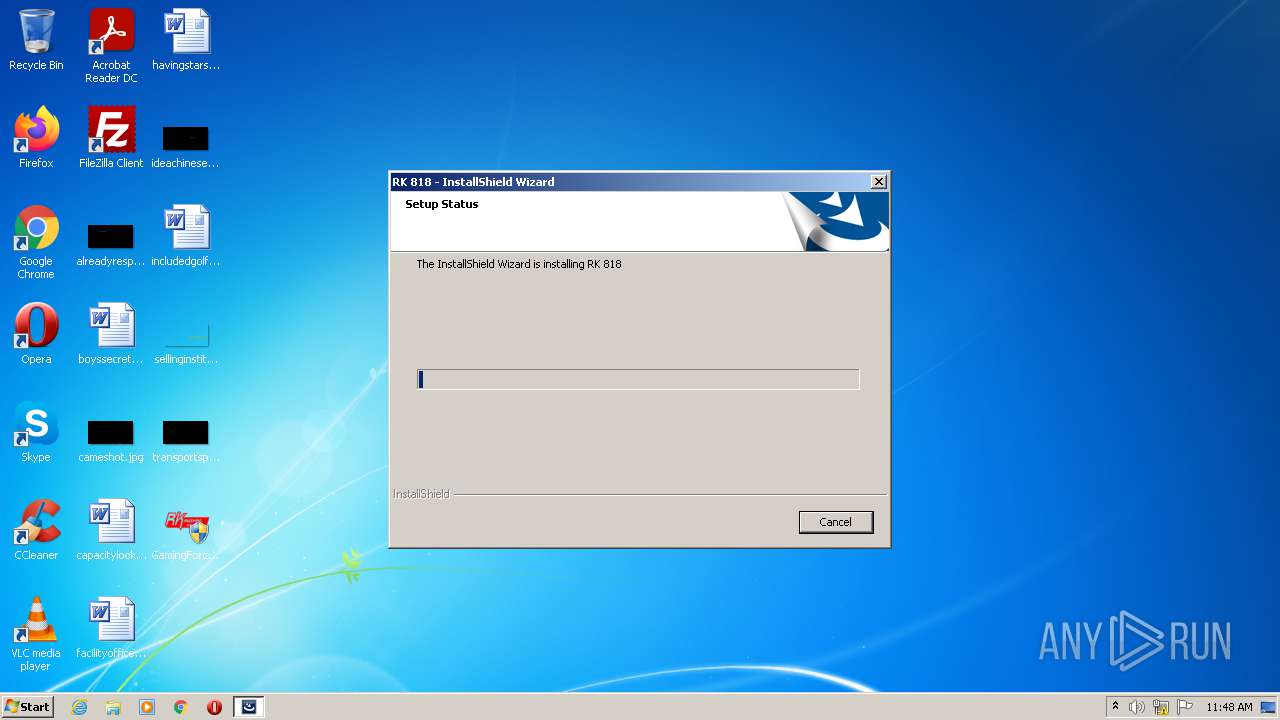
Loads dropped or rewritten executable
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Drops executable file immediately after starts
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
SUSPICIOUS
Executable content was dropped or overwritten
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Reads the computer name
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
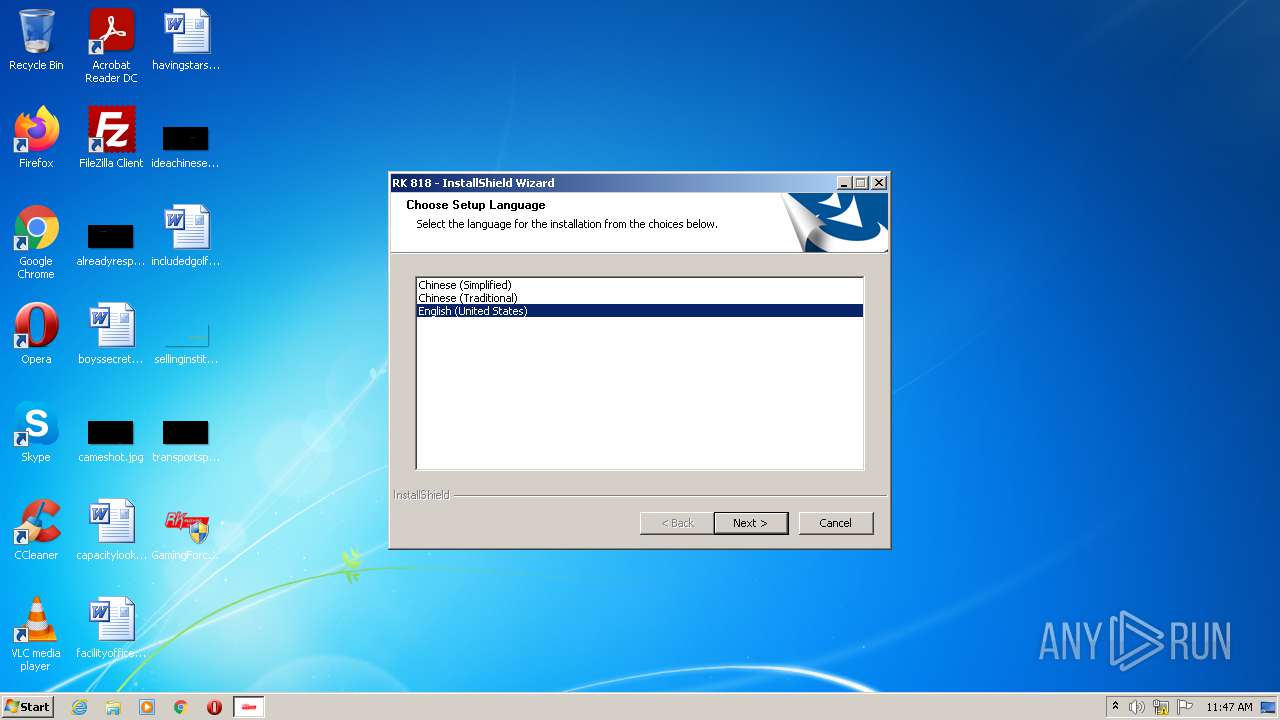
Checks supported languages
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Reads Windows owner or organization settings
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Uses TASKKILL.EXE to kill process
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Reads the Windows organization settings
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Drops a file that was compiled in debug mode
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
Executed as Windows Service
- vssvc.exe (PID: 1868)
Reads Environment values
- vssvc.exe (PID: 1868)
Searches for installed software
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
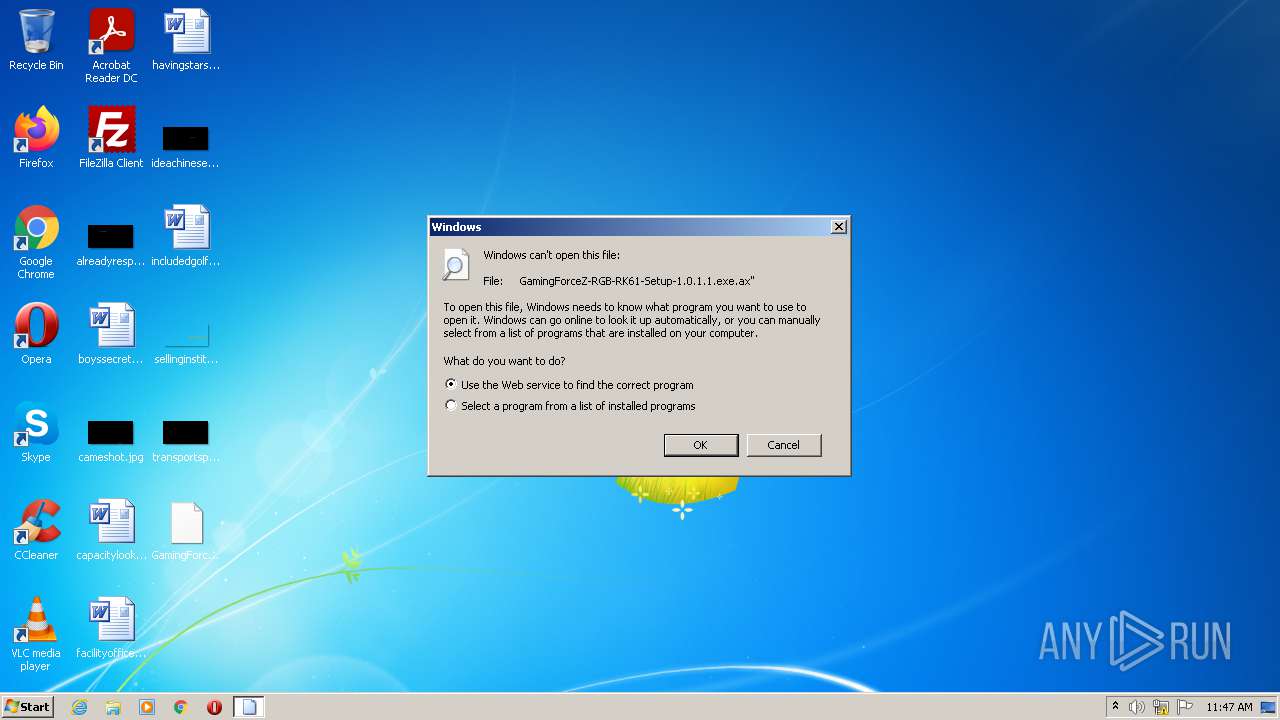
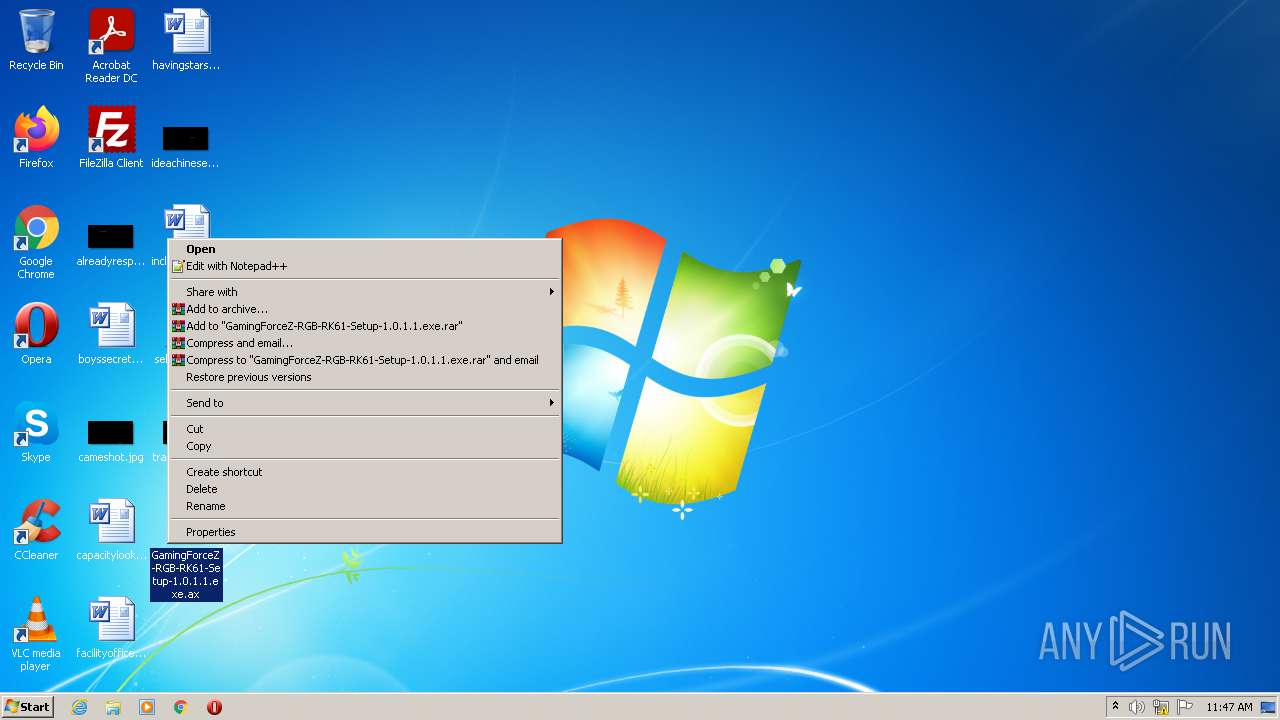
INFO
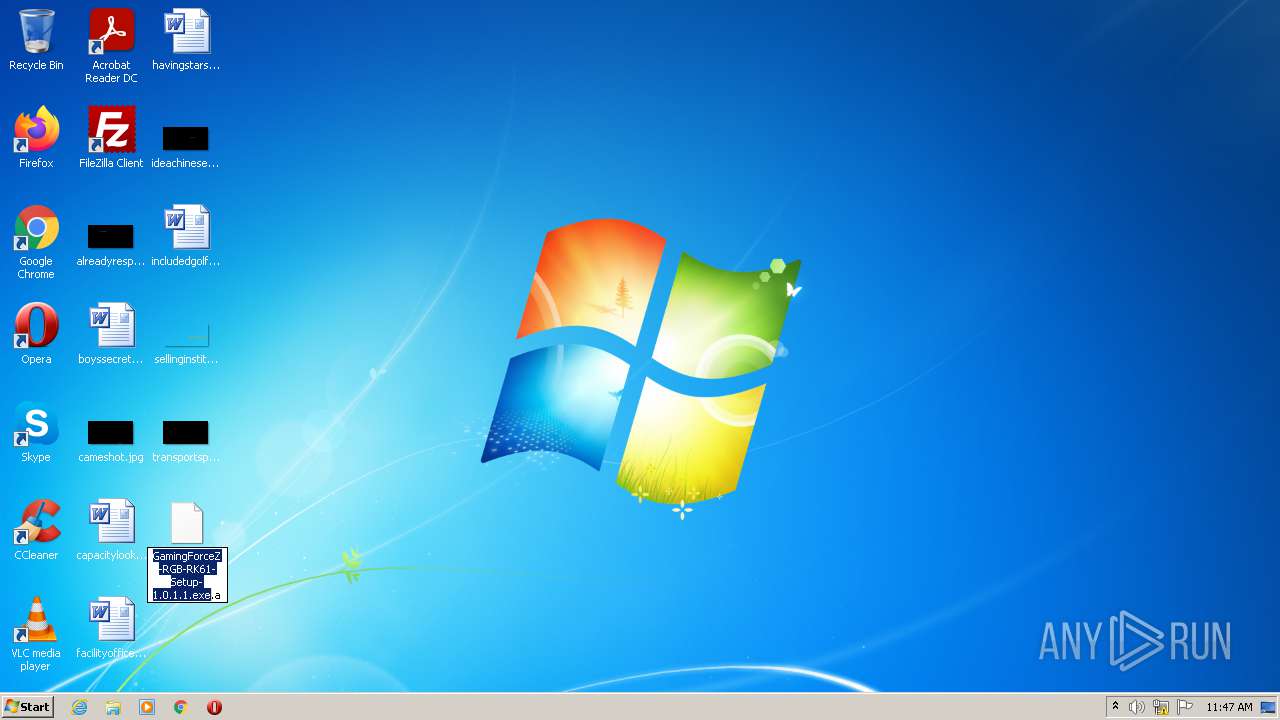
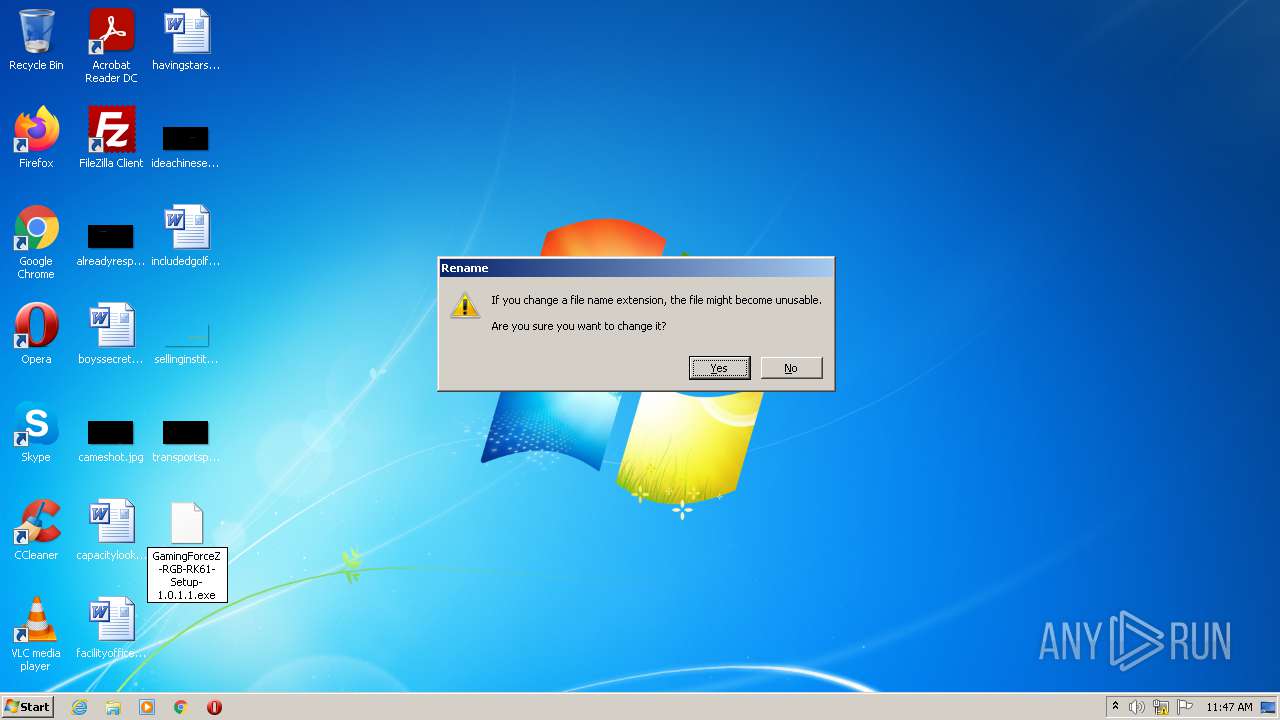
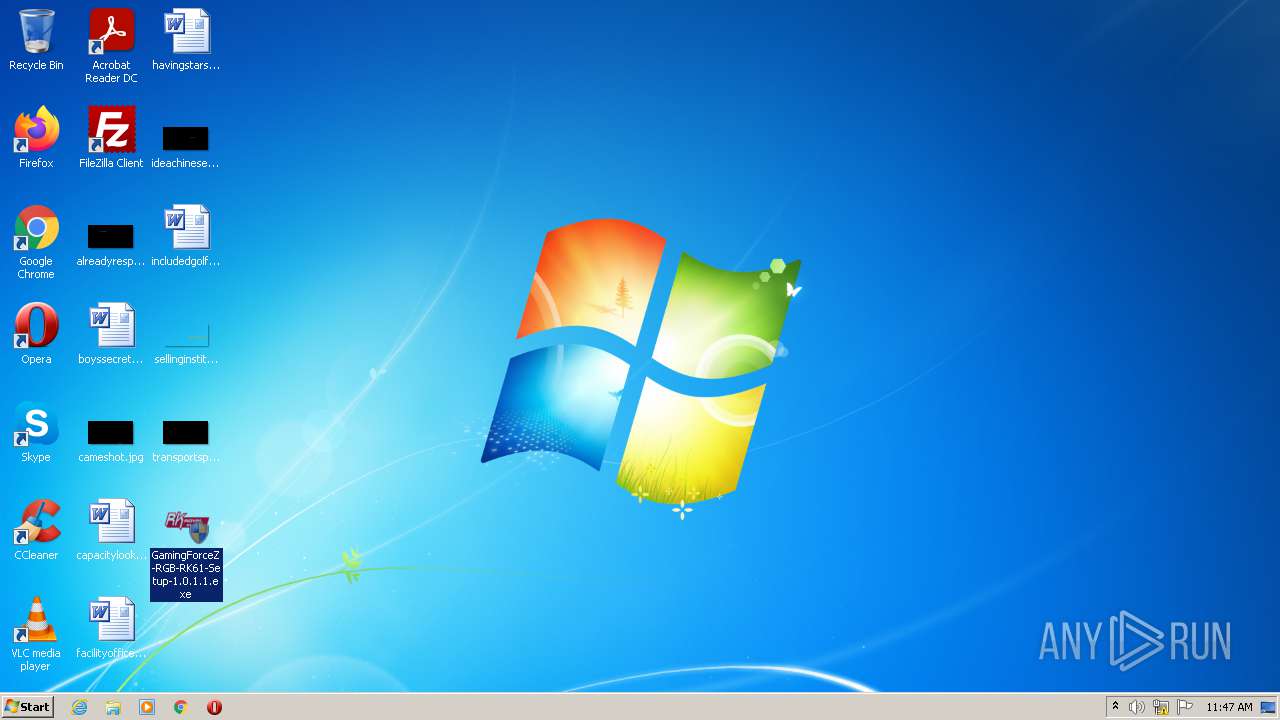
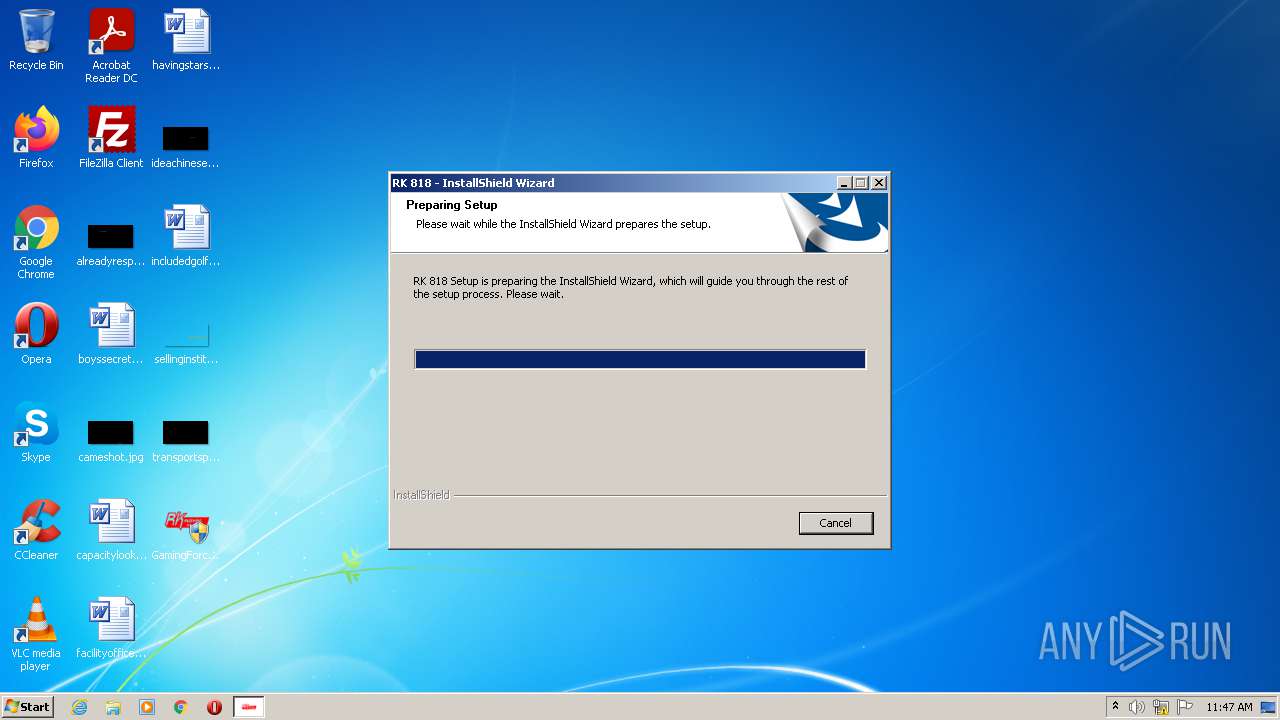
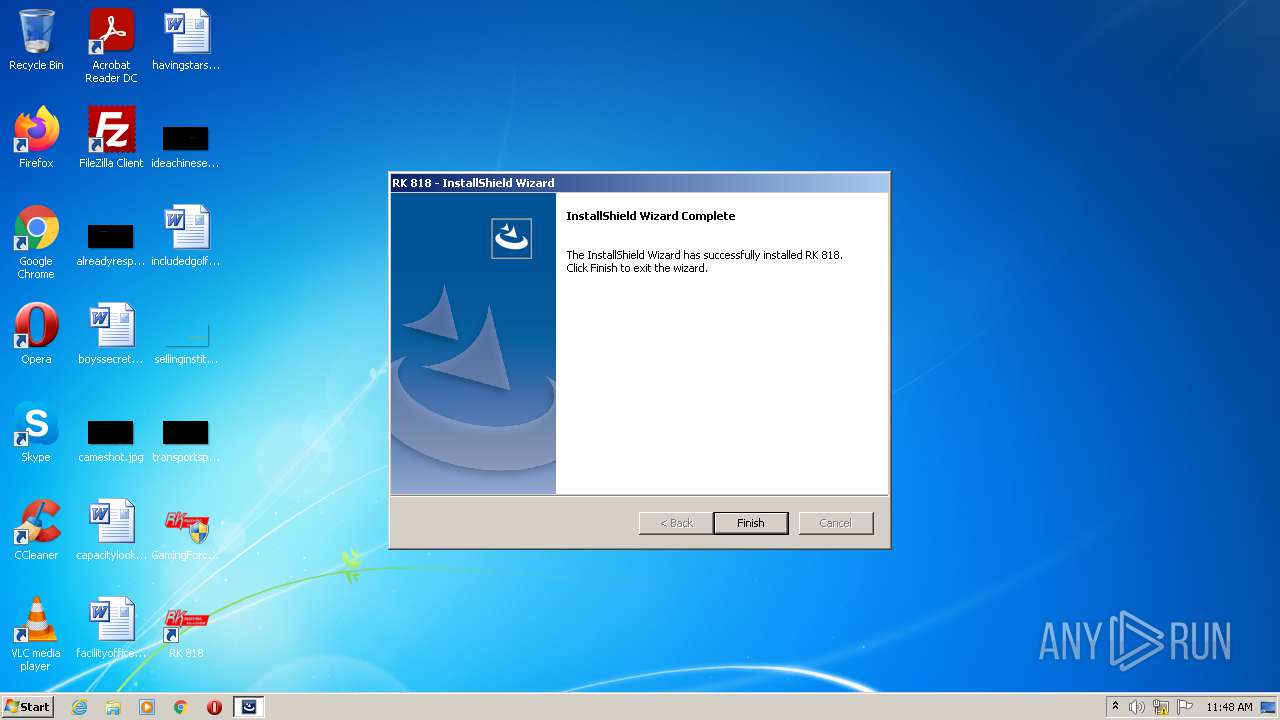
Manual execution by user
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 3760)
- GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe (PID: 2416)
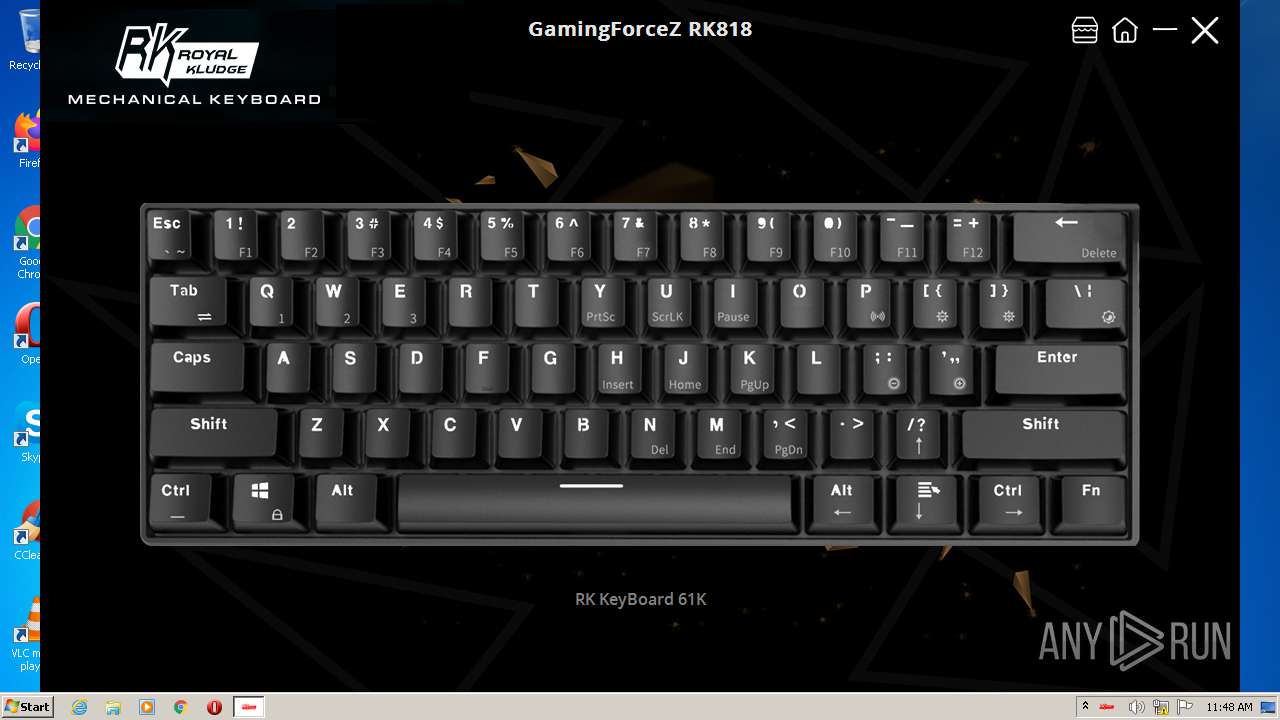
- DeviceDriver.exe (PID: 3936)
Checks supported languages
- rundll32.exe (PID: 1840)
- taskkill.exe (PID: 3140)
- vssvc.exe (PID: 1868)
Reads the computer name
- taskkill.exe (PID: 3140)
- vssvc.exe (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (43) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (v2.x) (12.6) |
| .exe | | | Win32 EXE PECompact compressed (generic) (8.8) |
| .exe | | | Win64 Executable (generic) (5.9) |
EXIF
EXE
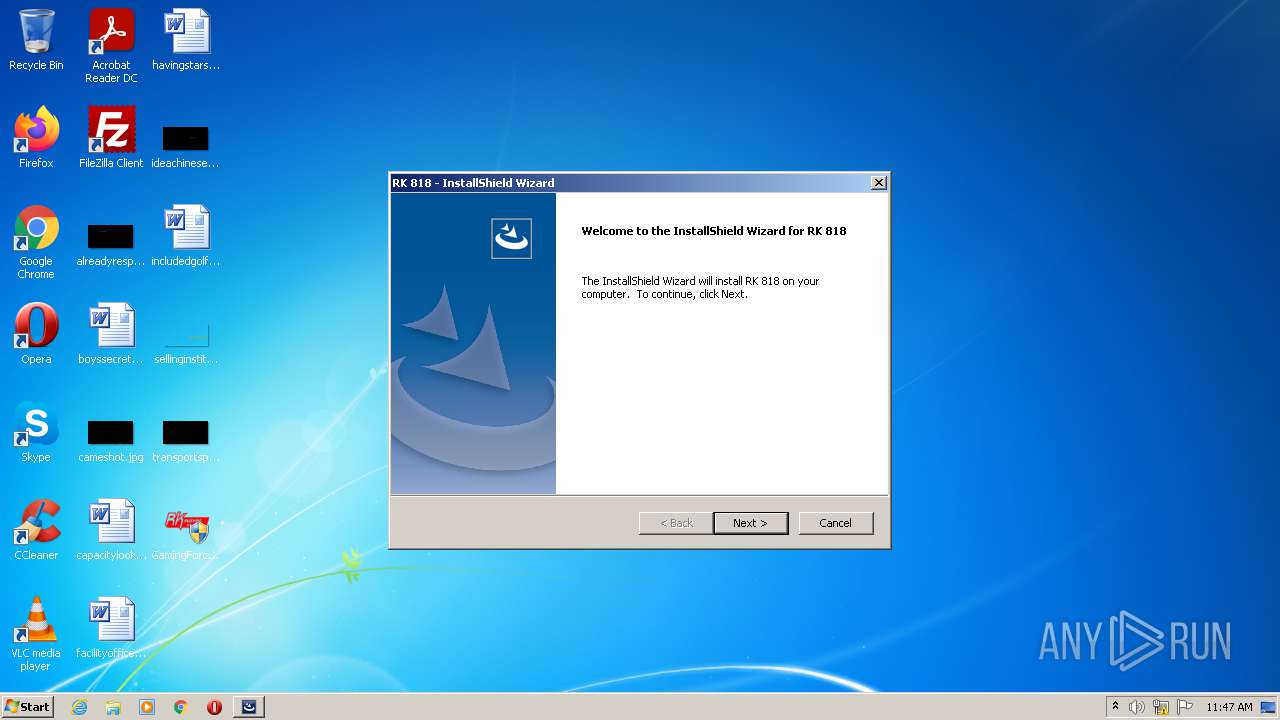
| ISInternalDescription: | InstallScript Setup Launcher Unicode |
|---|---|
| ISInternalVersion: | 22.0.284 |
| InternalBuildNumber: | 154432 |
| ProductVersion: | 1.0.1.1 |
| ProductName: | RK 818 |
| OriginalFileName: | InstallShield Setup.exe |
| LegalCopyright: | Copyright (c) 2015 Flexera Software LLC. All Rights Reserved. |
| InternalName: | Setup |
| FileVersion: | 1.0.1.1 |
| FileDescription: | InstallScript Setup Launcher Unicode |
| CompanyName: | RK |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.1.1 |
| FileVersionNumber: | 1.0.1.1 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x5e1af |
| UninitializedDataSize: | - |
| InitializedDataSize: | 512512 |
| CodeSize: | 702976 |
| LinkerVersion: | 11 |
| PEType: | PE32 |
| TimeStamp: | 2015:06:08 05:57:36+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Jun-2015 03:57:36 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | RK |
| FileDescription: | InstallScript Setup Launcher Unicode |
| FileVersion: | 1.0.1.1 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2015 Flexera Software LLC. All Rights Reserved. |
| OriginalFilename: | InstallShield Setup.exe |
| ProductName: | RK 818 |
| ProductVersion: | 1.0.1.1 |
| Internal Build Number: | 154432 |
| ISInternalVersion: | 22.0.284 |
| ISInternalDescription: | InstallScript Setup Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-Jun-2015 03:57:36 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000AB81B | 0x000ABA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53923 |
.rdata | 0x000AD000 | 0x00028426 | 0x00028600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.19029 |
.data | 0x000D6000 | 0x00004BE4 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.35285 |
.rsrc | 0x000DB000 | 0x00052404 | 0x00052600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.03198 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09026 | 775 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.78476 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.83967 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.31832 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.88702 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 1.3404 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 1.43556 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 1.47777 | 6760 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 1.48913 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 1.61806 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
LZ32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
Total processes
48
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1840 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\Desktop\GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe.ax" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1868 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\Desktop\GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe" | C:\Users\admin\Desktop\GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | Explorer.EXE | ||||||||||||
User: admin Company: RK Integrity Level: HIGH Description: InstallScript Setup Launcher Unicode Exit code: 0 Version: 1.0.1.1 Modules
| |||||||||||||||
| 3140 | "C:\Windows\system32\taskkill.exe " /f /im "DeviceDriver.exe" | C:\Windows\system32\taskkill.exe | — | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3760 | "C:\Users\admin\Desktop\GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe" | C:\Users\admin\Desktop\GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | — | Explorer.EXE | |||||||||||
User: admin Company: RK Integrity Level: MEDIUM Description: InstallScript Setup Launcher Unicode Exit code: 3221226540 Version: 1.0.1.1 Modules
| |||||||||||||||
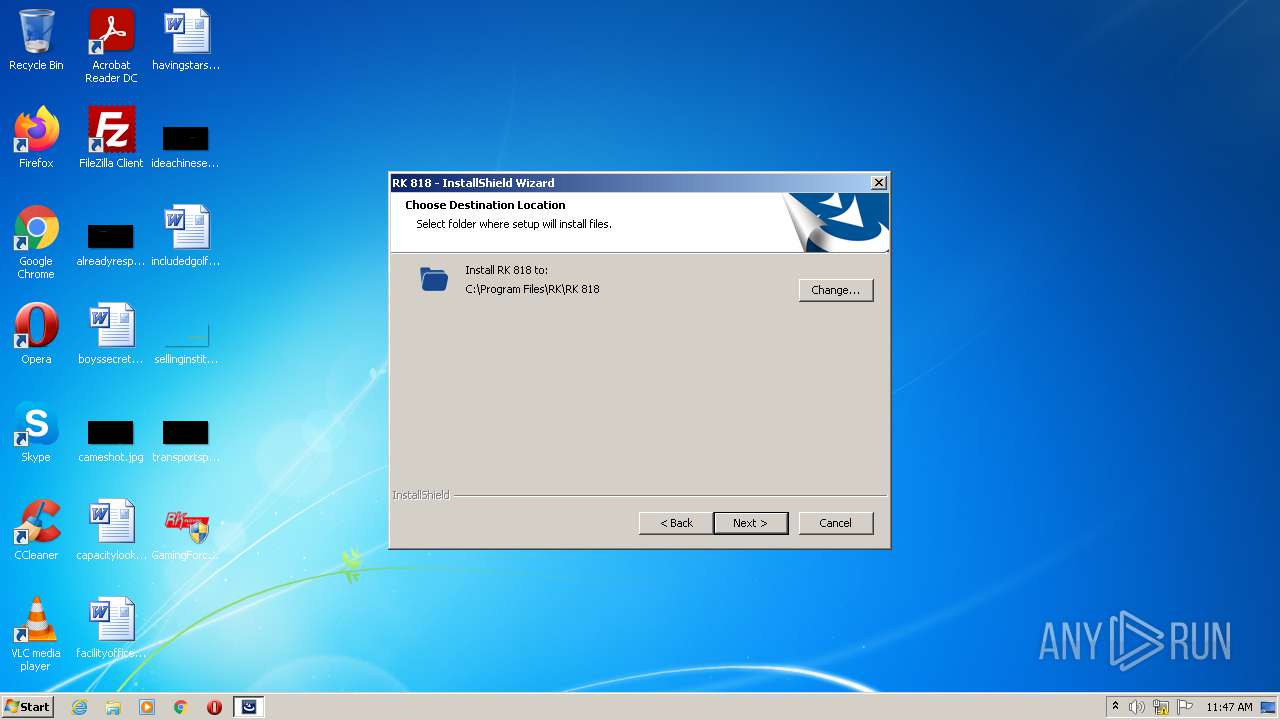
| 3936 | "C:\Program Files\RK\RK 818\DeviceDriver.exe" | C:\Program Files\RK\RK 818\DeviceDriver.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.1.1 Modules
| |||||||||||||||
Total events
1 441
Read events
1 277
Write events
164
Delete events
0
Modification events
| (PID) Process: | (2416) GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000C2A5425431A6D7017009000060090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2416) GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000C2A5425431A6D7017009000060090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2416) GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 68 | |||
| (PID) Process: | (2416) GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000F4C9875431A6D7017009000060090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2416) GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000004E2C8A5431A6D70170090000200C0000E8030000010000000000000000000000A447024E076E5E42BA5EBC41A58E289E0000000000000000 | |||
| (PID) Process: | (1868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001018965431A6D7014C070000780F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001018965431A6D7014C070000540A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001018965431A6D7014C070000DC0A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000001018965431A6D7014C07000028090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1868) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000C4DC9A5431A6D7014C070000540A0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
16
Suspicious files
20
Text files
214
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{9D278972-57B3-4496-BCE8-19502E71E706}\Disk1\ISSetup.dll | executable | |
MD5:1E032A0608412C89627523B534E39379 | SHA256:0EC17D0E628CD5C9475C88164C642C6FE62322CA62FACB0C3937029A39099D31 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{9D278972-57B3-4496-BCE8-19502E71E706}\Disk1\0x0804.ini | text | |
MD5:6F4C6D5B044895684A1E11BFE98B2ABD | SHA256:792E2ED82640E22F9D86F19EC34FD4BB89450B8B874EDEB4FDCBE07935A63110 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{9D278972-57B3-4496-BCE8-19502E71E706}\Disk1\layout.bin | binary | |
MD5:D65125888477E3B6C6C7CA2C46E4D92A | SHA256:18C0E447FA038180275129240C990D3879C8CCD7733929CC172F5DD3A40E3C71 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{9D278972-57B3-4496-BCE8-19502E71E706}\Disk1\data1.hdr | compressed | |
MD5:ACED3CF9D6865464C52D9E83EF4B3F40 | SHA256:AB5662DF987CBD82470AB511BE66907F62324563D24EEA27AF2D3710E154FCDE | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{78E97268-2F93-4DB3-9037-3FE357B32F78}\{AFBC646C-1994-4B5E-85A0-B35C6C8BD849}\Fon99EE.tmp | text | |
MD5:8CE28395A49EB4ADA962F828ECA2F130 | SHA256:A7E91B042CE33490353C00244C0420C383A837E73E6006837A60D3C174102932 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{78E97268-2F93-4DB3-9037-3FE357B32F78}\{AFBC646C-1994-4B5E-85A0-B35C6C8BD849}\FontData.ini | text | |
MD5:8CE28395A49EB4ADA962F828ECA2F130 | SHA256:A7E91B042CE33490353C00244C0420C383A837E73E6006837A60D3C174102932 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{78E97268-2F93-4DB3-9037-3FE357B32F78}\{AFBC646C-1994-4B5E-85A0-B35C6C8BD849}\lic99ED.tmp | text | |
MD5:E7EB45E877C8CB80F56E9DBC9504E757 | SHA256:2301902EC24434DD7475A3823902851B4BC66D23B25281392E4E310223F7A706 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{78E97268-2F93-4DB3-9037-3FE357B32F78}\{AFBC646C-1994-4B5E-85A0-B35C6C8BD849}\license.rtf | text | |
MD5:E7EB45E877C8CB80F56E9DBC9504E757 | SHA256:2301902EC24434DD7475A3823902851B4BC66D23B25281392E4E310223F7A706 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{9D278972-57B3-4496-BCE8-19502E71E706}\Disk1\setup.exe | executable | |
MD5:D2EF6BEA56C41155073C45EE644FD7A6 | SHA256:7F39603D9C75E586CF96F96DC7399333047FC5E88344568EC1859971B4DBECC2 | |||
| 2416 | GamingForceZ-RGB-RK61-Setup-1.0.1.1.exe | C:\Users\admin\AppData\Local\Temp\{9D278972-57B3-4496-BCE8-19502E71E706}\Disk1\0x0404.ini | text | |
MD5:D2375044346BA50DD1E3F1208185FD0E | SHA256:CDDB0BBF712C57ACC6B8AD2D20514B25331A93FD1B95C1A2155C2F670A5C5CEA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report